NAT configureren en verifiëren op FTD
Downloadopties
Inclusief taalgebruik
De documentatie van dit product is waar mogelijk geschreven met inclusief taalgebruik. Inclusief taalgebruik wordt in deze documentatie gedefinieerd als taal die geen discriminatie op basis van leeftijd, handicap, gender, etniciteit, seksuele oriëntatie, sociaaleconomische status of combinaties hiervan weerspiegelt. In deze documentatie kunnen uitzonderingen voorkomen vanwege bewoordingen die in de gebruikersinterfaces van de productsoftware zijn gecodeerd, die op het taalgebruik in de RFP-documentatie zijn gebaseerd of die worden gebruikt in een product van een externe partij waarnaar wordt verwezen. Lees meer over hoe Cisco gebruikmaakt van inclusief taalgebruik.
Over deze vertaling
Cisco heeft dit document vertaald via een combinatie van machine- en menselijke technologie om onze gebruikers wereldwijd ondersteuningscontent te bieden in hun eigen taal. Houd er rekening mee dat zelfs de beste machinevertaling niet net zo nauwkeurig is als die van een professionele vertaler. Cisco Systems, Inc. is niet aansprakelijk voor de nauwkeurigheid van deze vertalingen en raadt aan altijd het oorspronkelijke Engelstalige document (link) te raadplegen.
Inhoud
Inleiding
In dit document wordt beschreven hoe u de standaard Network Address Translation (NAT) op Firepower Threat Defense (FTD) configureert en verifieert.
Voorwaarden
Vereisten
Er zijn geen specifieke vereisten van toepassing op dit document.
Gebruikte componenten
De informatie in dit document is gebaseerd op de volgende software- en hardware-versies:
- Secure Firewall Threat Defense Virtual draait op versie 7.7.0 (Build 89)
- Secure Firewall Management Center Virtual (FMC) met versie 7.7.0 (build 91)
- Drie Windows 7-hosts
- Cisco IOS® 3925-router die LAN-naar-LAN (L2L) VPN uitvoert
De informatie in dit document is gebaseerd op de apparaten in een specifieke laboratoriumomgeving. Alle apparaten die in dit document worden beschreven, hadden een opgeschoonde (standaard)configuratie. Als uw netwerk live is, moet u zorgen dat u de potentiële impact van elke opdracht begrijpt.
Achtergrondinformatie
FTD ondersteunt dezelfde NAT-configuratieopties als het klassieke Adaptive Security Appliance (ASA):
- NAT Rules Before – Twice NAT (sectie 1).
- Auto-NAT-regels – Sectie 2
- NAT-regels na – tweemaal NAT (deel 3).
Aangezien FTD-configuratie wordt uitgevoerd vanuit de FMC als het gaat om NAT-configuratie, is het noodzakelijk om bekend te zijn met de FMC GUI en de verschillende configuratieopties.
Configureren
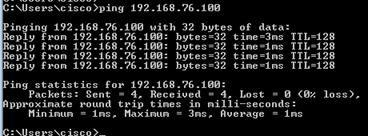
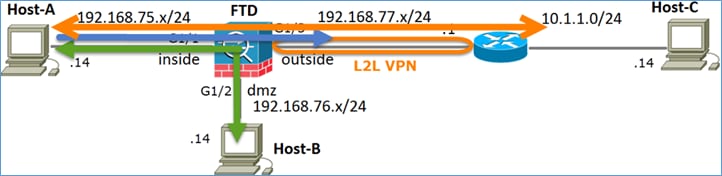
Netwerkdiagram
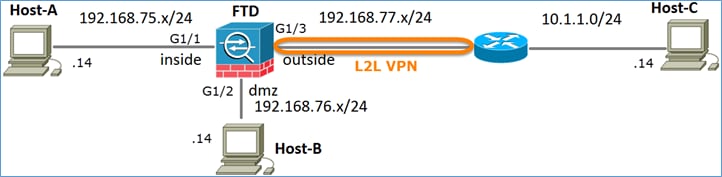
Taak 1. Statische NAT configureren op FTD
Configureer NAT volgens deze vereisten:
|
Naam NAT-beleid |
Naam van het FTD-apparaat |
|
NAT-regel |
Handmatige NAT-regel |
|
NAT-type |
statisch |
|
invoegen |
in afdeling 1 |
|
Broninterface |
Binnenzijde* |
|
Bestemmingsinterface |
DMZ* |
|
oorspronkelijke bron |
192.168.75.14 |
|
Vertaalde bron |
192.168.76.100 |
*Gebruik beveiligingszones voor de NAT-regel
Oplossing:
Terwijl op klassieke ASA, moet je naamgeving gebruiken in de NAT-regels. Op FTD moet u ofwel Beveiligingszones of Interfacegroepen gebruiken.
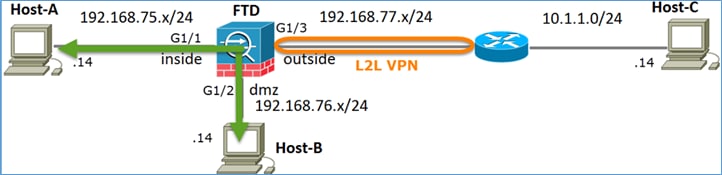
Stap 1. Wijs interfaces toe aan beveiligingszones/interfacegroepen.
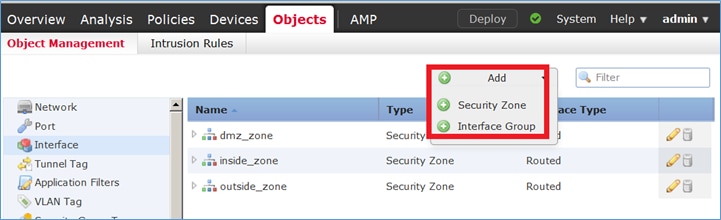
In deze taak wordt besloten om de FTD-interfaces die voor NAT worden gebruikt, toe te wijzen aan Security Zones. U kunt ze ook toewijzen aan interfacegroepen, zoals wordt weergegeven in de afbeelding.
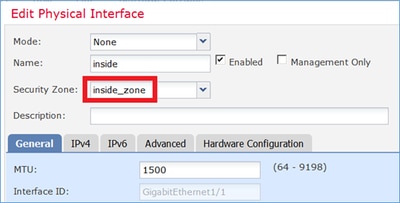
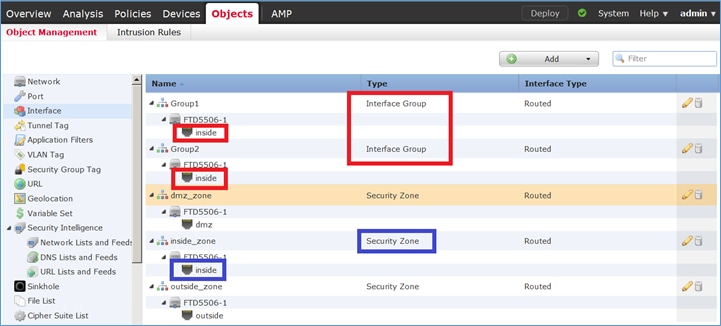
Stap 2. Het resultaat is zoals getoond in de afbeelding.
Stap 3. U kunt interfacegroepen en beveiligingszones maken/bewerken vanuit de pagina Objecten > Objectbeheer > Interface, zoals in de afbeelding wordt weergegeven.
Beveiligingszones versus interfacegroepen
Het belangrijkste verschil tussen beveiligingszones en interfacegroepen is dat een interface tot slechts één beveiligingszone kan behoren, maar tot meerdere interfacegroepen kan behoren. Praktisch gezien bieden de interfacegroepen dus meer flexibiliteit.
U kunt zien dat de interface binnen behoort tot twee verschillende interfacegroepen, maar slechts één beveiligingszone zoals weergegeven in de afbeelding.
Stap 4. Statische NAT configureren op FTD.
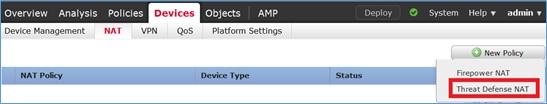
Navigeer naar Apparaten > NAT en maak een NAT-beleid. Selecteer Nieuw beleid > Dreigingsdefensie-NAT zoals in de afbeelding wordt weergegeven.
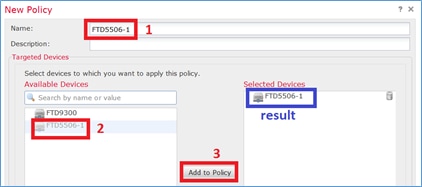
Stap 5. Geef de beleidsnaam op en wijs deze toe aan een doelapparaat zoals in de afbeelding wordt weergegeven.
Stap 6. Voeg een NAT-regel toe aan het beleid en klik op Regel toevoegen.
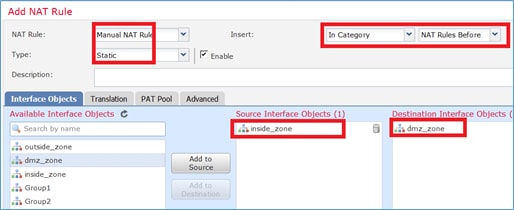
Geef deze op volgens de taakvereisten zoals weergegeven in de afbeeldingen.
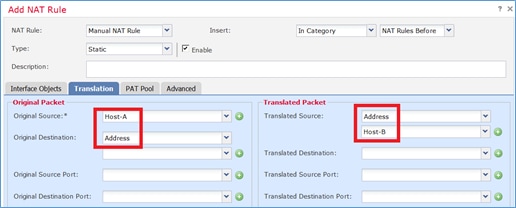
Host-A = 192 168 75 14
Host-B = 192 168 76 100
firepower# show run object object network Host-A host 192.168.75.14 object network Host-B host 192.168.76.100
Waarschuwing: Als u Statische NAT configureert en een interface opgeeft als Vertaalde bron, wordt al het verkeer dat bestemd is voor het IP-adres van de interface omgeleid. Gebruikers hebben geen toegang tot een service die is ingeschakeld op de toegewezen interface. Voorbeelden van dergelijke diensten zijn routeringsprotocollen zoals OSPF en EIGRP.
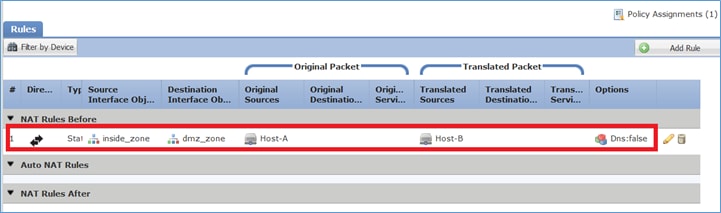
Stap 7. Het resultaat is zoals getoond in de afbeelding.
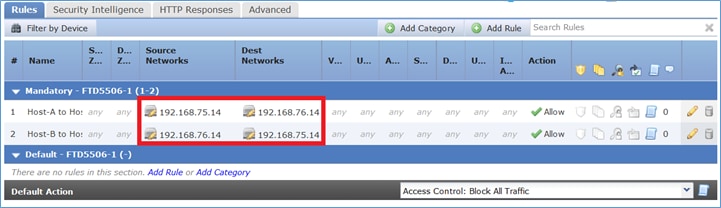
Stap 8. Zorg ervoor dat er een toegangscontrolebeleid is waarmee host-B toegang heeft tot host-A en vice versa. Statische NAT is standaard bidirectioneel. Vergelijkbaar met klassieke ASA, zie het gebruik van echte IP's.
Verificatie:
Van LINA CLI:
firepower# show run nat nat (inside,dmz) source static Host-A Host-B
De NAT-regel werd zoals verwacht in sectie 1 ingevoegd:
firepower# show nat
Manual NAT Policies (Section 1)
1 (inside) to (dmz) source static Host-A Host-B
translate_hits = 0, untranslate_hits = 0
Opmerking: De 2 platen die op de achtergrond worden gemaakt.
firepower# show xlate
2 in use, 4 most used
Flags: D - DNS, e - extended, I - identity, i - dynamic, r - portmap,
s - static, T - twice, N - net-to-net
NAT from inside:192.168.75.14 to dmz:192.168.76.100
flags sT idle 0:41:49 timeout 0:00:00
NAT from dmz:0.0.0.0/0 to inside:0.0.0.0/0
flags sIT idle 0:41:49 timeout 0:00:00
De ASP NAT-tabellen:
firepower# show asp table classify domain nat
Input Table
in id=0x7ff6036a9f50, priority=6, domain=nat, deny=false
hits=0, user_data=0x7ff60314dbf0, cs_id=0x0, flags=0x0, protocol=0
src ip/id=192.168.75.14, mask=255.255.255.255, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=inside, output_ifc=dmz
in id=0x7ff603696860, priority=6, domain=nat, deny=false
hits=0, user_data=0x7ff602be3f80, cs_id=0x0, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=192.168.76.100, mask=255.255.255.255, port=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=inside
Output Table:
L2 - Output Table:
L2 - Input Table:
Last clearing of hits counters: Never
firepower# show asp table classify domain nat-reverse
Input Table
Output Table:
out id=0x7ff603685350, priority=6, domain=nat-reverse, deny=false
hits=0, user_data=0x7ff60314dbf0, cs_id=0x0, use_real_addr, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=192.168.75.14, mask=255.255.255.255, port=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=inside
out id=0x7ff603638470, priority=6, domain=nat-reverse, deny=false
hits=0, user_data=0x7ff602be3f80, cs_id=0x0, use_real_addr, flags=0x0, protocol=0
src ip/id=192.168.75.14, mask=255.255.255.255, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=inside, output_ifc=dmz
L2 - Output Table:
L2 - Input Table:
Last clearing of hits counters: Never
Schakel vastleggen met traceringsdetails in op FTD en ping van host-B naar host-A en zoals weergegeven in de afbeelding.
firepower# capture DMZ interface dmz trace detail match ip host 192.168.76.14 host 192.168.76.100 firepower# capture INSIDE interface inside trace detail match ip host 192.168.76.14 host 192.168.75.14
Het aantal treffers staat in de ASP-tabellen:
firepower# show asp table classify domain nat
Input Table
in id=0x7ff6036a9f50, priority=6, domain=nat, deny=false
hits=0, user_data=0x7ff60314dbf0, cs_id=0x0, flags=0x0, protocol=0
src ip/id=192.168.75.14, mask=255.255.255.255, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=inside, output_ifc=dmz
in id=0x7ff603696860, priority=6, domain=nat, deny=false
hits=4, user_data=0x7ff602be3f80, cs_id=0x0, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=192.168.76.100, mask=255.255.255.255, port=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=inside
firepower# show asp table classify domain nat-reverse
Input Table
Output Table:
out id=0x7ff603685350, priority=6, domain=nat-reverse, deny=false
hits=4, user_data=0x7ff60314dbf0, cs_id=0x0, use_real_addr, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=192.168.75.14, mask=255.255.255.255, port=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=inside
out id=0x7ff603638470, priority=6, domain=nat-reverse, deny=false
hits=0, user_data=0x7ff602be3f80, cs_id=0x0, use_real_addr, flags=0x0, protocol=0
src ip/id=192.168.75.14, mask=255.255.255.255, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=inside, output_ifc=dmz
De pakketopname toont:
firepower# show capture DMZ 8 packets captured 1: 17:38:26.324812 192.168.76.14 > 192.168.76.100: icmp: echo request 2: 17:38:26.326505 192.168.76.100 > 192.168.76.14: icmp: echo reply 3: 17:38:27.317991 192.168.76.14 > 192.168.76.100: icmp: echo request 4: 17:38:27.319456 192.168.76.100 > 192.168.76.14: icmp: echo reply 5: 17:38:28.316344 192.168.76.14 > 192.168.76.100: icmp: echo request 6: 17:38:28.317824 192.168.76.100 > 192.168.76.14: icmp: echo reply 7: 17:38:29.330518 192.168.76.14 > 192.168.76.100: icmp: echo request 8: 17:38:29.331983 192.168.76.100 > 192.168.76.14: icmp: echo reply 8 packets shown
Sporen van een pakket (belangrijke punten worden gemarkeerd).
Opmerking: de ID van de NAT-regel en de correlatie met de ASP-tabel.
firepower# show capture DMZ packet-number 3 trace detail
8 packets captured
3: 17:38:27.317991 000c.2998.3fec d8b1.90b7.32e0 0x0800 Length: 74
192.168.76.14 > 192.168.76.100: icmp: echo request (ttl 128, id 9975)
Phase: 1
Type: CAPTURE
Subtype:
Result: ALLOW
Config:
Additional Information:
Forward Flow based lookup yields rule:
in id=0x7ff602c72be0, priority=13, domain=capture, deny=false
hits=55, user_data=0x7ff602b74a50, cs_id=0x0, l3_type=0x0
src mac=0000.0000.0000, mask=0000.0000.0000
dst mac=0000.0000.0000, mask=0000.0000.0000
input_ifc=dmz, output_ifc=any
Phase: 2
Type: ACCESS-LIST
Subtype:
Result: ALLOW
Config:
Implicit Rule
Additional Information:
Forward Flow based lookup yields rule:
in id=0x7ff603612200, priority=1, domain=permit, deny=false
hits=1, user_data=0x0, cs_id=0x0, l3_type=0x8
src mac=0000.0000.0000, mask=0000.0000.0000
dst mac=0000.0000.0000, mask=0100.0000.0000
input_ifc=dmz, output_ifc=any
Phase: 3
Type: UN-NAT
Subtype: static
Result: ALLOW
Config:
nat (inside,dmz) source static Host-A Host-B
Additional Information:
NAT divert to egress interface inside
Untranslate 192.168.76.100/0 to 192.168.75.14/0
Phase: 4
Type: ACCESS-LIST
Subtype: log
Result: ALLOW
Config:
access-group CSM_FW_ACL_ global
access-list CSM_FW_ACL_ advanced permit ip host 192.168.76.14 host 192.168.75.14 rule-id 268434440
access-list CSM_FW_ACL_ remark rule-id 268434440: ACCESS POLICY: FTD5506-1 - Mandatory/2
access-list CSM_FW_ACL_ remark rule-id 268434440: L4 RULE: Host-B to Host-A
Additional Information:
This packet will be sent to snort for additional processing where a verdict will be reached
Forward Flow based lookup yields rule:
in id=0x7ff602b72610, priority=12, domain=permit, deny=false
hits=1, user_data=0x7ff5fa9d0180, cs_id=0x0, use_real_addr, flags=0x0, protocol=0
src ip/id=192.168.76.14, mask=255.255.255.255, port=0, tag=any, ifc=any
dst ip/id=192.168.75.14, mask=255.255.255.255, port=0, tag=any, ifc=any, vlan=0, dscp=0x0
input_ifc=any, output_ifc=any
Phase: 5
Type: CONN-SETTINGS
Subtype:
Result: ALLOW
Config:
class-map class-default
match any
policy-map global_policy
class class-default
set connection advanced-options UM_STATIC_TCP_MAP
service-policy global_policy global
Additional Information:
Forward Flow based lookup yields rule:
in id=0x7ff60367cf80, priority=7, domain=conn-set, deny=false
hits=1, user_data=0x7ff603677080, cs_id=0x0, use_real_addr, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=any
Phase: 6
Type: NAT
Subtype:
Result: ALLOW
Config:
nat (inside,dmz) source static Host-A Host-B
Additional Information:
Static translate 192.168.76.14/1 to 192.168.76.14/1
Forward Flow based lookup yields rule:
in id=0x7ff603696860, priority=6, domain=nat, deny=false
hits=1, user_data=0x7ff602be3f80, cs_id=0x0, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=192.168.76.100, mask=255.255.255.255, port=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=inside
Phase: 7
Type: NAT
Subtype: per-session
Result: ALLOW
Config:
Additional Information:
Forward Flow based lookup yields rule:
in id=0x7ff602220020, priority=0, domain=nat-per-session, deny=true
hits=2, user_data=0x0, cs_id=0x0, reverse, use_real_addr, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=any, output_ifc=any
Phase: 8
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Forward Flow based lookup yields rule:
in id=0x7ff6035c0af0, priority=0, domain=inspect-ip-options, deny=true
hits=1, user_data=0x0, cs_id=0x0, reverse, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=any
Phase: 9
Type: INSPECT
Subtype: np-inspect
Result: ALLOW
Config:
class-map inspection_default
match default-inspection-traffic
policy-map global_policy
class inspection_default
inspect icmp
service-policy global_policy global
Additional Information:
Forward Flow based lookup yields rule:
in id=0x7ff602b5f020, priority=70, domain=inspect-icmp, deny=false
hits=2, user_data=0x7ff602be7460, cs_id=0x0, use_real_addr, flags=0x0, protocol=1
src ip/id=0.0.0.0, mask=0.0.0.0, icmp-type=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, icmp-code=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=any
Phase: 10
Type: INSPECT
Subtype: np-inspect
Result: ALLOW
Config:
Additional Information:
Forward Flow based lookup yields rule:
in id=0x7ff602b3a6d0, priority=70, domain=inspect-icmp-error, deny=false
hits=2, user_data=0x7ff603672ec0, cs_id=0x0, use_real_addr, flags=0x0, protocol=1
src ip/id=0.0.0.0, mask=0.0.0.0, icmp-type=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, icmp-code=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=any
Phase: 11
Type: NAT
Subtype: rpf-check
Result: ALLOW
Config:
nat (inside,dmz) source static Host-A Host-B
Additional Information:
Forward Flow based lookup yields rule:
out id=0x7ff603685350, priority=6, domain=nat-reverse, deny=false
hits=2, user_data=0x7ff60314dbf0, cs_id=0x0, use_real_addr, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=192.168.75.14, mask=255.255.255.255, port=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=inside
Phase: 12
Type: NAT
Subtype: per-session
Result: ALLOW
Config:
Additional Information:
Reverse Flow based lookup yields rule:
in id=0x7ff602220020, priority=0, domain=nat-per-session, deny=true
hits=4, user_data=0x0, cs_id=0x0, reverse, use_real_addr, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=any, output_ifc=any
Phase: 13
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Reverse Flow based lookup yields rule:
in id=0x7ff602c56d10, priority=0, domain=inspect-ip-options, deny=true
hits=2, user_data=0x0, cs_id=0x0, reverse, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=inside, output_ifc=any
Phase: 14
Type: FLOW-CREATION
Subtype:
Result: ALLOW
Config:
Additional Information:
New flow created with id 5084, packet dispatched to next module
Module information for forward flow ...
snp_fp_inspect_ip_options
snp_fp_snort
snp_fp_inspect_icmp
snp_fp_translate
snp_fp_adjacency
snp_fp_fragment
snp_ifc_stat
Module information for reverse flow ...
snp_fp_inspect_ip_options
snp_fp_translate
snp_fp_inspect_icmp
snp_fp_snort
snp_fp_adjacency
snp_fp_fragment
snp_ifc_stat
Phase: 15
Type: EXTERNAL-INSPECT
Subtype:
Result: ALLOW
Config:
Additional Information:
Application: 'SNORT Inspect'
Phase: 16
Type: SNORT
Subtype:
Result: ALLOW
Config:
Additional Information:
Snort Verdict: (pass-packet) allow this packet
Phase: 17
Type: ROUTE-LOOKUP
Subtype: Resolve Egress Interface
Result: ALLOW
Config:
Additional Information:
found next-hop 192.168.75.14 using egress ifc inside
Phase: 18
Type: ADJACENCY-LOOKUP
Subtype: next-hop and adjacency
Result: ALLOW
Config:
Additional Information:
adjacency Active
next-hop mac address 000c.2930.2b78 hits 140694538708414
Phase: 19
Type: CAPTURE
Subtype:
Result: ALLOW
Config:
Additional Information:
Forward Flow based lookup yields rule:
out id=0x7ff6036a94e0, priority=13, domain=capture, deny=false
hits=14, user_data=0x7ff6024aff90, cs_id=0x0, l3_type=0x0
src mac=0000.0000.0000, mask=0000.0000.0000
dst mac=0000.0000.0000, mask=0000.0000.0000
input_ifc=inside, output_ifc=any
Result:
input-interface: inside
input-status: up
input-line-status: up
output-interface: inside
output-status: up
output-line-status: up
Action: allow
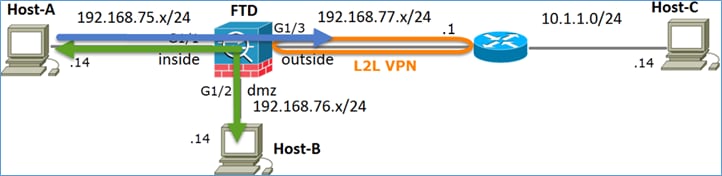
1 packet shownTaak 2. Port Address Translation (PAT) configureren op FTD
Configureer NAT volgens deze vereisten:
|
NAT-regel |
Handmatige NAT-regel |
|
NAT-type |
dynamisch |
|
invoegen |
in afdeling 1 |
|
Broninterface |
Binnenzijde* |
|
Bestemmingsinterface |
Buiten* |
|
oorspronkelijke bron |
192.168.75.0/24 |
|
Vertaalde bron |
Externe interface (PAT) |
*Gebruik beveiligingszones voor de NAT-regel
Oplossing:
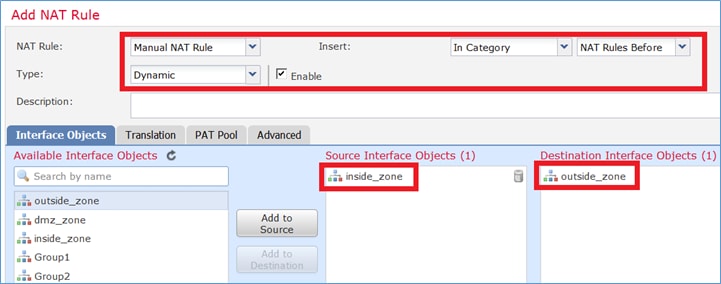
Stap 1. Voeg een tweede NAT-regel toe en configureer volgens de taakvereisten zoals weergegeven in de afbeelding.
Stap 2. Hier is hoe PAT is geconfigureerd zoals weergegeven in de afbeelding.
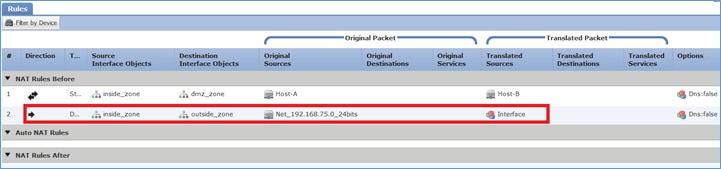
Stap 3. Het resultaat is zoals in de afbeelding.
Stap 4. Voor de rest van dit lab configureert u het toegangscontrolebeleid zodat al het verkeer kan worden doorgestuurd.
Verificatie:
NAT-configuratie:
firepower# show nat
Manual NAT Policies (Section 1)
1 (inside) to (dmz) source static Host-A Host-B
translate_hits = 26, untranslate_hits = 26
2 (inside) to (outside) source dynamic Net_192.168.75.0_24 interface
translate_hits = 0, untranslate_hits = 0
Van LINA CLI, let op de nieuwe vermelding:
firepower# show xlate
3 in use, 19 most used
Flags: D - DNS, e - extended, I - identity, i - dynamic, r - portmap,
s - static, T - twice, N - net-to-net
NAT from inside:192.168.75.14 to dmz:192.168.76.100
flags sT idle 1:15:14 timeout 0:00:00
NAT from dmz:0.0.0.0/0 to inside:0.0.0.0/0
flags sIT idle 1:15:14 timeout 0:00:00
NAT from outside:0.0.0.0/0 to inside:0.0.0.0/0
flags sIT idle 0:04:02 timeout 0:00:00
Opname inschakelen op de binnen- en buiteninterface. Op inside capture trace inschakelen:
firepower# capture CAPI trace interface inside match ip host 192.168.75.14 host 192.168.77.1 firepower# capture CAPO interface outside match ip any host 192.168.77.1
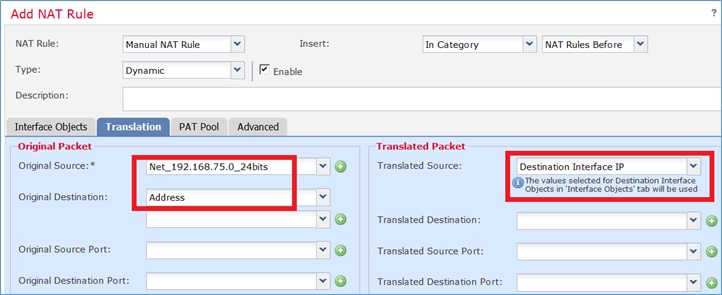
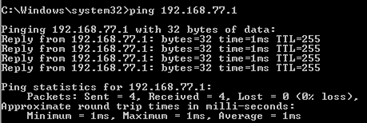
Ping van host-A (192.168.75.14) naar IP 192.168.77.1 zoals weergegeven in de afbeelding.
In LINA captures ziet u de PAT-vertaling:
firepower# show cap CAPI 8 packets captured 1: 18:54:43.658001 192.168.75.14 > 192.168.77.1: icmp: echo request 2: 18:54:43.659099 192.168.77.1 > 192.168.75.14: icmp: echo reply 3: 18:54:44.668544 192.168.75.14 > 192.168.77.1: icmp: echo request 4: 18:54:44.669505 192.168.77.1 > 192.168.75.14: icmp: echo reply 5: 18:54:45.682368 192.168.75.14 > 192.168.77.1: icmp: echo request 6: 18:54:45.683421 192.168.77.1 > 192.168.75.14: icmp: echo reply 7: 18:54:46.696436 192.168.75.14 > 192.168.77.1: icmp: echo request 8: 18:54:46.697412 192.168.77.1 > 192.168.75.14: icmp: echo reply
firepower# show cap CAPO 8 packets captured 1: 18:54:43.658672 192.168.77.6 > 192.168.77.1: icmp: echo request 2: 18:54:43.658962 192.168.77.1 > 192.168.77.6: icmp: echo reply 3: 18:54:44.669109 192.168.77.6 > 192.168.77.1: icmp: echo request 4: 18:54:44.669337 192.168.77.1 > 192.168.77.6: icmp: echo reply 5: 18:54:45.682932 192.168.77.6 > 192.168.77.1: icmp: echo request 6: 18:54:45.683207 192.168.77.1 > 192.168.77.6: icmp: echo reply 7: 18:54:46.697031 192.168.77.6 > 192.168.77.1: icmp: echo request 8: 18:54:46.697275 192.168.77.1 > 192.168.77.6: icmp: echo reply
Sporen van een pakket met belangrijke secties gemarkeerd:
firepower# show cap CAPI packet-number 1 trace 8 packets captured 1: 18:54:43.658001 192.168.75.14 > 192.168.77.1: icmp: echo request Phase: 1 Type: CAPTURE Subtype: Result: ALLOW Config: Additional Information: MAC Access list Phase: 2 Type: ACCESS-LIST Subtype: Result: ALLOW Config: Implicit Rule Additional Information: MAC Access list Phase: 3 Type: ROUTE-LOOKUP Subtype: Resolve Egress Interface Result: ALLOW Config: Additional Information: found next-hop 192.168.77.1 using egress ifc outside Phase: 4 Type: ACCESS-LIST Subtype: log Result: ALLOW Config: access-group CSM_FW_ACL_ global access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268434434 access-list CSM_FW_ACL_ remark rule-id 268434434: ACCESS POLICY: ACP - Mandatory access-list CSM_FW_ACL_ remark rule-id 268434434: L4 RULE: DEFAULT ACTION RULE Additional Information: This packet will be sent to snort for additional processing where a verdict will be reached Phase: 5 Type: CONN-SETTINGS Subtype: Result: ALLOW Config: class-map class-default match any policy-map global_policy class class-default set connection advanced-options UM_STATIC_TCP_MAP service-policy global_policy global Additional Information: Phase: 6 Type: NAT Subtype: Result: ALLOW Config: nat (inside,outside) source dynamic Net_192.168.75.0_24 interface Additional Information: Dynamic translate 192.168.75.14/1 to 192.168.77.6/1 Phase: 7 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Phase: 8 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Phase: 9 Type: INSPECT Subtype: np-inspect Result: ALLOW Config: class-map inspection_default match default-inspection-traffic policy-map global_policy class inspection_default inspect icmp service-policy global_policy global Additional Information: Phase: 10 Type: INSPECT Subtype: np-inspect Result: ALLOW Config: Additional Information: Phase: 11 Type: NAT Subtype: rpf-check Result: ALLOW Config: nat (inside,outside) source dynamic Net_192.168.75.0_24 interface Additional Information: Phase: 12 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Phase: 13 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Phase: 14 Type: FLOW-CREATION Subtype: Result: ALLOW Config: Additional Information: New flow created with id 6981, packet dispatched to next module Phase: 15 Type: EXTERNAL-INSPECT Subtype: Result: ALLOW Config: Additional Information: Application: 'SNORT Inspect' Phase: 16 Type: SNORT Subtype: Result: ALLOW Config: Additional Information: Snort Verdict: (pass-packet) allow this packet Phase: 17 Type: ROUTE-LOOKUP Subtype: Resolve Egress Interface Result: ALLOW Config: Additional Information: found next-hop 192.168.77.1 using egress ifc outside Phase: 18 Type: ADJACENCY-LOOKUP Subtype: next-hop and adjacency Result: ALLOW Config: Additional Information: adjacency Active next-hop mac address c84c.758d.4980 hits 140694538709114 Phase: 19 Type: CAPTURE Subtype: Result: ALLOW Config: Additional Information: MAC Access list Result: input-interface: outside input-status: up input-line-status: up output-interface: outside output-status: up output-line-status: up Action: allow 1 packet shown
De dynamische leisteen is gemaakt (let op de ri vlaggen):
firepower# show xlate
4 in use, 19 most used
Flags: D - DNS, e - extended, I - identity, i - dynamic, r - portmap,
s - static, T - twice, N - net-to-net
NAT from inside:192.168.75.14 to dmz:192.168.76.100
flags sT idle 1:16:47 timeout 0:00:00
NAT from dmz:0.0.0.0/0 to inside:0.0.0.0/0
flags sIT idle 1:16:47 timeout 0:00:00
NAT from outside:0.0.0.0/0 to inside:0.0.0.0/0
flags sIT idle 0:05:35 timeout 0:00:00
ICMP PAT from inside:192.168.75.14/1 to outside:192.168.77.6/1 flags ri idle 0:00:30 timeout 0:00:30
In de LINA-logs ziet u:
firepower# show log Aug 1 2025 18:54:43: %FTD-7-609001: Built local-host inside:192.168.75.14 Aug 1 2025 18:54:43: %FTD-6-305011: Built dynamic ICMP translation from inside:192.168.75.14/1 to outside:192.168.77.6/1 Aug 1 2025 18:54:43: %FTD-7-609001: Built local-host outside:192.168.77.1 Aug 1 2025 18:54:43: %FTD-6-302020: Built inbound ICMP connection for faddr 192.168.75.14/1 gaddr 192.168.77.1/0 laddr 192.168.77.1/0 Aug 1 2025 18:54:43: %FTD-6-302021: Teardown ICMP connection for faddr 192.168.75.14/1 gaddr 192.168.77.1/0 laddr 192.168.77.1/0 Aug 1 2025 18:54:43: %FTD-7-609002: Teardown local-host outside:192.168.77.1 duration 0:00:00 Aug 1 2025 18:55:17: %FTD-6-305012: Teardown dynamic ICMP translation from inside:192.168.75.14/1 to outside:192.168.77.6/1 duration 0:00:34
NAT-secties:
firepower# show nat
Manual NAT Policies (Section 1)
1 (inside) to (dmz) source static Host-A Host-B
translate_hits = 26, untranslate_hits = 26
2 (inside) to (outside) source dynamic Net_192.168.75.0_24 interface
translate_hits = 94, untranslate_hits = 138
ASP-tabellen tonen:
firepower# show asp table classify domain nat
Input Table
in id=0x7ff6036a9f50, priority=6, domain=nat, deny=false
hits=0, user_data=0x7ff60314dbf0, cs_id=0x0, flags=0x0, protocol=0
src ip/id=192.168.75.14, mask=255.255.255.255, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=inside, output_ifc=dmz
in id=0x7ff603696860, priority=6, domain=nat, deny=false
hits=4, user_data=0x7ff602be3f80, cs_id=0x0, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=192.168.76.100, mask=255.255.255.255, port=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=inside
in id=0x7ff602c75f00, priority=6, domain=nat, deny=false
hits=94, user_data=0x7ff6036609a0, cs_id=0x0, flags=0x0, protocol=0
src ip/id=192.168.75.0, mask=255.255.255.0, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=inside, output_ifc=outside
in id=0x7ff603681fb0, priority=6, domain=nat, deny=false
hits=276, user_data=0x7ff60249f370, cs_id=0x0, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=192.168.77.6, mask=255.255.255.255, port=0, tag=any, dscp=0x0
input_ifc=outside, output_ifc=inside
firepower# show asp table classify domain nat-reverse
Input Table
Output Table:
out id=0x7ff603685350, priority=6, domain=nat-reverse, deny=false
hits=4, user_data=0x7ff60314dbf0, cs_id=0x0, use_real_addr, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=192.168.75.14, mask=255.255.255.255, port=0, tag=any, dscp=0x0
input_ifc=dmz, output_ifc=inside
out id=0x7ff603638470, priority=6, domain=nat-reverse, deny=false
hits=0, user_data=0x7ff602be3f80, cs_id=0x0, use_real_addr, flags=0x0, protocol=0
src ip/id=192.168.75.14, mask=255.255.255.255, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=inside, output_ifc=dmz
out id=0x7ff60361bda0, priority=6, domain=nat-reverse, deny=false
hits=138, user_data=0x7ff6036609a0, cs_id=0x0, use_real_addr, flags=0x0, protocol=0
src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any
dst ip/id=192.168.75.0, mask=255.255.255.0, port=0, tag=any, dscp=0x0
input_ifc=outside, output_ifc=inside
out id=0x7ff60361c180, priority=6, domain=nat-reverse, deny=false
hits=94, user_data=0x7ff60249f370, cs_id=0x0, use_real_addr, flags=0x0, protocol=0
src ip/id=192.168.75.0, mask=255.255.255.0, port=0, tag=any
dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0
input_ifc=inside, output_ifc=outside
Taak 3. NAT-vrijstelling configureren voor FTD
Configureer NAT volgens deze vereisten:
|
NAT-regel |
Handmatige NAT-regel |
|
NAT-type |
statisch |
|
invoegen |
In deel 1 zijn alle bestaande regels |
|
Broninterface |
Binnenzijde* |
|
Bestemmingsinterface |
Buiten* |
|
oorspronkelijke bron |
192.168.75.0/24 |
|
Vertaalde bron |
192.168.75.0/24 |
|
oorspronkelijke bestemming |
10.1.1.0/24 |
|
Vertaalde bestemming |
10.1.1.0/24 |
*Gebruik beveiligingszones voor de NAT-regel
Oplossing:
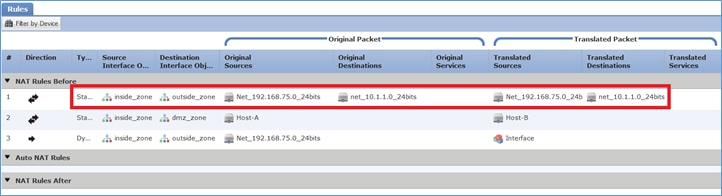
Stap 1. Voeg een derde NAT-regel toe en configureer per taak de vereisten zoals weergegeven in de afbeelding.
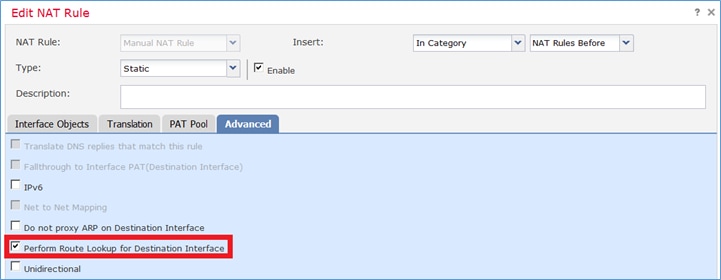
Stap 2. Route opzoeken uitvoeren voor het bepalen van de uitgang-interface.
Opmerking: voor NAT-identiteitsregels kunt u, net als bij de regels die u hebt toegevoegd, de manier wijzigen waarop de uitgang wordt bepaald en de normale routeweergave gebruiken zoals in de afbeelding wordt weergegeven.
Verificatie:
firepower# show run nat nat (inside,outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24 nat (inside,dmz) source static Host-A Host-B nat (inside,outside) source dynamic Net_192.168.75.0_24 interface
firepower# show nat
Manual NAT Policies (Section 1)
1 (inside) to (outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24
translate_hits = 0, untranslate_hits = 0
2 (inside) to (dmz) source static Host-A Host-B
translate_hits = 26, untranslate_hits = 26
3 (inside) to (outside) source dynamic Net_192.168.75.0_24 interface
translate_hits = 96, untranslate_hits = 138
Voer packet-tracer uit voor niet-VPN-verkeer afkomstig van binnen het netwerk. De PAT-regel wordt gebruikt zoals verwacht:
firepower# packet-tracer input inside tcp 192.168.75.14 1111 192.168.77.1 80 Phase: 1 Type: CAPTURE Subtype: Result: ALLOW Config: Additional Information: MAC Access list Phase: 2 Type: ACCESS-LIST Subtype: Result: ALLOW Config: Implicit Rule Additional Information: MAC Access list Phase: 3 Type: ROUTE-LOOKUP Subtype: Resolve Egress Interface Result: ALLOW Config: Additional Information: found next-hop 192.168.77.1 using egress ifc outside Phase: 4 Type: ACCESS-LIST Subtype: log Result: ALLOW Config: access-group CSM_FW_ACL_ global access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268434434 access-list CSM_FW_ACL_ remark rule-id 268434434: ACCESS POLICY: ACP - Mandatory access-list CSM_FW_ACL_ remark rule-id 268434434: L4 RULE: DEFAULT ACTION RULE Additional Information: This packet will be sent to snort for additional processing where a verdict will be reached Phase: 5 Type: CONN-SETTINGS Subtype: Result: ALLOW Config: class-map class-default match any policy-map global_policy class class-default set connection advanced-options UM_STATIC_TCP_MAP service-policy global_policy global Additional Information: Phase: 6 Type: NAT Subtype: Result: ALLOW Config: nat (inside,outside) source dynamic Net_192.168.75.0_24 interface Additional Information: Dynamic translate 192.168.75.14/1111 to 192.168.77.6/1111 Phase: 7 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Phase: 8 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Phase: 9 Type: NAT Subtype: rpf-check Result: ALLOW Config: nat (inside,outside) source dynamic Net_192.168.75.0_24 interface Additional Information: Phase: 10 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Phase: 11 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Phase: 12 Type: FLOW-CREATION Subtype: Result: ALLOW Config: Additional Information: New flow created with id 7227, packet dispatched to next module Result: input-interface: inside input-status: up input-line-status: up output-interface: outside output-status: up output-line-status: up Action: allow
Voer packet-tracer uit voor verkeer dat door de VPN-tunnel moet gaan (voer het twee keer uit sinds de eerste poging de VPN-tunnel omhoog brengt).
Opmerking: u moet de NAT-vrijstellingsregel kiezen.
Eerste poging tot packet-tracer:
firepower# packet-tracer input inside tcp 192.168.75.14 1111 10.1.1.1 80 Phase: 1 Type: CAPTURE Subtype: Result: ALLOW Config: Additional Information: MAC Access list Phase: 2 Type: ACCESS-LIST Subtype: Result: ALLOW Config: Implicit Rule Additional Information: MAC Access list Phase: 3 Type: UN-NAT Subtype: static Result: ALLOW Config: nat (inside,outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24 Additional Information: NAT divert to egress interface outside Untranslate 10.1.1.1/80 to 10.1.1.1/80 Phase: 4 Type: ACCESS-LIST Subtype: log Result: ALLOW Config: access-group CSM_FW_ACL_ global access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268434434 access-list CSM_FW_ACL_ remark rule-id 268434434: ACCESS POLICY: ACP - Mandatory access-list CSM_FW_ACL_ remark rule-id 268434434: L4 RULE: DEFAULT ACTION RULE Additional Information: This packet will be sent to snort for additional processing where a verdict will be reached Phase: 5 Type: CONN-SETTINGS Subtype: Result: ALLOW Config: class-map class-default match any policy-map global_policy class class-default set connection advanced-options UM_STATIC_TCP_MAP service-policy global_policy global Additional Information: Phase: 6 Type: NAT Subtype: Result: ALLOW Config: nat (inside,outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24 Additional Information: Static translate 192.168.75.14/1111 to 192.168.75.14/1111 Phase: 7 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Phase: 8 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Phase: 9 Type: VPN Subtype: encrypt Result: DROP Config: Additional Information: Result: input-interface: inside input-status: up input-line-status: up output-interface: outside output-status: up output-line-status: up Action: drop Drop-reason: (acl-drop) Flow is denied by configured rule
Tweede poging tot packet-tracer:
firepower# packet-tracer input inside tcp 192.168.75.14 1111 10.1.1.1 80 Phase: 1 Type: CAPTURE Subtype: Result: ALLOW Config: Additional Information: MAC Access list Phase: 2 Type: ACCESS-LIST Subtype: Result: ALLOW Config: Implicit Rule Additional Information: MAC Access list Phase: 3 Type: UN-NAT Subtype: static Result: ALLOW Config: nat (inside,outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24 Additional Information: NAT divert to egress interface outside Untranslate 10.1.1.1/80 to 10.1.1.1/80 Phase: 4 Type: ACCESS-LIST Subtype: log Result: ALLOW Config: access-group CSM_FW_ACL_ global access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268434434 access-list CSM_FW_ACL_ remark rule-id 268434434: ACCESS POLICY: ACP - Mandatory access-list CSM_FW_ACL_ remark rule-id 268434434: L4 RULE: DEFAULT ACTION RULE Additional Information: This packet will be sent to snort for additional processing where a verdict will be reached Phase: 5 Type: CONN-SETTINGS Subtype: Result: ALLOW Config: class-map class-default match any policy-map global_policy class class-default set connection advanced-options UM_STATIC_TCP_MAP service-policy global_policy global Additional Information: Phase: 6 Type: NAT Subtype: Result: ALLOW Config: nat (inside,outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24 Additional Information: Static translate 192.168.75.14/1111 to 192.168.75.14/1111 Phase: 7 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Phase: 8 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Phase: 9 Type: VPN Subtype: encrypt Result: ALLOW Config: Additional Information: Phase: 10 Type: NAT Subtype: rpf-check Result: ALLOW Config: nat (inside,outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24 Additional Information: Phase: 11 Type: VPN Subtype: ipsec-tunnel-flow Result: ALLOW Config: Additional Information: Phase: 12 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Phase: 13 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Phase: 14 Type: FLOW-CREATION Subtype: Result: ALLOW Config: Additional Information: New flow created with id 7226, packet dispatched to next module Result: input-interface: inside input-status: up input-line-status: up output-interface: outside output-status: up output-line-status: up Action: allow
Verificatie van aantal NAT-treffers:
firepower# show nat
Manual NAT Policies (Section 1)
1 (inside) to (outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24
translate_hits = 9, untranslate_hits = 9
2 (inside) to (dmz) source static Host-A Host-B
translate_hits = 26, untranslate_hits = 26
3 (inside) to (outside) source dynamic Net_192.168.75.0_24 interface
translate_hits = 98, untranslate_hits = 138
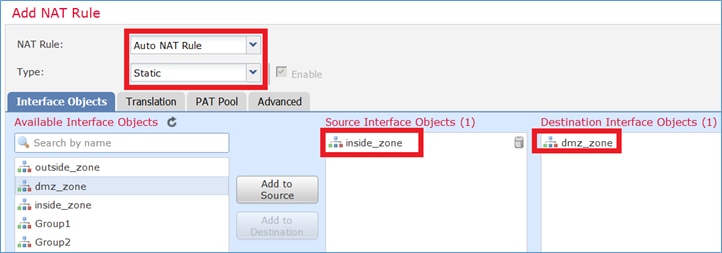
Taak 4. Object NAT configureren op FTD
Configureer NAT volgens deze vereisten:
|
NAT-regel |
Automatische NAT-regel |
|
NAT-type |
statisch |
|
invoegen |
in afdeling 2 |
|
Broninterface |
Binnenzijde* |
|
Bestemmingsinterface |
DMZ* |
|
oorspronkelijke bron |
192.168.75.99 |
|
Vertaalde bron |
192.168.76.99 |
|
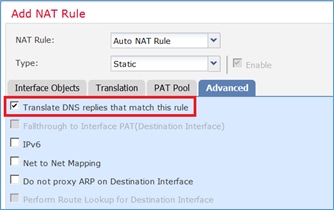
Antwoorden van DNS vertalen die overeenkomen met deze regel |
Ingeschakeld |
*Gebruik beveiligingszones voor de NAT-regel
Oplossing:
Stap 1. Configureer de regel volgens de taakvereisten zoals weergegeven in de afbeeldingen.
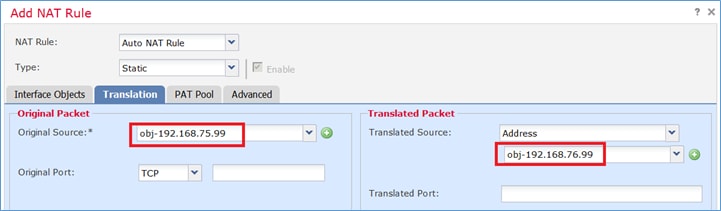
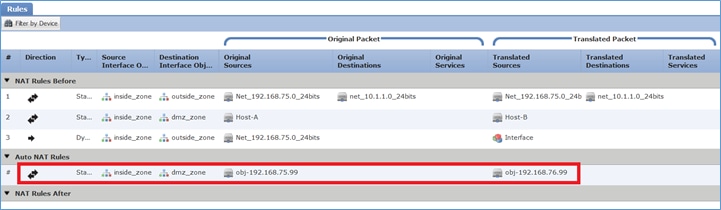
Stap 2. Het resultaat is zoals te zien in de afbeelding:
Verificatie:
firepower# show run nat nat (inside,outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24 nat (inside,dmz) source static Host-A Host-B nat (inside,outside) source dynamic Net_192.168.75.0_24 interface ! object network obj-192.168.75.99 nat (inside,dmz) static obj-192.168.76.99 dns
firepower# show nat
Manual NAT Policies (Section 1)
1 (inside) to (outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24
translate_hits = 9, untranslate_hits = 9
2 (inside) to (dmz) source static Host-A Host-B
translate_hits = 26, untranslate_hits = 26
3 (inside) to (outside) source dynamic Net_192.168.75.0_24 interface
translate_hits = 98, untranslate_hits = 138
Auto NAT Policies (Section 2)
1 (inside) to (dmz) source static obj-192.168.75.99 obj-192.168.76.99 dns
translate_hits = 0, untranslate_hits = 0
Verificatie met packet-tracer:
firepower# packet-tracer input inside tcp 192.168.75.99 1111 192.168.76.100 80 Phase: 1 Type: CAPTURE Subtype: Result: ALLOW Config: Additional Information: MAC Access list Phase: 2 Type: ACCESS-LIST Subtype: Result: ALLOW Config: Implicit Rule Additional Information: MAC Access list Phase: 3 Type: ROUTE-LOOKUP Subtype: Resolve Egress Interface Result: ALLOW Config: Additional Information: found next-hop 192.168.76.100 using egress ifc dmz Phase: 4 Type: ACCESS-LIST Subtype: log Result: ALLOW Config: access-group CSM_FW_ACL_ global access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268434434 access-list CSM_FW_ACL_ remark rule-id 268434434: ACCESS POLICY: ACP - Mandatory access-list CSM_FW_ACL_ remark rule-id 268434434: L4 RULE: DEFAULT ACTION RULE Additional Information: This packet will be sent to snort for additional processing where a verdict will be reached Phase: 5 Type: CONN-SETTINGS Subtype: Result: ALLOW Config: class-map class-default match any policy-map global_policy class class-default set connection advanced-options UM_STATIC_TCP_MAP service-policy global_policy global Additional Information: Phase: 6 Type: NAT Subtype: Result: ALLOW Config: object network obj-192.168.75.99 nat (inside,dmz) static obj-192.168.76.99 dns Additional Information: Static translate 192.168.75.99/1111 to 192.168.76.99/1111 Phase: 7 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Phase: 8 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Phase: 9 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Phase: 10 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Phase: 11 Type: FLOW-CREATION Subtype: Result: ALLOW Config: Additional Information: New flow created with id 7245, packet dispatched to next module Result: input-interface: inside input-status: up input-line-status: up output-interface: dmz output-status: up output-line-status: up Action: allow
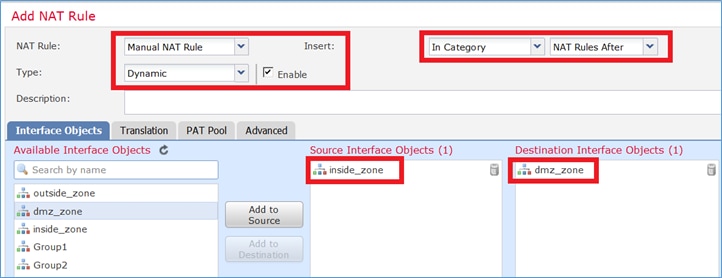
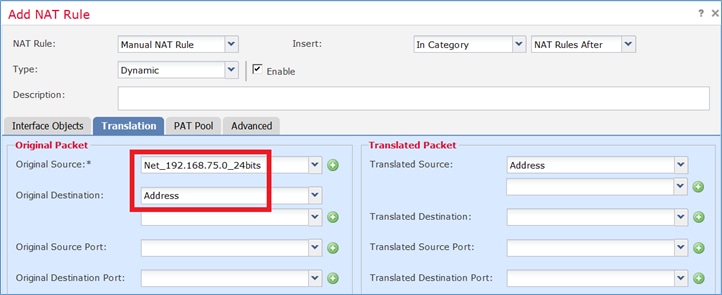
Taak 5. PAT-pool configureren voor FTD
Configureer NAT volgens deze vereisten:
|
NAT-regel |
Handmatige NAT-regel |
|
NAT-type |
dynamisch |
|
invoegen |
in afdeling 3 |
|
Broninterface |
Binnenzijde* |
|
Bestemmingsinterface |
DMZ* |
|
oorspronkelijke bron |
192.168.75.0/24 |
|
Vertaalde bron |
192.168.76.20-22 |
|
Gebruik het volledige bereik (1-65535) |
Ingeschakeld |
*Gebruik beveiligingszones voor de NAT-regel
Oplossing:
Stap 1. Configureer de regel per taak zoals weergegeven in de afbeeldingen.
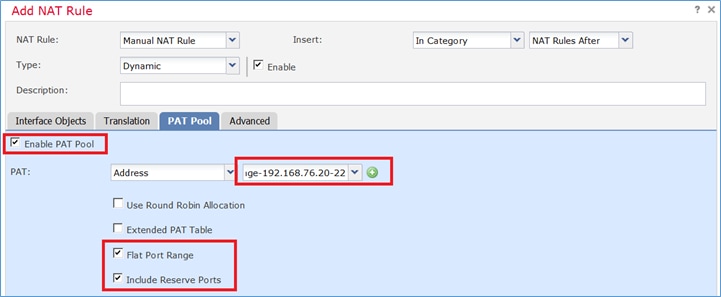
Stap 2. Schakel Flat Port Range in met Include Reserver Ports waarmee het volledige bereik (1-65535) zoals weergegeven in de afbeelding kan worden gebruikt.
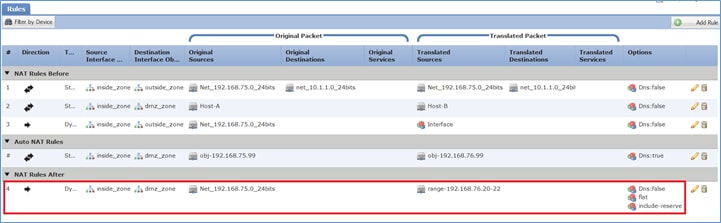
Stap 3. Het resultaat is zoals in de afbeelding.
Verificatie:
firepower# show run nat nat (inside,outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24 nat (inside,dmz) source static Host-A Host-B nat (inside,outside) source dynamic Net_192.168.75.0_24 interface ! object network obj-192.168.75.99 nat (inside,dmz) static obj-192.168.76.99 dns ! nat (inside,dmz) after-auto source dynamic Net_192.168.75.0_24 pat-pool range-192.168.76.20-22 flat include-reserve
De regel staat in paragraaf 3:
firepower# show nat
Manual NAT Policies (Section 1)
1 (inside) to (outside) source static Net_192.168.75.0_24 Net_192.168.75.0_24 destination static net_10.1.1.0_24 net_10.1.1.0_24
translate_hits = 9, untranslate_hits = 9
2 (inside) to (dmz) source static Host-A Host-B
translate_hits = 26, untranslate_hits = 26
3 (inside) to (outside) source dynamic Net_192.168.75.0_24 interface
translate_hits = 98, untranslate_hits = 138
Auto NAT Policies (Section 2)
1 (inside) to (dmz) source static obj-192.168.75.99 obj-192.168.76.99 dns
translate_hits = 1, untranslate_hits = 0
Manual NAT Policies (Section 3)
1 (inside) to (dmz) source dynamic Net_192.168.75.0_24 pat-pool range-192.168.76.20-22 flat include-reserve
translate_hits = 0, untranslate_hits = 0
Verificatie via pakkettracer:
firepower# packet-tracer input inside icmp 192.168.75.15 8 0 192.168.76.5 Phase: 1 Type: CAPTURE Subtype: Result: ALLOW Config: Additional Information: MAC Access list Phase: 2 Type: ACCESS-LIST Subtype: Result: ALLOW Config: Implicit Rule Additional Information: MAC Access list Phase: 3 Type: ROUTE-LOOKUP Subtype: Resolve Egress Interface Result: ALLOW Config: Additional Information: found next-hop 192.168.76.5 using egress ifc dmz Phase: 4 Type: ACCESS-LIST Subtype: log Result: ALLOW Config: access-group CSM_FW_ACL_ global access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268434434 access-list CSM_FW_ACL_ remark rule-id 268434434: ACCESS POLICY: ACP - Mandatory access-list CSM_FW_ACL_ remark rule-id 268434434: L4 RULE: DEFAULT ACTION RULE Additional Information: This packet will be sent to snort for additional processing where a verdict will be reached Phase: 5 Type: CONN-SETTINGS Subtype: Result: ALLOW Config: class-map class-default match any policy-map global_policy class class-default set connection advanced-options UM_STATIC_TCP_MAP service-policy global_policy global Additional Information: Phase: 6 Type: NAT Subtype: Result: ALLOW Config: nat (inside,dmz) after-auto source dynamic Net_192.168.75.0_24 pat-pool range-192.168.76.20-22 flat include-reserve Additional Information: Dynamic translate 192.168.75.15/0 to 192.168.76.20/11654 Phase: 7 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Phase: 8 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Phase: 9 Type: INSPECT Subtype: np-inspect Result: ALLOW Config: class-map inspection_default match default-inspection-traffic policy-map global_policy class inspection_default inspect icmp service-policy global_policy global Additional Information: Phase: 10 Type: INSPECT Subtype: np-inspect Result: ALLOW Config: Additional Information: Phase: 11 Type: NAT Subtype: rpf-check Result: ALLOW Config: nat (inside,dmz) after-auto source dynamic Net_192.168.75.0_24 pat-pool range-192.168.76.20-22 flat include-reserve Additional Information: Phase: 12 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Phase: 13 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Phase: 14 Type: FLOW-CREATION Subtype: Result: ALLOW Config: Additional Information: New flow created with id 7289, packet dispatched to next module Result: input-interface: inside input-status: up input-line-status: up output-interface: dmz output-status: up output-line-status: up Action: allow
Verifiëren
Gebruik deze sectie om te controleren of uw configuratie goed werkt.
Verificatie is uitgelegd in de afzonderlijke taaksecties.
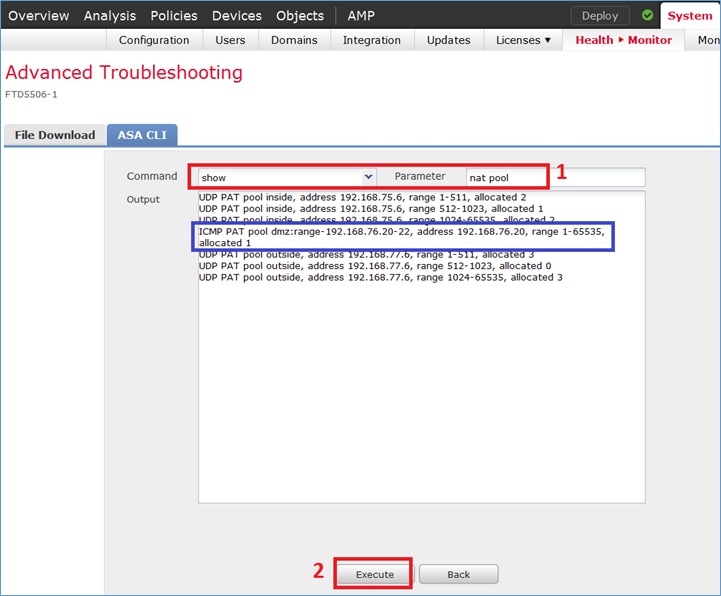
Problemen oplossen
Deze sectie bevat informatie die u kunt gebruiken om problemen met de configuratie te troubleshooten.
Open de pagina Apparaat > Problemen oplossen > Pakkettracer op de FMC en voer de pakkettracer uit en voer vervolgens de opdracht NAT-pool weergeven uit in Apparaat > Problemen oplossen > CLI voor bedreigingsbeveiliging.
Steekproefuitvoer:
FTDv# show nat pool
UDP PAT pool inside, address 192.168.75.6, range 1-511, allocated 2
UDP PAT pool inside, address 192.168.75.6, range 512-1023, allocated 1
UDP PAT pool inside, address 192.168.75.6, range 1024-65535, allocated 2
ICMP PAT pool dmz, range-192.168.76.20-22, address 192.168.76.20, range 1-65535, allocated 1
UDP PAT pool outside, address 192.168.77.6, range 1-511, allocated 3
UDP PAT pool outside, address 192.168.77.6, range 512-1023, allocated 0
UDP PAT pool outside, address 192.168.77.6, range 1024-65535, allocated 3
Gerelateerde informatie
- Alle versies van de Cisco Firepower Management Center-configuratiehandleiding vindt u hier:
Navigeren door de documentatie van Cisco Secure Firewall Threat Defense
- Cisco Global Technical Assistance Center (TAC) beveelt deze visuele gids ten zeerste aan voor diepgaande praktische kennis over Cisco Firepower Next Generation Security Technologies, waaronder de in dit artikel genoemde:
Cisco Press - Firepower Threat Defence
- Voor alle configuratie- en probleemoplossende TechNotes die betrekking hebben op Firepower-technologieën:
Revisiegeschiedenis
| Revisie | Publicatiedatum | Opmerkingen |
|---|---|---|
4.0 |
16-Mar-2026
|
Verwijder de laatste afbeelding. |
3.0 |
19-Dec-2024
|
Cisco Internal Info Box Code bijgewerkt naar rood en opmaak. |
2.0 |
02-Aug-2023
|
Alt-tekst toegevoegd.
Bijgewerkte SEO, machinevertaling, stijlvereisten en opmaak. |
1.0 |
29-Jan-2018
|
Eerste vrijgave |
Bijgedragen door Cisco-engineers
- Mikis Zafeiroudistechnisch adviseur
- John Longtechnisch adviseur
Contact Cisco
- Een ondersteuningscase openen

- (Vereist een Cisco-servicecontract)
 Feedback
Feedback