Future-ready networks built for lasting growth
Connect communities to new opportunities with flexible, high-performing networks that scale with demand.
Protect your investments
Set up an elastic infrastructure built to meet the increasing bandwidth demands on your network.
Grow your revenue
Make your network agile so you can bring connected, resilient experiences and services to your subscribers.
Cut costs with convergence
Build a flexible network that works across different access technologies and more efficiently utilizes network resources.
Boost performance and resiliency
Streamline operations, mitigate risks, and enhance network performance with deeper visibility, efficient troubleshooting, and automation across the network.
Advanced solutions for service providers
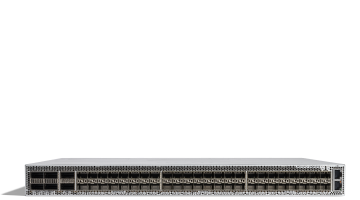
Agile Services Networking
Discover a network architecture optimized for flexible service deployment, to power AI-ready connectivity and improve user experiences.
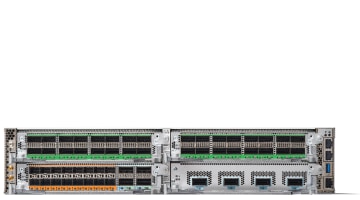
Routed Optical Networking
Improve network and operational efficiencies by converging IP and optical layers, cutting costs and ensuring reliable, high-speed connections.
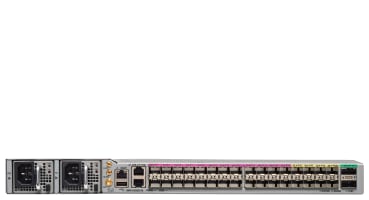
Routed PON
Unify services on a flexible network, ensuring top performance with real-time insights and proactive monitoring.
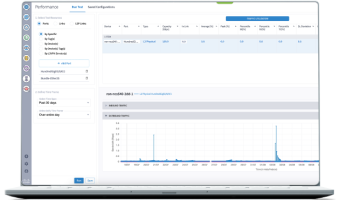
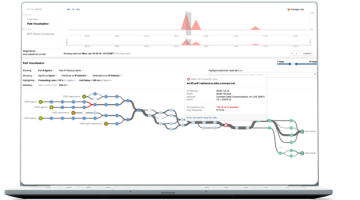
Crosswork Network Automation
Manage multivendor and multidomain networks efficiently with our scalable, AI-powered unified platform.
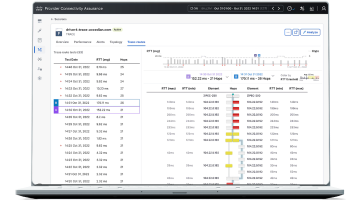
Provider Connectivity Assurance
Get granular visibility and insights across multivendor, multilayer, and multidomain networks to deliver exceptional digital experiences.
ThousandEyes
Assure digital experiences across every domain—including your owned and even unowned networks.
Unlock public broadband funding
Secure funding, expand your network, and connect more underserved communities with government programs and certified solutions.
See what customers have to say
Flexible deployment, optimized growth
Broadband Innovation Center (BIC) Tech Talk Series
Join monthly webinar sessions to explore cutting-edge solutions—like network convergence, AI, automation, and last-mile tech—and answer your top-of-mind challenges.
Cisco Capital payment solutions
Explore payment solutions to help you close funding gaps, accelerate deployments, and deliver broadband where it’s needed most.
Cisco sustainability programs
Transform your network and join Cisco on the journey to a sustainable and inclusive future.