- Index
- Preface
- Overview
- Using the Command-Line Interface
- Assigning the Switch IP Address and Default Gateway
- Configuring Cisco IOS Configuration Engine
- Managing Switch Stacks
- Clustering Switches
- Administering the Switch
- Configuring SDM Templates
- Managing Catalyst 3750-X Stack Power
- Configuring Switch-Based Authentication
- Configuring IEEE 802.1x Port-Based Authentication
- Configuring Web-Based Authentication
- Configuring Interface Characteristics
- Configuring Auto Smartports Macros
- Configuring VLANs
- Configuring VTP
- Configuring Voice VLANs
- Configuring Private VLANs
- Configuring IEEE 802.1Q and Layer 2 Protocol Tunneling
- Configuring STP
- Configuring MSTP
- Configuring Optional Spanning-Tree Features
- Configuring Flex Links
- Configuring DHCP Features and IP Source Guard
- Configuring Dynamic ARP Inspection
- Configuring IGMP Snooping and MVR
- Configuring IPv6 MLD Snooping
- Configuring Port-Based Traffic Control
- Configuring CDP
- Configuring LLDP, LLDP-MED, and Wired Location Service
- Configuring UDLD
- Configuring SPAN and RSPAN
- Configuring RMON
- Configuring System Message Logging
- Configuring SNMP
- Configuring Embedded Event Manager
- Configuring Network Security with ACLs
- Configuring IPv6 ACLs
- Configuring QoS
- Configuring EtherChannels
- Configuring TelePresence E911 IP Phone Support
- Configuring IP Unicast Routing
- Configuring IPv6 Unicast Routing
- Configuring HSRP
- Configuring Cisco IOS IP SLAs Operations
- Configuring Enhanced Object Tracking
- Configuring WCCP
- Configuring IP Multicast Routing
- Configuring MSDP
- Configuring Fallback Bridging
- Troubleshooting
- Configuring Online Diagnostics
- Supported MIBs
- Working with the Cisco IOS File System, Configuration Files, and Software Images
- Unsupported Commands in Cisco IOS Release 12.2(53)SE
Catalyst 3750-X and 3560-X Switch Software Configuration Guide, Release 12.2(53)SE2
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- October 22, 2007
Chapter: Configuring MSDP
- Understanding MSDP
- Configuring MSDP
- Default MSDP Configuration
- Configuring a Default MSDP Peer
- Caching Source-Active State
- Requesting Source Information from an MSDP Peer
- Controlling Source Information that Your Switch Originates
- Controlling Source Information that Your Switch Forwards
- Controlling Source Information that Your Switch Receives
- Configuring an MSDP Mesh Group
- Shutting Down an MSDP Peer
- Including a Bordering PIM Dense-Mode Region in MSDP
- Configuring an Originating Address other than the RP Address
- Monitoring and Maintaining MSDP
Configuring MSDP
This chapter describes how to configure the Multicast Source Discovery Protocol (MSDP) on the Catalyst 3750-X or 3560-X switch. The MSDP connects multiple Protocol-Independent Multicast sparse-mode (PIM-SM) domains.
MSDP is not fully supported in this software release because of a lack of support for Multicast Border Gateway Protocol (MBGP), which works closely with MSDP. However, it is possible to create default peers that MSDP can operate with if MBGP is not running.
To use this feature, the switch or stack master must be running the IP services feature set. Unless otherwise noted, the term switch refers to a Catalyst 3750-X or 3560-X standalone switch and to a Catalyst 3750-X switch stack.

Note![]() For complete syntax and usage information for the commands used in this chapter, see the Cisco IOS IP Command Reference, Volume 3 of 3: Multicast, Release 12.2.
For complete syntax and usage information for the commands used in this chapter, see the Cisco IOS IP Command Reference, Volume 3 of 3: Multicast, Release 12.2.
Understanding MSDP
MSDP allows multicast sources for a group to be known to all rendezvous points (RPs) in different domains. Each PIM-SM domain uses its own RPs and does not depend on RPs in other domains. An RP runs MSDP over the Transmission Control Protocol (TCP) to discover multicast sources in other domains.
An RP in a PIM-SM domain has an MSDP peering relationship with MSDP-enabled devices in another domain. The peering relationship occurs over a TCP connection, primarily exchanging a list of sources sending to multicast groups. The TCP connections between RPs are achieved by the underlying routing system. The receiving RP uses the source lists to establish a source path.
The purpose of this topology is to have domains discover multicast sources in other domains. If the multicast sources are of interest to a domain that has receivers, multicast data is delivered over the normal, source-tree building mechanism in PIM-SM. MSDP is also used to announce sources sending to a group. These announcements must originate at the domain’s RP.
MSDP depends heavily on the Border Gateway Protocol (BGP) or MBGP for interdomain operation. We recommend that you run MSDP in RPs in your domain that are RPs for sources sending to global groups to be announced to the Internet.
MSDP Operation
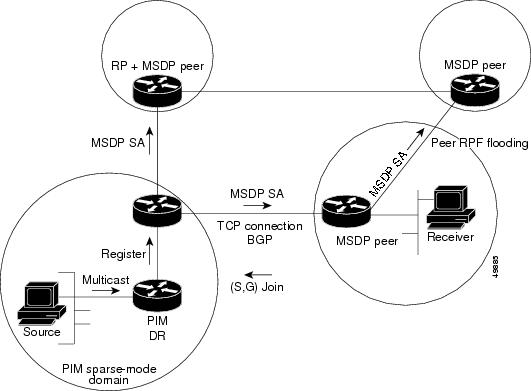
Figure 49-1 shows MSDP operating between two MSDP peers. PIM uses MSDP as the standard mechanism to register a source with the RP of a domain. When MSDP is configured, this sequence occurs.
When a source sends its first multicast packet, the first-hop router ( designated router or RP) directly connected to the source sends a PIM register message to the RP. The RP uses the register message to register the active source and to forward the multicast packet down the shared tree in the local domain. With MSDP configured, the RP also forwards a source-active (SA) message to all MSDP peers. The SA message identifies the source, the group the source is sending to, and the address of the RP or the originator ID (the IP address of the interface used as the RP address), if configured.
Each MSDP peer receives and forwards the SA message away from the originating RP to achieve peer reverse-path flooding (RPF). The MSDP device examines the BGP or MBGP routing table to discover which peer is the next hop toward the originating RP of the SA message. Such a peer is called an RPF peer (reverse-path forwarding peer). The MSDP device forwards the message to all MSDP peers other than the RPF peer. For information on how to configure an MSDP peer when BGP and MBGP are not supported, see the “Configuring a Default MSDP Peer” section.
If the MSDP peer receives the same SA message from a non-RPF peer toward the originating RP, it drops the message. Otherwise, it forwards the message to all its MSDP peers.
The RP for a domain receives the SA message from an MSDP peer. If the RP has any join requests for the group the SA message describes and if the (*,G) entry exists with a nonempty outgoing interface list, the domain is interested in the group, and the RP triggers an (S,G) join toward the source. After the (S,G) join reaches the source’s DR, a branch of the source tree has been built from the source to the RP in the remote domain. Multicast traffic can now flow from the source across the source tree to the RP and then down the shared tree in the remote domain to the receiver.
Figure 49-1 MSDP Running Between RP Peers
MSDP Benefits
- It breaks up the shared multicast distribution tree. You can make the shared tree local to your domain. Your local members join the local tree, and join messages for the shared tree never need to leave your domain.
- PIM sparse-mode domains can rely only on their own RPs, decreasing reliance on RPs in another domain. This increases security because you can prevent your sources from being known outside your domain.
- Domains with only receivers can receive data without globally advertising group membership.
- Global source multicast routing table state is not required, saving memory.
Configuring MSDP
- Default MSDP Configuration
- Configuring a Default MSDP Peer (required)
- Caching Source-Active State (optional)
- Requesting Source Information from an MSDP Peer (optional)
- Controlling Source Information that Your Switch Originates (optional)
- Controlling Source Information that Your Switch Forwards (optional)
- Controlling Source Information that Your Switch Receives (optional)
- Configuring an MSDP Mesh Group (optional)
- Shutting Down an MSDP Peer (optional)
- Including a Bordering PIM Dense-Mode Region in MSDP (optional)
- Configuring an Originating Address other than the RP Address (optional)
Default MSDP Configuration
Configuring a Default MSDP Peer
In this software release, because BGP and MBGP are not supported, you cannot configure an MSDP peer on the local switch by using the ip msdp peer global configuration command. Instead, you define a default MSDP peer (by using the ip msdp default-peer global configuration command) from which to accept all SA messages for the switch. The default MSDP peer must be a previously configured MSDP peer. Configure a default MSDP peer when the switch is not BGP- or MBGP-peering with an MSDP peer. If a single MSDP peer is configured, the switch always accepts all SA messages from that peer.
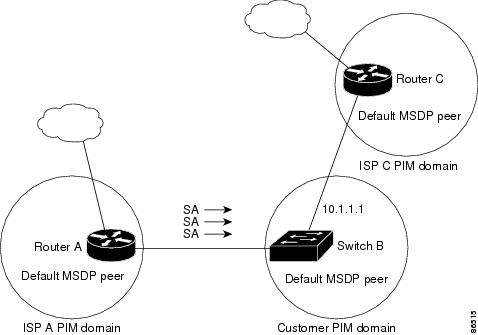
Figure 49-2 shows a network in which default MSDP peers might be used. In Figure 49-2, a customer who owns Switch B is connected to the Internet through two Internet service providers (ISPs), one owning Router A and the other owning Router C. They are not running BGP or MBGP between them. To learn about sources in the ISP’s domain or in other domains, Switch B at the customer site identifies Router A as its default MSDP peer. Switch B advertises SA messages to both Router A and Router C but accepts SA messages only from Router A or only from Router C. If Router A is first in the configuration file, it is used if it is running. If Router A is not running, only then does Switch B accept SA messages from Router C. This is the default behavior without a prefix list.
If you specify a prefix list, the peer is a default peer only for the prefixes in the list. You can have multiple active default peers when you have a prefix list associated with each. When you do not have any prefix lists, you can configure multiple default peers, but only the first one is the active default peer as long as the router has connectivity to this peer and the peer is alive. If the first configured peer fails or the connectivity to this peer fails, the second configured peer becomes the active default, and so on.
The ISP probably uses a prefix list to define which prefixes it accepts from the customer’s router.
Figure 49-2 Default MSDP Peer Network
Beginning in privileged EXEC mode, follow these steps to specify a default MSDP peer. This procedure is required.
To remove the default peer, use the no ip msdp default-peer ip-address | name global configuration command.
This example shows a partial configuration of Router A and Router C in Figure 49-2. Each of these ISPs have more than one customer (like the customer in Figure 49-2) who use default peering (no BGP or MBGP). In that case, they might have similar configurations. That is, they accept SAs only from a default peer if the SA is permitted by the corresponding prefix list.
Caching Source-Active State
By default, the switch does not cache source/group pairs from received SA messages. When the switch forwards the MSDP SA information, it does not store it in memory. Therefore, if a member joins a group soon after a SA message is received by the local RP, that member needs to wait until the next SA message to hear about the source. This delay is known as join latency.
If you want to sacrifice some memory in exchange for reducing the latency of the source information, you can configure the switch to cache SA messages.
Beginning in privileged EXEC mode, follow these steps to enable the caching of source/group pairs. This procedure is optional.

Note![]() An alternative to this command is the ip msdp sa-request global configuration command, which causes the switch to send an SA request message to the MSDP peer when a new member for a group becomes active. For more information, see the next section.
An alternative to this command is the ip msdp sa-request global configuration command, which causes the switch to send an SA request message to the MSDP peer when a new member for a group becomes active. For more information, see the next section.
To return to the default setting (no SA state is created), use the no ip msdp cache-sa-state global configuration command.
This example shows how to enable the cache state for all sources in 171.69.0.0/16 sending to groups 224.2.0.0/16:
Requesting Source Information from an MSDP Peer
Local RPs can send SA requests and get immediate responses for all active sources for a given group. By default, the switch does not send any SA request messages to its MSDP peers when a new member joins a group and wants to receive multicast traffic. The new member waits to receive the next periodic SA message.
If you want a new member of a group to learn the active multicast sources in a connected PIM sparse-mode domain that are sending to a group, configure the switch to send SA request messages to the specified MSDP peer when a new member joins a group. The peer replies with the information in its SA cache. If the peer does not have a cache configured, this command has no result. Configuring this feature reduces join latency but sacrifices memory.
Beginning in privileged EXEC mode, follow these steps to configure the switch to send SA request messages to the MSDP peer when a new member joins a group and wants to receive multicast traffic. This procedure is optional.
To return to the default setting, use the no ip msdp sa-request { ip-address | name } global configuration command.
This example shows how to configure the switch to send SA request messages to the MSDP peer at 171.69.1.1:
Controlling Source Information that Your Switch Originates
You can control the multicast source information that originates with your switch:
- Sources you advertise (based on your sources)
- Receivers of source information (based on knowing the requestor)
For more information, see the “Redistributing Sources” section and the “Filtering Source-Active Request Messages” section.
Redistributing Sources
SA messages originate on RPs to which sources have registered. By default, any source that registers with an RP is advertised. The A flag is set in the RP when a source is registered, which means the source is advertised in an SA unless it is filtered.
Beginning in privileged EXEC mode, follow these steps to further restrict which registered sources are advertised. This procedure is optional.
To remove the filter, use the no ip msdp redistribute global configuration command.
Filtering Source-Active Request Messages
By default, only switches that are caching SA information can respond to SA requests. By default, such a switch honors all SA request messages from its MSDP peers and supplies the IP addresses of the active sources.
However, you can configure the switch to ignore all SA requests from an MSDP peer. You can also honor only those SA request messages from a peer for groups described by a standard access list. If the groups in the access list pass, SA request messages are accepted. All other such messages from the peer for other groups are ignored.
Beginning in privileged EXEC mode, follow these steps to configure one of these options. This procedure is optional.
To return to the default setting, use the no ip msdp filter-sa-request { ip-address | name } global configuration command.
This example shows how to configure the switch to filter SA request messages from the MSDP peer at 171.69.2.2. SA request messages from sources on network 192.4.22.0 pass access list 1 and are accepted; all others are ignored.
Controlling Source Information that Your Switch Forwards
By default, the switch forwards all SA messages it receives to all its MSDP peers. However, you can prevent outgoing messages from being forwarded to a peer by using a filter or by setting a time-to-live (TTL) value. These methods are described in the next sections.
Using a Filter
By creating a filter, you can perform one of these actions:
- Filter all source/group pairs
- Specify an IP extended access list to pass only certain source/group pairs
- Filter based on match criteria in a route map
Beginning in privileged EXEC mode, follow these steps to apply a filter. This procedure is optional.
To remove the filter, use the no ip msdp sa-filter out { ip-address | name } [ list access-list-number ] [ route-map map-tag ] global configuration command.
This example shows how to allow only (S,G) pairs that pass access list 100 to be forwarded in an SA message to the peer named switch.cisco.com :
Using TTL to Limit the Multicast Data Sent in SA Messages
You can use a TTL value to control what data is encapsulated in the first SA message for every source. Only multicast packets with an IP-header TTL greater than or equal to the ttl argument are sent to the specified MSDP peer. For example, you can limit internal traffic to a TTL of 8. If you want other groups to go to external locations, you must send those packets with a TTL greater than 8.
Beginning in privileged EXEC mode, follow these steps to establish a TTL threshold. This procedure is optional.
|
|
|
|
|---|---|---|
Limit which multicast data is encapsulated in the first SA message to the specified MSDP peer. |
||
To return to the default setting, use the no ip msdp ttl-threshold { ip-address | name } global configuration command.
Controlling Source Information that Your Switch Receives
By default, the switch receives all SA messages that its MSDP RPF peers send to it. However, you can control the source information that you receive from MSDP peers by filtering incoming SA messages. In other words, you can configure the switch to not accept them.
You can perform one of these actions:
- Filter all incoming SA messages from an MSDP peer
- Specify an IP extended access list to pass certain source/group pairs
- Filter based on match criteria in a route map
Beginning in privileged EXEC mode, follow these steps to apply a filter. This procedure is optional.
To remove the filter, use the no ip msdp sa-filter in { ip-address | name } [ list access-list-number ] [ route-map map-tag ] global configuration command.
This example shows how to filter all SA messages from the peer named switch.cisco.com :
Configuring an MSDP Mesh Group
An MSDP mesh group is a group of MSDP speakers that have fully meshed MSDP connectivity among one another. Any SA messages received from a peer in a mesh group are not forwarded to other peers in the same mesh group. Thus, you reduce SA message flooding and simplify peer-RPF flooding. Use the ip msdp mesh-group global configuration command when there are multiple RPs within a domain. It is especially used to send SA messages across a domain. You can configure multiple mesh groups (with different names) in a single switch.
Beginning in privileged EXEC mode, follow these steps to create a mesh group. This procedure is optional.
|
|
|
|
|---|---|---|
Configure an MSDP mesh group, and specify the MSDP peer belonging to that mesh group. |
||
To remove an MSDP peer from a mesh group, use the no ip msdp mesh-group name { ip-address | name } global configuration command.
Shutting Down an MSDP Peer
If you want to configure many MSDP commands for the same peer and you do not want the peer to become active, you can shut down the peer, configure it, and later bring it up. When a peer is shut down, the TCP connection is terminated and is not restarted. You can also shut down an MSDP session without losing configuration information for the peer.
Beginning in privileged EXEC mode, follow these steps to shut down a peer. This procedure is optional.
|
|
|
|
|---|---|---|
Administratively shut down the specified MSDP peer without losing configuration information. For peer-name | peer address, enter the IP address or name of the MSDP peer to shut down. |
||
To bring the peer back up, use the no ip msdp shutdown { peer-name | peer address } global configuration command. The TCP connection is reestablished
Including a Bordering PIM Dense-Mode Region in MSDP
You can configure MSDP on a switch that borders a PIM sparse-mode region with a dense-mode region. By default, active sources in the dense-mode region do not participate in MSDP.

Note![]() We do not recommend using the ip msdp border sa-address global configuration command. It is better to configure the border router in the sparse-mode domain to proxy-register sources in the dense-mode domain to the RP of the sparse-mode domain and have the sparse-mode domain use standard MSDP procedures to advertise these sources.
We do not recommend using the ip msdp border sa-address global configuration command. It is better to configure the border router in the sparse-mode domain to proxy-register sources in the dense-mode domain to the RP of the sparse-mode domain and have the sparse-mode domain use standard MSDP procedures to advertise these sources.
Beginning in privileged EXEC mode, follow these steps to configure the border router to send SA messages for sources active in the dense-mode region to the MSDP peers. This procedure is optional.
|
|
|
|
|---|---|---|
Configure the switch on the border between a dense-mode and sparse-mode region to send SA messages about active sources in the dense-mode region. For interface-id, specify the interface from which the IP address is derived and used as the RP address in SA messages. The IP address of the interface is used as the Originator-ID, which is the RP field in the SA message. |
||
ip msdp redistribute [ list access-list-name ] [ asn aspath-access-list-number ] [ route-map map ] |
Configure which (S,G) entries from the multicast routing table are advertised in SA messages. For more information, see the “Redistributing Sources” section. |
|
Note that the ip msdp originator-id global configuration command also identifies an interface to be used as the RP address. If both the ip msdp border sa-address and the ip msdp originator-id global configuration commands are configured, the address derived from the ip msdp originator-id command specifies the RP address.
To return to the default setting (active sources in the dense-mode region do not participate in MSDP), use the no ip msdp border sa-address interface-id global configuration command.
Configuring an Originating Address other than the RP Address
You can allow an MSDP speaker that originates an SA message to use the IP address of the interface as the RP address in the SA message by changing the Originator ID. You might change the Originator ID in one of these cases:
- If you configure a logical RP on multiple switches in an MSDP mesh group.
- If you have a switch that borders a PIM sparse-mode domain and a dense-mode domain. If a switch borders a dense-mode domain for a site, and sparse-mode is being used externally, you might want dense-mode sources to be known to the outside world. Because this switch is not an RP, it would not have an RP address to use in an SA message. Therefore, this command provides the RP address by specifying the address of the interface.
Beginning in privileged EXEC mode, follow these steps to allow an MSDP speaker that originates an SA message to use the IP address on the interface as the RP address in the SA message. This procedure is optional.
|
|
|
|
|---|---|---|
Configures the RP address in SA messages to be the address of the originating device interface. For interface-id, specify the interface on the local switch. |
||
If both the ip msdp border sa-address and the ip msdp originator-id global configuration commands are configured, the address derived from the ip msdp originator-id command specifies the address of the RP.
To prevent the RP address from being derived in this way, use the no ip msdp originator-id interface-id global configuration command.
Monitoring and Maintaining MSDP
To monitor MSDP SA messages, peers, state, or peer status, use one or more of the privileged EXEC commands in Table 49-1 :
To clear MSDP connections, statistics, or SA cache entries, use the privileged EXEC commands in Table 49-2 :
 Feedback
Feedback