- Index
- New and Changed Information
- Preface
- Overview
- Configuring AAA
- Configuring RADIUS
- Configuring TACACS+
- Configuring SSH and Telnet
- Configuring User Accounts and RBAC
- Configuring 802.1X
- Configuring NAC
- Configuring Cisco TrustSec
- Configuring IP ACLs
- Configuring MAC ACLs
- Configuring VLAN ACLs
- Configuring Port Security
- Configuring DHCP Snooping
- Configuring Dynamic ARP Inspection
- Configuring IP Source Guard
- Configuring Keychain Management
- Configuring Traffic Storm Control
- Configuring Unicast RPF
- Configuring Contol Plane Policing
- Configuring Rate Limits
Cisco Nexus 7000 Series NX-OS Security Configuration Guide, Release 4.0
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- June 13, 2008
Chapter: Configuring NAC
- Information About NAC
- Licensing Requirements for NAC
- Prerequisites for NAC
- NAC Guidelines and Limitations
- Configuring NAC
- Process for Configuring NAC
- Enabling EAPoUDP
- Enabling the Default AAA Authenication Method for EAPoUDP
- Applying PACLs to Interfaces
- Enabling NAC on an Interface
- Configuring Identity Policies and Identity Profile Entries
- Allowing Clientless Endpoint Devices
- Enabling Logging for EAPoUDP
- Changing the Global EAPoUDP Maximum Retry Value
- Changing the EAPoUDP Maximum Retry Value for an Interface
- Changing the UDP Port for EAPoUDP
- Configuring Rate Limiting of Simultaneous EAPoUDP Posture Validation Sessions
- Configuring Global Automatic Posture Revalidation
- Configuring Automatic Posture Revalidation for an Interface
- Changing the Global EAPoUDP Timers
- Changing the EAPoUDP Timers for an Interface
- Resetting the EAPoUDP Global Configuration to the Default Values
- Resetting the EAPoUDP Interface Configuration to the Default Values
- Configuring IP Device Tracking
- Clearing IP Device Tracking
- Manually Initializing EAPoUDP Sessions
- Manually Revalidating EAPoUDP Sessions
- Clearing EAPoUDP Sessions
- Disabling the EAPoUDP Feature
- Verifying the NAC Configuration
- Example NAC Configuration
- Default Settings
- Additional References
Configuring NAC
This chapter describes how to configure Network Admission Control (NAC) on NX-OS devices.
This chapter includes the following sections:
•![]() Licensing Requirements for NAC
Licensing Requirements for NAC
•![]() NAC Guidelines and Limitations
NAC Guidelines and Limitations
•![]() Verifying the NAC Configuration
Verifying the NAC Configuration
Information About NAC
NAC allows you to check endpoint devices for security compliancy and vulnerability before these devices are allowed access to the network. This security compliancy check is referred to as posture validation. Posture validation allows you to prevent the spread of worms, viruses, and other rogue applications across the network.
NAC validates that the posture or state of endpoint devices complies with security policies before the devices can access protected areas of the network. For devices that comply with the security policies, NAC allows access to protected services in the network. For devices that do not comply with security policies, NAC allows access to the network only for remediation, when the posture of the device is checked again.
This section includes the following topics:
•![]() LPIP Validation and Other Security Features
LPIP Validation and Other Security Features
NAC Device Roles
NAC assigns roles to the devices in the network. Figure 8-1 shows an example of a network with the NAC device roles.
Figure 8-1 Posture Validation Devices
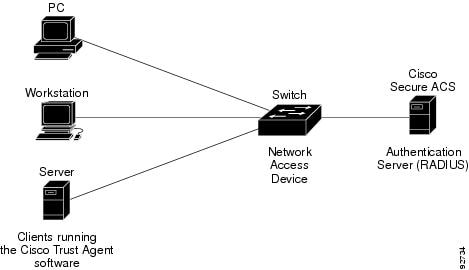
NAC supports the following roles for network devices:
•![]() Endpoint device—Systems or clients on the network such as a PC, workstation, or server that is connected to an NX-OS device access port through a direct connection. The endpoint device, which is running the Cisco Trust Agent software, requests access to the LAN and switch services and responds to requests from the switch. Endpoint devices are potential sources of virus infections, and NAC must validate their antivirus statuses before granting network access.
Endpoint device—Systems or clients on the network such as a PC, workstation, or server that is connected to an NX-OS device access port through a direct connection. The endpoint device, which is running the Cisco Trust Agent software, requests access to the LAN and switch services and responds to requests from the switch. Endpoint devices are potential sources of virus infections, and NAC must validate their antivirus statuses before granting network access.

Note ![]() The Cisco Trust Agent software is also referred to as the posture agent or the antivirus client. For more information on Cisco Trust Agent software, go to the following URL:
The Cisco Trust Agent software is also referred to as the posture agent or the antivirus client. For more information on Cisco Trust Agent software, go to the following URL:
http://www.cisco.com/en/US/products/sw/secursw/ps5057/index.html
•![]() Network access device (NAD)— Cisco NX-OS device that provides validation services and policy enforcement at the network edge and controls the physical access to the network based on the access policy of the client. The NAD relays Extensible Authentication Protocol (EAP) messages between the endpoints and the authentication server.
Network access device (NAD)— Cisco NX-OS device that provides validation services and policy enforcement at the network edge and controls the physical access to the network based on the access policy of the client. The NAD relays Extensible Authentication Protocol (EAP) messages between the endpoints and the authentication server.
The NAD queries for posture credentials whenever it detects a new connection to the network. When the endpoint device has a posture agent (PA) installed, the NAD performs an in-band posture validation. The NAD acts as a relay agent between the endpoint device and AAA server for all messages in the posture validation exchange. If the NAD does not find a PA, the NAD performs an out-of-band posture validation through an audit server.
The NAD controls which hosts have access to network destinations through that device based on a network access profile received from the AAA server once the posture validation exchange completes (whether in-band or out-of-band). The access profile can be one of the following forms:
–![]() VLAN or private VLAN.
VLAN or private VLAN.
–![]() Access control list (ACL)—Determines what type of traffic for which destinations are reachable for this host in addition to any default access that is provided to all hosts independent of the NAC process (for example, access to the Dynamic Host Configuration Protocol (DHCP) server, remediation server, audit server).
Access control list (ACL)—Determines what type of traffic for which destinations are reachable for this host in addition to any default access that is provided to all hosts independent of the NAC process (for example, access to the Dynamic Host Configuration Protocol (DHCP) server, remediation server, audit server).
The NAD triggers the posture validation process at the following times:
–![]() When a new session starts.
When a new session starts.
–![]() When the revalidation timer expires.
When the revalidation timer expires.
–![]() When you enter a system administrator command.
When you enter a system administrator command.
–![]() When the posture agent indicates that the posture has changed (only for an endpoint device with a posture agent).
When the posture agent indicates that the posture has changed (only for an endpoint device with a posture agent).
For Cisco NX-OS devices, the encapsulation information in the Extensible Authentication Protocol (EAP) messages is based on the User Datagram Protocol (UDP). When using UDP, the NX-OS device uses EAP over UDP (EAPoUDP or EoU) frames.
•![]() Authentication server— Server that performs the actual validation of the client. The authentication server validates the antivirus status of the client, determines the access policy, and notifies the NAD if the client is authorized to access the LAN and NAD services. Because the NAD acts as the proxy, the EAP message exchange between the NAD and authentication server is transparent to the NAD.
Authentication server— Server that performs the actual validation of the client. The authentication server validates the antivirus status of the client, determines the access policy, and notifies the NAD if the client is authorized to access the LAN and NAD services. Because the NAD acts as the proxy, the EAP message exchange between the NAD and authentication server is transparent to the NAD.
The Cisco NX-OS device supports the Cisco Secure Access Control Server (ACS) Version 4.0 or later with RADIUS, authentication, authorization, and accounting (AAA), and EAP extensions.
•![]() Posture validation server—Third-party server that acts as an application-specific policy decision point in NAC for authorizing a set of posture credentials against a set of policy rules. The posture validation server receives requests from an authentication server.
Posture validation server—Third-party server that acts as an application-specific policy decision point in NAC for authorizing a set of posture credentials against a set of policy rules. The posture validation server receives requests from an authentication server.
NAC Posture Validation
Posture validation occurs when a NAC-enabled NAD detects an endpoint device that is attempting to connect or use its network resources (see Figure 8-2). When the NAD detects a new endpoint device, it requests the network access profile for the endpoint device from an AAA server (such as the Cisco Secure ACS).
Figure 8-2 NAC Endpoint Device Posture Validation
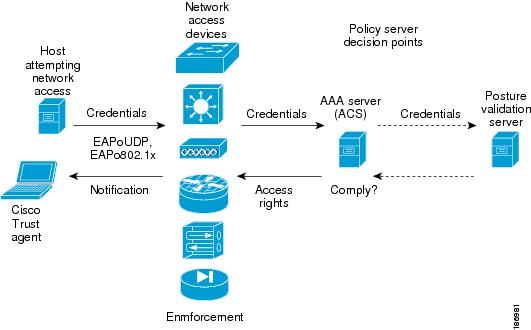
The AAA server determines if the endpoint device has a posture agent installed. If the endpoint device has a posture agent (such as the Cisco Trust Agent), the AAA server requests the endpoint device for posture information via the NAD. The endpoint device responds to the AAA server with a set of posture credentials. The AAA server then validates the posture information locally or delegates the posture validation decisions to one or more external posture validation servers.
If the endpoint device does not have a posture agent, the AAA server may request an audit server to collect posture information from the device through other means (for example, fingerprinting and port scanning). The AAA server also asks the audit server to validate that information and return a posture validation decision.
The AAA server aggregates the posture validation results from these sources and makes an authorization decision that is based on whether the endpoint device complies with the network policy. The AAA server determines the network access profile for the endpoint device and sends the profile to the NAD for enforcement of the endpoint device authorization.
The examination of endpoint device credentials by the AAA server can result in one or more application posture tokens (APTs). An APT represents a compliance check for a given vendor's application. The AAA server aggregates all APTs from the posture validation servers into a single system posture token (SPT) that represents the overall compliance of the endpoint device. The value SPT is based on the worst APT from the set of APTs. Both APTs and SPTs are represented using the following predefined tokens:
•![]() Healthy—The endpoint device complies with the posture policy so no restrictions are placed on this device.
Healthy—The endpoint device complies with the posture policy so no restrictions are placed on this device.
•![]() Checkup—The endpoint device is within policy but does not have the latest software; an update is recommended.
Checkup—The endpoint device is within policy but does not have the latest software; an update is recommended.
•![]() Transition—The endpoint device is in the process of having its posture checked and is given interim access pending a result from a complete posture validation. A transition result may occur when a host is booting and complete posture information is not available, or when complete audit results are not available.
Transition—The endpoint device is in the process of having its posture checked and is given interim access pending a result from a complete posture validation. A transition result may occur when a host is booting and complete posture information is not available, or when complete audit results are not available.
•![]() Quarantine—The endpoint device is out of compliance and must be restricted to a quarantine network for remediation. This device is not actively placing a threat on other endpoint devices but is vulnerable to attack or infection and must be updated as soon as possible.
Quarantine—The endpoint device is out of compliance and must be restricted to a quarantine network for remediation. This device is not actively placing a threat on other endpoint devices but is vulnerable to attack or infection and must be updated as soon as possible.
•![]() Infected—The endpoint device is an active threat to other endpoint devices; network access must be severely restricted and the endpoint device must be placed into remediation or denied all network access to the endpoint device.
Infected—The endpoint device is an active threat to other endpoint devices; network access must be severely restricted and the endpoint device must be placed into remediation or denied all network access to the endpoint device.
•![]() Unknown—The AAA server cannot determine the posture credentials of the endpoint device. You need to determine the integrity of the endpoint device so that proper posture credentials can be attained and assessed for network access authorization.
Unknown—The AAA server cannot determine the posture credentials of the endpoint device. You need to determine the integrity of the endpoint device so that proper posture credentials can be attained and assessed for network access authorization.
IP Device Tracking
The IP device tracking allows endpoint devices to remain connected to the network if the AAA server is not available. Typical deployments of NAC use Cisco Secure ACS to validate the client posture and to pass policies back to the NAD.
IP device tracking provides the following benefits:
•![]() While AAA is unavailable, the endpoint device still has connectivity to the network, although it may be restricted.
While AAA is unavailable, the endpoint device still has connectivity to the network, although it may be restricted.
•![]() When the AAA server is available again, a user can be revalidated and the user's policies can be downloaded from the ACS.
When the AAA server is available again, a user can be revalidated and the user's policies can be downloaded from the ACS.

Note ![]() When the AAA server is down, the NAD applies the IP device tracking policy only if there is no existing policy associated with the host. Typically, during revalidation when the AAA server goes down, the NAD retains the current policies used for the endpoint device.
When the AAA server is down, the NAD applies the IP device tracking policy only if there is no existing policy associated with the host. Typically, during revalidation when the AAA server goes down, the NAD retains the current policies used for the endpoint device.
NAC LAN Port IP Validation
NAC LAN port IP (LPIP) validation uses the Layer 3 transport EAPoUDP to carry posture validation information. LPIP validation has the following characteristics:
•![]() Operates only on Layer 2 ports and cannot operate on Layer 3 ports.
Operates only on Layer 2 ports and cannot operate on Layer 3 ports.
•![]() Subjects all hosts sending IP traffic on the port to posture validation.
Subjects all hosts sending IP traffic on the port to posture validation.
LPIP validation triggers admission control by snooping on DHCP messages or Address Resolution Protocol (ARP) messages rather than intercepting IP packets on the data path. LPIP validation performs policy enforcement using access control lists (ACLs).
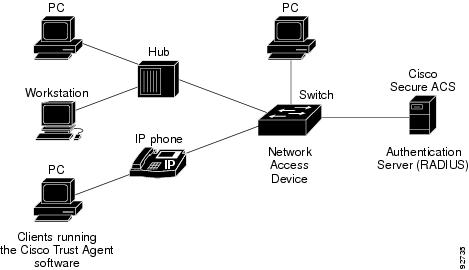
LPIP validation can process a single host connected to a NAD port or multiple hosts on the same NAD port as shown in Figure 8-3.
When you enable LPIP validation, EAPoUDP only supports IPv4 traffic. The NAD checks the antivirus status of the endpoint devices or clients and enforces access control policies.
Figure 8-3 Network Using LPIP Validation
This section describes LPIP validation and includes the following topics:
•![]() Policy Enforcement Using ACLs
Policy Enforcement Using ACLs
•![]() Audit Servers and Nonresponsive Hosts
Audit Servers and Nonresponsive Hosts
•![]() NAC Posture Validation and Redundant Supervisor Modules
NAC Posture Validation and Redundant Supervisor Modules
Posture Validation
When you enable LPIP validation on a port connected to one or more endpoint devices, the Cisco NX-OS device uses DHCP snooping and ARP snooping to identify connected hosts. The NX-OS device initiates posture validation after receiving an ARP packet or creating a DHCP snooping binding entry. ARP snooping is the default method to detect connected hosts. If you want the NAD to detect hosts when a DHCP snooping binding entry is created, you must enable DHCP snooping (see Chapter 14, "Configuring DHCP Snooping").
Admission Triggers
ARP snooping allows LPIP validation to detect hosts with either dynamically acquired or statically configured IP addresses. When the NAD receives an ARP packet from an unknown host, it triggers posture validation. If you have enabled DHCP snooping on the interface, the creation of a DHCP binding entry on the NAD triggers posture validation. DHCP snooping provides a slightly faster response time because DHCP packets are exchanged prior to sending ARP requests. Both ARP snooping and DHCP snooping can trigger posture validation on the same host. In this case, the trigger initiated by the creation of a DHCP snooping binding takes precedence over ARP snooping.

Note ![]() When you use DHCP snooping and ARP snooping to detect the presence of a host, a malicious host might set up a static ARP table to bypass posture validation. To protect against this type of exposure, you can enable IP Source Guard on the port. IP Source Guard prevents unauthorized hosts from accessing the network. (See Chapter 16, "Configuring IP Source Guard.")
When you use DHCP snooping and ARP snooping to detect the presence of a host, a malicious host might set up a static ARP table to bypass posture validation. To protect against this type of exposure, you can enable IP Source Guard on the port. IP Source Guard prevents unauthorized hosts from accessing the network. (See Chapter 16, "Configuring IP Source Guard.")
Posture Validation Methods
After posture validation is triggered for a host, you can use one of two possible methods to determine the policy to be applied for the host:
Exception Lists
An exception list contains local profile and policy configurations. Use the identity profile to statically authorize or validate devices based on the IP address and MAC address. You can associate an identity profile with a local policy that specifies the access control attributes.
Using an exception list, you can bypass posture validation for specific endpoint devices and apply a statically configured policy. After posture validation is triggered, the NAD checks for the host information in the exception list. If a match is found in the exception list, the NAD applies the configured policy for the endpoint device.
EAPoUDP
If an endpoint device does not match the exception list, the NAD sends an EAPoUDP packet to initiate posture validation. While posture validation occurs, the NAD enforces the default access policy. After the NAD sends an EAPoUDP message to the host and the host responds to the antivirus condition request, the NAD forwards the EAPoUDP response to the Cisco Secure ACS. If the NAD does not receive a response from the host after the specified number of attempts, the NAD classifies the host as nonresponsive. After the ACS validates the credentials, the authentication server returns an Access-Accept or Access-Reject message to the NAD. The NAD updates the EAPoUDP session table and enforces the access limitations, which segments and quarantines the poorly postured endpoint device or denies network access.

Note ![]() An Access-Reject message indicates that the EAPoUDP exchange has failed. This message does not indicate that the endpoint device is poorly postured.
An Access-Reject message indicates that the EAPoUDP exchange has failed. This message does not indicate that the endpoint device is poorly postured.
For an Access-Accept message, the NAD applies the enforcement policy that contains the policy-based ACL (PACL) name and starts the EAP revalidation and status query timers. For information on PACLs, see the "Policy Enforcement Using ACLs" section.
For an Access-Reject message, the NAD removes any enforcement policy for the host and puts the endpoint device into the Held state for a configured period of time (Hold timer). After the Hold timer expires, the NAD revalidates the endpoint device.

Note ![]() If you delete a DHCP snooping binding entry for an endpoint device, the NAD removes the client entry in the session table and the client is no longer authenticated.
If you delete a DHCP snooping binding entry for an endpoint device, the NAD removes the client entry in the session table and the client is no longer authenticated.
Policy Enforcement Using ACLs
LPIP validation uses PACLs for policy enforcement.
The NAD applies the PACL when the posture validation fails (the AAA server sends an Access-Reject message). The default policy is to use the active MAC ACL applied to the port (also called a port ACL [PACL]). The active MAC ACL could either be a statically configured PACL or an AAA server-specified PACL based on 802.1X authentication.
The PACL defines a group that expands to a list of endpoint device IP addresses. The PACLs usually contain the endpoint device IP addresses. Once the NAD classifies an endpoint device using a particular group, the NAD adds the IP address that corresponds to the endpoint device to the appropriate group. The result is that the policy is applied to the endpoint device.
When you configure LPIP validation for an NAD port, you must also configure a default PACL on that NAD port. In addition, you should apply the default ACL to the IP traffic for hosts that have not completed posture validation.
If you configure the default ACL on the NAD and the Cisco Secure ACS sends a host access policy to the NAD, the NAD applies the policy to that traffic from the host that is connected to a NAD port. If the policy applies to the traffic, the NAD forwards the traffic. If the policy does not apply, the NAD applies the default ACL. However, if the NAD gets an endpoint device access policy from the Cisco Secure ACS but the default ACL is not configured, the LPIP validation configuration does not take effect.

Note ![]() Both DHCP snooping and ARP snooping are enabled per VLAN. However, security ACLs downloaded as a result of NAC Layer 2 posture validation are applied per port. As a result, all DHCP and ARP packets are intercepted when these features are enabled on any VLAN.
Both DHCP snooping and ARP snooping are enabled per VLAN. However, security ACLs downloaded as a result of NAC Layer 2 posture validation are applied per port. As a result, all DHCP and ARP packets are intercepted when these features are enabled on any VLAN.
Audit Servers and Nonresponsive Hosts
Endpoint devices that do not run a posture agent (Cisco Trust Agent) cannot provide credentials when challenged by NADs. These devices are described as agentless or nonresponsive.
The NAC architecture supports audit servers to validate agentless endpoint devices. An audit server is a third-party server that can probe, scan, and determine security compliance of a host without needing a posture again on the endpoint device. The result of the audit server examination can influence the access servers to make network access policy decisions specific to the endpoint device instead of enforcing a common restrictive policy for all nonresponsive endpoint devices. You can build more robust host audit and examination functionality by integrating any third-party audit operations into the NAC architecture.
Figure 8-4 shows how audit servers fit into the typical topology.
Figure 8-4 NAC Device Roles
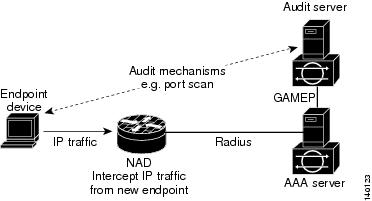
NAC assumes that the audit server can be reached so that the endpoint device can communicate with it. When an endpoint device makes network access through the NAD configured for posture validation, the network access device eventually requests the AAA server (Cisco Secure ACS) for an access policy to be enforced for the host. The AAA server can be configured to trigger a scan of the host with an external audit server. The audit server scan occurs asynchronously and takes several seconds to complete. During the scan, the AAA server conveys a minimal restrictive security policy to NAD for enforcement along with a short poll timer (session-timeout). The NAD polls the AAA sever at the specified timer interval until the result is available from the audit server. After the AAA server receives the audit result, it computes an access policy based on the audit result and sends it to the NAD for enforcement on its next request.
NAC Timers
This section describes the NAC timers and includes the following topics:
Hold Timer
The hold timer prevents a new EAPoUDP session from immediately starting after the previous attempt to validate that the session fails. NAC uses this time only when the Cisco Secure ACS sends an Accept-Reject message to the NAD. The default value of the hold timer is 180 seconds (3 minutes).
An EAPoUDP session might not be validated when the posture validation of the host fails, a session timer expires, or the NAD or Cisco Secure ACS receives invalid messages. If the NAD or authentication server continuously receives invalid messages, a malicious user might be trying to cause a denial-of-service attack.
AAA Timer
The AAA timer controls the amount of time that the NAD waits for a response from the AAA server before resending a request during posture validation. The default value of the retransmission timer is 60 seconds.

Note ![]() Setting the timer value too low might cause unnecessary transmissions; setting the timer value too high might cause poor response times.
Setting the timer value too low might cause unnecessary transmissions; setting the timer value too high might cause poor response times.
Retransmit Timer
The retransmit timer controls the amount of time that the NAD waits for a response from the client before resending a request during posture validation. The default value of the retransmission timer is 3 seconds.

Note ![]() Setting the timer value too low might cause unnecessary transmissions; setting the timer value too high might cause poor response times.
Setting the timer value too low might cause unnecessary transmissions; setting the timer value too high might cause poor response times.
Revalidation Timer
The revalidation timer controls the amount of time that the NAD applies a NAC policy to an endpoint device that used EAPoUDP messages during posture validation. The timer starts after the initial posture validation completes. The timer resets when the host is revalidated. The default value of the revalidation timer is 36000 seconds (10 hours).
The Cisco NX-OS software bases the revalidation timer operation on the Session-Timeout RADIUS attribute (Attribute[27]) and the Termination-Action RADIUS-REQUEST attribute (Attribute[29]) in the Access-Accept message from the AAA server (Cisco Secure ACS). If the NAD receives the Session-Timeout value, this value overrides the revalidation timer value on the NAD.
If the revalidation timer expires, the NAD action depends on one of these values of the Termination-Action attribute:
•![]() If the value of the Termination-Action RADIUS attribute is the default, the session ends.
If the value of the Termination-Action RADIUS attribute is the default, the session ends.
•![]() If the NAD receives a value for the Termination-Action attribute other than the default, the EAPoUDP session and the current access policy remain in effect during posture revalidation.
If the NAD receives a value for the Termination-Action attribute other than the default, the EAPoUDP session and the current access policy remain in effect during posture revalidation.
•![]() If the value of the Termination-Action attribute is RADIUS, the NAD revalidates the client.
If the value of the Termination-Action attribute is RADIUS, the NAD revalidates the client.
•![]() If the packet from the server does not include the Termination-Action attribute, the EAPoUDP session ends.
If the packet from the server does not include the Termination-Action attribute, the EAPoUDP session ends.
Status-Query Timer
The status-query timer controls the amount of time that the NAD waits before verifying that the previously validated client is present and that its posture has not changed. Only clients that were authenticated with EAPoUDP messages use this timer, which starts after the client is initially validated. The default value of the status-query timer is 300 seconds (5 minutes).
The timer resets when the host is reauthenticated. When the timer expires, the NAD checks the host posture validation by sending a Status-Query message to the host. If the host sends a message to the NAD that the posture has changed, the NAD revalidates the posture of the host.
NAC Posture Validation and Redundant Supervisor Modules
When a switchover occurs, the NX-OS device maintains information about the endpoint devices and the current PACL application but loses the current state of each EAPoUDP session. The NX-OS device removes the current PACL application and restarts posture validation.
LPIP Validation and Other Security Features
This section describes how LPIP validation interacts with other security features on the NX-OS device.
This section include the following topics:
802.1X
If you configure both 802.1X and LPIP on a port, the traffic that does not pass the 802.1X-authenticated source MAC check does not trigger posture validation. When you configure 802.1X on a port, the port cannot transmit or receive traffic (other than EAP over LAN [EAPOL] frames) until the attached host is authenticated via 802.1X. This mechanism ensures that the IP traffic from the host does not trigger posture validation before it is authenticated.
Port Security
The NAD checks the source MAC against the port security MACs and drops the endpoint device if the check fails. The NAD allows posture validation only on port security-validated MAC addresses. If a port security violation occurs and results in a port shutdown, the NX-OS software removes the LPIP state of the port.
DHCP Snooping
Posture validation does not occur until after a DHCP creates a binding entry. When you enable DHCP snooping and LPIP, the NX-OS software triggers posture validation for a host when DHCP creates a binding entry for the host using DHCP to acquire IP address.
For information about DHCP snooping, see Chapter 14, "Configuring DHCP Snooping."
Dynamic ARP Inspection
If you enable LPIP validation on the interface, posture validation is triggered only if the packet passes the dynamic ARP inspection (DAI) check. If you do not enable DAI, then all ARP packets (with valid MAC/IP pairs) will trigger posture validation.

Note ![]() ARP snooping is the default mechanism of detecting hosts. However, ARP snooping is not same as DAI. If you enable LPIP validation, the NX-OS software passes the ARP packets to LPIP validation. If you enable DAI, the NX-OS software passes the ARP packets to DAI.
ARP snooping is the default mechanism of detecting hosts. However, ARP snooping is not same as DAI. If you enable LPIP validation, the NX-OS software passes the ARP packets to LPIP validation. If you enable DAI, the NX-OS software passes the ARP packets to DAI.

Note ![]() If you have enabled DHCP snooping, the NX-OS software bypasses DAI.
If you have enabled DHCP snooping, the NX-OS software bypasses DAI.
For information about DAI, see Chapter 15, "Configuring Dynamic ARP Inspection."
IP Source Guard
The NX-OS software drops the packet if the source IP address is not on IP Source Guard list.

Note ![]() If you enable DHCP snooping or DAI, the NAD bypasses IP Source Guard.
If you enable DHCP snooping or DAI, the NAD bypasses IP Source Guard.
Posture Host-Specific ACEs
The NX-OS software drops the packet if the packet matches the deny condition and skips the active PACL if a packet matches a permit condition. If no implicit deny exists at end of the ACEs and no match occurs, the NX-OS software checks the packet against the active PACL.

Note ![]() If you enable DHCP snooping or DAI, the NAD does not process posture host-specific ACEs.
If you enable DHCP snooping or DAI, the NAD does not process posture host-specific ACEs.
Active PACL
The active PACL is either a statically configured PACL or an AAA server-specified PACL that is based on 802.1X authentication. Packet is dropped if matches any deny condition and moves to next step if matches a permit condition.

Note ![]() If you have enabled DHCP snooping or DAI, the NAD does not process the active PACL.
If you have enabled DHCP snooping or DAI, the NAD does not process the active PACL.
VACLs
The NX-OS software drops any packet that matches a deny condition.

Note ![]() If you have enabled DHCP snooping or DAI, the NAD bypasses the VACLs.
If you have enabled DHCP snooping or DAI, the NAD bypasses the VACLs.
Virtualization Support
NAC configuration and operation are local to the virtual device context (VDC).
For more information on VDCs, see the Cisco Nexus 7000 Series NX-OS Virtual Device Context Configuration Guide, Release 4.0.
Licensing Requirements for NAC
The following table shows the licensing requirements for this feature:
Prerequisites for NAC
NAC has the following prerequisites:
•![]() Ensure that a Layer 3 route exists between the NAD and each endpoint device.
Ensure that a Layer 3 route exists between the NAD and each endpoint device.
NAC Guidelines and Limitations
NAC has the following guidelines and limitations:
•![]() NAC uses only RADIUS for authentication.
NAC uses only RADIUS for authentication.
•![]() EAPoUDP bypass and AAA down policy are not supported.
EAPoUDP bypass and AAA down policy are not supported.
LPIP Limitations
LPIP validation has the following limitations:
•![]() LPIP validation is allowed only on access ports.
LPIP validation is allowed only on access ports.
•![]() You cannot enable LPIP validation on trunk ports or port channels.
You cannot enable LPIP validation on trunk ports or port channels.
•![]() LPIP validation is not allowed on ports that are SPAN destinations.
LPIP validation is not allowed on ports that are SPAN destinations.
•![]() LPIP validation is not allowed on ports that are part of a private VLAN.
LPIP validation is not allowed on ports that are part of a private VLAN.
•![]() LPIP validation does not support IPv6.
LPIP validation does not support IPv6.
•![]() LPIP validation is allowed only for endpoint devices directly connected to the NAD.
LPIP validation is allowed only for endpoint devices directly connected to the NAD.
•![]() You cannot use LPIP validation unless you have a Layer 3 route between the NAD and the endpoint device.
You cannot use LPIP validation unless you have a Layer 3 route between the NAD and the endpoint device.
Configuring NAC
This section includes the following topics:
•![]() Enabling the Default AAA Authenication Method for EAPoUDP
Enabling the Default AAA Authenication Method for EAPoUDP
•![]() Configuring Identity Policies and Identity Profile Entries
Configuring Identity Policies and Identity Profile Entries
•![]() Allowing Clientless Endpoint Devices
Allowing Clientless Endpoint Devices
•![]() Changing the Global EAPoUDP Maximum Retry Value
Changing the Global EAPoUDP Maximum Retry Value
•![]() Changing the EAPoUDP Maximum Retry Value for an Interface
Changing the EAPoUDP Maximum Retry Value for an Interface
•![]() Changing the UDP Port for EAPoUDP
Changing the UDP Port for EAPoUDP
•![]() Configuring Rate Limiting of Simultaneous EAPoUDP Posture Validation Sessions
Configuring Rate Limiting of Simultaneous EAPoUDP Posture Validation Sessions
•![]() Configuring Global Automatic Posture Revalidation
Configuring Global Automatic Posture Revalidation
•![]() Configuring Automatic Posture Revalidation for an Interface
Configuring Automatic Posture Revalidation for an Interface
•![]() Changing the Global EAPoUDP Timers
Changing the Global EAPoUDP Timers
•![]() Changing the EAPoUDP Timers for an Interface
Changing the EAPoUDP Timers for an Interface
•![]() Resetting the EAPoUDP Global Configuration to the Default Values
Resetting the EAPoUDP Global Configuration to the Default Values
•![]() Resetting the EAPoUDP Interface Configuration to the Default Values
Resetting the EAPoUDP Interface Configuration to the Default Values
•![]() Configuring IP Device Tracking
Configuring IP Device Tracking
•![]() Manually Initializing EAPoUDP Sessions
Manually Initializing EAPoUDP Sessions
•![]() Manually Revalidating EAPoUDP Sessions
Manually Revalidating EAPoUDP Sessions

Note ![]() If you are familiar with the Cisco IOS CLI, be aware that the Cisco NX-OS commands for this feature might differ from the Cisco IOS commands that you would use.
If you are familiar with the Cisco IOS CLI, be aware that the Cisco NX-OS commands for this feature might differ from the Cisco IOS commands that you would use.
Process for Configuring NAC
Follow these steps to configure NAC:
Step 1 ![]() Enable EAPoUDP (see the "Enabling EAPoUDP" section).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
Step 2 ![]() Configure the connection to the AAA server (see the "Enabling the Default AAA Authenication Method for EAPoUDP" section).
Configure the connection to the AAA server (see the "Enabling the Default AAA Authenication Method for EAPoUDP" section).
Step 3 ![]() Apply PACLs to the interfaces connected to endpoint devices (see the "Applying PACLs to Interfaces" section).
Apply PACLs to the interfaces connected to endpoint devices (see the "Applying PACLs to Interfaces" section).
Step 4 ![]() Enable NAC on the interfaces connected to the endpoint devices (see the "Enabling NAC on an Interface" section).
Enable NAC on the interfaces connected to the endpoint devices (see the "Enabling NAC on an Interface" section).
You can perform any of the following optional configuration tasks for NAC:
•![]() Configure identity policies and identity profile entries for LPIP posture validation exceptions (see the "Configuring Identity Policies and Identity Profile Entries" section).
Configure identity policies and identity profile entries for LPIP posture validation exceptions (see the "Configuring Identity Policies and Identity Profile Entries" section).
•![]() Allow LPIP posture validation for clientless endpoint devices (see the "Allowing Clientless Endpoint Devices" section).
Allow LPIP posture validation for clientless endpoint devices (see the "Allowing Clientless Endpoint Devices" section).
•![]() Enable logging of EAPoUDP events (see the "Enabling Logging for EAPoUDP" section).
Enable logging of EAPoUDP events (see the "Enabling Logging for EAPoUDP" section).
•![]() Change the global maximum number of retries for EAPoUDP messages (see the "Changing the Global EAPoUDP Maximum Retry Value" section).
Change the global maximum number of retries for EAPoUDP messages (see the "Changing the Global EAPoUDP Maximum Retry Value" section).
•![]() Change the maximum number of retries for EAPoUDP messages (see the "Changing the EAPoUDP Maximum Retry Value for an Interface" section).
Change the maximum number of retries for EAPoUDP messages (see the "Changing the EAPoUDP Maximum Retry Value for an Interface" section).
•![]() Change the UDP port number on the NX-OS device used by EAPoUDP (see the "Changing the UDP Port for EAPoUDP" section).
Change the UDP port number on the NX-OS device used by EAPoUDP (see the "Changing the UDP Port for EAPoUDP" section).
•![]() Configure rate limiting for EAPoUDP for simultaneous posture validation sessions (see the "Configuring Rate Limiting of Simultaneous EAPoUDP Posture Validation Sessions" section).
Configure rate limiting for EAPoUDP for simultaneous posture validation sessions (see the "Configuring Rate Limiting of Simultaneous EAPoUDP Posture Validation Sessions" section).
•![]() Configure global periodic automatic LPIP posture validation for endpoint devices (see the "Configuring Global Automatic Posture Revalidation" section).
Configure global periodic automatic LPIP posture validation for endpoint devices (see the "Configuring Global Automatic Posture Revalidation" section).
•![]() Configure periodic automatic LPIP posture validation for endpoint devices on an interface (see the "Configuring Automatic Posture Revalidation for an Interface" section).
Configure periodic automatic LPIP posture validation for endpoint devices on an interface (see the "Configuring Automatic Posture Revalidation for an Interface" section).
•![]() Change the values of the global EAPoUDP timers used by LPIP posture validation (see the "Changing the Global EAPoUDP Timers" section).
Change the values of the global EAPoUDP timers used by LPIP posture validation (see the "Changing the Global EAPoUDP Timers" section).
•![]() Change the values of the EAPoUDP timers for an interface used by LPIP posture validation (see the "Changing the EAPoUDP Timers for an Interface" section).
Change the values of the EAPoUDP timers for an interface used by LPIP posture validation (see the "Changing the EAPoUDP Timers for an Interface" section).
•![]() Reset the EAPoUDP global configuration to the default values (see the "Resetting the EAPoUDP Global Configuration to the Default Values" section).
Reset the EAPoUDP global configuration to the default values (see the "Resetting the EAPoUDP Global Configuration to the Default Values" section).
•![]() Reset the EAPoUDP configuration on an interface to the default values (see the "Resetting the EAPoUDP Interface Configuration to the Default Values" section).
Reset the EAPoUDP configuration on an interface to the default values (see the "Resetting the EAPoUDP Interface Configuration to the Default Values" section).
•![]() Configure IP device tracking (see the "Configuring IP Device Tracking" section).
Configure IP device tracking (see the "Configuring IP Device Tracking" section).
•![]() Manually initialize some or all EAPoUDP sessions (see the "Manually Initializing EAPoUDP Sessions" section).
Manually initialize some or all EAPoUDP sessions (see the "Manually Initializing EAPoUDP Sessions" section).
•![]() Manually revalidate some or all EAPoUDP sessions (see the "Manually Revalidating EAPoUDP Sessions" section).
Manually revalidate some or all EAPoUDP sessions (see the "Manually Revalidating EAPoUDP Sessions" section).
Enabling EAPoUDP
The NX-OS device relays Extensible Authentication Protocol (EAP) messages between the endpoints and the authentication server. You must enable EAPoUDP before configuring NAC on the NX-OS device.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() feature eou
feature eou
3. ![]() exit
exit
4. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Enabling the Default AAA Authenication Method for EAPoUDP
You must enable the default AAA authentication method EAPoUDP. For more information on AAA authentication methods, see Chapter 2, "Configuring AAA." For information on configuring RADIUS servers, see Chapter 3, "Configuring RADIUS."

Note ![]() LPIP can use only RADIUS for authentication.
LPIP can use only RADIUS for authentication.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
Configure RADIUS or TACACS+ server groups, as needed.
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() aaa authentication eou default group group-list
aaa authentication eou default group group-list
3. ![]() exit
exit
4. ![]() show aaa authentication
show aaa authentication
5. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Applying PACLs to Interfaces
You must apply a PACL to the access interfaces on the NAD that perform LPIP posture validation if no PACL is available from the AAA server.
For more information on PACLs, see Chapter 11, "Configuring MAC ACLs."
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Create a MAC ACL.
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() interface ethernet slot/port
interface ethernet slot/port
3. ![]() mac access-group access-list
mac access-group access-list
4. ![]() exit
exit
5. ![]() show running-config interface
show running-config interface
6. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Enabling NAC on an Interface
You must enable NAC on an interface for posture validation to occur.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() interface ethernet slot/port
interface ethernet slot/port
3. ![]() switchport
switchport
4. ![]() switchport mode access
switchport mode access
5. ![]() nac enable
nac enable
6. ![]() exit
exit
7. ![]() show running-config interface
show running-config interface
8. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Configuring Identity Policies and Identity Profile Entries
You can use the identity profile to configure exceptions to LPIP posture validation. The identity profile contains entries for the endpoint devices for which are not subject to LPIP validation. You can optionally configure an identity policy for each identity profile entry that specifies a PACL that the NX-OS device applies to the endpoint device. The default identity policy is the PACL for the interface.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() identity policy policy-name
identity policy policy-name
3. ![]() object-group access-list
object-group access-list
4. ![]() description "text"
description "text"
5. ![]() exit
exit
6. ![]() show identity policy
show identity policy
7. ![]() identity profile eapoudp
identity profile eapoudp
8. ![]() device {authenticate | not-authenticate} {ip-address ipv4-address [ipv4-subnet-mask] | mac-address mac-address [mac-subnet-mask]} policy name
device {authenticate | not-authenticate} {ip-address ipv4-address [ipv4-subnet-mask] | mac-address mac-address [mac-subnet-mask]} policy name
9. ![]() exit
exit
10. ![]() show identity profile eapoudp
show identity profile eapoudp
11. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Allowing Clientless Endpoint Devices
You can allow posture validation endpoint devices in your network that do not have a posture agent installed (clientless). The posture validation is performed by an audit server that has access to the endpoint devices.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
Verify that the AAA server and clientless endpoint devices can access the audit server.
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() eou allow clientless
eou allow clientless
3. ![]() exit
exit
4. ![]() show eou
show eou
5. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Enabling Logging for EAPoUDP
You can enable logging for EAPoUDP event messages. EAPoUDP events include errors and status changes. The destination for these event messages is the configured syslog.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() eou logging
eou logging
3. ![]() exit
exit
4. ![]() show eou
show eou
5. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Changing the Global EAPoUDP Maximum Retry Value
You can change the global maximum number of EAPoUDP retries. The default value is three.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() eou max-retry count
eou max-retry count
3. ![]() exit
exit
4. ![]() show eou
show eou
5. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Changing the EAPoUDP Maximum Retry Value for an Interface
You can change the maximum number of EAPoUDP retries for an interface. The default value is three.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
Enable NAC on the interface (see the "Enabling NAC on an Interface" section)
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() interface ethernet slot/port
interface ethernet slot/port
3. ![]() eou max-retry count
eou max-retry count
4. ![]() exit
exit
5. ![]() show eou
show eou
6. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Changing the UDP Port for EAPoUDP
You can change the UDP port used by EAPoUDP. The default port is 21862.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() eou port udp-port
eou port udp-port
3. ![]() exit
exit
4. ![]() show eou
show eou
5. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Configuring Rate Limiting of Simultaneous EAPoUDP Posture Validation Sessions
You can configure rate limiting to control the number of simultaneous EAPoUDP posture validations sessions. You can change the rate-limiting value that controls the maximum number of simultaneous EAPoUDP posture validation sessions. The default number is 20. Setting the number to zero (0) disables rate limiting.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() eou ratelimit number-of-sessions
eou ratelimit number-of-sessions
3. ![]() exit
exit
4. ![]() show eou
show eou
5. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Configuring Global Automatic Posture Revalidation
The NX-OS software automatically revalidates the posture of the endpoint devices for the NX-OS device at a configured interval. The default interval is 36,000 seconds (10 hours). You can disable revalidation or change the length of the revalidation interval.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() eou revalidate
eou revalidate
3. ![]() eou timeout revalidation seconds
eou timeout revalidation seconds
4. ![]() exit
exit
5. ![]() show eou
show eou
6. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Configuring Automatic Posture Revalidation for an Interface
The NX-OS software automatically revalidates the posture of the endpoint devices for the NX-OS device at a configured interval. The default interval is 36,000 seconds (10 hours). You can disable revalidation or change the length of the revalidation interval.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
Enable NAC on the interface (see the "Enabling NAC on an Interface" section).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() interface ethernet slot/port
interface ethernet slot/port
3. ![]() eou revalidate
eou revalidate
4. ![]() eou timeout revalidation seconds
eou timeout revalidation seconds
5. ![]() exit
exit
6. ![]() show eou
show eou
7. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Changing the Global EAPoUDP Timers
The NX-OS software supports the following global timers for EAPoUDP:
•![]() AAA—Controls the amount of time that the NAD waits for a response from the AAA server before resending a request during posture validation.
AAA—Controls the amount of time that the NAD waits for a response from the AAA server before resending a request during posture validation.
•![]() Hold period—Prevents a new EAPoUDP session from immediately starting after the previous attempt to validate that the session fails. NAC uses this time only when the Cisco Secure ACS sends an Accept-Reject message to the NAD.
Hold period—Prevents a new EAPoUDP session from immediately starting after the previous attempt to validate that the session fails. NAC uses this time only when the Cisco Secure ACS sends an Accept-Reject message to the NAD.
•![]() Retransmit—Controls the amount of time that the NAD waits for a response from the client before resending a request during posture validation.
Retransmit—Controls the amount of time that the NAD waits for a response from the client before resending a request during posture validation.
•![]() Revalidation—Controls the amount of time that the NAD applies a NAC policy to an endpoint device that used EAPoUDP messages during posture validation. The timer starts after the initial posture validation completes.
Revalidation—Controls the amount of time that the NAD applies a NAC policy to an endpoint device that used EAPoUDP messages during posture validation. The timer starts after the initial posture validation completes.
•![]() Status query—Controls the amount of time that the NAD waits before verifying that the previously validated client is present and that its posture has not changed. Only clients that were authenticated with EAPoUDP messages use this timer, which starts after the client is initially validated.
Status query—Controls the amount of time that the NAD waits before verifying that the previously validated client is present and that its posture has not changed. Only clients that were authenticated with EAPoUDP messages use this timer, which starts after the client is initially validated.
For more information on these timers, see the "NAC Timers" section.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() eou timeout aaa seconds
eou timeout aaa seconds
3. ![]() eou timeout hold-period seconds
eou timeout hold-period seconds
4. ![]() eou timeout retransmit seconds
eou timeout retransmit seconds
5. ![]() eou timeout revalidation seconds
eou timeout revalidation seconds
6. ![]() eou timeout status-query seconds
eou timeout status-query seconds
7. ![]() exit
exit
8. ![]() show eou
show eou
9. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Changing the EAPoUDP Timers for an Interface
The NX-OS software supports the following timers for EAPoUDP for each interface enabled for NAC:
•![]() AAA—Controls the amount of time that the NAD waits for a response from the AAA server before resending a request during posture validation.
AAA—Controls the amount of time that the NAD waits for a response from the AAA server before resending a request during posture validation.
•![]() Hold period—Prevents a new EAPoUDP session from immediately starting after the previous attempt to validate that the session fails. NAC uses this time only when the Cisco Secure ACS sends an Accept-Reject message to the NAD.
Hold period—Prevents a new EAPoUDP session from immediately starting after the previous attempt to validate that the session fails. NAC uses this time only when the Cisco Secure ACS sends an Accept-Reject message to the NAD.
•![]() Retransmit—Controls the amount of time that the NAD waits for a response from the client before resending a request during posture validation.
Retransmit—Controls the amount of time that the NAD waits for a response from the client before resending a request during posture validation.
•![]() Revalidation—Controls the amount of time that the NAD applies a NAC policy to an endpoint device that used EAPoUDP messages during posture validation. The timer starts after the initial posture validation completes.
Revalidation—Controls the amount of time that the NAD applies a NAC policy to an endpoint device that used EAPoUDP messages during posture validation. The timer starts after the initial posture validation completes.
•![]() Status query—Controls the amount of time that the NAD waits before verifying that the previously validated client is present and that its posture has not changed. Only clients that were authenticated with EAPoUDP messages use this timer, which starts after the client is initially validated.
Status query—Controls the amount of time that the NAD waits before verifying that the previously validated client is present and that its posture has not changed. Only clients that were authenticated with EAPoUDP messages use this timer, which starts after the client is initially validated.
For more information on these timers, see the "NAC Timers" section.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
Enable NAC on the interface (see the "Enabling NAC on an Interface" section).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() interface ethernet slot/port
interface ethernet slot/port
3. ![]() eou timeout aaa seconds
eou timeout aaa seconds
4. ![]() eou timeout hold-period seconds
eou timeout hold-period seconds
5. ![]() eou timeout retransmit seconds
eou timeout retransmit seconds
6. ![]() eou timeout revalidation seconds
eou timeout revalidation seconds
7. ![]() eou timeout status-query seconds
eou timeout status-query seconds
8. ![]() exit
exit
9. ![]() show eou
show eou
10. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Resetting the EAPoUDP Global Configuration to the Default Values
You can reset the EAPoUDP global configuration to the default values.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() eou default
eou default
3. ![]() exit
exit
4. ![]() show eou
show eou
5. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Resetting the EAPoUDP Interface Configuration to the Default Values
You can reset the EAPoUDP configuration for an interface to the default values.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
Enabled NAC on the interface (see the "Enabling NAC on an Interface" section).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() interface ethernet slot/port
interface ethernet slot/port
3. ![]() eou default
eou default
4. ![]() exit
exit
5. ![]() show eou
show eou
6. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Configuring IP Device Tracking
You can configure IP device tracking. The process for the IP device tracking for AAA servers operates is as follows:
1. ![]() The NX-OS device detects a new session.
The NX-OS device detects a new session.
2. ![]() Before posture validation is triggered and if the AAA server is unreachable, the NX-OS device applies the IP device tracking policy and maintains the session state as AAA DOWN.
Before posture validation is triggered and if the AAA server is unreachable, the NX-OS device applies the IP device tracking policy and maintains the session state as AAA DOWN.
3. ![]() When the AAA server is once again available, a revalidation occurs for the host.
When the AAA server is once again available, a revalidation occurs for the host.

Note ![]() When the AAA server is down, the NX-OS device applies the IP device tracking policy only if no existing policy is associated with the endpoint device. During revalidation when the AAA server goes down, the NX-OS device retains the policies that are used for the endpoint device.
When the AAA server is down, the NX-OS device applies the IP device tracking policy only if no existing policy is associated with the endpoint device. During revalidation when the AAA server goes down, the NX-OS device retains the policies that are used for the endpoint device.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() ip device tracking enable
ip device tracking enable
3. ![]() ip device tracking probe {count count | interval seconds}
ip device tracking probe {count count | interval seconds}
4. ![]() radius server host {hostname | ip-address} text [username username [password password]] [idle-time minutes]
radius server host {hostname | ip-address} text [username username [password password]] [idle-time minutes]
5. ![]() exit
exit
6. ![]() show ip device tracking all
show ip device tracking all
7. ![]() show radius-server {hostname | ip-address}
show radius-server {hostname | ip-address}
8. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Clearing IP Device Tracking
You can clear IP device tracking information for AAA servers.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
SUMMARY STEPS
1. ![]() clear ip device tracking all
clear ip device tracking all
2. ![]() clear ip device tracking interface ethernet slot/port
clear ip device tracking interface ethernet slot/port
3. ![]() clear ip device tracking ip-address ipv4-address
clear ip device tracking ip-address ipv4-address
4. ![]() clear ip device tracking mac-address mac-address
clear ip device tracking mac-address mac-address
5. ![]() show ip device tracking all
show ip device tracking all
DETAILED STEPS
Manually Initializing EAPoUDP Sessions
You can manually initialize EAPoUDP sessions.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
SUMMARY STEPS
1. ![]() eou initialize all
eou initialize all
2. ![]() eou initialize authentication {clientless | eap | static}
eou initialize authentication {clientless | eap | static}
3. ![]() eou initialize interface ethernet slot/port
eou initialize interface ethernet slot/port
4. ![]() eou initialize ip-address ipv4-address
eou initialize ip-address ipv4-address
5. ![]() eou initialize mac-address mac-address
eou initialize mac-address mac-address
6. ![]() eou initialize posturetoken name
eou initialize posturetoken name
7. ![]() show eou all
show eou all
DETAILED STEPS
Manually Revalidating EAPoUDP Sessions
You can manually revalidate EAPoUDP sessions.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
SUMMARY STEPS
1. ![]() eou revalidate all
eou revalidate all
2. ![]() eou revalidate authentication {clientless | eap | static}
eou revalidate authentication {clientless | eap | static}
3. ![]() eou revalidate interface ethernet slot/port
eou revalidate interface ethernet slot/port
4. ![]() eou revalidate ip-address ipv4-address
eou revalidate ip-address ipv4-address
5. ![]() eou revalidate mac-address mac-address
eou revalidate mac-address mac-address
6. ![]() eou revalidate posturetoken name
eou revalidate posturetoken name
7. ![]() show eou all
show eou all
DETAILED STEPS
Clearing EAPoUDP Sessions
You can clear EAPoUDP sessions from the NX-OS device.
BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable EAPoUDP (see the "Enabling EAPoUDP" section).
SUMMARY STEPS
1. ![]() clear eou all
clear eou all
2. ![]() clear eou authentication {clientless | eap | static}
clear eou authentication {clientless | eap | static}
3. ![]() clear eou interface ethernet slot/port
clear eou interface ethernet slot/port
4. ![]() clear eou ip-address ipv4-address
clear eou ip-address ipv4-address
5. ![]() clear eou mac-address mac-address
clear eou mac-address mac-address
6. ![]() clear eou posturetoken name
clear eou posturetoken name
7. ![]() show eou all
show eou all
DETAILED STEPS
Disabling the EAPoUDP Feature
You can disable the EAPoUDP feature on the NX-OS device.

BEFORE YOU BEGIN
Ensure that you are in the correct VDC (or use the switchto vdc command).
Enable the 802.1X feature on the NX-OS device (see the "Enabling the 802.1X Feature" section on page 7-10).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() no feature eou
no feature eou
3. ![]() exit
exit
4. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Verifying the NAC Configuration
To display NAC configuration information, perform one of the following tasks:
For detailed information about the fields in the output from this command, see the Cisco Nexus 7000 Series NX-OS Security Command Reference, Release 4.0.
Example NAC Configuration
The following example shows how to configure NAC:
feature eou
aaa authentication eou default group radius
mac access-list macacl-01
10 permit any any 0x100
interface Ethernet8/1
mac access-group macacl-01
Default Settings
Table 8-1 lists the default settings for NAC parameters.
Additional References
For additional information related to implementing NAC, see the following sections:
Related Documents
|
|
|
|---|---|
Licensing |
Cisco Nexus 7000 Series NX-OS Licensing Guide, Release 4.0 |
Command reference |
Cisco Nexus 7000 Series NX-OS Security Command Reference, Release 4.0 |
 Feedback
Feedback