Information About Installing Cisco PNSC and Cisco VSG
You must install Cisco Prime Network Services Controller (PNSC) and Cisco VSG in a particular sequence on the Cisco Nexus 1000V switch to have a functioning virtual system.
Information About Cisco VSG
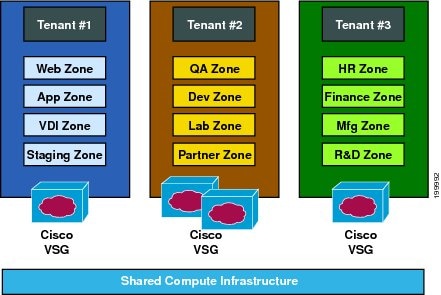
Cisco VSG is a virtual firewall appliance that provides trusted access to virtual data center and cloud environments with dynamic policy-driven operation, mobility-transparent enforcement, and scale-out deployment for dense multi-tenancy. By associating one or more Virtual Machines (VMs) into distinct trust zones, Cisco VSG ensures that access to trust zones is controlled and monitored through established security policies. The following figure shows the trusted zone-based access control that is used in per-tenant enforcement with Cisco VSG.
Cisco Prime NSC and VSG Architecture
Cisco vPath supports the following features:
-
Tenant-aware flow classification and subsequent redirection to a designated Cisco VSG tenant
-
Per-tenant policy enforcement of flows offloaded by the Cisco VSG to Cisco vPath
Cisco VSG and the VEM provide the following benefits:
-
Each Cisco VSG can provide protection across multiple physical servers, which eliminates the need for you to deploy a virtual appliance per physical server.
- By offloading the fast-path to one or more Cisco vPath Virtual Ethernet Modules (VEMs), Cisco VSG enhances security performance through distributed Cisco vPath-based enforcement.
-
You can use Cisco VSG without creating multiple switches or temporarily migrating VMs to different switches or servers. Zone scaling, which is based on security profiles, simplifies physical server upgrades without compromising security or incurring application outages.
-
For each tenant, you can deploy Cisco VSG in an active-standby mode to ensure that Cisco vPath redirects packets to the standby Cisco VSG when the primary Cisco VSG is unavailable.
-
You can place Cisco VSG on a dedicated server so that you can allocate the maximum compute capacity to application workloads. This feature enables capacity planning to occur independently and allows for operational segregation across security, network, and server groups.
Trusted Multitenant Access
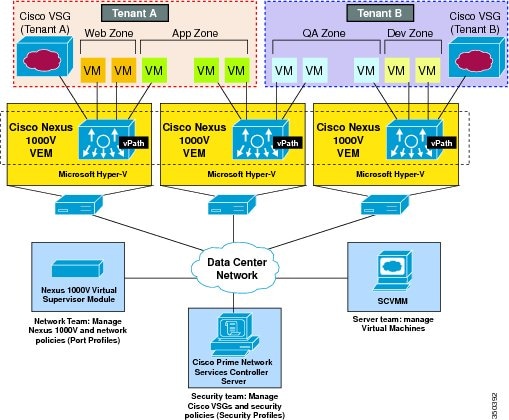
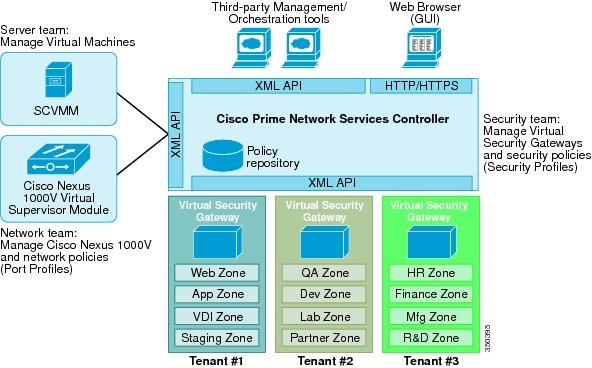
You can transparently insert a Cisco VSG into the Microsoft Hyper-V environment where Cisco Nexus 1000V is deployed. One or more instances of Cisco VSG is deployed on a per-tenant basis, which allows a highly scale-out deployment across many tenants. Tenants are isolated from each other, so no traffic can cross tenant boundaries. You can deploy Cisco VSG at the tenant level in Hyper-V and manage each tenant instance using Microsoft System Center Virtual Machine Manager (SCVMM).
As you instantiate VMs for a given tenant, their association to security profiles (or zone membership) occurs immediately through binding with the Cisco Nexus 1000V port profile. Each VM is placed upon instantiation into a logical trust zone. Security profiles contain context-aware rule sets that specify access policies for traffic that enters and exits each zone. You can apply controls to zone-to-zone traffic and to external-to-zone (and zone-to-external) traffic. Zone-based enforcement occurs within a VLAN because a VLAN often identifies a tenant boundary. The Cisco VSG evaluates access control rules and then offloads enforcement to the Cisco Nexus 1000V VEM vPath module. Upon enforcement, Cisco VSG can permit or deny access and can generate optional access logs. Cisco VSG also provides policy-based traffic monitoring capability with access logs.
Dynamic Virtualization-Aware Operation
A virtualization environment is dynamic, where frequent additions, deletions, and changes occur across tenants and across VMs. The following figure shows how the structured environment can change over time due to dynamic VMs.
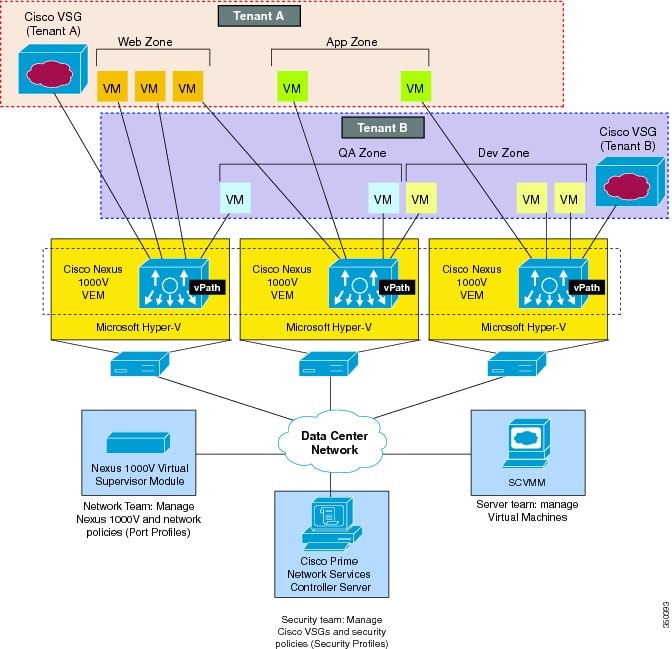
Cisco VSG operating with Cisco Nexus 1000V (and Cisco vPath) supports a dynamic VM environment. When you create a tenant with Cisco VSG (standalone or active-standby pair) on Cisco Prime NSC, associated security profiles are defined that include trust zone definitions and access control rules. Each security profile is bound to a Cisco Nexus 1000V port profile (authored on the Cisco Nexus 1000V Virtual Supervisor Module (VSM) and published to Microsoft SCVMM.
When a new VM is instantiated, the server administrator assigns appropriate port profiles to the virtual Ethernet port of the VM. Because the port profile uniquely refers to a security profile and VM zone membership, Cisco VSG immediately applies the security controls. You can repurpose a VM by assigning it to a different port profile or security profile.
As VM migration events are triggered, VMs move across physical servers. Because Cisco Nexus 1000V ensures that port profile policies follow the VMs, associated security profiles also follow these moving VMs, and security enforcement and monitoring remain transparent to the migration events.
Setting Up Cisco VSG and VLAN
You can set up Cisco VSG in an overlay fashion so that VMs can reach Cisco VSG irrespective of its location. The Cisco vPath component in Cisco Nexus 1000V VEM intercepts the packets from the VM and sends them to Cisco VSG for further processing.

-
The service VLAN provides communications between Cisco Nexus 1000V VEM and Cisco VSG through a physical router. Cisco VSG data interface and VEM interface are configured on different subnets. All the Cisco VSG data interfaces are part of the service VLAN and the VEM interacts with Cisco VSG using the router.
-
The management VLAN connects the management platforms such as ????Microsoft SCVMM????, Cisco PNSC, Cisco Nexus 1000V VSM, and managed Cisco VSGs. The Cisco VSG management vNIC is part of the management VLAN.
-
The HA VLAN provides the heartbeat mechanism and identifies the active and standby relationship between the Cisco VSGs. The Cisco VSG vNICs are part of the HA VLAN.
You can allocate one or more VM data VLANs for VM-to-VM communications. In a typical multi-tenant environment, the management VLAN is shared among all the tenants and the service VLAN, HA VLAN, and the VM data. VLANs are allocated on a per-tenant basis. However, when VLAN resources become scarce, you might decide to use a single VLAN for service and HA functions.

 Feedback
Feedback