簡介
本檔案介紹在Nexus 7000/9000交換器上設定封鎖或過濾特定多點傳播流量的可能方法的不同方式。一個常見的例子是Microsoft實現的通用即插即用操作,它使用SSDP實現伺服器之間的通訊。
必要條件
需求
思科建議您瞭解使用PIM稀疏模式的任何源組播(ASM)在Nexus平台上的運作方式。
採用元件
本文中的資訊係根據以下軟體和硬體版本:
- 運行NXOS 7.3(4)D1(1)的Nexus 7K,帶F3/M3 LC
- 採用7.0(3)I7(9)或9.3(5)的Nexus N9K-C93180YC-EX/FX
附註:如果軟體/硬體不同,結果可能會有所不同。
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路運作中,請確保您瞭解任何指令可能造成的影響。
背景資訊
以下是所用的縮寫詞清單:
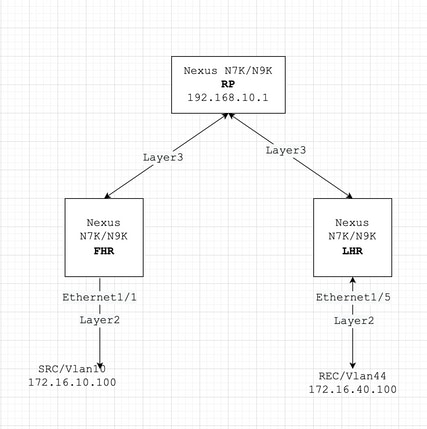
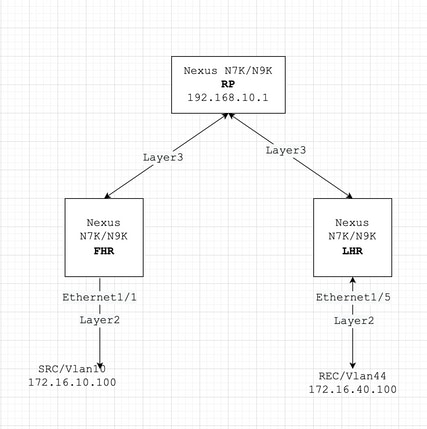
RP — 集結點
FHR — 第一跳路由器
LHR — 最後一跳路由器
SRC — 多點傳送來源
REC — 多點傳送接收器
PACL — 埠訪問清單
RACL — 路由存取清單
SVI — 交換虛擬介面
ACL — 訪問控制清單
設定
通用拓撲
組態設定範例
我們假設一下:
RP的IP地址是192.168.10.1
SRC的IP地址是172.16.10.100/32
SSDP組:239.255.255.250/239.255.255.253
現在,我們根據裝置的角色討論配置。例如FHR、LHR、RP等。
FHR — 通常組播源在此直接連線
1.過濾對現有RP的註冊。
ip pim rp-address 192.168.10.1 route-map filter-registration
!
Route-map filter-registration deny 5
match ip multicast source 172.16.10.100/32 group 239.255.255.250/32
// Above line is specific to SRC/GROUP pair
Route-map filter-registration deny 7
match ip multicast group 239.255.255.250/32
// Above line is for any SRC and specific group
!
Route-map filter-registration permit 100
Match ip multicast group 224.0.0.0/4
|
2.通過為SSDP組定義虛假RP(不存在,例如1.1.1.1)來過濾對RP的註冊;在本例中,FHR承擔RP的角色。
ip route 1.1.1.1/32 Null0
!
ip pim rp-address 1.1.1.1 route-map SSDP_groups
!
Route-map SSDP_groups permit 5
match ip multicast group 239.255.255.250/32
Route-map SSDP_groups permit 10
match ip multicast group 239.255.255.253/32
Route-map SSDP_groups deny 20
match ip multicast group 224.0.0.0/4
!
ip pim rp-address 192.168.10.1 route-map all_other_groups
!
Route-map all_other_groups deny 5
match ip multicast group 239.255.255.250/32
Route-map all_other_groups deny 10
match ip multicast group 239.255.255.253/32
Route-map all_other_groups permit 20
match ip multicast group 224.0.0.0/4
|
驗證:
Nexus9K_OR_N7K# show ip pim rp
PIM RP Status Information for VRF "default"
BSR disabled
Auto-RP disabled
BSR RP Candidate policy: None
BSR RP policy: None
Auto-RP Announce policy: None
Auto-RP Discovery policy: None
RP: 192.168.10.1, (0),
uptime: 00:00:27 priority: 0,
RP-source: (local), group-map: Filter-registration,
group rangs:
224.0.0.0/4
239.255.255.253/32 (deny)
239.255.255.250/32 (deny)
Nexus9K_OR_N7K# show ip mroute
IP Multicast Routing Table for VRF "default"
(172.16.10.100/32, 239.255.255.250/32), uptime: 00:04:12, ip pim
Incoming interface: Vlan10, RPF nbr: 172.16.10.100
Outgoing interface list: (count: 0)
Nexus9K_OR_N7K# show system internal mfwd event-history pkt
pkt events for MCASTFWD process
2021 Jan 1 11:11:41.792316 mcastfwd [21914]: [21933]: Create state for (172.16.10.100, 239.255.255.250)
Nexus9K_OR_N7K # show ip pim internal event-history null-register
2021 Jan 01 11:15:19.095711: E_DEBUG pim [21935]: Null Register not sent for (172.16.10.100/32, 239.255.255.250/32) yes
|
此輸出確認FHR未向RP註冊流。
LHR — 通常多播REC在此直接連線
3.對輸入SVI(REC所在的位置)應用IGMP策略。 此處的想法是從REC過濾SSDP組的IGMP成員報告。
ip pim rp-address 192.168.10.1 group-list 224.0.0.0/4
!
route-map filter-SSDP-joins deny 5
match ip multicast group 239.255.255.250/32
route-map filter-SSDP-joins deny 6
match ip multicast group 239.255.255.253/32
route-map filter-SSDP-joins permit 100
match ip multicast group 224.0.0.0/4
!
Interface VlanXX
ip igmp report-policy filter-SSDP-joins
|
驗證:
Nexus9K_OR_N7K (config)# show ip mroute 239.255.255.250
IP Multicast Routing Table for VRF "default"
Group not found
!
Nexus9K_OR_N7K (config)# show ip igmp snooping groups vlan 44
Type: S - Static, D - Dynamic, R - Router port, F - Fabricpath core port
Vlan Group Address Ver Type Port list
44 */* - R Vlan44
44 239.255.255.250 v2 D Eth1/5
!
Nexus9K_OR_N7K (config)# show ip igmp internal event-history debugs
debugs events for IGMP process
2021 Jan 1 11:52:21.277915 igmp [1125]: : Filtered group 239.255.255.250
2021 Jan 1 11:52:21.277903 igmp [1125]: : Received v2 Report for 239.255.255.250 from 172.16.44.100 (Vlan44)
|
此輸出確認已過濾IGMP成員身份報告並且未將加入(*,G)傳送到RP。
PIM — 啟用路由器充當FHR/LHR
根據您的要求,您可以使用選項1、2和3的組合。
舉例來說:
4.對現有RP(FHR角色)進行篩選器註冊:
ip pim rp-address 192.168.10.1 route-map filter-registration
!
Route-map filter-registration deny 5
match ip multicast source 172.16.10.100/32 group 239.255.255.250/32
Route-map filter-registration deny 7
match ip multicast group 239.255.255.250/32
!
Route-map filter-registration permit 100
Match ip multicast group 224.0.0.0/4
|
5. IGMP策略從REC(LHR角色)中篩選IGMP成員報告。
ip pim rp-address 192.168.10.1 group-list 224.0.0.0/4
!
route-map filter-SSDP-joins deny 5
match ip multicast group 239.255.255.250/32
route-map filter-SSDP-joins deny 6
match ip multicast group 239.255.255.253/32
route-map filter-SSDP-joins permit 100
match ip multicast group 224.0.0.0/4
!
Interface VlanXX
ip igmp report-policy filter-igmp-joins
|
驗證:
與前文提及的C點和D點進行的核查幾乎相同。
Show ip mroute
Show ip pim rp
Show ip pim internal event-history join-prune
Show ip igmp internal event-history debugs
|
RP — 這是集結點
6.阻止從FHR註冊SSDP組的註冊策略。
ip pim rp-address 192.168.10.1 group-list 224.0.0.0/4
ip pim register-policy all_groups
!
Route-map all_groups deny 5
match ip multicast group 239.255.255.250/32
Route-map all_groups deny 10
match ip multicast group 239.255.255.253/32
Route-map all_groups permit 20
match ip multicast group 224.0.0.0/4
|
驗證:
Nexus9K_OR_N7K (config)# show ip mroute 239.255.255.250
IP Multicast Routing Table for VRF "default"
Group not found
!
Nexus9K_OR_N7K (config)# show ip pim internal event-history data-register-receive
2021 Jan 08 03:33:06.353951: E_DEBUG pim [1359]: Register disallowed by policy
2021 Jan 08 03:33:06.353935: E_DEBUG pim [1359]: Received DATA Register from 172.16.10.1 for (172.16.10.100/32, 239.255.255.250/32) (pktlen 1028)
2021 Jan 08 03:29:42.602744: E_DEBUG pim [1359]: Add new route (172.16.10.100/32, 239.1.1.1/32) to MRIB, multi-route TRUE
F241.01.13-C93180YC-EX-1(config)# show ip pim internal event-history null-register
2021 Jan 08 03:35:40.966617: E_DEBUG pim [1359]: Send Register-Stop to 172.16.10.1 for (172.16.10.100/32, 239.255.255.250/32)
2021 Jan 08 03:35:40.966613: E_DEBUG pim [1359]: Register disallowed by policy
2021 Jan 08 03:35:40.966597: E_DEBUG pim [1359]: Received NULL Register from 172.16.10.1 for (172.16.10.100/32, 239.255.255.250/32) (pktlen 20)
|
此輸出確認RP正在阻止組239.255.255.250的註冊。
7.在RP上應用合併修剪策略 — 僅適用於SSDP組的pim(*,G)聯接和(S,G)聯接。
ip pim rp-address 192.168.10.1 group-list 224.0.0.0/4
ip pim register-policy all_groups
!
Route-map all_groups deny 5
match ip multicast group 239.255.255.250/32
Route-map all_groups deny 10
match ip multicast group 239.255.255.253/32
Route-map all_groups permit 20
match ip multicast group 224.0.0.0/4
!
Interface Ethernet/Y
ip pim sparse-mode
ip pim jp-policy all_groups
|
驗證:
Nexus9K_OR_N7K # show ip mroute 239.255.255.253
IP Multicast Routing Table for VRF "default"
Group not found
!
F241.01.13-C93180YC-EX-1# show ip pim internal event-history join-prune
2021 Jan 08 03:53:41.643419: E_DEBUG pim [1359]: Join disallowed by inbound JP policy
|
此輸出確認(*,G)PIM連線被RP阻止。
配置組播的保留硬體條目
儘管A、B或C節中討論了所有備選方案;阻止FHR、LHR或FHR/LHR在RP處註冊流,或阻止分別向RP傳送PIM加入(*,G);仍可建立mroute或snooping條目,該條目會使用組播HW條目。
附註:如果已設定VPC,則可以在輸入SVI或第2層介面/連線埠通道/VPC連線埠通道上使用RACL或PACL。如果SRC/REC噴出到不同的VLAN或L2介面,則也意味著需要將RACL或PACL應用到所有這些介面上。但是,根據硬體/軟體(主要由於硬體限制),結果可能會有所不同。
PACL
在入口第2層埠、埠通道或VPC埠通道上配置PACL以阻止SSDP流量或在FHR上建立(S, G)條目。
附註:根據使用的硬體(例如Nexus N9000),應用PACL時可能需要先雕刻TCAM(需要重新載入)。
舉例來說:
ip access-list BlockAllSSDP
Statistics per-entry
10 deny ip any 239.255.255.250/32
20 deny ip any 239.255.255.253/32
30 permit ip any any
!
Interface Ethernet X/Y
Or
Interface port-channel XX
ip port-access group BlockAllSSDP in
|
驗證:
F241.01.13-C93180YC-EX-1# sh ip mroute 239.255.255.250
IP Multicast Routing Table for VRF "default"
Group not found
!
show ip access-lists BlockAllSSDP
IP access list BlockAllSSDP
statistics per-entry
10 deny ip any 239.255.255.250/32 [match=3] -> Drop counters
20 deny ip any 239.255.255.253/32 [match=0]
30 permit ip any any [match=0]
|
由於兩個多點傳播流量/IGMP成員連線埠均透過PACL封鎖,因此您不會看到任何窺探、mroute專案。實際上是PACL丟棄了這兩者。
RACL
您可以在SRC所在的輸入SVI上配置RACL,但取決於使用的軟體/硬體;(S, G)條目仍然可以建立,或者流量可以轉發到其他本地VLAN。
ip access-list BlockAllSSDP
Statistics per-entry
10 deny ip any 239.255.255.250/32
20 deny ip any 239.255.255.253/32
30 permit ip any any
!
Interface VlanXX
ip port-access group BlockAllSSDP in
|
驗證:
它與PACL基本相同,但RACL選項不能提供與PACL相同的結果;在前面也提到了它的硬體限制。
COPP
也可以在COPP處阻止SSDP。以下是組態範例:
class-map type control-plane match-any nossdp
match access-group name nossdp
policy-map type control-plane nossdp
class nossdp
police cir 0 bps bc 0 bytes conform transmit violate drop control-plane dynamic
service-policy-dyn input nossdp
!
ip access-list nossdp
statistics per-entry
10 permit ip any 239.255.255.250/32
20 permit igmp any 239.255.255.250/32
30 permit pim any 239.255.255.250/32
|
全域多點傳送邊界
從Cisco NX-OS版本10.2(1)開始,支援全域性邊界組播配置。
您需要設定{ip | ipv6} multicast group-range prefix-list <prefix-list-name>命令在VRF配置模式下定義全域性組播邊界允許或拒絕的IP組播組和通道的全域性範圍。此命令用於禁用路由器上所有介面的未授權組或通道的組播協定操作和流量轉發。字首清單配置邊界。下面提供了示例配置:
vrf context enterprise
ip multicast group-range prefix-list test
|
https://www.cisco.com/c/en/us/td/docs/dcn/nx-os/nexus9000/102x/configuration/multicast-routing/cisco-nexus-9000-series-nx-os-multicast-routing-configuration-guide-release-102x/m-overview.html#concept_29A33F30E7F84F7AA20C8D7D1A22ED98
 意見
意見