- Index
- Preface
- Overview
- Using the Command-Line Interface
- Getting Started with CMS
- Assigning the Switch IP Address and Default Gateway
- Clustering Switches
- Administering the Switch
- Configuring SDM Templates
- Configuring Switch-Based Authentication
- Configuring 802.1X Port-Based Authentication
- Configuring Interface Characteristics
- Configuring SmartPort Macros
- Configuring VLANs
- Configuring VTP
- Configuring Voice VLAN
- Configuring STP
- Configuring MSTP
- Configuring Optional Spanning-Tree Features
- Configuring DHCP Features
- Configuring IGMP Snooping and MVR
- Configuring Port-Based Traffic Control
- Configuring CDP
- Configuring UDLD
- Configuring SPAN and RSPAN
- Configuring RMON
- Configuring System Message Logging
- Configuring SNMP
- Configuring Network Security with ACLs
- Configuring QoS
- Configuring EtherChannels
- Configuring IP Unicast Routing
- Configuring HSRP
- Configuring IP Multicast Routing
- Configuring MSDP
- Configuring Fallback Bridging
- Troubleshooting
- Supported MIBs
- Working with the Cisco IOS File System, Configuration Files, and Software Images
- Unsupported Commands in Cisco IOS Release 12.1(19)EA1
Catalyst 3560 Switch Software Configuration Guide, Rel. 12.1(19)EA1
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- August 3, 2007
Chapter: Configuring Port-Based Traffic Control
Configuring Port-Based Traffic Control
This chapter describes how to configure the port-based traffic control features on the Catalyst 3560 switch.

Note ![]() For complete syntax and usage information for the commands used in this chapter, refer to the command reference for this release.
For complete syntax and usage information for the commands used in this chapter, refer to the command reference for this release.
This chapter consists of these sections:
•![]() Displaying Port-Based Traffic Control Settings
Displaying Port-Based Traffic Control Settings
Configuring Storm Control
These sections include storm control configuration information and procedures:
•![]() Default Storm Control Configuration
Default Storm Control Configuration
Understanding Storm Control
Storm control prevents switchports on a LAN from being disrupted by a broadcast, multicast, or unicast storm on one of the physical interfaces. A LAN storm occurs when packets flood the LAN, creating excessive traffic and degrading network performance. Errors in the protocol-stack implementation or in the network configuration can cause a storm.
Storm control (or traffic suppression) monitors incoming traffic statistics over a time period and compares the measurement with a predefined suppression level threshold. The threshold represents the percentage of the total available bandwidth of the port. The switch supports separate storm control thresholds for broadcast, multicast, and unicast traffic. If the threshold of a traffic type is reached, further traffic of that type is suppressed until the incoming traffic falls below the threshold level.

Note ![]() When the storm control threshold for multicast traffic is reached, all multicast traffic except control traffic, such as bridge protocol data unit (BDPU) and Cisco Discovery Protocol (CDP) frames, are blocked. However, the switch does not differentiate between routing updates, such as OSPF, and regular multicast data traffic, so both types of traffic are blocked.
When the storm control threshold for multicast traffic is reached, all multicast traffic except control traffic, such as bridge protocol data unit (BDPU) and Cisco Discovery Protocol (CDP) frames, are blocked. However, the switch does not differentiate between routing updates, such as OSPF, and regular multicast data traffic, so both types of traffic are blocked.
When storm control is enabled, the switch monitors packets passing from an interface to the switching bus and determines if the packet is unicast, multicast, or broadcast. The switch monitors the number of broadcast, multicast, or unicast packets received within a 200-millisecond time interval, and when a threshold for one type of traffic is reached, that type of traffic is dropped. This threshold is specified as a percentage of total available bandwidth that can be used by broadcast (multicast or unicast) traffic.
The graph in Figure 20-1 shows broadcast traffic patterns on an interface over a given period of time. The example can also be applied to multicast and unicast traffic. In this example, the broadcast traffic being forwarded exceeded the configured threshold between time intervals T1 and T2 and between T4 and T5. When the amount of specified traffic exceeds the threshold, all traffic of that kind is dropped for the next time period. Therefore, broadcast traffic is blocked during the intervals following T2 and T5. At the next time interval (for example, T3), if broadcast traffic does not exceed the threshold, it is again forwarded.
Figure 20-1 Broadcast Storm Control Example
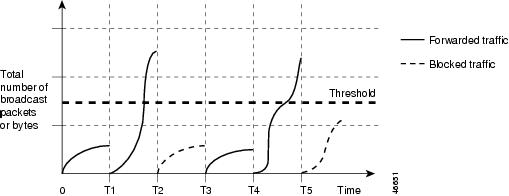
The combination of the storm-control suppression level and the 200-millisecond time interval control the way the storm control algorithm works. A higher threshold allows more packets to pass through. A threshold value of 100 percent means that no limit is placed on the traffic. A value of 0.0 means that all broadcast, multicast, or unicast traffic on that port is blocked.

Note ![]() Because packets do not arrive at uniform intervals, the 200-millisecond time interval during which traffic activity is measured can affect the behavior of storm control.
Because packets do not arrive at uniform intervals, the 200-millisecond time interval during which traffic activity is measured can affect the behavior of storm control.
The switch continues to monitor traffic on the port, and when the utilization level is below the threshold level, the type of traffic that was dropped is forwarded again.
You use the storm-control interface configuration commands to set the threshold value for each traffic type.

Note ![]() Although visible in the command-line interface (CLI) online help, the switchport broadcast, switchport multicast, and switchport unicast interface configuration commands for setting suppression levels are not available. These commands are obsolete, replaced by the storm-control interface configuration commands.
Although visible in the command-line interface (CLI) online help, the switchport broadcast, switchport multicast, and switchport unicast interface configuration commands for setting suppression levels are not available. These commands are obsolete, replaced by the storm-control interface configuration commands.
Default Storm Control Configuration
By default, unicast, broadcast, and multicast storm control is disabled on the switch interfaces; that is, the suppression level is 100 percent.
Enabling Storm Control
You enable storm control on an interface and enter the percentage of total available bandwidth that you want to be used by a particular type of traffic; entering 100 percent allows all traffic. However, because of hardware limitations and the way in which packets of different sizes are counted, threshold percentages are approximations. Depending on the sizes of the packets making up the incoming traffic, the actual enforced threshold might differ from the configured level by several percentage points.

Note ![]() Storm control is supported only on physical interfaces; it is not supported on EtherChannel port channels even though the command is available in the CLI.
Storm control is supported only on physical interfaces; it is not supported on EtherChannel port channels even though the command is available in the CLI.
Beginning in privileged EXEC mode, follow these steps to enable a particular type of storm control:
To disable storm control, use the no storm-control broadcast level, no storm-control multicast level, or no storm-control unicast level interface configuration commands.
This example shows how to set the multicast storm control level at 70.5 percent on a port and to verify the configuration:
Switch# configure terminal
Switch(config)# interface gigabitethernet0/1
Switch(config-if)# storm-control multicast level 70.5
Switch(config-if)# end
Switch# show storm-control gigabitethernet0/1 multicast
Interface Filter State Level Current
--------- ------------- ------- -------
Gi0/1 Forwarding 70.50% 0.00%
This example shows how to disable the multicast storm control on a port:
Switch# configure terminal
Switch(config)# interface gigabitethernet0/1
Switch(config-if)# no storm-control multicast level
Switch(config-if)# end
Configuring Protected Ports
Some applications require that no traffic be forwarded at Layer 2 between ports on the same switch so that one neighbor does not see the traffic generated by another neighbor. In such an environment, the use of protected ports ensures that there is no exchange of unicast, broadcast, or multicast traffic between these ports on the switch.
Protected ports have these features:
•![]() A protected port does not forward any traffic (unicast, multicast, or broadcast) to any other port that is also a protected port. Traffic cannot be forwarded between protected ports at Layer 2; all traffic passing between protected ports must be forwarded through a Layer 3 device.
A protected port does not forward any traffic (unicast, multicast, or broadcast) to any other port that is also a protected port. Traffic cannot be forwarded between protected ports at Layer 2; all traffic passing between protected ports must be forwarded through a Layer 3 device.
•![]() Forwarding behavior between a protected port and a nonprotected port proceeds as usual.
Forwarding behavior between a protected port and a nonprotected port proceeds as usual.
Default Protected Port Configuration
The default is to have no protected ports defined.
Protected Port Configuration Guidelines
You can configure protected ports on a physical interface (for example, Gigabit Ethernet port 1) or an EtherChannel group (for example, port-channel 5). When you enable protected ports for a port channel, it is enabled for all ports in the port-channel group.
Configuring a Protected Port
Beginning in privileged EXEC mode, follow these steps to define a port as a protected port:
To disable protected port, use the no switchport protected interface configuration command.
This example shows how to configure a port as a protected port:
Switch# configure terminal
Switch(config)# interface gigabitethernet0/1
Switch(config-if)# switchport protected
Switch(config-if)# end
Configuring Port Blocking
By default, the switch floods packets with unknown destination MAC addresses out of all ports. If unknown unicast and multicast traffic is forwarded to a protected port, there could be security issues. To prevent unknown unicast or multicast traffic from being forwarded from one port to another, you can block a port (protected or nonprotected) from flooding unknown unicast or multicast packets to other ports.
Default Port Blocking Configuration
The default is to not block flooding of unknown multicast and unicast traffic out of a port, but to flood these packets to all ports.
Blocking Flooded Traffic on an Interface

Note ![]() The interface can be a physical interface or an EtherChannel group. When you block multicast or unicast traffic for a port channel, it is blocked on all ports in the port channel group.
The interface can be a physical interface or an EtherChannel group. When you block multicast or unicast traffic for a port channel, it is blocked on all ports in the port channel group.
Beginning in privileged EXEC mode, follow these steps to disable the flooding of multicast and unicast packets out of an interface:
To return the interface to the default condition where no traffic is blocked and normal forwarding occurs on the port, use the no switchport block {multicast | unicast} interface configuration commands.
This example shows how to block unicast and multicast flooding on a port:
Switch# configure terminal
Switch(config)# interface gigabitethernet0/1
Switch(config-if)# switchport block multicast
Switch(config-if)# switchport block unicast
Switch(config-if)# end
Configuring Port Security
You can use the port security feature to restrict input to an interface by limiting and identifying MAC addresses of the stations allowed to access the port. When you assign secure MAC addresses to a secure port, the port does not forward packets with source addresses outside the group of defined addresses. If you limit the number of secure MAC addresses to one and assign a single secure MAC address, the workstation attached to that port is assured the full bandwidth of the port.
If a port is configured as a secure port and the maximum number of secure MAC addresses is reached, when the MAC address of a station attempting to access the port is different from any of the identified secure MAC addresses, a security violation occurs. Also, if a station with a secure MAC address configured or learned on one secure port attempts to access another secure port, a violation is flagged.
These sections include port security configuration information and procedures:
•![]() Default Port Security Configuration
Default Port Security Configuration
•![]() Enabling and Configuring Port Security
Enabling and Configuring Port Security
•![]() Enabling and Configuring Port Security Aging
Enabling and Configuring Port Security Aging
Understanding Port Security
This section contains information about these topics:
Secure MAC Addresses
You configure the maximum number of secure addresses allowed on a port by using the switchport port-security maximum value interface configuration command.

Note ![]() If you try to set the maximum value to a number less than the number of secure addresses already configured on an interface, the command is rejected.
If you try to set the maximum value to a number less than the number of secure addresses already configured on an interface, the command is rejected.
The switch supports these types of secure MAC addresses:
•![]() Static secure MAC addresses—These are manually configured by using the switchport port-security mac-address mac-address interface configuration command, stored in the address table, and added to the switch running configuration.
Static secure MAC addresses—These are manually configured by using the switchport port-security mac-address mac-address interface configuration command, stored in the address table, and added to the switch running configuration.
•![]() Dynamic secure MAC addresses—These are dynamically configured, stored only in the address table, and removed when the switch restarts.
Dynamic secure MAC addresses—These are dynamically configured, stored only in the address table, and removed when the switch restarts.
•![]() Sticky secure MAC addresses—These can be dynamically learned or manually configured, stored in the address table, and added to the running configuration. If these addresses are saved in the configuration file, when the switch restarts, the interface does not need to dynamically reconfigure them.
Sticky secure MAC addresses—These can be dynamically learned or manually configured, stored in the address table, and added to the running configuration. If these addresses are saved in the configuration file, when the switch restarts, the interface does not need to dynamically reconfigure them.
You can configure an interface to convert the dynamic MAC addresses to sticky secure MAC addresses and to add them to the running configuration by enabling sticky learning. To enable sticky learning, enter the switchport port-security mac-address sticky interface configuration command. When you enter this command, the interface converts all the dynamic secure MAC addresses, including those that were dynamically learned before sticky learning was enabled, to sticky secure MAC addresses. All sticky secure MAC addresses are added to the running configuration.
The sticky secure MAC addresses do not automatically become part of the configuration file, which is the startup configuration used each time the switch restarts. If you save the sticky secure MAC addresses in the configuration file, when the switch restarts, the interface does not need to relearn these addresses. If you do not save the sticky secure addresses, they are lost.
If sticky learning is disabled, the sticky secure MAC addresses are converted to dynamic secure addresses and are removed from the running configuration.
The maximum number of secure MAC addresses that you can configure on a switch is determined by the maximum number of available MAC addresses allowed in the system. This number is determined by the active Switch Database Management (SDM) template. See "Configuring SDM Templates." This number represents the total of available MAC addresses, including those used for other Layer 2 functions and any other secure MAC addresses configured on interfaces.
Security Violations
It is a security violation when one of these situations occurs:
•![]() The maximum number of secure MAC addresses have been added to the address table, and a station whose MAC address is not in the address table attempts to access the interface.
The maximum number of secure MAC addresses have been added to the address table, and a station whose MAC address is not in the address table attempts to access the interface.
•![]() An address learned or configured on one secure interface is seen on another secure interface in the same VLAN.
An address learned or configured on one secure interface is seen on another secure interface in the same VLAN.
You can configure the interface for one of three violation modes, based on the action to be taken if a violation occurs:
•![]() protect—when the number of secure MAC addresses reaches the maximum limit allowed on the port, packets with unknown source addresses are dropped until you remove a sufficient number of secure MAC addresses to drop below the maximum value or increase the number of maximum allowable addresses. You are not notified that a security violation has occurred.
protect—when the number of secure MAC addresses reaches the maximum limit allowed on the port, packets with unknown source addresses are dropped until you remove a sufficient number of secure MAC addresses to drop below the maximum value or increase the number of maximum allowable addresses. You are not notified that a security violation has occurred.

Note ![]() We do not recommend configuring the protect violation mode on a trunk port. The protect mode disables learning when any VLAN reaches its maximum limit, even if the port has not reached its maximum limit.
We do not recommend configuring the protect violation mode on a trunk port. The protect mode disables learning when any VLAN reaches its maximum limit, even if the port has not reached its maximum limit.
•![]() restrict—when the number of secure MAC addresses reaches the maximum limit allowed on the port, packets with unknown source addresses are dropped until you remove a sufficient number of secure MAC addresses to drop below the maximum value or increase the number of maximum allowable addresses. In this mode, you are notified that a security violation has occurred. An SNMP trap is sent, a syslog message is logged, and the violation counter increments.
restrict—when the number of secure MAC addresses reaches the maximum limit allowed on the port, packets with unknown source addresses are dropped until you remove a sufficient number of secure MAC addresses to drop below the maximum value or increase the number of maximum allowable addresses. In this mode, you are notified that a security violation has occurred. An SNMP trap is sent, a syslog message is logged, and the violation counter increments.
•![]() shutdown—a port security violation causes the interface to become error-disabled and to shut down immediately, and the port LED turns off. An SNMP trap is sent, a syslog message is logged, and the violation counter increments. When a secure port is in the error-disabled state, you can bring it out of this state by entering the errdisable recovery cause psecure-violation global configuration command, or you can manually re-enable it by entering the shutdown and no shut down interface configuration commands. This is the default mode.
shutdown—a port security violation causes the interface to become error-disabled and to shut down immediately, and the port LED turns off. An SNMP trap is sent, a syslog message is logged, and the violation counter increments. When a secure port is in the error-disabled state, you can bring it out of this state by entering the errdisable recovery cause psecure-violation global configuration command, or you can manually re-enable it by entering the shutdown and no shut down interface configuration commands. This is the default mode.
Table 20-1 shows the violation mode and the actions taken when you configure an interface for port security.
|
|
|
|
|
|
|
|
|---|---|---|---|---|---|---|
protect |
No |
No |
No |
No |
No |
No |
restrict |
No |
Yes |
Yes |
No |
Yes |
No |
shutdown |
No |
Yes |
Yes |
No |
Yes |
Yes |
1 Packets with unknown source addresses are dropped until you remove a sufficient number of secure MAC addresses. 2 The switch returns an error message if you manually configure an address that would cause a security violation. |
Default Port Security Configuration
Table 20-2 shows the default port security configuration for an interface.
Configuration Guidelines
Follow these guidelines when configuring port security:
•![]() Port security can only be configured on static access ports or trunk ports. A secure port cannot be a dynamic access port.
Port security can only be configured on static access ports or trunk ports. A secure port cannot be a dynamic access port.
•![]() A secure port cannot be a destination port for Switched Port Analyzer (SPAN).
A secure port cannot be a destination port for Switched Port Analyzer (SPAN).
•![]() A secure port cannot belong to a Fast EtherChannel a Gigabit EtherChannel port group.
A secure port cannot belong to a Fast EtherChannel a Gigabit EtherChannel port group.
•![]() You cannot configure static secure or sticky secure MAC addresses in the voice VLAN.
You cannot configure static secure or sticky secure MAC addresses in the voice VLAN.

Note ![]() Voice VLAN is only supported on access ports and not on trunk ports, even though the configuration is allowed.
Voice VLAN is only supported on access ports and not on trunk ports, even though the configuration is allowed.
•![]() When you enable port security on an interface that is also configured with a voice VLAN, you must set the maximum allowed secure addresses on the port to two plus the maximum number of secure addresses allowed on the access VLAN. When the port is connected to a Cisco IP phone, the IP phone requires up to two MAC addresses. The IP phone address is learned on the voice VLAN and might also be learned on the access VLAN. Connecting a PC to the IP phone requires additional MAC addresses.
When you enable port security on an interface that is also configured with a voice VLAN, you must set the maximum allowed secure addresses on the port to two plus the maximum number of secure addresses allowed on the access VLAN. When the port is connected to a Cisco IP phone, the IP phone requires up to two MAC addresses. The IP phone address is learned on the voice VLAN and might also be learned on the access VLAN. Connecting a PC to the IP phone requires additional MAC addresses.
•![]() If any type of port security is enabled on the access VLAN, dynamic port security is automatically enabled on the voice VLAN. You cannot configure port security on a per-VLAN basis.
If any type of port security is enabled on the access VLAN, dynamic port security is automatically enabled on the voice VLAN. You cannot configure port security on a per-VLAN basis.
•![]() When a voice VLAN is configured on a secure port that is also configured as a sticky secure port, all addresses on the voice VLAN are learned as dynamic secure addresses, and all addresses seen on the access VLAN to which the port belongs are learned as sticky secure addresses.
When a voice VLAN is configured on a secure port that is also configured as a sticky secure port, all addresses on the voice VLAN are learned as dynamic secure addresses, and all addresses seen on the access VLAN to which the port belongs are learned as sticky secure addresses.
•![]() When you enter a maximum secure address value for an interface, and the new value is greater than the previous value, the new value overwrites the previously configured value. If the new value is less than the previous value and the number of configured secure addresses on the interface exceeds the new value, the command is rejected.
When you enter a maximum secure address value for an interface, and the new value is greater than the previous value, the new value overwrites the previously configured value. If the new value is less than the previous value and the number of configured secure addresses on the interface exceeds the new value, the command is rejected.
•![]() The switch does not support port security aging of sticky secure MAC addresses.
The switch does not support port security aging of sticky secure MAC addresses.
Enabling and Configuring Port Security
Beginning in privileged EXEC mode, follow these steps to restrict input to an interface by limiting and identifying MAC addresses of the stations allowed to access the port:
|
|
|
|
|---|---|---|
Step 1 |
configure terminal |
Enter global configuration mode. |
Step 2 |
interface interface-id |
Enter interface configuration mode, and enter the physical interface to configure. |
Step 3 |
switchport mode {access | trunk} |
Set the interface switchport mode as access or trunk; an interface in the default mode (dynamic auto) cannot be configured as a secure port. |
Step 4 |
switchport port-security |
Enable port security on the interface. |
Step 5 |
switchport port-security maximum value [vlan [vlan-list]] |
(Optional) Set the maximum number of secure MAC addresses for the interface. The maximum number of secure MAC addresses that you can configure on a switch is determined by the maximum number of available MAC addresses allowed in the system. This number is determined by the active Switch Database Management (SDM) template. See "Configuring SDM Templates."This number represents the total of available MAC addresses, including those used for other Layer 2 functions and any other secure MAC addresses configured on interfaces. (Optional) For trunk ports, you can set the maximum number of secure MAC addresses on a VLAN. If the vlan keyword is not entered, the default value is used. • • |
Step 6 |
switchport port-security violation {protect | restrict | shutdown} |
(Optional) Set the violation mode, the action to be taken when a security violation is detected, as one of these: • Note • • Note |
Step 7 |
switchport port-security mac-address mac-address |
(Optional) Enter a secure MAC address for the interface. You can use this command to enter the maximum number of secure MAC addresses. If you configure fewer secure MAC addresses than the maximum, the remaining MAC addresses are dynamically learned. (Optional) On a trunk port, you can specify the VLAN ID and the MAC address. If no VLAN ID is specified, the native VLAN is used. Note |
Step 8 |
switchport port-security mac-address sticky |
(Optional) Enable stick learning on the interface. |
Step 9 |
switchport port-security mac-address sticky mac-address |
(Optional) Enter a sticky secure MAC address, repeating the command as many times as necessary. If you configure fewer secure MAC addresses than the maximum, the remaining MAC addresses are dynamically learned, are converted to sticky secure MAC addresses, and are added to the running configuration. Note |
Step 10 |
end |
Return to privileged EXEC mode. |
Step 11 |
show port-security |
Verify your entries. |
Step 12 |
copy running-config startup-config |
(Optional) Save your entries in the configuration file. |
To return the interface to the default condition as not a secure port, use the no switchport port-security interface configuration command. If you enter this command when sticky learning is enabled, the sticky secure addresses remain part of the running configuration but are removed from the address table. All addresses are now dynamically learned.
To return the interface to the default number of secure MAC addresses, use the no switchport port-security maximum value interface configuration command. To return the violation mode to the default condition (shutdown mode), use the no switchport port-security violation {protocol | restrict} interface configuration command.
To disable sticky learning on an interface, use the no switchport port-security mac-address sticky interface configuration command. The interface converts the sticky secure MAC addresses to dynamic secure addresses. However, if you have previously saved the configuration with the sticky MAC addresses, you should save the configuration again after entering the no switchport port-security mac-address sticky command, or the sticky addresses will be restored if the switch reboots.
To delete a specific secure MAC address from the address table, use the no switchport port-security mac-address mac-address interface configuration command.
To delete all dynamic secure addresses on an interface from the address table, enter the no switchport port-security interface configuration command followed by the switchport port-security command (to re-enable port security on the interface). If you use the no switchport port-security mac-address sticky interface configuration command to convert sticky secure MAC addresses to dynamic secure MAC addresses before entering the no switchport port-security command, all secure addresses on the interface except those that were manually configured are deleted.
You must specifically delete configured secure MAC addresses from the address table by using the no switchport port-security mac-address mac-address interface configuration command.
This example shows how to enable port security on a port and to set the maximum number of secure addresses to 50. The violation mode is the default, no static secure MAC addresses are configured, and sticky learning is enabled.
Switch(config)# interface gigabitethernet0/1
Switch(config-if)# switchport mode access
Switch(config-if)# switchport port-security
Switch(config-if)# switchport port-security maximum 50
Switch(config-if)# switchport port-security mac-address sticky
This example shows how to configure a static secure MAC address on VLAN 3 on a port:
Switch(config)# interface gigabitethernet0/2
Switch(config-if)# switchport mode trunk
Switch(config-if)# switchport port-security
Switch(config-if)# switchport port-security mac-address 0000.02000.0004 vlan 3
Enabling and Configuring Port Security Aging
You can use port security aging to set the aging time for all secure addresses on a port. Two types of aging are supported per port:
•![]() Absolute—The secure addresses on the port are deleted after the specified aging time.
Absolute—The secure addresses on the port are deleted after the specified aging time.
•![]() Inactivity—The secure addresses on the port are deleted only if the secure addresses are inactive for the specified aging time.
Inactivity—The secure addresses on the port are deleted only if the secure addresses are inactive for the specified aging time.
Use this feature to remove and add devices on a secure port without manually deleting the existing secure MAC addresses and to still limit the number of secure addresses on a port. You can enable or disable the aging of secure addresses on a per-port basis.
Beginning in privileged EXEC mode, follow these steps to configure port security aging:
To disable port security aging for all secure addresses on a port, use the no switchport port-security aging time interface configuration command. To disable aging for only statically configured secure addresses, use the no switchport port-security aging static interface configuration command.
This example shows how to set the aging time as 2 hours for the secure addresses on a port:
Switch(config)# interface gigabitethernet0/1
Switch(config-if)# switchport port-security aging time 120
This example shows how to set the aging time as 2 minutes for the inactivity aging type with aging enabled for the configured secure addresses on the interface:
Switch(config-if)# switchport port-security aging time 2
Switch(config-if)# switchport port-security aging type inactivity
Switch(config-if)# switchport port-security aging static
You can verify the previous commands by entering the show port-security interface interface-id privileged EXEC command.
Displaying Port-Based Traffic Control Settings
The show interfaces interface-id switchport privileged EXEC command displays (among other characteristics) the interface traffic suppression and control configuration. The show interfaces counters privileged EXEC commands display the count of discarded packets. The show storm-control and show port-security privileged EXEC commands display those features.
To display traffic control information, use one or more of the privileged EXEC commands in Table 20-3.
 Feedback
Feedback