使用ISE配置ASA VPN安全評估
下載選項
無偏見用語
本產品的文件集力求使用無偏見用語。針對本文件集的目的,無偏見係定義為未根據年齡、身心障礙、性別、種族身分、民族身分、性別傾向、社會經濟地位及交織性表示歧視的用語。由於本產品軟體使用者介面中硬式編碼的語言、根據 RFP 文件使用的語言,或引用第三方產品的語言,因此本文件中可能會出現例外狀況。深入瞭解思科如何使用包容性用語。
關於此翻譯
思科已使用電腦和人工技術翻譯本文件,讓全世界的使用者能夠以自己的語言理解支援內容。請注意,即使是最佳機器翻譯,也不如專業譯者翻譯的內容準確。Cisco Systems, Inc. 對這些翻譯的準確度概不負責,並建議一律查看原始英文文件(提供連結)。
簡介
本文檔介紹如何配置ASA以根據ISE對VPN使用者進行安全評估。
必要條件
需求
思科建議您瞭解以下主題:
- ASA CLI配置和安全套接字層(SSL) VPN配置的基本知識
- ASA上遠端訪問VPN配置的基本知識
- ISE和狀態服務基礎知識
採用元件
本檔案中的資訊是根據以下軟體版本:
- Cisco ASA軟體版本9.16及更高版本
- Microsoft Windows版本7與Cisco AnyConnect安全移動客戶端4.10版
- Cisco ISE版本3.0
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路運作中,請確保您瞭解任何指令可能造成的影響。
背景資訊
Cisco ASA版本9.16支援RADIUS授權更改(CoA) (RFC 5176)。這允許對Cisco ISE的VPN使用者進行定位。在VPN使用者登入後,ASA將網路流量重定向到ISE,在該處為使用者調配了網路准入控制(NAC)代理或Web代理。代理程式會對使用者機器執行特定檢查,以確定其是否符合一組已設定的狀況規則,例如作業系統(OS)、修補程式、防毒軟體、服務、應用程式或登入規則。
然後將狀態驗證結果傳送到ISE。如果電腦被視為投訴,則ISE可以使用新的授權策略集向ASA傳送RADIUS CoA。在成功進行狀態驗證和CoA之後,使用者可以訪問內部資源。
設定
網路圖和流量流程
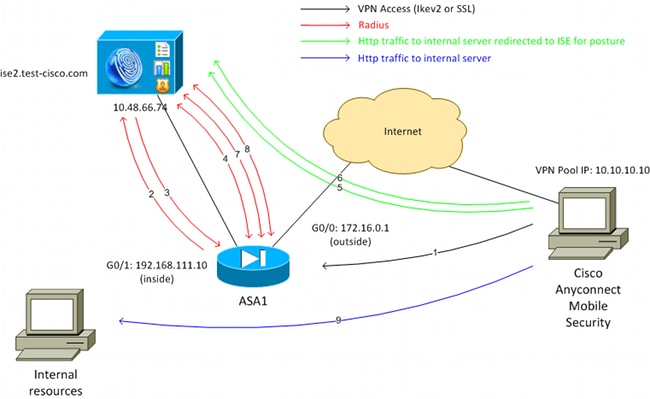
如網路圖所示,流量如下:
- 遠端使用者使用Cisco Anyconnect透過VPN訪問ASA。
- ASA向ISE傳送該使用者的RADIUS訪問請求。
- 該請求在ISE上命中名為ASA916-posture的策略。因此,將返回ASA916-posture授權配置檔案。ISE傳送RADIUS Access-Accept和兩個Cisco屬性-值對:
- url-redirect-acl=redirect -這是在ASA本地定義的訪問控制清單(ACL)名稱,用於確定必須重定向的流量。
- url-redirect -這是遠端使用者必須重定向到的URL。
提示:分配給VPN客戶端的域名系統(DNS)伺服器必須能夠解析重定向URL中返回的完全限定域名(FQDN)。如果配置VPN過濾器以便在隧道組級別限制訪問,請確保客戶端池能夠訪問已配置埠上的ISE伺服器(在本示例中為TCP 8443)。
- url-redirect-acl=redirect -這是在ASA本地定義的訪問控制清單(ACL)名稱,用於確定必須重定向的流量。
- ASA傳送RADIUS Accounting-Request start資料包並接收響應。要向ISE傳送有關會話的所有詳細資訊,需要執行此操作。這些詳細資訊包括session_id、VPN客戶端的外部IP地址和ASA的IP地址。ISE使用session_id來標識該會話。ASA還會定期傳送臨時帳戶資訊,其中最重要的屬性是具有ASA分配給客戶端的IP的Framed-IP-Address(在本示例中為10.10.10.10)。
- 當來自VPN使用者的流量與本地定義的ACL匹配時(重定向)。根據配置,ISE調配NAC代理或Web代理。
- 在客戶端電腦上安裝代理之後,它會自動執行特定的檢查。在本示例中,它搜尋c:\test.txt檔案。它還向ISE傳送狀態報告,其中可能包括使用SWISS協定和埠TCP/UDP 8905的多個交換以訪問ISE。
- 當ISE從代理收到狀態報告時,它會再次處理授權規則。此時,狀態結果為已知,並且已到達另一規則。它會傳送RADIUS CoA封包:
- 如果使用者相容,則傳送允許完全訪問的可下載ACL (DACL)名稱(AuthZ規則ASA916相容)。
- 如果使用者不相容,則傳送允許有限訪問的DACL名稱(AuthZ rule ASA916-not compliant)。
注意:RADIUS CoA始終得到確認;也就是說,ASA向ISE傳送響應以進行確認。
- 如果使用者相容,則傳送允許完全訪問的可下載ACL (DACL)名稱(AuthZ規則ASA916相容)。
- ASA刪除重定向。如果沒有快取DACL,則必須傳送訪問請求以便從ISE下載它們。特定DACL附加到VPN會話。
- VPN使用者下次嘗試訪問網頁時,可以訪問ASA上安裝的DACL允許的所有資源。
如果使用者不合規,則僅授予有限的訪問許可權。
注意:此流模型與使用RADIUS CoA的大多數方案不同。對於有線/無線802.1x身份驗證,RADIUS CoA不包括任何屬性。它只會觸發附加所有屬性(例如DACL)的第二次身份驗證。對於ASA VPN狀態,沒有第二次身份驗證。所有屬性都在RADIUS CoA中返回。VPN會話處於活動狀態,無法更改大多數VPN使用者設定。
組態
使用此部分來配置ASA和ISE。
ASA
以下是思科AnyConnect訪問的基本ASA配置:
ip local pool POOL 10.10.10.10-10.10.10.100 mask 255.255.255.0
interface GigabitEthernet0/0
nameif outside
security-level 0
ip address xxxx 255.255.255.0
!
interface GigabitEthernet0/1
nameif inside
security-level 100
ip address 162.168.111.10 255.255.255.0
aaa-server ISE protocol radius
aaa-server ISE (inside) host 10.48.66.74
key cisco
webvpn
enable outside
anyconnect image disk0:/anyconnect-win-arm64-4.10.06079-webdeploy-k9.pkg 1
anyconnect enable
tunnel-group-list enable
group-policy GP-SSL internal
group-policy GP-SSL attributes
vpn-tunnel-protocol ikev1 ikev2 ssl-client ssl-clientless
tunnel-group RA type remote-access
tunnel-group RA general-attributes
address-pool POOL
authentication-server-group ISE
default-group-policy GP-SSL
tunnel-group RA webvpn-attributes
group-alias RA enable
對於ASA與ISE終端安全評估整合,請確保您:
- 為動態授權配置身份驗證、授權和記帳(AAA)伺服器,以接受CoA。
- 將記帳配置為隧道組,以便向ISE傳送VPN會話詳細資訊。
- 配置臨時記帳,傳送分配給使用者的IP地址並定期更新ISE上的會話狀態
- 配置重定向ACL,以決定是否允許DNS和ISE流量。所有其他HTTP流量重定向到ISE進行安全評估。

附註:只有完成註冊的思科使用者能存取思科內部工具與資訊。
以下是組態範例:
access-list redirect extended deny udp any any eq domain
access-list redirect extended deny ip any host 10.48.66.74
access-list redirect extended deny icmp any any
access-list redirect extended permit tcp any any eq www
aaa-server ISE protocol radius
authorize-only
interim-accounting-update periodic 1
dynamic-authorization
aaa-server ISE (inside) host 10.48.66.74
key cisco
tunnel-group RA general-attributes
address-pool POOL
authentication-server-group ISE
accounting-server-group ISE
default-group-policy GP-SSL
ASA記帳模式:
ASA上的記帳模式必須是單一(預設),否則ASA無法正確處理ISE會話;也就是說,ASA拒絕帶有「操作不受支援」的CoA請求。
ISE
完成以下步驟以配置ISE:
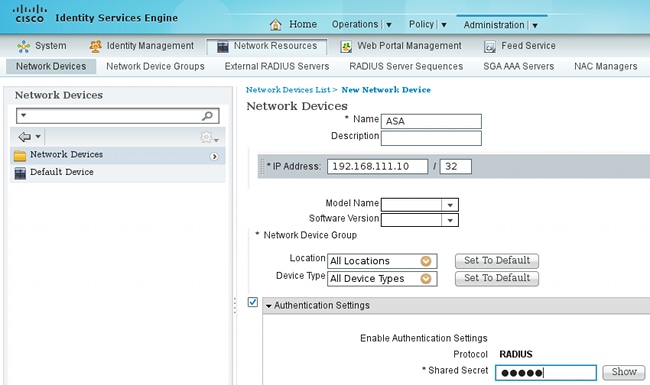
- 導航到管理>網路資源>網路裝置,並將ASA增加為網路裝置:
- 導航到策略>結果>授權>可下載ACL,然後將DACL配置為允許完全訪問。預設ACL配置允許ISE上的所有IP流量:
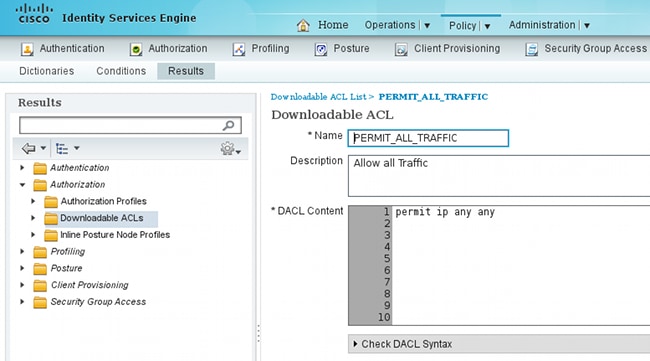
- 配置一個類似的ACL,它提供有限的訪問許可權(針對不合規使用者)。
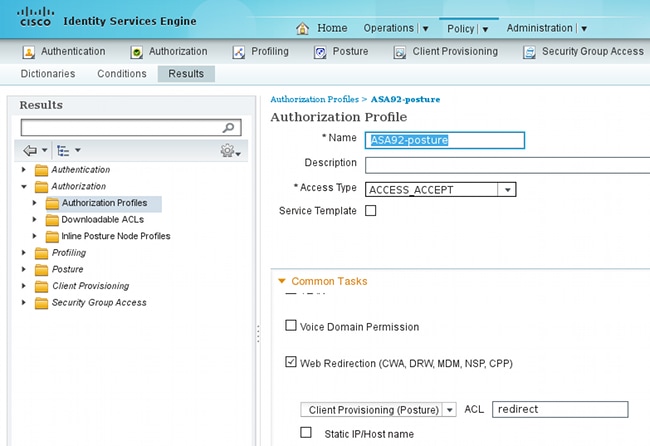
- 導航到策略>結果>授權>授權配置檔案,配置名為ASA92-posture的授權配置檔案,該檔案重定向使用者進行終端安全評估。選中Web Redirection 覈取方塊,從下拉選單中選擇Client Provisioning,並確保redirect顯示在ACL欄位中(該ACL在ASA上本地定義):
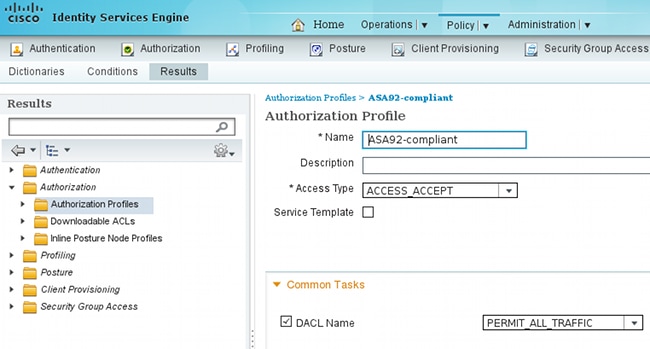
- 配置名為ASA92-compliant的授權配置檔案,該檔案僅必須返回名為PERMIT_ALL_TRAFFIC的DACL,為相容使用者提供完全訪問許可權:
- 配置名為ASA916-not compliant的類似授權配置檔案,該檔案必須返回具有有限訪問許可權的DACL(針對不合規使用者)。
- 導航到策略>授權,然後配置授權規則:
- 建立一條規則,如果安全評估結果符合標準,則允許完全訪問。結果是授權策略ASA916相容。
- 建立一條規則,在狀況結果不符合時允許有限訪問。其結果是授權策略ASA916不相容。
- 確保如果上述兩個規則均未命中,則預設規則返回ASA916-posture,這將在ASA上強制執行重定向。

- 建立一條規則,如果安全評估結果符合標準,則允許完全訪問。結果是授權策略ASA916相容。
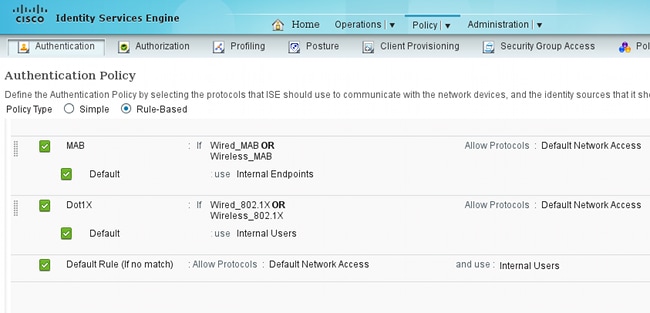
- 預設身份驗證規則檢查內部身份庫中的使用者名稱。如果必須更改此設定(例如,在Active Directory (AD)中檢查),請導航到策略>身份驗證,並進行更改:
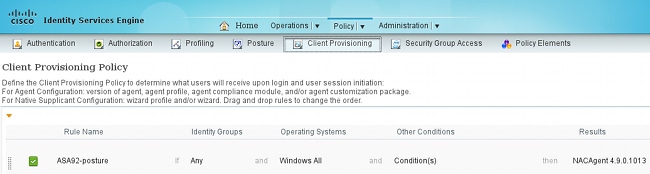
- 導航到策略>客戶端調配,配置調配規則。這些規則決定必須調配的代理型別。在本示例中,只有一個簡單規則,並且ISE為所有Microsoft Windows系統選擇NAC代理:
當代理不在ISE上時,可以下載它們:
- 如果需要,您可以導航到Administration > System > Settings > Proxy,然後為ISE配置Proxy(以訪問Internet)。
- 配置狀態規則,以驗證客戶端配置。您可以配置檢查以下內容的規則:
- 檔案- 存在、版本、日期
- registry -鍵、值、存在
- 應用程式- 程式名稱,執行中,未執行
- service -服務名稱,正在運行,未運行
- 防病毒- 更新定義時,支援100多家供應商(版本)
- 反間諜軟體- 更新定義時,支援100多家供應商(版本)
- 複合條件- 混合所有
- 自定義詞典條件- 大多數ISE詞典的使用
- 檔案- 存在、版本、日期
- 在此範例中,只會執行簡單的檔案存在性檢查。如果客戶端電腦上存在c:\test.txt檔案,則此檔案是相容的,允許完全訪問。導航到策略>條件>檔案條件,然後配置檔案條件:

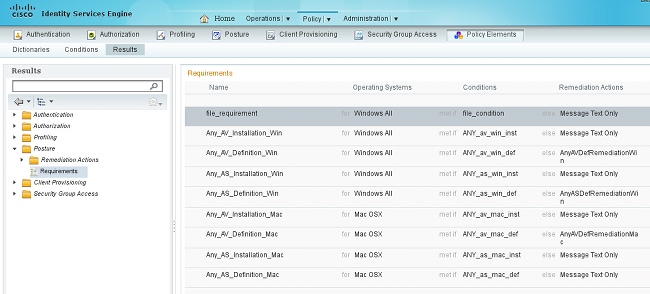
- 導航到策略>結果>狀態>要求,建立要求。當滿足上一個條件時,必須滿足此要求。如果不是,則執行修正動作。可用的補救措施型別有很多種,但在此示例中,最簡單的補救措施是顯示特定消息。
注意:在正常情況下,可以使用檔案補救操作(ISE提供可下載檔案)。
- 導航到策略>狀態,並在狀態規則中使用您在上一步建立的要求(命名為file_requirement)。唯一的狀態規則要求所有Microsoft Windows系統都滿足file_requirement。如果滿足此要求,則表示該站點符合要求;如果不符合,則表示該站點不符合要求。

定期重新評估
預設情況下,狀態為一次性事件。但是,有時需要定期檢查使用者合規性並根據結果調整對資源的訪問。此資訊透過SWISS協定(NAC代理)推送或在應用程式(Web代理)中編碼。
完成以下步驟以檢查使用者合規性:
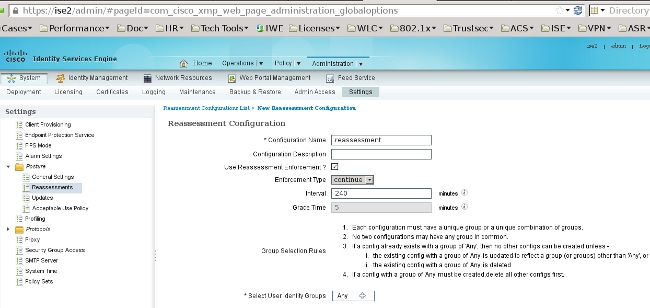
- 導航到Administration > Settings > Posture > Reassessments,並全局啟用重新評估(根據身份組配置):
- 建立與所有重新評估相匹配的狀態條件:

- 建立僅符合初始評量的類似條件:
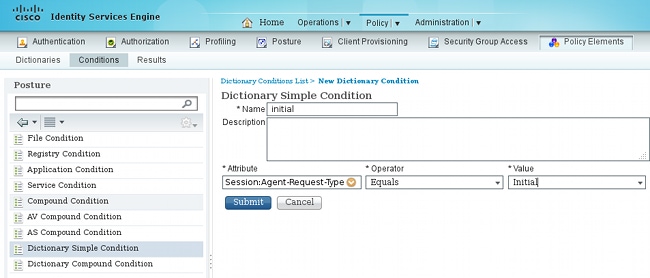
這兩種情況都可用於姿勢規則中。第一條 規則僅與初始評量匹配,第二條規則與所有後續評量匹配:

驗證
為了確認您的配置是否正常工作,請確保按照以下說明完成以下步驟:
- VPN使用者連線到ASA。
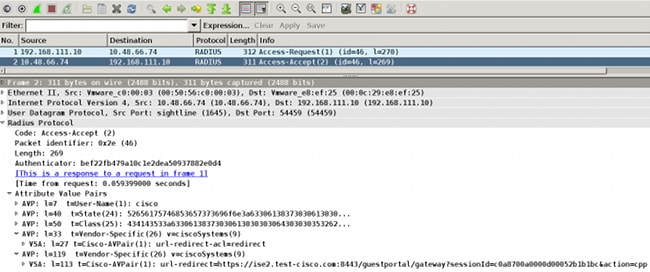
- ASA傳送RADIUS-Request並接收具有url-redirect和url-redirect-acl屬性的響應:
- ISE日誌指示授權與狀態配置檔案匹配(第一個日誌條目):
- ASA向VPN會話增加重定向:
aaa_url_redirect: Added url redirect:https://ise2.test-cisco.com:8443/
guestportal/gateway?sessionId=c0a8700a0000900052b840e6&action=cpp
acl:redirect for 10.10.10.10 - ASA上VPN會話的狀態顯示需要安全評估並重定向HTTP流量:
ASA# show vpn-sessiondb detail anyconnect
Session Type: AnyConnect Detailed
Username : cisco Index : 9
Assigned IP : 10.10.10.10 Public IP : 10.147.24.61
Protocol : AnyConnect-Parent SSL-Tunnel DTLS-Tunnel
License : AnyConnect Essentials
Encryption : AnyConnect-Parent: (1)none SSL-Tunnel: (1)RC4 DTLS-Tunnel: (1)AES128
Hashing : AnyConnect-Parent: (1)none SSL-Tunnel: (1)SHA1 DTLS-Tunnel: (1)SHA1
Bytes Tx : 16077 Bytes Rx : 16497
Pkts Tx : 43 Pkts Rx : 225
Pkts Tx Drop : 0 Pkts Rx Drop : 0
Group Policy : GP-SSL Tunnel Group : RA
Login Time : 14:55:50 CET Mon Dec 23 2013
Duration : 0h:01m:34s
Inactivity : 0h:00m:00s
VLAN Mapping : N/A VLAN : none
Audt Sess ID : c0a8700a0000900052b840e6
Security Grp : 0
AnyConnect-Parent Tunnels: 1
SSL-Tunnel Tunnels: 1
DTLS-Tunnel Tunnels: 1
AnyConnect-Parent:
Tunnel ID : 9.1
Public IP : 10.147.24.61
Encryption : none Hashing : none
TCP Src Port : 50025 TCP Dst Port : 443
Auth Mode : userPassword
Idle Time Out: 30 Minutes Idle TO Left : 28 Minutes
Client OS : win
Client Type : AnyConnect
Client Ver : Cisco AnyConnect VPN Agent for Windows 3.1.02040
Bytes Tx : 5204 Bytes Rx : 779
Pkts Tx : 4 Pkts Rx : 1
Pkts Tx Drop : 0 Pkts Rx Drop : 0
SSL-Tunnel:
Tunnel ID : 9.2
Assigned IP : 10.10.10.10 Public IP : 10.147.24.61
Encryption : RC4 Hashing : SHA1
Encapsulation: TLSv1.0 TCP Src Port : 50044
TCP Dst Port : 443 Auth Mode : userPassword
Idle Time Out: 30 Minutes Idle TO Left : 28 Minutes
Client OS : Windows
Client Type : SSL VPN Client
Client Ver : Cisco AnyConnect VPN Agent for Windows 3.1.02040
Bytes Tx : 5204 Bytes Rx : 172
Pkts Tx : 4 Pkts Rx : 2
Pkts Tx Drop : 0 Pkts Rx Drop : 0
DTLS-Tunnel:
Tunnel ID : 9.3
Assigned IP : 10.10.10.10 Public IP : 10.147.24.61
Encryption : AES128 Hashing : SHA1
Encapsulation: DTLSv1.0 UDP Src Port : 63296
UDP Dst Port : 443 Auth Mode : userPassword
Idle Time Out: 30 Minutes Idle TO Left : 29 Minutes
Client OS : Windows
Client Type : DTLS VPN Client
Client Ver : Cisco AnyConnect VPN Agent for Windows 3.1.02040
Bytes Tx : 5669 Bytes Rx : 18546
Pkts Tx : 35 Pkts Rx : 222
Pkts Tx Drop : 0 Pkts Rx Drop : 0
ISE Posture:
Redirect URL : https://ise2.test-cisco.com:8443/guestportal/gateway?
sessionId=c0a8700a0000900052b840e6&action=cpp
Redirect ACL : redirect - 啟動與重定向ACL匹配的HTTP流量的客戶端被重定向到ISE:
aaa_url_redirect: Created proxy for 10.10.10.10
aaa_url_redirect: Sending url redirect:https://ise2.test-cisco.com:8443/
guestportal/gateway?sessionId=c0a8700a0000900052b840e6&action=cpp
for 10.10.10.10 - 客戶端被重定向到ISE以進行安全評估:

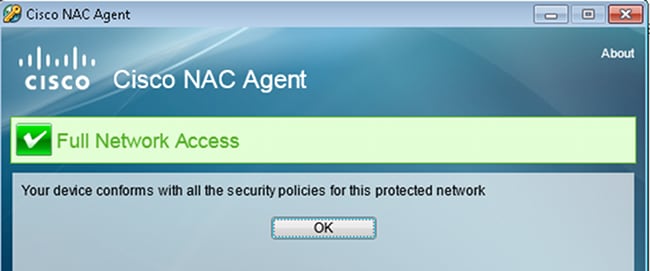
- 已安裝NAC代理。安裝NAC代理後,它會透過SWISS協定下載狀態規則並執行檢查以確定合規性。然後,安全評估報告將傳送到ISE。
- ISE接收狀態報告,重新評估授權規則,並且(如果需要)更改授權狀態並傳送CoA。這可以在ise-psc.log中驗證:
cisco.cpm.posture.runtime.PostureHandlerImpl -:cisco:c0a8700a0000900052b840e6
:::- Decrypting report
cisco.cpm.posture.runtime.PostureManager -:cisco:c0a8700a0000900052b840e6
:::- User cisco belongs to groups NAC Group:NAC:IdentityGroups:User Identity
Groups:Employee,NAC Group:NAC:IdentityGroups:An
cisco.cpm.posture.runtime.PostureManager -:cisco:c0a8700a0000900052b840e6
:::- Posture report token for endpoint mac 08-00-27-CD-E8-A2 is Healthy
cisco.cpm.posture.runtime.PostureManager -:cisco:c0a8700a0000900052b840e6
:::- Posture state is compliant for endpoint with mac 08-00-27-CD-E8-A2
cisco.cpm.posture.runtime.PostureCoA -:cisco:c0a8700a0000900052b840e6
:::- Posture CoA is triggered for endpoint [null] with session
[c0a8700a0000900052b840e6] - ISE傳送一個RADIUS CoA,其中包括session_id和允許完全訪問的DACL名稱:

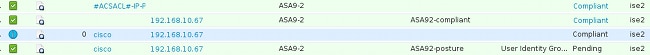
這反映在ISE日誌中:
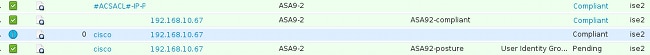
- 第一個日誌條目用於返回狀態配置檔案(帶重定向)的初始身份驗證。
- 第二個日誌條目將在收到合規的SWISS報告後填充。
- 第三個日誌條目在傳送CoA時與確認一起填充(描述為Dynamic Authorization Succeeded)。
- 最終日誌條目在ASA下載DACL時建立。
- 第一個日誌條目用於返回狀態配置檔案(帶重定向)的初始身份驗證。
- ASA上的調試顯示已接收CoA並刪除重定向。如果需要,ASA會下載DACL:
ASA# Received RAD_COA_REQUEST
RADIUS packet decode (CoA-Request)
Radius: Value (String) =
41 43 53 3a 43 69 73 63 6f 53 65 63 75 72 65 2d | ACS:CiscoSecure-
44 65 66 69 6e 65 64 2d 41 43 4c 3d 23 41 43 53 | Defined-ACL=#ACS
41 43 4c 23 2d 49 50 2d 50 45 52 4d 49 54 5f 41 | ACL#-IP-PERMIT_A
4c 4c 5f 54 52 41 46 46 49 43 2d 35 31 65 66 37 | LL_TRAFFIC-51ef7
64 62 31 | db1
Got AV-Pair with value audit-session-id=c0a8700a0000900052b840e6
Got AV-Pair with value ACS:CiscoSecure-Defined-ACL=
#ACSACL#-IP-PERMIT_ALL_TRAFFIC-51ef7db1
aaa_url_redirect: Deleted url redirect for 10.10.10.10 - 在VPN會話之後,Cisco為使用者應用了DACL(完全訪問):
ASA# show vpn-sessiondb detail anyconnect
Session Type: AnyConnect Detailed
Username : cisco Index : 9
Assigned IP : 10.10.10.10 Public IP : 10.147.24.61
Protocol : AnyConnect-Parent SSL-Tunnel DTLS-Tunnel
License : AnyConnect Essentials
Encryption : AnyConnect-Parent: (1)none SSL-Tunnel: (1)RC4 DTLS-Tunnel: (1)AES128
Hashing : AnyConnect-Parent: (1)none SSL-Tunnel: (1)SHA1 DTLS-Tunnel: (1)SHA1
Bytes Tx : 94042 Bytes Rx : 37079
Pkts Tx : 169 Pkts Rx : 382
Pkts Tx Drop : 0 Pkts Rx Drop : 0
Group Policy : GP-SSL Tunnel Group : RA
Login Time : 14:55:50 CET Mon Dec 23 2013
Duration : 0h:05m:30s
Inactivity : 0h:00m:00s
VLAN Mapping : N/A VLAN : none
Audt Sess ID : c0a8700a0000900052b840e6
Security Grp : 0
AnyConnect-Parent Tunnels: 1
SSL-Tunnel Tunnels: 1
DTLS-Tunnel Tunnels: 1
AnyConnect-Parent:
Tunnel ID : 9.1
Public IP : 10.147.24.61
Encryption : none Hashing : none
TCP Src Port : 50025 TCP Dst Port : 443
Auth Mode : userPassword
Idle Time Out: 30 Minutes Idle TO Left : 24 Minutes
Client OS : win
Client Type : AnyConnect
Client Ver : Cisco AnyConnect VPN Agent for Windows 3.1.02040
Bytes Tx : 5204 Bytes Rx : 779
Pkts Tx : 4 Pkts Rx : 1
Pkts Tx Drop : 0 Pkts Rx Drop : 0
SSL-Tunnel:
Tunnel ID : 9.2
Assigned IP : 10.10.10.10 Public IP : 10.147.24.61
Encryption : RC4 Hashing : SHA1
Encapsulation: TLSv1.0 TCP Src Port : 50044
TCP Dst Port : 443 Auth Mode : userPassword
Idle Time Out: 30 Minutes Idle TO Left : 24 Minutes
Client OS : Windows
Client Type : SSL VPN Client
Client Ver : Cisco AnyConnect VPN Agent for Windows 3.1.02040
Bytes Tx : 5204 Bytes Rx : 172
Pkts Tx : 4 Pkts Rx : 2
Pkts Tx Drop : 0 Pkts Rx Drop : 0
Filter Name : #ACSACL#-IP-PERMIT_ALL_TRAFFIC-51ef7db1
DTLS-Tunnel:
Tunnel ID : 9.3
Assigned IP : 10.10.10.10 Public IP : 10.147.24.61
Encryption : AES128 Hashing : SHA1
Encapsulation: DTLSv1.0 UDP Src Port : 63296
UDP Dst Port : 443 Auth Mode : userPassword
Idle Time Out: 30 Minutes Idle TO Left : 29 Minutes
Client OS : Windows
Client Type : DTLS VPN Client
Client Ver : Cisco AnyConnect VPN Agent for Windows 3.1.02040
Bytes Tx : 83634 Bytes Rx : 36128
Pkts Tx : 161 Pkts Rx : 379
Pkts Tx Drop : 0 Pkts Rx Drop : 0
Filter Name : #ACSACL#-IP-PERMIT_ALL_TRAFFIC-51ef7db1
注意:即使CoA未連線任何DACL,ASA也始終刪除重定向規則。
疑難排解
本節提供的資訊可用於對組態進行疑難排解。
ISE上的調試
導航到管理>日誌記錄>調試日誌配置以啟用調試。思科建議您為以下各項啟用臨時調試:
- 瑞士
- 不間斷轉發(NSF)
- NSF會話
- 提供
- 姿勢
在CLI中輸入以下命令以檢視調試:
ise2/admin# show logging application ise-psc.log tail count 100
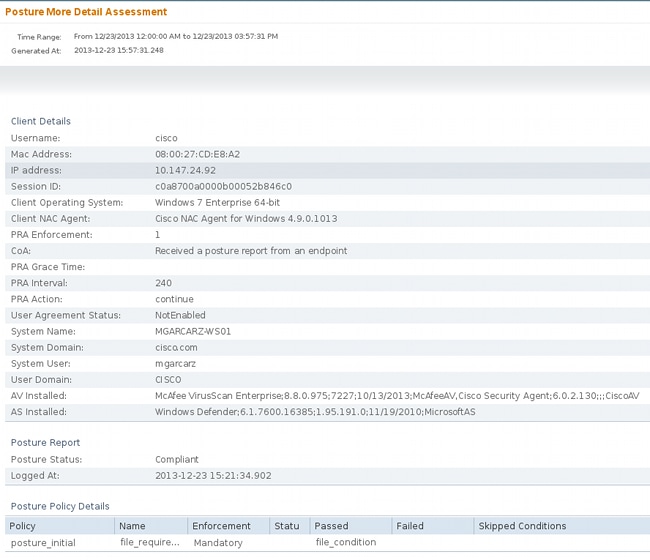
導航到操作>報告> ISE報告>終端和使用者>終端安全評估詳細資訊評估以檢視終端安全評估報告:
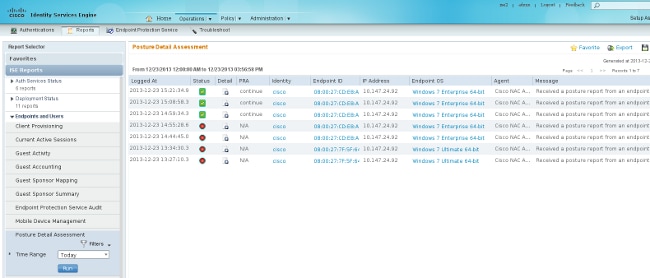
在Posture More Detail Assessment頁面上,將顯示具有要求名稱的策略名稱以及結果:
ASA上的調試
您可以在ASA上啟用以下調試:
- debug aaa url-redirect
- debug aaa authorization
- debug radius dynamic-authorization
- debug radius decode
- debug radius user cisco
代理程式的偵錯
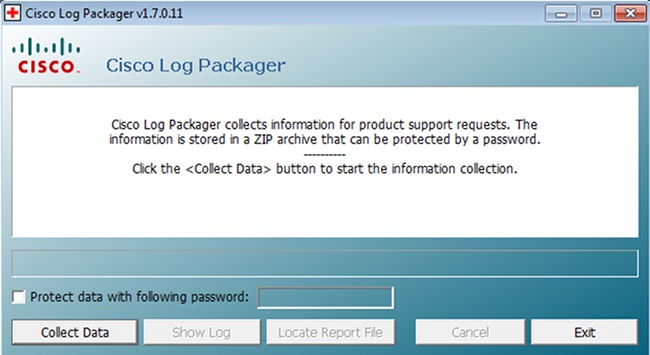
對於NAC Agent,可以使用Cisco Log Packager(從GUI或CLI啟動)收集調試,並使用CCAAgentLogPackager.app。
提示:您可以使用技術支援中心(TAC)工具將結果解碼。
若要擷取Web代理程式的記錄,請瀏覽以下位置:
- C: > Document and Settings > <user> > Local Settings > Temp > webagent.log(使用TAC工具解碼)
- C: > Document and Settings > <user> > Local Settings > Temp > webagentsetup.log
注意:如果日誌不在這些位置,請驗證TEMP環境變數。
NAC代理狀態故障
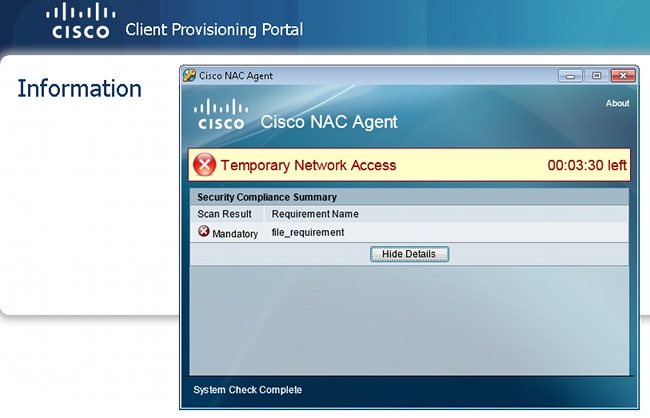
如果終端安全評估失敗,則會向使用者顯示原因:
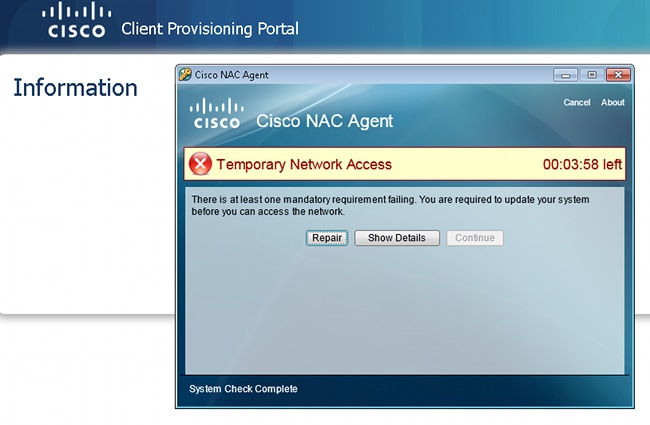
然後允許使用者採取補救動作(若已設定):
相關資訊
修訂記錄
| 修訂 | 發佈日期 | 意見 |
|---|---|---|
1.0 |
09-May-2014
|
初始版本 |
 意見
意見