- Index
- Preface
- Overview
- Using the Command-Line Interface
- Assigning the Switch IP Address and Default Gateway
- Configuring Cisco EnergyWise
- Configuring Cisco IOS Configuration Engine
- Clustering Switches
- Administering the Switch
- Configuring SDM Templates
- Configuring Switch-Based Authentication
- Configuring IEEE 802.1x Port-Based Authentication
- Configuring Interface Characteristics
- Configuring Auto Smartports Macros
- Configuring VLANs
- Configuring VTP
- Configuring Voice VLAN
- Configuring STP
- Configuring MSTP
- Configuring Optional Spanning-Tree Features
- Configuring Flex Links and the MAC Address-Table Move Update Feature
- Configuring DHCP Features and IP Source Guard
- Configuring Dynamic ARP Inspection
- Configuring IGMP Snooping and MVR
- Configuring Port-Based Traffic Control
- Configuring UDLD
- Configuring CDP
- Configuring LLDP, LLDP-MED, and Wired Location Service
- Configuring SPAN and RSPAN
- Configuring RMON
- Configuring System Message Logging
- Configuring SNMP
- Configuring Network Security with ACLs
- Configuring Cisco IOS IP SLAs Operations
- Configuring QoS
- Configuring IPv6 Unicast Routing
- Configuring IPv6 MLD Snooping
- Configuring EtherChannels and Link-State Tracking
- Troubleshooting
- Supported MIBs
- Working with the Cisco IOS File System, Configuration Files, and Software Images
- Recommendations for Upgrading a Catalyst 2950 Switch to a Catalyst 2960 Switch
- Unsupported Commands in Cisco IOS Release 12.2(50)SE
Catalyst 2960 Switch Software Configuration Guide, Rel. 12.2(50)SE
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- August 27, 2008
Chapter: Configuring Cisco IOS IP SLAs Operations
Configuring Cisco IOS IP SLAs Operations

Note ![]() To use Cisco IOS IP Service Level Agreements (SLAs), the switch must be running the LAN Base image.
To use Cisco IOS IP Service Level Agreements (SLAs), the switch must be running the LAN Base image.
This chapter describes how to use Cisco IOS IP Service Level Agreements (SLAs) on the Catalyst 2960 switch. Cisco IP SLAs is a part of Cisco IOS software that allows Cisco customers to analyze IP service levels for IP applications and services by using active traffic monitoring—the generation of traffic in a continuous, reliable, and predictable manner—for measuring network performance. With Cisco IOS IP SLAs, service provider customers can measure and provide service level agreements, and enterprise customers can verify service levels, verify outsourced service level agreements, and understand network performance. Cisco IOS IP SLAs can perform network assessments, verify quality of service (QoS), ease the deployment of new services, and assist with network troubleshooting.

Note ![]() The switch supports only IP SLAs responder functionality and must be configured with another device that supports full IP SLAs functionality.
The switch supports only IP SLAs responder functionality and must be configured with another device that supports full IP SLAs functionality.
For more information about IP SLAs, see the Cisco IOS IP SLAs Configuration Guide, Release 12.4T at this URL:
http://www.cisco.com/en/US/docs/ios/ipsla/configuration/guide/12_4t/sla_12_4t_book.html
For command syntax information, see the command reference at this URL:
http://www.cisco.com/en/US/docs/ios/ipsla/command/reference/sla_book.html
This chapter consists of these sections:
•![]() Understanding Cisco IOS IP SLAs
Understanding Cisco IOS IP SLAs
•![]() Configuring IP SLAs Operations
Configuring IP SLAs Operations
•![]() Monitoring IP SLAs Operations
Monitoring IP SLAs Operations
Understanding Cisco IOS IP SLAs
Cisco IOS IP SLAs sends data across the network to measure performance between multiple network locations or across multiple network paths. It simulates network data and IP services and collects network performance information in real time. Cisco IOS IP SLAs generates and analyzes traffic either between Cisco IOS devices or from a Cisco IOS device to a remote IP device such as a network application server. Measurements provided by the various Cisco IOS IP SLAs operations can be used for troubleshooting, for problem analysis, and for designing network topologies.
Depending on the specific Cisco IOS IP SLAs operation, various network performance statistics are monitored within the Cisco device and stored in both command-line interface (CLI) and Simple Network Management Protocol (SNMP) MIBs. IP SLAs packets have configurable IP and application layer options such as source and destination IP address, User Datagram Protocol (UDP)/TCP port numbers, a type of service (ToS) byte (including Differentiated Services Code Point [DSCP] and IP Prefix bits), Virtual Private Network (VPN) routing/forwarding instance (VRF), and URL web address.
Because Cisco IP SLAs is Layer 2 transport independent, you can configure end-to-end operations over disparate networks to best reflect the metrics that an end user is likely to experience. IP SLAs collects a unique subset of these performance metrics:
•![]() Delay (both round-trip and one-way)
Delay (both round-trip and one-way)
•![]() Jitter (directional)
Jitter (directional)
•![]() Packet loss (directional)
Packet loss (directional)
•![]() Packet sequencing (packet ordering)
Packet sequencing (packet ordering)
•![]() Path (per hop)
Path (per hop)
•![]() Connectivity (directional)
Connectivity (directional)
•![]() Server or website download time
Server or website download time
Because Cisco IOS IP SLAs is SNMP-accessible, it can also be used by performance-monitoring applications like CiscoWorks Internetwork Performance Monitor (IPM) and other third-party Cisco partner performance management products. You can find more details about network management products that use Cisco IOS IP SLAs at this URL:
http://www.cisco.com/go/ipsla
Using IP SLAs can provide these benefits:
•![]() Service-level agreement monitoring, measurement, and verification.
Service-level agreement monitoring, measurement, and verification.
•![]() Network performance monitoring
Network performance monitoring
–![]() Measures the jitter, latency, or packet loss in the network.
Measures the jitter, latency, or packet loss in the network.
–![]() Provides continuous, reliable, and predictable measurements.
Provides continuous, reliable, and predictable measurements.
•![]() IP service network health assessment to verify that the existing QoS is sufficient for new IP services.
IP service network health assessment to verify that the existing QoS is sufficient for new IP services.
•![]() Edge-to-edge network availability monitoring for proactive verification and connectivity testing of network resources (for example, shows the network availability of an NFS server used to store business critical data from a remote site).
Edge-to-edge network availability monitoring for proactive verification and connectivity testing of network resources (for example, shows the network availability of an NFS server used to store business critical data from a remote site).
•![]() Troubleshooting of network operation by providing consistent, reliable measurement that immediately identifies problems and saves troubleshooting time.
Troubleshooting of network operation by providing consistent, reliable measurement that immediately identifies problems and saves troubleshooting time.
•![]() Multiprotocol Label Switching (MPLS) performance monitoring and network verification (if the switch supports MPLS)
Multiprotocol Label Switching (MPLS) performance monitoring and network verification (if the switch supports MPLS)
This section includes this information about IP SLAs functionality:
•![]() Using Cisco IOS IP SLAs to Measure Network Performance
Using Cisco IOS IP SLAs to Measure Network Performance
•![]() IP SLAs Responder and IP SLAs Control Protocol
IP SLAs Responder and IP SLAs Control Protocol
•![]() Response Time Computation for IP SLAs
Response Time Computation for IP SLAs
Using Cisco IOS IP SLAs to Measure Network Performance
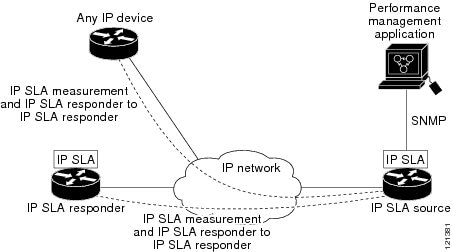
You can use IP SLAs to monitor the performance between any area in the network—core, distribution, and edge—without deploying a physical probe. It uses generated traffic to measure network performance between two networking devices. Figure 31-1 shows how IP SLAs begins when the source device sends a generated packet to the destination device. After the destination device receives the packet, depending on the type of IP SLAs operation, it responds with time-stamp information for the source to make the calculation on performance metrics. An IP SLAs operation performs a network measurement from the source device to a destination in the network using a specific protocol such as UDP.
Figure 31-1 Cisco IOS IP SLAs Operation
To implement IP SLAs network performance measurement, you need to perform these tasks:
1. ![]() Enable the IP SLAs responder, if required.
Enable the IP SLAs responder, if required.
2. ![]() Configure the required IP SLAs operation type.
Configure the required IP SLAs operation type.
3. ![]() Configure any options available for the specified operation type.
Configure any options available for the specified operation type.
4. ![]() Configure threshold conditions, if required.
Configure threshold conditions, if required.
5. ![]() Schedule the operation to run, then let the operation run for a period of time to gather statistics.
Schedule the operation to run, then let the operation run for a period of time to gather statistics.
6. ![]() Display and interpret the results of the operation using the Cisco IOS CLI or a network management system (NMS) system with SNMP.
Display and interpret the results of the operation using the Cisco IOS CLI or a network management system (NMS) system with SNMP.
For more information about IP SLAs operations, see the operation-specific chapters in the Cisco IOS IP SLAs Configuration Guide at this URL:
http://www.cisco.com/en/US/docs/ios/ipsla/configuration/guide/12_4t/sla_12_4t_book.html

Note ![]() The switch does not support Voice over IP (VoIP) service levels using the gatekeeper registration delay operations measurements. Before configuring any IP SLAs application, you can use the show ip sla application privileged EXEC command to verify that the operation type is supported on your software image.
The switch does not support Voice over IP (VoIP) service levels using the gatekeeper registration delay operations measurements. Before configuring any IP SLAs application, you can use the show ip sla application privileged EXEC command to verify that the operation type is supported on your software image.
IP SLAs Responder and IP SLAs Control Protocol
The IP SLAs responder is a component embedded in the destination Cisco device that allows the system to anticipate and respond to IP SLAs request packets. The responder provides accurate measurements without the need for dedicated probes. The responder uses the Cisco IOS IP SLAs Control Protocol to provide a mechanism through which it can be notified on which port it should listen and respond. Only a Cisco IOS device can be a source for a destination IP SLAs Responder.

Note ![]() The IP SLAs responder can be a Cisco IOS Layer 2, responder-configurable switch, such as a Catalyst 2960, or a Cisco ME 2400 or IE 3000 switch, or a Catalyst 3560 or 3750 switch running the IP base image. The responder does not need to support full IP SLAs functionality.
The IP SLAs responder can be a Cisco IOS Layer 2, responder-configurable switch, such as a Catalyst 2960, or a Cisco ME 2400 or IE 3000 switch, or a Catalyst 3560 or 3750 switch running the IP base image. The responder does not need to support full IP SLAs functionality.
Figure 31-1 shows where the Cisco IOS IP SLAs responder fits in the IP network. The responder listens on a specific port for control protocol messages sent by an IP SLAs operation. Upon receipt of the control message, it enables the specified UDP or TCP port for the specified duration. During this time, the responder accepts the requests and responds to them. It disables the port after it responds to the IP SLAs packet, or when the specified time expires. MD5 authentication for control messages is available for added security.
You do not need to enable the responder on the destination device for all IP SLAs operations. For example, a responder is not required for services that are already provided by the destination router (such as Telnet or HTTP). You cannot configure the IP SLAs responder on non-Cisco devices and Cisco IOS IP SLAs can send operational packets only to services native to those devices.
Response Time Computation for IP SLAs
Switches and routers can take tens of milliseconds to process incoming packets due to other high priority processes. This delay affects the response times because the test-packet reply might be in a queue while waiting to be processed. In this situation, the response times would not accurately represent true network delays. IP SLAs minimizes these processing delays on the source device as well as on the target device (if the responder is being used) to determine true round-trip times. IP SLAs test packets use time stamping to minimize the processing delays.
When the IP SLAs responder is enabled, it allows the target device to take time stamps when the packet arrives on the interface at interrupt level and again just as it is leaving, eliminating the processing time. This time stamping is made with a granularity of sub-milliseconds (ms).
Figure 31-2 demonstrates how the responder works. Four time stamps are taken to make the calculation for round-trip time. At the target router, with the responder functionality enabled, time stamp 2 (TS2) is subtracted from time stamp 3 (TS3) to produce the time spent processing the test packet as represented by delta. This delta value is then subtracted from the overall round-trip time. Notice that the same principle is applied by IP SLAs on the source router where the incoming time stamp 4 (TS4) is also taken at the interrupt level to allow for greater accuracy.
Figure 31-2 Cisco IOS IP SLAs Responder Time Stamping
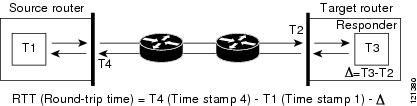
An additional benefit of the two time stamps at the target device is the ability to track one-way delay, jitter, and directional packet loss. Because much network behavior is asynchronous, it is critical to have these statistics. However, to capture one-way delay measurements, you must configure both the source router and target router with Network Time Protocol (NTP) so that the source and target are synchronized to the same clock source. One-way jitter measurements do not require clock synchronization.
Configuring IP SLAs Operations
This section does not include configuration information for all available operations as the configuration information details are included in the Cisco IOS IP SLAs Configuration Guide. It includes only the procedure for configuring the responder, as the switch includes only responder support.
For details about configuring other operations, see he Cisco IOS IP SLAs Configuration Guide at this URL:
http://www.cisco.com/en/US/docs/ios/ipsla/configuration/guide/12_4t/sla_12_4t_book.html
This section includes this information:
•![]() Configuring the IP SLAs Responder
Configuring the IP SLAs Responder
Default Configuration
No IP SLAs operations are configured.
Configuration Guidelines
For information on the IP SLAs commands, see the Cisco IOS IP SLAs Command Reference, Release 12.4T command reference at this URL:
http://www.cisco.com/en/US/docs/ios/ipsla/command/reference/sla_book.html
For detailed descriptions and configuration procedures, see the Cisco IOS IP SLAs Configuration Guide, Release 12.4T at this URL:
http://www.cisco.com/en/US/docs/ios/ipsla/configuration/guide/12_4t/sla_12_4t_book.html
Configuring the IP SLAs Responder
The IP SLAs responder is available only on Cisco IOS software-based devices, including some Layer 2 switches that do not support full IP SLAs functionality, such as the Catalyst 2960 or the Cisco ME 2400 or IE 3000 switch. Beginning in privileged EXEC mode, follow these steps to configure the IP SLAs responder on the target device (the operational target):
To disable the IP SLAs responder, enter the no ip sla responder global configuration command. This example shows how to configure the device as a responder for the UDP jitter IP SLAs operation in the next procedure:
Switch(config)# ip sla responder udp-echo 172.29.139.134 5000

Note ![]() For the IP SLAs responder to function, you must also configure a source device, such as a Catalyst 3750 or Catalyst 3560 switch running the IP services image, that has full IP SLAs support. Refer to the documentation for the source device for configuration information.
For the IP SLAs responder to function, you must also configure a source device, such as a Catalyst 3750 or Catalyst 3560 switch running the IP services image, that has full IP SLAs support. Refer to the documentation for the source device for configuration information.
Monitoring IP SLAs Operations
Use the User EXEC or Privileged EXEC commands in Table 31-1 to display IP SLAs operations configuration.
|
|
|
|---|---|
show ip sla authentication |
Display IP SLAs authentication information. |
show ip sla responder |
Display information about the IP SLAs responder. |
 Feedback
Feedback