Cisco 1000 Series Connected Grid Routers Security Software Configuration Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- June 27, 2014
Chapter: Zero Touch Deployment
Zero Touch Deployment
This chapter provides an high-level description of Zero Touch Deployment.
Zero Touch Deployment is an ease-of-use feature that automatically registers (enrolls) and distributes X.509 certificates and provisioning information over secure connections within a connected grid network. (See Figure 11-1.)
Figure 11-1 Zero Touch Deployment within a Cisco Connected Grid Network
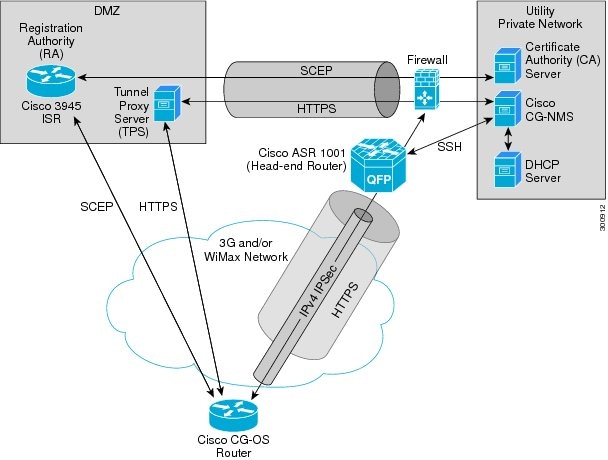
Figure 11-1 provides a high-level view of the systems and communication that might exist in a Utility connected grid network in which Zero Touch Deployment is in use.
In this example, the firewall provides separation between those items in the Utility public network (identified as DMZ) and its private network.
The Utility private network shows systems that might reside behind the firewall such as the
Cisco CG-NMS, the DHCP server, and the Certificate Authority (CA). The Tunnel Proxy Server (TPS) and Registration Authority (RA) might be located in the public network (DMZ).
After installing and powering on the Cisco CG-OS router on a pole top, it becomes active in the network and registers its certificate with the RA by employing the Simple Certificate Enrollment Protocol (SCEP). The RA (
Cisco 3945 ISR
), functioning as a CA proxy, obtains certificates for the
Cisco CG-OS router from the CA. Additionally, the Cisco CG-OS router establishes an HTTPS connection with the provisioning server (Cisco CG-NMS) through the TPS.
Cisco CG-NMS manages collection of all the information necessary to configure a tunnel between the Cisco CG-OS router and the head-end router (
Cisco ASR 1001
). The tunnel can be built to support
IPv4 traffic over IPSec, which is encapsulated within an HTTPS tunnel.
When the tunnel is active, the Cisco CG-OS router (after configuration) connects to the Utility network like a Virtual Private Network (VPN).

Tip For details on implementing Zero Touch Deployment within your network, please contact your
Cisco partner or Cisco system engineer.
 Feedback
Feedback