Configurar vazamentos de VRF no IOS XE
Opções de download
Linguagem imparcial
O conjunto de documentação deste produto faz o possível para usar uma linguagem imparcial. Para os fins deste conjunto de documentação, a imparcialidade é definida como uma linguagem que não implica em discriminação baseada em idade, deficiência, gênero, identidade racial, identidade étnica, orientação sexual, status socioeconômico e interseccionalidade. Pode haver exceções na documentação devido à linguagem codificada nas interfaces de usuário do software do produto, linguagem usada com base na documentação de RFP ou linguagem usada por um produto de terceiros referenciado. Saiba mais sobre como a Cisco está usando a linguagem inclusiva.
Sobre esta tradução
A Cisco traduziu este documento com a ajuda de tecnologias de tradução automática e humana para oferecer conteúdo de suporte aos seus usuários no seu próprio idioma, independentemente da localização. Observe que mesmo a melhor tradução automática não será tão precisa quanto as realizadas por um tradutor profissional. A Cisco Systems, Inc. não se responsabiliza pela precisão destas traduções e recomenda que o documento original em inglês (link fornecido) seja sempre consultado.
Contents
Introdução
Este documento descreve e fornece exemplos de configurações para métodos comuns de vazamento de rota de Virtual Routing and Forwarding (VRF).
Pré-requisitos
Requisitos
A Cisco recomenda que você tenha conhecimento destes tópicos:
- Protocolo de gateway de borda (BGP)
- Redistribuição do Routing Protocol
- VRF
- Software Cisco IOS® XE
Para obter mais informações sobre esses tópicos, consulte:
Redistribuir protocolos de roteamento
Exemplo de Configuração de Redistribuição Mútua entre EIGRP e BGP
Entender a redistribuição de rotas OSPF no BGP
Componentes Utilizados
As informações neste documento são baseadas nos roteadores com Cisco IOS® XE versões 16.12.X e 17.X
As informações neste documento foram criadas a partir de dispositivos em um ambiente de laboratório específico. Todos os dispositivos utilizados neste documento foram iniciados com uma configuração (padrão) inicial. Se a rede estiver ativa, certifique-se de que você entenda o impacto potencial de qualquer comando.
Informações de Apoio
O VRF permite que um roteador mantenha tabelas de roteamento separadas para diferentes redes virtuais. Quando as exceções são necessárias, o vazamento de rota VRF permite que algum tráfego seja roteado entre os VRFs sem o uso de rotas estáticas.
Cenário 1 - Vazamento de rota VRF entre BGP e IGP ( EIGRP )
O Cenário 1 fornece um exemplo de vazamento de rota VRF entre BGP e EIGRP. Esse método pode ser usado para outros IGPs.
Diagrama de Rede
O Diagrama de Rede, como visto na Imagem 1, mostra a topologia da camada 3 onde o vazamento de rota é necessário.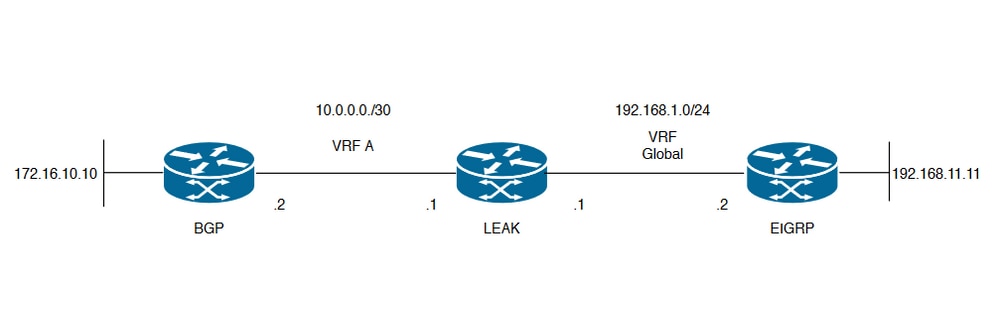
Imagem 1. Topologia de Vazamento de Rota para o Cenário 1
O VAZAMENTO do roteador tem uma vizinhança BGP para um vizinho no VRF A e um vizinho EIGRP no VRF global. O dispositivo 192.168.11.11 precisa ser capaz de se conectar ao dispositivo 172.16.10.10 através da rede.
O VAZAMENTO do roteador não pode rotear entre os dois, pois as rotas estão em VRFs diferentes. Essas tabelas de roteamento mostram as rotas atuais por VRF e indicam quais rotas precisam vazar entre o VRF global e o VRF A.
Tabelas de roteamento LEAK:
| Tabela de Roteamento EIGRP (Roteamento Global) |
LEAK#show ip route
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, m - OMP
n - NAT, Ni - NAT inside, No - NAT outside, Nd - NAT DIA
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
H - NHRP, G - NHRP registered, g - NHRP registration summary
o - ODR, P - periodic downloaded static route, l - LISP
a - application route
+ - replicated route, % - next hop override, p - overrides from PfR
Gateway of last resort is not set
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.1.0/24 is directly connected, GigabitEthernet2
L 192.168.1.1/32 is directly connected, GigabitEthernet2
192.168.11.0/32 is subnetted, 1 subnets
D 192.168.11.11 [90/130816] via 192.168.1.2, 02:30:29, GigabitEthernet2 >> Route to be exchange to the VRF A routing table.
| Tabela de roteamento VRF A |
LEAK#show ip route vrf A
Routing Table: A
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, m - OMP
n - NAT, Ni - NAT inside, No - NAT outside, Nd - NAT DIA
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
H - NHRP, G - NHRP registered, g - NHRP registration summary
o - ODR, P - periodic downloaded static route, l - LISP
a - application route
+ - replicated route, % - next hop override, p - overrides from PfR
Gateway of last resort is not set
10.0.0.0/8 is variably subnetted, 2 subnets, 2 masks
C 10.0.0.0/30 is directly connected, GigabitEthernet1
L 10.0.0.1/32 is directly connected, GigabitEthernet1
172.16.0.0/32 is subnetted, 1 subnets
B 172.16.10.10 [200/0] via 10.0.0.2, 01:47:58 >> Route to be exchange to the global routing table.
Configurar
Conclua os procedimentos para criar o vazamento entre as duas tabelas de roteamento:
Step 1.
Create route-maps to filter the routes to be injected in both routing tables.
LEAK(config)#Route-map VRF_TO_EIGRP
LEAK(config-route-map)#match ip address prefix-list VRF_TO_EIGRP
LEAK(config-route-map)#exit
!
Prefix-list created to match the host that is attached to the previous route-map configured.
!
ip prefix-list VRF_TO_EIGRP permit 172.16.10.10/32
or
LEAK(config)#Route-map VRF_TO_EIGRP
LEAK(config-route-map)# match ip address 10
LEAK(config-route-map)#exit
!
ACL created to match the host that is attached to the previous route-map.
!
LEAK#show ip access-lists 10
10 permit 172.16.10.10
LEAK(config)#Route-map EIGRP_TO_VRF
LEAK(config-route-map)#match ip address prefix-list EIGRP_TO_VRF
LEAK(config-route-map)#exit
LEAK(config)#
!
Prefix-list created to match the host that is attached to the previous route-map configured.
!
ip prefix-list EIGRP_TO_VRF permit 192.168.11.11/32
or
LEAK(config)#Route-map EIGRP_TO_VRF
LEAK(config-route-map)#match ip address 20
LEAK(config-route-map)#exit
LEAK(config)#
!
ACL created to match the host that is attached to the previous route-map.
!
LEAK#show ip access-list 20
10 permit 192.168.11.11
Step 2.
Define the import/export maps and add the route-map names.
LEAK(config)#vrf definition A
LEAK(config-vrf)#address-family ipv4
LEAK(config-vrf-af)#import ipv4 unicast map EIGRP_TO_VRF >> Import the global routing table routes at the VRF routing table.
LEAK(config-vrf-af)#export ipv4 unicast map VRF_TO_EIGRP >> Export the VRF routes to the Global Routing Table.
LEAK(config-vrf-af)#end
Step 3.
Proceed with the dual redistribution.
Redistribute EIGRP
LEAK(config)#router bgp 1
LEAK(config-router)#redistribute eigrp 1
LEAK(config-router)#end
Redistribution BGP
LEAK(config)#router eigrp 1
LEAK(config-router)#redistribute bgp 1 metric 100 1 255 1 1500
LEAK(config-router)#end
Verificar
Routing table from VRF A
LEAK#show ip route vrf A
Routing Table: A
< Snip for resume >
10.0.0.0/8 is variably subnetted, 2 subnets, 2 masks
C 10.0.0.0/30 is directly connected, GigabitEthernet1
L 10.0.0.1/32 is directly connected, GigabitEthernet1
172.16.0.0/32 is subnetted, 1 subnets
B 172.16.10.10 [200/0] via 10.0.0.2, 00:58:53
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
B 192.168.1.0/24 is directly connected, 00:01:00, GigabitEthernet2
L 192.168.1.1/32 is directly connected, GigabitEthernet2
192.168.11.0/32 is subnetted, 1 subnets
B 192.168.11.11 [20/130816] via 192.168.1.2, 00:01:00, GigabitEthernet2 >> Route from global routing table at VRF A routing table.
Global Routing Table (EIGRP)
LEAK#show ip route
< snip for resume >
Gateway of last resort is not set
172.16.0.0/32 is subnetted, 1 subnets
B 172.16.10.10 [200/0] via 10.0.0.2 (A), 00:04:47 >> Route from VRF A at global routing table.
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.1.0/24 is directly connected, GigabitEthernet2
L 192.168.1.1/32 is directly connected, GigabitEthernet2
192.168.11.0/32 is subnetted, 1 subnets
D 192.168.11.11 [90/130816] via 192.168.1.2, 01:03:35, GigabitEthernet2
LEAK#
Cenário 2 - Vazamento de VRF entre VRF A e VRF B
O cenário 2 descreve o vazamento entre dois VRFs diferentes.
Diagrama de Rede
Este documento usa esta configuração de rede:
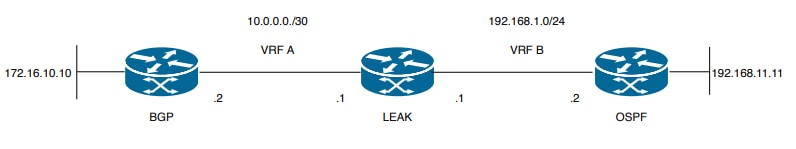
Imagem 2. Topologia de Vazamento de Rota para o Cenário 2
O VAZAMENTO do roteador tem uma vizinhança BGP com um vizinho no VRF A e um vizinho OSPF no VRF B. O dispositivo 192.168.11.11 precisa se conectar ao dispositivo 172.16.10.10 através da rede.
O VAZAMENTO do roteador não pode rotear entre os dois, pois as rotas estão em VRFs diferentes. Essas tabelas de roteamento mostram as rotas atuais por VRF e indicam quais rotas precisam vazar entre o VRF A e o VRF B.
Tabela de roteamento LEAK:
| Tabela de roteamento VRF A |
LEAK#show ip route vrf A
Routing Table: A
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, m - OMP
n - NAT, Ni - NAT inside, No - NAT outside, Nd - NAT DIA
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
H - NHRP, G - NHRP registered, g - NHRP registration summary
o - ODR, P - periodic downloaded static route, l - LISP
a - application route
+ - replicated route, % - next hop override, p - overrides from PfR
Gateway of last resort is not set
10.0.0.0/8 is variably subnetted, 2 subnets, 2 masks
C 10.0.0.0/30 is directly connected, Ethernet0/0
L 10.0.0.2/32 is directly connected, Ethernet0/0
172.16.0.0/32 is subnetted, 1 subnets
B 172.16.10.10 [200/0] via 10.0.0.1, 00:03:08 >> Route to be exchange to routing table VRF B.
| Tabela de roteamento VRF B |
LEAK#show ip route vrf B
Routing Table: B
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, m - OMP
n - NAT, Ni - NAT inside, No - NAT outside, Nd - NAT DIA
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
H - NHRP, G - NHRP registered, g - NHRP registration summary
o - ODR, P - periodic downloaded static route, l - LISP
a - application route
+ - replicated route, % - next hop override, p - overrides from PfR
Gateway of last resort is not set
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.1.0/24 is directly connected, Ethernet0/1
L 192.168.1.2/32 is directly connected, Ethernet0/1
192.168.11.0/32 is subnetted, 1 subnets
O 192.168.11.11 [110/11] via 192.168.1.1, 00:58:45, Ethernet0/1 >> Route to be exchange to routing table VRF A.
Configurar
Conclua estes procedimentos para criar o vazamento entre as duas tabelas de roteamento:
Step 1.
Create route-maps to filter the routes to be injected in both routing tables.
LEAK(config)#Route-map VRFA_TO_VRFB
LEAK(config-route-map)#match ip address prefix-list VRFA_TO_VRFB
LEAK(config-route-map)#exit
!
Prefix-list created to match the host and IP segment that is attached to the previous route-map configured.
!
ip prefix-list VRFA_TO_VRFB permit 172.16.10.10/32
ip prefix-list VRFA_TO_VRFB permit 10.0.0.0/30
or
LEAK(config)#Route-map VRFA_TO_VRFB
LEAK(config-route-map)#match ip address 10
LEAK(config-route-map)#exit
!
ACL created to match the host and IP segment that is attached to the previous route-map.
!
LEAK#show ip access-lists 10
10 permit 172.16.10.10
20 permit 10.0.0.0
LEAK(config)#Route-map VRFB_TO_VRFA
LEAK(config-route-map)#match ip address prefix-list VRFB_TO_VRFA
LEAK(config-route-map)#exit
!
Prefix-list created to match the host and IP segment that is attached to the previous route-map configured.
!
ip prefix-list VRFB_TO_VRFA permit 192.168.11.11/32
ip prefix-list VRFB_TO_VRFA permit 192.168.1.0/24
or
LEAK(config)#Route-map VRFB_TO_VRFA
LEAK(config-route-map)#match ip address 20
LEAK(config-route-map)#exit
!
ACL created to match the host and IP segment that is attached to the previous route-map configured.
!
LEAK#show ip access-lists 20
10 permit 192.168.11.11
20 permit 192.168.1.0
Step 2.
At the VRFs configure the import/export map, use the route-map names to leak the routes.
LEAK(config)#vrf definition A
LEAK(config-vrf)#address-family ipv4
LEAK(config-vrf-af)#export map VRFA_TO_VRFB
LEAK(config-vrf-af)#import map VRFB_TO_VRFA
LEAK(config)#vrf definition B
LEAK(config-vrf)#address-family ipv4
LEAK(config-vrf-af)#export map VRFB_TO_VRFA
LEAK(config-vrf-af)#import map VRFA_TO_VRFB
Step 3.
Add the route-target to import and export the route distinguisher from both VRFs.
! --- Current configuration for VRF A
vrf definition A
rd 1:2
!
address-family ipv4
route-target export 1:2
route-target import 1:1
exit-address-family
! --- Current configuration from VRF B
vrf definition B
rd 2:2
!
address-family ipv4
exit-address-family
! --- Import the routes from VRF B into VRF A
LEAK(config)#vrf definition A
LEAK(config-vrf)#address-family ipv4
LEAK(config-vrf-af)#route-target import 2:2
! --- Import routes from VRF A to VRF B and export routes from VRF B
LEAK(config-vrf-af)#vrf definition B
LEAK(config-vrf)#address-family ipv4
LEAK(config-vrf-af)#route-target import 1:2
LEAK(config-vrf-af)#route-target export 2:2
Verificar
Check the Routing Tables
VRF A Routing Table
LEAK#show ip route vrf A
Routing Table: A
< Snip for resume >
10.0.0.0/8 is variably subnetted, 2 subnets, 2 masks
C 10.0.0.0/30 is directly connected, Ethernet0/0
L 10.0.0.2/32 is directly connected, Ethernet0/0
172.16.0.0/32 is subnetted, 1 subnets
B 172.16.10.10 [200/0] via 10.0.0.1, 00:07:20
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
B 192.168.1.0/24 is directly connected, 00:00:10, Ethernet0/1
L 192.168.1.2/32 is directly connected, Ethernet0/1
192.168.11.0/32 is subnetted, 1 subnets
B 192.168.11.11 [20/11] via 192.168.1.1 (B), 00:00:10, Ethernet0/1 >> Route from VRF B routing table at VRF A.
VRF B Routing Table
LEAK#show ip route vrf B
Routing Table: B
< Snip for resume >
10.0.0.0/30 is subnetted, 1 subnets
B 10.0.0.0 [200/0] via 10.0.0.1 (A), 00:00:15
172.16.0.0/32 is subnetted, 1 subnets
B 172.16.10.10 [200/0] via 10.0.0.1 (A), 00:00:15 >> Route from VRF A routing table at VRF B.
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.1.0/24 is directly connected, Ethernet0/1
L 192.168.1.2/32 is directly connected, Ethernet0/1
192.168.11.0/32 is subnetted, 1 subnets
O 192.168.11.11 [110/11] via 192.168.1.1, 01:05:12, Ethernet0/1
Cenário 3 - Vazamento de VRF entre OSPF (VRF) e EIGRP (Global) com BGP (Opcional)
O cenário 3 descreve o vazamento de rota entre dois IGPs (VRF B e VRF global).
Diagrama de Rede
Este documento utiliza a seguinte configuração de rede: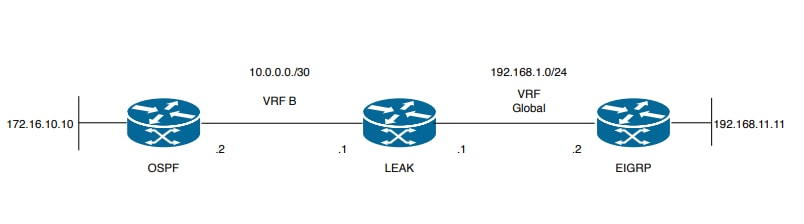
Imagem 3. Topologia de Vazamento de Rota para o Cenário 3
O VAZAMENTO do roteador tem uma vizinhança OSPF com um vizinho no VRF B e um vizinho EIGRP no VRF global. O dispositivo 172.16.10.10 precisa poder se conectar ao dispositivo 192.168.11.11 através da rede.
O VAZAMENTO do roteador não consegue conectar esses dois hosts. Essas tabelas de roteamento mostram as rotas atuais por VRF e indicam quais rotas precisam vazar entre o VRF B e o VRF Global.
Tabela de roteamento LEAK:
| Tabela de Roteamento EIGRP (EIGRP) |
LEAK#show ip route
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, m - OMP
n - NAT, Ni - NAT inside, No - NAT outside, Nd - NAT DIA
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
H - NHRP, G - NHRP registered, g - NHRP registration summary
o - ODR, P - periodic downloaded static route, l - LISP
a - application route
+ - replicated route, % - next hop override, p - overrides from PfR
Gateway of last resort is not set
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.1.0/24 is directly connected, Ethernet0/1
L 192.168.1.1/32 is directly connected, Ethernet0/1
192.168.11.0/32 is subnetted, 1 subnets
D 192.168.11.11 [90/1024640] via 192.168.1.2, 01:08:38, Ethernet0/1 >> Route to be exchange from global routing table at VRF B routing table.
| Tabela de Roteamento VRF B (OSPF) |
LEAK#show ip route vrf B
Routing Table: B
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, m - OMP
n - NAT, Ni - NAT inside, No - NAT outside, Nd - NAT DIA
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
H - NHRP, G - NHRP registered, g - NHRP registration summary
o - ODR, P - periodic downloaded static route, l - LISP
a - application route
+ - replicated route, % - next hop override, p - overrides from PfR
Gateway of last resort is not set
10.0.0.0/8 is variably subnetted, 2 subnets, 2 masks
C 10.0.0.0/30 is directly connected, Ethernet0/0
L 10.0.0.2/32 is directly connected, Ethernet0/0
172.16.0.0/32 is subnetted, 1 subnets
O 172.16.10.10 [110/11] via 10.0.0.1, 01:43:45, Ethernet0/0 >> Route to be exchange from routing table VRF B at global routing table.
Configurar
Conclua estes procedimentos para criar o vazamento entre as duas tabelas de roteamento:
Step 1.
Create route-maps for import and export to be injected in both routing tables.
LEAK(config)#Route-map OSPF_TO_EIGRP
LEAK(config-route-map)#match ip address prefix-list OSPF_TO_EIGRP
LEAK(config-route-map)#exit
!
Prefix-list created to match the host that is attached to the previous route-map configured.
!
ip prefix-list OSPF_TO_EIGRP permit 172.16.10.10/32
ip prefix-list OSPF_TO_EIGRP permit 10.0.0.0/30
or
LEAK(config)#Route-map OSPF_TO_EIGRP
LEAK(config-route-map)#match ip address 10
LEAK(config-route-map)#exit
!
ACL created to match the host that is attached to the previous route-map.
!
LEAK#show ip access-lists 10
10 permit 172.16.10.10
20 permit 10.0.0.0
LEAK(config)#Route-map EIGRP_TO_OSPF
LEAK(config-route-map)#match ip address prefix-list EIGRP_TO_OSPF
LEAK(config-route-map)#exit
!
Prefix-list created to match the host that is attached to the previous route-map configured.
!
ip prefix-list EIGRP_TO_OSPF permit 192.168.11.11/32
ip prefix-list EIGRP_TO_OSPF permit 192.168.1.0/24
or
LEAK(config)#Route-map EIGRP_TO_OSPF
LEAK(config-route-map)#match ip address 20
LEAK(config-route-map)#exit
!
ACL created to match the host that is attached to the previous route-map.
!
LEAK#show ip access-lists 20
10 permit 192.168.11.11
20 permit 192.168.1.0/24
Step 2.
Add the import/export maps in order to match the route-map names.
Current configuration
!
vrf definition B
rd 1:2
!
address-family ipv4
exit-address-family
!
!
LEAK(config-vrf)#vrf definition B
LEAK(config-vrf)#address-family ipv4
LEAK(config-vrf-af)#import ipv4 unicast map EIGRP_TO_OSPF
LEAK(config-vrf-af)#export ipv4 unicast map OSPF_TO_EIGRP
Step 3.
To perform the leak is necessary to create a BGP process, in order to redistribute
the IGPs protocols.
router bgp 1
bgp log-neighbor-changes
!
address-family ipv4 vrf B >> Include the address-family to inject VRF B routing table (OSPF)
!
exit-address-family
Note: Certifique-se de que o VRF tenha um diferenciador de rota configurado para evitar o erro:"%vrf B does not have rd configured, configure "rd" before configuring import route-map"
Step 4.
Create a Dual Redistribution.
IGPs redistribution.
LEAK(config-router)#router bgp 1
LEAK(config-router)#redistribute eigrp 1
!
LEAK(config-router)#address-family ipv4 vrf B
LEAK(config-router-af)#redistribute ospf 1 match internal external 1 external 2
LEAK(config-router-af)#end
BGP Redistribution
LEAK(config)#router ospf 1 vrf B
LEAK(config-router)#redistribute bgp 1
!
LEAK(config-router)#router eigrp TAC
LEAK(config-router)#
LEAK(config-router)# address-family ipv4 unicast autonomous-system 1
LEAK(config-router-af)#
LEAK(config-router-af)# topology base
LEAK(config-router-af-topology)#redistribute bgp 1 metric 100 1 255 1 1500
Verificar
Verifique as tabelas de roteamento
| Tabela de roteamento global |
LEAK#show ip route
< Snip for resume >
172.16.0.0/32 is subnetted, 1 subnets
B 172.16.10.10 [20/11] via 10.0.0.1, 00:14:48, Ethernet0/0 >> Route from VRF B routing table at global routing table ( EIGRP ).
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.1.0/24 is directly connected, Ethernet0/1
L 192.168.1.1/32 is directly connected, Ethernet0/1
192.168.11.0/32 is subnetted, 1 subnets
D 192.168.11.11 [90/1024640] via 192.168.1.2, 02:16:51, Ethernet0/1
| Tabela de roteamento VRF B |
LEAK#show ip route vrf B
Routing Table: B
< Snip for resume >
10.0.0.0/8 is variably subnetted, 2 subnets, 2 masks
C 10.0.0.0/30 is directly connected, Ethernet0/0
L 10.0.0.2/32 is directly connected, Ethernet0/0
172.16.0.0/32 is subnetted, 1 subnets
O 172.16.10.10 [110/11] via 10.0.0.1, 00:34:25, Ethernet0/0
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
B 192.168.1.0/24 is directly connected, 00:08:51, Ethernet0/1
L 192.168.1.1/32 is directly connected, Ethernet0/1
192.168.11.0/32 is subnetted, 1 subnets
B 192.168.11.11 [20/1024640] via 192.168.1.2, 00:08:51, Ethernet0/1 >> Route from global routing table ( EIGRP ) at VRF B routing table.
Cenário 4 - Vazamento de rota padrão VRF de OSPF para BGP
O cenário 4 fornece um exemplo de vazamento de rota padrão VRF de OSPF para BGP.
Diagrama de Rede
O Diagrama de Rede, como visto na Imagem 4, mostra a topologia da camada 3, onde o vazamento de rota padrão é necessário.

Imagem 4. Topologia de Vazamento de Rota para o Cenário 4
O OSPF e o processo BGP estão sendo executados em VRF diferentes no VAZAMENTO do roteador. A rota padrão está presente no Roteador OSPF. O Router LEAK tem uma vizinhança BGP no VRF A com o Router BGP e uma vizinhança OSPF no VRF B com o Router OSPF.
O vazamento de rota padrão do OSPF para o BGP no VAZAMENTO do roteador é demonstrado abaixo.
Configurar
Step 1
Check if a static default route is present in Router OSPF.
OSPF#sh ip route
<output snipped>
Gateway of last resort is 192.168.10.2 to network 0.0.0.0
S* 0.0.0.0/0 [1/0] via 192.168.10.2 >>> default route is present in the routing table.
C 192.168.0.0/24 is directly connected, GigabitEthernet2
L 192.168.0.2/32 is directly connected, GigabitEthernet2
192.168.10.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.10.0/24 is directly connected, GigabitEthernet1
L 192.168.10.1/32 is directly connected, GigabitEthernet1
Step 2
From the OSPF router, the default route needs to be advertised in OSPF to Router LEAK.
Use the command "default-information originate" on Router OSPF under OSPF process:( if there is static route in the OSPF router, routing table as verified in Step 1)
OSPF(config)#router ospf 1
OSPF(config-router)#default-information originate
If there is no static route in the Router OSPF routing table then we can generate and advertise a default route to the OSPF neighbour.
OSPF(config)#router ospf 1
OSPF(config-router)#default-information originate always
This forces the router to advertise a default route even if it doesn't have one in its routing table.
Step 3.1
Verify on Router LEAK, if an external OE2 route is installed in the VRF B routing table:
LEAK#sh ip route VRF B
Routing Table: B
<output snipped>
Gateway of last resort is 192.168.0.2 to network 0.0.0.0
O*E2 0.0.0.0/0 [110/1] via 192.168.0.2, 00:05:51, GigabitEthernet2 >>> OE2 route is installed in the VRF B routing table (This needs to be leaked in BGP)
192.168.0.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.0.0/24 is directly connected, GigabitEthernet2
L 192.168.0.1/32 is directly connected, GigabitEthernet2
Step 3.2
Configure a prefix-list on Router LEAK
LEAK# conf t
LEAK(config)# ip prefix-list OSPF_TO_BGP seq 5 permit 0.0.0.0/0
Configure a route-map to match the prefix-list.
LEAK(config-route-map)#route-map OSPF_TO_BGP permit 10
LEAK(config-route-map)# match ip address prefix-list OSPF_TO_BGP
LEAK(config-route-map)#exit
Step 3.3
Verify on Router LEAK, that required VRFs , Route Distinguishers (RD) an Route Targets (RT) are configured.
LEAK(config)#vrf definition A
LEAK(config-vrf)#rd 1:1
LEAK(config-vrf)#address-family ipv4
LEAK(config-vrf-af)#route-target import 6500:1
LEAK(config-vrf-af)#exit-address-family
LEAK(config-vrf-af)#end
LEAK#
LEAK(config)#vrf definition B
LEAK(config-vrf)#rd 2:2
LEAK(config-vrf)#address-family ipv4
LEAK(config-vrf-af)#route-target export 6500:1
LEAK(config-vrf-af)#exit-address-family
LEAK(config-vrf-af)#end
LEAK#
Step 3.4
Configure import map in VRF A.
LEAK#conf t
LEAK(config)#vrf definition A
LEAK(config-vrf)#address-family ipv4
LEAK(config-vrf-af)#import map OSPF_TO_BGP
LEAK(config-vrf-af)#end
LEAK#
Step 3.5
Create an address family VRF B in the BGP configuration and advertise “0.0.0.0”
LEAK#sh run | sec bgp
redistribute bgp 6501
router bgp 6501
bgp router-id 10.0.0.1
bgp log-neighbor-changes
!
address-family ipv4 vrf A
neighbor 10.0.0.2 remote-as 6500
neighbor 10.0.0.2 activate
exit-address-family
!
address-family ipv4 vrf B
network 0.0.0.0
exit-address-family
Observação: criar uma família de endereços VRF com no BGP funciona mesmo sem ativar nenhum vizinho. É necessário apenas gerar o processo BGP para vazar as rotas entre o VRF.
Verificar
Verify the default route available in BGP.
LEAK#sh ip route vrf A
Routing Table: A
<output snipped>
Gateway of last resort is 192.168.0.2 to network 0.0.0.0
B* 0.0.0.0/0 [20/1] via 192.168.0.2 (B), 00:15:36, GigabitEthernet2 >>> Default route of VRF B routing table in VRF A routing table.
10.0.0.0/8 is variably subnetted, 2 subnets, 2 masks
C 10.0.0.0/24 is directly connected, GigabitEthernet1
L 10.0.0.1/32 is directly connected, GigabitEthernet1
Outros recursos
Histórico de revisões
| Revisão | Data de publicação | Comentários |
|---|---|---|
4.0 |
16-Oct-2024
|
Formatação atualizada. |
3.0 |
12-Jan-2023
|
Ajuste de título e corrigiu um nome de autor. Recertificado. |
2.0 |
26-Oct-2021
|
Ajuste de título e um nome de autor corrigido |
1.0 |
16-Dec-2020
|
Versão inicial |
Colaborado por engenheiros da Cisco
- Adriana PachecoEngenheiro de consultoria técnica
- José FonsecaEngenheiro de consultoria técnica
- Mohammed Shihan AEngenheiro de consultoria técnica
Contate a Cisco
- Abrir um caso de suporte

- (É necessário um Contrato de Serviço da Cisco)
 Feedback
Feedback