簡介
本文檔介紹如何配置裝置感測器,以便其在ISE上用於分析目的。
必要條件
需求
思科建議您瞭解以下主題:
- Radius通訊協定
- 思科探索通訊協定(CDP)和連結層探索通訊協定(LLDP)
- 思科身分識別服務引擎(ISE)
- Cisco Catalyst交換器9300
採用元件
本文中的資訊係根據以下軟體和硬體版本:
- Cisco ISE版本3.4補丁3
- Cisco Catalyst交換器9300-48P版本17.12.4
- Cisco IP電話8811版本12.8.1
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路運作中,請確保您瞭解任何指令可能造成的影響。
背景資訊
裝置感測器是接入裝置的一項功能,用於使用思科發現協定(CDP)、鏈路層發現協定(LLDP)和動態主機配置協定(DHCP)等協定從網路裝置收集原始終端資料。 端點資料有助於完成網路接入裝置的配置功能。收集資訊後,可以將其封裝在radius記帳資料包中,並傳送到分析伺服器,在本文中,該伺服器將是ISE。

附註:裝置感測器僅分析距離NAD(網路訪問裝置)一跳的裝置。
收集資訊後,可以將其封裝在radius記帳中,並傳送到分析伺服器。在本文中,ISE用作分析伺服器。
設定
步驟1.標準AAA配置
若要設定驗證、授權及記帳(AAA),請參閱以下步驟:
- 使用aaa new-model命令啟用AAA,並在交換機上全域性啟用802.1X
- 配置Radius伺服器並啟用動態授權(授權更改 — CoA)
- 啟用CDP和LLDP協定。新增switchport身份驗證配置
-
新增switchport身份驗證配置
!
aaa new-model
!
!
aaa group server radius ISE-GROUP
server name ise
!
aaa authentication dot1x default group radius
aaa authorization network default group radius
aaa accounting update newinfo
aaa accounting dot1x default start-stop group radius
!
!
aaa server radius dynamic-author
client server-key Krakow123
!
dot1x system-auth-control
!
lldp run
cdp run
!
interface GigabitEthernet1/0/1
description IP_Phone
switchport mode access
switchport voice vlan 101
authentication event fail action next-method
authentication host-mode multi-domain
authentication order dot1x mab
authentication priority dot1x mab
authentication port-control auto
mab
dot1x pae authenticator
dot1x timeout tx-period 2
spanning-tree portfast
!
radius server ise
address ipv4 auth-port 1812 acct-port 1813
key
!

注意:必須配置交換機以將思科供應商特定屬性(VSA)傳送到ISE。
可通過配置以下命令在記帳資料包內部傳送這些屬性:
radius-server vsa send accounting
步驟2.配置裝置感測器
1.確定需要來自CDP/LLDP的哪些屬性才能分析裝置。對於Cisco IP電話8811,您可以使用以下內容:
- LLDP SystemDescription屬性
- CDP CachePlatform屬性
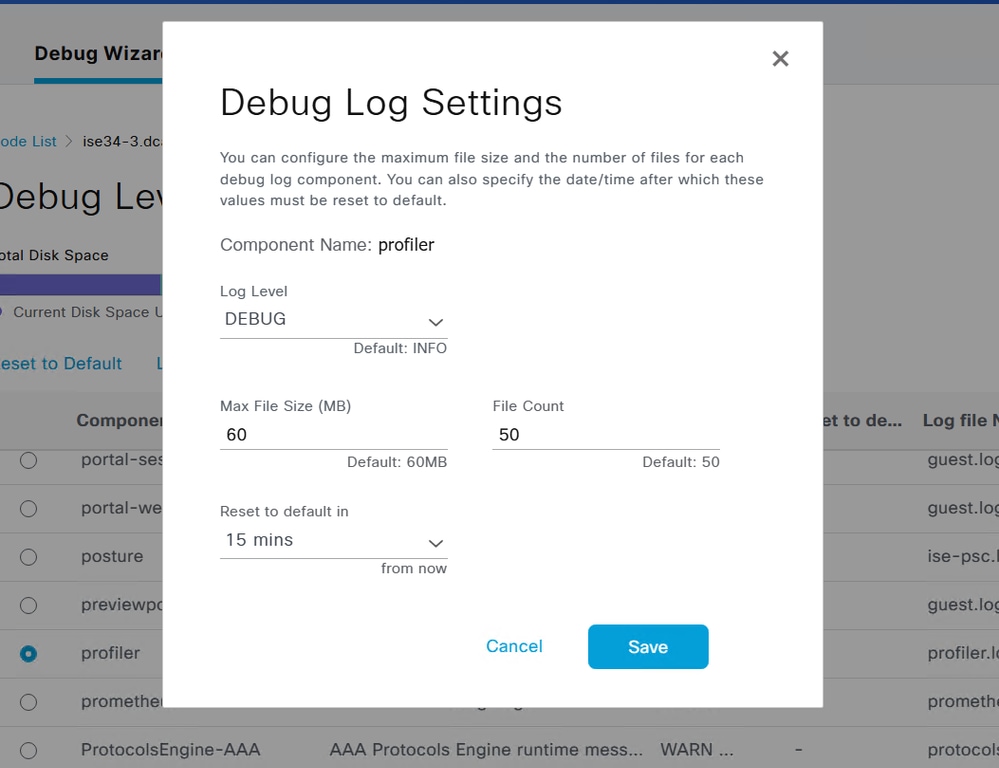
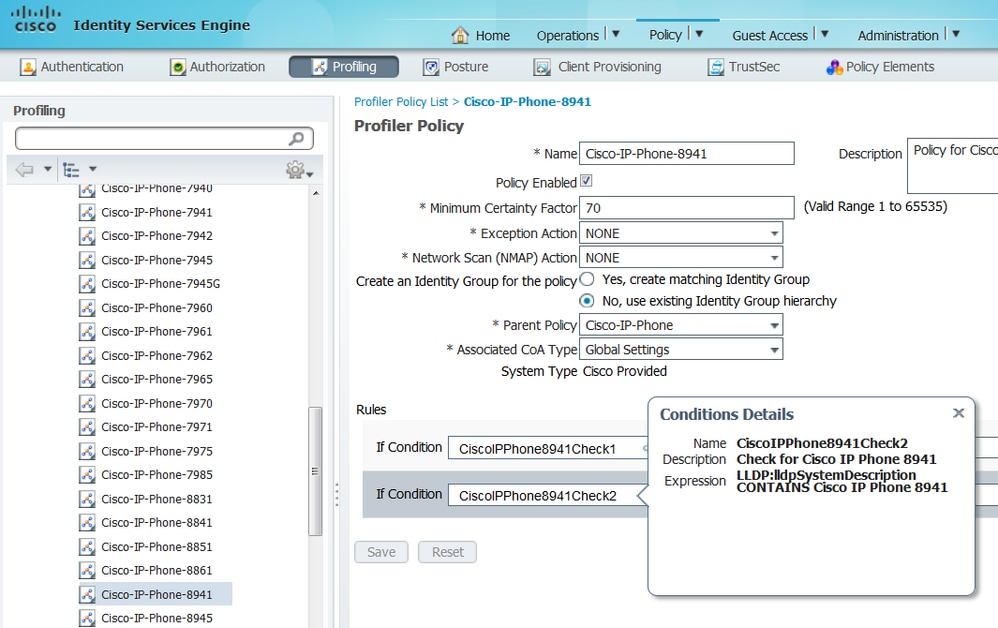
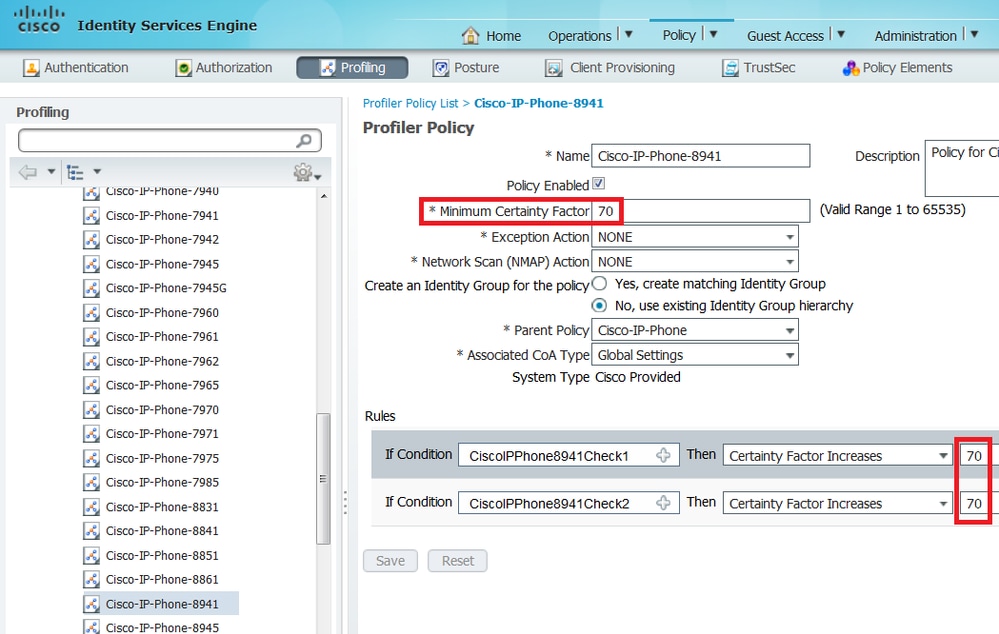
您可以通過檢查Profiler策略來驗證用於分析裝置的屬性。為此,您可以導航到Work Centers > Profiler > Profiling Policies,然後選擇要匹配的分析策略。
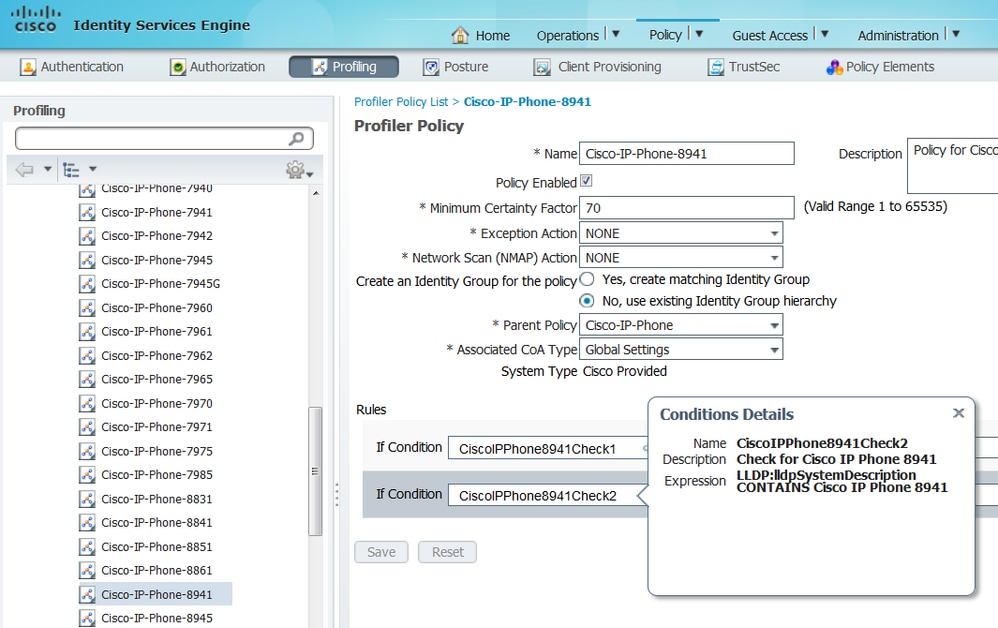
從下面的螢幕截圖中,我們可以看到,將終端描述為Cisco-IP-Phone-8811所需的最小確定性工廠為70。因此,由於這兩個屬性提供的確定性工廠增加70,因此僅獲得其中一個屬性就足夠了:
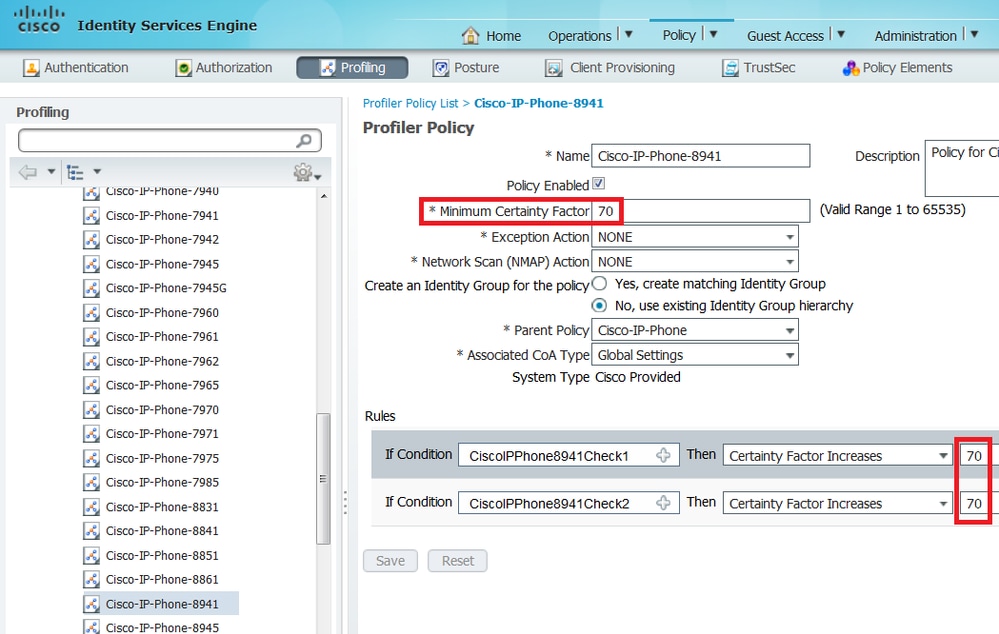

註:要分析為特定的Cisco IP電話,您必須滿足所有父配置檔案的最低條件。這意味著分析器必須匹配思科裝置(最小確定係數10)和思科IP電話(最小確定係數20)。 雖然探查器匹配這兩個配置檔案,但由於每個IP電話型號的最小確定係數為70,因此仍必須將其描述為特定的Cisco IP電話。裝置將分配給具有最高確定係數的配置檔案。
2.配置兩個篩選器清單:一個用於CDP,另一個用於LLDP。這些指示必須在Radius記帳消息中包含哪些屬性。此步驟是可選的。
3.為CDP和LLDP建立兩個filter-specs。在filter-spec中,您可以指明必須包括在記帳消息中或排除的屬性清單。在示例中,包括以下屬性:
如果需要,可以配置通過Radius傳輸到ISE的其他屬性。此步驟也是可選的。
4.添加device-sensor notify all-changes命令,以在當前會話新增、修改或刪除TLV時觸發更新。
5.為實際傳送通過裝置感測器功能收集的資訊,您必須使用命令device-sensor accounting明確告知交換機完成此操作。
!
device-sensor filter-list cdp list cdp-list
tlv name device-name
tlv name platform-type
!
device-sensor filter-list lldp list lldp-list
tlv name system-description
!
device-sensor filter-spec lldp include list lldp-list
device-sensor filter-spec cdp include list cdp-list
!
device-sensor accounting
device-sensor notify all-changes
!
步驟3.在ISE上配置分析
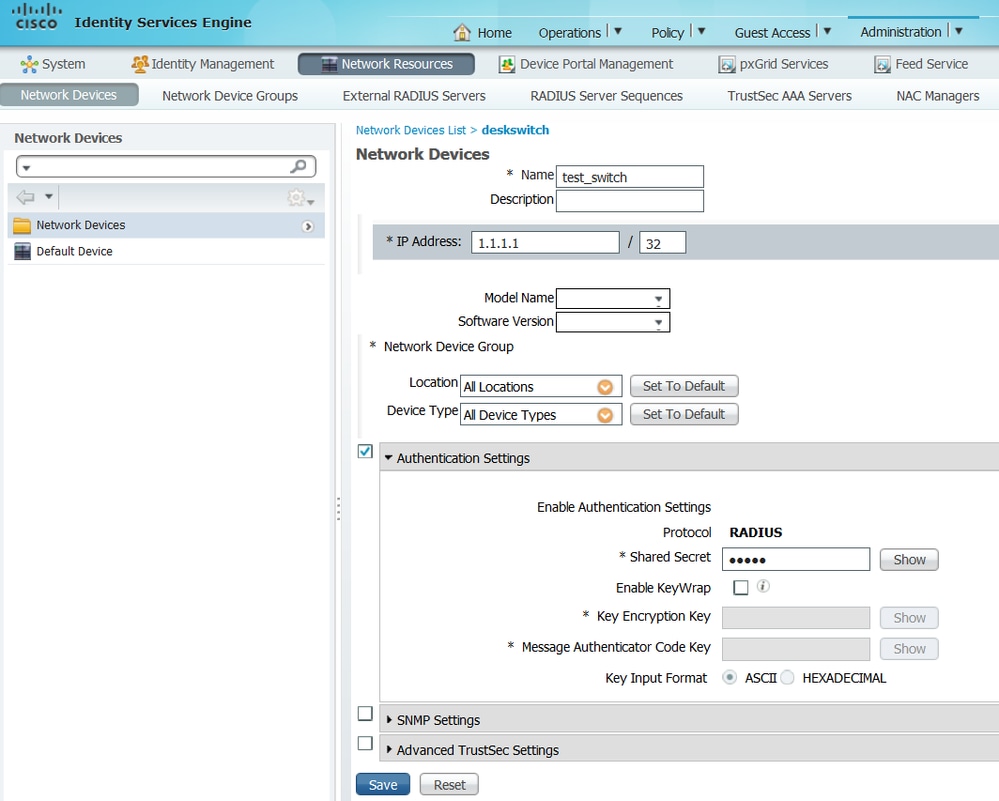
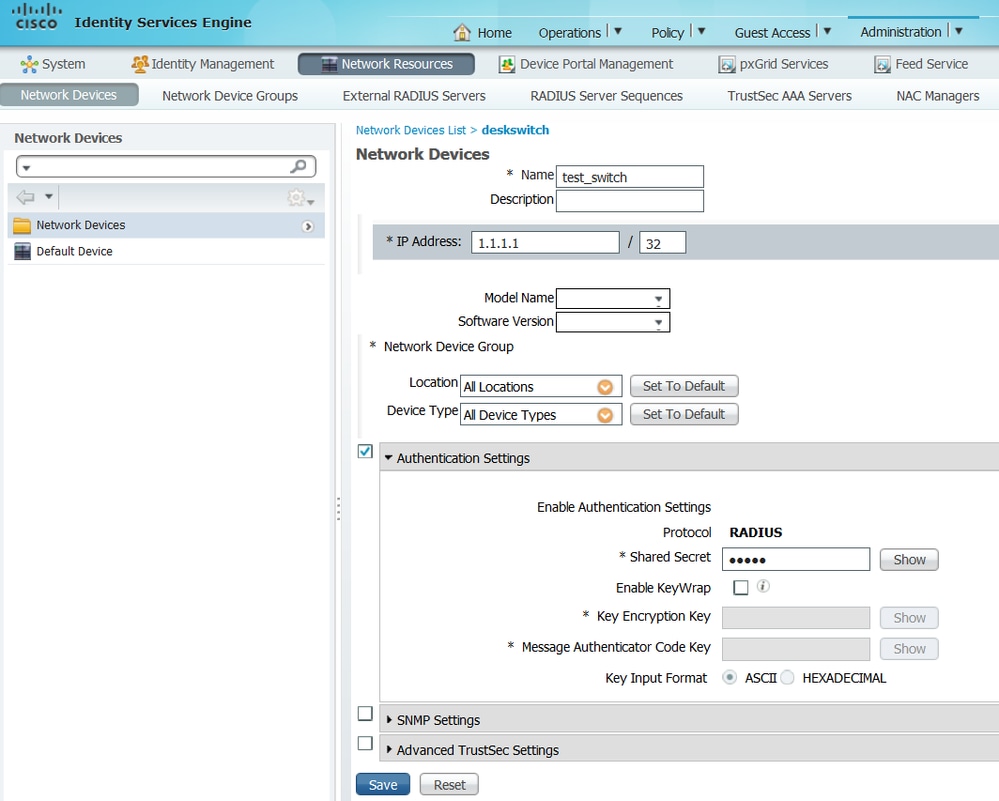
1.在Administration > Network Resources > Network Devices中,將交換機新增為網路裝置。在身份驗證設定中,使用交換機的radius伺服器金鑰作為共用金鑰:
2. 在ISE節點上啟用分析服務。為此,請轉到管理>系統>部署,選擇ISE節點,然後在「策略服務」頁籤上啟用分析服務選項。如果您需要對多個PSN進行分析,則可以為其中的每一個啟用此服務。但是,請記住,新增的探測越多,啟用分析服務的節點越多,對效能的打擊就越大,因此要明智地啟用它們。
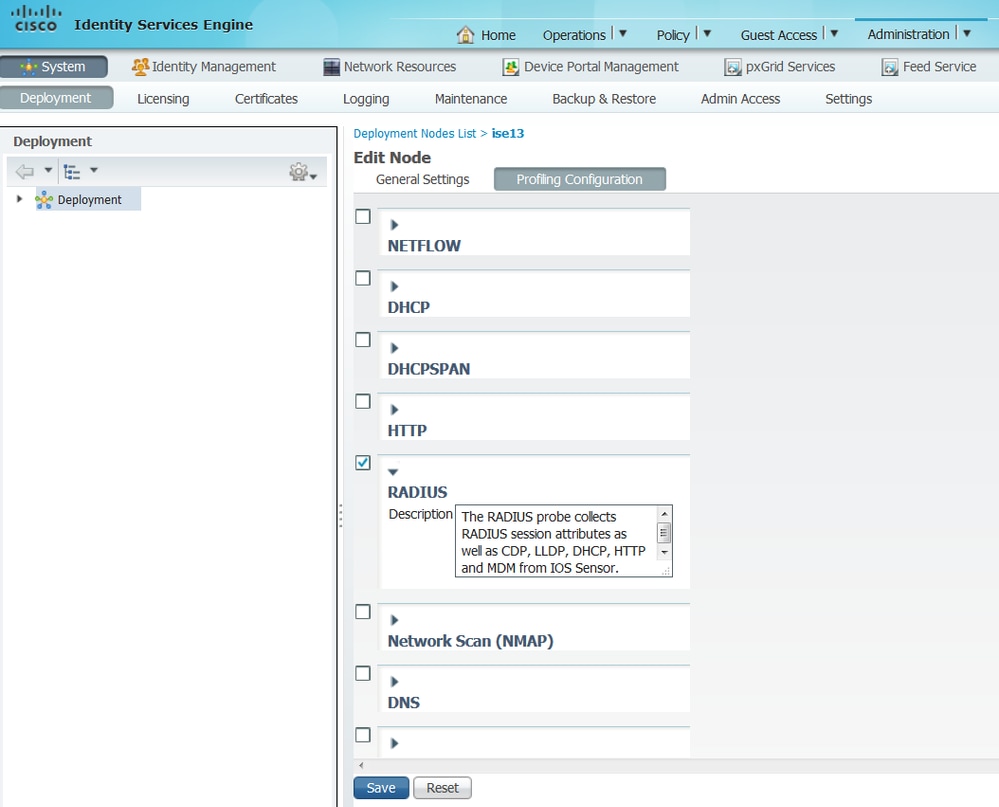
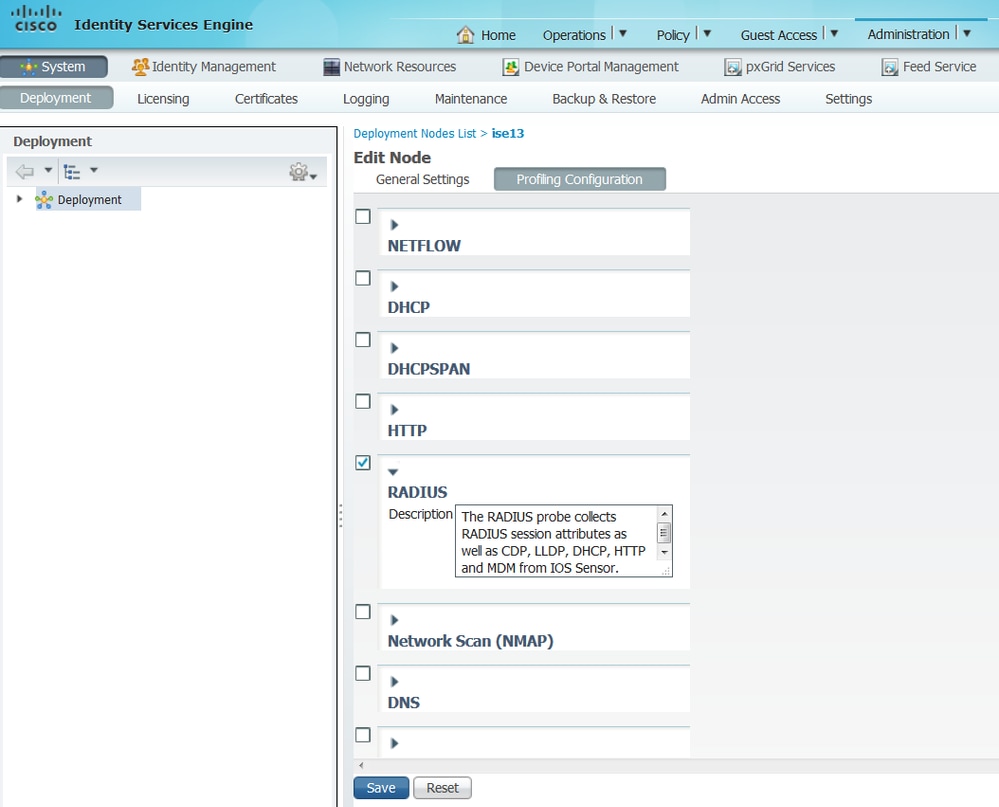
3. 在分析節點上啟用Radius探測。為此,請導航到Administration > System > Deployment,選擇ISE節點,然後按一下Profiling Configuration頁籤。
4.將CoA(授權變更)型別設定為Reauth,以在分析端點時強制重新驗證。此外,請確保選中了端點屬性過濾器。為此,請導航到管理>系統>設定>分析。

附註:最佳做法是在生產部署中啟用端點屬性篩選器,以避免在收集太多不必要的分析器資料時出現效能問題。要將某個屬性新增到當前不存在的allowlist中,可以建立使用該屬性的新Profiler Condition and Policy。該屬性將自動新增到已儲存和已複製屬性的白名單中。
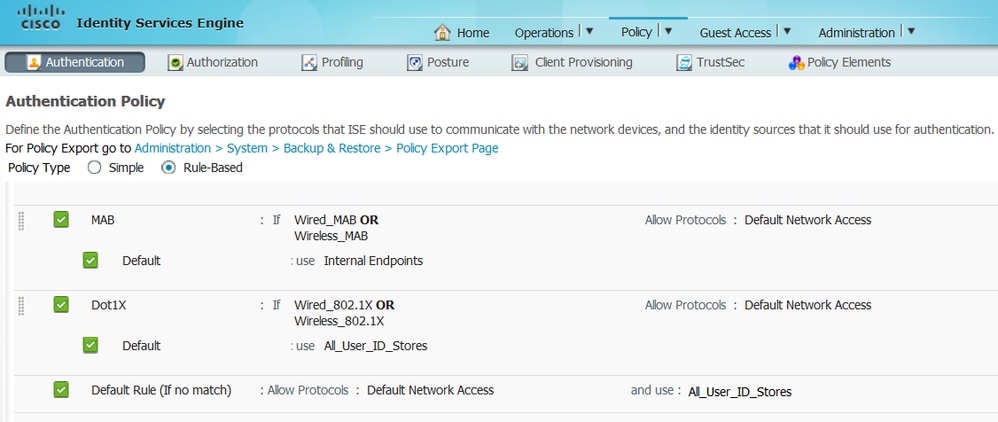
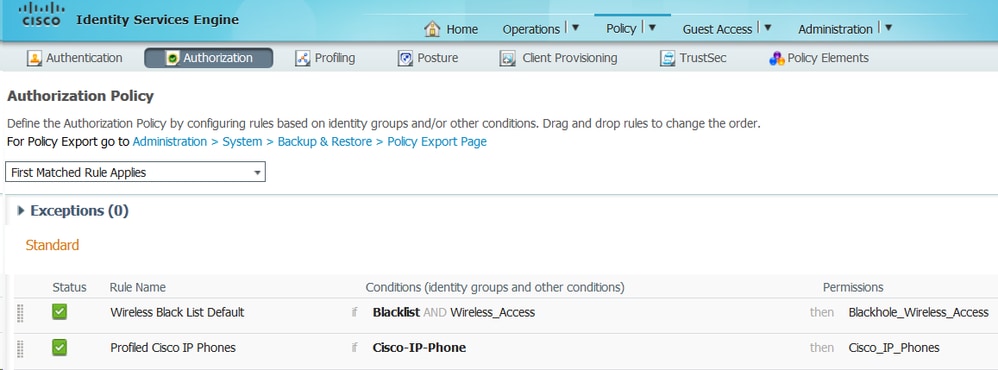
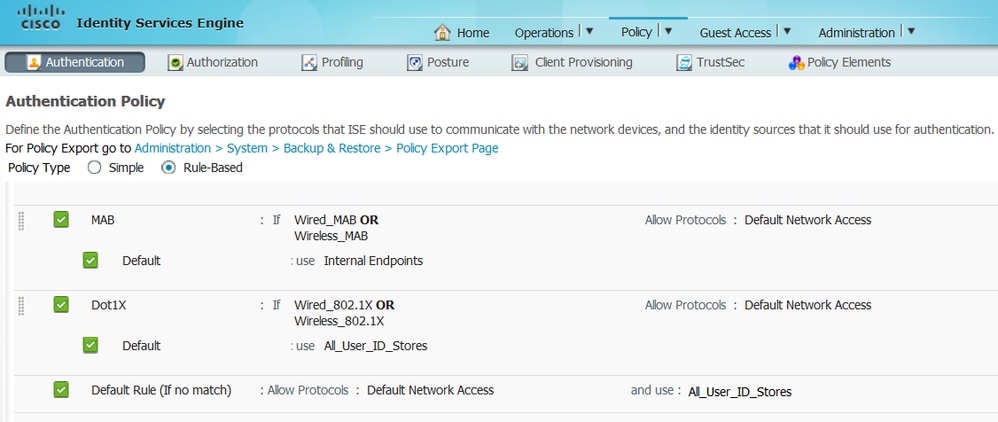
5. 配置ISE身份驗證規則:
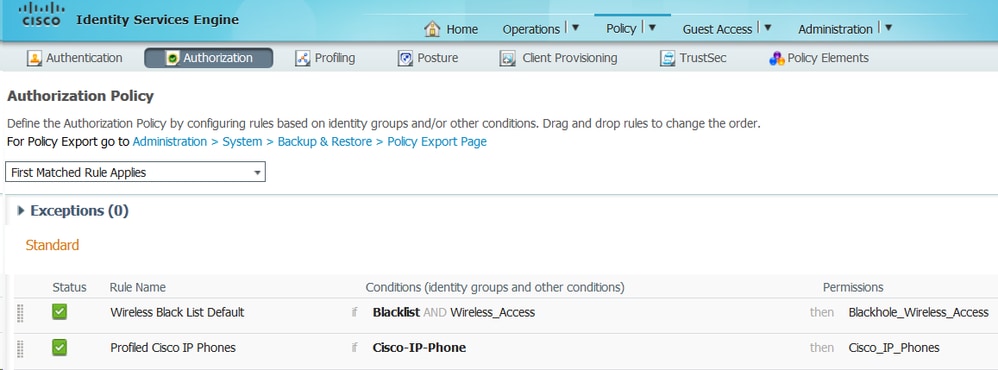
6. 配置ISE授權規則。使用已分析的Cisco-IP-Phone規則,該規則在ISE上預先配置:
您可以配置將充當catch策略的授權策略,這將允許終端獲得網路授權(有限訪問),以確保在記帳資料包中傳送屬性。此外,請建立另一個策略,在裝置分析完畢後進行匹配,確保裝置可以訪問網路中的必要資源。
驗證
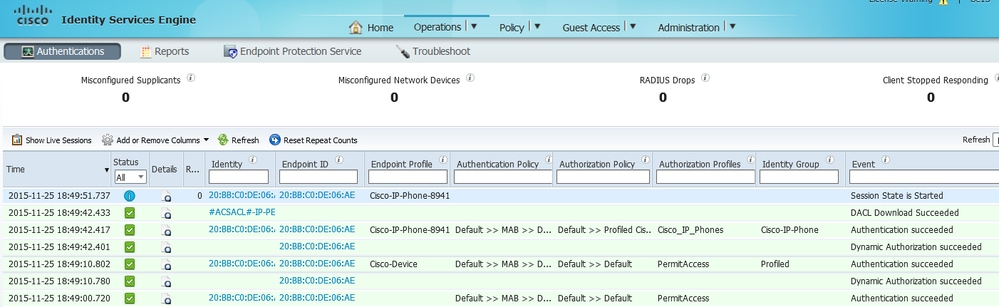
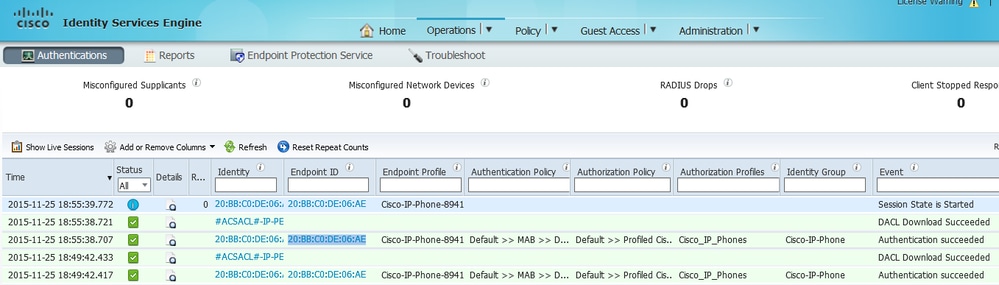
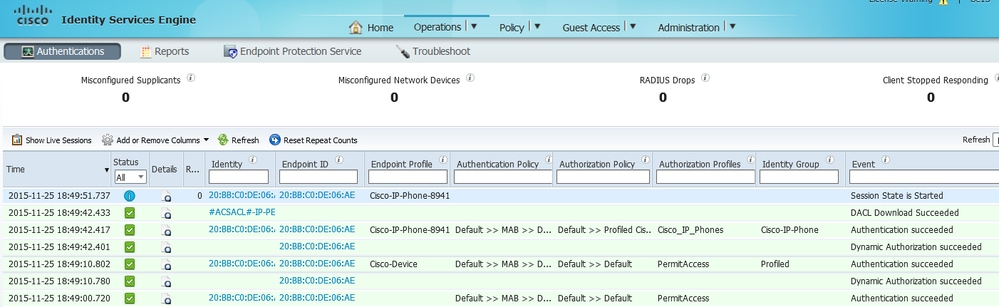
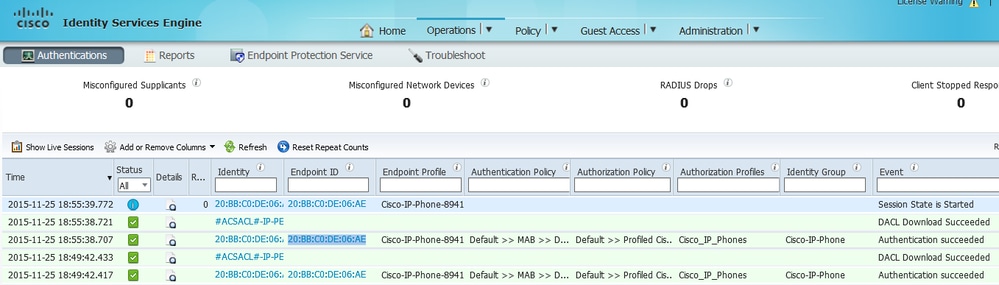
若要驗證分析是否正常工作,請參閱操作> Radius > Live Logs on ISE:
首先,身份驗證預期會失敗,因為我們在交換機上將身份驗證方法順序配置為dot1x,後跟MAB。因此,在dot1x身份驗證失敗後,IP電話嘗試使用MAB進行身份驗證,並且身份驗證在下午02:36:14成功。在此即時日誌中,我們可以看到裝置被分析為Cisco裝置,因為OUI包含「Cisco」一詞,與預定義的思科裝置分析策略相匹配。然後,由於裝置可以訪問網路,CDP和LLDP屬性將在Radius Accounting資料包中傳送。因此,在02:36:15 pm,裝置被分析並且ISE傳送CoA以強制終端重新進行身份驗證。成功執行CoA後,我們可以看到裝置會驗證進入網路,並達到正確的授權策略,該策略僅用於Cisco IP電話。
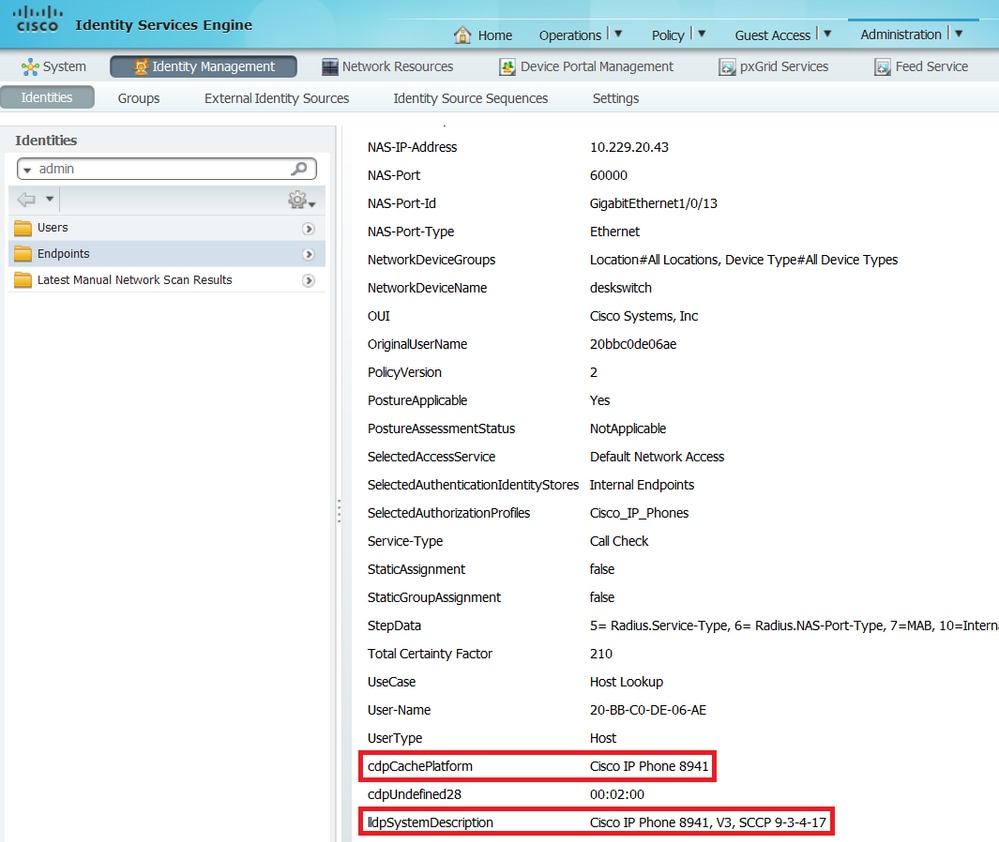
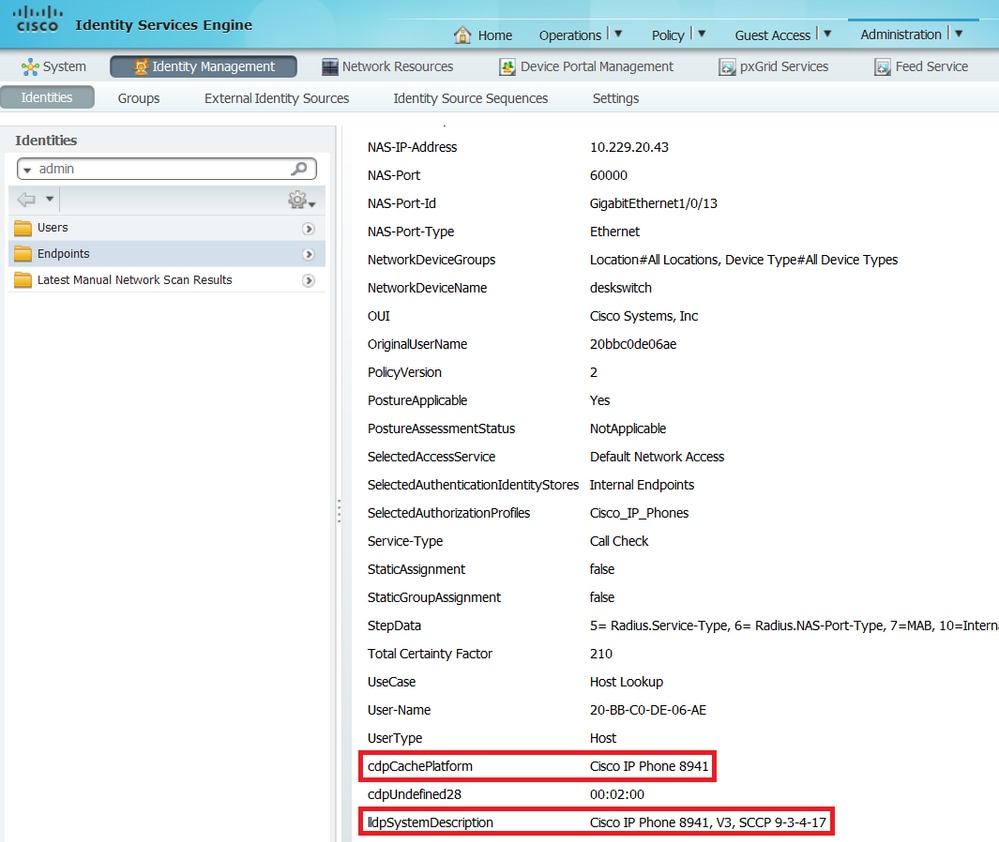
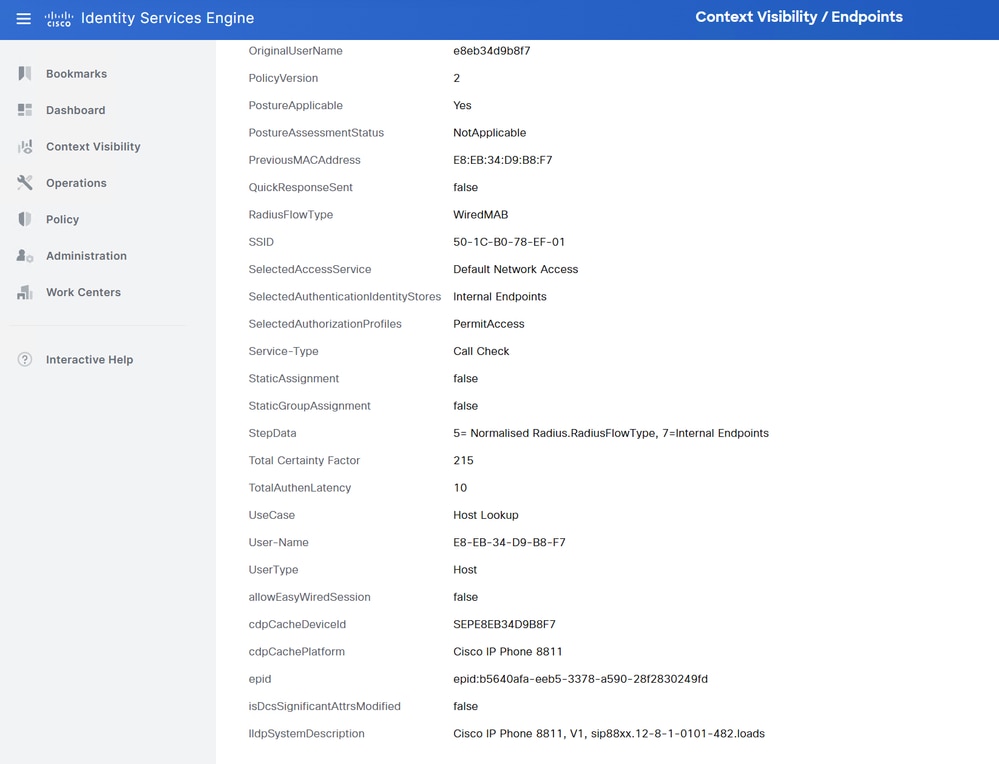
在Administration > Identity Management > Identities > Endpoints中,可以按測試的終端MAC地址進行過濾,並且您可以檢視Radius探測收集了何種屬性及其值:
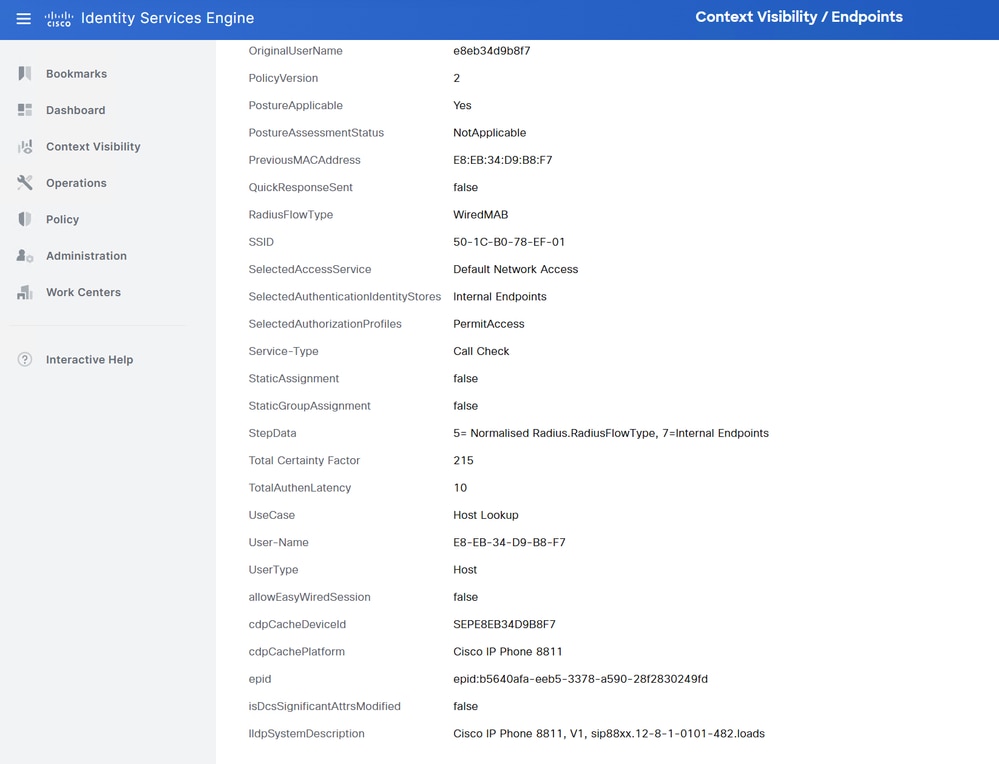
您可以看到,在此場景中計算的總確定性因子為215。這是因為端點還匹配思科裝置配置檔案(總確定係數為30)和思科IP電話配置檔案(總確定係數為45)。 此外,分析器還匹配了配置檔案Cisco-IP-Phone-8811中的兩個條件,此配置檔案的確定係數為140(根據分析策略,每個屬性為70)。 總結一下:30+45+70+70=215。
疑難排解
步驟1.檢驗CDP/LLDP收集的資訊
Switch#show cdp neighbors GigabitEthernet1/0/1 details
-------------------------
Device ID: SEPE8EB34D9B8F7
Entry address(es):
Platform: Cisco IP Phone 8811, Capabilities: Host Phone Two-port Mac Relay
Interface: GigabitEthernet1/0/1, Port ID (outgoing port): Port 1
Holdtime : 151 sec
Second Port Status: Down
Version :
sip88xx.12-8-1-0101-482.loads
advertisement version: 2
Peer Source MAC: e8eb.34d9.b8f7
Duplex: full
Power drawn: 6.086 Watts
Power request id: 63418, Power management id: 4
Power request levels are:6086 0 0 0 0
Switch#show lldp neighbors GigabitEthernet1/0/1 details
------------------------------------------------
Local Intf: Gi1/0/1
Local Intf service instance: -
Chassis id: 0.0.0.0
Port id: E8EB34D9B8F7:P1
Port Description: SW PORT
System Name: SEPE8EB34D9B8F7
System Description:
Cisco IP Phone 8811, V1, sip88xx.12-8-1-0101-482.loads
Time remaining: 175 seconds
System Capabilities: B,T
Enabled Capabilities: B,T
Management Addresses - not advertised
Auto Negotiation - supported, enabled
Physical media capabilities:
1000baseT(FD)
100base-TX(FD)
100base-TX(HD)
10base-T(FD)
10base-T(HD)
Media Attachment Unit type: 30
Vlan ID: - not advertised
Peer Source MAC: e8eb.34d9.b8f7
MED Information:
MED Codes:
(NP) Network Policy, (LI) Location Identification
(PS) Power Source Entity, (PD) Power Device
(IN) Inventory
H/W revision: 1
F/W revision: sb2388xx.BE-01-027.sbn size=-1
S/W revision: sip88xx.12-8-1-0101-482.loads
Serial number: FCH25023CZN
Manufacturer: Cisco Systems, Inc.
Model: CP-8811
Capabilities: NP, PD, IN
Device type: Endpoint Class III
Network Policy(Voice): VLAN 101, tagged, Layer-2 priority: 5, DSCP: 46
Network Policy(Voice Signal): VLAN 101, tagged, Layer-2 priority: 4, DSCP: 32
PD device, Power source: PSE, Power Priority: Unknown, Wattage: 5.9
Location - not advertised
Total entries displayed: 1
如果您看不到收集的任何資料,請驗證以下情況:
OCEAN#sh access-session int gig1/0/1 det
Interface: GigabitEthernet1/0/1
IIF-ID: 0x172041DB
MAC Address: e8eb.34d9.b8f7
IPv6 Address: Unknown
IPv4 Address: Unknown
User-Name: E8-EB-34-D9-B8-F7
Status: Authorized
Domain: DATA
Oper host mode: multi-domain
Oper control dir: both
Session timeout: N/A
Common Session ID: F24D300A0000001B9A787BED
Acct Session ID: 0x0000012b
Handle: 0x79000011
Current Policy: POLICY_Gi1/0/1
Local Policies:
Service Template: DEFAULT_LINKSEC_POLICY_SHOULD_SECURE (priority 150)
Security Policy: Should Secure
Security Status: Link Unsecured
Server Policies:
Method status list:
Method State
dot1x Stopped
mab Authc Success
- 檢查CDP和LLDP協定是否已啟用。檢查是否存在任何有關CDP/LLDP的非預設命令,以及這些命令如何影響從端點進行屬性檢索。
Switch#show running-config all | include cdp run
cdp run
Switch#show running-config all | include lldp run
lldp run
- 在終端配置指南中驗證它是否支援CDP/LLDP等。
步驟2.檢查裝置感測器快取
Switch#show device-sensor cache interface GigabitEthernet1/0/1
Device: e8eb.34d9.b8f7 on port GigabitEthernet1/0/1
----------------------------------------------------------------------------
Proto Type:Name Len Value Text
LLDP 6:system-description 56 0C 36 43 69 73 63 6F 20 49 .6Cisco I
50 20 50 68 6F 6E 65 20 38 P Phone 8
38 31 31 2C 20 56 31 2C 20 811, V1,
73 69 70 38 38 78 78 2E 31 sip88xx.1
32 2D 38 2D 31 2D 30 31 30 2-8-1-010
31 2D 34 38 32 2E 6C 6F 61 1-482.loa
64 73 ds
CDP 6:platform-type 23 00 06 00 17 43 69 73 63 6F ....Cisco
20 49 50 20 50 68 6F 6E 65 IP Phone
20 38 38 31 31 8811
CDP 1:device-name 19 00 01 00 13 53 45 50 45 38 ....SEPE8
45 42 33 34 44 39 42 38 46 EB34D9B8F
37 7
如果您在此欄位中未看到任何資料或資訊不完整,請驗證device-sensor命令;特別是過濾器清單和過濾器規格。
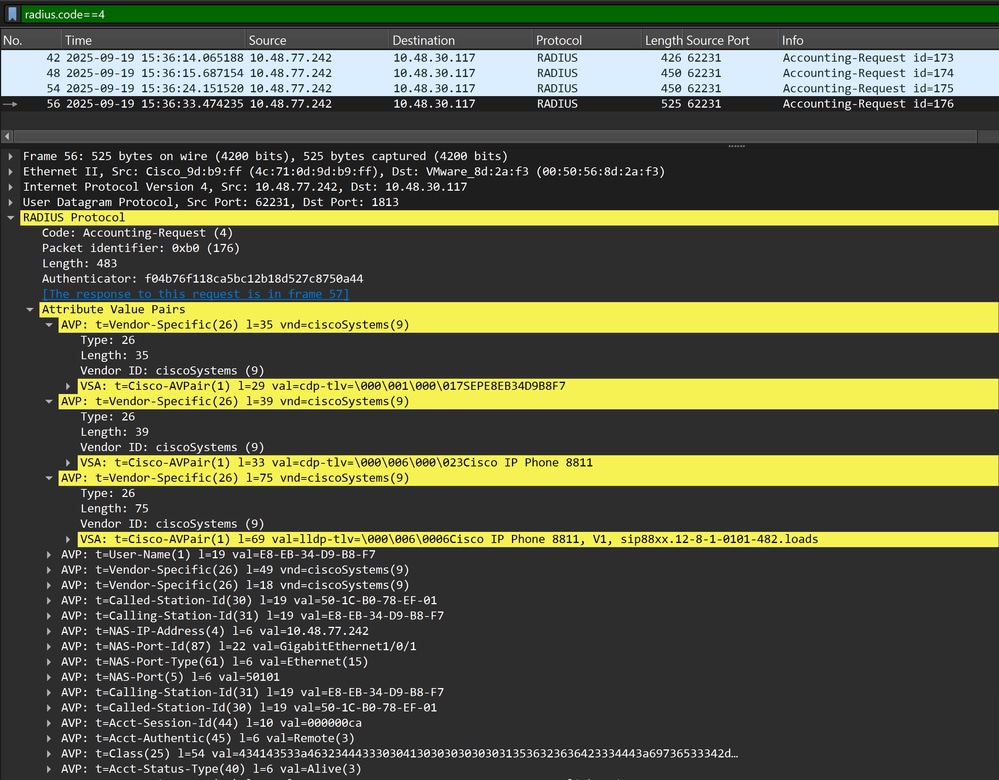
步驟3.檢查Radius計費中是否存在屬性
可以在交換機上使用debug radius命令或在交換機和ISE之間執行資料包捕獲。
Radius偵錯
Switch#debug radius
Switch#set platform software trace smd switch active R0 dot1x-all verbose
Switch#show platform software trace level smd switch active R0 | inc dot1x
dot1x Notice
dot1x-all Verbose
dot1x-redun Notice
Switch#set platform software trace all notice
Switch#show logging process smd | include RADIUS
2025/09/19 14:36:25.431793040 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Send Accounting-Request to 10.48.30.117:1813 id 1813/180, len 459
2025/09/19 14:36:25.431800182 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: authenticator 37 19 72 c0 54 6b 63 a4 - e2 93 7b c1 c8 93 24 4c
2025/09/19 14:36:25.431804371 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Vendor, Cisco [26] 35
2025/09/19 14:36:25.431808600 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Cisco AVpair [1] 29 "cdp-tlv= "
2025/09/19 14:36:25.431811616 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Vendor, Cisco [26] 39
2025/09/19 14:36:25.431815180 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Cisco AVpair [1] 33 "cdp-tlv= "
2025/09/19 14:36:25.431817947 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Vendor, Cisco [26] 75
2025/09/19 14:36:25.431822305 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Cisco AVpair [1] 69 "lldp-tlv= "
2025/09/19 14:36:25.431826085 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: User-Name [1] 19 "E8-EB-34-D9-B8-F7"
2025/09/19 14:36:25.431828885 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Vendor, Cisco [26] 49
2025/09/19 14:36:25.431832691 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Cisco AVpair [1] 43 "audit-session-id=F24D300A000000156266B34D"
2025/09/19 14:36:25.431835418 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Vendor, Cisco [26] 18
2025/09/19 14:36:25.431839009 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Cisco AVpair [1] 12 "method=mab"
2025/09/19 14:36:25.431842591 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Called-Station-Id [30] 19 "50-1C-B0-78-EF-01"
2025/09/19 14:36:25.431846145 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Calling-Station-Id [31] 19 "E8-EB-34-D9-B8-F7"
2025/09/19 14:36:25.431851298 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: NAS-IP-Address [4] 6 10.48.77.242
2025/09/19 14:36:25.431854702 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: NAS-Port-Id [87] 22 "GigabitEthernet1/0/1"
2025/09/19 14:36:25.431859269 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: NAS-Port-Type [61] 6 Ethernet [15]
2025/09/19 14:36:25.431863238 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: NAS-Port [5] 6 50101
2025/09/19 14:36:25.431866514 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Calling-Station-Id [31] 19 "E8-EB-34-D9-B8-F7"
2025/09/19 14:36:25.431870007 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Called-Station-Id [30] 19 "50-1C-B0-78-EF-01"
2025/09/19 14:36:25.431873587 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Acct-Session-Id [44] 10 "000000cc"
2025/09/19 14:36:25.431882560 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Acct-Authentic [45] 6 Remote [3]
2025/09/19 14:36:25.431885338 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Class [25] 54 ...
2025/09/19 14:36:25.431933331 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Acct-Status-Type [40] 6 Start [1]
2025/09/19 14:36:25.431937105 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Event-Timestamp [55] 6 1758292585
2025/09/19 14:36:25.431940547 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Acct-Delay-Time [41] 6 0
2025/09/19 14:36:25.431973200 {smd_R0-0}{1}: [radius] [23554]: (info): RADIUS: Started 5 sec timeout
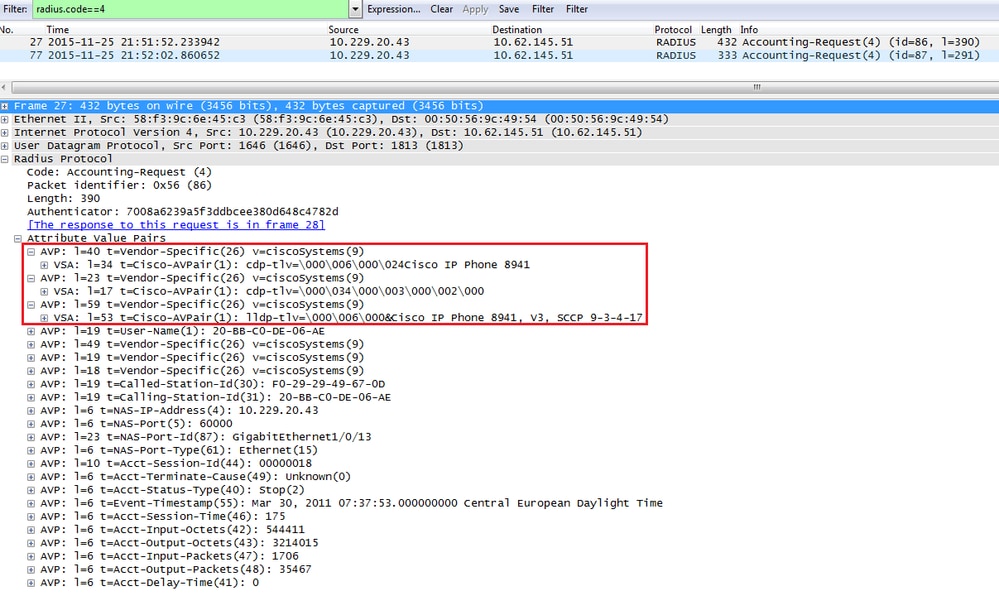
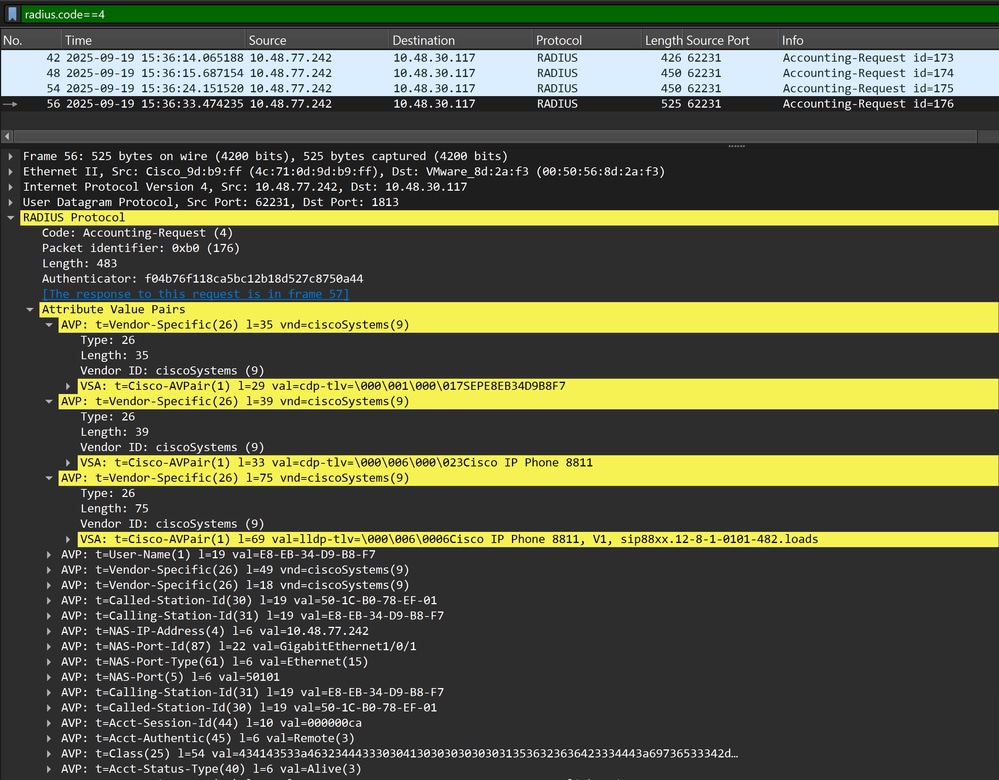
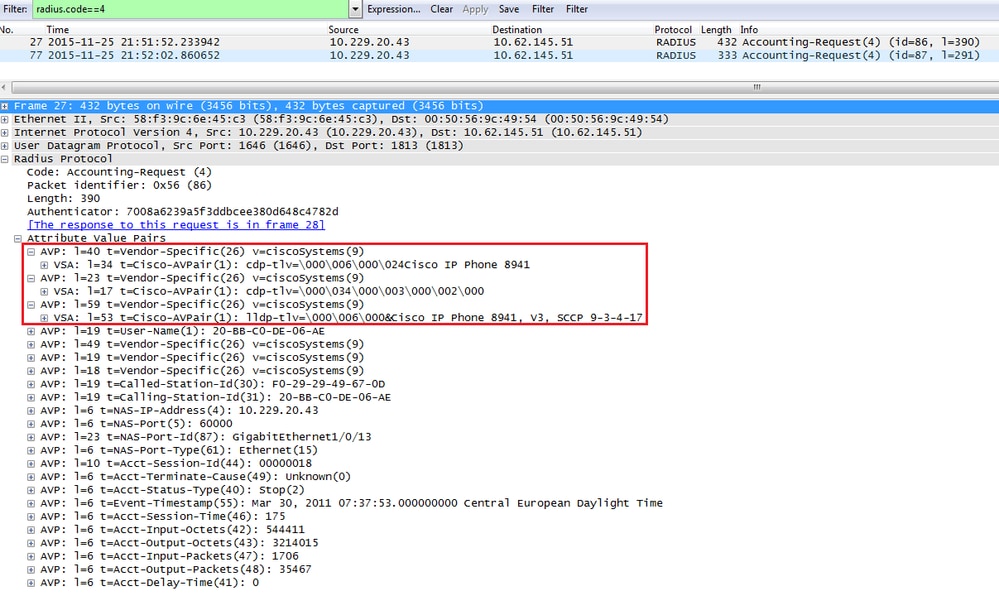
封包捕獲
步驟4.驗證ISE上的分析器調試
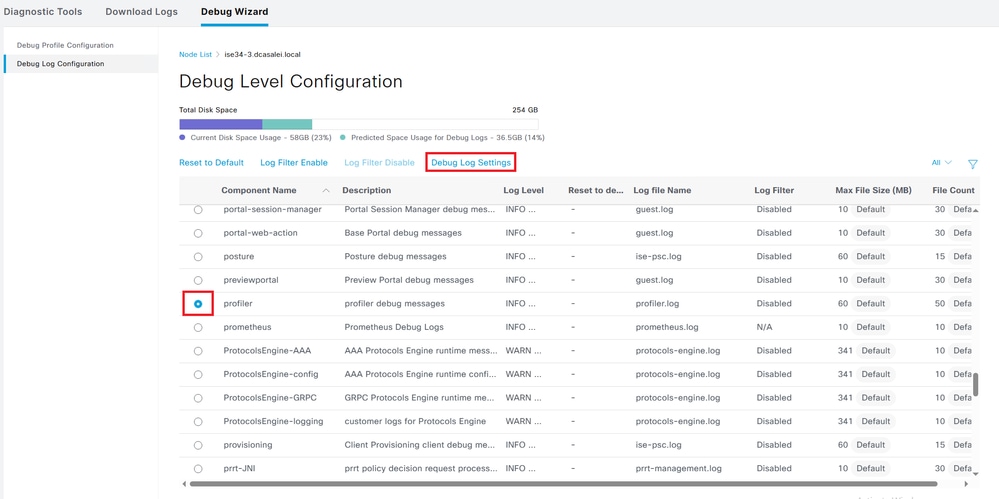
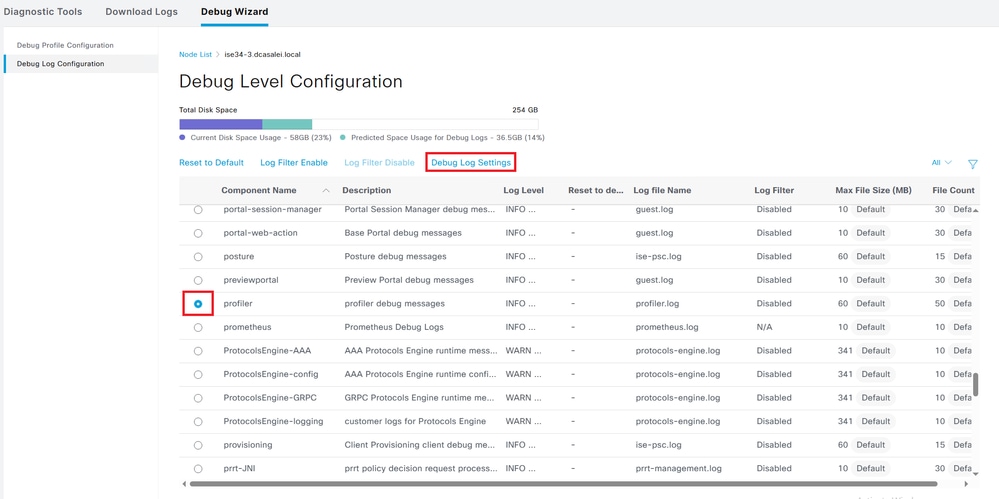
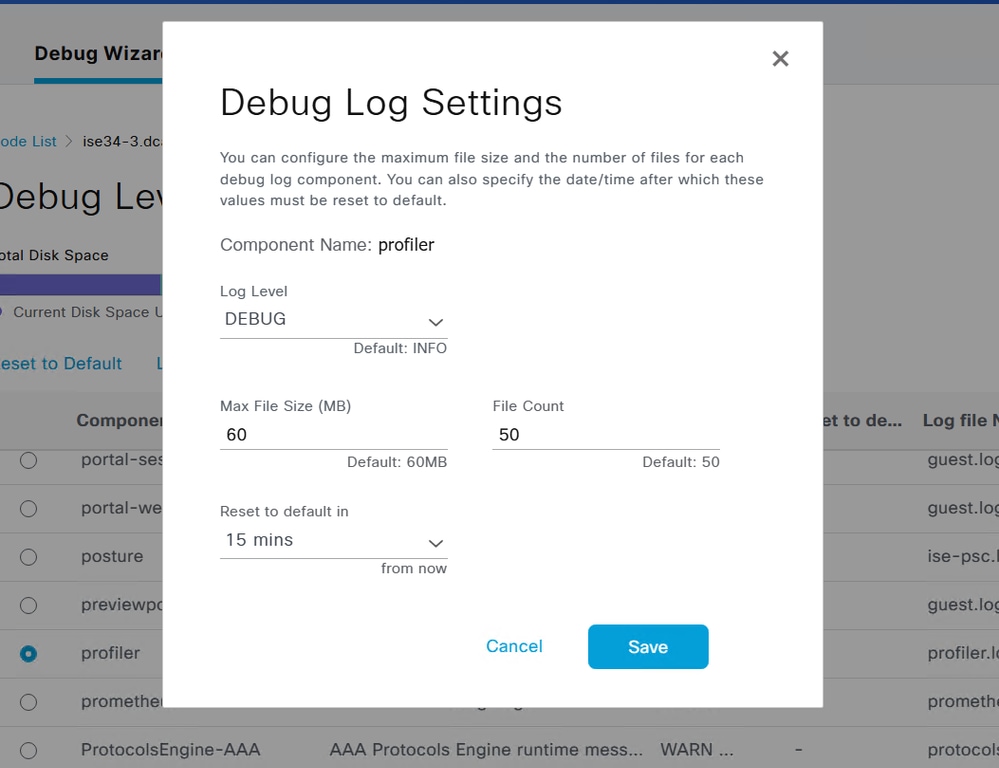
如果屬性是從交換機傳送的,則可以檢查屬性是否在ISE上接收。若要檢查此情況,請為正確的PSN節點啟用Profiler調試(Administration > System > Logging > Debug Log Configuration > PSN > Profiler > debug),並再次執行終端的身份驗證。
尋找以下資訊:
- 調試指示radius探測功能收到屬性:
2025-09-21 07:14:07,574 INFO [RADIUSParser-1-thread-2][[]] cisco.profiler.probes.radius.RadiusParser -:F24D300A000000166B1DB387::::- MSG_CODE=[3000], VALID=[true], PRRT_TIMESTAMP=[2025-09-21 07:14:07.571 +00:00], MAC=[E8-EB-34-D9-B8-F7]
2025-09-21 07:14:07,574 DEBUG [RADIUSParser-1-thread-2][[]] cisco.profiler.probes.radius.RadiusParser -:F24D300A000000166B1DB387::::- ATTRS=[Device IP Address=10.48.77.242, UserName=CP-8811-SEPE8EB34D9B8F7, NetworkDeviceName=Test_Switch, User-Name=CP-8811-SEPE8EB34D9B8F7, NAS-IP-Address=10.48.77.242, NAS-Port=50101, Class=CACS:F24D300A000000166B1DB387:ise34-3/547062375/1383, Called-Station-ID=50-1C-B0-78-EF-01, Calling-Station-ID=E8-EB-34-D9-B8-F7, Acct-Status-Type=Start, Acct-Delay-Time=0, Acct-Session-Id=000000ce, Acct-Authentic=Remote, Event-Timestamp=1758438796, NAS-Port-Type=Ethernet, NAS-Port-Id=GigabitEthernet1/0/1, cisco-av-pair=cdp-tlv=cdpCacheDeviceId=SEPE8EB34D9B8F7, cisco-av-pair=cdp-tlv=cdpCachePlatform=Cisco IP Phone 8811, cisco-av-pair=lldp-tlv=lldpSystemDescription=Cisco IP Phone 8811\, V1\, sip88xx.12-8-1-0101-482.loads, cisco-av-pair=audit-session-id=F24D300A000000166B1DB387, cisco-av-pair=method=mab, QuickResponseSent=true, AcsSessionID=ise34-3/547062375/1389, SelectedAccessService=Default Network Access, RequestLatency=8, Step=11004, Step=11017, Step=15049, Step=15008, Step=22095, Step=11005, NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, NetworkDeviceGroups=Location#All Locations, NetworkDeviceGroups=Device Type#All Device Types, CPMSessionID=F24D300A000000166B1DB387, StepLatency=1=0\;2=0\;3=0\;4=6\;5=0, TotalAuthenLatency=8, ClientLatency=0, Network Device Profile=Cisco, Location=Location#All Locations, Device Type=Device Type#All Device Types, IPSEC=IPSEC#Is IPSEC Device#No, ]
- 調試指示已成功分析屬性:
2025-09-21 07:14:07,574 DEBUG [RADIUSParser-1-thread-2][[]] cisco.profiler.probes.radius.RadiusParser -:F24D300A000000166B1DB387::::- Parsed IOS Sensor 1: cdpCacheDeviceId=[SEPE8EB34D9B8F7]
2025-09-21 07:14:07,574 DEBUG [RADIUSParser-1-thread-2][[]] cisco.profiler.probes.radius.RadiusParser -:F24D300A000000166B1DB387::::- Parsed IOS Sensor 2: cdpCachePlatform=[Cisco IP Phone 8811]
2025-09-21 07:14:07,574 DEBUG [RADIUSParser-1-thread-2][[]] cisco.profiler.probes.radius.RadiusParser -:F24D300A000000166B1DB387::::- Parsed IOS Sensor 3: lldpSystemDescription=[Cisco IP Phone 8811, V1, sip88xx.12-8-1-0101-482.loads]
- 調試,指示轉發器處理屬性:
2025-09-21 07:14:08,709 DEBUG [pool-55-thread-8][[]] cisco.profiler.infrastructure.probemgr.Forwarder -:F24D300A000000166B1DB387::90decf50-96ba-11f0-91c8-525ff9f6e55c:ProfilerCollection:- Endpoint Attributes:EndPoint[id=,name=]
MAC: E8:EB:34:D9:B8:F7
Attribute:AAA-Server value:ise34-3
(... more attributes ...)
Attribute:User-Name value:CP-8811-SEPE8EB34D9B8F7
Attribute:cdpCacheDeviceId value:SEPE8EB34D9B8F7
Attribute:cdpCachePlatform value:Cisco IP Phone 8811
Attribute:lldpSystemDescription value:Cisco IP Phone 8811, V1, sip88xx.12-8-1-0101-482.loads
Attribute:SkipProfiling value:false

附註:轉發器將終端與其屬性資料一起儲存在思科ISE資料庫中,然後通知分析器您的網路中檢測到的新終端。分析器將端點分類到端點身份組,並將具有匹配配置檔案的端點儲存在資料庫中。
步驟5.分析新屬性和裝置分配
通常在將新屬性新增到特定裝置的現有集合後,會將此裝置或終端新增到分析隊列,以檢查是否需要基於新屬性為其分配不同的配置檔案:
2025-09-21 07:14:08,714 INFO [pool-3352-thread-8][[]] cisco.profiler.infrastructure.profiling.ProfilerManager -:F24D300A000000166B1DB387::90decf50-96ba-11f0-91c8-525ff9f6e55c:Profiling:- Classify Mac E8:EB:34:D9:B8:F7 MessageCode 3000 epSource RADIUS Probe
2025-09-21 07:14:08,724 DEBUG [pool-3352-thread-8][[]] cisco.profiler.infrastructure.profiling.ProfilerManager -:F24D300A000000166B1DB387::90decf50-96ba-11f0-91c8-525ff9f6e55c:Profiling:- Policy Cisco-Device matched E8:EB:34:D9:B8:F7 (certainty 30)
2025-09-21 07:14:08,727 DEBUG [pool-3352-thread-8][[]] cisco.profiler.infrastructure.profiling.ProfilerManager -:F24D300A000000166B1DB387::90decf50-96ba-11f0-91c8-525ff9f6e55c:Profiling:- Policy Cisco-IP-Phone matched E8:EB:34:D9:B8:F7 (certainty 45)
2025-09-21 07:14:08,729 DEBUG [pool-3352-thread-8][[]] cisco.profiler.infrastructure.profiling.ProfilerManager -:F24D300A000000166B1DB387::90decf50-96ba-11f0-91c8-525ff9f6e55c:Profiling:- Policy Cisco-IP-Phone-8811 matched E8:EB:34:D9:B8:F7 (certainty 140)
2025-09-21 07:14:08,729 DEBUG [pool-3352-thread-8][[]] cisco.profiler.infrastructure.profiling.ProfilerManager -:F24D300A000000166B1DB387::90decf50-96ba-11f0-91c8-525ff9f6e55c:Profiling:- After analyzing policy hierarchy: Endpoint: E8:EB:34:D9:B8:F7 EndpointPolicy:Cisco-IP-Phone-8811 for:215 ExceptionRuleMatched:false
相關資訊

 意見
意見