配置ISE 2.0 TrustSec SXP偵聽器和揚聲器
下載選項
無偏見用語
本產品的文件集力求使用無偏見用語。針對本文件集的目的,無偏見係定義為未根據年齡、身心障礙、性別、種族身分、民族身分、性別傾向、社會經濟地位及交織性表示歧視的用語。由於本產品軟體使用者介面中硬式編碼的語言、根據 RFP 文件使用的語言,或引用第三方產品的語言,因此本文件中可能會出現例外狀況。深入瞭解思科如何使用包容性用語。
關於此翻譯
思科已使用電腦和人工技術翻譯本文件,讓全世界的使用者能夠以自己的語言理解支援內容。請注意,即使是最佳機器翻譯,也不如專業譯者翻譯的內容準確。Cisco Systems, Inc. 對這些翻譯的準確度概不負責,並建議一律查看原始英文文件(提供連結)。
簡介
本文檔介紹如何配置思科身份服務引擎(ISE) 2.0版在偵聽器和揚聲器模式下支援TrustSec SGT交換協定(SXP)的功能並對其進行故障排除。
必要條件
需求
思科建議您瞭解以下主題:
- Cisco Catalyst交換機配置
- 身份服務引擎(ISE)和TrustSec服務
採用元件
本檔案中的資訊是根據以下軟體版本:
- Cisco Catalyst 3850交換機,帶軟體IOS-XE 3.7.2及更高版本
- Cisco ISE,版本2.0及更高版本
設定
網路圖表
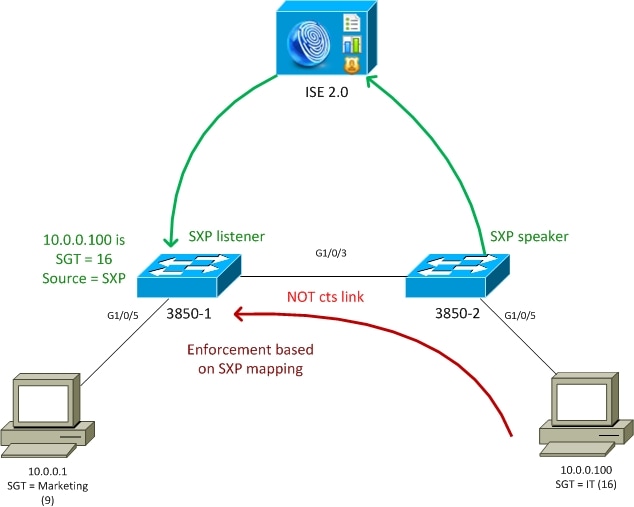
流量傳輸
- 3850-2是10.0.0.100的802.1x身份驗證器- ISE返回安全組標籤(SGT) 16 (IT)以成功進行身份驗證
- 3850-2交換機學習請求方ip地址(ip裝置跟蹤)並使用SXP協定將對映資訊(IP-SGT)傳送到ISE
- 3850-1是10.0.0.1的802.1x身份驗證器- ISE返回SGT標籤9 (行銷)以成功進行身份驗證
- 3850-1從ISE接收SXP對映資訊(10.0.0.100是SGT 16),從ISE下載策略
- 從10.0.0.100傳送到10.0.0.1的流量由3850-2(未下載具體策略)轉發到3850-1,後者執行器將策略IT完成(16) ->市場行銷(9)
請注意,交換機之間的鏈路不是cts鏈路,因此交換機上的所有遠端對映都是透過SXP協定安裝的。
注意:並非所有交換機都有允許根據接收的SXP對映透過ISE接收的策略進行程式設計的硬體。如需驗證,請始終參閱最新的TrustSec相容性清單或聯絡思科系統。
組態
有關基本TrustSec配置的詳細資訊,請參閱參考部分中的文章。
交換機3850-1
交換機透過SGT分配終止802.1x會話,並作為SXP揚聲器向ISE傳送。
aaa authentication dot1x default group ISE_mgarcarz
aaa authorization network default group ISE_mgarcarz
aaa authorization network ISE_mgarcarz group ISE_mgarcarz
aaa accounting dot1x default start-stop group ISE_mgarcarz
aaa accounting update newinfo
radius server ISE_mgarcarz
address ipv4 10.48.17.235 auth-port 1645 acct-port 1646
pac key cisco
aaa group server radius ISE_mgarcarz
server name ISE_mgarcarz
interface GigabitEthernet1/0/3
switchport mode trunk
interface GigabitEthernet1/0/5
description mgarcarz
switchport access vlan 100
switchport mode access
ip flow monitor F_MON input
ip flow monitor F_MON output
authentication order dot1x mab
authentication priority dot1x mab
authentication port-control auto
mab
dot1x pae authenticator
cts authorization list ISE_mgarcarz
cts role-based enforcement
cts role-based enforcement vlan-list 1-4094
cts sxp enable
cts sxp default password cisco
cts sxp connection peer 10.48.17.235 password default mode local listener hold-time 0
交換機3850-2
交換機透過SGT分配終止802.1x會話,並作為SXP偵聽器從ISE獲取對映。
aaa authentication dot1x default group ISE_mgarcarz
aaa authorization network default group ISE_mgarcarz
aaa authorization network ISE_mgarcarz group ISE_mgarcarz
aaa accounting dot1x default start-stop group ISE_mgarcarz
aaa accounting update newinfo
radius server ISE_mgarcarz
address ipv4 10.48.17.235 auth-port 1645 acct-port 1646
pac key cisco
aaa group server radius ISE_mgarcarz
server name ISE_mgarcarz
interface GigabitEthernet1/0/3
switchport mode trunk
interface GigabitEthernet1/0/5
description mgarcarz
switchport access vlan 100
switchport mode access
authentication order dot1x mab
authentication priority dot1x mab
authentication port-control auto
mab
dot1x pae authenticator
cts authorization list ISE_mgarcarz
cts role-based enforcement
cts role-based enforcement vlan-list 1-4094
cts sxp enable
cts sxp default password cisco
cts sxp connection peer 10.48.17.235 password default mode local speaker hold-time 0
ISE
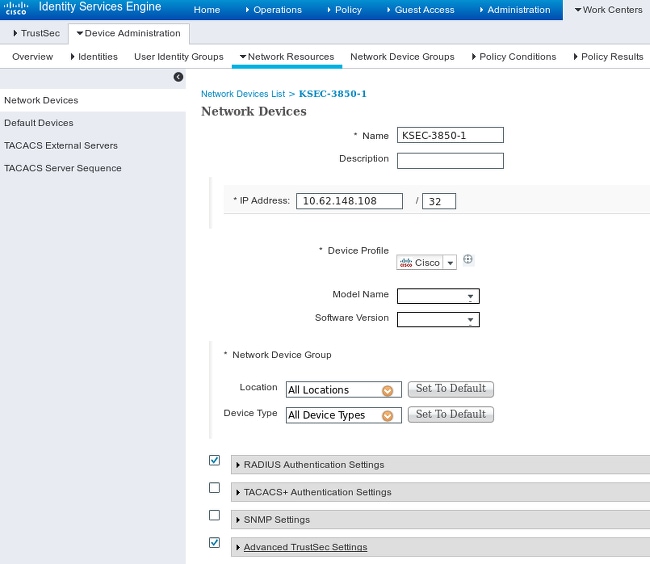
步驟1.網路接入裝置
導航到工作中心>裝置管理>網路資源,使用共用金鑰cisco和TrustSec口令Krakow123增加兩台交換機。
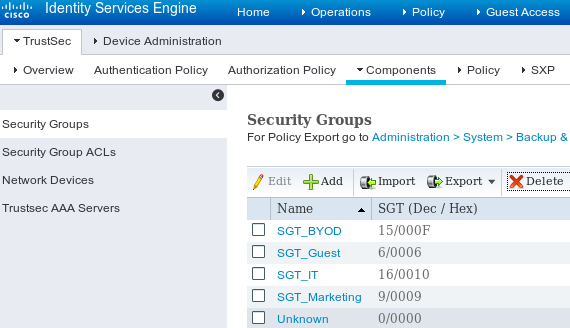
步驟 2.安全性群組
要增加面向IT和市場行銷的SGT,請導航到工作中心> TrustSec >元件>安全組。
步驟3.安全組ACL
要增加安全組ACL,請導航到工作中心> TrustSec >元件>安全組ACL。
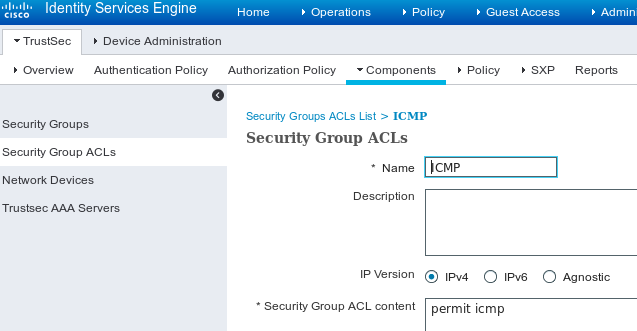
僅允許ICMP流量。
步驟 4.TrustSec策略
要增加控制從IT到行銷的資料流的策略,請導航到工作中心> TrustSec >元件>出口策略>矩陣。
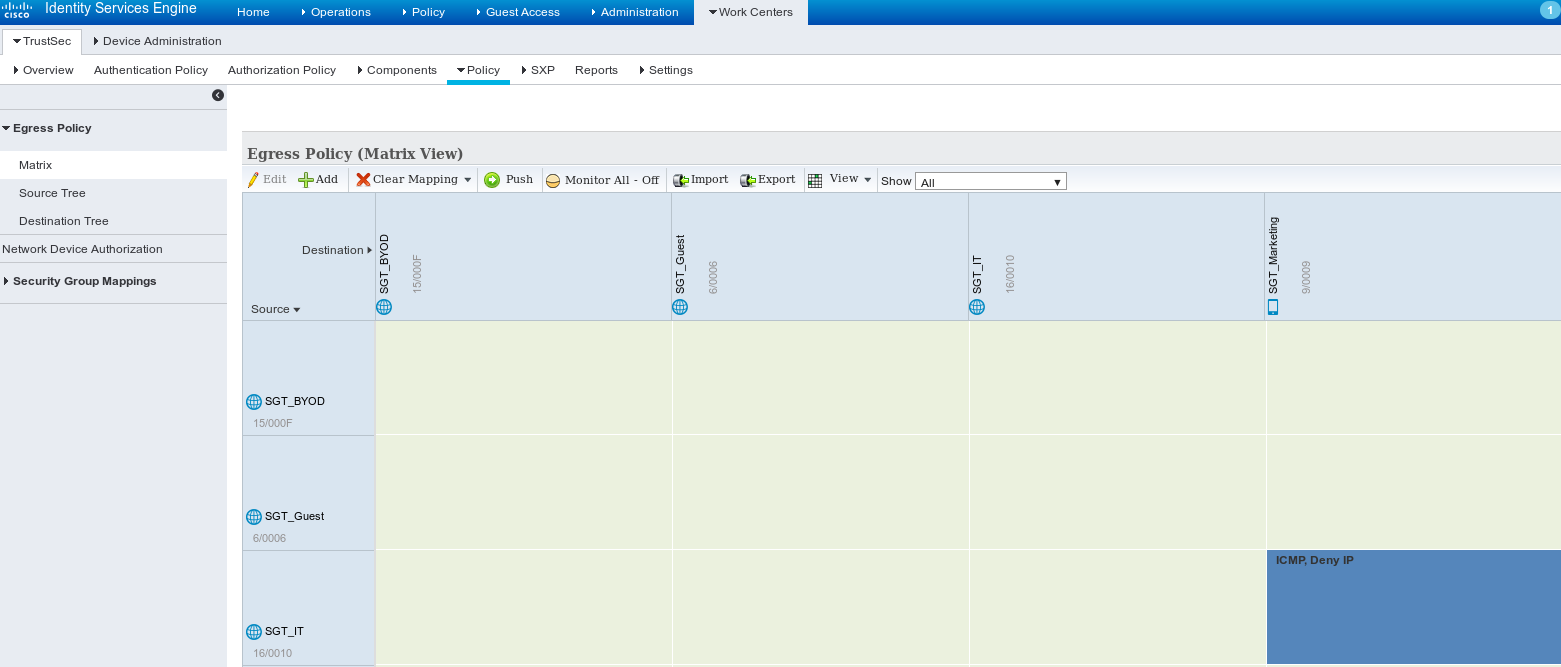
設定預設條目catch all規則以拒絕所有流量。
步驟 5.SXP裝置
要為相應交換機配置SXP偵聽器和揚聲器,請導航到工作中心> TrustSec > SXP裝置。
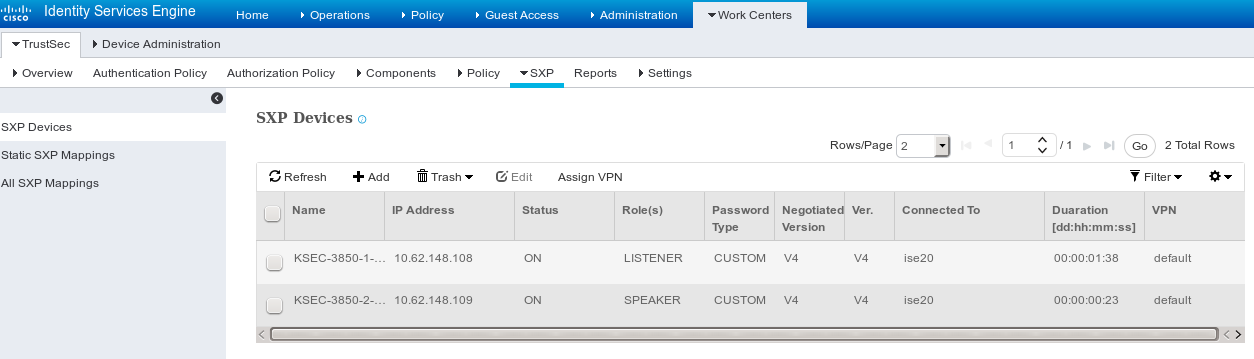
使用口令cisco(或為交換機上的sxp配置的任何其它口令)。
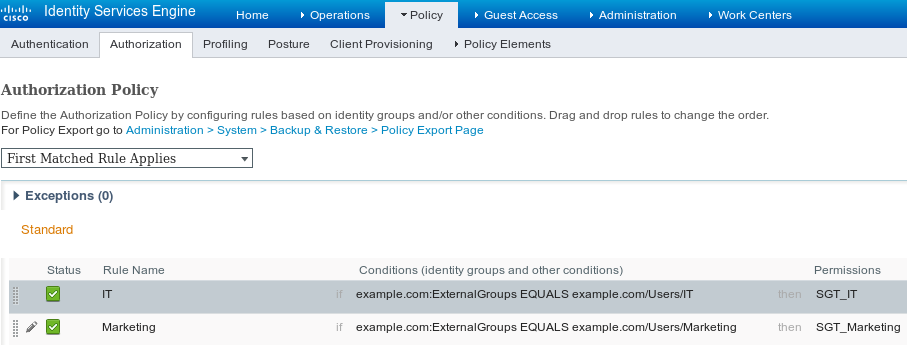
步驟 6.授權策略
確保授權策略為每個使用者返回正確的SGT標籤,然後導航到策略>授權。
驗證
步驟 1.交換機加入CTS的ISE
從每台交換機提供TrustSec憑證(在ISE/Step1中配置)以獲取PAC。
KSEC-3850-2#cts credentials id KSEC-3850-2 password Krakow123
CTS device ID and password have been inserted in the local keystore. Please make sure that the same ID and password are configured in the server database.
確保已下載PAC。
KSEC-3850-2#show cts pacs
AID: 65D55BAF222BBC73362A7810A04A005B
PAC-Info:
PAC-type = Cisco Trustsec
AID: 65D55BAF222BBC73362A7810A04A005B
I-ID: KSEC-3850-2
A-ID-Info: Identity Services Engine
Credential Lifetime: 20:42:37 UTC Nov 13 2015
PAC-Opaque: 000200B8000300010004001065D55BAF222BBC73362A7810A04A005B0006009C00030100B26D8DDC125B6595067D64F917DA624C0000001355CB2E1C00093A800E567155E0DE76419D2F3B97D890F34F109C4C42F586B29050CEC7B441E0CA60FC6684D4F6E8263FA2623A6E450927815A140CD3B9D68988E95D8C1E65544E222E187C647B9F7F3F230F6DB4F80F3C201ACD623B309077E27688EDF7704740A1CD3F18CE8485788054C19909083ED303BB49A6975AC0395D41E1227B
Refresh timer is set for 12w4d
並刷新環境策略。
KSEC-3850-2#show cts environment-data
CTS Environment Data
====================
Current state = COMPLETE
Last status = Successful
Local Device SGT:
SGT tag = 0-00:Unknown
Server List Info:
Installed list: CTSServerList1-0001, 1 server(s):
*Server: 10.48.17.235, port 1812, A-ID 65D55BAF222BBC73362A7810A04A005B
Status = ALIVE
auto-test = FALSE, keywrap-enable = FALSE, idle-time = 60 mins, deadtime = 20 secs
Multicast Group SGT Table:
Security Group Name Table:
0-00:Unknown
6-00:SGT_Guest
9-00:SGT_Marketing
15-00:SGT_BYOD
16-00:SGT_IT
255-00:SGT_Quarantine
Environment Data Lifetime = 86400 secs
Last update time = 20:47:04 UTC Sat Aug 15 2015
Env-data expires in 0:08:09:13 (dd:hr:mm:sec)
Env-data refreshes in 0:08:09:13 (dd:hr:mm:sec)
Cache data applied = NONE
State Machine is running
對3850-1重複相同的過程
第2步:802.1x會話
在IT使用者透過身份驗證後,將分配正確的標籤。
KSEC-3850-2#show authentication sessions interface g1/0/5 details
Interface: GigabitEthernet1/0/5
IIF-ID: 0x107E700000000C4
MAC Address: 0050.b611.ed31
IPv6 Address: Unknown
IPv4 Address: 10.0.0.100
User-Name: cisco
Status: Authorized
Domain: DATA
Oper host mode: single-host
Oper control dir: both
Session timeout: N/A
Common Session ID: 0A3E946D00000FF214D18E36
Acct Session ID: 0x00000FDC
Handle: 0xA4000020
Current Policy: POLICY_Gi1/0/5
Local Policies:
Service Template: DEFAULT_LINKSEC_POLICY_SHOULD_SECURE (priority 150)
Security Policy: Should Secure
Security Status: Link Unsecure
Server Policies:
SGT Value: 16
Method status list:
Method State
dot1x Authc Success
該對映安裝在本地SGT-IP表中。
KSEC-3850-2#show cts role-based sgt-map all
Active IPv4-SGT Bindings Information
IP Address SGT Source
============================================
10.0.0.100 16 LOCAL
步驟 3.SXP揚聲器
3850-2將對映傳送到ISE,交換機調試用於cts sxp。
KSEC-3850-2(config)#do show debug
CTS:
CTS SXP message debugging is on
*Aug 16 12:48:30.173: CTS-SXP-MSG:trp_send_msg <1>, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.173: CTS-SXP-MSG:trp_socket_write fd<1>, cdbp->ph_sock_pending<1>, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.226: CTS-SXP-MSG:trp_process_read_sock <1>, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.226: CTS-SXP-MSG:trp_process_read_sock socket_recv result:-1 errno:11; <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.226: CTS-SXP-MSG:trp_process_read_sock socket_conn is accepted; <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.226: CTS-SXP-MSG:trp_socket_write fd<1>, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.226: CTS-SXP-MSG:trp_socket_write freeing tx_msgq_entry, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.227: CTS-SXP-MSG:after socket_send, wlen=28, slen=0, tot_len=28, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.227: CTS-SXP-MSG:trp_socket_write freeing tx_buf, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.227: CTS-SXP-MSG:trp_socket_read <1>, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.227: CTS-SXP-MSG:trp_socket_read readlen = -1; errno = 11, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.278: CTS-SXP-MSG:trp_process_read_sock <1>, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.278: CTS-SXP-MSG:trp_socket_read <1>, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.278: CTS-SXP-MSG:RCVD peer 10.48.17.235 readlen:32, datalen:0 remain:4096 bufp =
*Aug 16 12:48:30.278: CTS-SXP-MSG:sxp_handle_rx_msg_v2 <1>, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.279: CTS-SXP-MSG:imu_sxp_conn_cr <1>, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.279: CTS-SXP-MSG:wrt_sxp_opcode_info_v4 cdbp 0x3D541160
*Aug 16 12:48:30.279: CTS-SXP-MSG:trp_send_msg <1>, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.279: CTS-SXP-MSG:trp_socket_write fd<1>, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.279: CTS-SXP-MSG:trp_socket_write freeing tx_msgq_entry, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.279: CTS-SXP-MSG:after socket_send, wlen=28, slen=0, tot_len=28, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.279: CTS-SXP-MSG:trp_socket_write freeing tx_buf, <10.48.17.235, 10.62.148.109>
*Aug 16 12:48:30.280: CTS-SXP-MSG:trp_socket_read readlen = 32; errno = 11, <10.48.17.235, 10.62.148.109>
ISE報告(sxp_appserver/sxp.log)
2015-08-16 14:44:07,029 INFO [nioEventLoopGroup-2-3] opendaylight.sxp.core.behavior.Strategy:473 - [ISE:10.48.17.235][10.48.17.235:21121/10.62.148.109:64999][O|Lv4/Sv4 192.168.77.2] PURGEALL processing
2015-08-16 14:44:07,029 WARN [nioEventLoopGroup-2-3] opendaylight.sxp.core.handler.MessageDecoder:173 - [ISE:10.48.17.235][10.48.17.235:21121/10.62.148.109:64999] Channel inactivation
2015-08-16 14:44:07,029 INFO [pool-3-thread-1] sxp.util.database.spi.MasterDatabaseProvider:721 - SXP_PERF:BINDINGS_PER_SXP_UPDATE_MESSAGE(CHUNK)=1, onlyChanged=true
2015-08-16 14:44:07,030 INFO [pool-3-thread-1] sxp.util.database.spi.MasterDatabaseProvider:725 - SXP_PERF:NUM_OF_CHUNKS=1, onlyChanged=true
2015-08-16 14:44:07,030 INFO [pool-3-thread-9] opendaylight.sxp.core.service.UpdateExportTask:93 - SXP_PERF:SEND_UPDATE_BUFFER_SIZE=16
2015-08-16 14:44:07,030 INFO [pool-3-thread-9] opendaylight.sxp.core.service.UpdateExportTask:119 - SENT_UPDATE to [ISE:10.48.17.235][10.48.17.235:57719/10.62.148.108:64999][O|Sv4]
2015-08-16 14:44:07,030 INFO [pool-3-thread-9] opendaylight.sxp.core.service.UpdateExportTask:140 - SENT_UPDATE SUCCESSFUL to [ISE:10.48.17.235][10.48.17.235:57719/10.62.148.108:64999][O|Sv4]:false
2015-08-16 14:44:07,030 INFO [pool-3-thread-1] opendaylight.sxp.core.service.BindingDispatcher:198 - SXP_PERF:MDB_PARTITON_AND_SXP_DISPATCH:DURATION=1 milliseconds, NUM_CONNECTIONS=1
2015-08-16 14:44:07,031 INFO [pool-3-thread-1] sxp.util.database.spi.MasterDatabaseProvider:725 - SXP_PERF:NUM_OF_CHUNKS=0, onlyChanged=true
2015-08-16 14:44:12,534 INFO [nioEventLoopGroup-2-4] opendaylight.sxp.core.behavior.Strategy:232 - [ISE:10.48.17.235][10.48.17.235:64999/10.62.148.109:1035][X|Lv4/Sv4 192.168.77.2] received Message Open
2015-08-16 14:44:12,535 INFO [nioEventLoopGroup-2-4] opendaylight.sxp.core.behavior.Strategy:358 - [ISE:10.48.17.235][10.48.17.235:64999/10.62.148.109:1035][O|Lv4/Sv4 192.168.77.2] Sent RESP 0 0 0 32 0 0 0 2 | 0 0 0 4 0 0 0 2 80 6 6 3 0 2 0 1 0 80 7 4 0 120 0 180
2015-08-16 14:44:12,585 INFO [nioEventLoopGroup-2-4] opendaylight.sxp.core.behavior.Strategy:451 - [ISE:10.48.17.235][10.48.17.235:64999/10.62.148.109:1035][O|Lv4/Sv4 192.168.77.2] received Message Update
2015-08-16 14:44:12,586 INFO [pool-3-thread-2] opendaylight.sxp.core.service.SimpleBindingHandler:663 - PERF_SXP_PROCESS_UPDATE from [ISE:10.48.17.235][10.48.17.235:64999/10.62.148.109:1035][O|Lv4/Sv4 192.168.77.2]
2015-08-16 14:44:12,586 INFO [pool-3-thread-2] opendaylight.sxp.core.service.SimpleBindingHandler:666 - PERF_SXP_PROCESS_UPDATE_DONE from [ISE:10.48.17.235][10.48.17.235:64999/10.62.148.109:1035][O|Lv4/Sv4 192.168.77.2]
2015-08-16 14:44:12,586 INFO [pool-3-thread-1] sxp.util.database.spi.MasterDatabaseProvider:721 - SXP_PERF:BINDINGS_PER_SXP_UPDATE_MESSAGE(CHUNK)=1, onlyChanged=true
2015-08-16 14:44:12,587 INFO [pool-3-thread-1] sxp.util.database.spi.MasterDatabaseProvider:725 - SXP_PERF:NUM_OF_CHUNKS=1, onlyChanged=true
2015-08-16 14:44:12,587 INFO [pool-3-thread-11] opendaylight.sxp.core.service.UpdateExportTask:93 - SXP_PERF:SEND_UPDATE_BUFFER_SIZE=32
2015-08-16 14:44:12,587 INFO [pool-3-thread-11] opendaylight.sxp.core.service.UpdateExportTask:119 - SENT_UPDATE to [ISE:10.48.17.235][10.48.17.235:57719/10.62.148.108:64999][O|Sv4]
2015-08-16 14:44:12,587 INFO [pool-3-thread-11] opendaylight.sxp.core.service.UpdateExportTask:140 - SENT_UPDATE SUCCESSFUL to [ISE:10.48.17.235][10.48.17.235:57719/10.62.148.108:64999][O|Sv4]:false
2015-08-16 14:44:12,587 INFO [pool-3-thread-1] opendaylight.sxp.core.service.BindingDispatcher:198 - SXP_PERF:MDB_PARTITON_AND_SXP_DISPATCH:DURATION=1 milliseconds, NUM_CONNECTIONS=1
並透過GUI顯示所有對應(包括從3850-2接收的10.0.0.100對應),如下圖所示。
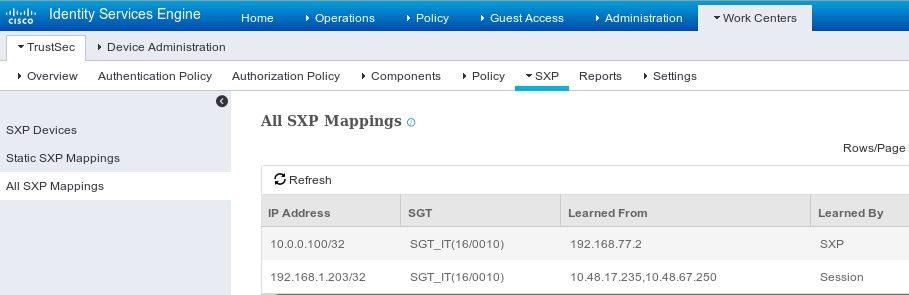
192.168.77.2是3850-2上SXP連線的識別符號(定義的最高ip地址)。
KSEC-3850-2#show ip interface brief
Interface IP-Address OK? Method Status Protocol
GigabitEthernet0/0 unassigned YES unset down down
Vlan1 unassigned YES NVRAM administratively down down
Vlan100 10.0.0.2 YES manual up up
Vlan480 10.62.148.109 YES NVRAM up up
Vlan613 unassigned YES NVRAM administratively down down
Vlan666 192.168.66.2 YES NVRAM down down
Vlan777 192.168.77.2 YES NVRAM down down
步驟 4.SXP偵聽程式
然後ISE將該對映重新傳送到3850-1,交換機調試。
*Aug 16 05:42:54.199: CTS-SXP-MSG:trp_send_msg <1>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.199: CTS-SXP-MSG:trp_socket_write fd<1>, cdbp->ph_sock_pending<1>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.248: CTS-SXP-MSG:trp_process_read_sock <1>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.248: CTS-SXP-MSG:trp_process_read_sock socket_recv result:-1 errno:11; <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.248: CTS-SXP-MSG:trp_process_read_sock socket_conn is accepted; <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.248: CTS-SXP-MSG:trp_socket_write fd<1>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.248: CTS-SXP-MSG:trp_socket_write freeing tx_msgq_entry, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.248: CTS-SXP-MSG:after socket_send, wlen=32, slen=0, tot_len=32, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.248: CTS-SXP-MSG:trp_socket_write freeing tx_buf, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.249: CTS-SXP-MSG:trp_socket_read <1>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.249: CTS-SXP-MSG:trp_socket_read readlen = -1; errno = 11, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.300: CTS-SXP-MSG:trp_process_read_sock <1>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.300: CTS-SXP-MSG:trp_socket_read <1>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.300: CTS-SXP-MSG:RCVD peer 10.48.17.235 readlen:28, datalen:0 remain:4096 bufp =
*Aug 16 05:42:54.301: CTS-SXP-MSG:sxp_handle_rx_msg_v2 <1>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.301: CTS-SXP-MSG:imu_sxp_conn_cr ci<1> cdbp->ph_conn_state<2>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.301: CTS-SXP-MSG:trp_socket_read readlen = 28; errno = 11, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.301: CTS-SXP-MSG:trp_process_read_sock <1>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.302: CTS-SXP-MSG:trp_socket_read <1>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.302: CTS-SXP-MSG:RCVD peer 10.48.17.235 readlen:52, datalen:0 remain:4096 bufp =
*Aug 16 05:42:54.302: CTS-SXP-MSG:sxp_handle_rx_msg_v2 <1>, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.302: CTS-SXP-MSG:sxp_recv_update_v4 <1> peer ip: 10.48.17.235
*Aug 16 05:42:54.302: CTS-SXP-MSG:1. msg type:3, total len:52, payl len:44, opc_ptr:0x3DFC7308, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.302: CTS-SXP-MSG:1. msg type:3, total len:52, payl len:37, opc_ptr:0x3DFC730F, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.302: CTS-SXP-MSG:1. msg type:3, total len:52, payl len:32, opc_ptr:0x3DFC7314, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.302: CTS-SXP-MSG:1. msg type:3, total len:52, payl len:24, opc_ptr:0x3DFC731C, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.302: CTS-SXP-MSG:1. msg type:3, total len:52, payl len:13, opc_ptr:0x3DFC7327, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.302: CTS-SXP-MSG:1. msg type:3, total len:52, payl len:8, opc_ptr:0x3DFC732C, <10.48.17.235, 10.62.148.108>
*Aug 16 05:42:54.303: CTS-SXP-MSG:1. msg type:3, total len:52, payl len:0, opc_ptr:0x3DFC7334, <10.48.17.235, 10.62.148.108>
從ISE對通向3850-1的流量進行資料包捕獲確認正在傳送SXP對映。
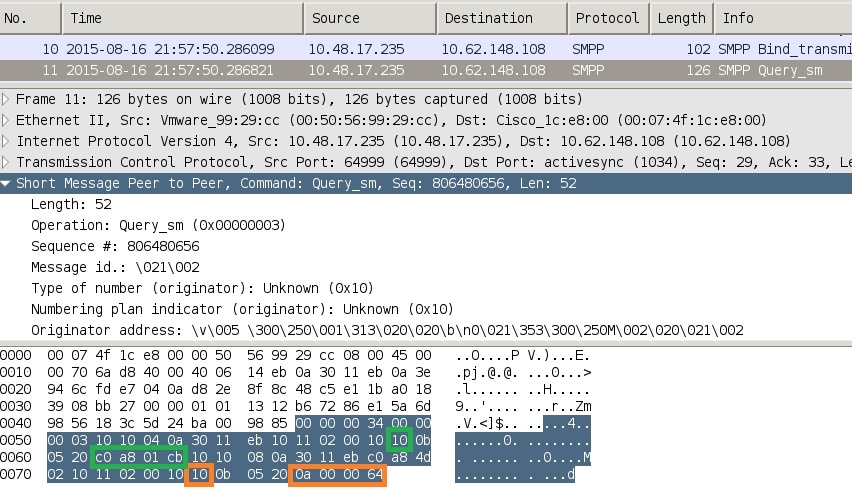
Wireshark使用標準SMPP解碼器。檢查負載:
「c0 a8 01 cb」(192.168.1.203)為10 (SGT = 16)
「0a 00 00 64」(10.0.0.100)為10 (SGT = 16)
3850-1安裝從ISE接收的所有對映。
KSEC-3850-1# show cts sxp sgt-map
SXP Node ID(generated):0xC0A84D01(192.168.77.1)
IP-SGT Mappings as follows:
IPv4,SGT: <10.0.0.100 , 16:SGT_IT>
source : SXP;
Peer IP : 10.48.17.235;
Ins Num : 2;
Status : Active;
Seq Num : 439
Peer Seq: 0A3011EB,C0A84D02,
IPv4,SGT: <192.168.1.203 , 16:SGT_IT>
source : SXP;
Peer IP : 10.48.17.235;
Ins Num : 6;
Status : Active;
Seq Num : 21
Peer Seq: 0A3011EB,
Total number of IP-SGT Mappings: 2
KSEC-3850-1# show cts role-based sgt-map all
Active IPv4-SGT Bindings Information
IP Address SGT Source
============================================
10.0.0.100 16 SXP
192.168.1.203 16 SXP
IP-SGT Active Bindings Summary
============================================
Total number of CLI bindings = 1
Total number of SXP bindings = 2
Total number of active bindings = 3
步驟 5.策略下載和實施
從ISE下載正確的策略。(使用SGT 16的矩陣行)
KSEC-3850-1#show cts role-based permissions
IPv4 Role-based permissions default:
Permit IP-00
IPv4 Role-based permissions from group 16:SGT_IT to group 9:SGT_Marketing:
ICMP-10
Deny IP-00
RBACL Monitor All for Dynamic Policies : FALSE
RBACL Monitor All for Configured Policies : FALSE
允許從10.0.0.100 (SGT IT)到10.0.0.1 (SGT行銷)的ICMP流量,計數增加。
KSEC-3850-1#show cts role-based counters from 16
Role-based IPv4 counters
#Hardware counters are not available for specific SGT/DGT
#Use this command without arguments to see hardware counters
From To SW-Denied SW-Permitted
16 9 0 0 11 0
當嘗試使用telnet連線失敗時,丟棄計數器增加。
KSEC-3850-1#show cts role-based counters from 16
Role-based IPv4 counters
#Hardware counters are not available for specific SGT/DGT
#Use this command without arguments to see hardware counters
From To SW-Denied SW-Permitted
16 9 3 0 11 0
請注意,3850-2沒有特定策略,允許所有流量。
KSEC-3850-2#show cts role-based permissions
IPv4 Role-based permissions default:
Permit IP-00
RBACL Monitor All for Dynamic Policies : FALSE
RBACL Monitor All for Configured Policies : FALSE
在ISE上修改SG ACL後,在3850-1上增加permit tcp和cts刷新策略-然後接受telnet流量。
還可以使用Flexible Netflow(從IOS-XE 3.7.2開始為SGT感知)本地快取來確認行為。
flow record cts-v4
match ipv4 protocol
match ipv4 source address
match ipv4 destination address
match transport source-port
match transport destination-port
match flow direction
match flow cts source group-tag
match flow cts destination group-tag
collect counter packets long
flow monitor F_MON
record cts-v4
interface GigabitEthernet1/0/3
ip flow monitor F_MON input
ip flow monitor F_MON output
結果顯示從3850-2接收的流量。源SGT為0,因為接收的資料流沒有任何SGT(無cts鏈路),但目標組標籤根據本地對映表自動替換。
KSEC-3850-1#show flow monitor F_MON cache
Cache type: Normal (Platform cache)
Cache size: Unknown
Current entries: 6
Flows added: 1978
Flows aged: 1972
- Active timeout ( 1800 secs) 30
- Inactive timeout ( 15 secs) 1942
IPV4 SRC ADDR IPV4 DST ADDR TRNS SRC PORT TRNS DST PORT FLOW DIRN FLOW CTS SRC GROUP TAG FLOW CTS DST GROUP TAG IP PROT pkts long
=============== =============== ============= ============= ========= ====================== ====================== ======= ====================
150.1.7.1 224.0.0.10 0 0 Output 0 0 88 57
10.62.148.1 224.0.0.13 0 8192 Output 0 0 103 0
7.7.4.1 224.0.0.10 0 0 Output 0 0 88 56
10.0.0.1 10.0.0.100 0 0 Output 0 0 1 1388
150.1.7.105 224.0.0.5 0 0 Output 0 0 89 24
150.1.7.1 224.0.0.5 0 0 Output 0 0 89 24
10.0.0.100 10.0.0.1 0 2048 Input 0 9 1 1388
Netflow本地快取可用於確認收到的流量。如果該流量被接受或丟棄,則由之前顯示的cts計數器確認。
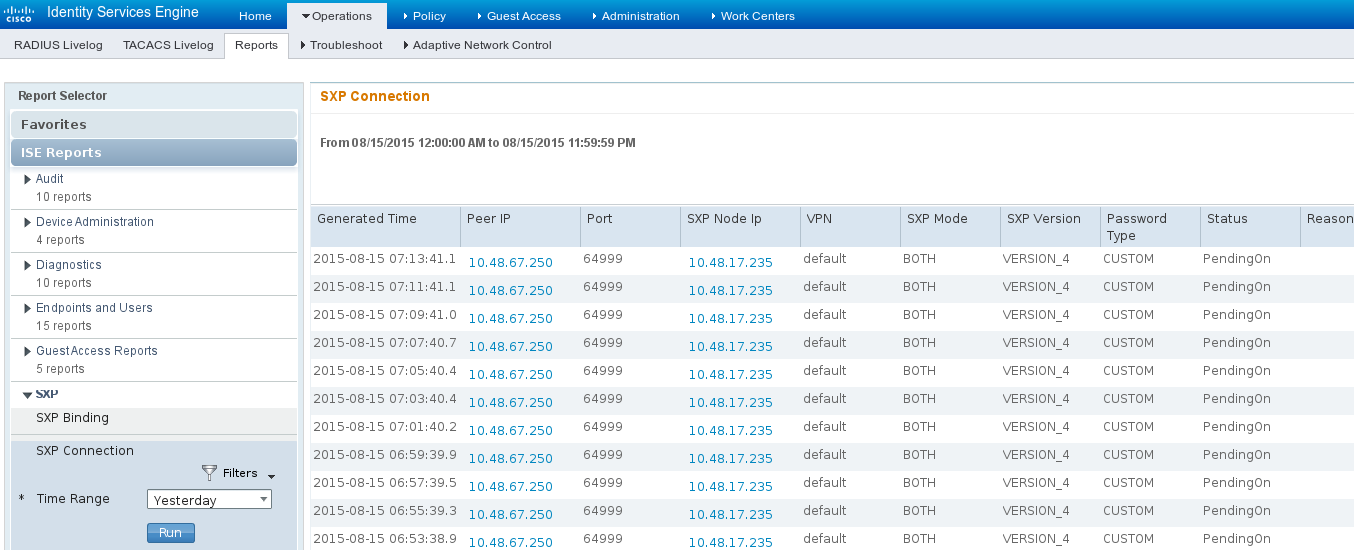
ISE還允許生成SXP繫結和連線報告,如下圖所示。
參考資料
修訂記錄
| 修訂 | 發佈日期 | 意見 |
|---|---|---|
1.0 |
01-Dec-2015
|
初始版本 |
由思科工程師貢獻
- 米哈爾·加爾卡斯Cisco TAC工程師
 意見
意見