The standard IP
multicast infrastructure in the Internet and many enterprise intranets is based
on the PIM-SM protocol and Multicast Source Discovery Protocol (MSDP). These
protocols have proved to be reliable, extensive, and efficient. However, they
are bound to the complexity and functionality limitations of the Internet
Standard Multicast (ISM) service model. For example, with ISM, the network must
maintain knowledge about which hosts in the network are actively sending
multicast traffic. With SSM, this information is provided by receivers through
the source addresses relayed to the last-hop devices by IGMPv3. SSM is an
incremental response to the issues associated with ISM and is intended to
coexist in the network with the protocols developed for ISM. In general, SSM
provides IP multicast service for applications that utilize SSM.
ISM service is
described in RFC 1112. This service consists of the delivery of IP datagrams
from any source to a group of receivers called the multicast host group. The
datagram traffic for the multicast host group consists of datagrams with an
arbitrary IP unicast source address S and the multicast group address G as the
IP destination address. Systems will receive this traffic by becoming members
of the host group. Membership in a host group simply requires signaling the
host group through IGMP Version 1, 2, or 3.
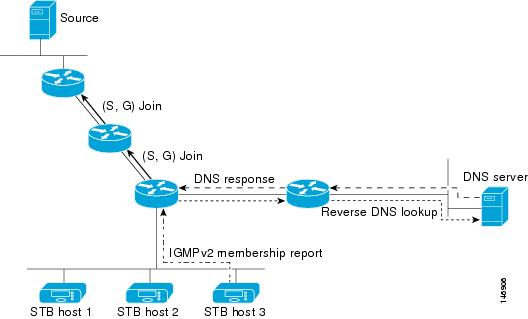
In SSM, delivery of
datagrams is based on (S, G) channels. Traffic for one (S, G) channel consists
of datagrams with an IP unicast source address S and the multicast group
address G as the IP destination address. Systems will receive this traffic by
becoming members of the (S, G) channel. In both SSM and ISM, no signaling is
required to become a source. However, in SSM, receivers must subscribe or
unsubscribe to (S, G) channels to receive or not receive traffic from specific
sources. In other words, receivers can receive traffic only from (S, G)
channels to which they are subscribed, whereas in ISM, receivers need not know
the IP addresses of sources from which they receive their traffic. The proposed
standard approach for channel subscription signaling utilizes IGMP INCLUDE mode
membership reports, which are supported only in IGMP Version 3.

 Feedback
Feedback