Configuring ISA Policies for Regulating Network Access
Available Languages
Table Of Contents
Configuring ISA Policies for Regulating Network Access
Information About ISA Policies for Regulating Network Access
Methods of Regulating Network Access
How to Configure ISA Policies for Regulating Network Access
Configuring Policing in a Service Policy Map on the Router
Configuring Policing in a Service Profile or User Profile on the AAA Server
Configuring Per-Subscriber Firewalls
Configuring Per-Subscriber Firewalls in User Profiles or Service Profiles on a AAA Server
Configuring Per-Subscriber Firewalls in a Service Policy Map
Verifying ISA Per-Subscriber Firewalls
Configuration Examples for ISA Policies for Regulating Network Access
Per-Subscriber Firewalls: Examples
Feature Information for ISA Policies for Regulating Network Access
Configuring ISA Policies for Regulating Network Access
The Intelligent Service Architecture (ISA) is a core set of Cisco IOS components that provide a structured framework in which edge access devices can deliver flexible and scalable services to subscribers. A Cisco device that is running a Cisco IOS image with ISA is called an Intelligent Service Gateway (ISG). ISA supports the use of policies for governing subscriber session bandwidth and network accessibility. This module provides information about the following methods of regulating session bandwidth and network access: Modular Quality of Service (QoS) command-line interface (CLI) policies, Dynamic Subscriber Bandwidth Selection (DBS), per-subscriber firewalls, and ISA policing.
Module History
This module was first published on April 28, 2005, and last updated on April 28, 2005.
Finding Feature Information in This Module
Your Cisco IOS software release may not support all features. To find information about feature support and configuration, use the "Feature Information for ISA Policies for Regulating Network Access" section.
Contents
•
Information About ISA Policies for Regulating Network Access
•
How to Configure ISA Policies for Regulating Network Access
•
Configuration Examples for ISA Policies for Regulating Network Access
•
Feature Information for ISA Policies for Regulating Network Access
Information About ISA Policies for Regulating Network Access
Before you configure ISA policies for regulating network access, you should understand the following concept:
•
Methods of Regulating Network Access
Methods of Regulating Network Access
ISA supports the following methods of regulating network access. Each of these methods can be applied to an ISA session and can be dynamically updated.
Modular QoS CLI (MQC) Policies
QoS policies configured using the MQC are supported for subscriber sessions only. MQC policies cannot be applied to ISA services.
Dynamic Subscriber Bandwidth Selection (DBS)
DBS enables you to control bandwidth at the ATM virtual circuit (VC) level. ATM QoS parameters from the subscriber domain are applied to the ATM permanent virtual circuit (PVC) on which a PPP over Ethernet (PPPoE) or PPP over ATM (PPPoA) session has been established.
Per-Subscriber Firewalls
Per-subscriber firewalls are access control lists (ACLs) that are used to prevent subscribers, services, and pass-through traffic from accessing specific IP addresses and ports. Per-subscriber firewalls can be configured in user profiles and service profiles.
ISA Policing
ISA policing supports policing of upstream and downstream traffic. ISA policing differs from policing configured using the MQC in that ISA policing can be configured in service profiles to support policing of traffic flows. MQC policies cannot be configured in service profiles. ISA policing can also be configured in user profiles and service profiles to support session policing.
How to Configure ISA Policies for Regulating Network Access
This section contains procedures for configuring ISA policing and per-subscriber firewalls. See the "Additional References" section for references to information on how to configure MQC policies, DBS, and support for dynamic updates to policies for regulating network access.
This section contains the following tasks:
•
Configuring Per-Subscriber Firewalls
Configuring ISA Policing
Before you configure ISA policing, you should understand the following concept:
To configure ISA policing, perform the following tasks:
•
Configuring Policing in a Service Policy Map on the Router
•
Configuring Policing in a Service Profile or User Profile on the AAA Server
Overview of ISA Policing
Traffic policing allows you to control the maximum rate of traffic sent or received on an interface. Policing is often configured on interfaces at the edge of a network to limit traffic into or out of the network. Traffic that falls within the rate parameters is sent, whereas traffic that exceeds the parameters is dropped or sent with a different priority.
ISA policing supports policing of upstream and downstream traffic and can be applied to a session or a flow. The following sections describe session- based and flow-based policing.
Session-Based Policing
Session-based policing applies to the aggregate of subscriber traffic for a session. In Figure 3, session policing would be applied to all traffic moving from the PPPoE client to ISG and from ISG to the PPPoE client.
Figure 3 Session-Based Policing

Session-based policing parameters can be configured on a AAA server in either a user profile or a service profile that does not specify a traffic class. It can also be configured on the router in a service policy map. Session-based policing parameters that are configured in a user profile take precedence over session-based policing parameters configured in a service profile or service policy map.
Flow-Based Policing
Flow-based policing applies only to the destination-based traffic flows that are specified by a traffic class. In Figure 4 flow-based policing would allow you to police the traffic between the PPPoE client and Internet 1 or Internet 2.
Figure 4 Flow-Based Policing
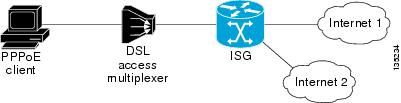
Flow-based policing can be configured on a AAA server in a service profile that specifies a traffic class. It can also be configured on the router under a traffic class in a service policy map. Flow-based policing and session-based policing can coexist and operate simultaneously on subscriber traffic.
Configuring Policing in a Service Policy Map on the Router
Perform this task to configure ISA policing on the router using the CLI.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
policy-map type service policy-map-name
4.
class type traffic class-map-name
5.
police input committed-rate normal-burst excess-burst
6.
police output committed-rate normal-burst excess-burst
DETAILED STEPS
What to Do Next
You may want to configure a method of activating the service policy map; for example, control policies can be used to activate services. For more information about methods of service activation, see the module "Configuring ISA Subscriber Services."
Configuring Policing in a Service Profile or User Profile on the AAA Server
SUMMARY STEPS
1.
Add the Policing VSA to the user profile or service profile on the AAA server.
DETAILED STEPS
What to Do Next
You may want to configure a method of activating the service profile; for example, control policies can be used to activate services. For more information about methods of service activation, see the module "Configuring ISA Subscriber Services."
Verifying ISA Policing
Perform this task to verify ISA policing configuration.
SUMMARY STEPS
1.
enable
2.
show subscriber session [detailed] [identifier identifier | uid session-id | username name]
DETAILED STEPS
Examples
The following example shows output for the show subscriber session command when policing parameters have been configured in the service profile. The "Config level" field indicates where the policing parameters are configured; in this case, in the service profile.
Router# show subscriber session detailedCurrent Subscriber Information: Total sessions 2Unique Session ID: 1.....Session inbound features:Feature: PolicingUpstream Params:Average rate = 24000, Normal burst = 4500, Excess burst = 9000Config level = ServiceSession outbound features:Feature: PolicingDnstream Params:Average rate = 16000, Normal burst = 3000, Excess burst = 6000Config level = Service.....The following example shows output for the show subscriber session command where upstream policing parameters are specified in a user profile and downstream policing parameters are specified in a service profile.
Router# show subscriber session allCurrent Subscriber Information: Total sessions 2Unique Session ID: 2.....Session inbound features:Feature: PolicingUpstream Params:Average rate = 24000, Normal burst = 4500, Excess burst = 9000Config level = Per-user ===========> Upstream parameters are specified inthe user profile.Session outbound features:Feature: PolicingDnstream Params:Average rate = 16000, Normal burst = 3000, Excess burst = 6000Config level = Service ============> No downstream parameters in the userprofile, hence the parameters in the service profile are applied......Configuring Per-Subscriber Firewalls
Before you configure per-subscriber firewalls, you should understand the following concepts:
To configure per-session ACLs, perform the following tasks:
•
Configuring Per-Subscriber Firewalls in User Profiles or Service Profiles on a AAA Server
•
Configuring Per-Subscriber Firewalls in a Service Policy Map
•
Verifying ISA Per-Subscriber Firewalls
Per-Subscriber Firewalls
Per-subscriber firewalls are Cisco IOS ACLs that are used to prevent subscribers, services, and pass-through traffic from accessing specific IP addresses and ports.
ACLs can be configured in user profiles or service profiles on a AAA server or in service policy maps on the ISG. The ACLs can be numbered or named access lists that are configured on the ISG, or the ACL statements can be included in the profile configuration.
When an ACL is added to a service, all subscribers of that service are prevented from accessing the specified IP address, subnet mask, and port combinations through the service.
When an ACL attribute is added to a user profile, it applies globally to all traffic for the subscriber.
Prerequisites
This task assumes that you know how to configure access control lists.
Restrictions
Only IP ACLs are supported on flows, IP subscriber sessions, and forwarded sessions. IPX and IPv6 ACLs are not supported.
Configuring Per-Subscriber Firewalls in User Profiles or Service Profiles on a AAA Server
Perform this task to configure per-subscriber firewalls in user profiles or service profiles on a AAA server.
SUMMARY STEPS
1.
Add the Upstream Access Control List Cisco AV-Pair attribute to the user profile or service profile.
2.
Add the Downstream Access Control List Cisco AV-Pair attribute to the user profile or service profile.
DETAILED STEPS
What to Do Next
You may want to configure a method of activating the service profile; for example, control policies can be used to activate services. For more information about methods of service activation, see the module "Configuring ISA Subscriber Services."
Configuring Per-Subscriber Firewalls in a Service Policy Map
Perform this task to configure a per-subscriber firewall in a service policy map on the ISG.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
policy-map type service policy-map-name
4.
ip access-group {access-list-number | access-list-name}{in | out}
DETAILED STEPS
What to Do Next
You may want to configure a method of activating the service profile; for example, control policies can be used to activate services. For more information about methods of service activation, see the module "Configuring ISA Subscriber Services."
Verifying ISA Per-Subscriber Firewalls
Perform this task to verify the configuration of ISA per-subscriber firewalls.
SUMMARY STEPS
1.
enable
2.
show subscriber session detailed
3.
show ip access-lists
DETAILED STEPS
Examples
The following example is sample output for the show subscriber session detailed command. Information about per-subscriber firewalls appears in the "Session inbound features" and "Session outbound features" fields.
Router# show subscriber session detailedCurrent Subscriber Information: Total sessions 1--------------------------------------------------Session inbound features:Feature: Access listsActive IP access list:104Session outbound features:Feature: Access listsActive IP access list:subscriber_feature#102341017649The show ip access-lists command can be used to display access list statements. The following example is sample output for the show ip access-lists command:
Router# show ip access-listsExtended IP access list 104 (Compiled)10 permit ip host 10.0.1.6 any (500 matches)Extended IP access list subscriber_feature#102341017649 (per-user)10 deny icmp host 25.25.25.25 host 3.3.3.320 permit ip any anyConfiguration Examples for ISA Policies for Regulating Network Access
This section contains the following examples:
•
Per-Subscriber Firewalls: Examples
ISA Policing: Examples
Flow-Based Policing Configured in a Service Policy Map Using the CLI: Example
The following example shows the configuration of ISA flow-based policing in a service policy map:
class-map type traffic match-any C3match access-group in 103match access-group out 203policy-map type service P3class type traffic C3police input 20000 30000 60000police output 21000 31500 63000Session-Based Policing Configured in a User Profile on a AAA Server: Example
The following example shows policing configured in a user profile:
Cisco:Account-Info = "QU;23465;8000;12000;D;64000"Session-Based Policing Configured in a Service Profile on a AAA Server: Example
The following example shows policing configured in a service profile:
Cisco:Service-Info = "QU;16000;D;31000"Per-Subscriber Firewalls: Examples
The following example shows per-subscriber firewalls configured in a user profile or service profile on the AAA server. In this case the ACLs 104 and 105 are configured on the router. "In" and "out" represent the inbound and outbound direction of ACL application.
Cisco-AVpair="ip:inacl=104",Cisco-AVpair="ip:outacl=105"The following example shows per-subscriber firewalls configured in a user profile or service profile on the AAA server. In this case the named ACLs are configured on the router.
Cisco-AVpair="ip:inacl=named-inacl-123",Cisco-AVpair="ip:outacl=named-outacl-123"The following example of per-subscriber firewall configuration includes the individual ACL statements in the user profile or service profile configuration:
Cisco-AVpair="ip:inacl#1=deny icmp host 25.25.25.25 host 3.3.3.3",Cisco-AVpair="ip:inacl#2=permit ip any any",Cisco-AVpair="ip:outacl#1=permit ip any any"Additional References
The following sections provide references related to ISA policies for regulating network access.
Related Documents
Technical Assistance
Feature Information for ISA Policies for Regulating Network Access
Table 17 lists the features in this module and provides links to specific configuration information. Only features that were introduced or modified in Cisco IOS Release 12.2(27)SBA or later releases appear in the table.
Not all commands may be available in your Cisco IOS software release. For details on when support for specific commands was introduced, see the command reference documents.
If you are looking for information on a feature in this technology that is not documented here, see the "Intelligent Service Architecture Features Roadmap."
Cisco IOS software images are specific to a Cisco IOS software release, a feature set, and a platform. Use Cisco Feature Navigator to find information about platform support and Cisco IOS software image support. Access Cisco Feature Navigator at http://www.cisco.com/go/fn. You must have an account on Cisco.com. If you do not have an account or have forgotten your username or password, click Cancel at the login dialog box and follow the instructions that appear.

Note
Table 17 lists only the Cisco IOS software release that introduced support for a given feature in a given Cisco IOS software release train. Unless noted otherwise, subsequent releases of that Cisco IOS software release train also support that feature.
Table 17 Feature Information for Policies for Regulating Network Access
ISA: Flow Control: QoS Control: Dynamic Rate Limiting
12.2(27)SBA
ISA can change the allowed bandwidth of a session or flow by dynamically applying rate-limiting policies.
The following sections provide information about this feature:
•
Methods of Regulating Network Access

Copyright © 2005 Cisco Systems, Inc. All rights reserved.
This module first published April 28, 2005. Last updated April 28, 2005.
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
This Document Applies to These Products
- Collaboration Endpoints - Retired Products
- Conferencing - Retired Products
- Contact Center - Retired Products
- Optical Networking - Retired Products
- Routers - Retired Products
- Security - Retired Products
- Servers - Unified Computing (UCS) Retired Products
- Storage Networking Retired Products
- Switches - Retired Products
- Video - Retired Products
- Wireless - Retired Products
 Feedback
Feedback