Feedback Feedback
|
Table Of Contents
FIPS 140-2 Non-Proprietary Security Policy for the Cisco PIX 515/515E Security Appliance
PIX Security Appliance Validation Level
Physical Characteristics and Module Interfaces
Crypto Officer Guidance - System Initialization
Crypto Officer Guidance - System Configuration
Approved Cryptographic Algorithms
Applying Tamper-Evident Labels
Obtaining Documentation, Obtaining Support, and Security Guidelines
FIPS 140-2 Non-Proprietary Security Policy for the Cisco PIX 515/515E Security Appliance
Introduction
This is a non-proprietary Cryptographic Module Security Policy for the PIX515/515E, referred to in this document as the PIX security appliance, devices, modules, or appliances. This security policy describes how the PIX security appliance meet the security requirements of FIPS 140-2 and how to run the device in a FIPS 140-2 mode of operation.
This policy was prepared as part of the Level 2 FIPS 140-2 validation of the PIX515/515E security appliance.
FIPS 140-2 (Federal Information Processing Standards Publication 140-2 — Security Requirements for Cryptographic Modules) details the U.S. government requirements for cryptographic modules. More information about the FIPS 140-2 standard and validation program is available on the NIST website at http://csrc.nist.gov/cryptval/.
Note
This document may be copied in its entirety and without modification. All copies must include the copyright notice and statements on the last page.
This document includes the following sections:
•
PIX Security Appliance Validation Level
•
Physical Characteristics and Module Interfaces
•
Approved Cryptographic Algorithms
•
Applying Tamper-Evident Labels
•
Obtaining Documentation, Obtaining Support, and Security Guidelines
Submission Package
The security policy document is one document in a complete FIPS 140-2 Submission Package. In addition to this document, the complete FIPS 140-2 Submission Package contains:
•
Vendor Evidence
•
Finite State Machine
•
Other supporting documentation as additional references
With the exception of this Non-Proprietary Security Policy, the FIPS 140-2 Validation Documentation is proprietary to Cisco Systems, Inc. and is releasable only under appropriate non-disclosure agreements. For access to these documents, please contact Cisco Systems, Inc. See "Obtaining Documentation, Obtaining Support, and Security Guidelines" section for more information.
Overview
The market-leading Cisco PIX security appliance deliver robust user and application policy enforcement, multi-vector attack protection, and secure connectivity services in cost-effective, easy-to-deploy solutions. Cisco PIX security appliances provide comprehensive security, performance, and reliability for network environments of all sizes.
These purpose-built appliances provide multiple integrated security and networking services, including:
•
Advanced application-aware firewall services
•
Market-leading Voice over IP (VoIP) and multimedia security
•
Robust site-to-site and remote-access IPSec VPN connectivity
•
Award-winning resiliency
•
Intelligent networking services
•
Flexible management solutions
The Cisco PIX515/515E security appliances are validated with the VPN Acceleration Card+ (VAC+), which delivers high-performance, hardware-accelerated IP Security (IPSec) VPN support for state-of-the-art international cryptographic standards and highly scalable VPN tunnel aggregation in a solution that comes integrated with, or as an upgrade for, most models of the market-leading Cisco PIX security appliance. Ranging from solutions for small to midsize businesses (SMBs) to large enterprises and service providers, the Cisco PIX security appliance offers extensible platforms that provide robust, enterprise-class integrated network security services and solid investment protection. The Cisco PIX VAC+ takes full advantage of this extensibility and maximizes platform investment protection by off loading computationally intensive VPN cryptographic functions. This enables the Cisco PIX security appliances to deliver higher-performance stateful inspection firewall services, advanced application and protocol inspection, inline intrusion protection, and robust multimedia and voice security services.
PIX Security Appliance Validation Level
Table 1 lists the level of validation for each area in the FIPS 140-2 security policy.
Physical Characteristics and Module Interfaces
Each PIX security appliance is a multi-chip standalone device. The cryptographic boundary is defined as encompassing the "top," "front," "left," "right," and "bottom" surfaces of the case and the "backplane" of the case which are not designed to accommodate a removable interface or service card, and inverse of the three-dimensional space within the case that would otherwise be occupied by an installed service card. The cryptographic boundary includes the connection apparatus between the service card and the motherboard/daughterboard that hosts the service card, but the boundary does not include the service card itself (except when a VAC+ is inserted into an available PIX Circuit Board Interface). In other words, the cryptographic boundary encompasses all hardware components within the case of the device except any installed modular service card (except when a VAC+ is inserted into an available PIX Circuit Board Interface).
Each PIX security appliance provides a number of physical and logical interfaces to the device, and the physical interfaces provided by the device are mapped to four FIPS 140-2 defined logical interfaces: data input, data output, control input, and status output.
The logical interfaces and their mapping are described in Table 2:
Roles and Services
The device can be accessed in one of the following ways:
•
Console Port
•
Telnet over IPSec
•
SSH
•
ASDM via HTTPS/TLS
As required by FIPS 140-2, there are two main roles in the PIX security appliance that operators may assume: a crypto officer role and a user role. The PIX security appliance supports role-based authentication, and the respective services for each role are described in the "Crypto Officer Services" section, and the "User Services" section.
Crypto Officer Services
The crypto officer role is responsible for the configuration and maintenance of the PIX security appliance and authenticates from the enable command (for local authentication) or the login command (for AAA authentication) from the user services. The crypto officer services consist of the following:
•
Configure the Device—Define network interfaces and settings; set the protocols the PIX security appliance will support; enable interfaces and network services; set system date and time; load authentication information; and configure authentication servers, filters and access lists for interfaces and users, and privileges.
•
Define Rules and Filters—Create packet filters that are applied to user data streams on each interface. Each filter consists of a set of rules, which define a set of packets to permit or deny based on characteristics such as protocol ID, addresses, ports, TCP connection establishment, or packet direction.
•
View Status—View the configuration, routing tables, active sessions, use gets to view SNMP MIB statistics, health, temperature, memory status, packet statistics, review accounting logs, and view physical interface status.
•
Manage the Device—Log off users, shut down or reload the PIX security appliance, view complete configurations, view full status, manage user rights, and restore configurations.
•
Set Encryption/Bypass—Set up the configuration tables for IP tunneling, set keys and algorithms to be used for each IP range or allow plaintext packets to be sent from specified IP address.
•
Install Service Card—Remove tamper-evident seals to install or replace service cards.
User Services
A user enters the system by accessing the console port with a terminal program or via IPSec protected Telnet or SSH session to a LAN port. The PIX security appliance will prompt the user for their password. If the password is correct, the user is allowed entry to the executive program. The services available to the user role consist of the following:
•
Status Functions—Image version currently running, installed hardware components, and version of hardware installed
•
Network Functions—Initiate diagnostic network services, such as ping
•
Directory Services—Display directory of files kept in Flash memory
Critical Security Parameters
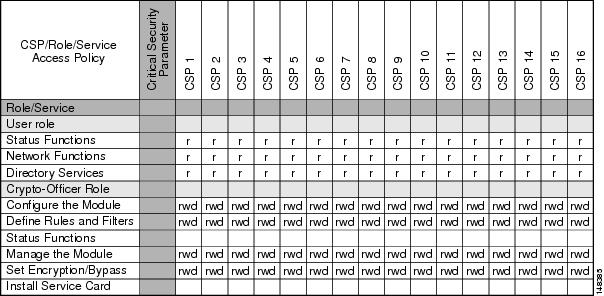
The services accessing the Critical Security Parameters (CSPs), the type of access and which role accesses the CSPs are listed in the Table 3.
Table 3 Role and Service Access to Security Relevant Data Items
rwd: r = read, w = write, d = delete.
Authentication Mechanisms
The PIX security appliance supports either a password or digital certificates for authenticating IPSec users. To log on to the PIX security appliance for management purposes, an operator must connect to it through one of the management interfaces (Console Port, SSH, Telnet, or ASDM) and provide a password.
Table 4 describes the estimated strength of the authentication mechanism.
Table 4 Estimated Strength of Authentication Mechanism
Username Password mechanism
Passwords must be a minimum of 6 characters (see the "Secure Operation" section). The password can consist of alphanumeric values, a-zA-Z0-9, yielding 62 choices per character. The probability of a successful random attempt is 1/62^6, which is less than 1/1,000,000. This is also valid for RADIUS or TACACS+ shared secret keys.
Certificate based authentication
The PIX security appliance supports a public key based authentication with 1024 and 2048 (for RSA) bit keys.
A 1024-bit RSA key has at least 80-bits of equivalent strength. The probability of a successful random attempt is 1/2^80, which is less than 1/1,000,000.
A 2048-bit RSA key has at least 112-bits of equivalent strength. The probability of a successful random attempt is 1/2^112, which is less than 1/1,000,000.
Cryptographic Key Management
The PIX security appliances use a variety of critical security parameters during operation.
Table 5 lists the critical security parameters used by the PIX security appliance.
Self-Tests
The PIX security appliances include an array of self-tests that are run during startup and periodically during operations to prevent any secure data from being released and to ensure all components are functioning correctly.
Table 6 lists the PIX security appliance power-on self-tests.
The PIX security appliances perform all power-on self-tests automatically at boot-up when FIPS mode is enabled. All power-on self-tests must be passed before a user/crypto officer can perform services. The power-on self-tests are performed after the cryptographic systems are initialized but prior to the initialization of the LANs; this prevents the device from passing any data during a power-on self-test failure. In the unlikely event that a power-on self-test fails, an error message is displayed on the console followed by a system reboot.
Table 7 lists the conditional self-tests that the PIX security appliance performs.
Mitigation of Other Attacks
The PIX security appliances do not claim to mitigate any attacks in a FIPS-approved mode of operation above and beyond the protection inherently provided by the PIX security appliance.
Secure Operation
The Cisco PIX515/515E security appliances meet FIPS 140-2 Level 2 requirements.
This section describes how to place and keep the PIX security appliance in a FIPS-approved mode of operation. Operating the PIX security appliance without maintaining the settings described in the "Crypto Officer Guidance - System Initialization" section and "Crypto Officer Guidance - System Configuration" section will remove the PIX security appliance from the FIPS-approved mode of operation.
Crypto Officer Guidance - System Initialization
The PIX security appliance were validated with adaptive security appliance software version 7.0.4 (file name: pix704.bin). This is the only allowable image for FIPS-approved mode of operation.
To initialize the system, the crypto officer must perform the following steps:
Step 1
Ensure the security context mode is set to single mode by entering the following command:
(config)# mode singleStep 2
Ensure the firewall mode is set to routed mode by entering the following command:
(config)# no firewall transparentStep 3
Disable the console output of system crash information by entering the following command:
(config)# crashinfo console disableStep 4
Enable "FIPS Mode" to allow the device to internally enforce FIPS-compliant behavior, such as running power-on self tests and bypass test by entering the following command:
(config)# fips enableStep 5
Install Triple DES/AES licenses to require the device to use Triple DES and AES (for data traffic and SSH).
Step 6
Disable password recovery by entering the following command:
(config)# no service password-recoveryStep 7
Set the configuration register to bypass ROMMON prompt at boot by entering the following command:
(config)# config-register 0x10011Step 8
Define the failover key to ensure encryption of the link to redundant modules prior to enabling failover by entering the following command:
(config)# failover key hex <key>
Note
Failover is not required for FIPS mode of operation. If failover is to be enabled, then the above configuration should be followed. Also, only LAN-based failover is allowed for FIPS mode of operation; serial link failover is not allowed in FIPS mode of operation. Failover should not be configured over the lowest-numbered interface (e.g., Ethernet 0); ports Ethernet 1 or above should be used. If the lowest-numbered interface is already implemented as the failover interface, the Crypto Officer should take the following action:
- Before upgrading to V7.0.4, copy the configuration to a location off the device
- Use a text editor to modify the interface configuration
- Change the failover cables to the specified failover interface
- Upgrade to V7.0.4 and reload the modified configurationStep 9
Enable AAA authorization for the console by entering the following command:
(config-terminal)# aaa authentication serial console LOCAL(config-terminal)# username <name> password <password>Step 10
Enable AAA authorization for SSH and Telnet by entering the following command:
(config-terminal)# aaa authentication ssh console LOCAL(config-terminal)# aaa authentication telnet console LOCALStep 11
Enable AAA authorization for Enable mode by entering the following command:
(config-terminal)# aaa authentication enable console LOCALStep 12
Specify Privilege Level 15 for crypto officer and Privilege Level 1 for user and set up username/password for each role by entering the following command:
(config-terminal)# username <name> password <password> privilege 15(config-terminal)# username <name> password <password> privilege 1Step 13
Ensure passwords are at least 6 characters long.
Step 14
All default passwords (e.g., enable, Telnet) should be replaced with new passwords.
Step 15
Apply tamper-evident labels as described in the "Applying Tamper-Evident Labels" section.
Note
The Crypto Officer may install any Service Card modules that only provide a physical interface (e.g., PIX-1FE, PIX-1GE-66, PIX-4FE-66).The PIX modules are validated only with the VPN Acceleration Card PLUS (VAC+) for cryptographic acceleration; the legacy VAC is not supported in FIPS approved mode of operation.
Step 16
Reboot the PIX security appliance.
Crypto Officer Guidance - System Configuration
To configure the system, perform the following steps:
Step 1
Assign users a Privilege Level of 1.
Step 2
Define RADIUS and TACACS+ shared secret keys that are at least 6 characters long and secure all traffic between the PIX security appliance and the RADIUS/TACACS+ server via IPSec tunnel.
Note
Use only if RADIUS/TACACS+ is configured.
Step 3
Configure the TLS protocol when using HTTPS to protect administrative functions. Due to known issues relating to the use of TLS with certain versions of the Java plugin, it is recommended that the customer upgrade to JRE 1.5.0_05 or later. The following configuration settings are known to work when launching ASDM in a TLS-only environment with JRE 1.5.0_05:
•
Configure the device to allow only TLSv1 packets.
(config)# ssl server-version tlsv1-only•
Uncheck the SSL Version 2.0 check box in both the web browser and JRE security settings.
•
Check the TLS V1.0 check box in both the web browser and JRE security settings.
Step 4
Configure the PIX security appliance to use SSHv2 by entering the following command:
(config)# ssh version 2
Note
All operators must still authenticate after remote access is granted.
Step 5
Configure the PIX security appliance to assure that any remote connections via Telnet are secured through IPSec.
Step 6
Configure the PIX security appliance to assure that only FIPS-approved algorithms are used for IPSec tunnels.
Step 7
Configure the PIX security appliance to assure that error messages can only be viewed by an authenticated crypto officer.
Step 8
SNMP packets must be sent over an IPSec tunnel for secure SNMP operations. PIX devices only support SNMP v1 and v2c, which use community strings for authentication and exchange data in clear-text.
Step 9
Disable the FTP, and TFTP servers as well as HTTP for performing system management.
Step 10
Ensure that installed digital certificates are signed using FIPS approved algorithms (SHA-1).
Step 11
Ensure that 512-bit and 768-bit RSA keys are not used.
Step 12
Ensure that the DSA algorithm uses at least a 512-bit modulus.
Approved Cryptographic Algorithms
The appliances support many different cryptographic algorithms; however, only FIPS approved algorithms may be used. The following cryptographic algorithms are to be used:
•
AES encryption/decryption
•
Triple DES encryption/decryption
•
SHA-1 hashing
•
SHA-1 HMAC for hashed message authentication
•
RSA signing and verifying
•
DSA signing and verifying
•
X9.31 for RNG
•
TLS for Layer 7 security
Note
Pursuant to the DES Transition Plan and the approval of the Withdrawal of Federal Information Processing Standard (FIPS) 46-3, Data Encryption Standard (DES); FIPS 74, Guidelines for Implementing and Using the NBS Data Encryption Standard; and FIPS 81, DES Modes of Operation, the DES algorithm should not be used in FIPS approved mode of operation. The DES algorithm must not be used when the Triple DES/AES licenses are installed.
Each cryptographic implementation in the PIX security appliance software release with on-board acceleration has achieved the certifications listed in Table 8.
Non-FIPS Approved Algorithms
The PIX security appliances implement the following non-FIPS-approved cryptographic algorithms:
•
DES
•
SSL
•
RC4
•
MD5
•
MD5 HMAC
•
Diffie-Hellman (allowed for use in FIPS mode) (key establishment methodology provides 80-bits or 96-bits of encryption strength)
•
RSA encryption/decryption (allowed in FIPS mode for key transport) (key establishment methodology provides 80-bits or 112-bits of encryption strength)
Applying Tamper-Evident Labels
All Critical Security Parameters (CSPs) are stored and protected within the PIX security appliance tamper-evident enclosure. The administrator is responsible for properly placing all tamper-evident labels. The security labels recommended for FIPS 140-2 compliance are provided in FIPS Kit. These security labels are very fragile and cannot be removed without clear signs of damage to the labels.
The crypto officer should inspect the tamper-evident labels periodically to verify they are intact and the serial numbers on the applied tamper-evident labels match the records in the security log.
Note
The tamper-evident seals are produced from a special thin gauge vinyl with self-adhesive backing. Any attempt to open the PIX security appliance will damage the tamper-evident seals or the material of the PIX security appliance cover. Because the tamper-evident seals have non-repeated serial numbers, they may be inspected for damage and compared against the applied serial numbers to verify that the device has not been tampered with. Tamper-evident seals can also be inspected for signs of tampering, which include the following: curled corners, rips, and slices. The word Open may appear if the label was peeled back. Extra tamper-evident seals have been included in your FIPS kit to accommodate maintenance of your chassis.
To apply the serialized tamper-evident labels, perform the following steps:
Step 1
Turn off and unplug the system before cleaning the chassis and applying labels.
Step 2
Clean the chassis of any grease, dirt, or oil before applying the labels. Alcohol-based cleaning pads are recommended for this purpose.
Step 3
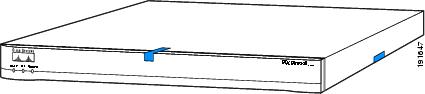
Apply a label on the front of the chassis so that the label covers the front plate and the top of the PIX515/515E chassis See Figure 1.
Step 4
Apply a label to cover the PIX515/515E side and bottom portions of the chassis. See Figure 1.
Figure 1 Cisco PIX 515/515E Front Tamper-Evident Label Placement
Step 5
On the back of the chassis, apply labels to cover the interface slots. SeeFigure 2.
Step 6
Apply a label to cover the PIX515/515E side and bottom portions of the case on the opposite side as in Step 3. SeeFigure 2.
Figure 2 Cisco PIX 515/515E Back Tamper-Evident Label Placement
Step 7
Record the serial numbers of the labels applied to the system in a security log.
Related Documentation
This document deals only with operations and capabilities of the PIX security appliance in the technical terms of a FIPS 140-2 cryptographic device security policy.
More information is available on the PIX security appliance from the following sources:
•
PIX security appliance (hardware): http://www.cisco.com/en/US/products/hw/vpndevc/ps2030/tsd_products_support_series_home.html
•
PIX security appliance software: http://www.cisco.com/en/US/products/sw/secursw/ps2120/tsd_products_support_series_home.html
•
PIX security appliance licenses: http://www.cisco.com/en/US/products/hw/vpndevc/ps2030/products_data_sheet09186a00800b0d85.html
•
The NIST Cryptographic Module Validation Program website contains contact information for answers to technical or sales-related questions for the PIX security appliance. (See (http://csrc.ncsl.nist.gov/cryptval/.)
Obtaining Documentation, Obtaining Support, and Security Guidelines
For information on obtaining documentation, obtaining support, providing documentation feedback, security guidelines, and also recommended aliases and general Cisco documents, see the monthly What's New in Cisco Product Documentation, which also lists all new and revised Cisco technical documentation, at:
http://www.cisco.com/en/US/docs/general/whatsnew/whatsnew.html
Definitions
AES—Advanced Encryption Standard
CMVP—Cryptographic Module Validation Program
CSP—Critical Security Parameter
DES—Data Encryption Standard
FIPS—Federal Information Processing Standard
HTTP—HyperText Transfer Protocol
KAT—Known Answer Test
LED—Light Emitting Diode
MAC—Message Authentication Code
NIST—National Institute of Standards and Technology
NVLAP—National Voluntary Laboratory Accreditation Program
RAM—Random Access Memory
RSA—Rivest Shamir and Adleman method for asymmetric encryption
SCEP—Simple Certificate Enrollment Protocol
Service Card—A service card may provide additional interfaces, feature acceleration or additional services. Service cards may take a Circuit Board form factor for PIX security appliance.
SHA—Secure Hash Algorithm
SSL—Secure Sockets Layer
TLS—Transport Layer Security
CCVP, the Cisco Logo, and the Cisco Square Bridge logo are trademarks of Cisco Systems, Inc.; Changing the Way We Work, Live, Play, and Learn is a service mark of Cisco Systems, Inc.; and Access Registrar, Aironet, BPX, Catalyst, CCDA, CCDP, CCIE, CCIP, CCNA, CCNP, CCSP, Cisco, the Cisco Certified Internetwork Expert logo, Cisco IOS, Cisco Press, Cisco Systems, Cisco Systems Capital, the Cisco Systems logo, Cisco Unity, Enterprise/Solver, EtherChannel, EtherFast, EtherSwitch, Fast Step, Follow Me Browsing, FormShare, GigaDrive, GigaStack, HomeLink, Internet Quotient, IOS, iPhone, IP/TV, iQ Expertise, the iQ logo, iQ Net Readiness Scorecard, iQuick Study, LightStream, Linksys, MeetingPlace, MGX, Networking Academy, Network Registrar, Packet, PIX, ProConnect, RateMUX, ScriptShare, SlideCast, SMARTnet, StackWise, The Fastest Way to Increase Your Internet Quotient, and TransPath are registered trademarks of Cisco Systems, Inc. and/or its affiliates in the United States and certain other countries.
All other trademarks mentioned in this document or Website are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (0612R)
© 2007 Cisco Systems, Inc. All rights reserved.
Printed in the USA on recycled paper containing 10% postconsumer waste.