Troubleshooting Guide for Synchronous Digital Hierarchy
Available Languages
Contents
Introduction
This document discusses the principles of measuring performance parameters in Synchronous Digital Hierarchy (SDH) networks. This document provides a description of basic alarms associated with SDH networks, and also signal processes involved in an Add/Drop Multiplexer (ADM). Some of the most significant ADM alarms that are generated at various points in the SDH network are illustrated.
After reading this document, you will be able to state:
-
The relationship error indications at various levels in the SDH network.
-
The main performance parameters available from SDH equipment.
-
The effect on traffic to given error rates.
-
The meaning of some of the most significant alarms generated in SDH equipment.
-
Some of the most significant alarms generated at given points in an SDH network.
Performance Monitoring in the SDH Network
This section describes SDH paths and selections.
SDH Paths and Selections
Figure 1 displays how Regenerator Section Overheads (RSOHs) terminate at each end of the RS, and how Multiplex Section Overheads (MSOHs) terminate at each end of the MS. Path OHs (POHs) terminate at the end of the path, and will be Higher Order (HO) or Lower Order (LO).
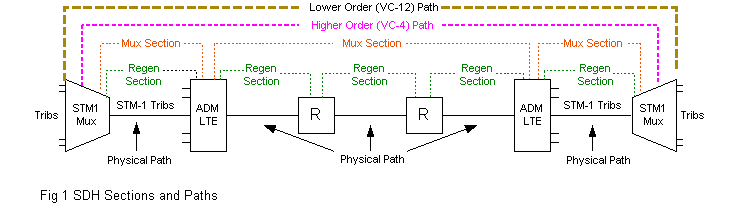
Figure 2 shows the Synchronous Transport Module-1 (STM-1) SOHs and a VC-4 POH:
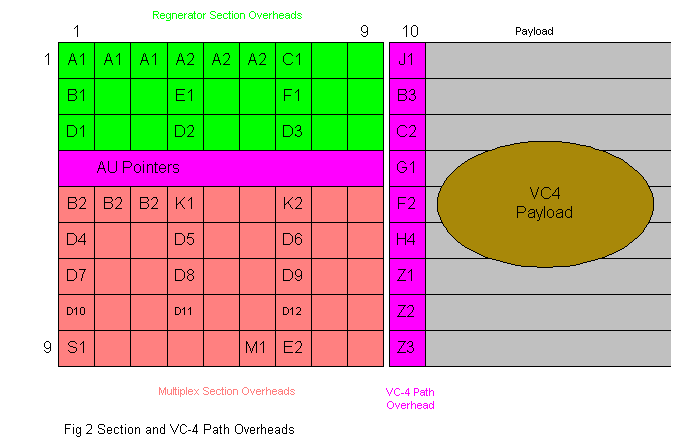
Note: Empty bytes are marked Z, and currently have no specified function.
The tables in this section describe the various types of bytes.
RSOH Bytes
| Byte | Description |
|---|---|
| A1, A2 | Frame Alignment Word (FAW). These bytes produce a fixed pattern which identifies the beginning of each STM-1 frame. |
| C1 (J0) | C1 identifies the STM-1 frame within an Synchronous Transport Module-n (STM-n) signal. This could be replaced on future equipment releases by a J0 byte, which is the RS trace byte. |
| B1 | Bit Interleaved Parity-8 (BIP-8) error check byte, for checking errors on the complete STM-1 signal at the end of an RS. |
| D1 to D3 | Data Communications Channel (DCC) to monitor and control functions between regenerator terminating equipment. |
| E1 | E1 is used to provide a speaker channel. It is not used by some vendors. |
| F1 | F1 provides a data channel for miscellaneous optional users. |
MSOH Bytes
| Byte | Description |
|---|---|
| B2 | BIP-24 error check bytes for checking an STM-1 signal (minus the RSOH) at the end of the MS. |
| K1 and K2 | These are used for controlling MS protection switching, signaling Alarm Indication Signal (AIS), Far End Remote Failure (FERF), and Automatic Protection Switching (APS) alarms, when implemented. |
| D4 to D12 | DCC to monitor and control functions between the MS terminating equipment. |
| S1 | Synchronization Status Message Byte (SSMB), used for signaling the quality of the currently working sync source to a downstream Network Element (NE). |
| M1 | M1 is used to signal error information to the originating end of the MS. |
| E2 | E2 is used to provide a speaker channel. It is not used by some vendors. |
VC-4 Path OH Bytes
| Byte | Description |
|---|---|
| J1 | VC-4 path trace can be used to carry an operator assigned pattern to identify specific VC-4s. |
| B3 | BIP-8 error check byte used for checking errors across a VC-4 path end-to-end. |
| C2 | It describes the contents and structure of the payload. |
| G1 | It sends error data and FERF alarms to the originating end of the VC-4 path. |
| F2 | User channel. |
| H4 | Multiframe identifier. A Tributary Unit (TU) is distributed across four consecutive frames known as a multiframe. This byte is used to ensure the correct sequence of frames within the multiframe. |
VC-12 Path OH Bytes
| Byte | Description |
|---|---|
| J2 | LO path trace. |
| N2 | Tandem connection monitoring byte. |
| K4 | Enhanced remote detect indication and APS. |
The main LO path OH is the V5 byte.
The structure is like this:
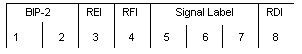
| Bits | Description |
|---|---|
| Bits 1 and 2 | These are used to detect errors in the LO path end-to-end. |
| Bit 3 | Remote Error Indicator (REI), formerly a far end block error path (FEBE) alarm. |
| Bit 4 | RFI alarm. |
| Bits 5 to 7 | Signal Label (SL). Describes the VC-12 payload composition. For example: 000= Unequipped 001= Equipment non-specific 010= Asynchronous 011= Bit synchronous 100= Byte synchronous 111= Virtual Circuit (VC)-AIS |
| Bit 8 | Remote defect indication, formerly a FERF alarm. |
Error Monitoring in the SDH Network
So far, this document has discussed these points:
-
a B1 byte is used to check for errors in the RS.
-
a B2 byte is used to check for errors in the MS.
-
a B3 byte is used to check for errors in the VC-4 path.
-
a V5 byte is used to check for errors in the VC-12 path.
Figure 3 represents the same module as discussed earlier, but the equipment has been labeled A to F. The STM-1 Multiplexer (MUX) is configured to multiplex 63 x 2 Mbit/s.
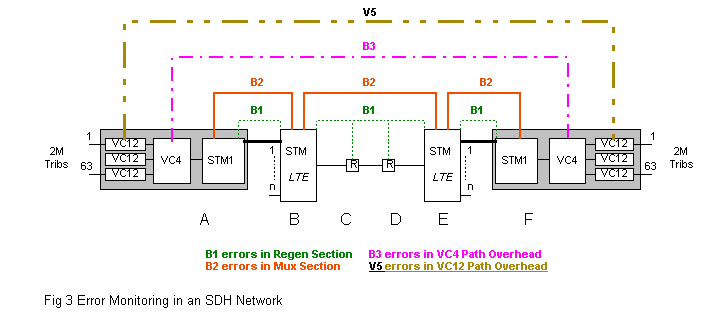
Using the principles discussed, and the information in the OHs, ensure that you know the answers to these questions before proceeding with this document:
Question 1
A fault on a tributary card in the STM-1 MUX A introduces errors into a single VC-12. Check where the errors will be indicated to the network operator.
A B C D E F
Question 2
A fault is corrupting the VC-4. These errors would usually be described as B3 errors. Check where the errors will be indicated to the network operator.
A B C D E F
Question 3
The STM-n MUX Line Terminating Equipment (LTE) at B is indicating B1 errors on a tributary input. The fault must be between ___ and ___.
Question 4
Check any other locations where you think B1 errors will be indicated for this fault.
A B C D E F
Question 5
How many 2M signals will be affected? ___.
Question 6
The STM-n MUX at E is indicating B2 errors on the optical signal from B. The fault must be between ___ and ___.
Question 7
Would there be a B2 error indication at F?
Question 8
Would there be B3 error indication at F?
Click here to review the correct answers to the above questions.
Performance Parameters
We have seen how bytes B1, B2, B3, and V5 can be used to detect errors in specific sections and paths. The error checking mechanisms are based upon BIP error detection. This works by considering B1 errors, which are BIP-8.
The STM-1 frame consists of a series of 8-bit bytes. The first bit of each byte across the whole frame is examined. If the total number of the binary 1s is odd, the first bit of the B1 byte in the next frame is set to binary 1 to make the total number of 1s even. If the total number of 1s is already even, the first bit of the B1 byte is set to binary 0. This is known as even parity.
The second bit of each byte across the frame is examined. The second bit in the B1 byte in the next frame is set to produce even parity. This process is repeated for each of the eight possible bit sequences.
Parity violations are registered as Code Violations (CVs). The process is similar for B2 errors. The mechanism is BIP-24, that is, the STM-1 frame minus the RSOH, is divided into 24-bit units. There are three B2 bytes. The bits are set to produce even parity as before, but over 24 possible bit streams. B3 (BIP-8) checks the VC-4 only, and V5 (BIP-2) checks the VC-11/12 only. CVs may be reported as a straight forward count, or processed to calculate a number of other performance parameters. The following table lists the most commonly monitored parameters on SDH equipment.
| Acronym | Parameter | Description |
|---|---|---|
| CV | Code Violations | Number of BIP-n parity violations in the previous frame. |
| EBER | Equivalent Binary Error Rate | The equivalent rate at which the customer will experience errors as a ratio. For example, 1 in 10 ee-3. |
| ES | Errored Seconds | At least one second interval during which at least one error occurred. |
| SES | Severely Errored Second | A one-second interval during which the EBER has exceeded 1 in 10 EE-3. |
| UAS | Unavailable Seconds | The number of seconds during which the signal is alarmed or experiencing an EBER exceeding 1 in 10 EE-3 for 10 consecutive seconds. |
Most SDH equipment can be set to report performance parameters. On demand, they can be set to report over a preset period of 24 hours, 15 minutes when a preset threshold has been exceeded. In addition, excess error alarms may be raised when the rate of a given entity (B1, B2, B3, and so on) exceeds 1 in 10 e-3. This will result in AISs replacing the corrupted traffic. Signal Degrade (SD) alarms may be raised when the error rate of a given entity (B1, B2, B3, and so on) exceeds 1 in 10 e-6. This rate may cause protection switching if the equipment has been configured appropriately.
Performance Management
Performance monitoring on specific objects, for example, B3 errors in a specified VC-4 path or V5 errors on a customer's circuit (VC-12 trail), may be initiated on an ad-hoc basis, and the results examined as required. However, it would be impractical to apply this manual process generally. A performance management platform has been developed to collect and report performance parameters in a form, which can be used by appropriate business units. For example, they could be used by Network Operations Center (NOC) personnel to identify network problems, or by marketing personnel to produce reports for major customers.
Out-of-Service Testing
VC-12 (V5) errors only check for errors between where the POH is added, to the end of the trail where it is examined. The mechanism does not check the complete circuit from one customer interface to another. Circumstances may arise where the customer insists that the circuit is faulty, but we have no indication of this. In this situation, the circuit is usually taken out-of-service, and tested end-to-end. The technique is to send a known bit pattern from one end of the circuit, and examine it at the other end for errors.
The test signal most commonly used is known as pseudo-random. This is an internationally agreed pattern, which simulates random bit-patterns. Pseudo-random patterns are available at a variety of lengths, that is the number of bits sent before the pattern is repeated. The pattern length used is related to the bit rate of the circuit. A tester at the receiving end reads the incoming pattern. Each incorrect bit is registered as a bit error. Bit errors may be reported as a straight forward error count, or may be further processed to calculate the types of parameters mentioned in the above table.
SDH Alarms
Basic Alarms
Now, we examine some basic alarms which are common to most SDH equipment. To illustrate the meaning of these alarms, let us review the sequence of operations that an NE must perform, in order to select a specific 2 Mbit/ tributary signal from within an STM-1 signal. The process is illustrated in Figure 4.
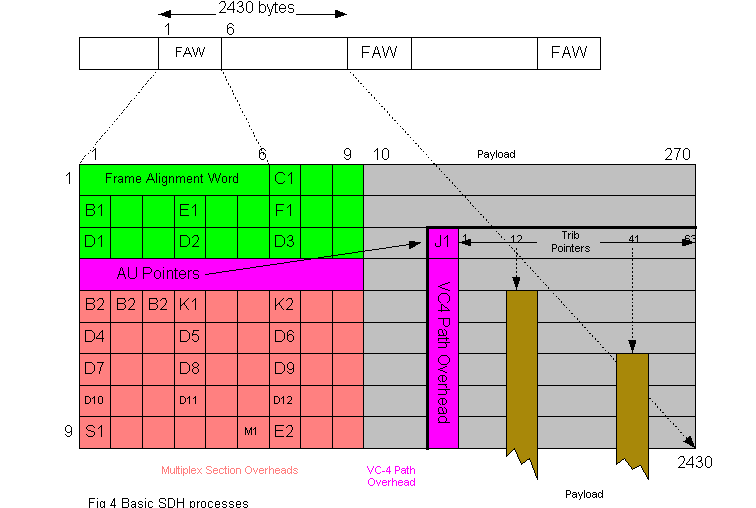
Although we conventionally show the 2430 byte SDH frame in 270 columns and nine rows, an NE receiving an SDH signal actually sees serial data. The serial data consists of STM-1 frames. The most fundamental problem that could occur is that there is no signal at the physical interface. This condition will raise a Loss of Signal (LOS) alarm. Assuming the signal is present, the first task of the NE is to identify where the STM-1 frames are within the serial data. It does this by identifying the FAW which is contained in the first six bytes of the RSOH. If it cannot identify the FAW, a Loss of Frame (LOF) alarm will be raised.
The next step is to find where the VC-4s are located relative to the FAW. This is established by reading the Admin Unit (AU) pointer to locate the J1 byte in the VC-4 POH. If a sensible pointer cannot be found, a Loss of Pointer (LOP) alarm is raised at the AU level. This is usually referred to as an AU-LOP, although it has been seen as VC-4 LOP, which is not strictly correct. The next step is to locate and read theTributary Unit (TU) pointer for the specified TU. If a sensible pointer cannot be found, then a LOP alarm is raised at the TU level.
AIS and FERF Alarms
LOS, LOF, and LOP alarms will render the whole signal unusable. In this case, the missing or corrupted signal is replaced by an AIS consisting of continuous binary 1s. This will produce AIS alarms on all equipment downstream of the fault. The NE detecting the fault also sends an indication to the distant (sending) end that an alarm has been raised. This raises a FERF alarm at the appropriate level at the transmitting NE. Thus, a fault at the MS level will produce an MS-FERF. At the VC-4 level, it will produce a VC-4 FERF or, on some equipment, HO-FERFs. Some SDH elements refer to a remote alarm indication at some levels in the hierarchy.
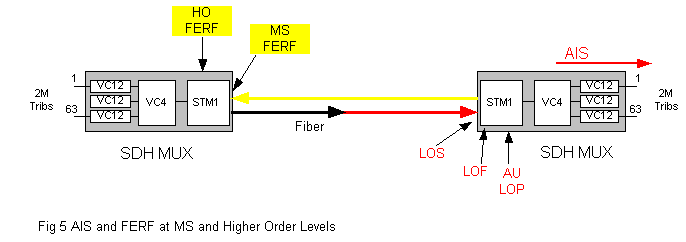
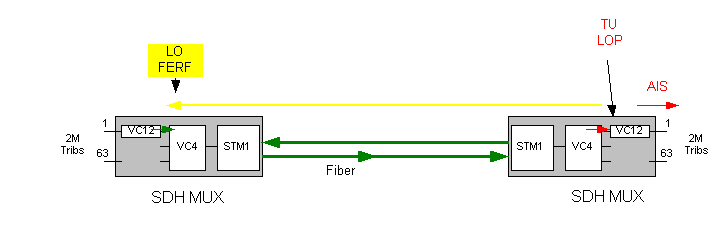
If the fault is at the LO, for example, the TU-12 level, the signal proper (customer data) to the affected tributary is replaced by AIS and FERFs (RAIs) being sent to the appropriate distant transmitting element. This process is illustrated in Figure 6.
Distant Error Indications
Errors detected in an incoming signal can be indicated to the distant originating element in a similar fashion. In this case, the indication is a FEBE alarm, and is indicated at the transmitting NE at the level at which the errors are detected. For example, MS for B2 errors, VC-4 level for B3 errors, and V5 for VC-11/12 errors. The term FEBE has been replaced by Remote Error Indication (REI).
Typical SDH Traffic-Path Alarms
Figure 7 represents a typical STM-1 ADM. The physical cards involved with processing the signals are the tributary card, switch card, and STM-1 line card. Each card is shown with the appropriate processes which occur on that card. The processes for both directions of transmission are shown as well. Outside of the boxes is a list of typical alarms associated with the process to which each alarm relates.
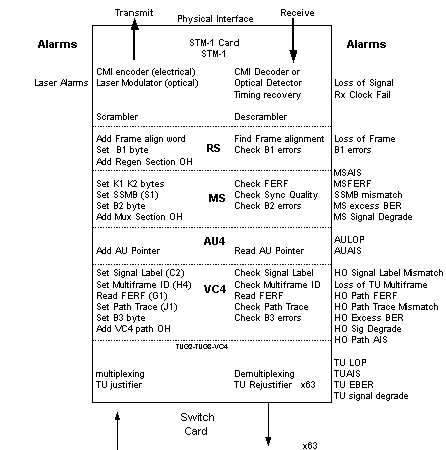
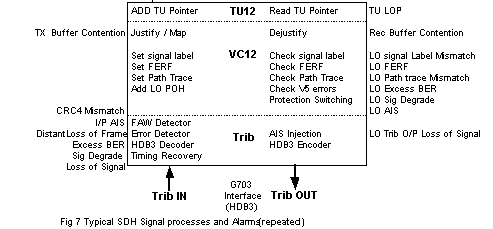
If the tributary input signal is not present, a LOS alarm is raised, and an AIS will be injected to replace the missing signal. The tributary input signal is examined for HDB-3 code errors. Alarms can be raised if the EBER exceeds preconfigured thresholds.
An SD alarm is raised at 1.10-6, and an EBER is raised at 1.10-3. The 2 Mbit/s tributary input signal is used to lock a phase locked loop timing recovery circuit. This recovered clock is used to clock the data into a transmit buffer. The signal is then HDB-3 decoded. The input port on some equipment may be configured to examine the G704 (30chan PCM) frame structure of the tributary input signal, and raise alarms as appropriate. These alarms are as follows:
-
LOF: the FAW cannot be found.
-
I/P AIS: the tributary input signal consists of all 1s.
-
Distant: an alarm is raised on the attachment in the receive direction.
-
Cyclic Redundancy Check-4 (CRC-4) mismatch: an error checking device for checking the integrity of the G704 structure.
The tributary data is mapped into a container Class 12 (C12), and the POHs are added to form a VC-12. The VC-12 OH bits are set appropriately as follows:
-
The path trace message may be set by the operator if this facility is required.
The Signal Label (SL) is set to describe the contents of the VC-12, as follows:
-
G703 inputs will normally be set to asynchronous or equipped-non specific.
-
G704 (structured) ports will be set to byte synchronous.
-
Unused ports will be set automatically to unequipped.
-
If there is an alarm associated with the receive side of the TU, a FERF will be set in the path OH.
As the tributary signal is read from the transmit buffer, a TU pointer is added to form a TU-12. If the buffer fills or empties beyond preset limits, a transmission buffer contention alarm is raised.
The TU-12 is now cross connected on the switch card to a time slot on the STM-1 line card, and multiplexed into the VC-4 payload. The VC-4 POH bytes are set appropriately as follows:
-
The SLl (C2) byte is set to describe the structure of the VC-4.
-
The multiframe ID (H4) byte is set to describe the position of the VC-4 in the four-frame multi-frame sequence.
A path trace message may be set by the operator in the J1 byte if this facility is required. The B3 byte is set to produce even parity across all BIP-8 sequences in the VC-4 of the previous frame. If an alarm is raised at the VC-4 level in the receive direction, a FERF is sent to the far end in the G1 byte.
A pointer is added to the VC-4 to form an AU-4. The MSOHs are added and set as follows:
-
The B2 bytes are set to produce even parity across all BIP-24 sequences in the previous STM-1 frame, minus its RSOH. The SSMB is set to the status of the currently used source. The K1 and K2 bytes are set to send a MS-FERF to the distant end if appropriate, and initiate Multiprotocol over Asynchronous Transfer Mode (ATM) Server (MPS)/APS when used.
The RSOHs are then added and set as follows:
-
The B1 byte is set to produce even parity across all BIP-8 sequences in the whole of the previous STM-1 frame. The FAW is added.
We now have an STM-1 frame. However, if we sent this signal to line in this form, there would be a strong possibility that it would contain long sequences of binary 1s and / or binary 0s, that is, no signal transitions. This would mean that timing extraction circuits (phase locked loops) in downstream equipment would not be able to recover timing from the signal.
Previously, line signals were encoded into a proprietary line code. This meant that both ends of the system had to be provided by the same manufacturer. With SDH, we no longer use such line codes, but the signal (minus the FAW) is scrambled. This means that an internationally agreed complex pattern (scrambling algorithm) is superimposed on the traffic signal. This ensures that there will always be sufficient transitions in the signal to guarantee a usable timing component independent of traffic bit patterns. The pattern is removed by a de-scrambler at the other end of the RS.
The next stage is to adapt the signal to the physical interface, often referred to as the Network Node Interface (NNI). If the card has an electrical interface, the STM-1 signal is encoded into the Cisco Messaging Interface (CMI). If the interface is optical, the STM-1 signal is used to modulate a laser (switch it on and off in accordance with the data binary 1s and 0s).
Laser parameters are monitored and alarms raised if limits are exceeded. The alarms usually include the following:
-
Laser high power: the optical output power has increased (usually by 1 to 3 dBm).
-
Laser low power: the optical output power has decreased (usually by 1 to 3 dBm).
-
Laser bias high: usually an indication that the laser is nearing the end of its life.
Receive Direction
The incoming signal could be optical or electrical. If it is an optical interface, the optical signal is converted to electrical by means of an optical detector. If the optical power falls to a pre-determined level (usually about -35 dBm), a LOS alarm is raised.
The electrical STM-1 signal is applied to a phase locked loop timing recovery device to extract a clock, which will be used to time the rest of the processing for this direction of transmission (which can usually be made available at an external connector for the other network timing applications.)
If a clock cannot be extracted, a Loss of Receive Clock (LRC) alarm will be raised. This is also referred to as Loss of Recovered Clock. If the NNI is electrical, the CMI STM-1 signal is used to phase lock the timing recovery circuit. If a clock cannot be extracted, a LRC alarm will be raised. The CMI signal is then decoded.
The ADM is now looking at a stream of anonymous serial data which actually represents a stream of STM-1 frames. The ADM must therefore find the FAWs within this serial data. If it cannot find them, a LOF alarm will be raised. Having found the FAWs, the remainder of the signal is de-scrambled. The ADM now knows the location of all the OH bytes. In the RSOH, the B1 byte can be examined to measure the error performance of the RS it is terminating. Error threshold alarms could also be provided on some equipment.
Examining the MSOH
The next step is to examine the MSOH. If the overhead bytes contain all binary 1s, a MS-AIS alarm is raised. Bytes K1 and K2 are examined, and a FERF alarm is raised, if necessary, indicating the presence of an active alarm at the distant end of the MS. Multiplexed Switch Protocol (MSP) switching, and/or Automatic Protection Switching (APS) would be initiated at this point in response to K1/K2 settings if they were implemented, which they aren't at the moment.
The S1 SSMB is examined. If the quality level is less than the required, preconfigured level, the ADM will switch to the next priority source, and an SSMB mismatch alarm will be raised. The SSMB is not implemented on all SDH equipment. The B2 bytes are examined in association with the previous frame. If the BIP-24 check shows parity violations, alarms will be raised. An error rate of 1.10-6 will raise a SD alarm. An error rate of 10-3 will raise an EBER alarm. These thresholds are usually configurable, but these are very typical values. The next process is to identify and read the AU pointer. If the ADM cannot make sense of the pointer value, an AU-LOP alarm is raised. If the pointer contains only binary 1s, an AU-AIS alarm will be raised.
Having identified and read the AU pointer, the VC-4 POH can now be examined. The C2 SLl byte is compared with the actual structure found in the VC-4. If this does not match the structure described in the C2 byte, a Signal Label Mismatch (SLM) alarm will be raised. Siemens describes this as a Wrong Signal Label (WSL) alarm. The comparison process is automatic on Guam-Philippines-Taiwan (GPT) and Siemens equipment. On Marconi and Ericcson equipment, the expected C2 value is manually configured.
The H4 mulitframe sequence (1234) byte is examined. If the sequence is violated, a loss of TU multiframe alarm is raised.
The G1 byte is examined and a HO path FERF alarm is raised, if necessary, indicating the presence of an active alarm at the distant end or the VC-4 path.
The J1 byte is examined. If the path trace facility has been enabled, the message in the J1 byte sequence is compared with the preconfigured expected value. If they are different, a HO path trace mismatch alarm is raised.
The B3 byte is examined in association with the previous frame. If the BIP-8 check shows parity violations, SD (10-6) or EBER (10-3) alarms will be raised.
If the POH bytes consist of all binary 1s, the HO path AIS alarm is raised.
The VC-4 is now de-multiplexed.
Examining the TU-12
The TU-12 must be examined as well. If a sensible TU-12 pointer cannot be found, a TU-LOP alarm is raised. If the pointer consists of all binary 1s, a TU-AIS alarm is raised.
The V5 VC-12 POH byte is examined in association with the previous frame. If the BIP-2 check shows parity violations, SD (10-6) or EBER (10-3) alarms will be raised.
The TU-12 is now cross connected by the switch card to a tributary port on the tributary card. As the TU arrives at the tributary card, the pointer is re-examined. If a sensible pointer cannot be found, a TU-LOP alarm is raised.
Examining the VC-12
The VC-12 path overhead bytes are also examined.
If the path trace facility has been enabled, the message in the path trace sequence is compared with the preconfigured expected value. If they are different, a LO path trace mismatch alarm is raised.
The SL is compared with the actual structure found in the VC-12. If this does not match the structure described in the SL bits of V5, a LO SLM alarm will be raised.
The FERF bit in the V5 byte is examined and a LO path FERF alarm raised, if necessary, indicating the presence of an active alarm at the distant end of the VC-12 path.
The BIP-2 bits of V5 byte are examined. If the BIP-8 check shows parity violations, LO path SD (10-6) or EBER (10-3) alarms will be raised.
If the POH bits consist of all 1s, a lower order path AIS alarm is raised.
Data is clocked into a receive buffer, where it is de-justified.
If the buffer fills or empties beyond predetermined limits, a receive buffer contention alarm is raised. The signal is clocked out of the buffer at exactly the rate it went in at the far end of the circuit. A failure of the output signal will raise a tributary output LOS alarm.
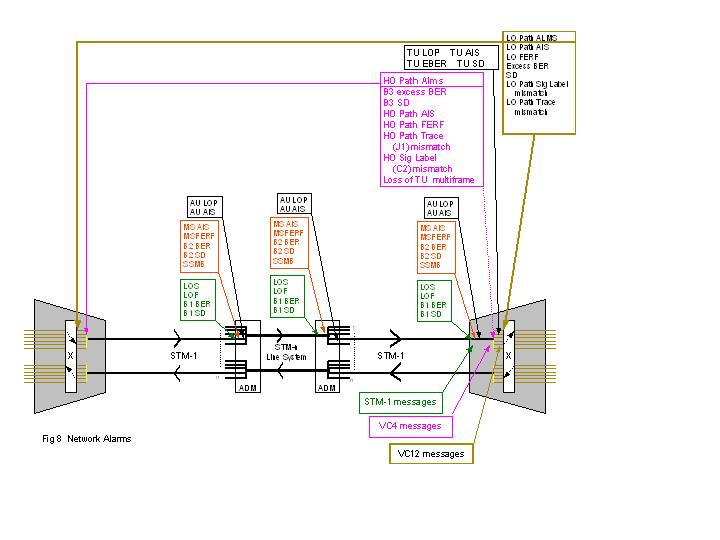
Network Alarms
Now that we have met and fully understand the alarms associated with a typical ADM, we can consider what alarms you might expect to see on virtually any type of SDH NE, anywhere in the network. This is because they are all performing similar functions in the same way at each level in the SDH hierarchy. For instance, all of the processes and alarms mentioned in this document apply to synchronous Cross Connects (XCs) with the STM-1 and LO 2 Mbit/s tributary ports. There are other processes and alarms involved as you might expect, but this document only covers the basics.
Figure 8 shows a hypothetical SDH network with similar connectivity as in a concert GMP-2 trunk.

Answers
Question 1
A fault on a tributary card in the STM-1 Mux A introduces errors into a single VC-12. Check where the errors will be indicated to the network operator.
Answer: F
Question 2
A fault is corrupting the VC-4. These errors would usually be described as B3 errors. Check where the errors will be indicated to the network operator.
Answer: F
Question 3
The STM-n MUX (LTE) at B is indicating B1 errors on a tributary input. The fault must be between A and B.
Question 4
Check any other locations where you think B1 errors will be indicated for this fault.
Answer: None - B1 errors are confined to the individual RS.
Question 5
How many 2 M signals will be affected?
Answer: All
Question 6
The STM-n mux at E is indicating B2 errors on the optical signal from B. The fault must be between B and E.
Question 7
Would there be a B2 error indication at F?
Answer: No. B2 errors are confined to the individual MS.
Question 8
Would there be B3 error indication at F?
Answer: Yes. The payload must be affected if the transport module is corrupted.
Related Information
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
02-Dec-2005 |
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback