Release Notes for Cisco Secure Access Control System 5.8.1
Available Languages
Table of Contents
Release Notes for Cisco Secure Access Control System 5.8.1
Supported Virtual Environments
Supported Device and User Repositories
New Features in ACS 5.8.1 Release
Cisco SNS 3515 and 3595 appliances support
Upgrading Cisco Secure ACS Software
Monitoring and Reports Data Export Compatibility
Installation and Upgrade Notes
Installing, Setting Up, and Configuring Cisco SNS 3500 Series Appliances
Installing, Setting Up, and Configuring Cisco SNS 3400 Series Appliances
Installing, Setting Up, and Configuring CSACS-1121
Limitations in ACS Deployments
Search Bugs Using the Bug Search Tool
Supplemental License Agreement
Obtaining Documentation and Submitting a Service Request
Release Notes for Cisco Secure Access Control System 5.8.1
This release notes pertain to the Cisco Secure Access Control System (ACS), Release 5.8.1, hereafter referred to as ACS 5.8.1. This release notes describes the features, limitations and restrictions (caveats), and related documentation for Cisco Secure ACS. The release notes supplement the Cisco Secure ACS documentation that is included with the product hardware and software release.
■![]() New Features in ACS 5.8.1 Release
New Features in ACS 5.8.1 Release
■![]() Upgrading Cisco Secure ACS Software
Upgrading Cisco Secure ACS Software
■![]() Monitoring and Reports Data Export Compatibility
Monitoring and Reports Data Export Compatibility
■![]() Installation and Upgrade Notes
Installation and Upgrade Notes
■![]() Limitations in ACS Deployments
Limitations in ACS Deployments
■![]() Supplemental License Agreement
Supplemental License Agreement
■![]() Obtaining Documentation and Submitting a Service Request
Obtaining Documentation and Submitting a Service Request
Introduction
This release of ACS introduces new hardware platforms for the ACS product. The ACS 5.8.1 software can now run on a dedicated Cisco SNS-3595 or a Cisco SNS-3515 appliance. This is in addition to the existing platforms that continue to be supported: Cisco SNS-3495 or Cisco SNS-3415 appliance, on a Cisco 1121 Secure Access Control System (CSACS-1121) or a VMware server. For more information on upgrade procedures, see Upgrading Cisco Secure ACS Software.
This release of ACS does not provide any new or enhanced functionality and is functionally equivalent to ACS 5.8. Throughout this document, Cisco SNS-3595, Cisco SNS-3515, Cisco SNS-3495, Cisco SNS-3415 and CSACS-1121 refer to the appliance hardware, and ACS server refers to ACS software.
System Requirements
■![]() Supported Virtual Environments
Supported Virtual Environments
■![]() Supported Device and User Repositories
Supported Device and User Repositories
Note: For more details on Cisco Secure ACS hardware platform and installation, see the Installation and Upgrade Guide for Cisco Secure Access Control System 5.8.1.
Supported Hardware
Cisco Secure ACS 5.8.1 ships on the following platforms:.
| ■ |
|
| ■ |
|
| ■ |
|
| ■ |
|
Cisco 1121 Secure Access Control System Hardware (CSACS-1121) |
■ |
■ ■ ■ ■ |
Note: Cisco recommends you to use more than a 4GB RAM platform for a deployment that has more than 100,000 devices. ACS runtime crashes when you use a machine with 4GB RAM or less in a deployment that has more than 100,000 devices.
Supported Virtual Environments
ACS 5.8.1 supports the following VMware versions:
For information on VMware machine requirements and installation procedures, see the “ Installing ACS in a VMware Virtual Machine” chapter in the Installation and Upgrade Guide for Cisco Secure Access Control System 5.8.1.
Supported Browsers
You can access the ACS 5.8.1 administrative user interface using the following browsers:
ACS 5.8.1 supports the following browser platforms:
–![]() Mozilla Firefox version 45.0.2 ESR
Mozilla Firefox version 45.0.2 ESR
■![]() Windows 7 32-bit and Windows 7 64-bit
Windows 7 32-bit and Windows 7 64-bit
–![]() Internet Explorer version 11.x
Internet Explorer version 11.x
–![]() Mozilla Firefox version 38.4.0 ESR
Mozilla Firefox version 38.4.0 ESR
–![]() Mozilla Firefox version 38.5.2 ESR
Mozilla Firefox version 38.5.2 ESR
–![]() Mozilla Firefox version 45.0.2 ESR
Mozilla Firefox version 45.0.2 ESR
–![]() Internet Explorer version 10.x (Windows 8)
Internet Explorer version 10.x (Windows 8)
–![]() Internet Explorer version 11.x (Windows 8.1)
Internet Explorer version 11.x (Windows 8.1)
–![]() Mozilla Firefox version 38.5.2 ESR
Mozilla Firefox version 38.5.2 ESR
–![]() Mozilla Firefox version 45.0.2 ESR
Mozilla Firefox version 45.0.2 ESR
Note: Mozilla Firefox version 46.x or later is supported only after installing ACS 5.8 patch 3 or later on top of ACS 5.8.1 release.
Note: Adobe Flash Player 11.2.0.0 or above must be installed on the system running the client browser.
Note: When you import or export a .csv![]() file from ACS 5.x, you must turn off the pop-up blocker.
file from ACS 5.x, you must turn off the pop-up blocker.
Supported Device and User Repositories
For information on supported devices, 802.1X clients, and user repositories, see Supported and Interoperable Devices and Software for Cisco Secure Access Control System 5.8.1.
New Features in ACS 5.8.1 Release
There is no new or enhanced functionality in ACS 5.8.1 and it is functionally equivalent to ACS 5.8. However, the following sections describe the new hardware platforms supported in ACS 5.8.1 release:
■![]() Cisco SNS 3515 and 3595 appliances support
Cisco SNS 3515 and 3595 appliances support
Cisco SNS 3515 and 3595 appliances support
ACS 5.8.1 supports two new Hardware Appliances called Cisco SNS-3515 and Cisco SNS-3595. ACS 5.8.1 is shipped with SNS-3515 or SNS-3595 depending on the requirements from the customer. For more information on SNS-3515 and SNS-3595 appliances, see Installation and Upgrade Guide for Cisco Secure Access Control System 5.8.1.
Upgrading Cisco Secure ACS Software
Cisco Secure Access Control System (ACS) supports upgrades from different versions of ACS 5.x to ACS 5.8.1. The supported upgrade paths include:
■![]() Cisco Secure ACS, Release 5.5, recommended with latest patch applied
Cisco Secure ACS, Release 5.5, recommended with latest patch applied
■![]() Cisco Secure ACS, Release 5.6, recommended with latest patch applied
Cisco Secure ACS, Release 5.6, recommended with latest patch applied
■![]() Cisco Secure ACS, Release 5.7, recommended with latest patch applied
Cisco Secure ACS, Release 5.7, recommended with latest patch applied
■![]() Cisco Secure ACS, Release 5.8, recommended with latest patch applied
Cisco Secure ACS, Release 5.8, recommended with latest patch applied
Follow the upgrade instructions in the Installation and Upgrade Guide for Installation and Upgrade Guide for Cisco Secure Access Control System 5.8.1. to upgrade to Cisco Secure ACS, Release 5.8.1.
Monitoring and Reports Data Export Compatibility
Exporting monitoring and troubleshooting records to a remote database does not work if the remote database is an Oracle database and it is configured in a cluster setup.
Installation and Upgrade Notes
This section provides information on the installation tasks and configuration process for ACS 5.8.1.
■![]() Installing, Setting Up, and Configuring Cisco SNS 3500 Series Appliances
Installing, Setting Up, and Configuring Cisco SNS 3500 Series Appliances
■![]() Installing, Setting Up, and Configuring Cisco SNS 3400 Series Appliances
Installing, Setting Up, and Configuring Cisco SNS 3400 Series Appliances
■![]() Installing, Setting Up, and Configuring CSACS-1121
Installing, Setting Up, and Configuring CSACS-1121
Installing, Setting Up, and Configuring Cisco SNS 3500 Series Appliances
ACS 5.8.1 is shipped with Cisco SNS-3515 or SNS-3595 appliances depending on the customer requirements. The SNS-3595 and SNS-3515 appliances do not have a DVD drive. You must use the CIMC on the appliance or a bootable USB to install, set up, and configure ACS 5.8 on this appliance. For more details, see the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8 .
This section describes how to install, set up and configure the Cisco SNS-3595 and Cisco SNS-3515 appliance. The Cisco SNS-3595 and Cisco SNS-3515 appliance are preinstalled with the software.
To set up and configure the Cisco SNS-3595 and Cisco SNS-3515:
1.![]() Open the box containing the Cisco SNS-3595 and Cisco SNS-3515 appliances and verify that it includes:
Open the box containing the Cisco SNS-3595 and Cisco SNS-3515 appliances and verify that it includes:
■![]() The Cisco SNS-3595 and Cisco SNS-3515 appliance
The Cisco SNS-3595 and Cisco SNS-3515 appliance
■![]() Regulatory Compliance and Safety Information for Cisco Secure Access Control System 5.8
Regulatory Compliance and Safety Information for Cisco Secure Access Control System 5.8
2.![]() Go through the specifications of the Cisco SNS-3595 or Cisco SNS-3515 appliance.
Go through the specifications of the Cisco SNS-3595 or Cisco SNS-3515 appliance.
For more details, see the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8 .
3.![]() Read the general precautions and safety instructions that you must follow before installing the Cisco SNS-3515 or Cisco SNS-3595 appliance.
Read the general precautions and safety instructions that you must follow before installing the Cisco SNS-3515 or Cisco SNS-3595 appliance.
For more details, see the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8 and pay special attention to all safety warnings.
4.![]() Install the appliance in the 4-post rack, and complete the rest of the hardware installation.
Install the appliance in the 4-post rack, and complete the rest of the hardware installation.
For more details on installing the Cisco SNS-3595 or Cisco SNS-3515 appliance, see the Installation and Upgrade guide for the Cisco Secure Access Control System 5.8.
5.![]() Connect the Cisco SNS-3595 or Cisco SNS-3515 appliance to the network and connect either a USB keyboard and Video Graphics Array (VGA) monitor or a serial console to the serial port.
Connect the Cisco SNS-3595 or Cisco SNS-3515 appliance to the network and connect either a USB keyboard and Video Graphics Array (VGA) monitor or a serial console to the serial port.
See the Installation and Upgrade guide for Cisco Secure Access Control System 5.8 for illustrations of the front and back panel of the Cisco SNS-3595 and Cisco SNS-3515 appliance and the various cable connectors.
Note: For the initial setup, you must have either a USB keyboard and VGA monitor or a serial console running terminal-emulation software.
For more details, see the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8 .
For information on installing ACS 5.8 on VMware, see the” Installing ACS in a VMware Virtual Machine” chapter in the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8.
6.![]() After completing the hardware installation, power up the appliance.
After completing the hardware installation, power up the appliance.
The first time you power up the appliance, you must run the setup program to configure the appliance. For more information, see the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8.
Installing, Setting Up, and Configuring Cisco SNS 3400 Series Appliances
You can install ACS software on Cisco SNS-3495 and SNS-3415 appliances. These appliances do not have a DVD drive. You must use the CIMC on the appliance or a bootable USB to install, set up, and configure ACS software on this appliance. For more details, see the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8.1 .
This section describes how to install, set up and configure the Cisco SNS-3495 and Cisco SNS-3415 appliance. The Cisco SNS-3495 and Cisco SNS-3415 appliance are preinstalled with the software.
To set up and configure the Cisco SNS-3495 and Cisco SNS-3415:
1.![]() Open the box containing the Cisco SNS-3495 and Cisco SNS-3415 appliances and verify that it includes:
Open the box containing the Cisco SNS-3495 and Cisco SNS-3415 appliances and verify that it includes:
■![]() The Cisco SNS-3495 and Cisco SNS-3415 appliance
The Cisco SNS-3495 and Cisco SNS-3415 appliance
■![]() Regulatory Compliance and Safety Information for Cisco Secure Access Control System 5.8.1
Regulatory Compliance and Safety Information for Cisco Secure Access Control System 5.8.1
2.![]() Go through the specifications of the Cisco SNS-3495 or Cisco SNS-3415 appliance.
Go through the specifications of the Cisco SNS-3495 or Cisco SNS-3415 appliance.
For more details, see the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8.1 .
3.![]() Read the general precautions and safety instructions that you must follow before installing the Cisco SNS-3415 or Cisco SNS-3495 appliance.
Read the general precautions and safety instructions that you must follow before installing the Cisco SNS-3415 or Cisco SNS-3495 appliance.
For more details, see the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8.1 and pay special attention to all safety warnings.
4.![]() Install the appliance in the 4-post rack, and complete the rest of the hardware installation.
Install the appliance in the 4-post rack, and complete the rest of the hardware installation.
For more details on installing the Cisco SNS-3495 or Cisco SNS-3415 appliance, see the Installation and Upgrade guide for the Cisco Secure Access Control System 5.8.1.
5.![]() Connect the Cisco SNS-3495 or Cisco SNS-3415 appliance to the network and connect either a USB keyboard and Video Graphics Array (VGA) monitor or a serial console to the serial port.
Connect the Cisco SNS-3495 or Cisco SNS-3415 appliance to the network and connect either a USB keyboard and Video Graphics Array (VGA) monitor or a serial console to the serial port.
See the Installation and Upgrade guide for Cisco Secure Access Control System 5.8.1 for illustrations of the front and back panel of the Cisco SNS-3495 and Cisco SNS-3415 appliance and the various cable connectors.
Note: For the initial setup, you must have either a USB keyboard and VGA monitor or a serial console running terminal-emulation software.
For more details, see the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8.1 .
For information on installing ACS 5.8.1 on VMware, see the” Installing ACS in a VMware Virtual Machine” chapter in the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8.1.
6.![]() After completing the hardware installation, power up the appliance.
After completing the hardware installation, power up the appliance.
The first time you power up the appliance, you must run the setup program to configure the appliance. For more information, see the Installation and Upgrade Guide for the Cisco Secure Access Control System 5.8.1.
Installing, Setting Up, and Configuring CSACS-1121
This section describes how to install, set up, and configure the CSACS-1121 series appliance. The CSACS-1121 series appliance is preinstalled with the software.
To set up and configure the CSACS-1121:
1.![]() Open the box containing the CSACS-1121 Series appliance and verify that it includes:
Open the box containing the CSACS-1121 Series appliance and verify that it includes:
■![]() The CSACS-1121 Series appliance
The CSACS-1121 Series appliance
■![]() Regulatory Compliance and Safety Information for Cisco Secure Access Control System 5.8.1
Regulatory Compliance and Safety Information for Cisco Secure Access Control System 5.8.1
2.![]() Go through the specifications of the CSACS-1121 Series appliance.
Go through the specifications of the CSACS-1121 Series appliance.
For more details, see the Installation and Upgrade Guide for Cisco Secure Access Control System 5.8.1 .
3.![]() Read the general precautions and safety instructions that you must follow before installing the CSACS-1121 Series appliance.
Read the general precautions and safety instructions that you must follow before installing the CSACS-1121 Series appliance.
For more details, see the Installation and Upgrade Guide for Cisco Secure Access Control System 5.8.1 and pay special attention to all safety warnings.
4.![]() Install the appliance in the 4-post rack, and complete the rest of the hardware installation.
Install the appliance in the 4-post rack, and complete the rest of the hardware installation.
For more details on installing the CSACS-1121 Series appliance, see the Installation and Upgrade Guide for Cisco Secure Access Control System 5.8.1.
5.![]() Connect the CSACS-1121 Series appliance to the network, and connect either a USB keyboard and Video Graphics Array (VGA) monitor or a serial console to the serial port.
Connect the CSACS-1121 Series appliance to the network, and connect either a USB keyboard and Video Graphics Array (VGA) monitor or a serial console to the serial port.
Figure 1 shows the back panel of the CSACS-1121 Series appliance and the various cable connectors.
Note: For the initial setup, you must have either a USB keyboard and VGA monitor or a serial console running terminal emulation software.
For more details, see the Installation and Upgrade Guide for Cisco Secure Access Control System 5.8.1.
For information on installing ACS 5.8.1 on VMware, see the “ Installing ACS in a VMware Virtual Machine” chapter in the Installation and Upgrade Guide for Cisco Secure Access Control System 5.8.1.
Figure 1 CSACS 1121 Series Appliance Rear View
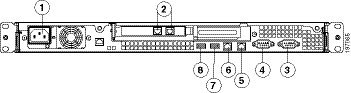
The following table describes the callouts in Figure 1.
6.![]() After completing the hardware installation, power up the appliance.
After completing the hardware installation, power up the appliance.
The first time you power up the appliance, you must run the setup program to configure the appliance. For more information, see Running the Setup Program.
Running the Setup Program
The setup program launches an interactive CLI that prompts you for the required parameters. An administrator can use the console or a dumb terminal to configure the initial network settings and enter the initial administrator credentials for the ACS 5.8.1 server that is using the setup program. The setup process is a one-time configuration task.
At the login prompt, enter setup and press Enter.
The console displays a set of parameters. You must enter the parameters as described in Table 2.
Note: You can interrupt the setup process at any time by typing Ctrl-C![]() before the last setup value is entered.
before the last setup value is entered.
After you enter the parameters, the console displays:
After the ACS server is installed, the system reboots automatically. Now, you can log into ACS with the CLI username and password that was configured during the setup process.
You can use this username and password to log in to ACS only through the CLI. To log in to the web interface, you must use the predefined username ACSAdmin and password default.
When you access the web interface for the first time, you are prompted to change the predefined password for the administrator. You can also define access privileges for other administrators who will access the web interface.
Licensing in ACS 5.8.1
To operate ACS, you must install a valid license. ACS prompts you to install a valid license when you first access the web interface.
Each ACS instance (primary or secondary) in a distributed deployment requires a unique base license.
Types of Licenses
Table 3 lists the types of licenses that are available in ACS 5.8.1.
ACS 5.8.1 does not support auto installation of the evaluation license. Therefore, if you need an evaluation version of ACS 5.8.1, then you must obtain the evaluation license from Cisco.com and install ACS 5.8.1 manually.
If you do not have a valid SAS contract with any of the ACS products, you will not be able to download the ISO image from Cisco.com. In such case, you need to contact your local partner or the Cisco representative to get the ISO image.
Upgrading an ACS Server
If you have ACS 5.5, ACS 5.6, ACS 5.7, or ACS 5.8 installed on your machine, you can upgrade to ACS 5.8.1 using one of the following two methods:
■![]() Upgrading an ACS server using the Application Upgrade Bundle
Upgrading an ACS server using the Application Upgrade Bundle
■![]() Re imaging and upgrading an ACS server
Re imaging and upgrading an ACS server
You can perform an application upgrade on a Cisco appliance or a virtual machine only if the disk size is greater than or equal to 500 GB. If your disk size is lesser than 500 GB, you must re image to ACS 5.8.1, followed by a restore of the backup taken in ACS 5.5, 5.6, 5.7, or ACS 5.8, to move to ACS 5.8.1 Release.
See the Installation and Upgrade Guide for Cisco Secure Access Control System 5.8.1 for information on upgrading your ACS server.
Note: You must provide full permission to NFS directory when you configure the NFS location using the backup-stagging-url command in ACS 5.8.1 to perform a successful On Demand Backup.
Applying Cumulative Patches
Periodically, patches will be posted on Cisco.com that provide fixes to ACS 5.8.1. These patches are cumulative. Each patch includes all the fixes that were included in previous patches for the release.
You can download ACS 5.8.1 cumulative patches from the following location:
http://software.cisco.com/download/navigator.html
The ACS 5.8 and 5.8.1 releases are functionally equivalent and only difference is the set of hardware platforms that are supported. Therefore a common set of patches are provided that can be installed on either ACS 5.8 or ACS 5.8.1. For more information on ACS 5.8 patches, see Resolved Issues in Cumulative Patch ACS 5.8.0.32.1.
To download and apply the patches:
1.![]() Log in to Cisco.com and navigate to Products > Security > Access Control and Policy > Cisco Secure Access Control System > Cisco Secure Access Control System 5.8.
Log in to Cisco.com and navigate to Products > Security > Access Control and Policy > Cisco Secure Access Control System > Cisco Secure Access Control System 5.8.
3.![]() Install the ACS 5.8 cumulative patch. To do so:
Install the ACS 5.8 cumulative patch. To do so:
Enter the following acs patch command in EXEC mode to install the ACS patch:
acs patch install patch-name .tar.gpg repository repository-name
ACS displays the following confirmation message:
Installing an ACS patch requires a restart of ACS services.
Would you like to continue? yes/no
Saved the ADE-OS running configuration to startup successfully
Getting bundle to local machine...
md5: aa45b77465147028301622e4c590cb84
sha256: 3b7f30d572433c2ad0c4733a1d1fb55cceb62dc1419b03b1b7ca354feb8bbcfa
% Please confirm above crypto hash with what is posted on download site.
5.![]() The ACS 5.8 patch displays the md5 and sha256 checksum. Compare it with the value displayed on Cisco.com at the download site. Do one of the following:
The ACS 5.8 patch displays the md5 and sha256 checksum. Compare it with the value displayed on Cisco.com at the download site. Do one of the following:
■![]() Enter Y if the crypto hashes match. If you enter Y, ACS proceeds with the installation steps.
Enter Y if the crypto hashes match. If you enter Y, ACS proceeds with the installation steps.
% Installing an ACS patch requires a restart of ACS services.
Would you like to continue? yes/no
■![]() Enter N if the crypto hashes do not match. If you enter N, ACS stops the installation process.
Enter N if the crypto hashes do not match. If you enter N, ACS stops the installation process.
The ACS version is upgraded to the applied patch. Check whether all services are running properly, using the show application status acs command from EXEC mode.
7.![]() Enter the show application version acs command in EXEC mode and verify if the patch is installed properly or not.
Enter the show application version acs command in EXEC mode and verify if the patch is installed properly or not.
Limitations in ACS Deployments
Table 4 describes the limitations in ACS deployments.
Using the Bug Search Tool
This section explains how to use the Bug Search Tool to search for a specific bug or to search for all bugs in a release.
■![]() Search Bugs Using the Bug Search Tool
Search Bugs Using the Bug Search Tool
Search Bugs Using the Bug Search Tool
Use the Bug Search Tool to view the list of outstanding and resolved bugs in a release.
1.![]() Go to https://tools.cisco.com/bugsearch/search.
Go to https://tools.cisco.com/bugsearch/search.
2.![]() At the Log In screen, enter your registered Cisco.com username and password; then, click Log In. The Bug Toolkit page opens.
At the Log In screen, enter your registered Cisco.com username and password; then, click Log In. The Bug Toolkit page opens.
Note: If you do not have a Cisco.com username and password, you can register for them at http://tools.cisco.com/RPF/register/register.do.
3.![]() To search for a specific bug, enter the bug ID in the Search For field and press Enter.
To search for a specific bug, enter the bug ID in the Search For field and press Enter.
4.![]() To search for bugs in the current release:
To search for bugs in the current release:
a.![]() Click Select from list link. The Select Product page is displayed.
Click Select from list link. The Select Product page is displayed.
b.![]() Choose Security > Access Control and Policy > Cisco Secure Access Control system > Cisco Secure Access Control System 5.8.1.
Choose Security > Access Control and Policy > Cisco Secure Access Control system > Cisco Secure Access Control System 5.8.1.
d.![]() When the search results are displayed, use the filter tools to find the types of bugs you are looking for. You can search for bugs based on different criteria such as status, severity, and modified date.
When the search results are displayed, use the filter tools to find the types of bugs you are looking for. You can search for bugs based on different criteria such as status, severity, and modified date.
Export to Spreadsheet
The Bug Search Tool provides the following option to export bugs to an Excel spreadsheet:
Click Export Results to Excel link in the Search Results page under the Search Bugs tab to export all the bug details from your search to the Excel spreadsheet. Presently, up to 10000 bugs can be exported at a time to an Excel spreadsheet.
If you are unable to export the spreadsheet, log in to the Technical Support Website at http://www.cisco.com/cisco/web/support/index.html for more information or call Cisco TAC (1-800-553-2447).
Documentation Updates
Table 5 lists the updates to Release Notes for Cisco Secure Access Control System 5.8.1.
Product Documentation
Note: It is possible for the printed and electronic documentation to be updated after original publication. Therefore, you should review the documentation on http://www.cisco.com for any updates.
Table 6 lists the product documentation that is available for ACS 5.8.1. To find end-user documentation for all the products on Cisco.com, go to: http://www.cisco.com/go/techdocs.
Select Products > Security > Access Control and Policy > Cisco Secure Access Control System > Cisco Secure Access Control System 5.8.1.
Notices
The following notices pertain to this software license.
This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit ( http://www.openssl.org/).
This product includes cryptographic software written by Eric Young (eay@cryptsoft.com).
This product includes software written by Tim Hudson (tjh@cryptsoft.com).
The OpenSSL toolkit stays under a dual license, i.e. both the conditions of the OpenSSL License and the original SSLeay license apply to the toolkit. See below for the actual license texts. Actually both licenses are BSD-style Open Source licenses. In case of any license issues related to OpenSSL please contact openssl-core@openssl.org.
Copyright © 1998-2007 The OpenSSL Project. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1.![]() Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
2.![]() Redistributions in binary form must reproduce the above copyright notice, this list of conditions, and the following disclaimer in the documentation and/or other materials provided with the distribution.
Redistributions in binary form must reproduce the above copyright notice, this list of conditions, and the following disclaimer in the documentation and/or other materials provided with the distribution.
3.![]() All advertising materials mentioning features or use of this software must display the following acknowledgment: “This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit ( http://www.openssl.org/)”.
All advertising materials mentioning features or use of this software must display the following acknowledgment: “This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit ( http://www.openssl.org/)”.
4.![]() The names “OpenSSL Toolkit” and “OpenSSL Project” must not be used to endorse or promote products derived from this software without prior written permission. For written permission, please contact openssl-core@openssl.org.
The names “OpenSSL Toolkit” and “OpenSSL Project” must not be used to endorse or promote products derived from this software without prior written permission. For written permission, please contact openssl-core@openssl.org.
5.![]() Products derived from this software may not be called “OpenSSL” nor may “OpenSSL” appear in their names without prior written permission of the OpenSSL Project.
Products derived from this software may not be called “OpenSSL” nor may “OpenSSL” appear in their names without prior written permission of the OpenSSL Project.
6.![]() Redistributions of any form whatsoever must retain the following acknowledgment:
Redistributions of any form whatsoever must retain the following acknowledgment:
“This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit ( http://www.openssl.org/)”.
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT “AS IS”' AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL PROJECT OR ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young (eay@cryptsoft.com). This product includes software written by Tim Hudson (tjh@cryptsoft.com).
Copyright © 1995-1998 Eric Young (eay@cryptsoft.com). All rights reserved.
This package is an SSL implementation written by Eric Young (eay@cryptsoft.com).
The implementation was written so as to conform with Netscapes SSL.
This library is free for commercial and non-commercial use as long as the following conditions are adhered to. The following conditions apply to all code found in this distribution, be it the RC4, RSA, lhash, DES, etc., code; not just the SSL code. The SSL documentation included with this distribution is covered by the same copyright terms except that the holder is Tim Hudson (tjh@cryptsoft.com).
Copyright remains Eric Young’s, and as such any Copyright notices in the code are not to be removed. If this package is used in a product, Eric Young should be given attribution as the author of the parts of the library used. This can be in the form of a textual message at program startup or in documentation (online or textual) provided with the package.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1.![]() Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
2.![]() Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
3.![]() All advertising materials mentioning features or use of this software must display the following acknowledgement:
All advertising materials mentioning features or use of this software must display the following acknowledgement:
“This product includes cryptographic software written by Eric Young (eay@cryptsoft.com)”.
The word ‘cryptographic’ can be left out if the routines from the library being used are not cryptography-related.
4.![]() If you include any Windows specific code (or a derivative thereof) from the apps directory (application code) you must include an acknowledgement: “This product includes software written by Tim Hudson (tjh@cryptsoft.com)”.
If you include any Windows specific code (or a derivative thereof) from the apps directory (application code) you must include an acknowledgement: “This product includes software written by Tim Hudson (tjh@cryptsoft.com)”.
THIS SOFTWARE IS PROVIDED BY ERIC YOUNG “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
The license and distribution terms for any publicly available version or derivative of this code cannot be changed. i.e. this code cannot simply be copied and put under another distribution license [including the GNU Public License].
Supplemental License Agreement
END USER LICENSE AGREEMENT SUPPLEMENT FOR CISCO SYSTEMS ACCESS CONTROL SYSTEM SOFTWARE:
This End User License Agreement Supplement (“Supplement”) contains additional terms and conditions for the Software Product licensed under the End User License Agreement ("EULA") between you and Cisco (collectively, the "Agreement"). Capitalized terms used in this Supplement but not defined will have the meanings assigned to them in the EULA. To the extent that there is a conflict between the terms and conditions of the EULA and this Supplement, the terms and conditions of this Supplement will take precedence.
In addition to the limitations set forth in the EULA on your access and use of the Software, you agree to comply at all times with the terms and conditions provided in this Supplement. DOWNLOADING, INSTALLING, OR USING THE SOFTWARE CONSTITUTES ACCEPTANCE OF THE AGREEMENT, AND YOU ARE BINDING YOURSELF AND THE BUSINESS ENTITY THAT YOU REPRESENT (COLLECTIVELY, "CUSTOMER") TO THE AGREEMENT. IF YOU DO NOT AGREE TO ALL OF THE TERMS OF THE AGREEMENT, THEN CISCO IS UNWILLING TO LICENSE THE SOFTWARE TO YOU AND (A) YOU MAY NOT DOWNLOAD, INSTALL OR USE THE SOFTWARE, AND (B) YOU MAY RETURN THE SOFTWARE (INCLUDING ANY UNOPENED CD PACKAGE AND ANY WRITTEN MATERIALS) FOR A FULL REFUND, OR, IF THE SOFTWARE AND WRITTEN MATERIALS ARE SUPPLIED AS PART OF ANOTHER PRODUCT, YOU MAY RETURN THE ENTIRE PRODUCT FOR A FULL REFUND. YOUR RIGHT TO RETURN AND REFUND EXPIRES 30 DAYS AFTER PURCHASE FROM CISCO OR AN AUTHORIZED CISCO RESELLER, AND APPLIES ONLY IF YOU ARE THE ORIGINAL END USER PURCHASER.
For purposes of this Supplement, the Product name(s) and the Product description(s) you may order as part of Access Control System Software are:
A. Advanced Reporting and Troubleshooting License
Enables custom reporting, alerting and other monitoring and troubleshooting features.
Allows deployment to support more than 500 network devices (AAA clients that are counted by configured IP addresses). That is, the Large Deployment license enables the ACS deployment to support an unlimited number of network devices in the enterprise.
C. Advanced Access License (not available for Access Control System Software 5.0, will be released with a future Access Control System Software release)
Enables Security Group Access policy control functionality and other advanced access features.
2.![]() ADDITIONAL LICENSE RESTRICTIONS
ADDITIONAL LICENSE RESTRICTIONS
■![]() Installation and Use. The Cisco Secure Access Control System (ACS) Software component of the Cisco SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 Hardware Platforms are preinstalled. CDs containing tools to restore this Software to the SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 hardware are provided to Customer for re installation purposes only. Customer may only run the supported Cisco Secure Access Control System Software Products on the Cisco SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 Hardware Platforms designed for its use. No unsupported Software product or component may be installed on the SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 Hardware Platform.
Installation and Use. The Cisco Secure Access Control System (ACS) Software component of the Cisco SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 Hardware Platforms are preinstalled. CDs containing tools to restore this Software to the SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 hardware are provided to Customer for re installation purposes only. Customer may only run the supported Cisco Secure Access Control System Software Products on the Cisco SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 Hardware Platforms designed for its use. No unsupported Software product or component may be installed on the SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 Hardware Platform.
■![]() Software Upgrades, Major and Minor Releases. Cisco may provide Cisco Secure Access Control System Software upgrades for the Cisco SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 Hardware Platforms as Major Upgrades or Minor Upgrades. If the Software Major Upgrades or Minor Upgrades can be purchased through Cisco or a recognized partner or reseller, the Customer should purchase one Major Upgrade or Minor Upgrade for each Cisco SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 Hardware Platforms. If the Customer is eligible to receive the Software release through a Cisco extended service program, the Customer should request to receive only one Software upgrade or new version release per valid service contract.
Software Upgrades, Major and Minor Releases. Cisco may provide Cisco Secure Access Control System Software upgrades for the Cisco SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 Hardware Platforms as Major Upgrades or Minor Upgrades. If the Software Major Upgrades or Minor Upgrades can be purchased through Cisco or a recognized partner or reseller, the Customer should purchase one Major Upgrade or Minor Upgrade for each Cisco SNS 3595, SNS 3515, SNS 3495, SNS 3415, and CSACS 1121 Hardware Platforms. If the Customer is eligible to receive the Software release through a Cisco extended service program, the Customer should request to receive only one Software upgrade or new version release per valid service contract.
■![]() Reproduction and Distribution. Customer may not reproduce nor distribute software.
Reproduction and Distribution. Customer may not reproduce nor distribute software.
Major Upgrade means a release of Software that provides additional software functions. Cisco designates Major Upgrades as a change in the ones digit of the Software version number [(x).x.x].
Minor Upgrade means an incremental release of Software that provides maintenance fixes and additional software functions. Cisco designates Minor Upgrades as a change in the tenths digit of the Software version number [x.(x).x].
4.![]() DESCRIPTION OF OTHER RIGHTS AND LIMITATIONS
DESCRIPTION OF OTHER RIGHTS AND LIMITATIONS
Please refer to the Cisco Systems, Inc., End User License Agreement.
Obtaining Documentation and Submitting a Service Request
For information on obtaining documentation, submitting a service request, and gathering additional information, see the monthly What’s New in Cisco Product Documentation, which also lists all new and revised Cisco technical documentation, at:
http://www.cisco.com/en/US/docs/general/whatsnew/whatsnew.html
Subscribe to the What’s New in Cisco Product Documentation as a Really Simple Syndication (RSS) feed and set content to be delivered directly to your desktop using a reader application. The RSS feeds are a free service and Cisco currently supports RSS Version 2.0.
Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1721R)
Any Internet Protocol (IP) addresses used in this document are not intended to be actual addresses. Any examples, command display output, and figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses in illustrative content is unintentional and coincidental.
 Feedback
Feedback