About Firepower Threat Defense Dynamic Access Policy
VPN gateways operate in dynamic environments. Multiple variables can affect each VPN connection, for example, intranet configurations that frequently change, the various roles each user may inhabit within an organization, and logins from remote access sites with different configurations and levels of security. The task of authorizing users is much more complicated in a VPN environment than it is in a network with a static configuration.
You create a dynamic access policy by setting a collection of access control attributes that you associate with a specific user tunnel or session. These attributes address issues of multiple group membership and endpoint security. That is, the FTD grants access to a particular user for a particular session based on the policies you define. It generates a DAP during user authentication by selecting or aggregating attributes from one or more DAP records. It selects these DAP records based on the endpoint security information of the remote device and AAA authorization information for the authenticated user. It then applies the DAP record to the user tunnel or session.
Policy Enforcement of Permissions and Attributes in FTD
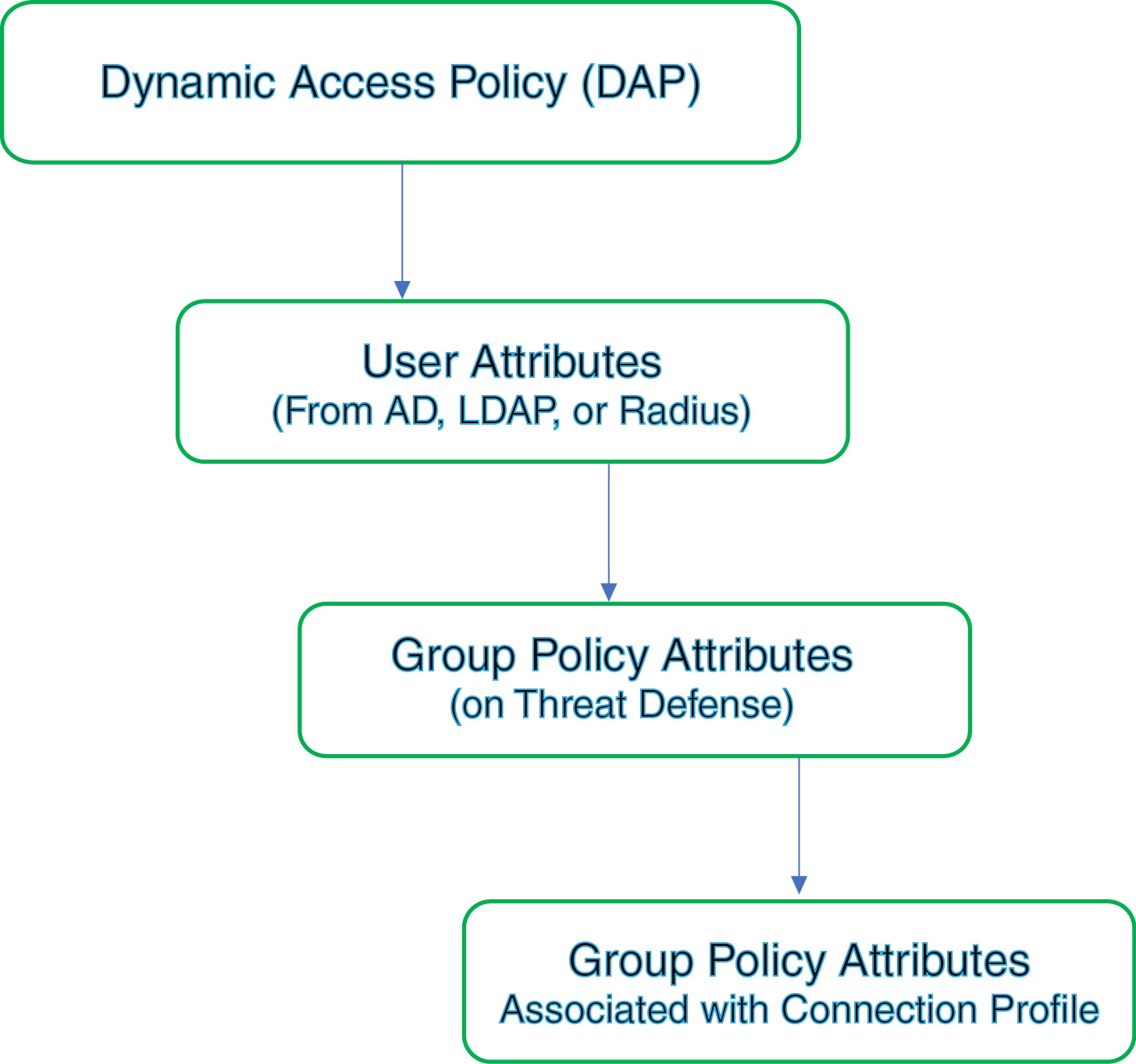
The Firepower Threat Defense device supports applying user authorization attributes (also called user entitlements or permissions) to VPN connections. The attributes are applied from a DAP on the 457903Firepower Threat Defense, external authentication server and/or authorization AAA server (RADIUS) or from a group policy on the Firepower Threat Defense device.
If the Firepower Threat Defense device receives attributes from all sources, Firepower Threat Defense evaluates, merges, and applies to the user policy. If conflicts occur among attributes coming from the DAP, the AAA server, or the group policy, the attributes obtained from the DAP always take precedence.
-
DAP attributes on the FTD—The DAP attributes take precedence over all others.
-
User attributes on the external AAA server—The server returns these attributes after successful user authentication and/or authorization.
-
Group policy configured on the FTD —If a RADIUS server returns the value of the RADIUS Class attribute IETF-Class-25 (OU= group-policy) for the user, the Firepower Threat Defense device places the user in the group policy of the same name and enforces any attributes in the group policy that are not returned by the server.
-
Group policy assigned by the Connection Profile (also known as Tunnel Group)—The Connection Profile has the preliminary settings for the connection, and includes a default group policy applied to the user before authentication.
 Note |
The Firepower Threat Defense device does not support inheriting system default attributes from the default group policy, DfltGrpPolicy. The group policy attributes assigned from the connection profile are used for the user session, if they are not overridden by user attributes or the group policy from the AAA server. |
 Feedback
Feedback