Configure Customer Instance for the 2000 Agent Deployment Model
Follow this sequence of tasks to create the customer instance to deploy 2000 agent for Cisco HCS for CC for Contact Center.
| Sequence | Task | Done? |
|---|---|---|
| 1 | ||
| 2 | ||
| 3 | ||
| 4 | ||
| 5 | ||
| 6 | ||
| 7 | ||
| 8 | ||
| 9 | ||
| 10 | ||
| 11 |
Upgrade VMware Tools
Procedure
|
Step 1 |
Right-click on the VM. Select . |
||
|
Step 2 |
Wait for the popup window (this may take time) and accept the default Automatic Tools Upgrade. |
||
|
Step 3 |
Click OK. |
||
|
Step 4 |
Restart, only if you are prompted.
|
Set Up Virtual Machine Startup and Shutdown
Procedure
|
Step 1 |
In the VMware vSphere Client window, select ESXi server. |
|
Step 2 |
Click the Configuration tab. |
|
Step 3 |
Click the Virtual Machine Startup/Shutdown link. |
|
Step 4 |
Click Properties. |
|
Step 5 |
In the Virtual Machine Startup and Shutdown dialog box, check the Allow virtual machines to start and stop automatically with the system check box. |
|
Step 6 |
Use the Move Up and Move Down buttons to rearrange the virtual machines under Automatic Startup in the following order:
|
|
Step 7 |
Click OK. |
Create a Domain Controller Server
Create a Virtual Machine for the Domain Controller
Procedure
|
Step 1 |
Create a new virtual machine from vCenter. |
|
Step 2 |
On the Name and Location page, provide a name for the Domain Controller. |
|
Step 3 |
In the Disk format field, choose the Thick Provisioned format. |
|
Step 4 |
Enter the virtual machine specifications, see Domain and Active Directory Considerations for HCSCC section of Solution Design Guide for Cisco Hosted Collaboration Solution for Contact Center http://www.cisco.com/c/en/us/support/unified-communications/hosted-collaboration-solution-contact-center/products-installation-guides-list.html. |
Install Antivirus Software
Perform this procedure for both golden-template and for direct-install options.
Install any of the antivirus software products supported by HCS for CC for Contact Center.
For more information on the anitvirus software and versions supported by HCS for CC for Contact Center, see Contact Center Enterprise Compatibility Matrix at https://www.cisco.com/c/en/us/support/unified-communications/hosted-collaboration-solution-contact-center/products-device-support-tables-list.html.
Install any of the antivirus software products supported by Enterprise Chat and Email. For more information on the anitvirus software and versions supported by Enterprise Chat and Email, see the System Requirements for Enterprise Chat and Email at https://www.cisco.com/c/en/us/support/customer-collaboration/cisco-enterprise-chat-email/products-implementation-design-guides-list.htm.
 Important |
Update antivirus software, manually - do not enable automatic updates. |
 Tip |
To allow required access to installation program files or folders, perform file-blocking exclusions in the antivirus product file-and-folder protection rules. To do this in McAfee VirusScan:
|
 Important |
HCS for CC for Contact Center supports Symantec Endpoint Protection. Be aware that in the firewall component of Symantec Endpoint Protection 12.1, the Network Threat Protection feature, must be disabled. If it remains enabled, which is the default, both sides of the duplexed router shows up in simplex mode, thus blocking communications between each side of the router. This blocking impacts all deployment types. If you retain the default (enabled) start services on side A and B of the router, a Symantec message pops up in the system tray indicating: The client will block traffic from IP address [side A router address] for the next 600 seconds(s). This message also appears in the client management security log. The Symantec Network Threat Protection traffic log indicates that a default firewall rule called “Block_all” was dynamically enabled. The result in both sides of the router come up in simplex mode. To avoid the issue, you must disable the Symantec firewall and restart both sides of the router. To do this, double click the Symantec icon in the system tray and select Change Settings. Then configure settings for Network Threat Protection and uncheck the Enable Firewall check box at the top of the Firewall tab. |
Disabling Port Blocking
On computers that
run Unified CVP Server components, such as Call Server and Reporting server,
which has an anti-virus software configured to block ports, exclude Unified CVP
processes and
tomcat6.exe. In addition, exclude Voice Browser.exe for
the call server process.
 Note |
If you use an anti-virus software other than McAfee Virus Scan, perform the equivalent exclusions in port blocking rules for that software. |
Procedure
|
Step 1 |
Launch McAfee. |
|
Step 2 |
In the VirusScan Console, double-click Access Protection, then choose Anti-virus Standard Protection. |
|
Step 3 |
Choose Prevent IRC communication from the list, then click Edit. |
|
Step 4 |
Add
|
|
Step 5 |
Click Ok. |
Enable DNS Server
Procedure
|
Step 1 |
Go to Start > Server Manager. |
||
|
Step 2 |
In the Server Manager window, select Manage > Add Roles and Features. |
||
|
Step 3 |
In the Before You Begin tab, click Next. |
||
|
Step 4 |
In the Installation Type tab, choose Role based or feature based installation option and click Next. |
||
|
Step 5 |
The Server Selection tab, displays the list of servers that are running on Windows Server. Select a server from this list and click Next. |
||
|
Step 6 |
On the Server Roles tab, do the following: |
||
|
Step 7 |
Select DNS Server. |
||
|
Step 8 |
In the Add Features that are required for DNS Server? dialog box, ensure the following tools are listed and then click Add Features.
|
||
|
Step 9 |
In the Features tab, ensure Remote Server Administration Tools and Role Administration Tools are selected and click Next. |
||
|
Step 10 |
In the AD DS tab, click Next. |
||
|
Step 11 |
In the DNS Sever tab, click Next. |
||
|
Step 12 |
n the Confirmation tab, click Install. |
||
|
Step 13 |
After the installation completes, click on the Promote this server to a domain controller link to make the server a domain controller. |
||
|
Step 14 |
In the Deployment Configuration tab, select Add a New Forest, enter a valid fully qualified domain DNS name, and click Next.
|
||
|
Step 15 |
In the Domain Controller Options tab, enter the following and click Next: |
||
|
Step 16 |
In the Additional Options tab, enter the NetBios name and click Next. |
||
|
Step 17 |
In the Paths tab, enter the paths where you would like to store the database, log files, and SYSVOL. |
||
|
Step 18 |
In the Review Options tab, click Next. |
||
|
Step 19 |
In the Prerequisites Check tab, you can read through the warning if any and click Install. |
Configure a DNS Server
To configuring a DNS server, see Configure DNS Server.
Create Two-Way Forest Trust
To create two-way forest trust between Unified CCE and CCDM,
Configure Cisco Unified CCE Rogger
This table lists the configuration procedures you must perform to configure Cisco Unified CCE Rogger.
| Sequence | Task | Done? |
|---|---|---|
| 1 | ||
| 2 | ||
| 3 | ||
| 4 | ||
| 5 | ||
| 6 | ||
| 7 | ||
| 8 | ||
| 9 | ||
| 10 | ||
| 11 |
Configure Network Cards
 Note |
Do this for all the Unified CCE virtual machines that have two network adapters. |
Procedure
|
Step 1 |
Navigate to Start > Control Panel > Network and Internet > Network and Sharing Center. |
|
Step 2 |
Click Change adapter settings to open the Network Connections page. |
|
Step 3 |
Rename the network adapter with Visible IP address configurations as Visible. |
|
Step 4 |
Rename the network adapter with Private IP address configurations as Private. |
|
Step 5 |
On the Network Connections page, press Alt N to display the Advanced menu. |
|
Step 6 |
From the Advanced menu, select Advanced Settings. |
|
Step 7 |
Under Adapters and Bindings, sort the connections so that visible is on top. |
|
Step 8 |
Click OK. |
Configure Private Ethernet Card
Procedure
|
Step 1 |
Right-click private and select Properties. |
||
|
Step 2 |
Uncheck Client for Microsoft Networks. |
||
|
Step 3 |
Uncheck File and Printer Sharing for Microsoft Networks. |
||
|
Step 4 |
Uncheck Internet Protocol Version 6 (TCP/IPV6). |
||
|
Step 5 |
Check Internet Protocol Version 4 (TCP/IPV4) and click Properties.
|
||
|
Step 6 |
Click the Advanced button. Open the DNS tab. Uncheck Register this connection's addresses in DNS. |
||
|
Step 7 |
Add an entry for the private IP address.
|
||
|
Step 8 |
Optional: Add another entry for the private high IP address.
|
||
|
Step 9 |
Click OK twice. Then, click Close. |
Configure Public Ethernet Card
Procedure
|
Step 1 |
Right-click Visible and select Properties. |
||
|
Step 2 |
Check Client for Microsoft Networks. |
||
|
Step 3 |
Check File and Printer Sharing for Microsoft Networks. |
||
|
Step 4 |
Uncheck Internet Protocol Version 6 (TCP/IPV6). |
||
|
Step 5 |
Check Internet Protocol Version 4 (TCP/IPV4) and click Properties. |
||
|
Step 6 |
Confirm the Public IP address, Subnet mask, Default gateway and Preferred DNs server, and click Advanced. |
||
|
Step 7 |
On the Advanced tab, enter the public IP addresses. |
||
|
Step 8 |
On the DNS tab, in the DNS suffix for this connection field, enter the name of the local DNS zone for the server and check Register this connection's addresses in DNS. |
||
|
Step 9 |
Optional: Add another entry for the public IP address.
|
||
|
Step 10 |
If the server requires access to resources in a different trusting or trusted domain or DNS zone, select Append these DNS suffixes (in order) and enter the local DNS zone for the server first, and then add the other secondary zones that represent the trusting or trusted domain. |
||
|
Step 11 |
Click OK twice. Then, click Close. |
Set Local Administrator Password
Procedure
|
Step 1 |
Open Computer Management. |
|
Step 2 |
In left pane, expand Local and Users Groups and select Users. |
|
Step 3 |
In right pane, right-click administrator and choose Set password. |
|
Step 4 |
Click Proceed. |
|
Step 5 |
Enter New Password and Confirm Password. |
Verify the Machine in Domain
For Unified CCE golden template, the Automation Tool script clones and deploys the virtual machines automatically to the destination domain. Complete the following procedure to verify if the Virtual Machine is placed in destination domain.
For small contact center deployment model Agent PG can be in customer domain instead of service provider domain.
Procedure
|
Step 1 |
Log in to the Unified CCE machine. |
|
Step 2 |
Navigate to Start > All Programs > Administrative Tools > Server Manager to verify if the Virtual Machine is mapped to correct domain. If the machine is not in Domain, follow the below steps. |
|
Step 3 |
Click Change System Properties on Right side panel to open System Properties. |
|
Step 4 |
In Computer name tab, Click Change. |
|
Step 5 |
Choose Domain radio button to change the member from Workgroup to Domain. |
|
Step 6 |
Enter fully qualified Domain name and Click OK. |
|
Step 7 |
In Windows security pop-up, Validate the domain credentials and click OK. |
|
Step 8 |
On successful authentication, Click OK. |
|
Step 9 |
Reboot the server and login with domain credentials. |
Configure the Domain Manager
This procedure creates a organizational unit (Cisco_Unified CCE, facility,instance) from any of the Unified CCE PGs.
 Note |
The domain manager is a one-time configuration. You do not need to configure the domain manager for side B. |
 Note |
For Small Contact Center agent deployment model, follow the below procedure to create OU structure for the Agent PG in sub customer domain similar to the Unified CCE domain or skip the below procedure if you want to install Agent PG in the Unified CCE domain. |
Procedure
|
Step 1 |
Click the Windows Start icon, and then select the Downward Arrow icon to display all applications. |
|
Step 2 |
Select the Domain Manager icon from the list of applications. |
|
Step 3 |
Log in as a user who has permissions to create organizational units (OUs) in the domain. |
|
Step 4 |
In the section on the left, expand the domain. |
|
Step 5 |
Add the Cisco root as Cisco_Unified CCE : |
|
Step 6 |
Add the facility organizational unit (OU):
|
|
Step 7 |
Add the Instance OU:
|
|
Step 8 |
Click Close. |
Configure Unified CCE Encryption Utility
Procedure
|
Step 1 |
Start . |
|
Step 2 |
Select SSL Encryption Utility. |
|
Step 3 |
Click the Certificate Administration tab. |
|
Step 4 |
Click Uninstall. Select Yes. |
|
Step 5 |
When the uninstallation completes, choose Install. You see a stream of messages, ending with SSL Certificate successfully installed. |
|
Step 6 |
Click Close. |
What to do next
Create and Bind System CLI Certificate
Complete the following procedure to create and bind the system CLI certificate:
Procedure
|
Step 1 |
Open the command prompt. |
|
Step 2 |
Enter the command cd C:\icm\serviceability\diagnostics\bin and press Enter. |
|
Step 3 |
Enter the command DiagFwCertMgr /task:CreateAndBindCert and press Enter. |
Configure SQL Server for CCE Components
Configure SQL Server on both the Unified CCE Rogger and the Unified CCE AW-HDS-DDS.
Procedure
|
Step 1 |
Click the Windows Start icon, and then select the Downward Arrow icon to display all applications. |
|
Step 2 |
Open Microsoft SQL Server Management Studio. |
|
Step 3 |
Log in. |
|
Step 4 |
Expand Security and then Logins. |
|
Step 5 |
If the BUILTIN\Administrators group is not listed:
|
Allocate a Second Virtual Hard Drive
Procedure
|
Step 1 |
Right-click the virtual machine and click Edit Settings. |
||||||||||||||
|
Step 2 |
In the Virtual Hardware tab, click on Add New Device. |
||||||||||||||
|
Step 3 |
You can select the type of device you wish to add. Select Hard Disk. The new hard disk appears. Assign the desired disk space to the hard disk.
|
||||||||||||||
|
Step 4 |
On the Disk Provisioning section, choose Thick provision Lazy Zeroed. |
||||||||||||||
|
Step 5 |
In the VM Options > Advanced Options section, retain the default options. |
||||||||||||||
|
Step 6 |
Click OK to confirm the changes. The Recent Tasks window at the bottom of the screen displays the progress. |
Configure the Unified CCE Logger
 Note |
Ensure that your browser is enabled. |
Procedure
|
Step 1 |
Launch the Unified CCE Web Setup. |
||||
|
Step 2 |
Sign in using as domain user having local Administrator permissions. |
||||
|
Step 3 |
Click Instance Management, and then click Add. |
||||
|
Step 4 |
In the Add Instance window, select Facility and Instance from the drop-down list. |
||||
|
Step 5 |
In the Instance Number field, enter 0 and click Save. |
||||
|
Step 6 |
Configure the logger database as follows:
|
||||
|
Step 7 |
In Create Database window, configure the following to create the Log:
|
||||
|
Step 8 |
In Add Device dialog box, configure as follows:
|
||||
|
Step 9 |
In Create Database window, in Storage section, click Add. |
||||
|
Step 10 |
In Add Device dialog box, configure as follows:
|
||||
|
Step 11 |
In Create Database window, click Create and click Start. When you see the successful creation message, click OK and click Close. |
||||
|
Step 12 |
Configure the logger component as follows:
|
||||
|
Step 13 |
In Additional Options window, configure as follows:
|
||||
|
Step 14 |
In Data Retention window, in the data retention table, retain the default values and click Next. |
||||
|
Step 15 |
In Data Purge window, configure purge for a time when there is low demand on the system. Click Next. |
||||
|
Step 16 |
In the Summary window
|
What to do next
Set database and log file size, see Database and Log File Size.
Database and Log File Size
Complete the following procedure to increase the database and log sizes.
Before you begin
To calculate database and log file size, download and use the Database Size Estimator from https://software.cisco.com/download/type.html?mdfid=268439622&catid=null.
Alternative option is to size the database and log using the values from the following table.
Procedure
|
Step 1 |
Open SQL Server Management Studio. |
||||||||||||
|
Step 2 |
Click Connect. In the left pane, expand Databases. |
||||||||||||
|
Step 3 |
Right-click Logger database [<Instance>_<Side>] and select Properties.. |
||||||||||||
|
Step 4 |
In the left pane, select Files. Ensure that Auto Growth is disabled for data and enabled for log files. Log files automatically grow in 10 percent increments. |
||||||||||||
|
Step 5 |
Set the initial size of the data and log files according to the Database Size Estimator or from the following table:
|
Configure the Unified CCE Router
Procedure
|
Step 1 |
Launch the Unified CCE Web Setup. |
||
|
Step 2 |
Sign in as the domain user with local Administrator permission. |
||
|
Step 3 |
Click Instance Management, and then click Add. |
||
|
Step 4 |
In the Add Instance window, select Facility and Instance from the drop-down list. |
||
|
Step 5 |
In the Instance Number field, enter 0. Click Save . |
||
|
Step 6 |
Select . |
||
|
Step 7 |
Click Add to set up the Call Router. |
||
|
Step 8 |
In the Deployment window, select the appropriate Side. |
||
|
Step 9 |
Select Duplexed as Fault Tolerance Mode. Click Next. |
||
|
Step 10 |
In the Router Connectivity window, configure the Private Interface and Public (Visible) Interfaces. Click Next. |
||
|
Step 11 |
In the Enable Peripheral Gateways dialog box, enter the following in the Enable Peripheral Gateways field. Click Next.
|
||
|
Step 12 |
In the Router Options window, configure as follows:
|
||
|
Step 13 |
In Router Quality of Service window, click Next. (Applicable to Side A only.) |
||
|
Step 14 |
In the Summary window, make sure that the router summary is correct, then click Finish.
|
What to do next
To enable the DNWildcard, select the Registry > HKEY_LOCAL_MACHINE > SOFTWARE > Cisco Systems > ICM > <instance> >RouterA > Router > CurrentVersion > Configurations > Global, and select the DNWildcardEnabled and set to 1.
Load Base Configuration
Procedure
|
Step 1 |
Based on your timezone, download the HCS-CC_11.6.1-Day1_2000.zip or file. Save it locally and unzip it. |
|
Step 2 |
Download the Domain_Update_Tool.zip file. Save it locally and unzip it. |
|
Step 3 |
Copy the configuration folder to the local drive of Unified CCE Rogger on Side A. |
|
Step 4 |
Open the ICMDBA Tool on the Unified CCE Rogger on Side A. |
|
Step 5 |
Select the Unified CCE Rogger and expand the tree to <instance name>_sideA. |
|
Step 6 |
Select Data on the menu bar and click Import. |
|
Step 7 |
Browse to locate the configuration folder and click Open. |
|
Step 8 |
Click OK and then click Import. |
|
Step 9 |
Click Start and then click OK on all messages. |
|
Step 10 |
Navigate to the folder Domain_Update_Tool and right-click UpdateDomain.PS1. and Run with PowerShell. Respond as follows:
|
|
Step 11 |
Return to the ICMDBA tool. Select Logger <instance name> database for the side that you want to synchronize. |
|
Step 12 |
Click Data in menu bar and select Synchronize and perform the following:
|
|
Step 13 |
Click Start and then click OK on all messages. |
Configure Unified CCE AW-HDS-DDS
This section explains the configuration procedures you must perform for the Unified CCE AW-HDS-DDS for Sides A and B.
| Sequence | Task | Done? |
|---|---|---|
| 1 | ||
| 2 | ||
| 3 | ||
| 4 | ||
| 5 | ||
| 6 | ||
| 7 | ||
|
8 |
||
| 9 | ||
| 10 |
AW-HDS-DDS
Create Instance
Procedure
|
Step 1 |
Launch Unified CCE Web Setup from the desktop and log in using the Domain Administrator credentials to complete the installation. |
|
Step 2 |
Click Instance Management, and then click Add. |
|
Step 3 |
In the Add Instance window, select Facility and Instance from the drop-down list. |
|
Step 4 |
In the Instance Number field, enter 0. Click Save. |
Create HDS Database
Procedure
|
Step 1 |
Configure the HDS database as follows:
|
|
Step 2 |
In the Select Component dialog box, choose Administration & Data Server from the drop-down list. Click OK. |
|
Step 3 |
At the prompt, SQL Server is not configured properly. Do you want to configure it now?" Click Yes. |
|
Step 4 |
On the Configure page, in the SQL Server Configurations pane check Memory (MB) and Recovery Interval. Click OK. |
|
Step 5 |
On the Stop Server page, click Yes to stop the services. |
|
Step 6 |
In the Select AW Type dialog box, choose Enterprise from drop-down list. Click OK. |
|
Step 7 |
In the Create Database dialog box, configure as follows:
|
|
Step 8 |
In the Add Device dialog box, configure as follows:
|
|
Step 9 |
In the Create Database dialog box, under Storage, click Add. |
|
Step 10 |
In the Add Device dialog box, configure as follows:
|
|
Step 11 |
In the Create Database dialog box, configure as follows:
|
Configure AW-HDS-DDS
Complete the following procedure to install the Cisco Unified CCE Administration Server & Real-time Data Server, Historical Data Server, and Detailed Data Server (AW-HDS-DDS).
Before you begin
Procedure
|
Step 1 |
Choose Component Management > Administration & Data Servers. |
||||
|
Step 2 |
Click Add. |
||||
|
Step 3 |
On the Deployment window, choose the current instance. |
||||
|
Step 4 |
On the Add Administration & Data Servers window, configure as follows:
|
||||
|
Step 5 |
On the Server Role in a Small to Medium Deployment window, configure as follows:
|
||||
|
Step 6 |
On the Administration & Data Servers Connectivity window, configure as follows: |
||||
|
Step 7 |
On the Database and Options window, configure as follows:
|
||||
|
Step 8 |
On the Central Controller Connectivity window, configure as follows:
|
||||
|
Step 9 |
In the Summary window
|
Database and Log File Size
Complete the following procedure to increase the database and log sizes.
Before you begin
Use Database Size Estimator to calculate database and log file size.
Alternative option is to size the database and log using the values from Table 1.Procedure
|
Step 1 |
Open Microsoft SQL Server Management Studio. |
||||||
|
Step 2 |
Expand the Database in Object Explorer. |
||||||
|
Step 3 |
Select HDS database. Right-click on the database and select Properties. |
||||||
|
Step 4 |
Click Files to increase the database and log sizes. |
||||||
|
Step 5 |
Ensure that Auto Growth is disabled for data and enabled for log files. Log files automatically grow in 10 percent increments. |
||||||
|
Step 6 |
Set the initial size of the data and log files according to Database Size Estimator or from the following table:
|
Set the HCS for CC Deployment Type
Before you begin
-
Ensure that a domain user logging into CCE Web Administration is part of the UcceConfig local group of all Unified CCE AW DB (real-time distributor) machines.
Procedure
|
Step 1 |
Launch CCE Web Administration. |
|
Step 2 |
Login with user credentials. |
|
Step 3 |
Set the HCS for CC for CC Deployment Type |
|
Step 4 |
View the Deployment Type.
|
|
Step 5 |
View the System Validation Rules
|
|
Step 6 |
View the System Configuration Limits
|
Configure Permissions in the Local Machine
In this release,Unified CCE defaults to providing user privileges by memberships to local user groups on local machines. This technique moves authorization out of Active Directory. However, it requires a one-time task on each local machine to grant the required permissions.
 Note |
You can use the ADSecurityGroupUpdate registry key to choose between the new default behavior and the previous behavior. For more information, see the chapter on solution security in the Solution Design Guide. |
Before using the Configuration Manager tool, configure the required registry and folder permissions for the UcceConfig group.
Configure Registry Permissions
Procedure
|
Step 1 |
Run the regedit.exe utility. |
||
|
Step 2 |
Select HKEY_LOCAL_MACHINE\SOFTWARE\Cisco Systems, Inc.\ICM. |
||
|
Step 3 |
Right-click and select Permissions. |
||
|
Step 4 |
If necessary, add UcceConfig in Group or user names. |
||
|
Step 5 |
Select UcceConfig and check Allow for the Full Control option. |
||
|
Step 6 |
Click OK to save the change. |
||
|
Step 7 |
Repeat the previous steps to grant Full Control to the UcceConfig group for HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Cisco Systems, Inc.\ICM. |
||
|
Step 8 |
Repeat the previous steps to grant Full Control to the UcceConfig group for HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\WinSock2.
|
Configure Folder Permissions
Grant the required folder permissions to the UcceConfig group on the local machine.
Procedure
|
Step 1 |
In Windows Explorer, select <ICM install directory>\icm. |
|
Step 2 |
Right-click and select Properties. |
|
Step 3 |
On the Security tab, select UcceConfig and check Allow for the Full Control option. |
|
Step 4 |
Click OK to save the change. |
|
Step 5 |
Repeat the previous steps to grant Full Control to the UcceConfig group for <SystemDrive>:\temp. |
Configure Unified CCE PG
The following table explains the tasks that you must perform to configure Unified CCE PG on both side A and B.
|
Sequence |
Tasks |
Done? |
|---|---|---|
|
1 |
||
|
2 |
||
|
3 |
||
|
4 |
||
|
5 |
||
|
6 |
||
|
7 |
||
|
8 |
||
|
9 |
||
|
10 |
||
|
11 |
Start Unified CCE Services |
Configure CUCM Peripheral Gateway
Complete the following tasks to configure CUCM peripheral gateways for the PG Server on Side A and then repeat the same procedure for Side B.
Configure CUCM PG
Before you begin
-
UcceConfig Local group
-
Local administrator group
Procedure
|
Step 1 |
Open Configuration Manager > PG Explorer. |
|
Step 2 |
Select the option Enable Agent Reporting for CUCMPG1 Routing Client. |
|
Step 3 |
Enter the Primary and Secondary CTI address and port information in the Unified Communications Manager PG for the Cisco Unified WIM and EIM feature. |
|
Step 4 |
In the Agent Distribution tab, enter a site name in Administration and Data Server field. |
Prepare to Add PG
Procedure
|
Step 1 |
Open Peripheral Gateway Setup. |
|
Step 2 |
In the ICM Instances pane, click Add. |
|
Step 3 |
In the Add Instance window, select the appropriate Facility and Instance Name from the drop-down list. |
|
Step 4 |
In the Instance Number field, enter 0. |
|
Step 5 |
Click Save. |
Add CUCM PG
Procedure
|
Step 1 |
Open Peripheral Gateway Setup. |
|
Step 2 |
In the Instance Components pane, click Add. |
|
Step 3 |
From the ICM/CCE/CCH Component Selection dialog box, select Peripheral Gateway. |
|
Step 4 |
In the Peripheral Gateway Properties dialog box:
|
Add CUCM PIM
Procedure
|
Step 1 |
In the Peripheral Gateway Component Properties window, click Add. |
||
|
Step 2 |
From the Client Type drop-down list, select CUCM. |
||
|
Step 3 |
From the Available PIMS list, select PIM, then click OK. |
||
|
Step 4 |
In the CUCM Configuration dialog box, check the Enabled check box. |
||
|
Step 5 |
In the Peripheral name field, enter the peripheral name. |
||
|
Step 6 |
In the Peripheral ID field, enter the logical controller ID. |
||
|
Step 7 |
In the Agent Extension Length field, enter the extension length for this deployment.
|
||
|
Step 8 |
In the CUCM Parameters pane, configure as follows:
|
||
|
Step 9 |
Repeat these steps to configure the remaining PIMs. Unified Communication Domain Manager sets the default password as "pguser", during Unified Communication Manager Integration. |
After Creating PIMs
Procedure
|
Step 1 |
In the Logical Controller ID field, enter the logical controller ID of the PIM. |
||
|
Step 2 |
In the CTI Wrapup Data Delay field, enter 0, then click Next. |
||
|
Step 3 |
In the Device Management Protocol Properties window:
|
||
|
Step 4 |
In the Peripheral Gateway Network interfaces window, enter PG Private Interfaces and PG Visible (Public) Interfaces. |
||
|
Step 5 |
For Side A only: |
||
|
Step 6 |
In the Peripheral Gateway Network Interfaces window, click Next. |
||
|
Step 7 |
In the Check setup Information window, click Next. |
||
|
Step 8 |
In the Setup Complete window, click Finish.
|
Configure VRU Peripheral Gateway
Add VRU PG
Procedure
|
Step 1 |
Open Peripheral Gateway Setup. |
|
Step 2 |
In the Instance Components pane, click Add. |
|
Step 3 |
From the Component Selection dialog box, select Peripheral Gateway. |
|
Step 4 |
In the Peripheral Gateway Properties dialog box:
|
Add VRU PIM
 Caution |
Before you enable secured connection between the components, ensure to complete the security certificate management process. For more information, see the Security Guide for Cisco Unified ICM/Contact Center Enterprise at https://www.cisco.com/c/en/us/support/customer-collaboration/unified-contact-center-enterprise/products-installation-and-configuration-guides-list.html. |
Procedure
|
Step 1 |
In the Peripheral Gateway Component Properties window, click Add. |
|
Step 2 |
From the Client Type drop-down list, select VRU. |
|
Step 3 |
Select the appropriate PIM from the Available PIMS list, then click OK. |
|
Step 4 |
In the Configuration dialog box, check the Enabled check box. |
|
Step 5 |
In the Peripheral name field, enter the CVP server name. |
|
Step 6 |
In the Peripheral ID field, enter the logical controller ID of CVP server. |
|
Step 7 |
In the VRU Hostname field, enter the hostname of the CVP server. |
|
Step 8 |
In the VRU Connect port field, enter 5000. |
|
Step 9 |
In the Reconnect interval (sec) field, enter 10. |
|
Step 10 |
In the Heartbeat interval (sec) field, enter 5. |
|
Step 11 |
From the DSCP drop-down list, select CS3(24). |
|
Step 12 |
Check the Enable Secured Connection option to enable secured connection. This establishes a secured connection between VRU PIM and CVP. |
|
Step 13 |
Click OK. |
|
Step 14 |
Repeat these steps to configure the remaining PIMs. |
Configure MR Peripheral Gateway
Add Media Routing PG
Configure Media Routing PG, though Multichannel and Outbound are not used. In this case, Media Routing PG remains idle or disabled.
Procedure
|
Step 1 |
Open Peripheral Gateway Setup. |
|
Step 2 |
In the Instance Components pane, click Add. |
|
Step 3 |
From the Component Selection dialog box, select Peripheral Gateway. |
|
Step 4 |
In the Peripheral Gateway Properties dialog box:
|
Add Multichannel PIM to 2000 Agent Deployment
 Caution |
Before performing the step to enable the secured connection between the components, ensure that the security certificate management process is completed. |
Procedure
|
Step 1 |
In the Peripheral Gateway Component Properties window, click Add. |
||
|
Step 2 |
From the Client Type drop-down list, select Media Routing. |
||
|
Step 3 |
From the Available PIMS list, select MR PIM1, then click OK. |
||
|
Step 4 |
In the Configuration dialog box, check the Enabled check box. |
||
|
Step 5 |
In the Peripheral name field, enter the peripheral name. |
||
|
Step 6 |
In the Peripheral ID field, enter the logical controller ID of the Unified CCE component you are adding. The following are the names by which the Unified CCE components are represented in the database. Refer Peripheral Gateway page in CCE Admin to get the peripheral ID of the corresponding PIM.
Example: |
||
|
Step 7 |
In the Application Hostname (1) field, enter the hostname or the IP address of the ECE services server. |
||
|
Step 8 |
In the Application connection port (1) field, enter the port number.
|
||
|
Step 9 |
In the Application Hostname (2) field, leave the field blank. |
||
|
Step 10 |
In the Application connection port (2) field, leave the field blank. |
||
|
Step 11 |
In the Heartbeat interval (sec) field, enter 5. |
||
|
Step 12 |
In the Reconnect interval (sec) field, enter 10. |
||
|
Step 13 |
Check the Enable Secured Connection option. This establishes a secured connection between the MR PIM and the application server. Ensure that you provide the correct information in the application hostname(1) and Application Connection Port(1) fields. |
||
|
Step 14 |
Click OK. |
Add Outbound PIM
 Caution |
Before you enable secured connection between the components, ensure to complete the security certificate management process. For more information, see the Security Guide for Cisco Unified ICM/Contact Center Enterprise at https://www.cisco.com/c/en/us/support/customer-collaboration/unified-contact-center-enterprise/products-installation-and-configuration-guides-list.html. |
Procedure
|
Step 1 |
In the Peripheral Gateway Component Properties window, click Add. |
|
Step 2 |
From the Client Type drop-down list, select Media Routing. |
|
Step 3 |
From the Available PIMS list, select MR PIM2, then click OK. |
|
Step 4 |
In the Configuration dialog box, check the Enabled check box. |
|
Step 5 |
In the Peripheral name field, enter the peripheral name. |
|
Step 6 |
In the Peripheral ID field, enter the logical controller ID. |
|
Step 7 |
In the Application Hostname (1) field, enter the hostname or the IP address of Agent PG machine of Side A. |
|
Step 8 |
In the Application connection port (1) field, retain the default value. |
|
Step 9 |
In the Application Hostname (2) field, enter the hostname or the IP address of Agent PG machine of Side B. |
|
Step 10 |
In the Application connection port (2) field, retain the default value. |
|
Step 11 |
In the Heartbeat interval (sec) field, enter 5. |
|
Step 12 |
In the Reconnect interval (sec) field, enter 10. |
|
Step 13 |
Check the Enable Secured Connection option. This establishes a secured connection between MR PIM and Application Server. Ensure that you provide the correct information in the Application Hostname(1) and Application Connection Port(1) fields. |
|
Step 14 |
Click OK. |
Configure CTI Server
 Caution |
Before enabling secured connection between the components, ensure that the security certificate management process is completed. For more information on security certificate management, see Security Guide for Cisco Unified ICM/Contact Center Enterprise at https://www.cisco.com/c/en/us/support/customer-collaboration/unified-contact-center-enterprise/products-installation-and-configuration-guides-list.html. |
Procedure
|
Step 1 |
Select Start > All Programs > Cisco Unified CCE Tools > Peripheral Gateway Setup. |
||
|
Step 2 |
In the Instance Components pane of the Components Setup dialog box click Add. |
||
|
Step 3 |
In the Component Selection dialog box, click CTI Server.
|
||
|
Step 4 |
In the Server Component Properties dialog box, configure as follows:
|
||
|
Step 5 |
Click Next. |
||
|
Step 6 |
In the Network Interface Properties dialog box, enter the private interfaces. |
||
|
Step 7 |
Enter the public (visible) interfaces and the CG visible interfaces, and click Next. |
||
|
Step 8 |
Under the Check Setup Information page, verify all the settings, and click Next. |
||
|
Step 9 |
In the Setup Completed dialog box, click Finish. |
||
|
Step 10 |
Click Exit Setup.
|
Upgrade Cisco JTAPI Client on PG
If you upgrade Unified Communications Manager (Unified CM) in the contact center, also upgrade the JTAPI client that resides on the PG. To upgrade the JTAPI client, uninstall the old version of the client, restart the server, and reinstall a new version. You install the JTAPI client using the Unified Communications Manager Administration application.
To install the JTAPI client for the Unified CM release that you have upgraded to, see the Install Cisco JTAPI Client on PG topic.
Before you begin
Before you perform this procedure, you must:
-
Uninstall the old JTAPI client from the Unified Communications Manager PG
-
Restart the PG server.
Verify Cisco Diagnostic Framework Portico
Do this for the Unified CCE machines.
Procedure
|
Step 1 |
Open the command prompt and enter cd C:\. |
|
Step 2 |
Enter cd icm\serviceability\diagnostics\bin and press Enter. |
|
Step 3 |
Enter DiagFwCertMgr /task:CreateAndBindCert /port:7890 and press Enter. |
|
Step 4 |
Go to Start -> Run and enter services.msc to open the Services tool. Make sure the Cisco Diagnostic Framework service is running. If it is not running start it. |
|
Step 5 |
Open Diagnostic Framework Portico: . Then make sure you can log in to the Diagnostic Framework Portico using domain user credentials. |
Cisco SNMP Setup
Complete the following procedures to configure Cisco SNMP:
Add Cisco SNMP Agent Management Snap-In
You can configure Cisco SNMP Agent Management settings using a Windows Management Console snap-in.
Complete the following procedure to add the snap-in and change Cisco SNMP Management settings.
Procedure
|
Step 1 |
From the Start menu, enter mmc.exe /32. |
|
Step 2 |
From the Console, choose. |
|
Step 3 |
In the Add or Remove Snap-ins dialog box, choose Cisco SNMP Agent Management from the list of available snap-ins. Click Add. |
|
Step 4 |
In the Selected snap-ins pane, double-click Cisco SNMP Agent Management. |
|
Step 5 |
In the Extentions for Cisco SNMP Agent Management dialog box, select Always enable all available extentions. Click OK. |
|
Step 6 |
In the Add/Remove Snap-in window, click OK. The Cisco SNMP Agent Management Snap-in is now loaded into the console. |
Save Cisco SNMP Agent Management Snap-In View
After you load the Cisco SNMP Agent Management MMC snap-in, you can save the console view to a file with a .MSC file extension. You can launch the file directly from Administrative Tools.
Complete the following procedure to save the Cisco SNMP Agent Management snap-in view.
Procedure
|
Step 1 |
Choose . |
|
Step 2 |
In the Filename field, enter Cisco SNMP Agent Management. |
|
Step 3 |
In the Save As type field, choose a file name to map to the administrative tools such as Microsoft Management Console Files(*.msc). |
|
Step 4 |
Click Save. |
Set Up Community Names for SNMP V1 and V2c
If you use SNMP v1 or v2c you must configure a community name so that Network Management Systems (NMSs) can access the data your server provides. Use SNMP community names to authenticate data exchange of SNMP information. An NMS can exchange SNMP information only with servers that use the same community name.
Complete the following procedure to configure the community name for SNMP v1 and v2c.
Before you begin
Ensure Cisco SNMP is added and saved using the procedures Add Cisco SNMP Agent Management Snap-In and Save Cisco SNMP Agent Management Snap-In View.
Procedure
|
Step 1 |
Choose . |
|
Step 2 |
Right-click Cisco SNMP Agent Management and choose Run as administrator. |
|
Step 3 |
The Cisco SNMP Agent Management screen lists some of the configurations that require SNMP for traps and system logs. |
|
Step 4 |
Right-click Community Names (SNMP v1/v2c) and choose Properties. |
|
Step 5 |
In the Community Names (SNMP v1/v2c) Properties dialog box, click Add New Community. |
|
Step 6 |
In the Community Name field, enter a community name. |
|
Step 7 |
In the Host Address List, enter the host IP address. |
|
Step 8 |
Click Apply and click OK. |
Set Up SNMP User Names for SNMP V3
If you use SNMP v3 you must configure a user name so that NMSs can access the data your server provides.
Complete the following procedure to configure a user name for SNMP v3.
Before you begin
Ensure Cisco SNMP is added and saved using the procedures Add Cisco SNMP Agent Management Snap-In and Save Cisco SNMP Agent Management Snap-In View.
Procedure
|
Step 1 |
From the Console Root, choose . |
|
Step 2 |
Click Add New User. |
|
Step 3 |
In the User Name field, enter a username. |
|
Step 4 |
Click Save. |
|
Step 5 |
The username appears in the Configured Users pane at the top of the dialog box. |
|
Step 6 |
Click Apply and click OK. |
Set Up SNMP Trap Destinations
You can configure SNMP Trap Destinations for SNMP v1, SNMP v2c, and SNMP v3. A Trap is a notification that the SNMP agent uses to inform the NMS of a certain event.
Complete the following procedure to configure the trap destinations.
Before you begin
Ensure Cisco SNMP is added and saved using the procedures Add Cisco SNMP Agent Management Snap-In and Save Cisco SNMP Agent Management Snap-In View.
Procedure
|
Step 1 |
From the Console Root, choose . |
|
Step 2 |
Click Add Trap Entity. |
|
Step 3 |
Click the SNMP version that your NMS uses. |
|
Step 4 |
In the Trap Entity Name field, enter a name for the trap entity. |
|
Step 5 |
Choose the User Name/Community Name that you want to associate with this trap. This list is auto-populated with existing configured users/community names. |
|
Step 6 |
Enter one or more IP addresses in the IP Address entry field. Click Insert to define the destinations for the traps. |
|
Step 7 |
Click Apply and click Save to save the new trap destination. The trap entity name appears in the Trap Entities section at the top of the dialog box. |
|
Step 8 |
Click OK. |
Set Up SNMP Syslog Destinations
You can configure Syslog destinations for SNMP from the Cisco SNMP Agent Management Snap-in.
Complete the following procedure to configure Syslog destinations.
Procedure
|
Step 1 |
From the Console Root, choose . |
|
Step 2 |
Choose an Instance from the list box. |
|
Step 3 |
Check Enable Feed. |
|
Step 4 |
Enter an IP address or host name in the Collector Address field. |
|
Step 5 |
Click Save. |
|
Step 6 |
Click OK and restart the logger. |
Start Unified CCE Services
The Unified CCE components run as a Windows service on the host computer. You can start, stop, or cycle these services from the Unified CCE Service Control tool on the desktop.
 Note |
This procedure is required for activating Unified CCE services. However, you must postpone this task until you install Unified CCE components in all virtual machines given in the deployment model. |
Procedure
|
Step 1 |
On eachUnified CCE Server machine, open Unified CCE Service Control. |
|
Step 2 |
Start the Unified CCE component services. |
Configure Unified CVP
| Sequence | Task | Done? |
|---|---|---|
|
1 |
||
|
2 |
||
|
3 |
Configure Unified CVP Server
This section explains the procedures to configure Unified CVP Server.
| Sequence | Task | Done? |
|---|---|---|
|
1 |
||
|
2 |
||
|
3 |
Validate Network Card
Procedure
|
Step 1 |
Select Start and right-click Network. |
|
Step 2 |
Select Properties. Then select Change Adapter Settings. |
|
Step 3 |
Right-click Local Area Connection and select Properties. |
|
Step 4 |
Uncheck Internet Protocol Version 6 (TCP/IPV6). |
|
Step 5 |
Check Internet Protocol Version 4 and select Properties. |
|
Step 6 |
Confirm the data for Visible IP addresses, Subnet mask, Default gateway and Preferred and alternate DNS servers. |
|
Step 7 |
Click OK. |
Setup Unified CVP Media Server IIS
Procedure
|
Step 1 |
Navigate to . |
|
Step 2 |
Choose Server Manager option navigate to . |
|
Step 3 |
Goto Installation Type tab, choose Role based or featue based installation option and click Next. |
|
Step 4 |
On Server Selection window, select server from the list and click Next. |
|
Step 5 |
Check Web Sever(IIS) check box to enable IIS and click Next. |
|
Step 6 |
No additional features are necessary to install Web Adaptor, click Next. |
|
Step 7 |
Click Next. |
|
Step 8 |
Ensure that the web server components listed below are enabled.
|
|
Step 9 |
Click Next. |
|
Step 10 |
Ensure that your settings are correct and click Install. |
|
Step 11 |
After installation click Close. |
Setup FTP Server
Install FTP Server
Procedure
|
Step 1 |
Select . |
|
Step 2 |
Select Server Manager and click Manage. |
|
Step 3 |
Select Add Roles and Features and click Next. |
|
Step 4 |
In the Installation Type tab, select Role-based or feature-based Installation and click Next. |
|
Step 5 |
Select required server from the list and click Next. |
|
Step 6 |
On the Server Roles page, expand Web Server (IIS). |
|
Step 7 |
Check FTP Server and click Next. |
|
Step 8 |
On the Features page, click Next. |
|
Step 9 |
On the Configuration page, click Install. |
Enable FTP Server
Procedure
|
Step 1 |
Goto . |
|
Step 2 |
Choose Sever Manager and click IIS. |
|
Step 3 |
Right-click on the server that you want to enable FTP server and choose Internet Information Services (IIS) Manager option from submenu. |
|
Step 4 |
Goto Connections panel:
|
|
Step 5 |
Enter FTP Site Name. |
|
Step 6 |
Browse C:\Inetpub\wwwroot in Physical Path field and click Next. |
|
Step 7 |
Choose IP Address of CVP from the drop-down list. |
|
Step 8 |
Enter Port number. |
|
Step 9 |
Check No SSL check box and click Next. |
|
Step 10 |
Check Anonymus and Basic check boxes in Authentication panel. |
|
Step 11 |
Choose All Users from Allow Access To drop-down list. |
|
Step 12 |
Check Read and Write check boxes and click Finish. |
Configure Basic Settings for FTP Server
Procedure
|
Step 1 |
Navigate to FTP server that you have created in Connections tab. |
|
Step 2 |
Goto Actions tab and click Basic Settings. |
|
Step 3 |
Click Connect As. |
|
Step 4 |
Choose Application User (pass-through authentication) option and click OK. |
|
Step 5 |
Click OK in Edit Site window. |
Configure Unified CVP Reporting Server
 Note |
|
This table lists the procedures to configure Unified CVP reporting server.
| Sequence | Task | Done ? |
|---|---|---|
| 1 | Validate Network Card | ? |
| 2 | ? | |
| 3 | Unified CVP Reporting Users | ? |
| 4 | Create Data Source for Cisco Unified CVP Report Data | ? |
Unified CVP Reporting Users
Create Reporting Users
Who can create a user:
-
Initially, the System Application User who is the default Superuser.
-
Eventually, any Superuser.
Unified CVP reporting users can sign in to Unified Intelligence Center only if they exist in the Administration console as Superusers or if Active Directory (AD) is configured in the Unified Intelligence Center Administration console for their domain:
-
Superusers who are added are considered to be IP Multimedia Subsystem (IMS) users.
-
Users who are authenticated through Active Directory are considered to be Lightweight Directory Access Protocol (LDAP) users.
Both IMS users and LDAP users can log in to Unified Intelligence Center reporting and are restricted to the limited Login User role until the Unified Intelligence Center reporting security administrator gives them additional roles and flags them as active users.
Create Superusers
Procedure
|
Step 1 |
Log in to the Cisco Unified Intelligence Center Administration Console |
|
Step 2 |
Navigate to Admin User Management > Admin User Management to open the Users page. |
|
Step 3 |
Click Add New to add and configure a new user or click an existing username to edit the configuration for that user. This page has three tabs: General, Credentials, and Policy. For information about completing these tabs, see Administration Console User Guide for Cisco Unified Intelligence Center at https://www.cisco.com/en/US/products/ps9755/prod_maintenance_guides_list.html or the Administration console online help. |
|
Step 4 |
Click Save. |
Set Up Active Directory Server for LDAP Users
Configure the Active Directory tab in the Cisco Unified Intelligence Center Administration console so that Unified CVP reporting users can log in to the Unified Intelligence Center reporting application with the user name and password that is defined in their domain.
Procedure
|
Step 1 |
In the Cisco Unified Intelligence Center Administration application, navigate to and select the Active Directory tab. |
|
Step 2 |
Complete all fields on this page, referring to the online help for guidance. |
|
Step 3 |
Click Test Connection. |
|
Step 4 |
When the connection is confirmed, click Save. |
Sign In to Cisco Unified Intelligence Center Reporting Interface
Who can sign in to the Unified Intelligence Center reporting interface:
-
Initially, the System Application User who is the default Superuser.
-
Eventually, any Unified CVP user who was created in the Administration Console as an IMS superuser or an LDAP user.
Perform the following procedure to sign in to the Unified Intelligence Center reporting interface.
Procedure
|
Step 1 |
Sign in to the Cisco Unified Intelligence Center Administration Console (https://<HOST ADDRESS>/oamp). |
|
Step 2 |
Navigate to Control Center > Device Control. |
|
Step 3 |
Click on the name of the Member node you want to access. This opens the Cisco Unified Intelligence Center login page for that member. |
|
Step 4 |
Enter your user ID and password. The Overview page appears. |
|
Step 5 |
What to do next
If you have CVP Reporting as an on-box VM or an external server, refer to sections in the Configure Unified Intelligence Center section for information on creating the data source for Unified CVP and importing CVP report templates.
Create Report Template
Follow these steps to create a Unified CVP Report Template from the Unified Intelligence Center at https://<hostname of CUICPublisher>:8444/cuic.
| Sequence | Task | Done? |
|---|---|---|
| 1 | Create Data Source for Cisco Unified CVP Report Data | |
| 2 | Obtain Cisco Unified CVP Report Templates | |
| 3 | Import Reports |
Create Data Source for Cisco Unified CVP Report Data
You can create or edit a data source only if you are assigned with a System Configuration Administrator role.
To create a data source, perform the following steps:
Procedure
|
Step 1 |
In the left navigation pane, choose . |
||||||||||||||||||||||||||||||
|
Step 2 |
In the Data Sources window, click New. |
||||||||||||||||||||||||||||||
|
Step 3 |
In the Create Data Source dialog box, enter the datasource Name, Description, and select the Data Source Type. |
||||||||||||||||||||||||||||||
|
Step 4 |
Click Next. |
||||||||||||||||||||||||||||||
|
Step 5 |
In the data source details page, enter the following (Primary Node tab):
|
||||||||||||||||||||||||||||||
|
Step 6 |
Click Test Connection to ensure that the database is accessible and the credentials provided are correct. |
||||||||||||||||||||||||||||||
|
Step 7 |
Click the Secondary Node tab to configure a failover for the data source. |
||||||||||||||||||||||||||||||
|
Step 8 |
Check the Enable Failover check box to configure a failover for the data source. |
||||||||||||||||||||||||||||||
|
Step 9 |
Enter the required details for the failover data source. (Refer step 5) |
||||||||||||||||||||||||||||||
|
Step 10 |
Click Save. |
||||||||||||||||||||||||||||||
Obtain Cisco Unified CVP Report Templates
Who can obtain import Unified CVP report templates: any user in your organization.
The Unified CVP reporting template XML files are installed with Unified CVP. Locate them and copy them to a Cisco Unified Intelligence Center client workstation.
Perform the following procedure to obtain import Unified CVP report templates.
Procedure
|
Step 1 |
In the Unified CVP server, locate the Unified CVP template files. These are XML files that reside on the reporting server in %CVP_HOME%\CVP_Reporting_Templates. You can also find them in the Installation directory \Downloads and Samples\Reporting Templates. |
|
Step 2 |
Choose the files and copy them to the client computer from where you can launch the Unified Intelligence Center Reporting web application. |
Import Reports
You can import the Unified Intelligence Center report, which is in either .xml or .zip file format.
The imported report retrieves data for the following entities:
-
Report
-
Report Definition
-
Value Lists
-
Views
-
Thresholds
-
Drilldowns
-
Template Help

Note
Each report template help folder has a size limit of 3 MB. If the folder size exceeds this limit, the system does not load the help content.
 Note |
You cannot import Report Filters and Collections. Ensure that the data source is used to import the Report Definition is configured in Unified Intelligence Center. Also, ensure that data source is used by any value list that is defined in Unified Intelligence Center, if the report definition has any value list defined. |
To import reports, perform the following steps:
Procedure
|
Step 1 |
In the left navigation pane, choose Reports. |
||
|
Step 2 |
In the Reports listing page, click Import. |
||
|
Step 3 |
Click Browse to select the file (.xml or .zip format) to be imported.
|
||
|
Step 4 |
Select the required file and click Open. |
||
|
Step 5 |
Select the file location from the Save to Folder list to save the file. |
||
|
Step 6 |
Click Upload. |
||
|
Step 7 |
Select a Data Source for the Report Definition only if the Report Definition for the report being imported is not defined in Unified Intelligence Center. |
||
|
Step 8 |
Select a Data Source for the Value List that is defined in the Report Definition.
|
||
|
Step 9 |
Select the files to import or overwrite.
|
||
|
Step 10 |
Click Import.
|
Configure Cisco Unified CVP Operations Console
Enable Unified CVP Operations Console
Procedure
|
Step 1 |
Go to Start > Run and type services.msc. |
|
Step 2 |
Check that Cisco CVP OPSConsoleServer service is running. If it is not, right-click that service and click Start. |
|
Step 3 |
Go to Start > All Programs > Cisco Unified Customer Voice Portal > Operation Console to open the Unified CVP OPSConsole page. If you are using Microsoft Internet Explorer, you will need to accept the self-signed certificate. |
Configure Unified CVP Call Server Component
 Note |
|
Procedure
|
Step 1 |
On the Unified CVP OAMP server, go to . |
|
Step 2 |
Click Operations Console and log in. |
|
Step 3 |
Navigate to Device Management > Unified CVP Call Server. |
|
Step 4 |
Click Add New. |
|
Step 5 |
On the General tab, enter the IP address and the hostname of the Cisco Unified CVP Server. Check ICM, IVR, and SIP. Click Next. |
|
Step 6 |
Click the ICM tab. For each of the Cisco Unified CVP Call Servers, retain the default port of 5000 for the VRU Connection Port. |
|
Step 7 |
Click the SIP tab:
|
|
Step 8 |
Click the Device Pool tab. Make sure the default device pool is selected. |
|
Step 9 |
(Optional) Click the Infrastructure tab. In the Configuration Syslog Settings pane, configure these fields as follows: |
|
Step 10 |
Click Save & Deploy. |
|
Step 11 |
Repeat this procedure for the remaining Unified CVP Servers. |
Configure Unified CVP Server Component
Procedure
|
Step 1 |
In the Unified CVP Operations console, navigate to . |
|
Step 2 |
Click Add New. |
|
Step 3 |
On the General tab, enter the IP address and the hostname of the Cisco Unified CVP Server. |
|
Step 4 |
Configure the primary and backup CVP Call Servers. |
|
Step 5 |
Click the Configuration tab. In the Enable reporting for this CVP VXML Server field, click Yes to optionally enable reporting. If you do not want to enable reporting, click No. |
|
Step 6 |
Click the Device Pool tab. Make sure the default device pool is selected. If prompted to restart the primary and secondary call servers, click No. Do not restart at this time. |
|
Step 7 |
Click Save & Deploy. |
|
Step 8 |
Repeat this procedure for all CVP Servers. |
Configure Unified CVP Reporting Server
 Note |
To load balance to the CVP reporting server, there are 2 CVP reporting servers deployed, one on each side. When a customer has 2 reporting servers, the customer should configure CVP Reporting server Side A and associate all the side A CVP call servers, and for Side B reporting server, associate all the CVP call servers belongs to side B, this is because each CVP call server and each VXML server can be associated with only one reporting server. Be aware that the reports cannot span multiple Informix databases. Side A call servers reports only of side A reporting server and side B call servers reports only of side B reporting server. If the customer chooses to have a single CVP reporting server, the customer should associate all the call servers to the single reporting server. During temporary database outages, messages are buffered to file and are inserted into the database after the database comes back on line. The amount of time that messages can be buffered depends on the system. |
Procedure
|
Step 1 |
In the CVP Operations Console, navigate to . |
|
Step 2 |
Click Add New. |
|
Step 3 |
On the General tab, configure the following:
|
|
Step 4 |
Configure the following on the Infrastructure tab: |
|
Step 5 |
Click Save & Deploy. |
|
Step 6 |
Repeat Steps 1 through 5 for all CVP Reporting Servers. |
Configure Unified CVP Media Server
Procedure
|
Step 1 |
In the CVP Operations Console, navigate to Device Management > Media Server. |
|
Step 2 |
Click Add New. |
|
Step 3 |
On the General tab, configure the following.
|
|
Step 4 |
Click Save. |
|
Step 5 |
Repeat Step 1 through 4 for all Media Servers. |
|
Step 6 |
After you configure all Media Servers, click Deploy. |
|
Step 7 |
Click Deployment Status to make sure that you applied the configuration. |
|
Step 8 |
In the CVP Operations Console, navigate to Device Management > Media Server. |
|
Step 9 |
Change Default Media Server from None to any one of the Unified CVP servers. Then click Set. |
|
Step 10 |
Click Deploy. |
Install Unified CVP licenses
Procedure
|
Step 1 |
Sign in to the CVP Operations Console. |
|
Step 2 |
Choose . |
|
Step 3 |
In the Select device type field, choose All Unified CVP devices. |
|
Step 4 |
Browse and select the license file. |
|
Step 5 |
Click Transfer. |
|
Step 6 |
Click File Transfer Status to monitor transfer progress. |
Configure Gateways
Procedure
|
Step 1 |
In the Unified CVP Operations Console, navigate to . |
|
Step 2 |
Click Add New. |
|
Step 3 |
On the General tab, configure as follows:
|
|
Step 4 |
Click Test Sign-in to verify that a connection with the gateway can be established and that the credentials are correct. |
|
Step 5 |
Click Save. |
|
Step 6 |
Repeat for every gateway. |
Transfer Scripts and Media Files
Procedure
|
Step 1 |
In the Unified CVP Operations Console, navigate to . |
|
Step 2 |
In the Select device type field, select the Gateway. |
|
Step 3 |
Move all Gateways to Selected. |
|
Step 4 |
Click Default Gateway files. |
|
Step 5 |
Click Transfer and select OK at the popup window. |
|
Step 6 |
Click File Transfer Status to monitor transfer progress. |
Configure SNMP
Procedure
|
Step 1 |
In the Unified CVP Operations Console, navigate to . |
|
Step 2 |
Click Add New.
|
|
Step 3 |
Create the notification destination and deploy to all of the Unified CVP devices.
|
Add Unified CCE Devices
Procedure
|
Step 1 |
Log in to the Unified CVP Operations Console. |
|
Step 2 |
Choose . |
|
Step 3 |
Click Add New. |
|
Step 4 |
On the General tab, configure as follows:
|
|
Step 5 |
Click Save. |
|
Step 6 |
Repeat Steps 1 to 5 for all Unified CCE machines. |
Add Unified Communications Manager Devices
Procedure
|
Step 1 |
Log in to the CVP Operations Console. |
||
|
Step 2 |
Choose . |
||
|
Step 3 |
Click Add New. |
||
|
Step 4 |
On the General tab, configure as follows:
|
||
|
Step 5 |
Click Save. |
||
|
Step 6 |
Repeat Steps 1 to 5 for all Unified Communications Manager Devices. |
Add Unified Intelligence Center Devices
Procedure
|
Step 1 |
Log in to the CVP Operations Console. |
|
Step 2 |
Navigate to the Cisco Unified Intelligence Center Device. Choose . |
|
Step 3 |
Click Add New. |
|
Step 4 |
On the General tab, configure as follows:
|
|
Step 5 |
Click Save. |
Configure SIP Server Group
SIP Server Groups are required for Cisco Unified Communications Manager and Gateways.
Procedure
|
Step 1 |
In the Unified CVP Operations Console, navigate to . |
|
Step 2 |
Create a server group for the Cisco Unified Communications Manager devices: |
|
Step 3 |
Create a server group for the gateway devices: |
|
Step 4 |
Associate these server groups to all Unified CVP Call Servers: |
Configure Dialed Number Patterns
Dialed number patterns are required for:
-
Agent Device
-
Network VRU
-
Ringtone
-
Error
Procedure
|
Step 1 |
In the Unified CVP Operations Console, navigate to . |
||||||||||||||||||||
|
Step 2 |
For each dialed number pattern in the following table:
|
||||||||||||||||||||
|
Step 3 |
After you configure all dialed number patterns, click Deploy. |
||||||||||||||||||||
|
Step 4 |
Click Deployment Status to make sure that you applied the configuration.
|
Configure Cisco IOS Enterprise Voice Gateway
Complete the following procedure to configure the Cisco IOS Voice Gateway. Instructions are applicable to both TDM and Cisco UBE Voice gateways, unless otherwise noted.
 Note |
Complete all configuration steps in mode. |
logging buffered 2000000 debugging
no logging console
service timestamps debug datetime msec localtime
ip routing
ip cef
ip source-route
interface GigabitEthernet0/0
ip route-cache same-interface
duplex auto
speed auto
no keepalive
no cdp enable
voice service voip
no ip address trusted authenticate
ip address trusted list
ipv4 0.0.0.0 0.0.0.0 # OR an explicit Source IP Address Trust List
allow-connections sip to sip
signaling forward unconditional
Configure Ingress Gateway
Procedure
|
Step 1 |
Configure global settings. |
||
|
Step 2 |
Configure voice codec preference: |
||
|
Step 3 |
Configure default services: |
||
|
Step 4 |
Configure gateway and sip-ua timers: |
||
|
Step 5 |
Configure POTS dial-peers: |
||
|
Step 6 |
Configure the switch leg: |
||
|
Step 7 |
Configure the hardware resources (transcoder, conference bridge, and MTP):
|
||
|
Step 8 |
Optional, configure the SIP Trunking: |
||
|
Step 9 |
Configure incoming PSTN SIP trunk dial peer: |
Configure VXML Gateway
Before you begin
 Note |
If you have configured VVB, it is not mandatory to configure VXML Gateway. You may configure either VVB or VXML Gateway, or configure both. |
Procedure
|
Step 1 |
Configure global settings: |
||
|
Step 2 |
Configure default Unified CVP services: |
||
|
Step 3 |
Configure dial-peers:
|
||
|
Step 4 |
Configure default Unified CVP HTTP, ivr, rtsp, mrcp and vxml settings: |
||
|
Step 5 |
Configure primary and secondary media servers: |
||
|
Step 6 |
Configure VXML leg where the incoming called-number matches the Network VRU Label: |
||
|
Step 7 |
Configure ASR TTS: |
||
|
Step 8 |
Exit configuration mode and use the Cisco IOS CLI command call application voice load <service_Name> to load the transferred Unified CVP files into the Cisco IOS memory for each Unified CVP service:
|
Configure Unified Communications Manager
Follow this sequence of tasks to configure Unified Communications Manager:
| Sequence | Task | Done? |
|---|---|---|
| 1 | ||
| 2 | ||
| 3 | ||
| 4 | ||
| 5 | ||
| 6 | ||
| 7 | ||
| 8 |
Configure Unified Communications Manager Publisher
You must customize the Unified Communications Manager publisher before you customize the subscribers.
Before you begin
Ensure that the Virtual Machine device status shows Connect at Power On checked for the Network adapter and Floppy drive.
Procedure
|
Step 1 |
Power on the Publisher. This begins the installation based on the information in the .flp file.The installation begins automatically and runs with no interaction from you. After an hour or more, a message appears indicating a successful installation. |
|
Step 2 |
Click the Console tab for the VM. Log in to the Publisher machine, using the credentials for the Administration User. The machine opens to the CLI interface. |
|
Step 3 |
Right-click the VM and choose Edit settings and uncheck Connect at Power on for the floppy drive. |
 Note |
During the customization of the publisher/primary, the username and the password are modified as follows. The customer should change the password.
|
Configure Unified Communications Manager Subscriber
Launch Unified Communications Manager Publisher to Add the Subscriber
To add the subscriber, you must launch the publisher node.
Procedure
|
Step 1 |
Launch the Unified Communications Manager Publisher in a browser (http://<IP Addr of CUCM Publisher>/ccmadmin). |
|
Step 2 |
Enter the username and password and login to the Unified Communications Manager. |
|
Step 3 |
Select . |
|
Step 4 |
On the Add a Server page, choose CUCM Voice/Video for the server type. Click Next. |
|
Step 5 |
On the Server Information page, enter the IP address of the first subscriber. |
|
Step 6 |
Click Save. |
|
Step 7 |
Repeat Steps 3 - 6 for the second subscriber. |
Configure Subscriber
Before you begin
Ensure that the Virtual Machine device status is Connect at Power On checked for the Network adapter and Floppy drive
Procedure
|
Step 1 |
Power on the Subscriber. |
|
Step 2 |
Click the Console tab for the VM. Log in to the CUCM Secondary machine, using the credentials for the Administration User. The machine opens to the CLI interface. |
|
Step 3 |
Right-click the VM and choose Edit settings and uncheck Connect at Power on for the floppy drive. |
 Note |
During the customization of the subscriber node, the username and the password are modified as follows. The customer should change the password.
|
Unified Communications Manager License
To configure the Unified Communications Manager license, first add a product instance, then generate and register the license, and then install the license.
Upgrade Unified Communications Manager License
Procedure
|
Step 1 |
Unzip the license file from the email message. |
|
Step 2 |
Launch Unified Communications Manager in a browser (https://<IP Address of CUCM Publisher>). |
|
Step 3 |
Click Cisco Prime License Manager and navigate to . |
|
Step 4 |
Under Other Fulfillment Options, select Fulfill Licenses from File. |
|
Step 5 |
Click Browse and locate your license file. |
|
Step 6 |
Click Install and close the popup window. |
|
Step 7 |
Navigate to Product Instances. Delete any old instances. Then click Add. |
|
Step 8 |
Fill in the name, hostname/IP address, username, and password for your Cisco Unified Communications Manager Publisher. |
|
Step 9 |
Select Product type of Unified CM. |
|
Step 10 |
Click OK. |
|
Step 11 |
Click Synchronize Now. |
Generate and Register License
Procedure
|
Step 1 |
Launch Unified Communications Manager in a browser (https://<IP Address of Unified CM Publisher>). |
|
Step 2 |
Click Cisco Prime License Manager and navigate to . |
|
Step 3 |
Under Other Fulfillment options, click Generate License Request. |
|
Step 4 |
When the License Request and Next Steps window opens, copy the text (PAK ID). |
|
Step 5 |
Click the Cisco License Registration link. |
|
Step 6 |
Sign in and click Continue to Product License Registration. |
|
Step 7 |
In the Enter a Single PAK or Token to fulfill field, paste your PAK ID and click Fulfill Single PAK/Token. You receive the license file in an email message. |
Install License
Complete the following procedure to install a license.
Procedure
|
Step 1 |
Unzip the license file from the email message. |
|
Step 2 |
Navigate to License Management > Licenses. |
|
Step 3 |
Under Other Fulfillment Options, choose Fulfill Licenses from File. |
|
Step 4 |
Browse for the license file and click Install. |
|
Step 5 |
Navigate to the Monitoring > License Usage page to verify a successful installation. |
Activate Services
Complete the following procedure to activate services.
Procedure
|
Step 1 |
Launch the Unified Communications Manager in a browser (http://<IP Address of CUCM Node>). |
||
|
Step 2 |
From the Cisco Unified Serviceability drop-down list, choose . |
||
|
Step 3 |
From the Server drop-down list, choose the server on which you want to activate the services, and then click Go. The window displays the service names and activation status of the services. |
||
|
Step 4 |
Check the following services to activate: |
||
|
Step 5 |
Click Save.
|
Validate Clusterwide Domain Configuration
Procedure
|
Step 1 |
In the Cisco Unified CM Administration, navigate to System > Enterprise Parameters. |
|
Step 2 |
Scroll down to Clusterwide Domain Configuration. Cluster Fully Qualified Domain Name should match the Server Group name in the Unified CVP SIP Server Groups Configure SIP Server Group. |
Upgrade Cisco JTAPI Client on PG
If you upgrade Unified Communications Manager (Unified CM) in the contact center, also upgrade the JTAPI client that resides on the PG. To upgrade the JTAPI client, uninstall the old version of the client, restart the server, and reinstall a new version. You install the JTAPI client using the Unified Communications Manager Administration application.
To install the JTAPI client for the Unified CM release that you have upgraded to, see the Install Cisco JTAPI Client on PG topic.
Before you begin
Before you perform this procedure, you must:
-
Uninstall the old JTAPI client from the Unified Communications Manager PG
-
Restart the PG server.
Install Cisco JTAPI Client on PG
After setting up the Cisco Unified Communications Manager (CUCM) PG, you must install the Cisco JTAPI client. PG uses Cisco JTAPI to communicate with CUCM. Install the Cisco JTAPI client from CUCM Administration.
 Note |
Continue with the steps provided in this section if you are installing the JTAPI client for CUCM version earlier than Release 12.5. To install the JTAPI client for CUCM, Release 12.5 and above, see Install Cisco JTAPI Client on PG. |
Before you begin
Before you install the JTAPI client, ensure that the previous version is uninstalled.
Procedure
|
Step 1 |
Open a browser window on the PG machine. |
|
Step 2 |
Enter the URL for the Unified Communications Manager Administration utility: http://<Unified Communications Manager machine name>/ccmadmin. |
|
Step 3 |
Enter the username and password that you created while installing and configuring the Unified Communications Manager. |
|
Step 4 |
Choose . Click Find. |
|
Step 5 |
Click the link next to Download Cisco JTAPI for Windows.We recommend you to download the 64 bit version. However, if you have already downloaded the 32 bit version, you can proceed to step 7. Download the JTAPI plugin file. |
|
Step 6 |
Choose Save and save the plugin file to a location of your choice. |
|
Step 7 |
Open the installer. |
|
Step 8 |
In the Security Warning box, click Yes to install. |
|
Step 9 |
Choose Next or Continue through the remaining Setup screens. Accept the default installation path. |
|
Step 10 |
When prompted for the TFTP Server IP address, enter the CUCM IP address. |
|
Step 11 |
Click Finish. |
|
Step 12 |
Reboot the machine. |
Install Cisco JTAPI Client on PG
Complete the following procedure only if you are installing JTAPI client to connect to Cisco Unified Communications Manager, Release 12.5 and above.
Before you begin
Before you install the JTAPI client, ensure that the previous version is uninstalled.
Procedure
|
Step 1 |
Open a browser window on the PG machine. |
|
Step 2 |
Enter the URL for the Unified Communications Manager Administration utility: http://<Unified Communications Manager machine name>/ccmadmin. |
|
Step 3 |
Enter the username and password that you created while installing and configuring the Unified Communications Manager. |
|
Step 4 |
Choose . Click Find. |
|
Step 5 |
Click the link next to Download Cisco JTAPI Client for Windows 64 bit or Download Cisco JTAPI Client for Windows 32 bit. Download the JTAPI plugin file. |
|
Step 6 |
Choose Save and save the plugin file to a location of your choice. |
|
Step 7 |
Unzip the JTAPI plugin zip file to the default location or a location of your choice. There are two folders in the unzipped folder CiscoJTAPIx64 and CiscoJTAPIx32. |
|
Step 8 |
Run the install64.bat file in the CiscoJTAPIx64 folder or run the install32.bat file in the CiscoJTAPIx32 folder. The default install path for JTAPI client is C:\Program Files\JTAPITools. |
|
Step 9 |
To accept the default installation path, click Enter and proceed. Follow the instructions. Click Enter whenever necessary as per the instructions. The JTAPI client installation completes at the default location. The following message is displayed: Installation Complete. |
|
Step 10 |
Reboot the machine. |
What to do next
 Note |
The default location, where the JTAPI client is installed, also contains the uninstall64.bat and uninstall32.bat file. Use this file to uninstall this version of the client, if necessary. |
Configure Unified Intelligence Center Coresident Deployment
Configure Unified Intelligence Center Publisher
You must customize the Cisco Unified Intelligence Center publisher before you customize the subscriber.
Before you begin
Ensure that the Virtual Machine device status is Connect at Power On checked for the Network adapter and Floppy drive
Procedure
|
Step 1 |
Power on the Publisher. |
|
Step 2 |
Click the Console tab for the VM. Log in to the CUIC Primary machine, using the credentials for the Administration User. The machine opens to the CLI interface. |
|
Step 3 |
Right-click the VM and choose Edit settings and uncheck Connect at Power on for the floppy drive. |
 Note |
During the customization of the publisher/primary, the username and the password are modified as follows. The customer should change the password.
|
Configure Unified Intelligence Center Subscriber
 Note |
Ensure that the license is updated before adding the subscriber node. |
Launch Publisher to Add Subscriber
Procedure
|
Step 1 |
Enter http://<HOST ADDRESS>/oamp URL in the browser, where HOST ADDRESS is the IP Address or Hostname of your Cisco Unified Intelligence Center publisher. |
|
Step 2 |
Sign in using the system application user ID and password that you defined during installation. |
|
Step 3 |
From the left panel, choose . |
|
Step 4 |
Click Add Member. |
|
Step 5 |
Enter hostname or IP address in Name field. |
|
Step 6 |
Enter Description for the device. |
|
Step 7 |
Click Save. |
Configure Subscriber
Before you begin
Ensure that the Virtual Machine device status is Connect at Power On checked for the Network adapter and Floppy drive
Procedure
|
Step 1 |
Power on the Subscriber. |
|
Step 2 |
Click the Console tab for the VM. Log in to the CUIC Secondary machine, using the credentials for the Administration User. The machine opens to the CLI interface. |
|
Step 3 |
Right-click the VM and choose Edit settings and uncheck Connect at Power on for the floppy drive. |
 Note |
During the customization of the subscriber node, the username and the password are modified as follows. The customer should change the password.
|
Add Coresident (Cisco Unified Intelligence Center with Live Data and IdS) Machine Type to the System Inventory
Procedure
|
Step 1 |
In Unified CCE Administration, navigate to . |
|
Step 2 |
Add the new machine to the System Inventory: The machine and its related Subscriber or Secondary machine are added to the System Inventory. |
What to do next
If you remove a component from your deployment, delete it from your System Inventory. If you add the component again, or add more components, add those components to the System Inventory.
Install VMware Tools for Windows
Procedure
|
Step 1 |
From the vSphere Client, right-click the virtual machine, select Power, and click Power On. |
|
Step 2 |
Click the Summary tab.
|
|
Step 3 |
Click the Console tab to make sure that the guest operating system starts successfully. Log in if prompted. |
|
Step 4 |
Right-click the virtual machine, select Guest OS, and then click Install/Upgrade VMware Tools. The Install/Upgrade VMware Tools window appears with the option - Interactive Tools Upgrade and Automatic Tools Upgrade.
|
Configure Unified Intelligence Center Reporting
Complete the following procedures to configure Unified Intelligence Center Reporting.
Configure the SQL User Account
Complete the following procedure on both sides of the Unified CCE Historical database servers and the Unified CCE Real-time database servers to allow SQL authentication and to enable TCP/IP protocol and remote network connections.
Procedure
|
Step 1 |
Log in to the Unified CCE Historical and Real-time database servers in your deployment. |
|
Step 2 |
Open SQL Server Management Studio. |
|
Step 3 |
Login using default credentials. |
|
Step 4 |
Expand Security tab. Right-click Logins and choose New Login. |
|
Step 5 |
In General page, enter the following values: |
|
Step 6 |
In Server Roles page, check the following check boxes:
|
|
Step 7 |
In User Mapping page, enter the following values: |
|
Step 8 |
Click OK. |
Configure Unified Intelligence Center Data Sources
Complete the following procedure to allow Unified Intelligence Center to configure Unified CCE Historical Data source and Unified CCE Real-time Data source.
 Note |
You can distribute the reporting load to several Unified CCE AW_HDS databases using the command line interface and conventional name resolution. If there is a need to direct a specific member node to a database host other than the one in configured on the data sources interface, you can use the "set cuic-properties host-to-ip" command to resolve the data source name differently on each node. |
Procedure
|
Step 1 |
Login to Unified Intelligence Center portal as administrator ( http://{hostname}) |
|
Step 2 |
From the navigation pane, click Configure > Data Sources. |
|
Step 3 |
Choose the Unified CCE Historical Data Source. Click Edit from the ellipsis to open the Data Source page. In the Primary tab, enter the following values
|
|
Step 4 |
Click on the Secondary tab and enter the following values.
|
|
Step 5 |
Click Test Connection to ensure the data source is online and click Save . |
|
Step 6 |
Choose the Unified CCE Realtime Data Source. Click Edit to open the Data Source > Edit page. In the Primary tab, enter the following values.
|
|
Step 7 |
Click on the Secondary tab and enter the following values.
|
|
Step 8 |
Click Test Connection to ensure the data source is online and click Save. |
What to do next
After configuring Unified Intelligence Center, you can import stock templates using the Import functionality and customize the stock reports based on your requirements. The stock templates are designed to present Unified CCE /CC data. Navigate to User Guide for the Cisco Unified Intelligence Center Reporting Application. Under Chapter Reports see section Stock Report Templates to import Unified CCE Report templates.
Configure Unified Intelligence Center Administration
Procedure
|
Step 1 |
Sign in to the Cisco Unified Intelligence Center Administration Console
|
||
|
Step 2 |
Configure the Active Directory tab under Cluster Configuration > Reporting Configuration.
|
||
|
Step 3 |
Configure syslog for all devices. |
||
|
Step 4 |
Configure SNMP for all devices, if used. |
Unified Intelligence Center License and Sign-In
Sign In to Administration Console
Who can sign in to the administration console: The System Application User who is the default Superuser.
To upload the license, you must sign in to the Unified Intelligence Center Administration Console. This is the OAMP interface for Unified Intelligence Center. The first person who signs in to the Administration application must do so using the user ID and password that were defined for the System Application User during the installation. This user is the initial Superuser for Unified Intelligence Center Administration.
Procedure
|
Step 1 |
Enter this URL:
|
|
Step 2 |
Enter the System Application User ID and password that you defined during installation. |
Upload License
Who can upload the license: The System Application User who is the default Superuser.
As soon as the System Application User signs in, the user must upload the license file. The file is uploaded to the Controller publisher node and, within a minute, is automatically replicated to all nodes in the cluster.
The partner must obtain a unique license and apply it to the imported Unified Intelligence Center servers at the customer site.
Procedure
|
Step 1 |
In Cisco Unified Intelligent Center Administration, choose . to open the License File Management page. 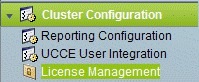 |
||
|
Step 2 |
Click Browse. |
||
|
Step 3 |
Navigate to the location where the *.lic file was saved. |
||
|
Step 4 |
Click Apply License to load the license. A message appears indicating that the license file was uploaded successfully and will be distributed to other nodes (if any) in the cluster in approximately one minute.
|
What to do next
Configure Live Data AW-Access
Live Data AW DB access commands allow you to configure and view Unified CCE AW DB (real-time distributor) access for Unified CCE Live Data Product Deployment Selection. You can also test the connection.
Procedure
|
Step 1 |
Log in to CUIC Live Data Console and run the following command: set live-data aw-access primary addr port db user pwd [test] set live-data aw-access secondary addr port db user pwd [test]
|
|||||||||||||||||||||
|
Step 2 |
Run the following command to view the primary and secondary Unified CCE AW DB access information. Optional, test the connection from Live Data to each AW DB, check if configured user (on each node) has appropriate AW DB access: show live-data aw-access primary addr port db user pwd [test] show live-data aw-access secondary addr port db user pwd [test] |
Configure Live Data Machine Services
Procedure
|
Step 1 |
Log in to CUIC Live Data Console. |
|||||||||||
|
Step 2 |
Run the below command to configure the latest information from Live Data with Machine Service table.
|
|||||||||||
|
Step 3 |
Run the below command to view Live Data entries in the Machine Services table:
|
|||||||||||
|
Step 4 |
After you updated the host name of the Live Data Server, you must re-run the following commands, to update the Live Data machine services with the new host name. |
Configure Live Data Unified Intelligence Data Sources
Before you begin
- Ensure that AW distributor and Cisco Unified Intelligence Center Publisher are in service
- Ensure that AW DB connection information is updated on the same node, where you want to configure Live Data CUIC data source
- Configure Live Data endpoints in the Machine Service table
Procedure
|
Step 1 |
Run the following command to configure the data source of Live Data in Cisco Unified Intelligence Center:
|
|||||||||||||||||
|
Step 2 |
Run the following command to display Data Source: |
Configure Live Data Reporting Interval
Procedure
|
Step 1 |
Log in to CUIC Live Data Console. |
||||||
|
Step 2 |
Run the following command to set Live Data reporting interval in minutes format:
|
||||||
|
Step 3 |
After Live Data reporting interval is set, run the below command to restart the publisher and subscriber node (Restart the inactive node first and active node next): |
||||||
|
Step 4 |
Run the below command to view Live Data reporting interval: |
Configure Transport Layer Security
Follow the procedures to set TLS Server and TLS Client minimum version.
Import Reports
You can import the Unified Intelligence Center report, which is in either .xml or .zip file format.
The imported report retrieves data for the following entities:
-
Report
-
Report Definition
-
Value Lists
-
Views
-
Thresholds
-
Drilldowns
-
Template Help

Note
Each report template help folder has a size limit of 3 MB. If the folder size exceeds this limit, the system does not load the help content.
 Note |
You cannot import Report Filters and Collections. Ensure that the data source is used to import the Report Definition is configured in Unified Intelligence Center. Also, ensure that data source is used by any value list that is defined in Unified Intelligence Center, if the report definition has any value list defined. |
To import reports, perform the following steps:
Procedure
|
Step 1 |
In the left navigation pane, choose Reports. |
||
|
Step 2 |
In the Reports listing page, click Import. |
||
|
Step 3 |
Click Browse to select the file (.xml or .zip format) to be imported.
|
||
|
Step 4 |
Select the required file and click Open. |
||
|
Step 5 |
Select the file location from the Save to Folder list to save the file. |
||
|
Step 6 |
Click Upload. |
||
|
Step 7 |
Select a Data Source for the Report Definition only if the Report Definition for the report being imported is not defined in Unified Intelligence Center. |
||
|
Step 8 |
Select a Data Source for the Value List that is defined in the Report Definition.
|
||
|
Step 9 |
Select the files to import or overwrite.
|
||
|
Step 10 |
Click Import.
|
Add Certificate for HTTPS Gadget
Add a certificate for a secure HTTP (HTTPS) gadget to allow the gadget to load into the Finesse desktop and successfully perform HTTPS requests to the Finesse server.
This process allows HTTPS communication between the Finesse gadget container and the third-party gadget site for loading the gadget and performing any API calls that the gadget makes to the third-party server.
 Note |
A gadget that loads using HTTPS may still use HTTP communication between that gadget and the application server where it resides. If all traffic must be secure, the gadget developer must ensure that HTTPS is used to make API calls to the application server. |
The certificate must be signed with a common name. The gadget URL in the desktop layout must use the same name (whether it uses an IP address or a fully qualified domain name) as the name with which the certificate is signed. If the certificate name and the name in the gadget URL do not match, the connection is not trusted and the gadget does not load.
Before you begin
Set up security certificates for finesse, Cisco Unified Intelligence Center and Live Data server to server communication. Import certificates into servers as shown in the table below:
|
Server |
Import Certificates |
|---|---|
|
Finesse |
Live Data and Cisco Unified Intelligence Center |
|
Cisco Unified Intelligence Center |
Live Data |
Procedure
|
Step 1 |
Download the tomcat-trust.pem certificate from the third-party gadget host.
|
|
Step 2 |
Upload the certificate to the Finesse Publisher server.
|
|
Step 3 |
Restart Cisco Tomcat and Cisco Finesse Tomcat services on the Finesse Publisher server. |
|
Step 4 |
Ensure the certificates are synchronized in Finesse Subscriber server. |
|
Step 5 |
Restart Cisco Tomcat and Cisco Finesse Tomcat services on Finesse Subscriber server. |
Configure Cisco Finesse
This table lists the configuration procedures for Cisco Finesse:
| Sequence | Task | Done? |
|---|---|---|
| 1 | ||
| 2 |
- |
|
| 3 | ||
| 4 | ||
| 5 | ||
| 6 |
Configure the Cisco Finesse Primary Node
 Note |
You must configure the Cisco Finesse primary node before you customize the secondary node. |
Before you begin
Ensure that the Virtual Machine device status is Connect at Power On checked for the Network adapter and Floppy drive
Procedure
|
Step 1 |
Power on the primary node. To begin the installation based on the information in the .flp file. |
|
Step 2 |
Click the Console tab for the VM. Log in to the Finesse Primary machine, using the credentials for the Administration User. The machine opens to the CLI interface. |
|
Step 3 |
Right-click the VM and choose Edit settings and uncheck Connect at Power on for the floppy drive. |
 Note |
During the customization of the primary, the username and the password are modified as follows. The customer should change the password.
After rebooting, the VM installation is complete with all the parameters provided in the spreadsheet for the VM. |
Configure Settings for the CTI Server and Administration and Data Server
Configure Contact Center Enterprise CTI Server Settings in the Cisco Finesse Primary Node
Access the administration console on the primary Finesse server to configure the A and B Side CTI servers.
 Note |
After you restart Finesse, it can take approximately 6 minutes for all server-related services to restart. Therefore, wait for 6 minutes before you attempt to access the Finesse administration console. |
 Note |
If you are using HTTPS, the first time you access the administration console, you see a browser security warning. To eliminate browser security warnings each time you sign in, trust the self-signed certificate provided with Finesse or obtain and upload a CA certificate. |
Procedure
|
Step 1 |
Sign in to the administration console on the primary Finesse server: http://FQDN of Finesse server/cfadmin |
||||||||||||
|
Step 2 |
Sign in with the Application User credentials defined during installation. |
||||||||||||
|
Step 3 |
In the Contact Center Enterprise CTI Server Settings area, enter the CTI server settings as described in the following table. Refer to your configuration worksheet if necessary.
|
||||||||||||
|
Step 4 |
Click Save. |
Contact Center Enterprise Administration and Data Server Settings
Use the Unified CCE Administration & Data Server Settings gadget to configure the database settings. These settings are required to enable authentication for Finesse agents and supervisors.
 Note |
To connect to the AW Database (AWDB) in the Unified CCE Administration, Cisco Finesse supports both SQL and Windows authentication. The Cisco Finesse Java Database Connectivity (JDBC) driver is configured to use NTLMv2. Therefore, Finesse can connect to the administration database even if the administration database is configured to use only NTLMv2. Primary Administration & Data Server is configured on Side A and Secondary Administration & Data Server is configured on Side B. Make sure Cisco Finesse server on both sides connect to Primary Administration & Data Server on side A and fall back to Secondary Administration & Data Server on side B only when Primary Administration & Data Server goes down. |
After you change and save any value on the Contact Center Enterprise Administration & Data Server Settings gadget, restart the Cisco Finesse Tomcat Service on the primary and secondary Finesse server. If you restart the Cisco Finesse Tomcat Service, agents must sign out and sign in again. To avoid this, you can make Contact Center Enterprise Administration & Data Server settings changes and restart the Cisco Finesse Tomcat service during hours when agents are not signed in to the Cisco Finesse desktop.
The following table describes the fields on the Unified CCE Administration & Data Server Settings gadget:
|
Field |
Description |
||
|---|---|---|---|
|
Primary Host/IP Address |
The hostname or IP address of the Unified CCE Administration & Data Server. |
||
|
Backup Host/IP Address |
(Optional) The hostname or IP address of the backup Unified CCE Administration & Data Server. |
||
|
Database Port |
The port of the Unified CCE Administration & Data Server. The default value is 1433.
|
||
|
AW Database Name |
The name of the AW Database (AWDB). For example, ucceinstance_awdb). |
||
|
Domain |
(Optional) The domain name of the AWDB. |
||
|
Username |
The username required to sign in to the AWDB.
|
||
|
Password |
The password required to sign in to the AWDB. |
For more information about these settings, see the Administration Guide for Cisco Unified Contact Center Enterprise and the Staging Guide for Cisco Unified ICM/Contact Center Enterprise.
Actions on the Unified CCE Administration & Data Server Settings gadget:
-
Save: Saves your configuration changes
-
Revert: Retrieves the most recently saved enterprise database settings
When you update any of the following fields and click Save, Cisco Finesse attempts to connect to the AWDB:
-
Primary Host/IP Address
-
Backup Host/IP Address
-
Database Port
-
AW Database Name
If Cisco Finesse cannot connect to the AWDB, an error message appears and you are asked if you still want to save. If you click Yes, the settings are saved. If you click No, the settings are not saved. You can change the settings and try again or click Revert to retrieve the previously saved settings.
When you update the Username or Password fields and click Save, Cisco Finesse attempts to authenticate against the AWDB. If authentication fails, an error message appears and you are asked if you still want to save. Click Yes to save the settings or click No to change the settings. Click Revert to retrieve the previously saved settings.
 Note |
Finesse will not come into service in case of AWDB errors when connecting Cisco Finesse 11.5(1) and higher versions to Unified CCE 11.5(1) and higher versions. |
Configure Contact Center Enterprise Administration and Data Server Settings
Configure the Unified CCE Administration & Data Server settings to enable authentication for Finesse agents and supervisors.
Procedure
|
Step 1 |
If you are not already signed in, sign in to the administration console. |
|
Step 2 |
In the Unified CCE Administration & Data Server Settings area, enter the Administration & Data Server settings as described in the preceding table. For more information, see Table 1. Refer to your configuration worksheet if necessary. |
|
Step 3 |
Click Save. |
What to do next
Restart the Cisco Tomcat Service
Procedure
|
Step 1 |
Enter utils service stop Cisco Tomcat command, to stop the Cisco Tomcat service. |
|
Step 2 |
Enter utils service start Cisco Tomcat command, to start the Cisco Tomcat service. |
Configure Cisco Finesse Secondary Node
Launch the Finesse Administration Console to Configure the Secondary Finesse
To add the secondary node, you must launch the primary node and add the secondary node to the cluster.
Procedure
|
Step 1 |
Launch the Cisco Finesse primary node in a browser (http://Primary Node FQDN/cfadmin), where the primary node or IP address is that of your host. |
|
Step 2 |
Select Settings > Cluster Settings. (Cluster settings are based on the default configuration and assumes that you have not changed the page for the Cluster Settings tool.) |
|
Step 3 |
Add the IP address for the Cisco Finesse secondary node. |
|
Step 4 |
Click Save. |
|
Step 5 |
Restart Cisco Tomcat as follows:
|
Install Cisco Finesse on the Secondary Node
Before you begin
Ensure that you select the Connect at Power on check box of the virtual machine for network adapter and floppy drive.
Procedure
|
Step 1 |
Power on the secondary node to begin the installation based on the information in the .flp file. |
|
Step 2 |
Click the Console tab for the virtual machine. Log into the Cisco Finesse secondary machine, using the credentials for the administration user. The machine opens to the CLI interface. |
|
Step 3 |
Right-click the virtual machine and choose Edit settings and uncheck Connect at Power on for the floppy drive. |
 Note |
During the customization of the secondary node, the username and the password is modified as follows. You can change the password:
|
Configure Cisco Finesse Administration
Obtain and Upload CA Certificate
 Note |
This procedure only applies if you are using HTTPS and is optional. If you are using HTTPS, you can choose to either obtain and upload a CA certificate or use the self-signed certificate provided with Finesse. |
To eliminate browser security warnings each time you sign in, obtain an application and root certificate signed by a CA. Use the Certificate Management utility from Cisco Unified Operating System Administration.
To open Cisco Unified Operating System Administration in your browser, enter:
https://FQDN of primary Finesse server:8443/cmplatform
Sign in using the username and password for the Application User account created during Finesse installation.
 Note |
You can find detailed explanations in the Security topics of the Cisco Unified Operating System Administration Online Help. |
Procedure
|
Step 1 |
Generate a CSR. |
||
|
Step 2 |
Download the CSR.
|
||
|
Step 3 |
Generate and download a CSR for the secondary Unified CCX server. To open Cisco Unified Operating System Administration for the secondary server in your browser, enter: https://FQDN of secondary Finesse server:8443/cmplatform |
||
|
Step 4 |
Use the CSRs to obtain the CA root certificate, intermediate certificate, and signed application certificate from the Certificate Authority.
|
||
|
Step 5 |
When you receive the certificates, click . |
||
|
Step 6 |
Upload the root certificate.
|
||
|
Step 7 |
Upload the intermediate certificate.
|
||
|
Step 8 |
Upload the application certificate.
|
||
|
Step 9 |
After the upload is complete, sign out from the Platform Admin page of Finesse. |
||
|
Step 10 |
Access the CLI on the primary Finesse server. |
||
|
Step 11 |
Enter the command utils service restart Cisco Finesse Notification Service to restart the Cisco Finesse Notification service. |
||
|
Step 12 |
Enter the command utils service restart Cisco Finesse Tomcat to restart the Cisco Finesse Tomcat service. |
||
|
Step 13 |
Upload the application certificate to the secondary Finesse server. The root and the intermediate certificates uploaded to the primary server are replicated to the secondary server. |
||
|
Step 14 |
Access the CLI on the secondary Finesse server and restart the Cisco Finesse Notification Service and the Cisco Finesse Tomcat Service. |
Set Up CA Certificate for Chrome and Edge Chromium (Microsoft Edge) Browsers
Procedure
|
Step 1 |
In the browser, go to Settings. |
|
Step 2 |
In the Chrome browser, select Advanced Settings > Privacy and Security, click Manage Certificates. |
|
Step 3 |
In the Microsoft Edge browser, select Privacy, search, and services. Under Security, click Manage Certificates. |
|
Step 4 |
Click Trusted Root Certification Authorities tab. |
|
Step 5 |
Click Import and browse to the ca_name.cer file. |
|
Step 6 |
Restart the browser for the certificate to install. |
Accept Security Certificates
Ensure that the pop-ups are enabled for the Finesse desktop.
After you enter the Finesse desktop URL in your browser, the procedure to add a certificate is as follows:
Install certificates on Windows operating system:
The procedure to add a certificate varies for each browser. The procedure for each browser is as follows:
Internet Explorer
 Note |
If you are using a Windows client, signed in as a Windows user, you must run Internet Explorer as an administrator to install the security certificates. In your Start menu, right-click Internet Explorer and select Run as administrator. Contact your administrator if you do not have the required permissions to install the security certificates. |
-
A page appears that states there is a problem with the website's security certificate. Click Continue to this website (not recommended) link to open the Finesse sign in page. The Finesse sign in screen appears with a certificate error in the address bar.
-
Click on the certificate error that appears in the address bar and then click View Certificates.
-
In the Certificate dialog box, click Install Certificate to open the Certificate Import Wizard.
-
Select Current User to install the certificate for the current user only, or select Local Machine to install the certificate for all Windows users.
-
On the Certificate Import Wizard, click Next.
-
Select Place all certificates in the following store and click Browse.
-
Select Trusted Root Certification Authorities and click OK.
-
Click Next and then click Finish. A Security Warning dialog box appears.
-
Click Yes to install the certificate. The Certificate Import dialog box appears.
-
Click OK and close the Certificate Import dialog box.
-
Close the browser tab. The accepted certificate link is removed from the SSL Certificate Not Accepted dialog box.
Repeat the preceding steps for all the certificate links. After you accept all the certificates, the sign-in process is complete.
 Note |
To remove the certificate error from the desktop, you must close and reopen your browser. |
Firefox
-
On Your connection is not secure page, click Advanced > Add Exception.

Note
Ensure that the Permanently store this exception box is checked.
-
Click Confirm Security Exception.
-
On and click Sign In.
-
In the SSL Certificate Not Accepted dialog box, click the certificate link. A browser tab opens for the certificate that you must accept.
-
On the browser tab, click I Understand the Risks > Add Exception. Ensure that the Permanently store this exception box is checked.
-
Click Confirm Security Exception. The browser tab closes after you accept the certificate and the accepted certificate link is removed from the SSL Certificate Not Accepted dialog box. Close the browser tab if it does not automatically close.
Repeat the preceding steps for all the certificate links. After you accept all the certificates, the sign-in process is complete.
Chrome and Edge Chromium (Microsoft Edge)
-
A page appears that states your connection is not private. To open the Finesse sign in page,
In Chrome, click Advanced > Proceed to <Hostname> (unsafe).
In Microsoft Edge, click Advanced > Continue to <Hostname> (unsafe).
-
Enter your agent ID or username, password, and extension, and then click Sign In.
-
In the SSL Certificate Not Accepted dialog box, click the certificate link. A browser tab opens for the certificate that you must accept.
-
On the browser tab,
In Chrome, click Advanced > Proceed to <Hostname> (unsafe).
In Microsoft Edge, click Advanced > Continue to <Hostname> (unsafe).
The browser tab closes after you accept the certificate and the accepted certificate link is removed from the SSL Certificate Not Accepted dialog box. Close the browser tab if it does not automatically close.

Note
If you click the certificate link and do not accept it, the certificate link stays enabled in the SSL Certificate Not Accepted dialog box. The certificate error appears every time you sign in. The procedure to permanently accept the certificate is as follows.
-
Click on the certificate error that appears in the address bar and then,
In Chrome, select Certificate (Invalid).
In Microsoft Edge, select Certificate (not valid).
The Certificate dialog box appears.
-
In the Details tab, click Copy to File. The Certificate Export Wizard appears.
-
Click Next.
-
Keep the default selection DER encoded binary X.509 (.CER) and click Next.
-
Click Browse and select the folder in which you want to save the certificate, enter a recognizable file name and click Save.
-
Browse to the folder where you have saved the certificate (.cer file), right-click on the file, and click Install Certificate. The Certificate Import Wizard appears.
-
Keep the default selection Current User and click Next.
-
Select Place all certificates in the following store and click Browse. The Select Certificate Store dialog box appears.
-
Select Trusted Root Certification Authorities and click OK.
-
Click Next and then click Finish. A Security Warning dialog box appears that asks if you want to install the certificate.
-
Click Yes. A Certificate Import dialog box that states the import was successful appears.
Close the browser and sign in to Finesse. The security error does not appear in the address bar.
Install certificates on macOS:
The procedure to download a certificate varies for each browser. The procedure for each browser is as follows:
Chrome and Edge Chromium (Microsoft Edge)
-
A warning page appears which states that your connection is not private. To open the Finesse Console sign in page,
In Chrome, click Advanced > Proceed to <Hostname> (unsafe).
In Microsoft Edge, click Advanced > Continue to <Hostname> (unsafe).
-
Click on the certificate error that appears in the address bar and then,
In Chrome, select Certificate (Invalid).
In Microsoft Edge, select Certificate (Not Valid).
A certificate dialog box appears with the certificate details.
-
Drag the Certificate icon to the desktop.
-
Double-click the certificate. The Keychain Access application opens.
-
In the right pane of Keychains dialog, browse to the certificate, right-click on the certificate, and select Get Info from the options that are listed. A dialog appears with more information about the certificate.
-
Expand Trust. From the When using this certificate drop-down, select Always Trust.
-
Close the dialog box that has more information about the certificate. A confirmation dialog box appears.
-
Authenticate the modification of Keychains by providing a password.
-
The certificate is now trusted, and the certificate error does not appear on the address bar.
Firefox
-
In your Firefox browser, enter the Finesse desktop URL. A warning page appears which states that there is a security risk.
-
Click Advanced and then click View Certificate link. The Certificate Viewer dialog box appears.
-
Click Details and then click Export. Save the certificate (.crt file) in a local folder.

Note
If .crt file option is not available, select .der option to save the certificate.
-
From the menu, select Firefox > Preferences. The Preferences page is displayed.
-
In the left pane, select Privacy & Security.
-
Scroll to the Certificates section and click View Certificates .... The Certificate Manager window is displayed.
-
Click Import and select the certificate.
-
The certificate is now authorized, and the certificate error does not appear on the address bar.
Configure SNMP
Procedure
|
Step 1 |
Log in to the Cisco Unified Serviceability (https://hostname of primary server:8443/ccmservice) using administrator credentials. |
|
Step 2 |
Select . |
|
Step 3 |
From Server drop-down list, select the server for which you want to configure a community string and click Find. |
|
Step 4 |
Click Add New to add new community string. |
|
Step 5 |
Select . |
|
Step 6 |
From Server drop-down list, select the server for which you want to configure a notification destination and click Find. |
|
Step 7 |
Click Add New button to add new notification destination. |
 Feedback
Feedback