Cisco Wireless Controller Configuration Guide, Release 8.3
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- July 28, 2016
Chapter: Workgroup Bridges
Workgroup
Bridges
Cisco WGBs
Information About Cisco Workgroup Bridges
A workgroup bridge (WGB) is a mode that can be configured on an autonomous IOS access point to provide wireless connectivity to a lightweight access point on behalf of clients that are connected by Ethernet to the WGB access point. A WGB connects a wired network over a single wireless segment by learning the MAC addresses of its wired clients on the Ethernet interface and reporting them to the lightweight access point using Internet Access Point Protocol (IAPP) messaging. The WGB provides wireless access connectivity to wired clients by establishing a single wireless connection to the lightweight access point. The lightweight access point treats the WGB as a wireless client.
A Cisco IOS AP as a WGB using the Cisco IOS 15.2 or later releases support Protected Extensible Authentication Protocol (PEAP) with the controller.
 Note | If the lightweight access point fails, the WGB attempts to associate to another access point. |
-
The WGB can be any autonomous access point that supports the workgroup bridge mode and is running Cisco IOS Release 12.4(3g)JA or later releases (on 32-MB access points) or Cisco IOS Release 12.3(8)JEB or later releases (on 16-MB access points). These access points include the AP1120, AP1121, AP1130, AP1231, AP1240, and AP1310. Cisco IOS releases prior to 12.4(3g)JA and 12.3(8)JEB are not supported. 
Note
See the sample WGB access point configuration in the WGB Configuration Example section.
-
Wired clients connected to the WGB are not authenticated for security. Instead, the WGB is authenticated against the access point to which it associates. Therefore, we recommend that you physically secure the wired side of the WGB.
-
Wired clients connected to a WGB inherit the WGB’s QoS and AAA override attributes.
-
To enable the WGB to communicate with the lightweight access point, create a WLAN and make sure that Aironet IE is enabled.
-
If you have to apply ACL to WGB during run time, do not modify the ACL configuration for interface in the controller during run time. If you need to modify any ACLs, then you must disable all WLANs that are in the controller or disable both the 802.11a and 80.11b networks. Also, ensure that there are no clients associated and mapped to that interface and then you can modify the ACL settings.
Workgroup Bridge (WGB) Downstream Broadcast On Multiple VLANs
Cisco Wireless LAN Controller (WLC) Release 8.3 provides an enhancement to broadcast traffic support on multiple 802.1Q VLAN workgroup bridge (WGB) deployments that traverse mesh networks and in Local mode. Specifically, support for WGB downstream broadcasts over multiple VLANs (to differentiate and prioritize traffic); and, bridging of VLAN traffic to wired clients connected to the WGB. Applications for this functionality are commonly found in the transportation and mining industries. For more information, see CSCub87583.
Supported platforms:
Supported AP mode:
-
Local mode
-
Bridge mode
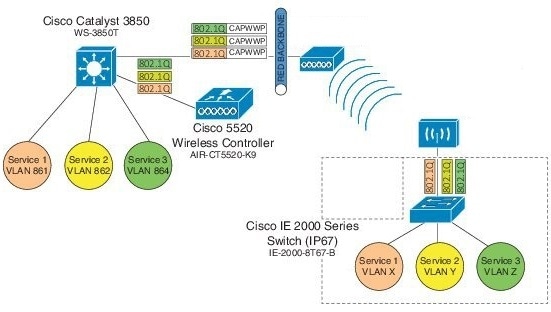
Prerequisites
You need to create the dynamic interfaces and bind them to the interface group before you proceed with the configuration.
-
Create the dynamic interfaces, by choosing on WLC. Add any dynamic interface that needs to support the downstream broadcast on Multiple VLANs feature into the interface group.
-
Bind the dynamic interfaces with Interface Groups, by choosing on WLC.
-
Bind the Interface Groups to WLAN. Choose WLAN. Under the specific WLAN General confirmation tab, choose the proper interface group.
Cisco Wireless Controller Configuration (CLI Only)
To enable or disable the downlink broadcast packet VLAN tagging on a WLAN (new command):
(Cisco Controller) >config wlan wgb broadcast-tagging {enable | disable} wlan-id
 Note | This feature is disabled by default. |
 Note | To enable this feature, you need to enable Broadcast Forwarding on WLC, by choosing and choose Enabled from the Broadcast Forwarding drop-down list. |
 Note | To enable this feature, you should also configure the AP Multicast Mode to Multicast rather than Unicast, by clicking and choosing Multicast, and then assign Multicast Group Address. |
WGB Configuration (CLI Only)
You can configure the following on Workgroup Bridges:
-
Broadcast Tagging
-
Native VLANs
By default, Broadcast Tagging is disabled.
By default, only Native VLAN broadcasts can be forwarded to wired clients in Native VLANs.
You use the no command to disable VLAN configurations on the WGB as shown in the examples below.
 Note | When you have multiple VLAN configurations on WGB, you need to configure the encryption cipher mode and keys as the following example shows: encryption vlan 861 mode ciphers aes-ccm encryption vlan 862 mode ciphers aes-ccm encryption vlan 864 mode ciphers aes-ccm Then, you should configure the encryption cipher mode globally on the multicast or broadcast interface by entering the following command: encryption mode ciphers aes-ccm |
VLAN Broadcast Tagging Configuration
-
To enable broadcast tagging on a VLAN (new command):
(WGB) (config)#workgroup-bridge unified-vlan-client broadcast-tagging
-
To disable broadcast tagging on a VLAN:
(WGB) (config)#no workgroup-bridge unified-vlan-client broadcast-tagging
 Note | The no workgroup-bridge unified-vlan-client broadcast-tagging command will disable workgroup-bridge unified-vlan-client as well. Make sure you have workgroup-bridge unified-vlan-client configured properly to enable the multiple vlan feature. |
Restrictions for Cisco Workgroup Bridges
-
Only WGBs in client mode (which is the default value) are supported. Those WGBs in infrastructure mode are not supported. Perform one of the following to enable client mode on the WGB:
-
On the WGB access point GUI, choose Disabled for the Reliable Multicast to WGB parameter.
-
On the WGB access point CLI, enter the no infrastructure client command.

Note
VLANs are not supported for use with WGBs.

Note
See the sample WGB access point configuration in the WGB Configuration Example section.
-
-
The following features are not supported for use with a WGB:
-
The WGB supports a maximum of 20 wired clients. If you have more than 20 wired clients, use a bridge or another device.
-
The DirectStream feature from the controller does not work for clients behind workgroup bridges and the stream is denied.
-
With Layer 3 roaming, if you plug a wired client into the WGB network after the WGB has roamed to another controller (for example, to a foreign controller), the wired client’s IP address displays only on the anchor controller, not on the foreign controller.
-
If a wired client does not send traffic for an extended period of time, the WGB removes the client from its bridge table, even if traffic is continuously being sent to the wired client. As a result, the traffic flow to the wired client fails. To avoid the traffic loss, prevent the wired client from being removed from the bridge table by configuring the aging-out timer on the WGB to a large value using the following Cisco IOS commands on the WGB:
configure terminal bridge bridge-group-number aging-time seconds exit end
where bridge-group-number is a value between 1 and 255, and seconds is a value between 10 and 1,000,000 seconds. We recommend configuring the seconds parameter to a value greater than the wired client’s idle period.
-
When you delete a WGB record from the controller, all of the WGB wired clients’ records are also deleted.
-
These features are not supported for wired clients connected to a WGB:
-
The broadcast forwarding toward wired WGB clients works only on the native VLAN. If additional VLANs are configured, only the native VLAN forwards broadcast traffic.
-
Wired clients behind a WGB cannot connect to a DMZ/Anchor controller. To enable wired clients behind a WGB to connect to an anchor controller in a DMZ, you must enable VLANs in the WGB using the config wgb vlan enable command.
-
The dot11 arp-cache global configuration command that you can enter on the access point that is in WGB mode is not supported.
-
WGB clients do not show enc-cipher and AKM because they are wired clients. WGB APs, however, show correct values of enc-cipher and AKM.
WGB Configuration Example
The following is an example of the configuration of a WGB access point using static WEP with a 40-bit WEP key:
ap# configure terminal Enter configuration commands, one per line. End with CNTL/Z. ap(config)# dot11 ssid WGB_with_static_WEP ap(config-ssid)# authentication open ap(config-ssid)# guest-mode ap(config-ssid)# exit ap(config)# interface dot11Radio 0 ap(config)# station-role workgroup-bridge ap(config-if)# encry mode wep 40 ap(config-if)# encry key 1 size 40 0 1234567890 ap(config-if)# ssid WGB_with_static_WEP ap(config-if)# end
Verify that the WGB is associated to an access point by entering this command on the WGB:
Information similar to the following appears:
ap# show dot11 associations 802.11 Client Stations on Dot11Radio0: SSID [FCVTESTING] : MAC Address IP address Device Name Parent State 000b.8581.6aee 10.11.12.1 WGB-client map1 - Assoc ap#
Viewing the Status of Workgroup Bridges (GUI)
Viewing the Status of Workgroup Bridges (CLI)
Debugging WGB Issues (CLI)
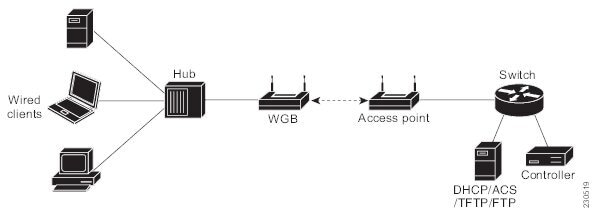
Third-Party WGBs and Client VMs
Information About Non-Cisco Workgroup Bridges
When a Cisco workgroup bridge (WGB) is used, the WGB informs the access points of all the clients that it is associated with. The controller is aware of the clients associated with the access point. When non-Cisco WGBs are used, the controller has no information about the IP address of the clients on the wired segment behind the WGB. Without this information, the controller drops the following types of messages:
-
The controller can accommodate non-Cisco WGBs so that the controller can forward ARP, DHCP, and data traffic to and from the wired clients behind workgroup bridges by enabling the passive client feature. To configure your controller to work with non-Cisco WGBs, you must enable the passive client feature so that all traffic from the wired clients is routed through the WGB to the access point. All traffic from the wired clients is routed through the work group bridge to the access point.

Note
For FlexConnect APs in local switching, non-Cisco workgroup-bridge clients in bridged mode are supported using the config flexconnect group group-name dhcp overridden-interface enable command.
-
When a WGB wired client leaves a multicast group, the downstream multicast traffic to other WGB wired clients is interrupted briefly.
-
If you have clients that use PC virtualization software such as VMware, you must enable this feature.
-
You must enable the passive client functionality for all non-Cisco workgroup bridges.
-
You might need to use the following commands to configure DHCP on clients:
Restrictions for Non-Cisco Workgroup Bridges
Layer 3 security (web authentication) is not support for WGB clients.
Visibility of wired hosts behind a WGB on a controller is not supported because the non-Cisco WGB device performs MAC hiding. Cisco WGB supports IAPP.
ARP poisoning detection does not work on a WLAN when the flag is enabled.
Some third-party WGBs need to operate in non-DHCP relay mode. If problems occur with the DHCP assignment on devices behind the non-Cisco WGB, use the config dhcp proxy disable and config dhcp proxy disable bootp-broadcast disable commands.
The default state is DHCP proxy enabled. The best combination depends on the third-party characteristics and configuration.
 Feedback
Feedback