Supported EVC Features
-
Service instance—you create, delete, and modify EFP service instances on Ethernet interfaces.
-
Encapsulation—you can map traffic to EFPs based on:
-
802.1Q VLANs (a single VLAN or a list or range of VLANs)
-
802.1Q tunneling (QinQ) VLANs (a single outer VLAN and a list or range of inner VLANs)
-
Double-tagged frames mapped to EVC based on C-tags (wildcard S-Tags)
-
-
Bridge domains—you can configure EFPs as members of a bridge domain (up to 64 EFPs per bridge domain for bridge domain with BDIs.).
-
Rewrite (VLAN translation)
-
Pop symmetric
pop 1 removes the outermost tag
pop 2 removes the two outermost tags
pop symmetric adds a tag (or 2 tags for pop 2 symmetric ) on egress for a push operation
-
Ingress push—The rewrite ingress tag push dot1q vlan-id symmetric command adds a tag to an ingress packet
-
QinQ with rewrite
rewrite ingress tag push is supported on QoS with CoS Marking for EVCs on RSP2 module.

Note
Ingress push on Qos on for EVC is not supported on RSP1 module.

Note
EVC push is also supported on 802.1ad.
-
-
EVC forwarding
-
MAC address learning and aging
-
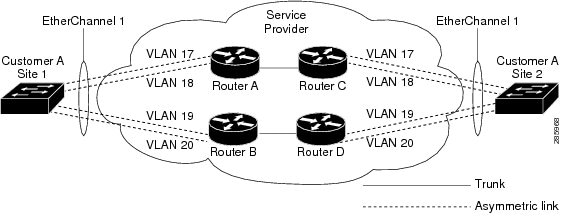
EVCs on EtherChannels
-
Hairpinning
-
Split horizon
-
Layer 2 protocol tunneling and QinQ
-
Bridging between EFPs
-
MSTP (MST on EVC bridge domain)
-
EFP statistics (packets and bytes)
-
QoS aware EVC/EFP per service instance
-
Static MAC Addresses
These Layer 2 port-based features can run with EVC configured on the port:
-
LACP
-
CDP
-
MSTP
-
EVC egress filtering

 Feedback
Feedback