VLAN Configuration Guide, Cisco IOS XE Release 3SE (Catalyst 3850 Switches)
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- October 8, 2013
Chapter: Configuring VLANs
- Finding Feature Information
- Prerequisites for VLANs
- Restrictions for VLANs
- Information About VLANs
- How to Configure VLANs
Configuring VLANs
- Finding Feature Information
- Prerequisites for VLANs
- Restrictions for VLANs
- Information About VLANs
- How to Configure VLANs
- Monitoring VLANs
- Where to Go Next
- Additional References
- Feature History and Information for VLANs
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Prerequisites for VLANs
The following are prerequisites and considerations for configuring VLANs:
- Before you create VLANs, you must decide whether to use VLAN Trunking Protocol (VTP) to maintain global VLAN configuration for your network.
- If you plan to configure many VLANs on the switch and to not enable routing, you can set the Switch Database Management (SDM) feature to the VLAN template, which configures system resources to support the maximum number of unicast MAC addresses.
- Switches running the LAN Base feature set support only static routing on SVIs.
- A VLAN should be present in the switch to be able to add it to the VLAN group.
Restrictions for VLANs
The following are restrictions for VLANs:
- The switch supports per-VLAN spanning-tree plus (PVST+) or rapid PVST+ with a maximum of 128 spanning-tree instances. One spanning-tree instance is allowed per VLAN.
- The switch supports IEEE 802.1Q trunking methods for sending VLAN traffic over Ethernet ports.
- Configuring an interface VLAN router's MAC address is not supported. The interface VLAN already has an MAC address assigned by default.
- Private VLANs are not supported on the switch.
- You cannot have a switch stack containing a mix of Catalyst 3850 and Catalyst 3650 switches.
Information About VLANs
Logical Networks
A VLAN is a switched network that is logically segmented by function, project team, or application, without regard to the physical locations of the users. VLANs have the same attributes as physical LANs, but you can group end stations even if they are not physically located on the same LAN segment. Any switch port can belong to a VLAN, and unicast, broadcast, and multicast packets are forwarded and flooded only to end stations in the VLAN. Each VLAN is considered a logical network, and packets destined for stations that do not belong to the VLAN must be forwarded through a router or a switch supporting fallback bridging. In a switch stack, VLANs can be formed with ports across the stack. Because a VLAN is considered a separate logical network, it contains its own bridge Management Information Base (MIB) information and can support its own implementation of spanning tree.
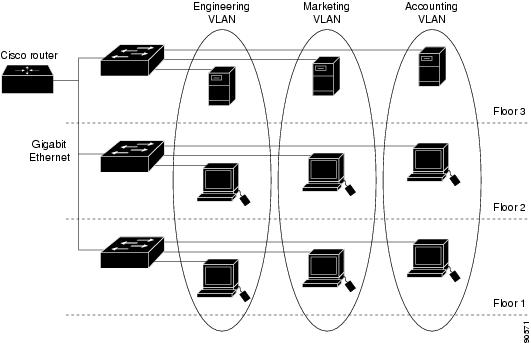
VLANs are often associated with IP subnetworks. For example, all the end stations in a particular IP subnet belong to the same VLAN. Interface VLAN membership on the switch is assigned manually on an interface-by-interface basis. When you assign switch interfaces to VLANs by using this method, it is known as interface-based, or static, VLAN membership.
Traffic between VLANs must be routed.
The switch can route traffic between VLANs by using switch virtual interfaces (SVIs). An SVI must be explicitly configured and assigned an IP address to route traffic between VLANs.
Supported VLANs
The switch supports VLANs in VTP client, server, and transparent modes. VLANs are identified by a number from 1 to 4094. VLAN 1 is the default VLAN and is created during system initialization. VLAN IDs 1002 through 1005 are reserved for Token Ring and FDDI VLANs. All of the VLANs except 1002 to 1005 are available for user configuration.
There are 3 VTP versions: VTP version 1, version 2, and version 3. All VTP versions support both normal and extended range VLANs, but only with VTP version 3, does the switch propagate extended range VLAN configuration information. When extended range VLANs are created in VTP versions 1 and 2, their configuration information is not propagated. Even the local VTP database entries on the switch are not updated, but the extended range VLANs configuration information is created and stored in the running configuration file.
You can configure up to 4094 VLANs on the switch.
VLAN Port Membership Modes
You configure a port to belong to a VLAN by assigning a membership mode that specifies the kind of traffic the port carries and the number of VLANs to which it can belong.
When a port belongs to a VLAN, the switch learns and manages the addresses associated with the port on a per-VLAN basis.
| Membership Mode |
VLAN Membership Characteristics |
VTP Characteristics |
|---|---|---|
| Static-access |
A static-access port can belong to one VLAN and is manually assigned to that VLAN. |
VTP is not required. If you do not want VTP to globally propagate information, set the VTP mode to transparent. To participate in VTP, there must be at least one trunk port on the switch or the switch stack connected to a trunk port of a second switch or switch stack. |
| Trunk (IEEE 802.1Q) : |
A trunk port is a member of all VLANs by default, including extended-range VLANs, but membership can be limited by configuring the allowed-VLAN list. You can also modify the pruning-eligible list to block flooded traffic to VLANs on trunk ports that are included in the list. |
VTP is recommended but not required. VTP maintains VLAN configuration consistency by managing the addition, deletion, and renaming of VLANs on a network-wide basis. VTP exchanges VLAN configuration messages with other switches over trunk links. |
| Voice VLAN |
A voice VLAN port is an access port attached to a Cisco IP Phone, configured to use one VLAN for voice traffic and another VLAN for data traffic from a device attached to the phone. |
VTP is not required; it has no effect on a voice VLAN. |
VLAN Configuration Files
Configurations for VLAN IDs 1 to 1005 are written to the vlan.dat file (VLAN database), and you can display them by entering the show vlan privileged EXEC command. The vlan.dat file is stored in flash memory. If the VTP mode is transparent, they are also saved in the switch running configuration file.
In a switch stack, the whole stack uses the same vlan.dat file and running configuration. On some switches, the vlan.dat file is stored in flash memory on the active switch.
You use the interface configuration mode to define the port membership mode and to add and remove ports from VLANs. The results of these commands are written to the running-configuration file, and you can display the file by entering the show running-config privileged EXEC command.
When you save VLAN and VTP information (including extended-range VLAN configuration information) in the startup configuration file and reboot the switch, the switch configuration is selected as follows:
- If the VTP mode is transparent in the startup configuration, and the VLAN database and the VTP domain name from the VLAN database matches that in the startup configuration file, the VLAN database is ignored (cleared), and the VTP and VLAN configurations in the startup configuration file are used. The VLAN database revision number remains unchanged in the VLAN database.
- If the VTP mode or domain name in the startup configuration does not match the VLAN database, the domain name and VTP mode and configuration for the VLAN IDs 1 to 1005 use the VLAN database information.
- In VTP versions 1 and 2, if VTP mode is server, the domain name and VLAN configuration for VLAN IDs 1 to 1005 use the VLAN database information. VTP version 3 also supports VLANs 1006 to 4094.
Normal-Range VLAN Configuration Guidelines
Normal-range VLANs are VLANs with IDs from 1 to 1005.
Follow these guidelines when creating and modifying normal-range VLANs in your network:
- Normal-range VLANs are identified with a number between 1 and 1001. VLAN numbers 1002 through 1005 are reserved for Token Ring and FDDI VLANs.
- VLAN configurations for VLANs 1 to 1005 are always saved in the VLAN database. If the VTP mode is transparent, VTP and VLAN configurations are also saved in the switch running configuration file.
- If the switch is in VTP server or VTP transparent mode, you can add, modify or remove configurations for VLANs 2 to 1001 in the VLAN database. (VLAN IDs 1 and 1002 to 1005 are automatically created and cannot be removed.)
- Extended-range VLANs created in VTP transparent mode are not saved in the VLAN database and are not propagated. VTP version 3 supports extended range VLAN (VLANs 1006 to 4094) database propagation in VTP server mode.
- Before you can create a VLAN, the switch must be in VTP server mode or VTP transparent mode. If the switch is a VTP server, you must define a VTP domain or VTP will not function.
- The switch does not support Token Ring or FDDI media. The switch does not forward FDDI, FDDI-Net, TrCRF, or TrBRF traffic, but it does propagate the VLAN configuration through VTP.
- The switch supports 128 spanning tree instances. If a switch has more active VLANs than supported spanning-tree instances, spanning tree can be enabled on 128 VLANs and is disabled on the remaining VLANs. If you have already used all available spanning-tree instances on a switch, adding another VLAN anywhere in the VTP domain creates a VLAN on that switch that is not running spanning-tree. If you have the default allowed list on the trunk ports of that switch (which is to allow all VLANs), the new VLAN is carried on all trunk ports. Depending on the topology of the network, this could create a loop in the new VLAN that would not be broken, particularly if there are several adjacent switches that all have run out of spanning-tree instances. You can prevent this possibility by setting allowed lists on the trunk ports of switches that have used up their allocation of spanning-tree instances. If the number of VLANs on the switch exceeds the number of supported spanning-tree instances, we recommend that you configure the IEEE 802.1s Multiple STP (MSTP) on your switch to map multiple VLANs to a single spanning-tree instance.
- When a switch in a stack learns a new VLAN or deletes or modifies an existing VLAN (either through VTP over network ports or through the CLI), the VLAN information is communicated to all stack members.
- When a switch joins a stack or when stacks merge, VTP information (the vlan.dat file) on the new switches will be consistent with the active switch.
Extended-Range VLAN Configuration Guidelines
Extended-range VLANs are VLANs with IDs from 1006 to 4094.
Follow these guidelines when creating extended-range VLANs:
- VLAN IDs in the extended range are not saved in the VLAN database and are not recognized by VTP unless the switch is running VTP version 3.
- You cannot include extended-range VLANs in the pruning eligible range.
- For VTP version 1 or 2, you can set the VTP mode to transparent in global configuration mode. You should save this configuration to the startup configuration so that the switch boots up in VTP transparent mode. Otherwise, you lose the extended-range VLAN configuration if the switch resets. If you create extended-range VLANs in VTP version 3, you cannot convert to VTP version 1 or 2.
- . When the maximum number of spanning-tree instances are on the switch, spanning tree is disabled on any newly created VLANs. If the number of VLANs on the switch exceeds the maximum number of spanning-tree instances, we recommend that you configure the IEEE 802.1s Multiple STP (MSTP) on your switch to map multiple VLANs to a single spanning-tree instance.
- In a switch stack, the whole stack uses the same running configuration and saved configuration, and extended-range VLAN information is shared across the stack.
How to Configure VLANs
How to Configure Normal-Range VLANs
You can set these parameters when you create a new normal-range VLAN or modify an existing VLAN in the VLAN database:
- VLAN ID
- VLAN name
- VLAN type
- VLAN state (active or suspended)
- Maximum transmission unit (MTU) for the VLAN
- Security Association Identifier (SAID)
- Bridge identification number for TrBRF VLANs
- Ring number for FDDI and TrCRF VLANs
- Parent VLAN number for TrCRF VLANs
- Spanning Tree Protocol (STP) type for TrCRF VLANs
- VLAN number to use when translating from one VLAN type to another
You can cause inconsistency in the VLAN database if you attempt to manually delete the vlan.dat file. If you want to modify the VLAN configuration, follow the procedures in this section.
- Creating or Modifying an Ethernet VLAN (CLI)
- Deleting a VLAN (CLI)
- Assigning Static-Access Ports to a VLAN (CLI)
Creating or Modifying an Ethernet VLAN (CLI)
With VTP version 1 and 2, if the switch is in VTP transparent mode, you can assign VLAN IDs greater than 1006, but they are not added to the VLAN database.
The switch supports only Ethernet interfaces. Because FDDI and Token Ring VLANs are not locally supported, you only configure FDDI and Token Ring media-specific characteristics for VTP global advertisements to other switches.
Although the switch does not support Token Ring connections, a remote device with Token Ring connections could be managed from one of the supported switches. Switches running VTP Version 2 advertise information about these Token Ring VLANs:
2. vlan vlan-id
3. name vlan-name
4. media { ethernet | fd-net | fddi | tokenring | trn-net }
5. remote-span
7. show vlan {name vlan-name | id vlan-id}
DETAILED STEPS
Deleting a VLAN (CLI)
When you delete a VLAN from a switch that is in VTP server mode, the VLAN is removed from the VLAN database for all switches in the VTP domain. When you delete a VLAN from a switch that is in VTP transparent mode, the VLAN is deleted only on that specific switch or a switch stack.
You cannot delete the default VLANs for the different media types: Ethernet VLAN 1 and FDDI or Token Ring VLANs 1002 to 1005.
 Caution |
When you delete a VLAN, any ports assigned to that VLAN become inactive. They remain associated with the VLAN (and thus inactive) until you assign them to a new VLAN. |
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 |
configure terminal Example: Switch# configure terminal |
|
| Step 2 | no vlan vlan-id Example:
Switch(config)# no vlan 4
|
Removes the VLAN by entering the VLAN ID. |
| Step 3 |
end Example: Switch(config)# end |
|
| Step 4 | show vlan brief Example:
Switch# show vlan brief
|
Verifies the VLAN removal. |
Assigning Static-Access Ports to a VLAN (CLI)
You can assign a static-access port to a VLAN without having VTP globally propagate VLAN configuration information by disabling VTP (VTP transparent mode).
If you assign an interface to a VLAN that does not exist, the new VLAN is created.
1. configure terminal
2. interface interface-id
3. switchport mode access
4. switchport access vlan vlan-id
5. end
6. show running-config interface interface-id
7. show interfaces interface-id switchport
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | configure terminal Example:
Switch# configure terminal
|
Enters global configuration mode |
| Step 2 | interface interface-id Example:
Switch(config)# interface gigabitethernet2/0/1
|
Enters the interface to be added to the VLAN. |
| Step 3 | switchport mode access Example:
Switch(config-if)# switchport mode access
|
Defines the VLAN membership mode for the port (Layer 2 access port). |
| Step 4 | switchport access vlan vlan-id Example:
Switch(config-if)# switchport access vlan 2
|
Assigns the port to a VLAN. Valid VLAN IDs are 1 to 4094. |
| Step 5 | end Example:
Switch(config-if)# end
|
Returns to privileged EXEC mode. |
| Step 6 | show running-config interface interface-id Example:
Switch# show running-config interface gigabitethernet2/0/1
|
Verifies the VLAN membership mode of the interface. |
| Step 7 | show interfaces interface-id switchport Example:
Switch# show interfaces gigabitethernet2/0/1 switchport
|
Verifies your entries in the Administrative Mode and the Access Mode VLAN fields of the display. |
How to Configure Extended-Range VLANs
Extended-range VLANs enable service providers to extend their infrastructure to a greater number of customers. The extended-range VLAN IDs are allowed for any switchport commands that allow VLAN IDs.
With VTP version 1 or 2, extended-range VLAN configurations are not stored in the VLAN database, but because VTP mode is transparent, they are stored in the switch running configuration file, and you can save the configuration in the startup configuration file. Extended-range VLANs created in VTP version 3 are stored in the VLAN database.
You can change only the MTU size and the remote SPAN configuration state on extended-range VLANs; all other characteristics must remain at the default state.
Creating an Extended-Range VLAN (CLI)
2. vlan vlan-id
3. remote-span
4. exit
5. interface vlan
6. ip mtu mtu-size
8. show vlan id vlan-id
9. copy running-config startup config
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 |
configure terminal Example: Switch# configure terminal |
|||
| Step 2 | vlan vlan-id Example: Switch(config)# vlan 2000 Switch(config-vlan)# |
Enters an extended-range VLAN ID and enters VLAN configuration mode. The range is 1006 to 4094. |
||
| Step 3 | remote-span Example:
Switch(config-vlan)# remote-span
|
(Optional) Configures the VLAN as the RSPAN VLAN. |
||
| Step 4 | exit Example: Switch(config-vlan)# exit Switch(config)# |
Returns to configuration mode. |
||
| Step 5 | interface vlan Example: Switch(config)# interface vlan 200 Switch(config-if)# |
Enters the interface configuration mode for the selected VLAN. |
||
| Step 6 | ip mtu mtu-size Example: Switch(config-if)# ip mtu 1024 Switch(config-if)# |
(Optional) Modifies the VLAN by changing the MTU size. You can configure the MTU size between 68 to 1500 bytes.
|
||
| Step 7 |
end Example: Switch(config)# end |
|||
| Step 8 | show vlan id vlan-id Example:
Switch# show vlan id 2000
|
Verifies that the VLAN has been created. |
||
| Step 9 | copy running-config startup config Example:
Switch# copy running-config startup-config
|
Saves your entries in the switch startup configuration file. To save an extended-range VLAN configuration, you need to save the VTP transparent mode configuration and the extended-range VLAN configuration in the switch startup configuration file. Otherwise, if the switch resets, it will default to VTP server mode, and the extended-range VLAN IDs will not be saved.
|
How to Configure VLANs (GUI)
Creating Layer2 VLAN (GUI)
To create a Layer2 VLAN using the switch web UI, you must follow the steps defined in this procedure.
| Step 1 |
To create a Layer2 VLAN, choose The VLAN Layer2 page appears. You must provide values for all parameters listed in the Layer2 page.
|
||||||||
| Step 2 | Click Apply. |
Creating Layer3 Interface (GUI)
To create a Layer3 interface using the switch web UI, you must follow the steps defined in this procedure.
| Step 1 |
To create a Layer3 interface, choose The Layer3 interface page appears. You must provide values for all parameters listed in the window.
|
||||||||||||||||
| Step 2 | Click Apply. |
Viewing Layer2 VLAN (GUI)
You can view the details of the Layer2 VLANs configured in the switch interface using the web UI.
| Command or Action | Purpose | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Step 1 | Choose | The Layer2 VLAN page appears, listing the following details of the Layer2 VLANs in the switch.
|
Viewing Layer3 Interface (GUI)
You can view the details of the Layer3 interfaces configured in the switch interface using the web UI.
|
The Layer2 VLAN page appears, listing the following details of the Layer3 interfaces in the switch.
|
Removing Layer2 VLAN (GUI)
To remove a Layer2 VLANs using the switch web UI, you must:
| Step 1 |
Choose The Layer2 VLAN page appears, listing the following details of the Layer2 VLANs associated with the switch.
|
||||||||||
| Step 2 |
Check the checkbox of the Layer2 VLAN you need to delete from the Layer2 VLANs displayed in the Layer2 VLAN list . You will receive a confirmation message confirming deletion of the selected Layer2 VLAN. |
||||||||||
| Step 3 | Click Ok. |
Removing Layer3 Interface (GUI)
To remove a Layer3 interface using the switch web UI, you must:
| Step 1 |
Choose The Layer3 interface page appears, listing the following details of the Layer3 interfaces associated with the switch.
|
||||||||||
| Step 2 |
Check the checkbox of the Layer3 interfaces you need to delete from the Layer3 interfaces displayed in the Layer3 interfaces. You will receive a confirmation message confirming deletion of the selected Layer3 interface. |
||||||||||
| Step 3 | Click Ok. |
Monitoring VLANs
| Command |
Purpose |
|---|---|
| show interfaces [vlan vlan-id] |
Displays characteristics for all interfaces or for the specified VLAN configured on the switch . |
| show vlan [ access-map name | brief | dot1q { tag native } | filter [ access-map | vlan ] | group [ group-name name ] | id vlan-id | ifindex | mtu | name name | remote-span | summary ] |
Displays parameters for all VLANs or the specified VLAN on the switch. The following command options are available:
|
Where to Go Next
After configuring VLANs, you can configure the following:
Additional References
Related Documents
| Related Topic | Document Title |
|---|---|
| For complete syntax and usage information for the commands used in this chapter. |
|
| VLAN access-maps |
Security Configuration Guide (Catalyst 3850 Switches) Security Command Reference (Catalyst 3850 Switches) |
| VLAN and Mobility Agents |
Mobility Configuration Guide, Cisco IOS XE Release 3SE (Catalyst 3850 Switches) |
| Cisco Flexible NetFlow |
Cisco Flexible NetFlow Configuration Guide, Cisco IOS XE Release 3SE (Catalyst 3850 Switches) Flexible Netflow Configuration Guide, Cisco IOS XE Release 3SE (Catalyst 3850 Switches) |
| IGMP Snooping |
IP Multicast Routing Command Reference (Catalyst 3850 Switches) IP Multicast Routing Configuration Guide (Catalyst 3850 Switches) |
| IPv6 |
|
| SPAN |
Network Management Command Reference (Catalyst 3850 Switches) Network Management Configuration Guide (Catalyst 3850 Switches) |
| Platform-independent configuration information |
Identity Based Networking Services Configuration Guide, Cisco IOS XE Release 3SE (Catalyst 3850 Switches) |
Error Message Decoder
| Description | Link |
|---|---|
| To help you research and resolve system error messages in this release, use the Error Message Decoder tool. |
https://www.cisco.com/cgi-bin/Support/Errordecoder/index.cgi |
Standards and RFCs
| Standard/RFC | Title |
|---|---|
| RFC 1573 |
Evolution of the Interfaces Group of MIB-II |
| RFC 1757 |
Remote Network Monitoring Management |
| RFC 2021 |
SNMPv2 Management Information Base for the Transmission Control Protocol using SMIv2 |
MIBs
| MIB | MIBs Link |
|---|---|
| All supported MIBs for this release. |
To locate and download MIBs for selected platforms, Cisco IOS releases, and feature sets, use Cisco MIB Locator found at the following URL: |
Technical Assistance
| Description | Link |
|---|---|
| The Cisco Support website provides extensive online resources, including documentation and tools for troubleshooting and resolving technical issues with Cisco products and technologies. To receive security and technical information about your products, you can subscribe to various services, such as the Product Alert Tool (accessed from Field Notices), the Cisco Technical Services Newsletter, and Really Simple Syndication (RSS) Feeds. Access to most tools on the Cisco Support website requires a Cisco.com user ID and password. |
Feature History and Information for VLANs
Release |
Modification |
|---|---|
Cisco IOS XE 3.2SE |
This feature was introduced. |
Cisco IOS XE 3.3SE |
VLAN GUI support. |
 Feedback
Feedback