This guide describes how the combination of Easy VPN and Dynamic Multipoint VPN (DMVPN) has been deployed in the Enterprise-Class Teleworker (ECT) solution.
INTRODUCTION
PURPOSE AND SCOPE
• When an existing Easy VPN deployment is based on Cisco IOS® Software and the customer wants to add DMVPN to the same hub. DMVPN configuration can be added to the same hub without impacting the existing Easy VPN setup. If the existing Easy VPN setup has clients based on Cisco IOS Software routers, this setup can be converted into DMVPN spokes if needed.
• When an ECT solution deployment to provide full-scale integrated access to both small office or home office (SOHO) teleworkers and mobile users using the same end-to-end secure solution setup is desired:
– For SOHO users, Easy VPN or DMVPN can run on a home router, providing corporate access to the computers and IP phones connected to the home network.
– For mobile users, the Easy VPN client (software VPN client) installed on a laptop provides the desired connectivity, because that client can work from any location and will integrate well with the same solution.
• Nonsplit tunnel mode, meaning that once a tunnel is up, all traffic flows through the tunnel.
• Split tunnel mode, in which only corporate traffic is routed through the tunnel. In this case, all other traffic is sent directly to the Internet, thereby lightening the load for the VPN headend.
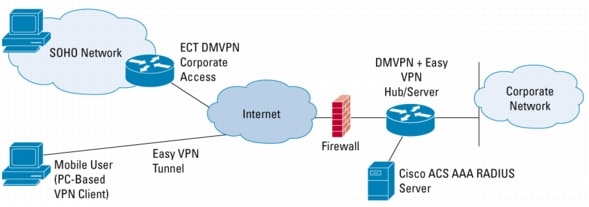
TOPOLOGY
Figure 1. ECT Solution with Integrated Easy VPN Support
CONFIGURATION
• PSKs
• PKI
• Split tunneling and nonsplit tunneling
• Client mode and network extension mode
Easy VPN with Preshared Keys
Server Configuration
Cisco IOS Software Router---Easy VPN Server
aaa group server radius EzVPN
server-private <ACS AAA server ip address> auth-port 1812 acct-port 1813 key <key>
aaa authentication login easyVPN local group EzVPN
aaa authorization network easyVPN local group EzVPN
crypto keyring ezvpn-spokes
!!! This is where the EzVPN PSK is set for the corresponding spokes.
pre-shared-key address 0.0.0.0 0.0.0.0 key <ezvpn-preshared-key>
crypto isakmp policy 10
encr 3des
authentication pre-share
group 2
crypto isakmp xauth timeout 20
crypto isakmp client configuration group easyvpn-group
key <ezvpn-preshared-key>
pool easyvpn-pool
dns 172.16.226.120 172.16.168.183
domain cisco.com
save-password
crypto isakmp profile easyvpn-group
!!! Use the EzVPN pre-shared key provided in the keyring
keyring ezvpn-spokes
match identity group easyvpn-group
!!! Client will need to XAUTH with the AAA
client authentication list easyVPN
isakmp authorization list easyVPN
client configuration address respond
crypto ipsec transform-set ts1 esp-3des esp-sha-hmac
crypto dynamic-map dmap 10
set transform-set ts1
!!! We associate the ezvpn isakmp profile to a dynamic crypto map.
set isakmp-profile easyvpn
!!! Reverse-route is used to allow the ezvpn assigned ip address to be injected into the corporate network. This used when a remote device will be visible from the corporate, which is needed for IP telephony, etc.
reverse-route
crypto map ezvpn-map 1 ipsec-isakmp dynamic dmap
interface GigabitEthernet0/0
ip address 192.169.123.83 255.255.255.240
crypto map ezvpn-map
!!! The client will be assigned one ip address from this pool. If client mode is used, the remote PC/IOS router will NAT all traffic through the EZVPN assigned ip address, other wise the end device will be directly routed to the corporate.
ip local pool easyvpn-pool 192.168.111.2 192.168.111.254
Client Configuration
Software VPN Client---Easy VPN Client (Client Mode)
Cisco IOS Software Router---Easy VPN Client (Network extension Mode)
connect auto
!!! the group name and key must match what is defined in the EzVPN server
group easyvpn-group key <ezvpn-preshared-key>
mode <client | network-extension>
peer 192.169.123.83
!!! these username/password are the ones define on the AAA for XAUTH. It can also be configured with a local user database in the EzVPN server.
username <ezvpn-user> password <ezvpn-password>
interface Ethernet0
description inside/private interface
!!! This is an example of the case where network-extension is used and we want the client to assigned ip addresses of this pool to connected devices.
ip address 10.32.247.65 255.255.255.240
crypto ipsec client ezvpn easyvpn-group inside
interface Ethernet1
description outside/public interface
!!! Use any possible way to connect to the Internet
ip address dhcp
crypto ipsec client ezvpn easyvpn-group
Easy VPN with Public Key Infrastructure
Cisco IOS Certificate Setup
Cisco IOS CS configuration:
crypto pki server ezvpn-certificate-server
database level names
!!! When only generating a few certificates, the router can store the database in flash. This example shows an external tftp server.
database url tftp://172.16.1.10/ezvpn-certificates
issuer-name CN=ezvpn-certificate-server, OU=pki-group, O=Cisco System, L=San Francisco, ST=CA, C=US
!!! Set "grant auto" only if you do not want to manually approve enrollment requests
grant auto
!!! CDP location embedded in certificate. If using CRL checking, routers will pick up CRL from this location. Make sure that your remote routers are able to reach this URL. Otherwise do `revocation-check none' for the remote devices.
cdp-url http://172.16.1.10/ezvpn-certificates/ezvpn-certificate-server.crl
Easy VPN Server and Client Enrollment with Cisco IOS Certificate
• For both server and client routers start by setting up the hostname and an accessible NTP server.
• Generate RSA keys:
The name for the keys will be: ezvpn-certificate-server.cisco.com
% The key modulus size is 1024 bits
% Generating 1024 bit RSA keys ...[OK]
ezvpn-certificate-server (config)#
crypto pki trustpoint ezvpn-certificate-server
enrollment url http://ezvpn-certificate-server:80
serial-number
!!! The OU fied MUST match the EzVPN server group name
subject-name OU=pki-group
!!! Configure CRL checking. Remotes might not need to check the CRL. If not, configure "revocation-check none".
revocation-check crl
• Authenticate the router with the Cisco IOS CS. This will download the CS root certificate so that the router will encrypt the enrollment request with the CS's public key:
• Now enroll with the Cisco IOS CS:
crypto pki enroll ezvpn-certificate-server
• Once the certificate is received, this message will pop up in the console:
• After that save the configuration to make sure the certificate is stored.
Server Configuration
Cisco IOS Software Router---Easy VPN Server
aaa group server radius EzVPN
server-private <acs AAA server ip address> auth-port 1812 acct-port 1813 key <key>
aaa authentication login easyVPN local group EzVPN
aaa authorization network easyVPN local group EzVPN
enrollment url http://ezvpn-certificate-server:80
serial-number
revocation-check crl
crypto pki certificate map map1 10
!!! The certificate map will be used to find a match for the ezvpn profile group.
subject-name co pki-group
crypto pki certificate chain ezvpn-certificate-server
certificate 00BE
certificate ca 01
crypto isakmp policy 20
encr 3des
group 2
crypto isakmp xauth timeout 20
crypto isakmp client configuration group pki-gr oup
dns 172.16.226.120 172.16.168.183
wins 172.16.235.228 172.16.2.87
domain cisco.com
pool easyvpn-pool
save-password
crypto isakmp profile ezvpn-pki
!!! The group name is the OU group field in the pki trustpoint definition
match identity group pki-group
match certificate map1
client authentication list easyVPN
isakmp authorization list easyVPN
client configuration address respond
crypto ipsec transform-set ts1 esp-3des esp-sha-hmac
crypto dynamic-map dmap 20
set transform-set ts1
set isakmp-profile ezvpn-pki
reverse-route
crypto map ezvpn-map 1 ipsec-isakmp dynamic dmap
interface GigabitEthernet0/0
ip address 192.169.123.83 255.255.255.240
crypto map ezvpn-map
ip local pool easyvpn-pool 192.168.111.2 192.168.111.254
Client Configuration
Software VPN Client - Easy VPN Client (Client Mode)
• Get the CS's server root certificate. Go to the CS and export the root certificate using base 64 encoding.
• In the PC where the VPN client is installed, start by opening "Import from File" on the VPN client and select the `Certificates -> Import'. Use the previously saved base 64 encoded certificate.
• Go to the `Certificate -> Enroll' menu option. Enter the CA URL. In the example above it is: http://ezvpn-certificate-server:80. Other fields are optional. Click next to go to the next screen. Enter the CN name; in this example use: ezvpn-certificate-server. Enter the OU (group) field name. This one MUST match the Easy VPN group name defined in the server. In this example the group is the "pki-group" group.
• Click enroll.
• Now add a new connection entry. In the "Authentication" tab select the option "certificate authentication" and pick up the one just created.
• Set the peer to the Easy VPN server's ip address.
Cisco IOS Software Router---Easy VPN Client (Network extension Mode)
enrollment url http://ezvpn-certificate-server:80
serial-number
!!! The OU field MUST be set to the same ezvpn group name.
subject-name OU=pki-group
revocation-check none
crypto pki certificate chain ezvpn-certificate-server
certificate 00BF
certificate ca 01
crypto ipsec client ezvpn easyvpn-group
!!! You don't need to configure the group name here. It is set in the pki trustpoint.
connect auto
mode <client | network-extension>
peer 192.169.123.83
!!! This username/password is the one defined on the AAA for XAUTH. It can also be configured with a local user database in the EzVPN server.
username <ezvpn-user> password <ezvpn-password>
interface Ethernet0
description inside/private interface
ip address 10.32.247.65 255.255.255.240
crypto ipsec client ezvpn easyvpn-group inside
interface Ethernet1
description outside/public interface
ip address dhcp
crypto ipsec client ezvpn easyvpn-group
permit ip 10.0.0.0 0.255.255.255 any
permit ip 192.168.0.0 0.0.255.255 any
permit ip 172.16.0.0 0.31.255.255 any
!!! Add all the corporate internal/public subnets that the client will be able to reach
crypto isakmp client configuration group easyvpn-group
!!! Add the respective access-list to the crypto isakmp client configuration
acl ezvpn_split_tunnel_acl
Easy VPN Client Mode Versus Network Extension Mode
Easy VPN Server Integrated with Dynamic Multipoint VPN Hub Using a Combination of Preshared Keys and Public Key Infrastructure
Full Configuration
service timestamps debug datetime msec localtime show-timezone
service timestamps log datetime msec localtime show-timezone
service password-encryption
!
hostname dmvpn_ezvpn_server
!
boot-start-marker
boot-end-marker
!
logging buffered 100000 debugging
enable secret 5 $1$0FKZ$WDLs7U.zJkav8B.tocviN1
!
clock timezone pst -8
clock summer-time pdt recurring
aaa new-model
!
!
aaa group server radius EzVPN
!!! This is the Cisco ACS (AAA Radius server) for XAUTH authentication for remote ezvpn users.
server-private 192.168.111.106 auth-port 1812 acct-port 1813 key <key>
!
aaa authentication login easyVPN local group EzVPN
aaa authorization network easyVPN local group EzVPN
aaa session-id common
ip subnet-zero
no ip source-route
ip cef
!
!
ip domain name cisco.com
ip host ezvpn-certificate-server.cisco.com 192.168.123.123
!
!
crypto pki trustpoint ezvpn-certificate-server
enrollment url http://ezvpn-certificate-server:80
serial-number
revocation-check crl
!
crypto pki certificate map map1 10
!!! The certificate map will be used to find a match for the ezvpn profile group.
subject-name co pki-group
!
crypto pki certificate chain ezvpn-certificate-server
certificate 00BE
certificate ca 01
!
!
crypto keyring ezvpn-spokes
!!! This if for ezvpn clients that use pre-shared keys
pre-shared-key address 0.0.0.0 0.0.0.0 key <key>
!
crypto isakmp policy 10
encr 3des
group 2
!
crypto isakmp policy 20
encr 3des
authentication pre-share
group 2
crypto isakmp keepalive 30 5
crypto isakmp xauth timeout 10
!
crypto isakmp client configuration group pki-group
dns 172.16.226.120 172.16.168.183
wins 172.16.235.228 172.16.2.87
domain cisco.com
pool easyvpn-pool
save-password
!!! Only add this line only if split-tunnel is wanted
acl ezvpn_split_tunnel_acl
!
crypto isakmp client configuration group easyvpn-group
key <ezvpn-preshare-key>
dns 172.16.226.120 172.16.168.183
wins 172.16.235.228 172.16.2.87
domain cisco.com
pool easyvpn-pool
save-password
!!! Only add this line only if split-tunnel is wanted
acl ezvpn_split_tunnel_acl
crypto isakmp profile easyvpn-group
description PSK group
keyring ezvpn-spokes
match identity group easyvpn-group
client authentication list easyVPN
isakmp authorization list easyVPN
client configuration address respond
crypto isakmp profile ezvpn-pki
description PKI group
match identity group pki-group
match certificate map1
client authentication list easyVPN
isakmp authorization list easyVPN
client configuration address respond
!
!
crypto ipsec transform-set ts1 esp-3des esp-sha-hmac
crypto ipsec transform-set ts2 esp-3des esp-sha-hmac
mode transport require
!
!!! This is for DMVPN
crypto ipsec profile dmvpn-profile
set transform-set ts2
!
!
crypto dynamic-map dmap 10
set transform-set ts1
set isakmp-profile ezvpn-pki
reverse-route
crypto dynamic-map dmap 20
set transform-set ts1
set isakmp-profile easyvpn-group
reverse-route
!
!
!!! This is the dynamic crypto map for the EzVPN server
crypto map ezvpn-map 1 ipsec-isakmp dynamic dmap
!
!
!!! This is the DMVPN mGRE interface
interface Tunnel200
description DMVPN - EIGRP network
bandwidth 2000
ip address 192.168.222.4 255.255.255.0
no ip redirects
ip mtu 1400
no ip next-hop-self eigrp 7
ip pim nbma-mode
ip pim sparse-dense-mode
ip multicast rate-limit out 768
ip nhrp map multicast dynamic
ip nhrp network-id 3686232
ip nhrp holdtime 600
ip nhrp server-only
ip tcp adjust-mss 1360
no ip split-horizon eigrp 7
no ip mroute-cache
delay 1500
tunnel source GigabitEthernet0/0
tunnel mode gre multipoint
tunnel key 123456
tunnel protection ipsec profile dmvpn-profile
!
!
interface GigabitEthernet0/0
!!! Here can go the public ip address of the Head end
ip address 192.169.123.83 255.255.255.240
ip pim sparse-dense-mode
duplex auto
crypto map ezvpn-map
!
router eigrp 7
network 192.168.222.0 0.0.0.255
network 192.169.123.83 0.0.0.15
distribute-list split_out in Tunnel200
no auto-summary
no eigrp log-neighbor-changes
!
ip local pool easyvpn-pool 192.168.111.2 192.168.111.254
ip classless
ip route 0.0.0.0 0.0.0.0 192.169.123.1
!
!
no ip http server
no ip http secure-server
ip pim bidir-enable
ip pim ssm range multicast_ssm_range
!
ip access-list standard split_out
!!! List all the subnets allowed for DMVPN spokes
permit 10.199.224.0 0.0.0.255
permit 10.199.225.0 0.0.0.255
!
ip access-list extended ezvpn_split_tunnel
!!! This is the split-tunnel access list, which should contain all the corporate subnets that the
zvpn client spoke is allowed to connect to
permit ip 10.0.0.0 0.255.255.255 any
permit ip 172.16.0.0 0.15.255.255 any
permit ip 192.168.0.0 0.0.255.255 any
!
route-map split_out permit 10
match ip address static split_out
!
!
line con 0
transport output all
stopbits 1
line aux 0
transport output all
stopbits 1
line vty 0 4
exec-timeout 120 0
!
scheduler allocate 20000 1000
ntp clock-period 17179531
ntp server 192.5.41.40
ntp server 192.5.41.41
!
end
dmvpn_ezvpn_server#
VERIFYING THE EASY VPN SETUP
Cisco IOS VPN Client side
Easy VPN Remote Phase: 4
Tunnel name : easyvpn-group
Inside interface list: Ethernet0,
Outside interface: Ethernet1
Current State: CONNECT_REQUIRED
Last Event: TUNNEL_HAS_PUBLIC_IP_ADD
Save Password: Disallowed
Current EzVPN Peer: 192.169.123.83
Easy VPN Remote Phase: 4
Tunnel name : easyvpn-group
Inside interface list: Ethernet0,
Outside interface: Ethernet1
Current State: XAUTH_REQ
Last Event: XAUTH_REQUEST
Save Password: Disallowed
Current EzVPN Peer: 192.169.123.83
username:<enter AAA username>
password:<enter AAA password>
ezvpn-client#show crypto ipsec ezvpn client
Easy VPN Remote Phase: 4
Tunnel name : easyvpn-group
Inside interface list: Ethernet0,
Outside interface: Ethernet1
Current State: IPSEC_ACTIVE
Last Event: SOCKET_UP
Address: 192.168.111.20
Mask: 255.255.255.255
DNS Primary: 172.16.226.120
DNS Secondary: 172.16.168.183
NBMS/WINS Primary: 172.16.235.228
NBMS/WINS Secondary: 172.16.2.87
Default Domain: cisco.com
Save Password: Allowed
Current EzVPN Peer: 192.169.123.83
Cisco IOS Router VPN Server side
ISAKMP PROFILE easyvpn-group
Identities matched are:
group easyvpn-group
Certificate maps matched are:
keyring(s): ezvpn-spokes
!!! If you have multiple trustpoint configured in your server, you might want to restrict the ones that can connect using EzVPN using a "ca trust-point <trustpoint-name>" in the crypto isakmp profile <name>
trustpoint(s): <all>
ISAKMP PROFILE ezvpn-pki (PKI group)
Identities matched are:
group pki-group
Certificate maps matched are:
map1
keyring(s): <none>
trustpoint(s): <all>
Peer: 192.168.33.21 Port: 1024 Local: 192.169.123.83
Phase1 id: easyvpn-group
Peer: 192.168.22.33 Port: 4500 Local: 192.169.123.83
!!! This example shows one client coming from a PC based VPN client using PSK and another one connecting from a router using PKI
Phase1 id: cn= ezvpn-certificate-server,ou=pki-group,hostname=ezvpn-client.cisco.com
Crypto Map "ezvpn-map" 65536 ipsec-isakmp
Peer = 192.168.22.33
!!! This is the ezvpn group name for the PKI clients
ISAKMP Profile: pki-group
Extended IP access list
access-list permit ip any host 192.168.111.20
dynamic (created from dynamic map dmap/2)
Current peer: 192.168.22.33
Security association lifetime: 4608000 kilobytes/3600 seconds
PFS (Y/N): N
Transform sets={
t1,
}
!!! Note the reverse route injection that will allow the ezvpn assigned ip address to be injected into the corporate network
Reverse Route Injection Enabled
Interfaces using crypto map test:
GigabitEthernet0/0
TROUBLESHOOTING
• debug crypto isakmp---Displays errors during Phase 1.
• debug crypto ipsec---Displays errors during Phase 2.
• debug crypto engine---Displays information from the crypto engine.
• debug crypto ipsec client ezvpn---displays Easy VPN client related debugs
• clear crypto isakmp---Clears the Phase 1 security associations.
• clear crypto sa---Clears the Phase 2 security associations.
• clear crypto ipsec client ezvpn---Clears the Easy VPN client connection.
REFERENCES
Links for Additional Information
• VPN Client User Guide for Windows, Release 4.0
