-
Intelligent Services Gateway Configuration Guide, Cisco IOS Release 15.1S
-
Overview of ISG
-
Configuring ISG Control Policies
-
Configuring ISG Access for PPP Sessions
-
Configuring ISG Access for IP Subscriber Sessions
-
Configuring MQC Support for IP Sessions
-
Configuring ISG Port-Bundle Host Key
-
Configuring ISG as a RADIUS Proxy
-
Configuring RADIUS-Based Policing
-
Configuring ISG Policies for Automatic Subscriber Logon
-
Configuring DHCP Option 60 and Option 82 with VPN-ID Support for Transparent Automatic Logon
-
Enabling ISG to Interact with External Policy Servers
-
Configuring ISG Subscriber Services
-
ISG Subscriber Aware Ethernet
-
Configuring ISG Network Forwarding Policies
-
Configuring ISG Accounting
-
Configuring ISG Support for Prepaid Billing
-
Configuring ISG Policies for Session Maintenance
-
Redirecting Subscriber Traffic Using ISG Layer 4 Redirect
-
Configuring ISG Policies for Regulating Network Access
-
ISG Support for SAMI Blade
-
Configuring ISG Integration with SCE
-
Service Gateway Interface
-
Troubleshooting ISG with Session Monitoring and Distributed Conditional Debugging
-
Configuring ISG Troubleshooting Enhancements
-
Contents
- Configuring ISG Subscriber Services
- Finding Feature Information
- Restrictions for ISG Subscriber Services
- Information About ISG Subscriber Services
- ISG Services
- Primary Services
- Traffic Classes and Traffic Class Priority
- Traffic Policies
- ISG Features
- Service Groups
- Service Activation Methods
- How to Configure ISG Services on the Router
- Configuring an ISG Service with Per-Session Functionality
- Configuring an ISG Service with a Traffic Policy
- Defining an ISG Traffic Class Map
- Configuring an ISG Service Policy Map with a Traffic Policy
- Configuring the Default Class in an ISG Service Policy Map
- Activating ISG Subscriber Services
- Configuring Automatic Service Activation in a User Profile
- Configuring ISG Control Policies to Activate Services
- Verifying ISG Services
- Configuration Examples for ISG Services
- Example Service for Per-Flow Accounting
- Example Service for Absolute Timeout and Idle Timeout
- Example Service for ISG Policing
- Example Service for Per-Subscriber Firewall
- Example Service for Redirecting Layer 4 Subscriber Traffic
- Example Deactivating a Layer 4 Redirection Service Following Authorization
- Additional References
- Feature Information for ISG Subscriber Services
Configuring ISG Subscriber Services
Intelligent Services Gateway (ISG) is a Cisco IOS software feature set that provides a structured framework in which edge devices can deliver flexible and scalable services to subscribers. ISG defines a service as a collection of policies that can be applied to any subscriber session. This module describes how ISG subscriber services work, how to configure services and traffic classes that may be used to qualify policies defined within a service, and how to activate services.
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the Feature Information Table at the end of this document.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
Restrictions for ISG Subscriber Services
Only one nondefault traffic class may be configured in each service.
When multiple services are active on a given session, class-based actions are executed on a first-match basis only; in other words, once a class is matched, the actions associated with that class will be executed, and no other class will be matched.
Services that are defined on the ISG device cannot be selected externally because they will not be advertised to a portal.
Removing or modifying a feature in the configuration, for example an access control list (ACL), is not supported by active sessions that reference that feature.
Information About ISG Subscriber Services
- ISG Services
- Primary Services
- Traffic Classes and Traffic Class Priority
- Traffic Policies
- ISG Features
- Service Groups
- Service Activation Methods
ISG Services
An ISG service is a collection of policies that may be applied to a subscriber session. ISG services can be applied to any session, regardless of subscriber access media or protocol, and a single service may be applied to multiple sessions. An ISG service is not necessarily associated with a destination zone or a particular uplink interface.
Services can be defined in two ways: in a service policy map that is configured on the ISG device by using the CLI, and in a service profile that is configured on an external device, such as an authentication, authorization, and accounting (AAA) server. Although they are configured differently, service policy maps and service profiles serve the same purpose: they contain a collection of traffic policies and other functionality that can be applied to a subscriber session. Traffic policies determine which functionality will be applied to which session traffic. A service policy map or service profile may also contain a network-forwarding policy, a specific type of traffic policy that determines how session data packets will be forwarded to the network.
Primary Services
When a network-forwarding policy is included in a service profile or service policy map, the service is known as a primary service . Primary services are mutually exclusive and may not be simultaneously active. Upon activation of a new primary service, ISG will deactivate the existing primary service and any other services dependent on the existing primary service through association with a service group.
If a primary service is deactivated, sessions may be left without a network-forwarding policy, that is, with no means to route or forward packets. A policy may be applied to defend against this condition such that a specific service is activated upon deactivation of all others (or all other primary services). This backup service would return network-forwarding policy to the session and allow the subscriber to reach a web portal. However, it should be noted that an IP session will not be automatically terminated when all services are deactivated unless such a policy has been defined and applied.
Traffic Classes and Traffic Class Priority
ISG traffic classes allow for differentiated behavior for different traffic streams to and from a particular subscriber. For traffic to be classified into streams, you must specify an access control list (ACL) that classifies the traffic and specify the direction of the traffic to which the ACL applies (inbound or outbound). Optionally, the priority of the traffic class can also be specified.
Traffic that meets the specifications of a traffic class is said to match the traffic class. Once a match is made, features defined in the traffic policy are executed for that traffic class.
The priority of a traffic class determines which class is used first for a specified match if more than one traffic policy has been activated for a single session. In other words, if a packet matches more than one traffic class, it is classified to the class with the higher priority.
Packets that do not match any of the ACLs are considered to be part of the default traffic class and are processed as if a traffic policy was not applied to the session. A default class exists for every service, and the default action of the default class is to pass traffic. The default class can be configured to drop traffic. Default traffic is accounted for in the main session accounting.
A service can contain one traffic class and one default class.
Traffic classes are assigned unique identifiers that can be tracked with Cisco IOS show commands.
Traffic Policies
Traffic policies define the handling of data packets. A traffic policy contains a traffic class and one or more features. Whereas you can specify the event that will trigger an ISG control policy, the trigger for a traffic policy is implicit--the arrival of a data packet.
The features configured within a traffic policy apply only to the traffic defined by the traffic class. Multiple traffic policies with various features can be applied to a session.
ISG Features
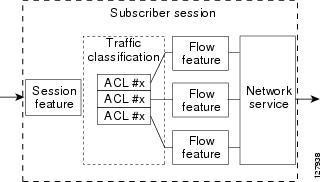
An ISG feature is a functional component that performs a specific operation on a sessionâs data stream. A feature may or may not be associated with a traffic class. However, once associated with a traffic class, a feature can be applied only to the packets that match that traffic class. Otherwise, the feature is applied to all packets for that session.
The figure below shows how features apply to a subscriber session and to traffic flows within the session.
Service Groups
A service group is a grouping of services that may be simultaneously active for a given session. Typically, a service group includes one primary service and one or more secondary services.
Secondary services in a service group are dependent on the primary service and should not be activated unless the primary service is already active. Once a primary service has been activated, any other services that reference the same group may also be activated. Services that belong to other groups, however, may be activated only if they are primary. If a primary service from another service group is activated, all services in the current service group will also be deactivated because they have a dependency on the previous primary service.
Service Activation Methods
There are three methods by which services can be activated:
- Automatic service activation
- Control policy service activation
- Subscriber-initiated service activation
Automatic Service Activation
The Auto Service attribute, which can be configured in user profiles, enables subscribers to be automatically logged in to specified services when the user profile is downloaded, usually following authentication. Features that are specified by the Auto Service attribute in a user profile are referred to as auto services . A user profile can specify more than one service as auto services.
Control Policy Service Activation
ISG control policies can be configured to activate services in response to specific conditions and events.
Subscriber-Initiated Service Activation
Subscriber-initiated service activation takes place when a subscriber manually selects a service at a portal.
When the system receives a subscriber request to activate a service, the ISG policy engine searches for a policy matching the event âservice-startâ. If no such policy is found, the policy engine will by default download the service via the default AAA network authorization method list. This default behavior is identical to the behavior generated by the following policy configuration:
class-map type control match-all SERVICE1_CHECK match service-name SERVICE1 policy-map type control SERVICE1_CHECK event service-start 1 service-policy type service name SERVICE1
The same default behavior applies to subscriber logoffs, with the ISG policy engine searching for a policy that matches the event âservice-stopâ.
If a policy is configured, it is the responsibility of the policy to specify how the service should be applied.
How to Configure ISG Services on the Router
There are two ways to configure an ISG service. One way is to configure a service policy map on the local device by using the CLI. The second way is to configure a service profile on a remote AAA server. To configure a service policy map directly on the ISG, perform the tasks in the following sections:
- Configuring an ISG Service with Per-Session Functionality
- Configuring an ISG Service with a Traffic Policy
- Configuring the Default Class in an ISG Service Policy Map
- Activating ISG Subscriber Services
- Verifying ISG Services
Configuring an ISG Service with Per-Session Functionality
Certain types of functionality that are configured in a service must be applied to the entire subscriber session rather than to a specific traffic flow. Services that are configured with this type of per-session functionality must not contain a traffic class. Perform this task to configure a service policy map without a traffic class on the ISG.
 Note | A service that is configured with per-session functionality and a traffic policy will not work correctly. |
DETAILED STEPS
Configuring an ISG Service with a Traffic Policy
An ISG traffic policy contains a traffic class and one or more ISG features. The traffic class defines the traffic to which the features will be applied. Perform the following tasks to configure an ISG service with a traffic policy on the router:
Defining an ISG Traffic Class Map
Perform this task to configure a traffic class map. A traffic class map usually specifies an access control list (ACL) that classifies the flow and the direction of traffic to which the ACL applies (inbound or outbound).
This task assumes that access control lists (ACLs) have been configured for classifying traffic.
DETAILED STEPS
Configuring an ISG Service Policy Map with a Traffic Policy
ISG services are configured by creating service policy maps on the ISG or service profiles on an external AAA server. Perform this task to configure a traffic policy in a service policy map on the ISG.
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 |
enable
Example: Router> enable |
Enables privileged EXEC mode.
|
| Step 2 |
configure
terminal
Example: Router# configure terminal |
Enters global configuration mode. |
| Step 3 |
policy-map
type
service
policy-map-name
Example: Router(config)# policy-map type service service1 |
Creates or modifies a service policy map, which is used to define an ISG service. |
| Step 4 |
[priority] class type traffic class-map-name Example: Router(config-service-policymap)# class type traffic classb |
Specifies a named traffic class whose policy you want to create or change.
|
| Step 5 |
accounting
aaa
list
AAA-method-list
Example: Router(config-service-policymap-class-traffic)# accounting aaa list mlist1 |
Enables accounting and specifies the AAA method list to which accounting updates will be sent. |
| Step 6 |
police
{input | output} committed-rate normal-burst excess-burst Example: Router(config-service-policymap-class-traffic)# police input 20000 30000 60000 |
Enables ISG policing for upstream or downstream traffic.
|
| Step 7 |
prepaid
config
name-of-configuratio
n Example: Router(config-service-policymap-class-traffic)# prepaid config conf-prepaid |
Enables ISG support for prepaid billing and applies a configuration that defines the prepaid billing parameters. |
| Step 8 |
redirect
[list access-list-number] to {group server-group-name | ip ip-address [port port-number]} [duration seconds] [frequency seconds] Example: Router(config-service-policymap-class-traffic)# redirect to ip 10.10.10.10 |
Redirects traffic to a specified server or server group. |
| Step 9 |
timeout
absolute
duration-in-seconds
Example: Router(config-control-policymap-class-traffic)# timeout absolute 30 |
Specifies the session lifetime, in a range from 30 to 4294967 seconds. |
| Step 10 |
timeout
idle
duration-in-seconds
Example: Router(config-control-policymap-class-traffic)# timeout idle 3000 |
Specifies how long a connection can be idle before it is terminated. The range is platform and release-specific. For more information, use the question mark (?) online help function. |
| Step 11 |
end
Example: Router(config-service-policymap-class-traffic)#end |
(Optional) Returns to privileged EXEC mode. |
Configuring the Default Class in an ISG Service Policy Map
Packets that do not match any traffic classes are considered to be part of default traffic and are processed as if a traffic policy were not applied to the session. A default class exists by default for every service, and the default action of the default class is to pass traffic. Perform this task to configure the default class.
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 |
enable
Example: Router> enable |
Enables privileged EXEC mode.
|
| Step 2 |
configure
terminal
Example: Router# configure terminal |
Enters global configuration mode. |
| Step 3 |
policy-map
type
service
policy-map-name
Example: Router(config)# policy-map type service service1 |
Creates or modifies a service policy map, which is used to define an ISG service. |
| Step 4 |
class
type
traffic
default
{in-out | input | output} Example: Router(config-service-policymap)# class type traffic default in-out |
Associates a default traffic class with a service policy map.
|
| Step 5 |
drop
Example: Router(config-service-policymap-class-traffic)# drop |
Configures the default traffic class to discard packets matching that class. |
Activating ISG Subscriber Services
There are three ways that ISG subscriber services can be activated: by specifying the service as an automatic activation service in a subscriberâs user profile, by configuring control policies to activate the service, and by a subscriber-initiated service logon. No special configuration is necessary to enable a subscriber to log on to a service.
To configure a service for automatic activation and to configure control policies to activate services, perform the following tasks:
- Configuring Automatic Service Activation in a User Profile
- Configuring ISG Control Policies to Activate Services
Configuring Automatic Service Activation in a User Profile
Perform this task to configure automatic service activation for a service in a subscriberâs user profile.
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 |
Add the Auto Service attribute to the user profile. Example: 26,9,251="A service-name[; username ; password]" |
Automatically logs the subscriber in to the specified service when the user profile is downloaded. |
Configuring ISG Control Policies to Activate Services
A control class map must be configured if you specify a named control class map in the control policy map. See the module "Configuring ISG Control Policies" for information about configuring control policies.
DETAILED STEPS
Verifying ISG Services
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 |
enable
Example: Router> enable |
Enables privileged EXEC mode.
|
| Step 2 |
show
class-map
type
traffic
Example: Router# show class-map type traffic |
Displays all traffic class maps and their matching criteria. |
| Step 3 |
show
policy-map
type
service
Example: Router# show policy-map type service |
Displays the contents of all service policy maps. |
Configuration Examples for ISG Services
- Example Service for Per-Flow Accounting
- Example Service for Absolute Timeout and Idle Timeout
- Example Service for ISG Policing
- Example Service for Per-Subscriber Firewall
- Example Service for Redirecting Layer 4 Subscriber Traffic
- Example Deactivating a Layer 4 Redirection Service Following Authorization
Example Service for Per-Flow Accounting
In the following examples, the service âSERVICE1â is configured with per-flow accounting. The access lists âSERVICE1_ACL_INâ and âSERVICE1_ACL_OUTâ are used to define the traffic class. These examples are equivalent and show the two alternative methods of service configuration: in a service policy map that is configured directly on the ISG, and in a service profile that is configured on a AAA server.
ISG Configuration
class-map type traffic match-any SERVICE1_TC match access-group input name SERVICE1_ACL_IN match access-group output name SERVICE1_ACL_OUT ! policy-map type service SERVICE1 10 class type traffic SERVICE1_TC accounting aaa list CAR_ACCNT_LIST class type traffic default in-out drop
AAA Server Configuration
Attributes/ Cisco-AVPair = "ip:traffic-class=in access-group name SERVICE1_ACL_IN priority 10" Cisco-AVPair = "ip:traffic-class=in default drop" Cisco-AVPair = "ip:traffic-class=out access-group name SERVICE1_ACL_OUT priority 10" Cisco-AVPair = "ip:traffic-class=out default drop" Cisco-AVPair = subscriber:accounting-list=CAR_ACCNT_LIST Cisco-SSG-Service-Info = ISERVICE1
Example Service for Absolute Timeout and Idle Timeout
In the following examples, the service âSERVICE1â is configured with per-flow accounting, an absolute timeout, and an idle timeout. The access lists âSERVICE1_ACL_INâ and âSERVICE1_ACL_OUTâ are used to define the traffic class. These examples are equivalent and show the two methods of service configuration: in a service policy map that is configured directly on the ISG, and in a service profile that is configured on a AAA server.
ISG Configuration
class-map type traffic match-any SERVICE1_TC match access-group input name SERVICE1_ACL_IN match access-group output name SERVICE1_ACL_OUT ! policy-map type service SERVICE1 10 class type traffic SERVICE1_TC timeout idle 600 timeout absolute 1800 accounting aaa list CAR_ACCNT_LIST class type traffic default in-out drop
AAA Server Configuration
Attributes/ Cisco-AVPair = "ip:traffic-class=in access-group name SERVICE1_ACL_IN priority 10" Cisco-AVPair = "ip:traffic-class=in default drop" Cisco-AVPair = "ip:traffic-class=out access-group name SERVICE1_ACL_OUT priority 10" Cisco-AVPair = "ip:traffic-class=out default drop" Cisco-AVPair = subscriber:accounting-list=CAR_ACCNT_LIST Cisco-SSG-Service-Info = ISERVICE1 session-timeout = 1800 idle-timeout = 600
Example Service for ISG Policing
In the following examples, the service âBOD1Mâ is configured with per-flow accounting and ISG policing. The access lists âBOD1M_IN_ACL_INâ and âBOD1M_ACL_OUTâ are used to define the traffic class. These examples are equivalent and show the two methods of service configuration: in a service policy map that is configured directly on the ISG, and in a service profile that is configured on a AAA server.
ISG Configuration
class-map type traffic match-any BOD1M_TC match access-group input name BOD1M_IN_ACL_IN match access-group output name BOD1M_ACL_OUT ! policy-map type service BOD1M 10 class type traffic BOD1M_TC accounting aaa list CAR_ACCNT_LIST police input 512000 256000 5000 police output 1024000 512000 5000 class type traffic default in-out drop
AAA Server Configuration
Attributes/ Cisco-AVPair = "ip:traffic-class=in access-group name BOD1M_IN_ACL priority 10" Cisco-AVPair = "ip:traffic-class=in default drop" Cisco-AVPair = "ip:traffic-class=out access-group name BOD1M _OUT_ACL priority 10" Cisco-AVPair = "ip:traffic-class=out default drop" Cisco-AVPair = subscriber:accounting-list=CAR_ACCNT_LIST Cisco-SSG-Service-Info = IBOD1M Cisco-SSG-Service-Info = QU;512000;256000;5000;D;1024000;512000;5000
Example Service for Per-Subscriber Firewall
In the following examples, the service âSERVICE2â is configured with a per-subscriber firewall. The service does not include a traffic class, so it will apply to the entire session. These examples are equivalent and show the two methods of service configuration: in a service policy map that is configured directly on the ISG, and in a service profile that is configured on a AAA server.
Example Service for Redirecting Layer 4 Subscriber Traffic
The following example shows the configuration of a service called âUNAUTHORIZED_REDIRECT_SVCâ. The control policy âUNAUTHEN_REDIRECTâ is configured to apply the service upon session start.
class-map type traffic match-any UNAUTHORIZED_TRAFFIC match access-group input 100 policy-map type service UNAUTHORIZED_REDIRECT_SVC class type traffic UNAUTHORIZED_TRAFFIC redirect to ip 10.0.0.148 port 8080 policy-map type control UNAUTHEN_REDIRECT class type control always event session-start 1 service-policy type service name UNAUTHORIZED_REDIRECT_SVC
Example Deactivating a Layer 4 Redirection Service Following Authorization
In the following example, a service configured with Layer 4 redirection is deactivated when traffic becomes authorized; that is, following activation of the appropriate service.
class-map traffic UNAUTHORIZED_TRAFFIC match access-group input 100 policy-map type service UNAUTHORIZED_REDIRECT_SVC class traffic UNAUTHORIZED_TRAFFIC redirect to ip 10.0.0.148 port 8080 class-map control match-all CHECK_ISP1 match service ISP1 policy-map control UNAUTHEN_REDIRECT class control always event session-start 1 service-policy type service name UNAUTHORIZED_REDIRECT_SVC class control CHECK_ISP1 event service-start 1 service-policy type service unapply UNAUTHORIZED_REDIRECT_SVC 1 service-policy type service name ISP1
Additional References
MIBs
Technical Assistance
|
Description |
Link |
|---|---|
|
The Cisco Support website provides extensive online resources, including documentation and tools for troubleshooting and resolving technical issues with Cisco products and technologies. To receive security and technical information about your products, you can subscribe to various services, such as the Product Alert Tool (accessed from Field Notices), the Cisco Technical Services Newsletter, and Really Simple Syndication (RSS) Feeds. Access to most tools on the Cisco Support website requires a Cisco.com user ID and password. |
Feature Information for ISG Subscriber Services
The following table provides release information about the feature or features described in this module. This table lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
|
Feature Name |
Releases |
Feature Configuration Information |
|---|---|---|
|
ISG: Policy Control: Service Profiles |
12.2(28)SB 12.2(33)SRC 15.0(1)S |
ISG defines a service as a collection of policies that can be applied to any subscriber session. Services can be configured on the router or on an external AAA server. In Cisco IOS Release 12.2(33)SRC, this feature was implemented on the Cisco 7600 router. |
|
ISG: Policy Control: User Profiles |
12.2(28)SB 12.2(33)SRC 15.0(1)S |
ISG user profiles specify services and functionality that can be applied to ISG sessions for the specified subscriber. User profiles are defined on an external AAA server. |
Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1005R)
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.