Smart Call Home User Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- February 4, 2011
Chapter: References
References
See the following items for additional information about Call Home feature and Smart Call Home service:
•![]() Resources for Smart Call Home.
Resources for Smart Call Home.
•![]() CA Root Certificate Update Process.
CA Root Certificate Update Process.
For More Information
For more information about Smart Call Home, there are several options available, you can:
•![]() "Smart Call Home Service Introduction - http://www.cisco.com/en/US/products/ps7334/serv_home.html
"Smart Call Home Service Introduction - http://www.cisco.com/en/US/products/ps7334/serv_home.html
•![]() Smart Call Home presentation - http://www.cisco.com/warp/public/437/services/smartcallhome/
Smart Call Home presentation - http://www.cisco.com/warp/public/437/services/smartcallhome/
•![]() Catalyst 6500 Call Home Configuration Guide - http://www.cisco.com/en/US/products/hw/switches/ps708/products_configuration_guide_book09186a00801609ea.html
Catalyst 6500 Call Home Configuration Guide - http://www.cisco.com/en/US/products/hw/switches/ps708/products_configuration_guide_book09186a00801609ea.html
•![]() Catalyst 6500 Command Reference - http://cisco.com/en/US/products/hw/switches/ps708/products_command_reference_book09186a0080160cd0.html
Catalyst 6500 Command Reference - http://cisco.com/en/US/products/hw/switches/ps708/products_command_reference_book09186a0080160cd0.html
•![]() Generic Online Diagnostics on the Cisco Catalyst 6500 Series Switch - http://www.cisco.com/en/US/products/hw/switches/ps708/products_white_paper0900aecd801e659f.shtml
Generic Online Diagnostics on the Cisco Catalyst 6500 Series Switch - http://www.cisco.com/en/US/products/hw/switches/ps708/products_white_paper0900aecd801e659f.shtml
•![]() Cisco Catalyst 6500 Series with Cisco IOS Software Modularity - http://www.cisco.com/en/US/products/hw/switches/ps708/prod_bulletin0900aecd80313e15.html
Cisco Catalyst 6500 Series with Cisco IOS Software Modularity - http://www.cisco.com/en/US/products/hw/switches/ps708/prod_bulletin0900aecd80313e15.html
•![]() Embedded Event Manager (EEM) on the Cisco Catalyst 6500 Series - http://cisco.com/en/US/products/hw/switches/ps708/products_white_paper0900aecd805457c3.shtml
Embedded Event Manager (EEM) on the Cisco Catalyst 6500 Series - http://cisco.com/en/US/products/hw/switches/ps708/products_white_paper0900aecd805457c3.shtml
•![]() Cisco 7600 Series Command References - http://www.cisco.com/en/US/products/hw/routers/ps368/prod_command_reference_list.html
Cisco 7600 Series Command References - http://www.cisco.com/en/US/products/hw/routers/ps368/prod_command_reference_list.html
•![]() Cisco 7600 Series Cisco IOS Software Configuration Guide, 12.2SX - http://www.cisco.com/en/US/partner/docs/routers/7600/ios/12.2SXF/configuration/guide/swcg.html
Cisco 7600 Series Cisco IOS Software Configuration Guide, 12.2SX - http://www.cisco.com/en/US/partner/docs/routers/7600/ios/12.2SXF/configuration/guide/swcg.html
•![]() Cisco 7600 Series Technical References - http://www.cisco.com/en/US/products/hw/routers/ps368/prod_technical_reference_list.html
Cisco 7600 Series Technical References - http://www.cisco.com/en/US/products/hw/routers/ps368/prod_technical_reference_list.html
•![]() Cisco 7600 White Papers - http://www.cisco.com/en/US/products/hw/routers/ps368/prod_white_papers_list.html
Cisco 7600 White Papers - http://www.cisco.com/en/US/products/hw/routers/ps368/prod_white_papers_list.html
•![]() Use the feedback box on the Smart Call Home web application
Use the feedback box on the Smart Call Home web application
•![]() Access the Smart Call Home Technical Overview - http://www.cisco.com/application/pdf/en/us/guest/products/ps7334/c1266/cdccont_0900aecd8063c595.pdf
Access the Smart Call Home Technical Overview - http://www.cisco.com/application/pdf/en/us/guest/products/ps7334/c1266/cdccont_0900aecd8063c595.pdf
•![]() Contact Smart Call Home at email address - sch-support@cisco.com
Contact Smart Call Home at email address - sch-support@cisco.com
Resources for Smart Call Home
The following items are resources that can be used with the Smart Call Home service:
•![]() Cisco server certificate
Cisco server certificate
•![]() Download Transport Gateway
Download Transport Gateway
•![]() Download (Smart) Call Home Configuration Script
Download (Smart) Call Home Configuration Script
•![]() Smart Call Home Users' Guide
Smart Call Home Users' Guide
•![]() Smart Call Home Technical Overview
Smart Call Home Technical Overview
•![]() Call Home Configuration Guide
Call Home Configuration Guide
•![]() Smart Call Home Web Application
Smart Call Home Web Application
Terminology
The following list defines the different components, tools and terms used in Smart Call Home:
•![]() Call Home (CH) - Product feature in IOS version 12.3(33)SXH that uses SMTP or HTTP connections established with a configurable destination to send formatted messages. The messages contain Inventory or Configuration information that are collected at scheduled intervals. Configuration, Diagnostics, Environmental, Inventory or System Log (syslog) information is collected during real-time events; Test, Inventory, Configuration Diagnostic and Environmental information are collected on-demand.
Call Home (CH) - Product feature in IOS version 12.3(33)SXH that uses SMTP or HTTP connections established with a configurable destination to send formatted messages. The messages contain Inventory or Configuration information that are collected at scheduled intervals. Configuration, Diagnostics, Environmental, Inventory or System Log (syslog) information is collected during real-time events; Test, Inventory, Configuration Diagnostic and Environmental information are collected on-demand.
The IOS code incorporates device diagnostics (i.e. GOLD) that enables the sending of the following outbound alerts and alarms in email messages to Smart Call Home.
•![]() Call Home Alert Group - Is a configurable Call Home feature that groups detectable events from one of the Configuration, Diagnostics, Environmental, Inventory or System Log categories for monitoring.
Call Home Alert Group - Is a configurable Call Home feature that groups detectable events from one of the Configuration, Diagnostics, Environmental, Inventory or System Log categories for monitoring.
•![]() Call Home Profile - Is a configurable Call Home feature that provides a structure to bundle together several Alert Groups, to select transport methods, to assign multiple destination addresses and to specify message format options.
Call Home Profile - Is a configurable Call Home feature that provides a structure to bundle together several Alert Groups, to select transport methods, to assign multiple destination addresses and to specify message format options.
•![]() Call Home message formats - Are configurable formatting options used by the IOS Call Home feature when creating messages. The Short Text format is suitable for pagers or printed reports and the Long Text format contains Full formatted message information suitable for human reading. The XML Messages contain the same data as the Long Message, but with the addition of XML tagging and AML specific transport information to allow machine-readable parsing and routing of the message in the Smart Call Home System.
Call Home message formats - Are configurable formatting options used by the IOS Call Home feature when creating messages. The Short Text format is suitable for pagers or printed reports and the Long Text format contains Full formatted message information suitable for human reading. The XML Messages contain the same data as the Long Message, but with the addition of XML tagging and AML specific transport information to allow machine-readable parsing and routing of the message in the Smart Call Home System.
•![]() Call Home message type - Is a field within an IOS Call Home message that indicates what type of message it contains: Configuration, Diagnostics, Environmental, Inventory, Test or System Log (syslog) information.
Call Home message type - Is a field within an IOS Call Home message that indicates what type of message it contains: Configuration, Diagnostics, Environmental, Inventory, Test or System Log (syslog) information.
•![]() Call Home message sub-type - Is a field within an IOS Call Home message that indicates that the message contains full or delta Configuration or Inventory information, Gold major, minor or normal Diagnostics information, minor or major Environmental information, Test or System Log (syslog) information.
Call Home message sub-type - Is a field within an IOS Call Home message that indicates that the message contains full or delta Configuration or Inventory information, Gold major, minor or normal Diagnostics information, minor or major Environmental information, Test or System Log (syslog) information.
•![]() Cisco.com profile - Where information on Cisco contracts, case management permissions and user's company are kept for use by the Smart Call Home service.
Cisco.com profile - Where information on Cisco contracts, case management permissions and user's company are kept for use by the Smart Call Home service.
•![]() Cisco Backend (CBE) - Contains a collection of various tools and information:
Cisco Backend (CBE) - Contains a collection of various tools and information:
–![]() Smart Call Home service.
Smart Call Home service.
–![]() Guided searches for the Smart Call Home reporting process.
Guided searches for the Smart Call Home reporting process.
–![]() Generation of customized reports for Smart Call Home users.
Generation of customized reports for Smart Call Home users.
–![]() Device install-base data and their associated contracts.
Device install-base data and their associated contracts.
–![]() Customer device-based troubleshooting tools.
Customer device-based troubleshooting tools.
•![]() Cisco Contracts:
Cisco Contracts:
Contract information is kept in the Cisco.com profile. A customer can register a device using one of the following types of branded contracts:
–![]() Cisco Branded - Direct: Customer bought product directly from Cisco and contacts Cisco directly if they need support.
Cisco Branded - Direct: Customer bought product directly from Cisco and contacts Cisco directly if they need support.
–![]() Cisco Branded - CBR (Cisco Branded Reseller): Customer bought product from Cisco reseller and customer contacts Cisco directly if they need support.
Cisco Branded - CBR (Cisco Branded Reseller): Customer bought product from Cisco reseller and customer contacts Cisco directly if they need support.
–![]() Other types of contracts will become supported in a future release.
Other types of contracts will become supported in a future release.
•![]() Customer Specific Network Alerts - Smart Call Home supports the following Call Home message types:
Customer Specific Network Alerts - Smart Call Home supports the following Call Home message types:
–![]() Configuration - Contains image name and feature, running and startup configs, SW features technologies and sub-technologies.
Configuration - Contains image name and feature, running and startup configs, SW features technologies and sub-technologies.
–![]() Environment - Contains information about environmental alarms for the device clock, VTT, power supply and modules. Depending on the type of alert, a notification is sent to the customer and a Service Request is generated.
Environment - Contains information about environmental alarms for the device clock, VTT, power supply and modules. Depending on the type of alert, a notification is sent to the customer and a Service Request is generated.
–![]() GOLD - Contains information about diagnostic tests, what tests were run, their status, and results. Depending on the type of failure, a Service Request is generated.
GOLD - Contains information about diagnostic tests, what tests were run, their status, and results. Depending on the type of failure, a Service Request is generated.
–![]() Inventory - Contains information about the device, software, modules.
Inventory - Contains information about the device, software, modules.
–![]() Test - Contains information that is common to all message types. The content of test messages is not processed by Smart Call Home and hence no specific message processing results will be available for test messages.
Test - Contains information that is common to all message types. The content of test messages is not processed by Smart Call Home and hence no specific message processing results will be available for test messages.
–![]() Embedded Event Manager (EEM) - Detects real time events and takes action based on a pre-defined rules policy. EEM has event detectors with which Call Home registers; the registration is dependent upon which alert-groups the EEM profile is configured. The profile can subscribe to alert-groups for the following type events:
Embedded Event Manager (EEM) - Detects real time events and takes action based on a pre-defined rules policy. EEM has event detectors with which Call Home registers; the registration is dependent upon which alert-groups the EEM profile is configured. The profile can subscribe to alert-groups for the following type events:
•![]() GOLD diagnostic
GOLD diagnostic
•![]() Environmental
Environmental
•![]() Configuration
Configuration
•![]() Inventory
Inventory
•![]() Generic Online Diagnostics (GOLD) - Provides a common command-line interface (CLI) for manually generating Smart Call Home messages and scheduling run-time diagnostics.
Generic Online Diagnostics (GOLD) - Provides a common command-line interface (CLI) for manually generating Smart Call Home messages and scheduling run-time diagnostics.
GOLD can detect faults in hardware and provides the triggers that proactively engage high-availability features and actions, such as the switch-hitter of modules or turning off modules or individual ports. The GOLD test suite also gives support personnel the tools to test the functioning of hardware modules and troubleshoot down to the field-replaceable unit (FRU) level.
•![]() Smart Call Home service- Is a service that captures and processes Call Home diagnostics and inventory alarms that are sent from a device containing the Smart Call Home feature. This service provides proactive messaging that resolves issues before they become problems and for those problems that occur, resolving them faster using enhanced diagnostics
Smart Call Home service- Is a service that captures and processes Call Home diagnostics and inventory alarms that are sent from a device containing the Smart Call Home feature. This service provides proactive messaging that resolves issues before they become problems and for those problems that occur, resolving them faster using enhanced diagnostics
•![]() Smart Call Home Client - A device that sends or forwards IOS Call Home or other supported messages to Smart Call Home using SMTP or HTTPS connections; the messages must be registered with the Smart Call Home system.
Smart Call Home Client - A device that sends or forwards IOS Call Home or other supported messages to Smart Call Home using SMTP or HTTPS connections; the messages must be registered with the Smart Call Home system.
•![]() Smart Call Home supported messages - Currently is an AML/XML message, created by a device using the IOS Call Home Feature, that contains Configuration (full), Diagnostics (major & minor), Environmental (major & minor), Inventory (full), Test or System Log information.
Smart Call Home supported messages - Currently is an AML/XML message, created by a device using the IOS Call Home Feature, that contains Configuration (full), Diagnostics (major & minor), Environmental (major & minor), Inventory (full), Test or System Log information.
•![]() Transport Gateway (TG) - Securely transports Call Home messages from the customer hardware to the Smart Call Home service on the Cisco Backend. A Smart Call Home software client that runs on a device under the Windows 2000, Windows 2003, Windows XP, Solaris or Linux operating systems. The Transport Gateway acts as an intermediary device and is capable of forwarding supported messages collected from Smart Call Home Client devices and sends them to the Smart Call Home System using an HTTPS connection.
Transport Gateway (TG) - Securely transports Call Home messages from the customer hardware to the Smart Call Home service on the Cisco Backend. A Smart Call Home software client that runs on a device under the Windows 2000, Windows 2003, Windows XP, Solaris or Linux operating systems. The Transport Gateway acts as an intermediary device and is capable of forwarding supported messages collected from Smart Call Home Client devices and sends them to the Smart Call Home System using an HTTPS connection.
CA Root Certificate Update Process
Periodically, Cisco updates security credentials to ensure the continued secure communications to the Smart Call Home back-end. This section applies to those who are using either Transport Gateway or the HTTPS method for communicating to the back-end.
When there is a security credential update from Cisco, instructions will be sent via e-mail to SCH-registered user e-mail addresses that are linked to a valid CCO ID. Instructions for updating security credentials are as follows:
There are two methods for secure communication to the Smart Call Home backend, Transport Gateway (TG) and HTTPS. Both of these options have a certificate update process:
There are two methods for secure communication to the Smart Call Home backend, Transport Gateway (TG) and HTTPS. Both of these options have a certificate update process:
•![]() For Transport Gateway, there are two variations for the certificate update process:
For Transport Gateway, there are two variations for the certificate update process:
–![]() Linux/Solaris, which uses the certUpgrader_script.zip to update the TG keystore (certificate) file.
Linux/Solaris, which uses the certUpgrader_script.zip to update the TG keystore (certificate) file.
–![]() Windows, which uses the certUpgrader_windows.zip to update the TG keystore (certificate) file.
Windows, which uses the certUpgrader_windows.zip to update the TG keystore (certificate) file.
•![]() For the HTTPS method, there are two variations (regardless of platform), IOS devices and Nexus 7000 devices.
For the HTTPS method, there are two variations (regardless of platform), IOS devices and Nexus 7000 devices.
–![]() IOS devices use either IOS certificate content from this section of the Smart Call Home User Guide, or use the contents from the Verisign-G3-SSCA.zip file.
IOS devices use either IOS certificate content from this section of the Smart Call Home User Guide, or use the contents from the Verisign-G3-SSCA.zip file.
–![]() Nexus 7000 devices use either the "chained" certificate content from this section of the Smart Call Home User Guide, or use the combined contents of the certificate files in the Verisign-CA-Certs.tar file.
Nexus 7000 devices use either the "chained" certificate content from this section of the Smart Call Home User Guide, or use the combined contents of the certificate files in the Verisign-CA-Certs.tar file.
Transport Gateway Certificate Update Process
There are two Transport Gateway certificate update processes:
•![]() Update the Linux/Solaris Root CA Certificate
Update the Linux/Solaris Root CA Certificate
•![]() Update the Window's Root CA Certificate
Update the Window's Root CA Certificate
Both of these processes use scripts that update the certificate file on the Transport Gateway.
Update the Linux/Solaris Root CA Certificate
The following information explains how to update the Linux/Solaris Root CA Certificate for Transport Gateway Users. This process instructs you how to download and use the certUpgrader_script.zip file:
•![]() Go to the following URL:
Go to the following URL:

•![]() On the Download Software window, click the Download Now button for the certUpgrader_script.zip file; the Download Cart window appears.
On the Download Software window, click the Download Now button for the certUpgrader_script.zip file; the Download Cart window appears.
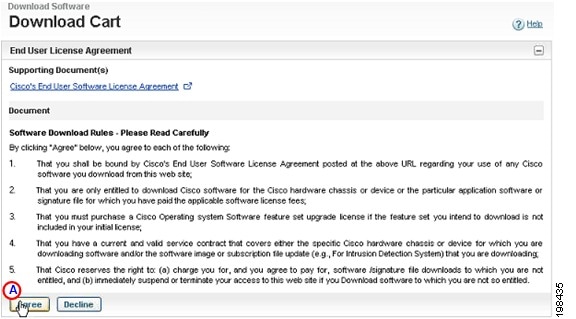
•![]() On the Download Cart window, click Agree;
On the Download Cart window, click Agree; the Select a Download Option area appears.
the Select a Download Option area appears.
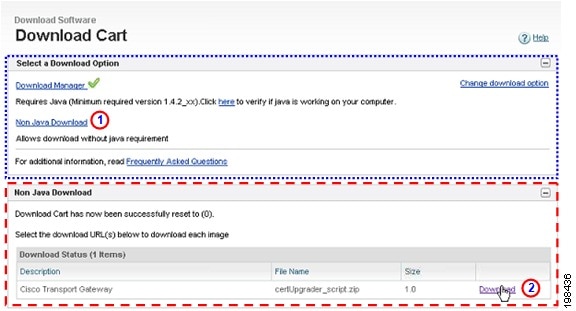
•![]() In the Select a Download Option area
In the Select a Download Option area  click the Non Java Download option;
click the Non Java Download option; the Non Java Download area appears.
the Non Java Download area appears.
•![]() Click Download
Click Download  for the certUpgrader_script.zip file; the file is downloaded to your computer.
for the certUpgrader_script.zip file; the file is downloaded to your computer.
•![]() On the Transport Gateway device, navigate to the bin directory of the Transport Gateway installation location.
On the Transport Gateway device, navigate to the bin directory of the Transport Gateway installation location.
Example: /opt/CSCOSchtg/tg/bin
•![]() Unzip the certUpgrader_script.zip file to the bin directory.
Unzip the certUpgrader_script.zip file to the bin directory.
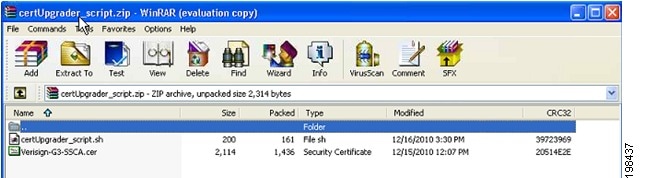
•![]() After unzipping the file, the certUpgrader_script.sh and Verisign-G3-SSCA.cer files will be available in the bin directory.
After unzipping the file, the certUpgrader_script.sh and Verisign-G3-SSCA.cer files will be available in the bin directory.
•![]() Stop the TG service, if it's running.
Stop the TG service, if it's running.
•![]() Click on the certUpgrader_script.sh batch file to start importing the new root CA cert to the TG Certificate chain.
Click on the certUpgrader_script.sh batch file to start importing the new root CA cert to the TG Certificate chain.

Note ![]() Give permission, if not available, for the certUpgrader_script.sh patch file (i.e. # chmod 777 certUpgrader_script.sh)
Give permission, if not available, for the certUpgrader_script.sh patch file (i.e. # chmod 777 certUpgrader_script.sh)
•![]() When asked if you want to trust this certificate, enter yes and press ENTER.
When asked if you want to trust this certificate, enter yes and press ENTER.
•![]() Restart the TG service; now the TG should be able to communicate with the backend servers, which have the new root CA certificate.
Restart the TG service; now the TG should be able to communicate with the backend servers, which have the new root CA certificate.
Update the Window's Root CA Certificate
The following information is the procedure for how to update the Windows Root CA Certificate for Transport Gateway Users. This process instructs you how to download and use the certUpgrader_windows.zip file:
•![]() Go to the following URL:
Go to the following URL:
http://www.cisco.com/cisco/software/release.html?mdfid=282152778&catid=268439477&softwareid=283490182&release=3.1.1&rellifecycle=&relind=AVAILABLE&reltype=latest

•![]() On the Download Software window, click the Download Now button for the certUpgrader_windows.zip file; the Download Cart window appears.
On the Download Software window, click the Download Now button for the certUpgrader_windows.zip file; the Download Cart window appears.
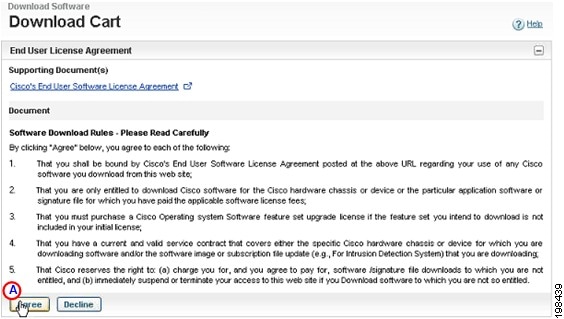
On the Download Cart window, click Agree;  the Select a Download Option area appears.
the Select a Download Option area appears.
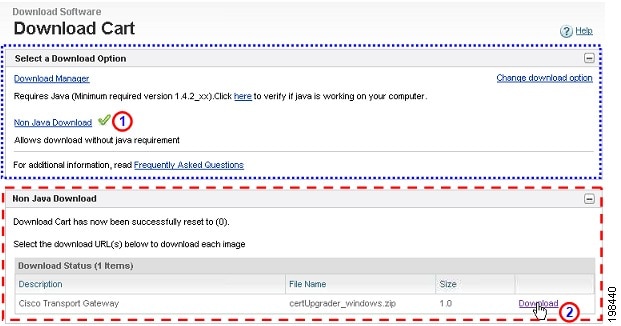
•![]() In the Select a Download Option area
In the Select a Download Option area  click the Non Java Download option;
click the Non Java Download option;  the Non Java Download area appears.
the Non Java Download area appears.
•![]() Click Download
Click Download  for the certUpgrader_windows.zip file; the file is downloaded to your computer.
for the certUpgrader_windows.zip file; the file is downloaded to your computer.
•![]() On the Transport Gateway device, navigate to the bin directory of the Transport Gateway installation location.
On the Transport Gateway device, navigate to the bin directory of the Transport Gateway installation location.
Example: C:\Program Files\Cisco Systems\Cisco Transport Gateway\Transport Gateway\bin
•![]() Unzip the certUpgrader_windows.zip file to the bin directory.
Unzip the certUpgrader_windows.zip file to the bin directory.
•![]() After unzipping the file the certUpgrader_windows.bat and Verisign-G3-SSCA.cer files will be available in the bin directory.
After unzipping the file the certUpgrader_windows.bat and Verisign-G3-SSCA.cer files will be available in the bin directory.
•![]() Stop the TG service, if it's running.
Stop the TG service, if it's running.
•![]() Click on the certUpgrader_windows.bat batch file to start importing the new root CA cert to the TG Certificate chain.
Click on the certUpgrader_windows.bat batch file to start importing the new root CA cert to the TG Certificate chain.
•![]() When asked to enter keystore password: enter Test123% and press ENTER.
When asked to enter keystore password: enter Test123% and press ENTER.
•![]() When asked if you want to trust this certificate, enter yes and press ENTER.
When asked if you want to trust this certificate, enter yes and press ENTER.
•![]() Restart the TG service; now the TG should be able to communicate with the backend servers, which have the new root CA certificate.
Restart the TG service; now the TG should be able to communicate with the backend servers, which have the new root CA certificate.
HTTPS Certificate Processes (New or Update)
There are two different HTTPS certificate processes:
•![]() HTTPS Certificate Process for All Devices Except Nexus 7000 Devices
HTTPS Certificate Process for All Devices Except Nexus 7000 Devices
•![]() HTTPS Certificate Process for Nexus 7000 Devices
HTTPS Certificate Process for Nexus 7000 Devices
HTTPS Certificate Process for All Devices Except Nexus 7000 Devices
There are two different time frames when you will be using certificate content on your IOS device, when you are:
•![]() Adding the certificate to an IOS device, for the first time; you will perform the steps and use the certificate data identified below in this document.
Adding the certificate to an IOS device, for the first time; you will perform the steps and use the certificate data identified below in this document.
•![]() When you are updating an expired security certificate on an IOS device, you can use the certificate content contained in the Verisign-G3-SSCA.zip file.
When you are updating an expired security certificate on an IOS device, you can use the certificate content contained in the Verisign-G3-SSCA.zip file.
Adding the Certificate to a non-Nexus 7000 Device
For all IOS devices, use this procedure to update the Root CA Certificate for HTTPS Users:
•![]() Identify all trust points.
Identify all trust points.
•![]() Delete the existing Smart Call Home Certificate trust point.
Delete the existing Smart Call Home Certificate trust point.
•![]() Create a new trust point.
Create a new trust point.
•![]() Copy the new certificate.
Copy the new certificate.
•![]() Save and send test message.
Save and send test message.
For all IOS devices, use the following specific instructions to install the new certificate:
•![]() If the old trustpoint name is not cisco then replace the text in <angle brackets> with the appropriate trustpoint name, or remove the lines with the blue text if the old trustpoint is needed or does not exist.
If the old trustpoint name is not cisco then replace the text in <angle brackets> with the appropriate trustpoint name, or remove the lines with the blue text if the old trustpoint is needed or does not exist.
•![]() Enter the following commands:
Enter the following commands:
config t
no crypto ca trustpoint <cisco>
yes
crypto ca trustpoint cisco
enroll terminal
exit
crypto ca authenticate cisco
When you are adding the certificate to your IOS device for the first time, use the following certificate content:
IMPORTANT: PLEASE COPY THE CERTIFICATE CONTENT BELOW USING A PLAIN TEXT EDITOR AND PASTE THE CONTENT AS PLAIN TEXT; THIS REMOVES ANY POSSIBLE FORMATTING SYMBOLS, WHICH ALTER THE CERTIFICATE CONTENT.

Note ![]() Your copy of the security certificate should include each and every character, including the certificate markers. Remove any blank lines either after or before the certificate markers.
Your copy of the security certificate should include each and every character, including the certificate markers. Remove any blank lines either after or before the certificate markers.
-----BEGIN CERTIFICATE-----
MIIF7DCCBNSgAwIBAgIQbsx6pacDIAm4zrz06VLUkTANBgkqhkiG9w0BAQUFADCByjELMA kGA1UEBhMCVVMxFzAVBgNVBAoTDlZlcmlTaWduLCBJbmMuMR8wHQYDVQQLExZWZXJpU2ln biBUcnVzdCBOZXR3b3JrMTowOAYDVQQLEzEoYykgMjAwNiBWZXJpU2lnbiwgSW5jLiAtIE ZvciBhdXRob3JpemVkIHVzZSBvbmx5MUUwQwYDVQQDEzxWZXJpU2lnbiBDbGFzcyAzIFB1 YmxpYyBQcmltYXJ5IENlcnRpZmljYXRpb24gQXV0aG9yaXR5IC0gRzUwHhcNMTAwMjA4MD AwMDAwWhcNMjAwMjA3MjM1OTU5WjCBtTELMAkGA1UEBhMCVVMxFzAVBgNVBAoTDlZlcmlT aWduLCBJbmMuMR8wHQYDVQQLExZWZXJpU2lnbiBUcnVzdCBOZXR3b3JrMTswOQYDVQQLEz JUZXJtcyBvZiB1c2UgYXQgaHR0cHM6Ly93d3cudmVyaXNpZ24uY29tL3JwYSAoYykxMDEv MC0GA1UEAxMmVmVyaVNpZ24gQ2xhc3MgMyBTZWN1cmUgU2VydmVyIENBIC0gRzMwggEiMA 0GCSqGSIb3DQEBAQUAA4IBDwAwggEKAoIBAQCxh4QfwgxF9byrJZenraI+nLr2wTm4i8rC rFbG5btljkRPTc5v7QlK1K9OEJxoiy6Ve4mbE8riNDTB81vzSXtig0iBdNGIeGwCU/m8f0 MmV1gzgzszChew0E6RJK2GfWQS3HRKNKEdCuqWHQsV/KNLO85jiND4LQyUhhDKtpo9yus3 nABINYYpUHjoRWPNGUFP9ZXse5jUxHGzUL4os4+guVOc9cosI6n9FAboGLSa6Dxugf3kzT U2s1HTaewSulZub5tXxYsU5w7HnO1KVGrJTcW/EbGuHGeBy0RVM5l/JJs/U0V/hhrzPPpt f4H1uErT9YU3HLWm0AnkGHs4TvoPAgMBAAGjggHfMIIB2zA0BggrBgEFBQcBAQQoMCYwJA YIKwYBBQUHMAGGGGh0dHA6Ly9vY3NwLnZlcmlzaWduLmNvbTASBgNVHRMBAf8ECDAGAQH/ AgEAMHAGA1UdIARpMGcwZQYLYIZIAYb4RQEHFwMwVjAoBggrBgEFBQcCARYcaHR0cHM6Ly 93d3cudmVyaXNpZ24uY29tL2NwczAqBggrBgEFBQcCAjAeGhxodHRwczovL3d3dy52ZXJp c2lnbi5jb20vcnBhMDQGA1UdHwQtMCswKaAnoCWGI2h0dHA6Ly9jcmwudmVyaXNpZ24uY2 9tL3BjYTMtZzUuY3JsMA4GA1UdDwEB/wQEAwIBBjBtBggrBgEFBQcBDARhMF+hXaBbMFkw VzBVFglpbWFnZS9naWYwITAfMAcGBSsOAwIaBBSP5dMahqyNjmvDz4Bq1EgYLHsZLjAlFi NodHRwOi8vbG9nby52ZXJpc2lnbi5jb20vdnNsb2dvLmdpZjAoBgNVHREEITAfpB0wGzEZ MBcGA1UEAxMQVmVyaVNpZ25NUEtJLTItNjAdBgNVHQ4EFgQUDURcFlNEwYJ+HSCrJfQBY9 i+eaUwHwYDVR0jBBgwFoAUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMwDQYJKoZIhvcNAQEFBQAD ggEBAAyDJO/dwwzZWJz+NrbrioBL0aP3nfPMU++CnqOh5pfBWJ11bOAdG0z60cEtBcDqbr IicFXZIDNAMwfCZYP6j0M3m+oOmmxw7vacgDvZN/R6bezQGH1JSsqZxxkoor7YdyT3hSaG bYcFQEFn0Sc67dxIHSLNCwuLvPSxe/20majpdirhGi2HbnTTiN0eIsbfFrYrghQKlFzyUO yvzv9iNw2tZdMGQVPtAhTItVgooazgW+yzf5VK+wPIrSbb5mZ4EkrZn0L74ZjmQoObj49n JOhhGbXdzbULJgWOw27EyHW4Rs/iGAZeqa6ogZpHFt4MKGwlJ7net4RYxh84HqTEy2Y=
-----END CERTIFICATE-----
quit
yes
end
write mem
call-home send alert-group inventory profile CiscoTAC-1
Downloading a New Certificate for an IOS Device
If you need the new CA Root certificate file it can be downloaded perform the following steps:
•![]() Go to the following URL:
Go to the following URL:
•![]() On the Download Software window, click the Download Now button for the Verisign-G3-SSCA.zip file
On the Download Software window, click the Download Now button for the Verisign-G3-SSCA.zip file
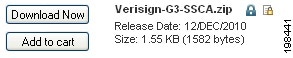
•![]() Unzip the file and use the data contained in the certificate file.
Unzip the file and use the data contained in the certificate file.
HTTPS Certificate Process for Nexus 7000 Devices
There are two different time frames when you will be using HTTPS certificate content on your Nexus 7000 device, when you are:
•![]() Adding the certificate to a Nexus 7000 device, for the first time; you will perform the steps and use the certificate data identified below in this document.
Adding the certificate to a Nexus 7000 device, for the first time; you will perform the steps and use the certificate data identified below in this document.
•![]() When you are updating an expired security certificate on a Nexus 7000 device, you will use the script files and certificate data contained in the Verisign-CAs-Certs.tar file.
When you are updating an expired security certificate on a Nexus 7000 device, you will use the script files and certificate data contained in the Verisign-CAs-Certs.tar file.
Adding the Certificate to a Nexus 7000 Device
For Nexus 7000 devices, use the following instructions to install a security root certificates chain:
•![]() Copy the root certificates chain below.
Copy the root certificates chain below.
•![]() Configure a trust-point and prepare to enroll the certificate via the terminal using copy and paste when prompted.
Configure a trust-point and prepare to enroll the certificate via the terminal using copy and paste when prompted.
NX-7000(config)#crypto ca trustpoint cisco
NX-7000(config-trustpoint)#enroll terminal
NX-7000(config-trustpoint)#crypto ca authenticate cisco
Input (cut & paste) the CA certificate (chain) in PEM format.
IMPORTANT: PLEASE COPY THE CERTIFICATE CONTENT BELOW USING A PLAIN TEXT EDITOR AND PASTE THE CONTENT AS PLAIN TEXT; THIS REMOVES ANY POSSIBLE FORMATTING SYMBOLS, WHICH ALTER THE CERTIFICATE CONTENT.

Note ![]() Your copy of the security certificate should include each and every character, including the certificate markers. Remove any blank lines either after or before the certificate markers.
Your copy of the security certificate should include each and every character, including the certificate markers. Remove any blank lines either after or before the certificate markers.
-----BEGIN CERTIFICATE-----
MIICPDCCAaUCEHC65B0Q2Sk0tjjKewPMur8wDQYJKoZIhvcNAQECBQAwXzELMAkGA1UEBh MCVVMxFzAVBgNVBAoTDlZlcmlTaWduLCBJbmMuMTcwNQYDVQQLEy5DbGFzcyAzIFB1Ymxp YyBQcmltYXJ5IENlcnRpZmljYXRpb24gQXV0aG9yaXR5MB4XDTk2MDEyOTAwMDAwMFoXDT I4MDgwMTIzNTk1OVowXzELMAkGA1UEBhMCVVMxFzAVBgNVBAoTDlZlcmlTaWduLCBJbmMu MTcwNQYDVQQLEy5DbGFzcyAzIFB1YmxpYyBQcmltYXJ5IENlcnRpZmljYXRpb24gQXV0aG 9yaXR5MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDJXFme8huKARS0EN8EQNvjV69q RUCPhAwL0TPZ2RHP7gJYHyX3KqhEBarsAx94f56TuZoAqiN91qyFomNFx3InzPRMxnVx0j nvT0Lwdd8KkMaOIG+YD/isI19wKTakyYbnsZogy1Olhec9vn2a/iRFM9x2Fe0PonFkTGUu gWhFpwIDAQABMA0GCSqGSIb3DQEBAgUAA4GBALtMEivPLCYATxQT3ab7/AoRhIzzKBxnki 98tsX63/Dolbwdj2wsqFHMc9ikwFPwTtYmwHYBV4GSXiHx0bH/59AhWM1pF+NEHJwZRDmJ XNycAA9WjQKZ7aKQRUzkuxCkPfAyAw7xzvjoyVGM5mKf5p/AfbdynMk2OmufTqj/ZA1k
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
MIIGNDCCBRygAwIBAgIQWrQ6b86cjzk7c3BoO7KqETANBgkqhkiG9w0BAQUFADCBtTELMA kGA1UEBhMCVVMxFzAVBgNVBAoTDlZlcmlTaWduLCBJbmMuMR8wHQYDVQQLExZWZXJpU2ln biBUcnVzdCBOZXR3b3JrMTswOQYDVQQLEzJUZXJtcyBvZiB1c2UgYXQgaHR0cHM6Ly93d3 cudmVyaXNpZ24uY29tL3JwYSAoYykxMDEvMC0GA1UEAxMmVmVyaVNpZ24gQ2xhc3MgMyBT ZWN1cmUgU2VydmVyIENBIC0gRzMwHhcNMTAxMjEyMDAwMDAwWhcNMTExMjEyMjM1OTU5Wj B5MQswCQYDVQQGEwJVUzETMBEGA1UECBMKQ2FsaWZvcm5pYTERMA8GA1UEBxQIU2FuIEpv c2UxFjAUBgNVBAoUDUNpc2NvIFN5c3RlbXMxEDAOBgNVBAsUB0FUUy1BV1MxGDAWBgNVBA MUD3Rvb2xzLmNpc2NvLmNvbTCBnzANBgkqhkiG9w0BAQEFAAOBjQAwgYkCgYEAzouIOWzv djJlWDPYk55kyhbnxxYv6S1eZ0blZ09XdipLrf+YluZ8++ux3Ld6lr6QnVdI1/AYYA2K5F 4+2D+ZJUwLnaQW1QYIzbmeVhbdcAa7IwuR+P8eMUaetOUAdC641QvMXtpZQ5I0WdTS2IV/ O7A3H1V3QInS2+0xnnehTT8CAwEAAaOCAv0wggL5MIIBKAYDVR0RBIIBHzCCARuCD3Rvb2 xzLmNpc2NvLmNvbYIOYXBwcy5jaXNjby5jb22CEHRvb2xzMS5jaXNjby5jb22CEHRvb2xz Mi5jaXNjby5jb22CEHRvb2xzOS5jaXNjby5jb22CFHRvb2xzLXdhczUuY2lzY28uY29tgh R0b29scy13YXM2LmNpc2NvLmNvbYIUdG9vbHMtd2FzNy5jaXNjby5jb22CFXRvb2xzLXRl c3QzLmNpc2NvLmNvbYIVdG9vbHMtdGVzdDQuY2lzY28uY29tghp0b29scy10ZXN0MS13YX M3LmNpc2NvLmNvbYIadG9vbHMyLXRlc3Qtd2FzNi5jaXNjby5jb22CGnRvb2xzMi10ZXN0 LXdhczcuY2lzY28uY29tMAkGA1UdEwQCMAAwCwYDVR0PBAQDAgWgMEUGA1UdHwQ+MDwwOq A4oDaGNGh0dHA6Ly9TVlJTZWN1cmUtRzMtY3JsLnZlcmlzaWduLmNvbS9TVlJTZWN1cmVH My5jcmwwRAYDVR0gBD0wOzA5BgtghkgBhvhFAQcXAzAqMCgGCCsGAQUFBwIBFhxodHRwcz ovL3d3dy52ZXJpc2lnbi5jb20vcnBhMB0GA1UdJQQWMBQGCCsGAQUFBwMBBggrBgEFBQcD AjAfBgNVHSMEGDAWgBQNRFwWU0TBgn4dIKsl9AFj2L55pTB2BggrBgEFBQcBAQRqMGgwJA YIKwYBBQUHMAGGGGh0dHA6Ly9vY3NwLnZlcmlzaWduLmNvbTBABggrBgEFBQcwAoY0aHR0 cDovL1NWUlNlY3VyZS1HMy1haWEudmVyaXNpZ24uY29tL1NWUlNlY3VyZUczLmNlcjBuBg grBgEFBQcBDARiMGChXqBcMFowWDBWFglpbWFnZS9naWYwITAfMAcGBSsOAwIaBBRLa7ko lgYMu9BSOJsprEsHiyEFGDAmFiRodHRwOi8vbG9nby52ZXJpc2lnbi5jb20vdnNsb2dvMS 5naWYwDQYJKoZIhvcNAQEFBQADggEBAIskILQZDB7FjTQoqyu3LlSLF1yl+6bdhgXOJFmC 9Zdl2g/91hHpKVs3CYPhGcTef8ehVwa3CN4Iuvatvpbf+u1/xayQ8kppjQ3G2Akv9QofB9 dbMmnd6r0KmcLNy7Bxn6L96Fu2XbAzoHQRYrLIMr4F4A+A1yDSjKO6DbIQQzT8vFHtboI0 HjoVGrKEH5+KqB1RGYwfJDUjdfQoifFHW78Ax/NbeUd8i4/HMbM3zT3TW8oGlrUJaFiFMJ wDTUspBzYYKPvDOcl+uRFSeeoOJsB3L6U2ckvqQOzSJ4vZ/Jh6B0UBpbjgL3Tm8PraGikU CCFlA7a9V0JX0dgLdRpWgUI=
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
MIIE0DCCBDmgAwIBAgIQJQzo4DBhLp8rifcFTXz4/TANBgkqhkiG9w0BAQUFADBfMQswCQ YDVQQGEwJVUzEXMBUGA1UEChMOVmVyaVNpZ24sIEluYy4xNzA1BgNVBAsTLkNsYXNzIDMg UHVibGljIFByaW1hcnkgQ2VydGlmaWNhdGlvbiBBdXRob3JpdHkwHhcNMDYxMTA4MDAwMD AwWhcNMjExMTA3MjM1OTU5WjCByjELMAkGA1UEBhMCVVMxFzAVBgNVBAoTDlZlcmlTaWdu LCBJbmMuMR8wHQYDVQQLExZWZXJpU2lnbiBUcnVzdCBOZXR3b3JrMTowOAYDVQQLEzEoYy kgMjAwNiBWZXJpU2lnbiwgSW5jLiAtIEZvciBhdXRob3JpemVkIHVzZSBvbmx5MUUwQwYD VQQDEzxWZXJpU2lnbiBDbGFzcyAzIFB1YmxpYyBQcmltYXJ5IENlcnRpZmljYXRpb24gQX V0aG9yaXR5IC0gRzUwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEKAoIBAQCvJAgIKXo1 nmAMqudLO07cfLw8RRy7K+D+KQL5VwijZIUVJ/XxrcgxiV0i6CqqpkKzj/i5Vbext0uz/o 9+B1fs70PbZmIVYc9gDaTY3vjgw2IIPVQT60nKWVSFJuUrjxuf6/WhkcIzSdhDY2pSS9KP 6HBRTdGJaXvHcPaz3BJ023tdS1bTlr8Vd6Gw9KIl8q8ckmcY5fQGBO+QueQA5N06tRn/Ar r0PO7gi+s3i+z016zy9vA9r911kTMZHRxAy3QkGSGT2RT+rCpSx4/VBEnkjWNHiDxpg8v+ R70rfk/Fla4OndTRQ8Bnc+MUCH7lP59zuDMKz10/NIeWiu5T6CUVAgMBAAGjggGbMIIBlz APBgNVHRMBAf8EBTADAQH/MDEGA1UdHwQqMCgwJqAkoCKGIGh0dHA6Ly9jcmwudmVyaXNp Z24uY29tL3BjYTMuY3JsMA4GA1UdDwEB/wQEAwIBBjA9BgNVHSAENjA0MDIGBFUdIAAwKj AoBggrBgEFBQcCARYcaHR0cHM6Ly93d3cudmVyaXNpZ24uY29tL2NwczAdBgNVHQ4EFgQU f9Nlp8Ld7LvwMAnzQzn6Aq8zMTMwbQYIKwYBBQUHAQwEYTBfoV2gWzBZMFcwVRYJaW1hZ2 UvZ2lmMCEwHzAHBgUrDgMCGgQUj+XTGoasjY5rw8+AatRIGCx7GS4wJRYjaHR0cDovL2xv Z28udmVyaXNpZ24uY29tL3ZzbG9nby5naWYwNAYIKwYBBQUHAQEEKDAmMCQGCCsGAQUFBz ABhhhodHRwOi8vb2NzcC52ZXJpc2lnbi5jb20wPgYDVR0lBDcwNQYIKwYBBQUHAwEGCCsG AQUFBwMCBggrBgEFBQcDAwYJYIZIAYb4QgQBBgpghkgBhvhFAQgBMA0GCSqGSIb3DQEBBQ UAA4GBABMC3fjohgDyWvj4IAxZiGIHzs73Tvm7WaGY5eE43U68ZhjTresY8g3JbT5KlCDD PLq9ZVTGr0SzEK0saz6r1we2uIFjxfleLuUqZ87NMwwq14lWAyMfs77oOghZtOxFNfeKW/ 9mz1Cvxm1XjRl4t7mi0VfqH5pLr7rJjhJ+xr3/
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
MIIF7DCCBNSgAwIBAgIQbsx6pacDIAm4zrz06VLUkTANBgkqhkiG9w0BAQUFADCByjELMA kGA1UEBhMCVVMxFzAVBgNVBAoTDlZlcmlTaWduLCBJbmMuMR8wHQYDVQQLExZWZXJpU2ln biBUcnVzdCBOZXR3b3JrMTowOAYDVQQLEzEoYykgMjAwNiBWZXJpU2lnbiwgSW5jLiAtIE ZvciBhdXRob3JpemVkIHVzZSBvbmx5MUUwQwYDVQQDEzxWZXJpU2lnbiBDbGFzcyAzIFB1 YmxpYyBQcmltYXJ5IENlcnRpZmljYXRpb24gQXV0aG9yaXR5IC0gRzUwHhcNMTAwMjA4MD AwMDAwWhcNMjAwMjA3MjM1OTU5WjCBtTELMAkGA1UEBhMCVVMxFzAVBgNVBAoTDlZlcmlT aWduLCBJbmMuMR8wHQYDVQQLExZWZXJpU2lnbiBUcnVzdCBOZXR3b3JrMTswOQYDVQQLEz JUZXJtcyBvZiB1c2UgYXQgaHR0cHM6Ly93d3cudmVyaXNpZ24uY29tL3JwYSAoYykxMDEv MC0GA1UEAxMmVmVyaVNpZ24gQ2xhc3MgMyBTZWN1cmUgU2VydmVyIENBIC0gRzMwggEiMA 0GCSqGSIb3DQEBAQUAA4IBDwAwggEKAoIBAQCxh4QfwgxF9byrJZenraI+nLr2wTm4i8rC rFbG5btljkRPTc5v7QlK1K9OEJxoiy6Ve4mbE8riNDTB81vzSXtig0iBdNGIeGwCU/m8f0 MmV1gzgzszChew0E6RJK2GfWQS3HRKNKEdCuqWHQsV/KNLO85jiND4LQyUhhDKtpo9yus3 nABINYYpUHjoRWPNGUFP9ZXse5jUxHGzUL4os4+guVOc9cosI6n9FAboGLSa6Dxugf3kzT U2s1HTaewSulZub5tXxYsU5w7HnO1KVGrJTcW/EbGuHGeBy0RVM5l/JJs/U0V/hhrzPPpt f4H1uErT9YU3HLWm0AnkGHs4TvoPAgMBAAGjggHfMIIB2zA0BggrBgEFBQcBAQQoMCYwJA YIKwYBBQUHMAGGGGh0dHA6Ly9vY3NwLnZlcmlzaWduLmNvbTASBgNVHRMBAf8ECDAGAQH/ AgEAMHAGA1UdIARpMGcwZQYLYIZIAYb4RQEHFwMwVjAoBggrBgEFBQcCARYcaHR0cHM6Ly 93d3cudmVyaXNpZ24uY29tL2NwczAqBggrBgEFBQcCAjAeGhxodHRwczovL3d3dy52ZXJp c2lnbi5jb20vcnBhMDQGA1UdHwQtMCswKaAnoCWGI2h0dHA6Ly9jcmwudmVyaXNpZ24uY2 9tL3BjYTMtZzUuY3JsMA4GA1UdDwEB/wQEAwIBBjBtBggrBgEFBQcBDARhMF+hXaBbMFkw VzBVFglpbWFnZS9naWYwITAfMAcGBSsOAwIaBBSP5dMahqyNjmvDz4Bq1EgYLHsZLjAlFi NodHRwOi8vbG9nby52ZXJpc2lnbi5jb20vdnNsb2dvLmdpZjAoBgNVHREEITAfpB0wGzEZ MBcGA1UEAxMQVmVyaVNpZ25NUEtJLTItNjAdBgNVHQ4EFgQUDURcFlNEwYJ+HSCrJfQBY9 i+eaUwHwYDVR0jBBgwFoAUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMwDQYJKoZIhvcNAQEFBQAD ggEBAAyDJO/dwwzZWJz+NrbrioBL0aP3nfPMU++CnqOh5pfBWJ11bOAdG0z60cEtBcDqbr IicFXZIDNAMwfCZYP6j0M3m+oOmmxw7vacgDvZN/R6bezQGH1JSsqZxxkoor7YdyT3hSaG bYcFQEFn0Sc67dxIHSLNCwuLvPSxe/20majpdirhGi2HbnTTiN0eIsbfFrYrghQKlFzyUO yvzv9iNw2tZdMGQVPtAhTItVgooazgW+yzf5VK+wPIrSbb5mZ4EkrZn0L74ZjmQoObj49n JOhhGbXdzbULJgWOw27EyHW4Rs/iGAZeqa6ogZpHFt4MKGwlJ7net4RYxh84HqTEy2Y=
-----END CERTIFICATE-----
On the next line following the certificate content, end the input by entering END OF INPUT:
Hit Enter, a prompt appears asking "Do you accept this certificate? [yes/no]:"; enter yes
Exit configuration mode and save the configuration -
NX-7000(config)#end
NX-7000#copy running-config startup-config
Downloading a New Certificate for a Nexus 7000 Device
If you need the new certificate files that comprise the CA Root certificate, perform the following steps:
Go to the following URL:
On the Download Software window, click the Download Now button for the Verisign-CAs-Certs.tar file
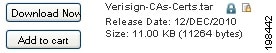
Gunzip the Verisign-CAs-Certs.tar file to the directory of your choice.
Additional Information
For more information on the SSL certificate, see the information at the following URL:
https://knowledge.verisign.com/support/ssl-certificates-support/index?page=content&id=AD146
For technical support, please contact Cisco Smart Services Bureau (SSB) via:
Email: ask-smart-services@cisco.com <mailto:ask-smart-services@cisco.com>
Telephone:
From the rest of the world, choose the appropriate phone number from http://www.cisco.com/en/US/support/tsd_cisco_worldwide_contacts.html
 Feedback
Feedback