-
- IP Access List Features Roadmap
- IP Access List Overview
- Creating an IP Access List and Applying It to an Interface
- Creating an IP Access List to Filter IP Options TCP Flags Noncontiguous Ports or TTL Values
- Refining an IP Access List
- Displaying and Clearing IP Access List Data Using ACL Manageability
- Controlling Access to a Virtual Terminal Line
- Access List-Based RBSCP
- ACL IP Options Selective Drop
- ACL Authentication of Incoming rsh and rcp Requests
- Configuring Lock-and-Key Security for Dynamic Access Lists
- Configuring IP Session Filtering of Reflexive Access Lists
- Configuring TCP Intercept and Preventing Denial-of-Service Attacks
-
- Configuring Context-based Access Control
- Application Firewall - Instant Message Traffic Enforcement
- Cisco IOS Firewall MIB
- Cisco IOS Firewall Performance Improvements
- Cisco IOS Firewall Stateful Failover
- Cisco IOS Firewall Support for TRP
- Email Inspection Engine
- ESMTP Support for Cisco IOS Firewall
- Firewall ACL Bypass
- Firewall N2H2 Support
- Firewall Stateful Inspection of ICMP
- Firewall Support for SIP
- Firewall Support of Skinny Client Control Protocol
- Firewall Websense URL Filtering
- Granular Protocol Inspection
- HTTP Inspection Engine
- Inspection of Router-Generated Traffic
- TCP Out-of-Order Packet Support for Cisco IOS Firewall and Cisco IOS IPS
- Transparent Cisco IOS Firewall
- Virtual Fragmentation Reassembly
- VRF Aware Cisco IOS Firewall
- Configuring Port to Application Mapping
- Configuring Cisco IOS Intrusion Prevention System (IPS)
- Configuring IP Security Options
Cisco IOS Security Configuration Guide: Securing the Data Plane, Release 12.4
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- May 5, 2008
Chapter: IP Access List Overview
- Finding Feature Information
- Contents
- Information About IP Access Lists
- Benefits of IP Access Lists
- Border Routers and Firewall Routers Should Use Access Lists
- Definition of an Access List
- Software Processing of an Access List
- Access List Rules
- Helpful Hints for Creating IP Access Lists
- Named or Numbered Access Lists
- Standard or Extended Access Lists
- IP Packet Fields You Can Filter to Control Access
- Wildcard Mask for Addresses in an Access List
- Access List Sequence Numbers
- Access List Logging
- Additional IP Access List Features
- Time-Based and Distributed Time-Based Access Lists
- Types of IP Access Lists
- Where to Apply an Access List
- Where to Go Next
- Additional References
- Feature Information for IP Access List Overview
IP Access List Overview
Access control lists (ACLs) perform packet filtering to control which packets move through the network and where. Such control provides security by helping to limit network traffic, restrict the access of users and devices to the network, and prevent traffic from leaving a network. IP access lists can reduce the chance of spoofing and denial-of-service attacks and allow dynamic, temporary user access through a firewall.
IP access lists can also be used for purposes other than security, such as bandwidth control, restricting the content of routing updates, redistributing routes, triggering dial-on-demand (DDR) calls, limiting debug output, and identifying or classifying traffic for quality of service (QoS) features. This module provides an overview of IP access lists.
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the "Feature Information for IP Access List Overview" section.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Contents
•![]() Information About IP Access Lists
Information About IP Access Lists
•![]() Feature Information for IP Access List Overview
Feature Information for IP Access List Overview
Information About IP Access Lists
•![]() Border Routers and Firewall Routers Should Use Access Lists
Border Routers and Firewall Routers Should Use Access Lists
•![]() Software Processing of an Access List
Software Processing of an Access List
•![]() Helpful Hints for Creating IP Access Lists
Helpful Hints for Creating IP Access Lists
•![]() Named or Numbered Access Lists
Named or Numbered Access Lists
•![]() Standard or Extended Access Lists
Standard or Extended Access Lists
•![]() IP Packet Fields You Can Filter to Control Access
IP Packet Fields You Can Filter to Control Access
•![]() Wildcard Mask for Addresses in an Access List
Wildcard Mask for Addresses in an Access List
•![]() Additional IP Access List Features
Additional IP Access List Features
•![]() Time-Based and Distributed Time-Based Access Lists
Time-Based and Distributed Time-Based Access Lists
•![]() Where to Apply an Access List
Where to Apply an Access List
Benefits of IP Access Lists
Access control lists (ACLs) perform packet filtering to control which packets move through the network and where. Such control can restrict the access of users and devices to the network, providing a measure of security. Access lists can save network resources by reducing traffic. Access lists provide diverse benefits, depending on how they are used. Many of the benefits fall into the following categories:
Block Unwanted Traffic or Users
Access lists can filter incoming or outgoing packets on an interface, thereby controlling access based on source addresses, destination addresses, or user authentication. You can also use access lists to determine which types of traffic are forwarded or blocked at the router interfaces. For example, you can permit e-mail traffic to be routed, but at the same time block all Telnet traffic.
Reduce the Chance of DOS Attacks
There are a number of ways to reduce the chance of denial-of-service attacks. For example, by specifying IP source addresses, you can control whether traffic from hosts, networks, or users access your network. You can filter on specific time-to-live (TTL) values in packets to control how many hops a packet can take before reaching a router in your network. By configuring the TCP Intercept feature, you can prevent servers from being flooded with requests for a connection.
Control Access to Virtual Terminal Lines
You can place an access list on inbound vty (Telnet) line access from certain nodes or networks. You can also place an access list on outbound vty access, blocking or permitting Telnet access to other devices.
Restrict the Content of Routing Updates
Access lists can control routing updates being sent, received, or redistributed.
Provide Bandwidth Control
An access list on a slow link can prevent excess traffic.
Identify or Classify Traffic for QoS Features
Access lists can provide congestion avoidance by setting IP precedence for WRED or CAR. It can provide congestion management for class-based weighted fair queuing (WFQ), priority queuing, and custom queuing.
Trigger Dial-on-Demand (DDR) Calls
An access list can enforce dialing and disconnect criteria.
Limit Debug Command Output
An access list can limit debug output based on an address or protocol.
Provide NAT Control
Access lists can control which addresses are translated by Network Address Translation (NAT).
Authenticate Incoming RSH and RCP Requests
To enable the Cisco IOS software to receive incoming remote shell (rsh) protocol and remote copy (rcp) protocol requests, customers must configure an authentication database to control access to the router. Access lists can simplify the identification of local users, remote hosts, and remote users in the database authentication configuration.
Border Routers and Firewall Routers Should Use Access Lists
There are many reasons to configure access lists; for example, you can use access lists to restrict contents of routing updates or to provide traffic flow control. One of the most important reasons to configure access lists is to provide a basic level of security for your network by controlling access to it. If you do not configure access lists on your router, all packets passing through the router could be allowed onto all parts of your network.
An access list can allow one host to access a part of your network and prevent another host from accessing the same area. In Figure 1, by applying an appropriate access list to the interfaces of the router, Host A is allowed to access the Human Resources network and Host B is prevented from accessing the Human Resources network.
Figure 1 Traffic Filters to Prevent Traffic from Being Routed to a Network
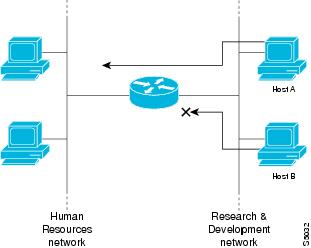
Access lists should be used in firewall routers, which are often positioned between your internal network and an external network such as the Internet. You can also use access lists on a router positioned between two parts of your network, to control traffic entering or exiting a specific part of your internal network.
To provide some security benefits of access lists, you should at least configure access lists on border routers—routers located at the edges of your networks. Such an access list provides a basic buffer from the outside network or from a less controlled area of your own network into a more sensitive area of your network. On these border routers, you should configure access lists for each network protocol configured on the router interfaces. You can configure access lists so that inbound traffic or outbound traffic or both are filtered on an interface.
Access lists are defined on a per-protocol basis. In other words, you should define access lists for every protocol enabled on an interface if you want to control traffic flow for that protocol.
Definition of an Access List
An access list is a sequential list consisting of at least one permit statement and possibly one or more deny statements. In the case of IP access lists, the statements can apply to IP addresses, upper-layer IP protocols, or other fields in IP packets. The access list is identified and referenced by a name or a number. The access list acts as a packet filter, filtering packets based on the criteria defined in the access list.
An access list may be configured, but it does not take effect until the access list is either applied to an interface (with the ip access-group command), a virtual terminal line (vty) (with the access-class command), or referenced by some other command that accepts an access list. Access lists have many uses, and therefore many Cisco IOS software commands accept a reference to an access list in their command syntax. Multiple commands can reference the same access list.
In the following configuration excerpt, the first three lines are an example of an IP access list named branchoffices, which is applied to serial interface 0 on incoming packets. No sources other than those on the networks specified by each source address and mask pair can access this interface. The destinations for packets coming from sources on network 172.20.7.0 are unrestricted. The destination for packets coming from sources on network 172.29.2.0 must be 172.25.5.4.
ip access-list extended branchoffices
10 permit 172.20.7.0 0.0.0.3 any
20 permit 172.29.2.0 0.0.0.255 host 172.25.5.4
!
interface serial 0
ip access-group branchoffices in
Software Processing of an Access List
The following general steps describe how the Cisco IOS software processes an access list when it is applied to an interface, a vty, or referenced by some other Cisco IOS command. These steps apply to an access list that has 13 or fewer access list entries.
•![]() The software receives an IP packet and tests parts of each packet being filtered against the conditions in the access list, one condition (permit or deny statement) at a time. For example, the software tests the source and destination addresses of the packet against the source and destination addresses in a permit or deny statement.
The software receives an IP packet and tests parts of each packet being filtered against the conditions in the access list, one condition (permit or deny statement) at a time. For example, the software tests the source and destination addresses of the packet against the source and destination addresses in a permit or deny statement.
•![]() If a packet does not match an access list statement, the packet is then tested against the next statement in the list.
If a packet does not match an access list statement, the packet is then tested against the next statement in the list.
•![]() If a packet and an access list statement match, the rest of the statements in the list are skipped and the packet is permitted or denied as specified in the matched statement. The first entry that the packet matches determines whether the software permits or denies the packet. That is, after the first match, no subsequent entries are considered.
If a packet and an access list statement match, the rest of the statements in the list are skipped and the packet is permitted or denied as specified in the matched statement. The first entry that the packet matches determines whether the software permits or denies the packet. That is, after the first match, no subsequent entries are considered.
•![]() If the access list denies a packet, the software discards the packet and returns an ICMP Host Unreachable message.
If the access list denies a packet, the software discards the packet and returns an ICMP Host Unreachable message.
•![]() If no conditions match, the software drops the packet. This is because each access list ends with an unwritten, implicit deny statement. That is, if the packet has not been permitted by the time it was tested against each statement, it is denied.
If no conditions match, the software drops the packet. This is because each access list ends with an unwritten, implicit deny statement. That is, if the packet has not been permitted by the time it was tested against each statement, it is denied.
In later Cisco IOS releases such as Release 12.4, 12.2S, and 12.0S, by default, an access list that has more than 13 access list entries is processed differently from one that has 13 or fewer entries. In order to be more efficient, an access list with more than 13 entries is processed using a trie-based lookup algorithm. This process will happen automatically; it does not need to be configured.
Access List Rules
Keep the following rules and characteristics of access lists in mind when creating one:
•![]() Only one access list per interface, per protocol, per direction is allowed.
Only one access list per interface, per protocol, per direction is allowed.
•![]() The access list must contain at least one permit statement or else all packets are denied.
The access list must contain at least one permit statement or else all packets are denied.
•![]() Because the software stops testing conditions after the first match, the order of the conditions is critical. The same permit or deny statements specified in a different order could result in a packet being passed under one circumstance and denied in another circumstance.
Because the software stops testing conditions after the first match, the order of the conditions is critical. The same permit or deny statements specified in a different order could result in a packet being passed under one circumstance and denied in another circumstance.
•![]() If an access list is referenced by name in a command, but the access list does not exist, all packets pass. That is, an interface or command with an empty access list applied to it permits all traffic.
If an access list is referenced by name in a command, but the access list does not exist, all packets pass. That is, an interface or command with an empty access list applied to it permits all traffic.
•![]() Standard access lists and extended access lists cannot have the same name.
Standard access lists and extended access lists cannot have the same name.
•![]() Inbound access lists process packets arriving at the router. Incoming packets are processed before being routed to an outbound interface. An inbound access list is efficient because it saves the overhead of routing lookups if the packet is to be discarded because it is denied by the filtering tests. If the packet is permitted by the tests, it is then processed for routing. For inbound lists, permit means continue to process the packet after receiving it on an inbound interface; deny means discard the packet.
Inbound access lists process packets arriving at the router. Incoming packets are processed before being routed to an outbound interface. An inbound access list is efficient because it saves the overhead of routing lookups if the packet is to be discarded because it is denied by the filtering tests. If the packet is permitted by the tests, it is then processed for routing. For inbound lists, permit means continue to process the packet after receiving it on an inbound interface; deny means discard the packet.
•![]() Outbound access lists process packets before they leave the router. Incoming packets are routed to the outbound interface and then processed through the outbound access list. For outbound lists, permit means send it to the output buffer; deny means discard the packet.
Outbound access lists process packets before they leave the router. Incoming packets are routed to the outbound interface and then processed through the outbound access list. For outbound lists, permit means send it to the output buffer; deny means discard the packet.
•![]() An access list can control traffic arriving at the router or leaving the router, but not traffic originating at the router.
An access list can control traffic arriving at the router or leaving the router, but not traffic originating at the router.
Helpful Hints for Creating IP Access Lists
The following tips will help you avoid unintended consequences and help you create more efficient, useful access lists.
•![]() Create the access list before applying it to an interface (or elsewhere), because if you apply a nonexistent access list to an interface and then proceed to configure the access list, the first statement is put into effect, and the implicit deny statement that follows could cause you immediate access problems.
Create the access list before applying it to an interface (or elsewhere), because if you apply a nonexistent access list to an interface and then proceed to configure the access list, the first statement is put into effect, and the implicit deny statement that follows could cause you immediate access problems.
•![]() Another reason to configure an access list before applying it is because an interface with an empty access list applied to it permits all traffic.
Another reason to configure an access list before applying it is because an interface with an empty access list applied to it permits all traffic.
•![]() All access lists need at least one permit statement; otherwise, all packets are denied and no traffic passes.
All access lists need at least one permit statement; otherwise, all packets are denied and no traffic passes.
•![]() Because the software stops testing conditions after it encounters the first match (to either a permit or deny statement), you will reduce processing time and resources if you put the statements that packets are most likely to match at the beginning of the access list. Place more frequently occurring conditions before less frequent conditions.
Because the software stops testing conditions after it encounters the first match (to either a permit or deny statement), you will reduce processing time and resources if you put the statements that packets are most likely to match at the beginning of the access list. Place more frequently occurring conditions before less frequent conditions.
•![]() Organize your access list so that more specific references in a network or subnet appear before more general ones.
Organize your access list so that more specific references in a network or subnet appear before more general ones.
•![]() Use the statement permit any any if you want to allow all other packets not already denied. Using the statement permit any any in effect avoids denying all other packets with the implicit deny statement at the end of an access list. Do not make your first access list entry permit any any because all traffic will get through; no packets will reach the subsequent testing. In fact, once you specify permit any any, all traffic not already denied will get through.
Use the statement permit any any if you want to allow all other packets not already denied. Using the statement permit any any in effect avoids denying all other packets with the implicit deny statement at the end of an access list. Do not make your first access list entry permit any any because all traffic will get through; no packets will reach the subsequent testing. In fact, once you specify permit any any, all traffic not already denied will get through.
•![]() Although all access lists end with an implicit deny statement, we recommend use of an explicit deny statement (for example, deny ip any any). On most platforms, you can display the count of packets denied by issuing the show access-list command, thus finding out more information about who your access list is disallowing. Only packets denied by explicit deny statements are counted, which is why the explicit deny statement will yield more complete data for you.
Although all access lists end with an implicit deny statement, we recommend use of an explicit deny statement (for example, deny ip any any). On most platforms, you can display the count of packets denied by issuing the show access-list command, thus finding out more information about who your access list is disallowing. Only packets denied by explicit deny statements are counted, which is why the explicit deny statement will yield more complete data for you.
•![]() While you are creating an access list or after it is created, you might want to delete an entry.
While you are creating an access list or after it is created, you might want to delete an entry.
–![]() You cannot delete an entry from a numbered access list; trying to do so will delete the entire access list. If you need to delete an entry, you need to delete the entire access list and start over.
You cannot delete an entry from a numbered access list; trying to do so will delete the entire access list. If you need to delete an entry, you need to delete the entire access list and start over.
–![]() You can delete an entry from a named access list. Use the no permit or no deny command to delete the appropriate entry.
You can delete an entry from a named access list. Use the no permit or no deny command to delete the appropriate entry.
•![]() In order to make the purpose of individual statements more scannable and easily understood at a glance, you can write a helpful remark before or after any statement by using the remark command.
In order to make the purpose of individual statements more scannable and easily understood at a glance, you can write a helpful remark before or after any statement by using the remark command.
•![]() If you want to deny access to a particular host or network and find out if someone from that network or host is attempting to gain access, include the log keyword with the corresponding deny statement so that the packets denied from that source are logged for you.
If you want to deny access to a particular host or network and find out if someone from that network or host is attempting to gain access, include the log keyword with the corresponding deny statement so that the packets denied from that source are logged for you.
•![]() This hint applies to the placement of your access list. When trying to save resources, remember that an inbound access list applies the filter conditions before the routing table lookup. An outbound access list applies the filter conditions after the routing table lookup.
This hint applies to the placement of your access list. When trying to save resources, remember that an inbound access list applies the filter conditions before the routing table lookup. An outbound access list applies the filter conditions after the routing table lookup.
Named or Numbered Access Lists
All access lists must be identified by a name or a number. Named and numbered access lists have different command syntax. Named access lists are compatible with Cisco IOS Release 11.2 and later. Named access lists are more convenient than numbered access lists because you can specify a meaningful name that is easier to remember and associate with a purpose. You may reorder statements in or add statements to a named access list.
Named access list are newer than numbered access lists and support the following features that are not supported in numbered access lists:
•![]() TCP flag filtering
TCP flag filtering
•![]() IP option filtering
IP option filtering
•![]() noncontiguous ports
noncontiguous ports
•![]() reflexive access lists
reflexive access lists
•![]() ability to delete entries with the no permit or no deny command
ability to delete entries with the no permit or no deny command
Not all commands that accept a numbered access list will accept a named access list. For example, virtual terminal lines use only numbered access lists.
Standard or Extended Access Lists
All access lists are either standard or extended access lists. If you only intend to filter on a source address, the simpler standard access list is sufficient. For filtering on anything other than a source address, an extended access list is necessary.
•![]() Named access lists are specified as standard or extended based on the keyword standard or extended in the ip access-list command syntax.
Named access lists are specified as standard or extended based on the keyword standard or extended in the ip access-list command syntax.
•![]() Numbered access lists are specified as standard or extended based on their number in the access-list command syntax. Standard IP access lists are numbered 1 to 99 or 1300 to 1999; extended IP access lists are numbered 100 to 199 or 2000 to 2699. The range of standard IP access lists was initially only 1 to 99, and was subsequently expanded with the range 1300 to 1999 (the intervening numbers were assigned to other protocols). The extended access list range was similarly expanded.
Numbered access lists are specified as standard or extended based on their number in the access-list command syntax. Standard IP access lists are numbered 1 to 99 or 1300 to 1999; extended IP access lists are numbered 100 to 199 or 2000 to 2699. The range of standard IP access lists was initially only 1 to 99, and was subsequently expanded with the range 1300 to 1999 (the intervening numbers were assigned to other protocols). The extended access list range was similarly expanded.
Standard Access Lists
Standard IP access lists test only source addresses of packets (except for two exceptions). Because standard access lists test source addresses, they are very efficient at blocking traffic close to a destination. There are two exceptions when the address in a standard access list is not a source address:
•![]() On outbound VTY access lists, when someone is trying to telnet, the address in the access list entry is used as a destination address rather than a source address.
On outbound VTY access lists, when someone is trying to telnet, the address in the access list entry is used as a destination address rather than a source address.
•![]() When filtering routes, you are filtering the network being advertised to you rather than a source address.
When filtering routes, you are filtering the network being advertised to you rather than a source address.
Extended Access Lists
Extended access lists are good for blocking traffic anywhere. Extended access lists test source and destination addresses and other IP packet data, such as protocols, TCP or UDP port numbers, type of service (ToS), precedence, TCP flags, IP options, and TTL value. Extended access lists can also provide capabilities that standard access lists cannot, such as the following:
•![]() Filtering IP Options
Filtering IP Options
•![]() Filtering TCP flags
Filtering TCP flags
•![]() Filtering noninitial fragments of packets (see the module "Refining an IP Access List")
Filtering noninitial fragments of packets (see the module "Refining an IP Access List")
•![]() Time-based entries (see the "Time-Based and Distributed Time-Based Access Lists" section and the module "Refining an IP Access List")
Time-based entries (see the "Time-Based and Distributed Time-Based Access Lists" section and the module "Refining an IP Access List")
•![]() Dynamic access lists (see the section "Types of IP Access Lists" section)
Dynamic access lists (see the section "Types of IP Access Lists" section)
•![]() Reflexive access lists (see the section "Types of IP Access Lists" section and the module "Configuring IP Session Filtering [Reflexive Access Lists])
Reflexive access lists (see the section "Types of IP Access Lists" section and the module "Configuring IP Session Filtering [Reflexive Access Lists])

Note ![]() Packets that are subject to an extended access list will not be autonomous switched.
Packets that are subject to an extended access list will not be autonomous switched.
IP Packet Fields You Can Filter to Control Access
You can use an extended access list to filter on any of the following fields in an IP packet. Source address and destination address are the two most frequently specified fields on which to base an access list:
•![]() Source address—Specifies a source address to control packets coming from certain networking devices or hosts.
Source address—Specifies a source address to control packets coming from certain networking devices or hosts.
•![]() Destination address—Specifies a destination address to control packets being sent to certain networking devices or hosts.
Destination address—Specifies a destination address to control packets being sent to certain networking devices or hosts.
•![]() Protocol—Specifies an IP protocol indicated by the keyword eigrp, gre, icmp, igmp, ip, ipinip, nos, ospf, tcp, or udp, or indicated by an integer in the range from 0 to 255 (representing an Internet protocol). If you specify a transport layer protocol (icmp, igmp, tcp, or udp), the command has a specific syntax.
Protocol—Specifies an IP protocol indicated by the keyword eigrp, gre, icmp, igmp, ip, ipinip, nos, ospf, tcp, or udp, or indicated by an integer in the range from 0 to 255 (representing an Internet protocol). If you specify a transport layer protocol (icmp, igmp, tcp, or udp), the command has a specific syntax.
–![]() Ports and non-contiguous ports—Specifies TCP or UDP ports by a port name or port number. The port numbers can be noncontiguous port numbers. Port numbers can be useful to filter Telnet traffic or HTTP traffic, for example.
Ports and non-contiguous ports—Specifies TCP or UDP ports by a port name or port number. The port numbers can be noncontiguous port numbers. Port numbers can be useful to filter Telnet traffic or HTTP traffic, for example.
–![]() TCP flags—Specifies that packets match any flag or all flags set in TCP packets. Filtering on specific TCP flags can help prevent false synchronization packets.
TCP flags—Specifies that packets match any flag or all flags set in TCP packets. Filtering on specific TCP flags can help prevent false synchronization packets.
•![]() IP options—Specifies IP options; one reason to filter on IP options is to prevent routers from being saturated with spurious packets containing them.
IP options—Specifies IP options; one reason to filter on IP options is to prevent routers from being saturated with spurious packets containing them.
•![]() TTL value—Specifies TTL values indicated by an operator and possibly a range of values. Filtering on TTL value can control who can reach an interface based on how many hops away the source is. Such filtering can also prevent packets from reaching the process level.
TTL value—Specifies TTL values indicated by an operator and possibly a range of values. Filtering on TTL value can control who can reach an interface based on how many hops away the source is. Such filtering can also prevent packets from reaching the process level.
Wildcard Mask for Addresses in an Access List
Address filtering uses wildcard masking to indicate to the software whether to check or ignore corresponding IP address bits when comparing the address bits in an access list entry to a packet being submitted to the access list. By carefully setting wildcard masks, you can specify one or more IP addresses for permit or deny tests.
Wildcard masking for IP address bits uses the number 1 and the number 0 to specify how the software treats the corresponding IP address bits. A wildcard mask is sometimes referred to as an inverted mask because a 1 and 0 mean the opposite of what they mean in a subnet (network) mask.
•![]() A wildcard mask bit 0 means check the corresponding bit value; they must match.
A wildcard mask bit 0 means check the corresponding bit value; they must match.
•![]() A wildcard mask bit 1 means ignore that corresponding bit value; they need not match.
A wildcard mask bit 1 means ignore that corresponding bit value; they need not match.
If you do not supply a wildcard mask with a source or destination address in an access list statement, the software assumes an implicit wildcard mask of 0.0.0.0, meaning all values must match.
Unlike subnet masks, which require contiguous bits indicating network and subnet to be ones, wildcard masks allow noncontiguous bits in the mask.
Table 1 shows examples of IP addresses and masks from an access list, along with the corresponding addresses that are considered a match.
Access List Sequence Numbers
The ability to apply sequence numbers to IP access list entries simplifies access list changes. Prior to the IP Access List Entry Sequence Numbering feature, there was no way to specify the position of an entry within an access list. If you wanted to insert an entry in the middle of an existing list, all of the entries after the desired position had to be removed, then the new entry was added, and then all the removed entries had to be reentered. This method was cumbersome and error prone.
This feature allows users to add sequence numbers to access list entries and resequence them. When you add a new entry, you specify the sequence number so that it is in a desired position in the access list. If necessary, entries currently in the access list can be resequenced to create room to insert the new entry.
Access List Logging
The Cisco IOS software can provide logging messages about packets permitted or denied by a single standard or extended IP access list entry. That is, any packet that matches the entry will cause an informational logging message about the packet to be sent to the console. The level of messages logged to the console is controlled by the logging console global configuration command.
The first packet that triggers the access list entry causes an immediate logging message, and subsequent packets are collected over 5-minute intervals before they are displayed or logged. The logging message includes the access list number, whether the packet was permitted or denied, the source IP address of the packet, and the number of packets from that source permitted or denied in the prior 5-minute interval.
However, you can use the ip access-list log-update command to set the number of packets that, when match an access list (and are permitted or denied), cause the system to generate a log message. You might want to do this to receive log messages more frequently than at 5-minute intervals.

Even if you use the ip access-list log-update command, the 5-minute timer remains in effect, so each cache is emptied at the end of 5 minutes, regardless of the count of messages in each cache. Regardless of when the log message is sent, the cache is flushed and the count reset to 0 for that message the same way it is when a threshold is not specified.

Note ![]() The logging facility might drop some logging message packets if there are too many to be handled or if there is more than one logging message to be handled in 1 second. This behavior prevents the router from crashing due to too many logging packets. Therefore, the logging facility should not be used as a billing tool or an accurate source of the number of matches to an access list.
The logging facility might drop some logging message packets if there are too many to be handled or if there is more than one logging message to be handled in 1 second. This behavior prevents the router from crashing due to too many logging packets. Therefore, the logging facility should not be used as a billing tool or an accurate source of the number of matches to an access list.
Alternative to Access List Logging
Packets matching an entry in an ACL with a log option are process switched. It is not recommended to use the log option on ACLs, but rather use NetFlow export and match on a destination interface of Null0. This is done in the CEF path. The destination interface of Null0 is set for any packet that is dropped by the ACL.
Additional IP Access List Features
Beyond the basic steps to create a standard or extended access list, you can enhance your access lists as mentioned below. Each of these methods is described completely in the module entitled "Refining an Access List."
•![]() You can impose dates and times when permit or deny statements in an extended access list are in effect, making your access list more granular and specific to an absolute or periodic time period.
You can impose dates and times when permit or deny statements in an extended access list are in effect, making your access list more granular and specific to an absolute or periodic time period.
•![]() After you create a named access list, you might want to add entries or change the order of the entries, known as resequencing an access list.
After you create a named access list, you might want to add entries or change the order of the entries, known as resequencing an access list.
•![]() You can achieve finer granularity when filtering packets by filtering on noninitial fragments of packets.
You can achieve finer granularity when filtering packets by filtering on noninitial fragments of packets.
Time-Based and Distributed Time-Based Access Lists
Time-based access lists implement access list entries based on particular times of the day or week. This is an advantage when you don't want access list entries always in effect or in effect as soon as they are applied. Use time-based access lists to make the enforcement of permit or deny conditions granular, based on time and date.
Distributed time-based access lists are those that are supported on line cards for the Cisco 7500 series routers. Packets destined for an interface configured with time-based access lists are distributed switched through the line card.
Types of IP Access Lists
There are several types of access lists that are distinct because of how they are triggered, their temporary nature, or how their behavior differs from an ordinary access list.
Authentication Proxy
Authentication proxy provides dynamic, per-user authentication and authorization, authenticating users against industry standard TACACS+ and RADIUS authentication protocols. Authenticating and authorizing connections by users provides more robust protection against network attacks.
Context-Based Access Control
Context-based access control (CBAC) examines not only network layer and transport layer information, but also the application-layer protocol information (such as FTP information) to learn about the state of TCP and UDP connections. CBAC maintains connection state information for individual connections. This state information is used to make intelligent decisions about whether packets should be permitted or denied, and dynamically creates and deletes temporary openings in the firewall.
Dynamic Access Lists with the Lock-and-Key Feature
Dynamic access lists provide temporary access to designated users who are using Telnet to reach designated hosts through a firewall. Dynamic access lists involve user authentication and authorization.
Reflexive Access Lists
Reflexive access lists provide filtering on upper-layer IP protocol sessions. They contain temporary entries that are automatically created when a new IP session begins. They are nested within extended, named IP access lists that are applied to an interface. Reflexive access lists are typically configured on border routers, which pass traffic between an internal and external network. These are often firewall routers. Reflexive access lists do not end with an implicit deny statement because they are nested within an access list and the subsequent statements need to be examined.
Where to Apply an Access List
If you are applying an access list to an interface, carefully consider whether to specify it as in (inbound) or out (outbound). Applying an access list to an incoming or outgoing interface controls the traffic that will enter or leave the router's interface or process level (in the case of filtering on TTL values).
•![]() When an inbound access list is applied to an interface, after the software receives a packet, the software checks the packet against the access list statements. If the access list permits the packet, the software continues to process the packet. Therefore, filtering on incoming packets can save router resources because filtered packets will not go through the router.
When an inbound access list is applied to an interface, after the software receives a packet, the software checks the packet against the access list statements. If the access list permits the packet, the software continues to process the packet. Therefore, filtering on incoming packets can save router resources because filtered packets will not go through the router.
•![]() Access lists that apply to outbound packets are filtering packets that have already gone through the router. Packets that pass the access list are transmitted (sent) out the interface.
Access lists that apply to outbound packets are filtering packets that have already gone through the router. Packets that pass the access list are transmitted (sent) out the interface.
•![]() The TCP ACL splitting feature of Rate-Based Satellite Control Protocol (RBSCP) is an example of a feature that can be used on an outgoing interface. The access list controls which packets are subject to TCP ACK splitting.
The TCP ACL splitting feature of Rate-Based Satellite Control Protocol (RBSCP) is an example of a feature that can be used on an outgoing interface. The access list controls which packets are subject to TCP ACK splitting.
Access lists can be used in ways other than applying them to interfaces. The following are additional places to apply an access list.
•![]() To restrict incoming and outgoing connections between a particular vty (into a Cisco device) and the network devices at addresses in an access list, apply an access list to a line. See the "Controlling Access to a Virtual Terminal Line" module.
To restrict incoming and outgoing connections between a particular vty (into a Cisco device) and the network devices at addresses in an access list, apply an access list to a line. See the "Controlling Access to a Virtual Terminal Line" module.
•![]() Referencing an access list from a debug command limits the amount of information displayed to only the information permitted by the access list, such as sources, destinations, or protocols, for example.
Referencing an access list from a debug command limits the amount of information displayed to only the information permitted by the access list, such as sources, destinations, or protocols, for example.
•![]() Access lists can be used to control routing updates, to control dial-on-demand routing (DDR), and to control quality of service (QoS) features, for example. See the appropriate configuration chapters for using access lists with these features.
Access lists can be used to control routing updates, to control dial-on-demand routing (DDR), and to control quality of service (QoS) features, for example. See the appropriate configuration chapters for using access lists with these features.
Where to Go Next
You must first decide what you want to restrict, and then select the type of access list that achieves your goal. Next, you will create an access list that permits or denies packets based on values in the fields you specify, and finally, you will apply the access list (which determines its placement).
Assuming you have decided what you want to restrict and what type of access list you need, your next step is to create an access list. Creating an access list based on source address, destination address, or protocol is described in the "Creating an IP Access List and Applying It to an Interface" module. You could create an access list that filters on other fields, as described in "Creating an IP Access List to Filter IP Options, TCP Flags, Noncontiguous Ports, or TTL Values." If you want to control access to a virtual line, see "Controlling Access to a Virtual Terminal Line." If the purpose of your access list is to control routing updates or QoS features, for example, see the appropriate technology chapter.
Additional References
Related Documents
|
|
|
|---|---|
Cisco IOS commands |
|
IP access list commands: complete command syntax, command mode, command history, defaults, usage guidelines, and examples |
|
Filtering on source address, destination address, or protocol |
"Creating an IP Access List and Applying It to an Interface" |
Filtering on IP Options, TCP flags, noncontiguous ports, or TTL |
"Creating an IP Access List to Filter IP Options, TCP Flags, Noncontiguous Ports, or TTL Values" |
Restricting access to a vty line. |
Standards
|
|
|
|---|---|
None |
— |
MIBs
|
|
|
|---|---|
None |
To locate and download MIBs for selected platforms, Cisco IOS releases, and feature sets, use Cisco MIB Locator found at the following URL: |
RFCs
|
|
|
|---|---|
None |
— |
Technical Assistance
Feature Information for IP Access List Overview
Table 2 lists the features in this module and provides links to specific configuration information.
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.

Note ![]() Table 2 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Table 2 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1005R)
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.
© 2006 Cisco Systems, Inc. All rights reserved.
 Feedback
Feedback