在 Firepower 设备上配置 FTD 高可用性
非歧视性语言
此产品的文档集力求使用非歧视性语言。在本文档集中,非歧视性语言是指不隐含针对年龄、残障、性别、种族身份、族群身份、性取向、社会经济地位和交叉性的歧视的语言。由于产品软件的用户界面中使用的硬编码语言、基于 RFP 文档使用的语言或引用的第三方产品使用的语言,文档中可能无法确保完全使用非歧视性语言。 深入了解思科如何使用包容性语言。
关于此翻译
思科采用人工翻译与机器翻译相结合的方式将此文档翻译成不同语言,希望全球的用户都能通过各自的语言得到支持性的内容。 请注意:即使是最好的机器翻译,其准确度也不及专业翻译人员的水平。 Cisco Systems, Inc. 对于翻译的准确性不承担任何责任,并建议您总是参考英文原始文档(已提供链接)。
简介
本文档介绍如何在 FPR9300 上配置和验证 Firepower Threat Defense (FTD) 高可用性 (HA) (主用/备用故障切换)。
先决条件
要求
本文档没有任何特定的要求。
使用的组件
本文档中的信息基于以下软件和硬件版本:
- 2xCisco Firepower 9300 安全设备 - FXOS SW 2.0(1.23)
- FTD版本10.10.1.1(内部版本1023)
- Firepower 管理中心 (FMC) - SW 10.10.1.1 (build 1023)
本文档中的信息都是基于特定实验室环境中的设备编写的。本文档中使用的所有设备最初均采用原始(默认)配置。如果您的网络处于活动状态,请确保您了解所有命令的潜在影响。
注意:在带有FTD的FPR9300设备上,只能配置机箱间HA。HA 配置中的两台设备必须满足此处提到的条件。
任务1.检验条件
任务要求:
验证两台FTD设备均符合注释要求并可配置为HA设备。
解决方案:
步骤1:连接到FPR9300管理IP并验证模块硬件。
验证 FPR9300-1 硬件。
KSEC-FPR9K-1-A# show server inventory Server Equipped PID Equipped VID Equipped Serial (SN) Slot Status Ackd Memory (MB) Ackd Cores ------- ------------ ------------ -------------------- ---------------- ---------------- ---------- 1/1 FPR9K-SM-36 V01 FLM19216KK6 Equipped 262144 36 1/2 FPR9K-SM-36 V01 FLM19206H71 Equipped 262144 36 1/3 FPR9K-SM-36 V01 FLM19206H7T Equipped 262144 36 KSEC-FPR9K-1-A#
验证 FPR9300-2 硬件。
KSEC-FPR9K-2-A# show server inventory Server Equipped PID Equipped VID Equipped Serial (SN) Slot Status Ackd Memory (MB) Ackd Cores ------- ------------ ------------ -------------------- ---------------- ---------------- ---------- 1/1 FPR9K-SM-36 V01 FLM19206H9T Equipped 262144 36 1/2 FPR9K-SM-36 V01 FLM19216KAX Equipped 262144 36 1/3 FPR9K-SM-36 V01 FLM19267A63 Equipped 262144 36 KSEC-FPR9K-2-A#
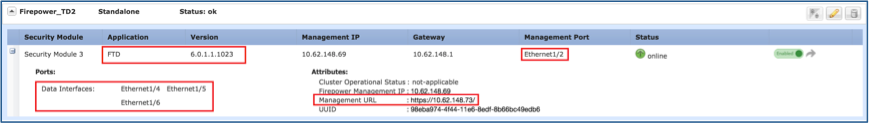
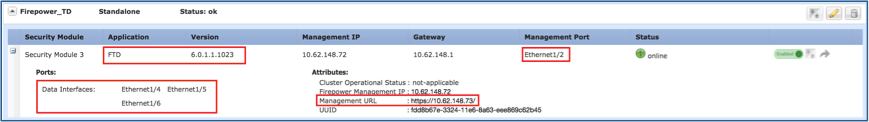
第二步:登录到FPR9300-1机箱管理器,然后导航到逻辑设备。
验证软件版本、编号和接口类型,如图所示。
FPR9300-1
FPR9300-2
任务2.在FPR9300上配置FTD HA
任务要求:
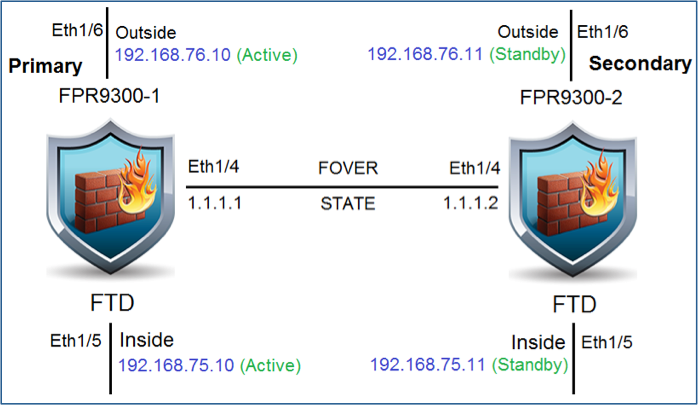
根据此图配置主用/备用故障切换 (HA) 。
解决方案:
两台 FTD 设备都已在 FMC 上注册,如下图所示。

步骤1:要配置FTD故障切换,请导航到设备>设备管理,然后选择添加高可用性,如图所示。

第二步:输入Primary Peer和Secondary Peer,然后选择Continue,如图所示。
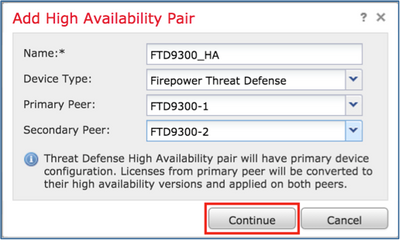
警告:确保选择正确的设备作为主设备。所选主设备上的所有配置都将复制到所选辅助FTD设备。通过复制,可以替换辅助设备上的当前配置。
条件
若要在两台 FTD 设备之间创建 HA,必须满足以下条件:
- 相同型号
- 相同版本 — 这适用于FXOS和FTD — 主要(第一个号码)、次要(第二个号码)和维护(第三个号码)必须相等。
- 相同数量的接口数
- 相同类型的接口
- 两台设备作为FMC中同一组/域的一部分。
- 具有相同的网络时间协议(NTP)配置。
- 在FMC上完全部署,无未提交的更改。
- 处于相同的防火墙模式:路由或透明。

注:必须在FTD设备和FMC GUI上检查此项,因为已经存在过FTD具有相同模式但FMC不反映此模式的情况。
- 所有接口中均未配置DHCP/以太网点对点协议(PPPoE)。
- 两个机箱的不同主机名[完全限定域名(FQDN)]。要检查机箱主机名,请导航至FTD CLI并运行以下命令:
firepower# show chassis-management-url https://KSEC-FPR9K-1.cisco.com:443//
注意:在6.3以后FTD中,使用show chassis detail命令。
firepower# show chassis detail Chassis URL : https://KSEC-FPR4100-1:443// Chassis IP : 192.0.2.1 Chassis Serial Number : JMX12345678 Security Module : 1
如果两个机箱的名称相同,请使用以下命令更改其中一个机箱的名称:
KSEC-FPR9K-1-A# scope system KSEC-FPR9K-1-A /system # set name FPR9K-1new Warning: System name modification changes FC zone name and redeploys them non-disruptively KSEC-FPR9K-1-A /system* # commit-buffer FPR9K-1-A /system # exit FPR9K-1new-A#
更改机箱名称后,从 FMC 上注销 FTD 并重新注册。然后继续创建 HA 对。
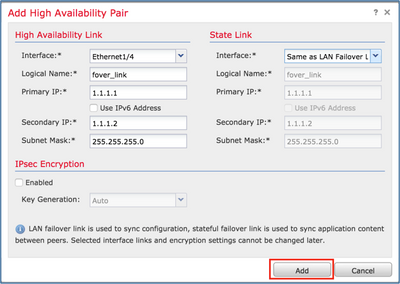
第三步:配置HA并声明链路设置。
在本例中,状态链路与高可用性链路采用相同的设置。
选择Add并等待几分钟,以便按图中所示部署HA对。
第四步:配置数据接口(主要和备用IP地址)
从FMC GUI中,选择HA Edit,如图所示。

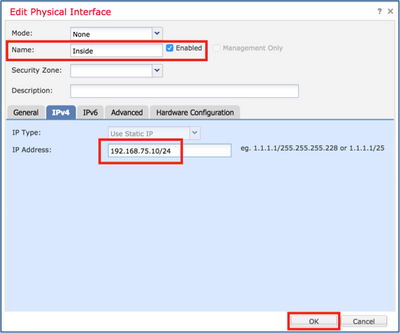
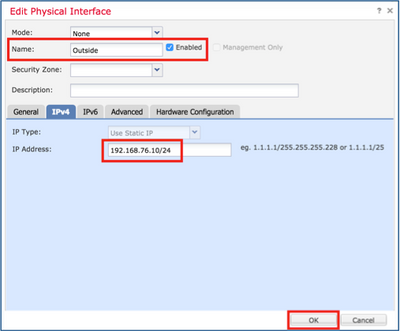
第五步:如图所示配置接口设置。
以太网 1/5 接口。
以太网 1/6 接口。
第六步:导航到高可用性,然后选择Interface Name Edit以添加备用IP地址,如图所示。
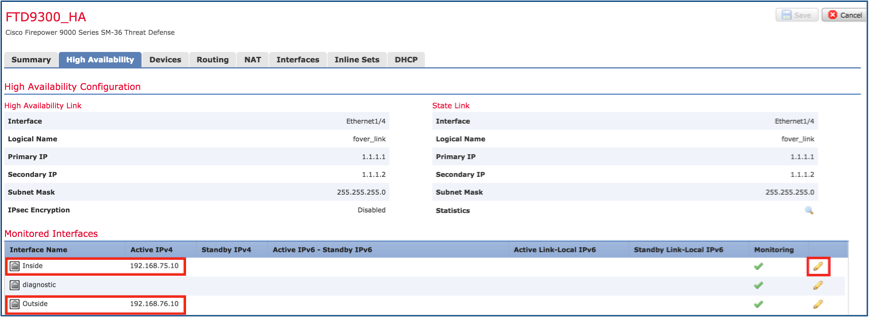
步骤 7.如图所示,用于内部接口。
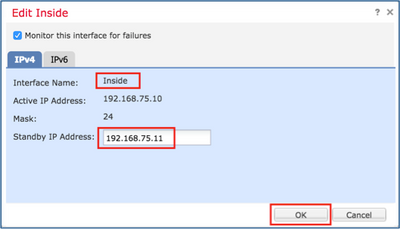
步骤 8对Outside接口执行相同操作。
步骤 9如图所示验证结果。
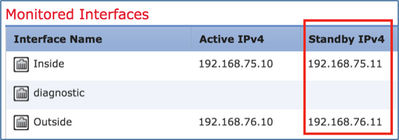
步骤 10保持高可用性选项卡,并配置虚拟MAC地址,如图所示。

步骤 11如图所示。
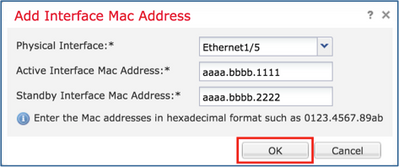
步骤 12对Outside接口执行相同操作。
步骤 13如图所示验证结果。
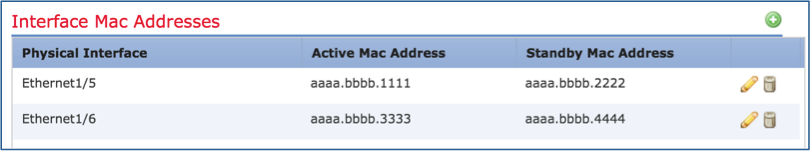
步骤 14配置更改后,选择Save和Deploy。
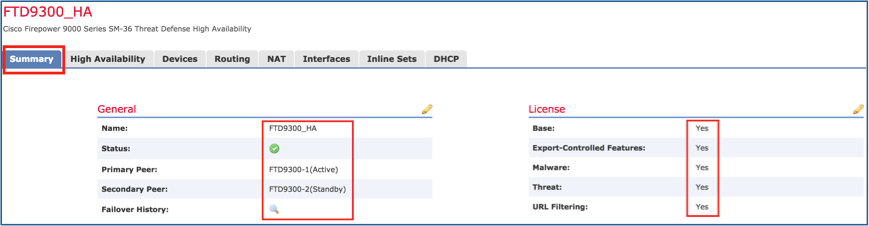
任务3.检验FTD HA和许可证
任务要求:
从 FMC GUI 和 FTD CLI 上验证 FTD HA 设置和启用的许可证。
解决方案:
步骤1:导航至摘要,然后检查高可用性设置和已启用的许可证,如图所示。
第二步:从FTD CLISH CLI运行以下命令:
> show high-availability config Failover On Failover unit Primary Failover LAN Interface: fover_link Ethernet1/4 (up) Reconnect timeout 0:00:00 Unit Poll frequency 1 seconds, holdtime 15 seconds Interface Poll frequency 5 seconds, holdtime 25 seconds Interface Policy 1 Monitored Interfaces 1 of 1041 maximum MAC Address Move Notification Interval not set failover replication http Version: Ours 9.6(1), Mate 9.6(1) Serial Number: Ours FLM19267A63, Mate FLM19206H7T Last Failover at: 18:32:38 EEST Jul 21 2016 This host: Primary - Active Active time: 3505 (sec) slot 0: UCSB-B200-M3-U hw/sw rev (0.0/9.6(1)) status (Up Sys) Interface diagnostic (0.0.0.0): Normal (Waiting) slot 1: snort rev (1.0) status (up) slot 2: diskstatus rev (1.0) status (up) Other host: Secondary - Standby Ready Active time: 172 (sec) slot 0: UCSB-B200-M3-U hw/sw rev (0.0/9.6(1)) status (Up Sys) Interface diagnostic (0.0.0.0): Normal (Waiting) slot 1: snort rev (1.0) status (up) slot 2: diskstatus rev (1.0) status (up) Stateful Failover Logical Update Statistics Link : fover_link Ethernet1/4 (up) Stateful Obj xmit xerr rcv rerr General 417 0 416 0 sys cmd 416 0 416 0 up time 0 0 0 0 RPC services 0 0 0 0 TCP conn 0 0 0 0 UDP conn 0 0 0 0 ARP tbl 0 0 0 0 Xlate_Timeout 0 0 0 0 IPv6 ND tbl 0 0 0 0 VPN IKEv1 SA 0 0 0 0 VPN IKEv1 P2 0 0 0 0 VPN IKEv2 SA 0 0 0 0 VPN IKEv2 P2 0 0 0 0 VPN CTCP upd 0 0 0 0 VPN SDI upd 0 0 0 0 VPN DHCP upd 0 0 0 0 SIP Session 0 0 0 0 SIP Tx 0 0 0 0 SIP Pinhole 0 0 0 0 Route Session 0 0 0 0 Router ID 0 0 0 0 User-Identity 1 0 0 0 CTS SGTNAME 0 0 0 0 CTS PAC 0 0 0 0 TrustSec-SXP 0 0 0 0 IPv6 Route 0 0 0 0 STS Table 0 0 0 0 Logical Update Queue Information Cur Max Total Recv Q: 0 10 416 Xmit Q: 0 11 2118 >
第三步:在辅助设备上执行相同操作。
第四步:从LINA CLI运行show failover state命令:
firepower# show failover state
State Last Failure Reason Date/Time
This host - Primary
Active None
Other host - Secondary
Standby Ready Comm Failure 18:32:56 EEST Jul 21 2016
====Configuration State===
Sync Done
====Communication State===
Mac set
firepower#
第五步:从主设备(LINA CLI)验证配置:
firepower# show running-config failover failover failover lan unit primary failover lan interface fover_link Ethernet1/4 failover replication http failover mac address Ethernet1/5 aaaa.bbbb.1111 aaaa.bbbb.2222 failover mac address Ethernet1/6 aaaa.bbbb.3333 aaaa.bbbb.4444 failover link fover_link Ethernet1/4 failover interface ip fover_link 10.10.1.1 255.255.255.0 standby 10.10.1.2 firepower# firepower# show running-config interface ! interface Ethernet1/2 management-only nameif diagnostic security-level 0 no ip address ! interface Ethernet1/4 description LAN/STATE Failover Interface ! interface Ethernet1/5 nameif Inside security-level 0 ip address 192.168.75.10 255.255.255.0 standby 192.168.75.11 ! interface Ethernet1/6 nameif Outside security-level 0 ip address 192.168.76.10 255.255.255.0 standby 192.168.76.11 firepower#
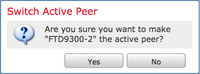
任务4.切换故障切换角色
任务要求:
从 FMC 上将故障切换角色从主/主用、辅助/备用切换到主/备用、和辅助/主用
解决方案:
步骤1:选择图标,如图所示。

第二步:确认弹出窗口中的操作,如图所示。
第三步:如图所示验证结果。

从 LINA CLI,可以看到系统在主/主用设备上执行了命令 no failover active:
Jul 22 2016 10:39:26: %ASA-5-111008: User 'enable_15' executed the 'no failover active' command. Jul 22 2016 10:39:26: %ASA-5-111010: User 'enable_15', running 'N/A' from IP 0.0.0.0, executed 'no failover active'
您还可以在 show failover history 命令的输出中进行验证:
firepower# show failover history ========================================================================== From State To State Reason 10:39:26 EEST Jul 22 2016 Active Standby Ready Set by the config command
第四步:验证后,使主设备再次处于活动状态。
任务5.中断HA对
任务要求:
从 FMC 上中断故障切换对。
解决方案:
步骤1:选择图标,如图所示。

第二步:检查如图所示的通知。
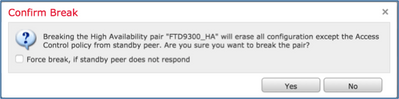
第三步:注意如图所示的消息。
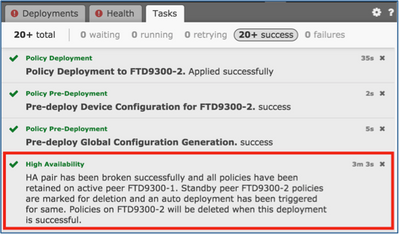
第四步:验证FMC GUI的结果,如图所示。

在 HA 中断前后在主设备上运行 show running-config:
| 在 HA 中断之前 |
在 HA 中断之后 |
| firepower# sh run : 已储存 : :序列号:FLM19267A63 :硬件:FPR9K-SM-36、135839 MB RAM、CPU Xeon E5系列2294 MHz、2个CPU(72个内核) : NGFW版本10.10.1.1 ! hostname firepower enable password 8Ry2YjIyt7RRXU24 encrypted 名称 ! interface Ethernet1/2 仅管理 nameif diagnostic 安全级别0 no ip address ! interface Ethernet1/4 说明LAN/STATE故障切换接口 ! interface Ethernet1/5 nameif内部 安全级别0 ip address 192.168.75.10 255.255.255.0 standby 192.168.75.11 ! interface Ethernet1/6 nameif外部 安全级别0 ip address 192.168.76.10 255.255.255.0 standby 192.168.76.11 ! ftp mode passive ngips conn-match vlan-id access-list CSM_FW_ACL_ remark rule-id 268447744:访问策略:FTD9300 — 必备/1 access-list CSM_FW_ACL_ remark rule-id 268447744: L4 RULE: Allow_ICMP access-list CSM_FW_ACL_ advanced permit icmp any any rule-id 268447744 event-log both access-list CSM_FW_ACL_ remark rule-id 268441600:访问策略:FTD9300 — 默认/1 access-list CSM_FW_ACL_ remark rule-id 268441600: L4规则:默认操作规则 access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268441600 ! tcp-map UM_STATIC_TCP_MAP tcp-options range 6 7 allow tcp-options range 9 255 allow urgent-flag allow ! 无传呼机 logging enable logging timestamp logging standby logging buffer-size 100000 logging buffered调试 logging flash-minimum-free 1024 logging flash-maximum-allocation 3076 mtu diagnostic 1500 mtu内部1500 1500以外的MTU 故障转移 failover lan unit primary failover lan interface fover_link Ethernet1/4 故障切换复制http failover mac address Ethernet1/5 aaaa.bbbb.1111 aaaa.bbbb.2222 failover mac address Ethernet1/6 aaaa.bbbb.3333 aaaaa.bbbb.4444 failover link fover_link Ethernet1/4 failover interface ip fover_link 10.10.1.1 255.255.255.0 standby 10.10.1.2 icmp unreachable rate-limit 1 burst-size 1 no asdm history enable arp timeout 14400 no arp permit-nonconnected access-group CSM_FW_ACL_ global timeout xlate 3:00:00 timeout pat-xlate 0:00:30 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:00:30 timeout floating-conn 0:00:00 aaa proxy-limit disable no snmp-server location no snmp-server contact no snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart crypto ipsec security-association pmtu-aging infinite crypto ca trustpool policy telnet timeout 5 ssh stricthostkeycheck ssh timeout 5 ssh key-exchange group dh-group1-sha1 控制台超时0 dynamic-access-policy-record DfltAccessPolicy ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map 参数 消息长度最大客户端自动 message-length maximum 512 policy-map type inspect ip-options UM_STATIC_IP_OPTIONS_MAP 参数 eool action allow nop action allow router-alert action allow policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect icmp inspect icmp error inspect dcerpc inspect ip-options UM_STATIC_IP_OPTIONS_MAP class class-default set connection advanced-options UM_STATIC_TCP_MAP ! service-policy global_policy global prompt hostname context call-home profile CiscoTAC-1 无活动 目的地址http https://tools.cisco.com/its/service/oddce/services/DDCEService 目的地址电邮callhome@cisco.com destination transport-method http subscribe-to-alert-group诊断 subscribe-to-alert-group环境 定期(每月)向警报组订用资产 定期(每月)配置subscribe-to-alert-group 订用警报组遥测每天定期 Cryptochecksum:933c594fc0264082edc0f24bad358031 :结束 firepower# |
firepower# sh run : 已储存 : :序列号:FLM19267A63 :硬件:FPR9K-SM-36、135839 MB RAM、CPU Xeon E5系列2294 MHz、2个CPU(72个内核) : NGFW版本10.10.1.1 ! hostname firepower enable password 8Ry2YjIyt7RRXU24 encrypted 名称 ! interface Ethernet1/2 仅管理 nameif diagnostic 安全级别0 no ip address ! interface Ethernet1/4 no nameif 无安全级别 no ip address ! interface Ethernet1/5 nameif内部 安全级别0 ip address 192.168.75.10 255.255.255.0 standby 192.168.75.11 ! interface Ethernet1/6 nameif外部 安全级别0 ip address 192.168.76.10 255.255.255.0 standby 192.168.76.11 ! ftp mode passive ngips conn-match vlan-id access-list CSM_FW_ACL_ remark rule-id 268447744:访问策略:FTD9300 — 必备/1 access-list CSM_FW_ACL_ remark rule-id 268447744: L4 RULE: Allow_ICMP access-list CSM_FW_ACL_ advanced permit icmp any any rule-id 268447744 event-log both access-list CSM_FW_ACL_ remark rule-id 268441600:访问策略:FTD9300 — 默认/1 access-list CSM_FW_ACL_ remark rule-id 268441600: L4规则:默认操作规则 access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268441600 ! tcp-map UM_STATIC_TCP_MAP tcp-options range 6 7 allow tcp-options range 9 255 allow urgent-flag allow ! 无传呼机 logging enable logging timestamp logging standby logging buffer-size 100000 logging buffered调试 logging flash-minimum-free 1024 logging flash-maximum-allocation 3076 mtu diagnostic 1500 mtu内部1500 1500以外的MTU 不执行故障切换 no monitor-interface service-module icmp unreachable rate-limit 1 burst-size 1 no asdm history enable arp timeout 14400 no arp permit-nonconnected access-group CSM_FW_ACL_ global timeout xlate 3:00:00 timeout pat-xlate 0:00:30 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:00:30 timeout floating-conn 0:00:00 aaa proxy-limit disable no snmp-server location no snmp-server contact no snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart crypto ipsec security-association pmtu-aging infinite crypto ca trustpool policy telnet timeout 5 ssh stricthostkeycheck ssh timeout 5 ssh key-exchange group dh-group1-sha1 控制台超时0 dynamic-access-policy-record DfltAccessPolicy ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map 参数 消息长度最大客户端自动 message-length maximum 512 policy-map type inspect ip-options UM_STATIC_IP_OPTIONS_MAP 参数 eool action allow nop action allow router-alert action allow policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect icmp inspect icmp error inspect dcerpc inspect ip-options UM_STATIC_IP_OPTIONS_MAP class class-default set connection advanced-options UM_STATIC_TCP_MAP ! service-policy global_policy global prompt hostname context call-home profile CiscoTAC-1 无活动 目的地址http https://tools.cisco.com/its/service/oddce/services/DDCEService 目的地址电邮callhome@cisco.com destination transport-method http subscribe-to-alert-group诊断 subscribe-to-alert-group环境 定期(每月)向警报组订用资产 定期(每月)配置subscribe-to-alert-group 订用警报组遥测每天定期 Cryptochecksum:fb6f5c369dee730b9125650517dbb059 :结束 firepower# |
在HA中断之前和之后,在辅助设备上显示running-config,如下表所示。
| 在 HA 中断之前 |
在 HA 中断之后 |
| firepower# sh run : 已储存 : :序列号:FLM19206H7T :硬件:FPR9K-SM-36、135841 MB RAM、CPU Xeon E5系列2294 MHz、2个CPU(72个内核) : NGFW版本10.10.1.1 ! hostname firepower enable password 8Ry2YjIyt7RRXU24 encrypted 名称 ! interface Ethernet1/2 仅管理 nameif diagnostic 安全级别0 no ip address ! interface Ethernet1/4 说明LAN/STATE故障切换接口 ! interface Ethernet1/5 nameif内部 安全级别0 ip address 192.168.75.10 255.255.255.0 standby 192.168.75.11 ! interface Ethernet1/6 nameif外部 安全级别0 ip address 192.168.76.10 255.255.255.0 standby 192.168.76.11 ! ftp mode passive ngips conn-match vlan-id access-list CSM_FW_ACL_ remark rule-id 268447744:访问策略:FTD9300 — 必备/1 access-list CSM_FW_ACL_ remark rule-id 268447744: L4 RULE: Allow_ICMP access-list CSM_FW_ACL_ advanced permit icmp any any rule-id 268447744 event-log both access-list CSM_FW_ACL_ remark rule-id 268441600:访问策略:FTD9300 — 默认/1 access-list CSM_FW_ACL_ remark rule-id 268441600: L4规则:默认操作规则 access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268441600 ! tcp-map UM_STATIC_TCP_MAP tcp-options range 6 7 allow tcp-options range 9 255 allow urgent-flag allow ! 无传呼机 logging enable logging timestamp logging standby logging buffer-size 100000 logging buffered调试 logging flash-minimum-free 1024 logging flash-maximum-allocation 3076 mtu diagnostic 1500 mtu内部1500 1500以外的MTU 故障转移 failover lan unit secondary failover lan interface fover_link Ethernet1/4 故障切换复制http failover mac address Ethernet1/5 aaaa.bbbb.1111 aaaa.bbbb.2222 failover mac address Ethernet1/6 aaaa.bbbb.3333 aaaaa.bbbb.4444 failover link fover_link Ethernet1/4 failover interface ip fover_link 10.10.1.1 255.255.255.0 standby 10.10.1.2 icmp unreachable rate-limit 1 burst-size 1 no asdm history enable arp timeout 14400 no arp permit-nonconnected access-group CSM_FW_ACL_ global timeout xlate 3:00:00 timeout pat-xlate 0:00:30 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:00:30 timeout floating-conn 0:00:00 user-identity default-domain LOCAL aaa proxy-limit disable no snmp-server location no snmp-server contact no snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart crypto ipsec security-association pmtu-aging infinite crypto ca trustpool policy telnet timeout 5 ssh stricthostkeycheck ssh timeout 5 ssh key-exchange group dh-group1-sha1 控制台超时0 dynamic-access-policy-record DfltAccessPolicy ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map 参数 消息长度最大客户端自动 message-length maximum 512 policy-map type inspect ip-options UM_STATIC_IP_OPTIONS_MAP 参数 eool action allow nop action allow router-alert action allow policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect icmp inspect icmp error inspect dcerpc inspect ip-options UM_STATIC_IP_OPTIONS_MAP class class-default set connection advanced-options UM_STATIC_TCP_MAP ! service-policy global_policy global prompt hostname context call-home profile CiscoTAC-1 无活动 目的地址http https://tools.cisco.com/its/service/oddce/services/DDCEService 目的地址电邮callhome@cisco.com destination transport-method http subscribe-to-alert-group诊断 subscribe-to-alert-group环境 定期(每月)向警报组订用资产 定期(每月)配置subscribe-to-alert-group 订用警报组遥测每天定期 Cryptochecksum:e648f92dd7ef47ee611f2aaa5c6cbd84 :结束 firepower# |
firepower# sh run : 已储存 : :序列号:FLM19206H7T :硬件:FPR9K-SM-36、135841 MB RAM、CPU Xeon E5系列2294 MHz、2个CPU(72个内核) : NGFW版本10.10.1.1 ! hostname firepower enable password 8Ry2YjIyt7RRXU24 encrypted 名称 ! interface Ethernet1/2 仅管理 nameif diagnostic 安全级别0 no ip address ! interface Ethernet1/4 shutdown no nameif 无安全级别 no ip address ! interface Ethernet1/5 shutdown no nameif 无安全级别 no ip address ! interface Ethernet1/6 shutdown no nameif 无安全级别 no ip address ! ftp mode passive ngips conn-match vlan-id access-list CSM_FW_ACL_ remark rule-id 268447744:访问策略:FTD9300 — 必备/1 access-list CSM_FW_ACL_ remark rule-id 268447744: L4 RULE: Allow_ICMP access-list CSM_FW_ACL_ advanced permit icmp any any rule-id 268447744 event-log both access-list CSM_FW_ACL_ remark rule-id 268441600:访问策略:FTD9300 — 默认/1 access-list CSM_FW_ACL_ remark rule-id 268441600: L4规则:默认操作规则 access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268441600 ! tcp-map UM_STATIC_TCP_MAP tcp-options range 6 7 allow tcp-options range 9 255 allow urgent-flag allow ! 无传呼机 no logging message 106015 no logging message 313001 no logging message 313008 no logging message 106023 no logging message 710003 no logging message 106100 no logging message 302015 no logging message 302014 no logging message 302013 no logging message 302018 no logging message 302017 no logging message 302016 no logging message 302021 no logging message 302020 mtu diagnostic 1500 不执行故障切换 no monitor-interface service-module icmp unreachable rate-limit 1 burst-size 1 no asdm history enable arp timeout 14400 no arp permit-nonconnected access-group CSM_FW_ACL_ global timeout xlate 3:00:00 timeout pat-xlate 0:00:30 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:00:30 timeout floating-conn 0:00:00 aaa proxy-limit disable no snmp-server location no snmp-server contact no snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart crypto ipsec security-association pmtu-aging infinite crypto ca trustpool policy telnet timeout 5 ssh stricthostkeycheck ssh timeout 5 ssh key-exchange group dh-group1-sha1 控制台超时0 dynamic-access-policy-record DfltAccessPolicy ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map 参数 消息长度最大客户端自动 message-length maximum 512 policy-map type inspect ip-options UM_STATIC_IP_OPTIONS_MAP 参数 eool action allow nop action allow router-alert action allow policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect icmp inspect icmp error inspect dcerpc inspect ip-options UM_STATIC_IP_OPTIONS_MAP class class-default set connection advanced-options UM_STATIC_TCP_MAP ! service-policy global_policy global prompt hostname context call-home profile CiscoTAC-1 无活动 目的地址http https://tools.cisco.com/its/service/oddce/services/DDCEService 目的地址电邮callhome@cisco.com destination transport-method http subscribe-to-alert-group诊断 subscribe-to-alert-group环境 定期(每月)向警报组订用资产 定期(每月)配置subscribe-to-alert-group 订用警报组遥测每天定期 Cryptochecksum:08ed87194e9f5cd9149fab3c0e9cefc3 :结束 firepower# |
关于 HA 中断的主要注意事项:
| 主要单元 |
辅助单元 |
| 所有故障切换配置已删除. 备用IP地址保留。 |
删除所有配置。 |
第五步:完成此任务后,重新创建HA对。
任务6.禁用高可用性对
任务要求:
从 FMC 上禁用故障切换对。
解决方案:
步骤1:选择如图所示的图标。

第二步:检查通知并确认如图所示。

第三步:删除HA后,两个设备都会从FMC中注销(删除)。
从 LINA CLI 运行 show running-config ,结果如下表所示:
| 主要单元 |
辅助单元 |
| firepower# sh run : 已储存 : :序列号:FLM19267A63 :硬件:FPR9K-SM-36、135839 MB RAM、CPU Xeon E5系列2294 MHz、2个CPU(72个内核) : NGFW版本10.10.1.1 ! hostname firepower enable password 8Ry2YjIyt7RRXU24 encrypted 名称 ! interface Ethernet1/2 仅管理 nameif diagnostic 安全级别0 no ip address ! interface Ethernet1/4 说明LAN/STATE故障切换接口 ! interface Ethernet1/5 nameif内部 安全级别0 ip address 192.168.75.10 255.255.255.0 standby 192.168.75.11 ! interface Ethernet1/6 nameif外部 安全级别0 ip address 192.168.76.10 255.255.255.0 standby 192.168.76.11 ! ftp mode passive ngips conn-match vlan-id access-list CSM_FW_ACL_ remark rule-id 268447744:访问策略:FTD9300 — 必备/1 access-list CSM_FW_ACL_ remark rule-id 268447744: L4 RULE: Allow_ICMP access-list CSM_FW_ACL_ advanced permit icmp any any rule-id 268447744 event-log both access-list CSM_FW_ACL_ remark rule-id 268441600:访问策略:FTD9300 — 默认/1 access-list CSM_FW_ACL_ remark rule-id 268441600: L4规则:默认操作规则 access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268441600 ! tcp-map UM_STATIC_TCP_MAP tcp-options range 6 7 allow tcp-options range 9 255 allow urgent-flag allow ! 无传呼机 logging enable logging timestamp logging standby logging buffer-size 100000 logging buffered调试 logging flash-minimum-free 1024 logging flash-maximum-allocation 3076 mtu diagnostic 1500 mtu内部1500 1500以外的MTU 故障转移 failover lan unit primary failover lan interface fover_link Ethernet1/4 故障切换复制http failover mac address Ethernet1/5 aaaa.bbbb.1111 aaaa.bbbb.2222 failover mac address Ethernet1/6 aaaa.bbbb.3333 aaaaa.bbbb.4444 failover link fover_link Ethernet1/4 failover interface ip fover_link 10.10.1.1 255.255.255.0 standby 10.10.1.2 icmp unreachable rate-limit 1 burst-size 1 no asdm history enable arp timeout 14400 no arp permit-nonconnected access-group CSM_FW_ACL_ global timeout xlate 3:00:00 timeout pat-xlate 0:00:30 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:00:30 timeout floating-conn 0:00:00 aaa proxy-limit disable no snmp-server location no snmp-server contact no snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart crypto ipsec security-association pmtu-aging infinite crypto ca trustpool policy telnet timeout 5 ssh stricthostkeycheck ssh timeout 5 ssh key-exchange group dh-group1-sha1 控制台超时0 dynamic-access-policy-record DfltAccessPolicy ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map 参数 消息长度最大客户端自动 message-length maximum 512 policy-map type inspect ip-options UM_STATIC_IP_OPTIONS_MAP 参数 eool action allow nop action allow router-alert action allow policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect icmp inspect icmp error inspect dcerpc inspect ip-options UM_STATIC_IP_OPTIONS_MAP class class-default set connection advanced-options UM_STATIC_TCP_MAP ! service-policy global_policy global prompt hostname context call-home profile CiscoTAC-1 无活动 目的地址http https://tools.cisco.com/its/service/oddce/services/DDCEService 目的地址电邮callhome@cisco.com destination transport-method http subscribe-to-alert-group诊断 subscribe-to-alert-group环境 定期(每月)向警报组订用资产 定期(每月)配置subscribe-to-alert-group 订用警报组遥测每天定期 Cryptochecksum:933c594fc0264082edc0f24bad358031 :结束 firepower# |
firepower# sh run : 已储存 : :序列号:FLM19206H7T :硬件:FPR9K-SM-36、135841 MB RAM、CPU Xeon E5系列2294 MHz、2个CPU(72个内核) : NGFW版本10.10.1.1 ! hostname firepower enable password 8Ry2YjIyt7RRXU24 encrypted 名称 ! interface Ethernet1/2 仅管理 nameif diagnostic 安全级别0 no ip address ! interface Ethernet1/4 说明LAN/STATE故障切换接口 ! interface Ethernet1/5 nameif内部 安全级别0 ip address 192.168.75.10 255.255.255.0 standby 192.168.75.11 ! interface Ethernet1/6 nameif外部 安全级别0 ip address 192.168.76.10 255.255.255.0 standby 192.168.76.11 ! ftp mode passive ngips conn-match vlan-id access-list CSM_FW_ACL_ remark rule-id 268447744:访问策略:FTD9300 — 必备/1 access-list CSM_FW_ACL_ remark rule-id 268447744: L4 RULE: Allow_ICMP access-list CSM_FW_ACL_ advanced permit icmp any any rule-id 268447744 event-log both access-list CSM_FW_ACL_ remark rule-id 268441600:访问策略:FTD9300 — 默认/1 access-list CSM_FW_ACL_ remark rule-id 268441600: L4规则:默认操作规则 access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268441600 ! tcp-map UM_STATIC_TCP_MAP tcp-options range 6 7 allow tcp-options range 9 255 allow urgent-flag allow ! 无传呼机 logging enable logging timestamp logging standby logging buffer-size 100000 logging buffered调试 logging flash-minimum-free 1024 logging flash-maximum-allocation 3076 mtu diagnostic 1500 mtu内部1500 1500以外的MTU 故障转移 failover lan unit secondary failover lan interface fover_link Ethernet1/4 故障切换复制http failover mac address Ethernet1/5 aaaa.bbbb.1111 aaaa.bbbb.2222 failover mac address Ethernet1/6 aaaa.bbbb.3333 aaaaa.bbbb.4444 failover link fover_link Ethernet1/4 failover interface ip fover_link 10.10.1.1 255.255.255.0 standby 10.10.1.2 icmp unreachable rate-limit 1 -size 1 no asdm history enable arp timeout 14400 no arp permit-nonconnected access-group CSM_FW_ACL_ global timeout xlate 3:00:00 timeout pat-xlate 0:00:30 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:00:30 timeout floating-conn 0:00:00 user-identity default-domain LOCAL aaa proxy-limit disable no snmp-server location no snmp-server contact no snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart crypto ipsec security-association pmtu-aging infinite crypto ca trustpool policy telnet timeout 5 ssh stricthostkeycheck ssh timeout 5 ssh key-exchange group dh-group1-sha1 控制台超时0 dynamic-access-policy-record DfltAccessPolicy ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map 参数 消息长度最大客户端自动 message-length maximum 512 policy-map type inspect ip-options UM_STATIC_IP_OPTIONS_MAP 参数 eool action allow nop action allow router-alert action allow policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect icmp inspect icmp error inspect dcerpc inspect ip-options UM_STATIC_IP_OPTIONS_MAP class class-default set connection advanced-options UM_STATIC_TCP_MAP ! service-policy global_policy global prompt hostname context call-home profile CiscoTAC-1 无活动 目的地址http https://tools.cisco.com/its/service/oddce/services/DDCEService 目的地址电邮callhome@cisco.com destination transport-method http subscribe-to-alert-group诊断 subscribe-to-alert-group环境 定期(每月)向警报组订用资产 定期(每月)配置subscribe-to-alert-group 订用警报组遥测每天定期 Cryptochecksum:e648f92dd7ef47ee611f2aaa5c6cbd84 :结束 firepower# |
第四步:两台FTD设备均未从FMC注册:
> show managers No managers configured.
在 FMC 中禁用 HA 选项的主要注意事项:
| 主要单元 |
辅助单元 |
| 设备会从 FMC 中删除。 未从 FTD 设备删除任何配置. |
设备会从 FMC 中删除。 未从 FTD 设备删除任何配置. |
第五步:运行以下命令以从FTD设备删除故障切换配置:
> configure high-availability disable High-availability will be disabled. Do you really want to continue? Please enter 'YES' or 'NO': yes Successfully disabled high-availability.
注:您必须在两台设备上运行命令
结果:
| 主要单元 |
辅助单元 |
|
> show failover Failover Off |
> show failover > |
| 主 |
辅助 |
| firepower# show run ! hostname firepower enable password 8Ry2YjIyt7RRXU24 encrypted 名称 arp timeout 14400 no arp permit-nonconnected arp rate-limit 16384 ! interface GigabitEthernet1/1 nameif outside cts manual propagate sgt preserve-untag 策略静态sgt已禁用,受信任 安全级别0 ip address 10.1.1.1 255.255.255.0 < — 删除了备用IP ! interface GigabitEthernet1/2 nameif inside cts manual propagate sgt preserve-untag 策略静态sgt已禁用,受信任 安全级别0 ip address 192.168.1.1 255.255.255.0 < — 删除了备用IP ! interface GigabitEthernet1/3 说明LAN故障切换接口 ! interface GigabitEthernet1/4 description STATE Failover Interface ! interface GigabitEthernet1/5 shutdown no nameif 无安全级别 no ip address ! interface GigabitEthernet1/6 shutdown no nameif 无安全级别 no ip address ! interface GigabitEthernet1/7 shutdown no nameif 无安全级别 no ip address ! interface GigabitEthernet1/8 shutdown no nameif 无安全级别 no ip address ! 接口管理1/1 仅管理 nameif diagnostic cts manual propagate sgt preserve-untag 策略静态sgt已禁用,受信任 安全级别0 no ip address ! ftp mode passive ngips conn-match vlan-id access-list CSM_FW_ACL_ remark rule-id 9998: PREFILTER POLICY: Default Tunnel and Priority Policy access-list CSM_FW_ACL_ remark rule-id 9998:规则:默认隧道操作规则 access-list CSM_FW_ACL_ advanced permit ipinip any any rule-id 9998 access-list CSM_FW_ACL_ advanced permit 41 any any rule-id 9998 access-list CSM_FW_ACL_ advanced permit gre any any rule-id 9998 access-list CSM_FW_ACL_ advanced permit udp any any eq 3544 rule-id 9998 access-list CSM_FW_ACL_remark rule-id 268435456:访问策略:FTD_HA — 默认/1 access-list CSM_FW_ACL_ remark rule-id 268435456: L4规则:默认操作规则 access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268435456 ! tcp-map UM_STATIC_TCP_MAP tcp-options range 6 7 allow tcp-options range 9 18 allow tcp-options range 20 255 allow tcp-options md5 clear urgent-flag allow ! 无传呼机 logging enable logging timestamp logging buffered调试 logging flash-minimum-free 1024 logging flash-maximum-allocation 3076 no logging message 106015 no logging message 313001 no logging message 313008 no logging message 106023 no logging message 710005 no logging message 710003 no logging message 106100 no logging message 302015 no logging message 302014 no logging message 302013 no logging message 302018 no logging message 302017 no logging message 302016 no logging message 302021 no logging message 302020 1500以外的MTU MTU内部1500 mtu diagnostic 1500 不执行故障切换 icmp unreachable rate-limit 1 burst-size 1 no asdm history enable access-group CSM_FW_ACL_ global 00 community ***** version 2c no snmp-server location no snmp-server contact snmp-server community ***** service sw-reset-button crypto ipsec security-association pmtu-aging infinite crypto ca trustpool policy telnet timeout 5 控制台超时0 dynamic-access-policy-record DfltAccessPolicy ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map 参数 消息长度最大客户端自动 message-length maximum 512 no tcp-inspection policy-map type inspect ip-options UM_STATIC_IP_OPTIONS_MAP 参数 eool action allow nop action allow router-alert action allow policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect esmtp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect icmp inspect icmp error inspect dcerpc inspect ip-options UM_STATIC_IP_OPTIONS_MAP class class-default set connection advanced-options UM_STATIC_TCP_MAP ! service-policy global_policy global prompt hostname context call-home profile CiscoTAC-1 无活动 目的地址http https://tools.cisco.com/its/service/oddce/services/DDCEService 目的地址电邮callhome@cisco.com destination transport-method http subscribe-to-alert-group诊断 subscribe-to-alert-group环境 定期(每月)向警报组订用资产 定期(每月)配置subscribe-to-alert-group 订用警报组遥测每天定期 Cryptochecksum:768a03e90b9d3539773b9d7af66b3452 |
firepower# show run ! hostname firepower enable password 8Ry2YjIyt7RRXU24 encrypted 名称 arp timeout 14400 no arp permit-nonconnected arp rate-limit 16384 ! interface GigabitEthernet1/1 shutdown no nameif 无安全级别 no ip address ! interface GigabitEthernet1/2 shutdown no nameif 无安全级别 no ip address ! interface GigabitEthernet1/3 说明LAN故障切换接口 ! interface GigabitEthernet1/4 description STATE Failover Interface ! interface GigabitEthernet1/5 shutdown no nameif 无安全级别 no ip address ! interface GigabitEthernet1/6 shutdown no nameif 无安全级别 no ip address ! interface GigabitEthernet1/7 shutdown no nameif 无安全级别 no ip address ! interface GigabitEthernet1/8 shutdown no nameif 无安全级别 no ip address ! 接口管理1/1 仅管理 nameif diagnostic cts manual propagate sgt preserve-untag 策略静态sgt已禁用,受信任 安全级别0 no ip address ! ftp mode passive ngips conn-match vlan-id access-list CSM_FW_ACL_ remark rule-id 9998: PREFILTER POLICY: Default Tunnel and Priority Policy access-list CSM_FW_ACL_ remark rule-id 9998:规则:默认隧道操作规则 access-list CSM_FW_ACL_ advanced permit ipinip any any rule-id 9998 access-list CSM_FW_ACL_ advanced permit 41 any any rule-id 9998 access-list CSM_FW_ACL_ advanced permit gre any any rule-id 9998 access-list CSM_FW_ACL_ advanced permit udp any any eq 3544 rule-id 9998 access-list CSM_FW_ACL_remark rule-id 268435456:访问策略:FTD_HA — 默认/1 access-list CSM_FW_ACL_ remark rule-id 268435456: L4规则:默认操作规则 access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268435456 ! tcp-map UM_STATIC_TCP_MAP tcp-options range 6 7 allow tcp-options range 9 18 allow tcp-options range 20 255 allow tcp-options md5 clear urgent-flag allow ! 无传呼机 logging enable logging timestamp logging buffered调试 logging flash-minimum-free 1024 logging flash-maximum-allocation 3076 no logging message 106015 no logging message 313001 no logging message 313008 no logging message 106023 no logging message 710005 no logging message 710003 no logging message 106100 no logging message 302015 no logging message 302014 no logging message 302013 no logging message 302018 no logging message 302017 no logging message 302016 no logging message 302021 no logging message 302020 1500以外的MTU MTU内部1500 mtu diagnostic 1500 不执行故障切换 failover lan unit secondary failover lan interface FOVER GigabitEthernet1/3 故障切换复制http failover link STATE GigabitEthernet1/4 failover interface ip FOVER 10.10.1.1 255.255.255.0 standby 10.10.1.2 failover interface ip STATE 10.10.2.1 255.255.255.0 standby 10.10.2.2 icmp unreachable rate-limit 1 burst-size 1 no asdm history enable access-group CSM_FW_ACL_ global timeout xlate 3:00:00 timeout pat-xlate 0:00:30 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:00:30 timeout floating-conn 0:00:00 timeout conn-holddown 0:00:15 user-identity default-domain LOCAL aaa proxy-limit disable snmp-server host outside 192.168.1.100 community ***** version 2c no snmp-server location no snmp-server contact snmp-server community ***** service sw-reset-button crypto ipsec security-association pmtu-aging infinite crypto ca trustpool policy telnet timeout 5 控制台超时0 dynamic-access-policy-record DfltAccessPolicy ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map 参数 消息长度最大客户端自动 message-length maximum 512 no tcp-inspection policy-map type inspect ip-options UM_STATIC_IP_OPTIONS_MAP 参数 eool action allow nop action allow router-alert action allow policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect esmtp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect icmp inspect icmp error inspect dcerpc inspect ip-options UM_STATIC_IP_OPTIONS_MAP class class-default set connection advanced-options UM_STATIC_TCP_MAP ! service-policy global_policy global prompt hostname context call-home profile CiscoTAC-1 无活动 目的地址http https://tools.cisco.com/its/service/oddce/services/DDCEService 目的地址电邮callhome@cisco.com destination transport-method http subscribe-to-alert-group诊断 subscribe-to-alert-group环境 定期(每月)向警报组订用资产 定期(每月)配置subscribe-to-alert-group 订用警报组遥测每天定期 Cryptochecksum:ac9b8f401e18491fee653f4cfe0ce18f |
从 FTD CLI 上禁用 HA 的主要注意事项:
| 主要单元 |
辅助单元 |
| 故障切换配置和备用IP aretimeout xlate 3:00:00 timeout pat-xlate 0:00:30 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:00:30 timeout floating-conn 0:00:00 timeout conn-holddown 0:00:15 aaa proxy-limit disable 已删除192.168.1.1外部的snmp-server主机。 |
|
第六步:完成任务后,将设备注册到FMC并启用HA对。
任务7.挂起HA
任务要求:
从 FTD CLISH CLI 上暂停 HA
解决方案:
步骤1:在主FTD上,运行命令并确认(键入YES)。
> configure high-availability suspend Please ensure that no deployment operation is in progress before suspending high-availability. Please enter 'YES' to continue if there is no deployment operation in progress and 'NO' if you wish to abort: YES Successfully suspended high-availability.
第二步:验证主设备上的更改:
> show high-availability config Failover Off Failover unit Primary Failover LAN Interface: fover_link Ethernet1/4 (up) Reconnect timeout 0:00:00 Unit Poll frequency 1 seconds, holdtime 15 seconds Interface Poll frequency 5 seconds, holdtime 25 seconds Interface Policy 1 Monitored Interfaces 1 of 1041 maximum MAC Address Move Notification Interval not set failover replication http
第三步:辅助设备上的结果:
> show high-availability config Failover Off (pseudo-Standby) Failover unit Secondary Failover LAN Interface: fover_link Ethernet1/4 (up) Reconnect timeout 0:00:00 Unit Poll frequency 1 seconds, holdtime 15 seconds Interface Poll frequency 5 seconds, holdtime 25 seconds Interface Policy 1 Monitored Interfaces 1 of 1041 maximum MAC Address Move Notification Interval not set failover replication http
第四步:恢复主设备上的HA:
> configure high-availability resume Successfully resumed high-availablity. > . No Active mate detected !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! Beginning configuration replication: Sending to mate. End Configuration Replication to mate >
> show high-availability config Failover On Failover unit Primary Failover LAN Interface: fover_link Ethernet1/4 (up) Reconnect timeout 0:00:00 Unit Poll frequency 1 seconds, holdtime 15 seconds Interface Poll frequency 5 seconds, holdtime 25 seconds Interface Policy 1 Monitored Interfaces 1 of 1041 maximum MAC Address Move Notification Interval not set failover replication http
第五步:恢复HA后辅助设备上的结果:
> .. Detected an Active mate Beginning configuration replication from mate. WARNING: Failover is enabled but standby IP address is not configured for this interface. WARNING: Failover is enabled but standby IP address is not configured for this interface. End configuration replication from mate. >
> show high-availability config Failover On Failover unit Secondary Failover LAN Interface: fover_link Ethernet1/4 (up) Reconnect timeout 0:00:00 Unit Poll frequency 1 seconds, holdtime 15 seconds Interface Poll frequency 5 seconds, holdtime 25 seconds Interface Policy 1 Monitored Interfaces 1 of 1041 maximum MAC Address Move Notification Interval not set failover replication http >
常见问题解答 (FAQ)
复制配置后,是立即(逐行)保存还是复制结束时保存?
在复制结束时保存。根据 debug fover sync 命令输出的末尾内容,其中显示了配置/命令复制:
cli_xml_server: frep_write_cmd: Cmd: access-list CSM_FW_ACL_ line 1506 remark rule-id 268442578: L7 RULE: ACP_Rule_500 cli_xml_server: frep_write_cmd: Cmd: access-list CSM_FW_ACL_ line 1507 advanced permit tcp object-group group_10 eq 48894 object-group group_10 eq 23470 vlan eq 1392 rule-id 268442578 cli_xml_server: frep_write_cmd: Cmd: access-list CSM_FW_ACL_ line 1508 remark rule-id 268442078: ACCESS POLICY: mzafeiro_500 - Default cli_xml_server: frep_write_cmd: Cmd: access-list CSM_FW_ACL_ line 1509 remark rule-id 268442078: L4 RULE: DEFAULT ACTION RULE ... cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ advanced permit tcp object-group group_2 eq 32881 object-group group_433 eq 39084 vlan eq 1693 rule-id 268442076 cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ line 1510 remark rule-id 268442077: ACCESS POLICY: mzafeiro_ACP1500 - Mandatory cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ line 1510 remark rule-id 268442077: L7 RULE: ACP_Rule_1500 cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ advanced permit tcp object-group group_6 eq 8988 object-group group_311 eq 32433 vlan eq 619 rule-id 268442077 cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ line 1510 remark rule-id 268440577: ACCESS POLICY: mzafeiro_ACP1500 - Default cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ line 1510 remark rule-id 268440577: L4 RULE: DEFAULT ACTION RULE cli_xml_server: frep_write_cmd: Cmd: access-list CSM_FW_ACL_ advanced deny ip any any rule-id 268442078 event-log flow-start cli_xml_server: frep_write_cmd: Cmd: crypto isakmp nat-traversal cli_xml_server: frep_write_cmd: Cmd: no object-group network group_311 cli_xml_server: frep_write_cmd: Cmd: no object-group network group_433 cli_xml_server: frep_write_cmd: Cmd: no object-group network group_6 cli_xml_server: frep_write_cmd: Cmd: no object-group network group_2 cli_xml_server: frep_write_cmd: Cmd: write memory <--
如果设备处于伪备用状态(禁用故障转移),然后您重新加载它,而另一设备已启用故障转移并且处于主用状态,会发生什么情况?
您最终会处于主用/主用场景(尽管从技术上讲,这是主用/故障切换关闭)。具体而言,设备启动后会禁用故障切换,但设备会使用与主用设备相同的 IP。因此,实际上您的设备状态如下:
- Unit-1:活动
- Unit-2:故障切换关闭。设备使用与设备1相同的数据IP,但使用不同的MAC地址。
如果您手动禁用故障切换(配置高可用性挂起),然后重新加载设备,故障切换配置会发生什么情况?
禁用故障切换时,它不是永久更改(除非您决定明确执行此操作,否则不会保存在startup-config中)。您可以通过两种不同的方式重新启动/重新加载设备,而第二种方式必须谨慎:
例 1.从CLISH重新启动
从 CLISH 重启不需要确认。 因此,配置更改不会保存到启动配置中:
> configure high-availability suspend Please ensure that no deployment operation is in progress before suspending high-availability. Please enter 'YES' to continue if there is no deployment operation in progress and 'NO' if you wish to abort: YES Successfully suspended high-availability.
running-config已禁用故障转移。在本例中,设备处于备用状态,并按照预期进入伪备用状态,以避免出现主用/主用场景:
firepower# show failover | include Failover Failover Off (pseudo-Standby) Failover unit Secondary Failover LAN Interface: FOVER Ethernet1/1 (up)
startup-config仍然启用故障切换:
firepower# show startup | include failover failover failover lan unit secondary failover lan interface FOVER Ethernet1/1 failover replication http failover link FOVER Ethernet1/1 failover interface ip FOVER 192.0.2.1 255.255.255.0 standby 192.0.2.2 failover ipsec pre-shared-key *****
从 CLISH 重启设备(reboot 命令):
> reboot This command will reboot the system. Continue? Please enter 'YES' or 'NO': YES Broadcast message from root@ Threat Defense System: CMD=-stop, CSP-ID=cisco-ftd.6.2.2.81__ftd_001_JMX2119L05CYRIBVX1, FLAG='' Cisco FTD stopping ...
设备启动后,由于故障切换处于启用状态,设备会进入故障切换协商阶段并尝试检测远程对等体:
User enable_1 logged in to firepower
Logins over the last 1 days: 1.
Failed logins since the last login: 0.
Type help or '?' for a list of available commands.
firepower> .
Detected an Active mate
案例 2.从LINA CLI重新启动
从 LINA 重启(reload 命令)需要确认。因此,如果选择Y(是),配置更改将保存到启动配置中:
firepower# reload System config has been modified. Save? [Y]es/[N]o: Y <-- Be careful. This will disable the failover in the startup-config Cryptochecksum: 31857237 8658f618 3234be7c 854d583a 8781 bytes copied in 0.940 secs Proceed with reload? [confirm] firepower# show startup | include failover no failover failover lan unit secondary failover lan interface FOVER Ethernet1/1 failover replication http failover link FOVER Ethernet1/1 failover interface ip FOVER 192.0.2.1 255.255.255.0 standby 192.0.2.2 failover ipsec pre-shared-key *****
设备启动后将禁用故障切换:
firepower# show failover | include Fail Failover Off Failover unit Secondary Failover LAN Interface: FOVER Ethernet1/1 (up)
注:要避免此情况,请确保在出现提示时,不要将更改保存到startup-config中。
相关信息
- 可以在此处找到所有版本的思科 Firepower 管理中心 (FMC) 配置指南
- 可以在此处找到所有版本的 FXOS 机箱管理器和 CLI 配置指南
导航Cisco Firepower 4100/9300 FXOS文档
- 思科全球技术支持中心(TAC)强烈推荐此可视化指南,以了解有关Cisco Firepower下一代安全技术的深入实践知识:
Cisco Firepower威胁防御(FTD):下一代防火墙(NGFW)、下一代入侵防御系统(NGIPS)和高级恶意软件防护(AMP)的配置和故障排除最佳实践
- 有关Firepower技术的所有配置和故障排除技术说明
修订历史记录
| 版本 | 发布日期 | 备注 |
|---|---|---|
3.0 |
07-Aug-2023 |
更新的SEO、样式要求和格式。 |
2.0 |
04-Aug-2022 |
文章针对格式、样式要求、机器翻译、动词和语法进行了更新。 |
1.0 |
29-Sep-2021 |
初始版本 |
 反馈
反馈