- Index
- Preface
- Overview
- Part 1
- Quick Start Guide for Cisco Virtual Security Gateway and Cisco Virtual Network Management Center
- Part 2
- Installing the Cisco Virtual Security Gateway
- Part 3
- Installing the Cisco Virtual Network Management Center
- Registering Devices with the Cisco VNMC
- Part 4
- Installing the Cisco Virtual Security Gateway on a Cisco Nexus 1010 Appliance
- Part 5
- Upgrading the Cisco Virtual Security Gateway and Cisco Virtual Network Management Center
- Examples of Cisco VNMC OVA Template Deployment and Cisco VNMC ISO Installations
Cisco Virtual Security Gateway, Rel. 4.2(1)VSG1(3.1) and Cisco Virtual Network Management Center, Rel. 1.3 Installation and Upgrade Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- January 31, 2012
Chapter: Upgrading the Cisco Virtual Security Gateway and Cisco Virtual Network Management Center
- Information About Cisco VSG Upgrades
- Information About Cisco VNMC Upgrades
- Complete Upgrade Procedure
- Mixed Version Upgrade Procedure
Upgrading the Cisco Virtual Security Gateway and Cisco Virtual Network Management Center
This chapter describes how to install and complete an upgrade for the Cisco Virtual Security Gateway (VSG) and the Cisco Virtual Network Management Center (VNMC).
This chapter includes the following sections:
•![]() Information About Cisco VSG Upgrades
Information About Cisco VSG Upgrades
•![]() Information About Cisco VNMC Upgrades
Information About Cisco VNMC Upgrades
•![]() Mixed Version Upgrade Procedure
Mixed Version Upgrade Procedure
•![]() Stage 1: Upgrading Cisco VNMC
Stage 1: Upgrading Cisco VNMC
•![]() Stage 2: Upgrading a Cisco VSG Pair
Stage 2: Upgrading a Cisco VSG Pair
•![]() Stage 3: Upgrading the VSM Pair and the VEM
Stage 3: Upgrading the VSM Pair and the VEM
Information About Cisco VSG Upgrades
The upgrade procedure for a standalone Cisco VSG is hitful, which means that you must manually reload the Cisco VSG for the new image to become effective. In HA mode, the upgrade is hitless, which means that the standby Cisco VSG is upgraded first and then after a switchover, the previously active Cisco VSG is upgraded.
Because license information is not stored with the Cisco VSG but is maintained between the Virtual Supervisor Module (VSM) and Virtual Ethernet Module (VEM), if packets are received at the Cisco VSG, that means that the license is valid and the packets are processed.
An upgrade affects two bin files: the kickstart file and the system file.
An upgrade does not erase any of the existing information. When the Cisco VSG comes online, everything is as is. Because the Cisco VSG is stateless, it gets all this information from the Cisco VNMC at bootup.
Information About Cisco VNMC Upgrades
When you upgrade the Cisco VNMC software, all current (command-line interface) CLI and (graphical user interface) GUI sessions are interrupted, which means that you must restart any CLI or GUI sessions.
Complete Upgrade Procedure
When you need to upgrade the Cisco VNMC, Cisco VSG, and Cisco Nexus 1000V, follow these steps:
1. ![]() Stage 1: Upgrading Cisco VNMC
Stage 1: Upgrading Cisco VNMC
2. ![]() Stage 2: Upgrading a Cisco VSG Pair
Stage 2: Upgrading a Cisco VSG Pair
3. ![]() Stage 3: Upgrading the VSM Pair and the VEM
Stage 3: Upgrading the VSM Pair and the VEM

Note ![]() We highly recommend that you upgrade the Cisco VSG and the Cisco VNMC in the order provided. Any deviation from the ordered steps could cause disruption of your connectivity and data communication.
We highly recommend that you upgrade the Cisco VSG and the Cisco VNMC in the order provided. Any deviation from the ordered steps could cause disruption of your connectivity and data communication.
The Cisco VNMC must be upgraded with the corresponding policy agent (PA)
For a full In-service Software Upgrade (ISSU) upgrade on both the Cisco VSG and VSM, follow these rules:
•![]() Install the Cisco VNMC before installing the Cisco VSG and VSM. The ISSU upgrade installs a new PA.
Install the Cisco VNMC before installing the Cisco VSG and VSM. The ISSU upgrade installs a new PA.
•![]() A new PA with an old Cisco VNMC is not supported and there should never be an interim stage in this state.
A new PA with an old Cisco VNMC is not supported and there should never be an interim stage in this state.
•![]() A copy run start is not required after the VSM upgrade.
A copy run start is not required after the VSM upgrade.

Note ![]() You should take a snapshot or backup (clone) of the original VNMC and VSM prior to the upgrade process. We recommend that you perform an ISSU upgrade process on both the VSM and the Cisco VSG. We do not recommend that you perform a manual upgrade.
You should take a snapshot or backup (clone) of the original VNMC and VSM prior to the upgrade process. We recommend that you perform an ISSU upgrade process on both the VSM and the Cisco VSG. We do not recommend that you perform a manual upgrade.
Table 7-1 provides the following information:
•![]() Different stages of complete upgrade procedures and operations which are supported at different stages.
Different stages of complete upgrade procedures and operations which are supported at different stages.
•![]() Different component versions after each stage.
Different component versions after each stage.
•![]() Different operations supported after each stage.
Different operations supported after each stage.
All the tests are performed on the Cisco VMware vCenter 5.0.
Mixed Version Upgrade Procedure
This section describes the different software version combinations supported and the upgrade process associated with these combinations.
The two software version combination supported are as follows:
1. ![]() Upgrade only the Cisco VNMC and the Cisco VSG to 4.2(1)VSG1(3.1) without upgrading the VSM and VEM. The VSM PA should remain on 1.2(1b). The Cisco VSG PA must be upgraded to 1.3(1c).
Upgrade only the Cisco VNMC and the Cisco VSG to 4.2(1)VSG1(3.1) without upgrading the VSM and VEM. The VSM PA should remain on 1.2(1b). The Cisco VSG PA must be upgraded to 1.3(1c).
To upgrade this combination, follow these steps:
a. ![]() Stage 1: Upgrading Cisco VNMC
Stage 1: Upgrading Cisco VNMC
b. ![]() Stage 2: Upgrading a Cisco VSG Pair
Stage 2: Upgrading a Cisco VSG Pair
2. ![]() Upgrade only the Cisco VNMC, VSM Pair and VEM to 4.2(1)SV1(5.1) without upgrading the Cisco VSG. The VSM PA must be upgraded to 1.3(1c). The Cisco VSG PA must remain on 1.2(1b).
Upgrade only the Cisco VNMC, VSM Pair and VEM to 4.2(1)SV1(5.1) without upgrading the Cisco VSG. The VSM PA must be upgraded to 1.3(1c). The Cisco VSG PA must remain on 1.2(1b).
To upgrade this combination of software, follow these steps:
a. ![]() Stage 1: Upgrading Cisco VNMC
Stage 1: Upgrading Cisco VNMC
b. ![]() Stage 3: Upgrading the VSM Pair and the VEM
Stage 3: Upgrading the VSM Pair and the VEM
Restricted Operations
•![]() The Cisco VSG in the Layer 3 mode is not supported.
The Cisco VSG in the Layer 3 mode is not supported.
•![]() The Virtual Extensible Local Area Network (VXLAN) is not supported.
The Virtual Extensible Local Area Network (VXLAN) is not supported.
Stage 1: Upgrading Cisco VNMC
This section describes how to upgrade the Cisco VNMC.
BEFORE YOU BEGIN
Before starting the procedure, you must know or do the following:
•![]() You are logged in as admin to the CLI in EXEC mode.
You are logged in as admin to the CLI in EXEC mode.
•![]() You have already copied the new software files into the bootflash file system.
You have already copied the new software files into the bootflash file system.
•![]() You must have the Cisco VNMC Release 1.3 installed.
You must have the Cisco VNMC Release 1.3 installed.
SUMMARY STEPS
1. ![]() connect local-mgmt
connect local-mgmt
2. ![]() (Optional) show version
(Optional) show version
3. ![]() copy scp://user@example-server-ip/example-dir/filename bootflash:/
copy scp://user@example-server-ip/example-dir/filename bootflash:/
4. ![]() dir bootflash:/
dir bootflash:/
5. ![]() update bootflash:/filename
update bootflash:/filename
6. ![]() (Optional) show version
(Optional) show version
DETAILED STEPS
EXAMPLES
This example shows how to connect to the local-mgmt mode:
vnmc# connect local-mgmt
Cisco Virtual Network Management Center
TAC support: http://www.cisco.com/tac
Copyright (c) 2002-2011, Cisco Systems, Inc. All rights reserved.
The copyrights to certain works contained in this software are
owned by other third parties and used and distributed under
license. Certain components of this software are licensed under
the GNU General Public License (GPL) version 2.0 or the GNU
Lesser General Public License (LGPL) Version 2.1. A copy of each
such license is available at
http://www.opensource.org/licenses/gpl-2.0.php and
http://www.opensource.org/licenses/lgpl-2.1.php
This example shows how to display version information for the Cisco VNMC:
vnmc(local-mgmt)# show version
Name Package Version GUI
---- ------- ------- ----
core Base System 1.2(1b) 1.2(1b)
service-reg Service Registry 1.2(1b) 1.2(1b)
policy-mgr Policy Manager 1.2(1b) 1.2(1b)
resource-mgr Resource Manager 1.2(1b) 1.2(1b)
vm-mgr VM manager 1.2(1b) none
This example shows how to copy the Cisco VNMC software to the VM:
vnmc(local-mgmt)# copy scp://<user@example-server-ip>/example1-dir/vnmc.1.2.0.635.bin bootflash:/
Enter password:
100% 143MB 11.9MB/s 00:12
This example shows how to see the directory information for the Cisco VNMC:
vnmc(local-mgmt)# dir bootflash:/
14M Jul 28 2011 gui-automation.tgz
887 Jul 28 2011 vnmc-dplug.1.2.1b.bin
20M Jul 28 2011 vnmc-vsgpa.1.2.1b.bin
20M Jul 28 2011 vnmc-vsmpa.1.2.1b.bin
403M Jan 31 01:58 vnmc.1.3.1a.bin
Usage for bootflash://
18187836 bytes used
3842128 bytes free
22029964 bytes total
This example shows how to start the update for the Cisco VNMC:
vnmc(local-mgmt)# update bootflash:/vnmc.1.2.0.635.bin
It is recommended that you perform a full-state backup before updating any VNMC component. Press enter to continue or Ctrl-c to exit.
This example shows how to display the updated version for the Cisco VNMC:
vnmc(local-mgmt)# show version
Name Package Version GUI
---- ------- ------- ----
core Base System 1.3(1a) 1.3(1a)
service-reg Service Registry 1.3(1a) 1.3(1a)
policy-mgr Policy Manager 1.3(1a) 1.3(1a)
resource-mgr Resource Manager 1.3(1a) 1.3(1a)
vm-mgr VM manager 1.3(1a) none
Stage 2: Upgrading a Cisco VSG Pair
This section describes how to upgrade a Cisco VSG pair from Cisco VSG 1.2 to Cisco VSG 1.3 and from Cisco VSG 1.1 to Cisco VSG 1.3.
BEFORE YOU BEGIN
Before starting the procedure, you must know or do the following:
•![]() You are logged in to the CLI in EXEC mode.
You are logged in to the CLI in EXEC mode.
•![]() You have already copied the system image, kickstart image, and the Cisco VSG policy agent image into the bootflash file system using the following commands:
You have already copied the system image, kickstart image, and the Cisco VSG policy agent image into the bootflash file system using the following commands:
switch# copy
scp://user@scpserver.cisco.com/downloads/nexus-1000v-kickstart-mz.VSG1.3.1.bin
bootflash:nexus-1000v-kickstart-mz.VSG1.3.1.bin
switch# copy scp://user@scpserver.cisco.com/downloads/nexus-1000v-mz.VSG1.3.1.bin
bootflash:nexus-1000v-mz.VSG1.3.1.bin
switch# copy scp://user@scpserver.cisco.com/downloads/vnmc-vsgpa.1.3.1c.bin
bootflash:vnmc-vsgpa.1.3.1c.bin
•![]() You have confirmed that the system is in high availability (HA) mode for an HA upgrade using the show system redundancy status command.
You have confirmed that the system is in high availability (HA) mode for an HA upgrade using the show system redundancy status command.
PROCEDURE
This procedure shows how to upgrade the Cisco VSG Pair from Cisco VSG 1.2 to Cisco VSG 1.3.
Step 1 ![]() Enter the following command on all the Cisco VSG nodes on your network.
Enter the following command on all the Cisco VSG nodes on your network.
VSG# config VSG(config)# feature http-server VSG(config)#
Step 2 ![]() Install the kickstart image, system image, and policy agent (PA) image.
Install the kickstart image, system image, and policy agent (PA) image.
vsg# install all kickstart bootflash:nexus-1000v-kickstart-mz.VSG1.3.1.bin system bootflash:nexus-1000v-mz.VSG1.3.1.bin vnmpa bootflash:vnmc-vsgpa.1.3.1c.bin

Note ![]() If you do not have a policy agent installed on the Cisco VSG before the install all command is executed, the PA will not be upgraded (installed) with the image. For example, see the1.3.1c image in the above command example.
If you do not have a policy agent installed on the Cisco VSG before the install all command is executed, the PA will not be upgraded (installed) with the image. For example, see the1.3.1c image in the above command example.
You can check if there is an existing PA installed by executing the following command:
vsg# show vnm-pa status
VNM Policy-Agent status is - Installed Successfully. Version 1.3(1c)-vsg
If a PA image is installed and passed as a parameter to the install all command, it upgrades the PA image with the system and kickstart images.

Note ![]() You must have an existing PA installed before upgrading the PA by using the install command.
You must have an existing PA installed before upgrading the PA by using the install command.
If the PA image is not passed as a parameter to the install all command, the other parts of the upgrade (kickstart 1.3.1 and system 1.3.1, in the example above) will be upgraded properly, but the PA will not be upgraded.
PROCEDURE
This procedure shows how to upgrade the Cisco VSG Pair from Cisco VSG 1.1 to Cisco VSG 1.3. There is no install or upgrade command in Cisco VSG 1.1.
Step 1 ![]() Enter the config menu:
Enter the config menu:
VSG# config
Step 2 ![]() Unset the kickstart and system images on the active Cisco VSG .
Unset the kickstart and system images on the active Cisco VSG .
a. ![]() VSG(config)# no boot kickstart
VSG(config)# no boot kickstart
b. ![]() VSG(config)# no boot system
VSG(config)# no boot system
Step 3 ![]() Set the kickstart and system images to the new image .
Set the kickstart and system images to the new image .
VSG(config)# boot kickstart nexus-1000v-kickstart-mz.VSG1.3.1.bin
VSG(config)# boot system nexus-1000v-mz.VSG1.3.1.bin
Step 4 ![]() Uninstall the existing VNM-PA on the Cisco VSG.
Uninstall the existing VNM-PA on the Cisco VSG.
a. ![]() Enter the PA sub-menu as follows:
Enter the PA sub-menu as follows:
VSG(config)# vnm-policy-agent
VSG(config-vnm-policy-agent)# no policy-agent-image
VSG(config-vnm-policy-agent)# end
Step 5 ![]() Enable the HTTP feature.
Enable the HTTP feature.
VSG# config t
VSG(config)# feature http-server
Step 6 ![]() Initiate an image and boot variable synchronization to the standby Cisco VSG.
Initiate an image and boot variable synchronization to the standby Cisco VSG.
VSG# copy running-config startup-config
Step 7 ![]() Verify if the boot images are set properly.
Verify if the boot images are set properly.
VSG(config)# show boot
Step 8 ![]() Once the image synchronization is done, reload the standby module.
Once the image synchronization is done, reload the standby module.
VSG(config)# reload module standby_module_no
If the primary Cisco VSG is active, the standby_module_no will be 2. If secondary Cisco VSG is active, the standby_module_no will be 1.
Step 9 ![]() Check for an established HA pair with the new images. The configuration will be synchronized. Enter the show system redundancy status command and verify "Active with standby" is displayed in the output.
Check for an established HA pair with the new images. The configuration will be synchronized. Enter the show system redundancy status command and verify "Active with standby" is displayed in the output.
VSG# show system redundancy status
Step 10 ![]() Perform a system switchover on current active VSG.
Perform a system switchover on current active VSG.
VSG# system switchover
Step 11 ![]() Check for an established HA pair with the new images. The configuration will be synchronized.
Check for an established HA pair with the new images. The configuration will be synchronized.
Enter the show system redundancy status command and verify "Active with standby" is displayed
VSG# show system redundancy status
Step 12 ![]() Copy the VSG PA image on the Cisco VSG under bootflash to the new active VSG (1.3 PA).
Copy the VSG PA image on the Cisco VSG under bootflash to the new active VSG (1.3 PA).
VSG# copy scp://ipaddress/location_of_pa_image/vnmc-vsgpa.1.3.1c.bin bootflash
Step 13 ![]() Install the new VNM-PA image on the Cisco VSG.
Install the new VNM-PA image on the Cisco VSG.
VSG# config
VSG(config)# vnm-policy-agent
VSG(config-vnm-policy-agent)# policy-agent-image vnmc-vsgpa.1.3.1c.bin
VSG(config-vnm-policy-agent)# end
Step 14 ![]() Check if the PA installation is successful.
Check if the PA installation is successful.
VSG# show vnm-pa status
Step 15 ![]() Copy the running configuration to the startup configuration.
Copy the running configuration to the startup configuration.
vsg# copy running-config startup-config
Executing this command ensures that the registration becomes part of the basic configuration.
Stage 3: Upgrading the VSM Pair and the VEM
This section provides information on upgrading to the Cisco Nexus 1000V to Release 4.2(1)SV1(5.1).

Note ![]() When installing the PA on the latest VSM, enable the feature http-server command on all VSM nodes on your network as follows:
When installing the PA on the latest VSM, enable the feature http-server command on all VSM nodes on your network as follows: VSM# config
VSM(config) # feature http-server
VSM(config)
This section includes the following topics:
•![]() Information About the Software Upgrade
Information About the Software Upgrade
•![]() Prerequisites for the Upgrade
Prerequisites for the Upgrade
•![]() Guidelines and Limitations for Upgrading the Cisco Nexus 1000V
Guidelines and Limitations for Upgrading the Cisco Nexus 1000V
•![]() Upgrading to Release 4.2(1)SV1(5.1)
Upgrading to Release 4.2(1)SV1(5.1)
Information About the Software Upgrade
This section provides information about how to upgrade the Cisco Nexus 1000V to Release 4.2(1)SV1(5.1).
This section includes the following topic:
•![]() Obtaining the Upgrade Software
Obtaining the Upgrade Software
Obtaining the Upgrade Software
You can obtain your upgrade-related software from the following sources listed in Table 7-2.
|
|
|
|---|---|
Cisco |
Download the Cisco Nexus 1000V Release 4.2(1)SV1(5.1) software from Cisco.com. |
VMware |
Download the VMware software from the VMware website. |
For information about your software and platform compatibility, see the Cisco Nexus 1000V Compatibility Information, Release 4.2(1)SV1(5.1).
Prerequisites for the Upgrade
This section describes how to upgrade the Cisco Nexus 1000V software on a Virtual Supervisor Module (VSM) virtual machine (VM) and how to upgrade the Virtual Ethernet Module (VEM).
This section includes the following topics:
•![]() Prerequisites for Upgrading VSMs
Prerequisites for Upgrading VSMs
•![]() Prerequisites for Upgrading VEMs
Prerequisites for Upgrading VEMs
Prerequisites for Upgrading VSMs
Upgrading the VSMs has the following prerequisites:
•![]() Close any active configuration sessions before upgrading the Cisco Nexus 1000V software.
Close any active configuration sessions before upgrading the Cisco Nexus 1000V software.
•![]() Note that the network and server administrators must coordinate the upgrade procedure with each other.
Note that the network and server administrators must coordinate the upgrade procedure with each other.
•![]() You have saved all changes in the running configuration to the startup configuration to be preserved through the upgrade.
You have saved all changes in the running configuration to the startup configuration to be preserved through the upgrade.
•![]() You have saved a backup copy of the running configuration in external storage.
You have saved a backup copy of the running configuration in external storage.
•![]() You have performed a VSM backup. See the "Configuring VSM Backup and Recovery" chapter in the Cisco Nexus 1000V System Management Configuration Guide, Release 4.2(1)SV1(5.1).
You have performed a VSM backup. See the "Configuring VSM Backup and Recovery" chapter in the Cisco Nexus 1000V System Management Configuration Guide, Release 4.2(1)SV1(5.1).
For information about backing up a configuration file, see the Cisco Nexus 1000V System Management Configuration Guide, Release 4.2(1)SV1(5.1).
Prerequisites for Upgrading VEMs
Upgrading the Cisco Nexus 1000V VEM software has the following prerequisites:


Note ![]() When you perform any VUM operation on hosts that are a part of a cluster, ensure that VMware high availability (HA), VMware fault tolerance (FT), and VMware Distributed Power Management (DPM) features are disabled for the entire cluster. Otherwise, VUM will fail to install the hosts in the cluster.
When you perform any VUM operation on hosts that are a part of a cluster, ensure that VMware high availability (HA), VMware fault tolerance (FT), and VMware Distributed Power Management (DPM) features are disabled for the entire cluster. Otherwise, VUM will fail to install the hosts in the cluster.
•![]() You are logged in to the VSM CLI in EXEC mode.
You are logged in to the VSM CLI in EXEC mode.
•![]() Network and server administrators coordinate the VEM upgrade with each other.
Network and server administrators coordinate the VEM upgrade with each other.
•![]() You have a copy of your VMware documentation available for installing software on a host.
You have a copy of your VMware documentation available for installing software on a host.
•![]() You have already obtained a copy of the VEM software file from one of the sources listed in
You have already obtained a copy of the VEM software file from one of the sources listed in
Table 2-1, "Obtaining VEM Software" of the Cisco Nexus 1000V Installation and Upgrade Guide, Release 4.2(1)SV1(5.1) at
•![]() For more information, see the Cisco Nexus 1000V Compatibility Information, Release 4.2(1)SV1(5.1).
For more information, see the Cisco Nexus 1000V Compatibility Information, Release 4.2(1)SV1(5.1).
•![]() You have placed the VEM software file in /tmp on the vSphere host. Placing it in the root (/) directory might interfere with the upgrade. Make sure that the root RAM disk has at least 12 MB of free space as displayed by the vdf command.
You have placed the VEM software file in /tmp on the vSphere host. Placing it in the root (/) directory might interfere with the upgrade. Make sure that the root RAM disk has at least 12 MB of free space as displayed by the vdf command.
•![]() If you use a proxy server to connect VUM to the Internet, you might need to disable the proxy before starting a VUM upgrade. In VMware versions before VUM Update 1, the proxy prevents VUM from communicating locally with the VSM. For this reason, automatic VEM upgrades might fail if you do not disable the proxy first.
If you use a proxy server to connect VUM to the Internet, you might need to disable the proxy before starting a VUM upgrade. In VMware versions before VUM Update 1, the proxy prevents VUM from communicating locally with the VSM. For this reason, automatic VEM upgrades might fail if you do not disable the proxy first.
•![]() On your upstream switches, you must have the following configuration.
On your upstream switches, you must have the following configuration.
–![]() On Catalyst 6500 Series Switches with Cisco IOS software:
On Catalyst 6500 Series Switches with Cisco IOS software:
(config-if) portfast trunk
or
(config-if) portfast edge trunk
–![]() On Cisco Nexus 5000 Series Switches with Cisco NX-OS software:
On Cisco Nexus 5000 Series Switches with Cisco NX-OS software:
(config-if) spanning-tree port type edge trunk
•![]() On your upstream switches, we highly recommend that you globally enable the following:
On your upstream switches, we highly recommend that you globally enable the following:
–![]() Global BPDU Filtering
Global BPDU Filtering
–![]() Global BPDU Guard
Global BPDU Guard
•![]() On your upstream switches where you cannot globally enable BPDU Filtering and BPDU Guard, we highly recommended that you enter the following commands:
On your upstream switches where you cannot globally enable BPDU Filtering and BPDU Guard, we highly recommended that you enter the following commands:
–![]() (config-if) spanning-tree bpdu filter
(config-if) spanning-tree bpdu filter
–![]() (config-if) spanning-tree bpdu guard
(config-if) spanning-tree bpdu guard
•![]() For more information about configuring spanning tree, BPDU, or PortFast, see the documentation for your upstream switch.
For more information about configuring spanning tree, BPDU, or PortFast, see the documentation for your upstream switch.
Guidelines and Limitations for Upgrading the Cisco Nexus 1000V
Before attempting to migrate to any software image version, follow these guidelines:
•![]() You are upgrading the Cisco Nexus 1000V software to Release 4.2(1)SV1(5.1).
You are upgrading the Cisco Nexus 1000V software to Release 4.2(1)SV1(5.1).
•![]() Scheduling — Schedule the upgrade when your network is stable and steady. Ensure that everyone who has access to the switch or the network is not configuring the switch or the network during this time. You cannot configure a switch during an upgrade.
Scheduling — Schedule the upgrade when your network is stable and steady. Ensure that everyone who has access to the switch or the network is not configuring the switch or the network during this time. You cannot configure a switch during an upgrade.
•![]() Hardware — Avoid power interruptions to the hosts that run the VSM VMs during any installation procedure.
Hardware — Avoid power interruptions to the hosts that run the VSM VMs during any installation procedure.
•![]() Connectivity to remote servers — do the following:
Connectivity to remote servers — do the following:
–![]() Copy the kickstart and system images from the remote server to the Cisco Nexus 1000V.
Copy the kickstart and system images from the remote server to the Cisco Nexus 1000V.
–![]() Ensure that the switch has a route to the remote server. The switch and the remote server must be in the same subnetwork if you do not have a router to route traffic between subnets.
Ensure that the switch has a route to the remote server. The switch and the remote server must be in the same subnetwork if you do not have a router to route traffic between subnets.
•![]() Software images — do the following:
Software images — do the following:
–![]() Make sure that the system and kickstart images are the same version.
Make sure that the system and kickstart images are the same version.
–![]() Retrieve the images in one of two ways:
Retrieve the images in one of two ways:
Locally—Images are locally available on the upgrade CD-ROM/ISO image.
Remotely—Images are in a remote location and you specify the destination using the remote server parameters and the filename to be used locally.
•![]() Commands to use — do the following:
Commands to use — do the following:
–![]() Verify connectivity to the remote server by using the ping command.
Verify connectivity to the remote server by using the ping command.
–![]() Use the one-step install all command to upgrade your software. This command upgrades the VSMs.
Use the one-step install all command to upgrade your software. This command upgrades the VSMs.
–![]() Do not enter another install all command while running the installation. You can run commands other than configuration commands.
Do not enter another install all command while running the installation. You can run commands other than configuration commands.
–![]() During the VSM upgrade, if you try to add a new VEM or any of the VEMs are detached due to uplink flaps, the VEM attachment is queued until the upgrade completes.
During the VSM upgrade, if you try to add a new VEM or any of the VEMs are detached due to uplink flaps, the VEM attachment is queued until the upgrade completes.

Note ![]() If the VEMs are not compatible with the software image that you install on the VSM, a traffic disruption occurs in those modules, depending on your configuration. The install all command output identifies these scenarios. You can choose to proceed with the upgrade or end at this point.
If the VEMs are not compatible with the software image that you install on the VSM, a traffic disruption occurs in those modules, depending on your configuration. The install all command output identifies these scenarios. You can choose to proceed with the upgrade or end at this point.
•![]() Local Authentication — We recommend that you use local authentication during the upgrade process. If a remote server is needed, you must make sure that the admin account is configured with network-admin privileges.
Local Authentication — We recommend that you use local authentication during the upgrade process. If a remote server is needed, you must make sure that the admin account is configured with network-admin privileges.
Before upgrading the VEMs, note these guidelines and limitations:
•![]() The VEM software can be upgraded manually using the CLI or upgraded automatically using VUM.
The VEM software can be upgraded manually using the CLI or upgraded automatically using VUM.
•![]() During the VEM upgrade process, VEMs reattach to the VSM.
During the VEM upgrade process, VEMs reattach to the VSM.
•![]() Connectivity to the VSM can be lost during a VEM upgrade when the interfaces of a VSM VM connect to its own Distributed Virtual Switch (DVS).
Connectivity to the VSM can be lost during a VEM upgrade when the interfaces of a VSM VM connect to its own Distributed Virtual Switch (DVS).
•![]() Connectivity between an active and standby VSM can be lost during a VEM upgrade when the VEM being upgraded provides interface connectivity to one of the VSMs. In this case, both VSMs become active and lose connectivity. To prevent this problem, make sure that you are at the appropriate patch levels. See Table 7-2.
Connectivity between an active and standby VSM can be lost during a VEM upgrade when the VEM being upgraded provides interface connectivity to one of the VSMs. In this case, both VSMs become active and lose connectivity. To prevent this problem, make sure that you are at the appropriate patch levels. See Table 7-2.
•![]() If you are upgrading a VEM using a Cisco Nexus 1000V bundle, follow the instructions in your VMware documentation. For more details about VMware bundled software, see the Cisco Nexus 1000V Compatibility Information, Release 4.2(1)SV1(5.1).
If you are upgrading a VEM using a Cisco Nexus 1000V bundle, follow the instructions in your VMware documentation. For more details about VMware bundled software, see the Cisco Nexus 1000V Compatibility Information, Release 4.2(1)SV1(5.1).

Upgrade Paths
This section describes how to upgrade the Cisco Nexus 1000V software on a Virtual Supervisor Module (VSM) virtual machine (VM) and how to upgrade the Virtual Ethernet Module (VEM).
Table 7-3 shows the upgrade procedure you must take to upgrade to Release 4.2(1)SV1(5.1).
|
|
|
|---|---|
4.2(1)SV1(4) |
|
4.0(4)SV1(3) |
Upgrading from Releases 4.0(4)SV1(3, 3a, 3b, 3c, 3d) to Release 4.2(1)SV1(5.1) |

Note ![]() Upgrades from Cisco Nexus 1000V Release 4.0(4)SV1(1) and Cisco Nexus 1000V Release 4.0(4)SV1(2) are no longer supported. VMware 4.0 is also no longer supported.
Upgrades from Cisco Nexus 1000V Release 4.0(4)SV1(1) and Cisco Nexus 1000V Release 4.0(4)SV1(2) are no longer supported. VMware 4.0 is also no longer supported.
For upgrade procedures to ESX/ESXi 4.1.0 and ESXi 5.0.0, see Appendix A, "Installing and Upgrading VMware" of the Cisco Nexus 1000V Installation and Upgrade Guide, Release 4.2(1)SV1(5.1) at
http://www.cisco.com/en/US/docs/switches/datacenter/nexus1000/sw/4_2_1_s_v_1_5_1/install_upgrade/vsm_vem/guide/n1000v_installupgrade_upgrade_vmware.html#wp705174
•![]() The upgrade process is irrevocable. After the software is upgraded, you can downgrade by removing the current installation and reinstalling the software. For more information, see the "Recreating the Installation" section of Cisco Nexus 1000V Troubleshooting Guide, Release 4.2(1)SV1(5.1).
The upgrade process is irrevocable. After the software is upgraded, you can downgrade by removing the current installation and reinstalling the software. For more information, see the "Recreating the Installation" section of Cisco Nexus 1000V Troubleshooting Guide, Release 4.2(1)SV1(5.1).

Upgrading to Release 4.2(1)SV1(5.1)
This section describes how to upgrade to Release 4.2(1)SV1(5.1).
This section contains the following topics:
•![]() Upgrading from Releases 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
Upgrading from Releases 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
•![]() Upgrading from Releases 4.0(4)SV1(3, 3a, 3b, 3c, 3d) to Release 4.2(1)SV1(5.1)
Upgrading from Releases 4.0(4)SV1(3, 3a, 3b, 3c, 3d) to Release 4.2(1)SV1(5.1)

Note ![]() For ESXi 5.0.0 releases and later releases, the minimum VC/VUM version required is 380461/380316.
For ESXi 5.0.0 releases and later releases, the minimum VC/VUM version required is 380461/380316.
For ESX/ESXi Release 4.1.0 and later releases, the minimum VC/VUM version required is 258902/256596.
This procedure is different from the upgrade to Release 4.2(1)SV1(4). In this procedure, you upgrade the VSMs first by using the install all command and then you upgrade the VEMs.

Appendix A, "Installing and Upgrading VMware" of the Cisco Nexus 1000V Installation and Upgrade Guide, Release 4.2(1)SV1(5.1) at http://www.cisco.com/en/US/docs/switches/datacenter/nexus1000/sw/4_2_1_s_v_1_5_1/install_upgrade/vsm_vem/guide/n1000v_installupgrade_upgrade_vmware.html#wp705174
Upgrading from Releases 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
The following section describes how to upgrade the Cisco Nexus 1000V software from Releases 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1).
This section includes the following topics:
•![]() Upgrading the VSMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
Upgrading the VSMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
•![]() Upgrading the VEMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
Upgrading the VEMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
Table 7-4 lists the upgrade steps when upgrading to vSphere 4.1 and Release 4.2(1)SV1(5.1).
BEFORE YOU BEGIN
Before starting the procedure, you must know or do the following:
•![]() You are running primary and secondary VSMs as an active-standby pair or a standalone VSM.
You are running primary and secondary VSMs as an active-standby pair or a standalone VSM.
•![]() The upgrade application cannot be used for the upgrade of the VSMs from Release 4.2(1)SV1(4) to Release 4.2(1)SV1(5.1).
The upgrade application cannot be used for the upgrade of the VSMs from Release 4.2(1)SV1(4) to Release 4.2(1)SV1(5.1).
•![]() A pair of VSMs in a high availability (HA) pair is required to support a nondisruptive upgrade.
A pair of VSMs in a high availability (HA) pair is required to support a nondisruptive upgrade.
•![]() A system with a single VSM can only be upgraded in a disruptive manner.
A system with a single VSM can only be upgraded in a disruptive manner.
When upgrading the VSM from Release 4.2(1)SV1(4) or a later release to Release 4.2(1)SV1(5.1), if any of the VEM hosts are running a vSphere version prior to 4.1, the install all command displays that host as incompatible. The incompatibility warning applies only if you do not upgrade the ESX version with the VEM version. It is possible to manually upgrade the ESX and VEM in one maintenance mode as follows:
1. ![]() Place the host in maintenance mode.
Place the host in maintenance mode.
2. ![]() Upgrade the ESX to 4.1 or 5.0, as needed.
Upgrade the ESX to 4.1 or 5.0, as needed.
3. ![]() Install the Release 4.2(1)SV1(5.1)VEM VIB, while the host is still in maintenance mode.
Install the Release 4.2(1)SV1(5.1)VEM VIB, while the host is still in maintenance mode.
4. ![]() Remove the host from maintenance mode.
Remove the host from maintenance mode.
This paired upgrade procedure is not applicable for VUM-based upgrades.
•![]() You can abort the upgrade procedure by pressing Ctrl-C.
You can abort the upgrade procedure by pressing Ctrl-C.
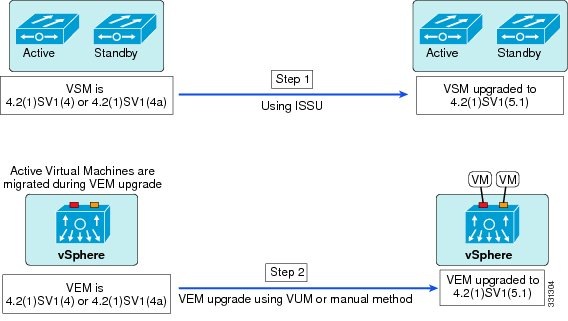
PROCEDURE
Step 1 ![]() Upgrade the VSMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1). For this procedure, see the "Upgrading the VSMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)" section. See Figure 7-1.
Upgrade the VSMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1). For this procedure, see the "Upgrading the VSMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)" section. See Figure 7-1.
Step 2 ![]() Upgrade the VEMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1). For this procedure, see the "Upgrading the VEMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)" section. See Figure 7-1.
Upgrade the VEMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1). For this procedure, see the "Upgrading the VEMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)" section. See Figure 7-1.
Figure 7-1 Upgrading from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
Upgrading the VSMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
This section includes the following topics:
•![]() In-Service Software Upgrades on Systems with Dual VSMs
In-Service Software Upgrades on Systems with Dual VSMs
•![]() Upgrading a System with Dual VSMs Using ISSU
Upgrading a System with Dual VSMs Using ISSU
•![]() Upgrading a System with Dual VSMs
Upgrading a System with Dual VSMs
Software Images
The software image install procedure is dependent on the following factors:
•![]() Software images—The kickstart, system, and VSM Policy-Agent image files reside in directories or folders that you can access from the Cisco Nexus 1000V software prompt.
Software images—The kickstart, system, and VSM Policy-Agent image files reside in directories or folders that you can access from the Cisco Nexus 1000V software prompt.
•![]() Image version—Each image file has a version.
Image version—Each image file has a version.
•![]() Disk—The bootflash: resides on the VSM.
Disk—The bootflash: resides on the VSM.
•![]() VSM—There are single or dual VSMs.
VSM—There are single or dual VSMs.
In-Service Software Upgrades on Systems with Dual VSMs
The Cisco Nexus 1000V software supports in-service software upgrades (ISSUs) for systems with dual VSMs. An ISSU can update the software images on your switch without disrupting data traffic. Only control traffic is disrupted. If an ISSU causes a disruption of data traffic, the Cisco Nexus 1000V software warns you before proceeding so that you can stop the upgrade and reschedule it to a time that minimizes the impact on your network.

Note ![]() On systems with dual VSMs, you should have access to the console of both VSMs to maintain connectivity when the switchover occurs during upgrades. If you are performing the upgrade over Secure Shell (SSH) or Telnet, the connection will drop when the system switchover occurs, and you must reestablish the connection.
On systems with dual VSMs, you should have access to the console of both VSMs to maintain connectivity when the switchover occurs during upgrades. If you are performing the upgrade over Secure Shell (SSH) or Telnet, the connection will drop when the system switchover occurs, and you must reestablish the connection.
An ISSU updates the following images:
•![]() Kickstart image
Kickstart image
•![]() System image
System image
•![]() VSM Policy-Agent image
VSM Policy-Agent image
•![]() VEM images
VEM images
All of the following processes are initiated automatically by the upgrade process after the network administrator enters the install all command.
Figure 7-2 shows the ISSU process.
Figure 7-2 ISSU Process
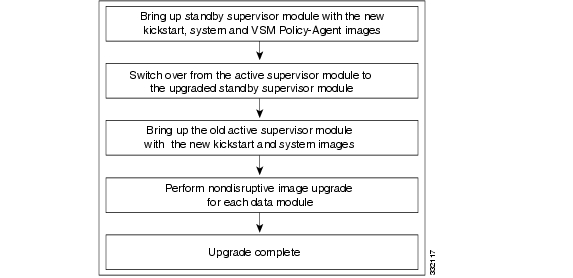
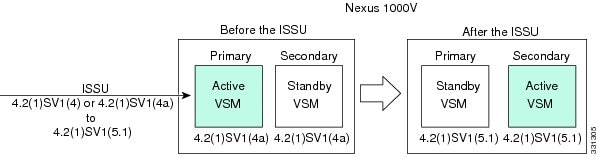
Figure 7-3 provides an example of the VSM status before and after an ISSU switchover.
Figure 7-3 Example of an ISSU VSM Switchover
Upgrading a System with Dual VSMs Using ISSU
The install all command supports an in-service software upgrade (ISSU) on dual VSMs in an HA environment and performs the following actions:
–![]() Determines whether the upgrade is disruptive and asks if you want to continue.
Determines whether the upgrade is disruptive and asks if you want to continue.
–![]() Copies the kickstart, system, and VSM Policy-Agent images to the standby VSM.
Copies the kickstart, system, and VSM Policy-Agent images to the standby VSM.
–![]() Sets the kickstart and system boot variables.
Sets the kickstart and system boot variables.
–![]() Reloads the standby VSM with the new Cisco Nexus 1000V software.
Reloads the standby VSM with the new Cisco Nexus 1000V software.
–![]() Causes the active VSM to reload when the switchover occurs.
Causes the active VSM to reload when the switchover occurs.
The install all command provides the following benefits:
•![]() You can upgrade the VSM by using just one command.
You can upgrade the VSM by using just one command.
•![]() You can receive descriptive information on the intended changes to your system before you continue with the installation.
You can receive descriptive information on the intended changes to your system before you continue with the installation.
•![]() You have the option to cancel the command. Once the effects of the command are presented, you can continue or cancel when you see this question (the default is no):
You have the option to cancel the command. Once the effects of the command are presented, you can continue or cancel when you see this question (the default is no):
Do you want to continue (y/n) [n]: y
•![]() You can upgrade the VSM using the least disruptive procedure.
You can upgrade the VSM using the least disruptive procedure.
•![]() You can see the progress of this command on the console, Telnet, and SSH screens:
You can see the progress of this command on the console, Telnet, and SSH screens:
–![]() After a switchover process, you can see the progress from both the VSMs.
After a switchover process, you can see the progress from both the VSMs.
–![]() Before a switchover process, you can only see the progress from the active VSM.
Before a switchover process, you can only see the progress from the active VSM.
•![]() The install all command automatically checks the image integrity, which includes the running kickstart and system images.
The install all command automatically checks the image integrity, which includes the running kickstart and system images.
•![]() The install all command performs a platform validity check to verify that a wrong image is not used.
The install all command performs a platform validity check to verify that a wrong image is not used.
•![]() The Ctrl-C escape sequence gracefully ends the install all command. The command sequence completes the update step in progress and returns to the switch prompt. (Other upgrade steps cannot be ended by using Ctrl-C.)
The Ctrl-C escape sequence gracefully ends the install all command. The command sequence completes the update step in progress and returns to the switch prompt. (Other upgrade steps cannot be ended by using Ctrl-C.)
•![]() After running the install all command, if any step in the sequence fails, the command completes the step in progress and ends.
After running the install all command, if any step in the sequence fails, the command completes the step in progress and ends.
Upgrading a System with Dual VSMs
This section describes how to upgrade to the latest Cisco Nexus 1000V software on systems with dual VSMs.
PROCEDURE
Step 1 ![]() Log in to the active VSM.
Log in to the active VSM.
Step 2 ![]() Log in to Cisco.com to access the links provided in this document. To log in to Cisco.com, go to the URL http://www.cisco.com/ and click Log In at the top of the page. Enter your Cisco username and password.
Log in to Cisco.com to access the links provided in this document. To log in to Cisco.com, go to the URL http://www.cisco.com/ and click Log In at the top of the page. Enter your Cisco username and password.

Note ![]() Unregistered cisco.com users cannot access the links provided in this document.
Unregistered cisco.com users cannot access the links provided in this document.
Step 3 ![]() Access the Software Download Center by using this URL: http://www.cisco.com/public/sw-center/index.shtml
Access the Software Download Center by using this URL: http://www.cisco.com/public/sw-center/index.shtml
Step 4 ![]() Navigate to the download site for your system.
Navigate to the download site for your system.
You see links to the download images for your switch.
Step 5 ![]() Choose and download the Cisco Nexus 1000V zip file and extract the kickstart and system software files to a server.
Choose and download the Cisco Nexus 1000V zip file and extract the kickstart and system software files to a server.
Step 6 ![]() Download the vnmc-vsmpa image.
Download the vnmc-vsmpa image.
Step 7 ![]() Ensure that the required space is available for the image file(s) to be copied.
Ensure that the required space is available for the image file(s) to be copied.
switch# dir bootflash:
.
.
.
Usage for bootflash://
485830656 bytes used
1109045248 bytes free
1594875904 bytes total

Tip ![]() We recommend that you have the kickstart and system image files for at least one previous release of the Cisco Nexus 1000V software on the system to use if the new image files do not load successfully.
We recommend that you have the kickstart and system image files for at least one previous release of the Cisco Nexus 1000V software on the system to use if the new image files do not load successfully.
Step 8 ![]() Verify that there is space available on the standby VSM.
Verify that there is space available on the standby VSM.
switch# dir bootflash://sup-standby/
.
.
.
Usage for bootflash://
485830656 bytes used
1109045248 bytes free
1594875904 bytes total
Step 9 ![]() Delete any unnecessary files to make space available if you need more space on the standby VSM.
Delete any unnecessary files to make space available if you need more space on the standby VSM.

Note ![]() When you download an image file, change your FTP environment IP address or DN name and the path where the files are located
When you download an image file, change your FTP environment IP address or DN name and the path where the files are located
Step 10 ![]() If you plan to install the images from the bootflash:, copy the Cisco Nexus 1000V kickstart, system, and VSM Policy-Agent images to the active VSM by using a transfer protocol. You can use ftp:, tftp:, scp:, or sftp:. The examples in this procedure use scp:.
If you plan to install the images from the bootflash:, copy the Cisco Nexus 1000V kickstart, system, and VSM Policy-Agent images to the active VSM by using a transfer protocol. You can use ftp:, tftp:, scp:, or sftp:. The examples in this procedure use scp:.

Note ![]() When you download an image file, change to your FTP environment IP address or DNS name and the path where the files are located.
When you download an image file, change to your FTP environment IP address or DNS name and the path where the files are located.
•![]() Copy kickstart, system, and VSM Policy-Agent images.
Copy kickstart, system, and VSM Policy-Agent images.
switch# copy
scp://user@scpserver.cisco.com/downloads/nexus-1000v-kickstart-4.2.1.SV1.5.1.bin
bootflash:nexus-1000v-kickstart-4.2.1.SV1.5.1.bin
switch# copy scp://user@scpserver.cisco.com/downloads/nexus-1000v-4.2.1.SV1.5.1.bin
bootflash:nexus-1000v-4.2.1.SV1.5.1.bin
switch# copy scp://user@scpserver.cisco.com/downloads/vnmc-vsmpa.1.3.1b.bin
bootflash:vnmc-vsmpa.1.3.1b.bin
Step 11 ![]() Check on the impact of the ISSU upgrade for the kickstart and system images.
Check on the impact of the ISSU upgrade for the kickstart and system images.
•![]() kickstart and system
kickstart and system
switch# show install all impact kickstart
bootflash:nexus-1000v-kickstart-4.2.1.SV1.5.1.bin system
bootflash:nexus-1000v-4.2.1.SV1.5.1.bin
Verifying image bootflash:/nexus-1000v-kickstart-4.2.1.SV1.5.1.bin for boot variable "kickstart".
[####################] 100% -- SUCCESS
Verifying image bootflash:/nexus-1000v-4.2.1.SV1.5.1.bin for boot variable "system".
[####################] 100% -- SUCCESS
Verifying image type.
[####################] 100% -- SUCCESS
Extracting "system" version from image bootflash:/nexus-1000v-4.2.1.SV1.5.1.bin.
[####################] 100% -- SUCCESS
Extracting "kickstart" version from image bootflash:/nexus-1000v-kickstart-4.2.1.SV1.5.1.bin.
[####################] 100% -- SUCCESS
Notifying services about system upgrade.
[####################] 100% -- SUCCESS
Compatibility check is done:
Module bootable Impact Install-type Reason
------ -------- -------------- ------------ ------
1 yes non-disruptive reset
2 yes non-disruptive reset
Images will be upgraded according to following table:
Module Image Running-Version New-Version Upg-Required
------ ---------- ---------------------- ---------------------- ------------
1 system 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
1 kickstart 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
2 system 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
2 kickstart 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
Module Running-Version ESX Version VSM Compatibility ESX Compatibility
------ ---------------------- ---------------------------------------------------- ---------------------- ----------------------
3 4.2(1)SV1(4a) VMware ESXi 5.0.0 Releasebuild-469512 (3.0) COMPATIBLE COMPATIBLE
4 4.2(1)SV1(4a) VMware ESXi 5.0.0 Releasebuild-469512 (3.0) COMPATIBLE COMPATIBLE
Step 12 ![]() Read the release notes for the related image file. See the Cisco Nexus 1000V Release Notes, Release 4.2(1)SV1(5.1).
Read the release notes for the related image file. See the Cisco Nexus 1000V Release Notes, Release 4.2(1)SV1(5.1).
Step 13 ![]() Save the running configuration to the startup configuration.
Save the running configuration to the startup configuration.
switch# copy running-config startup-config
Step 14 ![]() Save the running configuration on the bootflash and externally.
Save the running configuration on the bootflash and externally.
switch# copy running-config bootflash:run-cfg-backup
switch# copy running-config scp://user@tftpserver.cisco.com/n1kv-run-cfg-backup

Note ![]() You can also run a VSM backup. See the "Configuring VSM Backup and Recovery" chapter of the Cisco Nexus 1000V System Management Configuration Guide, Release 4.2(1)SV1(5.1).
You can also run a VSM backup. See the "Configuring VSM Backup and Recovery" chapter of the Cisco Nexus 1000V System Management Configuration Guide, Release 4.2(1)SV1(5.1).
Step 15 ![]() Perform the upgrade on the active VSM using the kickstart, system, and VSM Policy-Agent images.
Perform the upgrade on the active VSM using the kickstart, system, and VSM Policy-Agent images.
•![]() Upgrade using the kickstart, system, and VSM Policy-Agent images.
Upgrade using the kickstart, system, and VSM Policy-Agent images.
switch# install all kickstart bootflash:nexus-1000v-kickstart-mz.4.2.1.SV1.5.1.bin
system bootflash:nexus-1000v-mz.4.2.1.SV1.5.1.bin
vnmpa bootflash:vnmc-vnmpa.1.3.1b.bin
Verifying image bootflash:/nexus-1000v-kickstart-4.2.1.SV1.5.1.bin for boot variable "kickstart".
[####################] 100% -- SUCCESS
Verifying image bootflash:/nexus-1000v-4.2.1.SV1.5.1.bin for boot variable "system".
[####################] 100% -- SUCCESS
Verifying image type.
[####################] 100% -- SUCCESS
Extracting "system" version from image bootflash:/nexus-1000v-4.2.1.SV1.5.1.bin.
[####################] 100% -- SUCCESS
Extracting "kickstart" version from image bootflash:/nexus-1000v-kickstart-4.2.1.SV1.5.1.bin.
[####################] 100% -- SUCCESS
Notifying services about system upgrade.
[####################] 100% -- SUCCESS
Compatibility check is done:
Module bootable Impact Install-type Reason
------ -------- -------------- ------------ ------
1 yes non-disruptive reset
2 yes non-disruptive reset
Images will be upgraded according to following table:
Module Image Running-Version New-Version Upg-Required
------ ---------- ---------------------- ---------------------- ------------
1 system 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
1 kickstart 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
2 system 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
2 kickstart 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
Module Running-Version ESX Version VSM Compatibility ESX Compatibility
------ ---------------------- ---------------------------------------------------- ---------------------- ----------------------
3 4.2(1)SV1(4a) VMware ESXi 5.0.0 Releasebuild-469512 (3.0) COMPATIBLE COMPATIBLE
4 4.2(1)SV1(4a) VMware ESXi 5.0.0 Releasebuild-469512 (3.0) COMPATIBLE COMPATIBLE
Do you want to continue with the installation (y/n)? [n]
Step 16 ![]() Continue with the installation by pressing Y.
Continue with the installation by pressing Y.

Note ![]() If you press N, the installation exits gracefully.
If you press N, the installation exits gracefully.
Install is in progress, please wait.
Syncing image bootflash:/nexus-1000v-kickstart-4.2.1.SV1.5.1.bin to standby.
[####################] 100% -- SUCCESS
Syncing image bootflash:/nexus-1000v-4.2.1.SV1.5.1.bin to standby.
[####################] 100% -- SUCCESS
Setting boot variables.
[####################] 100% -- SUCCESS
Performing configuration copy.
[####################] 100%2011 Mar 31 03:49:42 BL1-VSM %SYSMGR-STANDBY-5-CFGWRITE_STARTED: Configuration copy started (PID 3660).
[####################] 100% -- SUCCESS

Note ![]() As part of the upgrade process, the standby VSM is reloaded with new images. Once it becomes the HA standby again, the upgrade process initiates a switchover. The upgrade then continues from the new active VSM with the following output.
As part of the upgrade process, the standby VSM is reloaded with new images. Once it becomes the HA standby again, the upgrade process initiates a switchover. The upgrade then continues from the new active VSM with the following output.
Continuing with installation, please wait
Module 2: Waiting for module online
-- SUCCESS
Install has been successful
Step 17 ![]() After the installation operation completes, log in and verify that the switch is running the required software version.
After the installation operation completes, log in and verify that the switch is running the required software version.
switch# show version
Nexus1000v# show version
Cisco Nexus Operating System (NX-OS) Software
TAC support: http://www.cisco.com/tac
Copyright (c) 2002-2012, Cisco Systems, Inc. All rights reserved.
The copyrights to certain works contained herein are owned by
other third parties and are used and distributed under license.
Some parts of this software are covered under the GNU Public
License. A copy of the license is available at
http://www.gnu.org/licenses/gpl.html.
Software
loader: version unavailable [last: loader version not available]
kickstart: version 4.2(1)SV1(5.1) [build 4.2(1)SV1(5.1)]
system: version 4.2(1)SV1(5.1) [build 4.2(1)SV1(5.1)]
kickstart image file is: bootflash:/nexus-1000v-kickstart-4.2.1.SV1.5.1.bin
kickstart compile time: 1/11/2012 3:00:00 [01/11/2012 12:49:49]
system image file is: bootflash:/nexus-1000v-4.2.1.SV1.5.1.bin
system compile time: 1/11/2012 3:00:00 [01/11/2012 13:42:57]
Hardware
cisco Nexus 1000V Chassis ("Virtual Supervisor Module")
Intel(R) Xeon(R) CPU with 2075740 kB of memory.
Processor Board ID T5056B1802D
Device name: Nexus1000v
bootflash: 1557496 kB
Kernel uptime is 4 day(s), 8 hour(s), 31 minute(s), 3 second(s)
plugin
Core Plugin, Ethernet Plugin, Virtualization Plugin
...
switch# show vnmc-vnmpa status
VSM Policy-Agent status is - Installed Successfully. Version 1.3(1b)-vsm
switch#
Step 18 ![]() Display the log of the last installation.
Display the log of the last installation.
switch# show install all status
This is the log of last installation.
Verifying image bootflash:/nexus-1000v-kickstart-4.2.1.SV1.5.1.bin for boot variable "kickstart".
-- SUCCESS
Verifying image bootflash:/nexus-1000v-4.2.1.SV1.5.1.bin for boot variable "system".
-- SUCCESS
Verifying image type.
-- SUCCESS
Extracting "system" version from image bootflash:/nexus-1000v-4.2.1.SV1.5.1.bin.
-- SUCCESS
Extracting "kickstart" version from image bootflash:/nexus-1000v-kickstart-4.2.1.SV1.5.1.bin.
-- SUCCESS
Notifying services about system upgrade.
-- SUCCESS
Compatibility check is done:
Module bootable Impact Install-type Reason
------ -------- -------------- ------------ ------
1 yes non-disruptive reset
2 yes non-disruptive reset
Images will be upgraded according to following table:
Module Image Running-Version New-Version Upg-Required
------ ---------- ---------------------- ---------------------- ------------
1 system 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
1 kickstart 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
2 system 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
2 kickstart 4.2(1)SV1(4a) 4.2(1)SV1(5.1) yes
Images will be upgraded according to following table:
Module Running-Version ESX Version VSM Compatibility ESX Compatibility
------ ---------------------- ---------------------------------------------------- ---------------------- ----------------------
3 4.2(1)SV1(4a) VMware ESXi 5.0.0 Releasebuild-469512 (3.0) COMPATIBLE COMPATIBLE
4 4.2(1)SV1(4a) VMware ESXi 5.0.0 Releasebuild-469512 (3.0) COMPATIBLE COMPATIBLE
Install is in progress, please wait.
Syncing image bootflash:/nexus-1000v-kickstart-4.2.1.SV1.5.1.bin to standby.
-- SUCCESS
Syncing image bootflash:/nexus-1000v-4.2.1.SV1.5.1.bin to standby.
-- SUCCESS
Setting boot variables.
-- SUCCESS
Performing configuration copy.
-- SUCCESS
Module 2: Waiting for module online.
-- SUCCESS
Notifying services about the switchover.
-- SUCCESS
"Switching over onto standby".
switch#
switch#
switch#
switch# attach module 2
Attaching to module 2 ...
To exit type 'exit', to abort type '$.'
Cisco Nexus Operating System (NX-OS) Software
TAC support: http://www.cisco.com/tac
Copyright (c) 2002-2011, Cisco Systems, Inc. All rights reserved.
The copyrights to certain works contained in this software are
owned by other third parties and used and distributed under
license. Certain components of this software are licensed under
the GNU General Public License (GPL) version 2.0 or the GNU
Lesser General Public License (LGPL) Version 2.1. A copy of each
such license is available at
http://www.opensource.org/licenses/gpl-2.0.php and
http://www.opensource.org/licenses/lgpl-2.1.php
switch(standby)#
switch(standby)# show in
incompatibility install interface inventory
switch(standby)# show install all status
This is the log of last installation.
Continuing with installation, please wait
Trying to start the installer...
Module 2: Waiting for module online.
-- SUCCESS
Install has been successful.
switch(standby)#
Upgrading the VEMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
This section describes how to upgrade VEMs from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)and includes the following topics:
•![]() Choosing a VEM Software Upgrade Procedure
Choosing a VEM Software Upgrade Procedure
•![]() Upgrading the VEMs Manually from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
Upgrading the VEMs Manually from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
Choosing a VEM Software Upgrade Procedure
This section describes how you can upgrade the ESX/ESXi host with the VEM software installed or install or upgrade the VEM software.
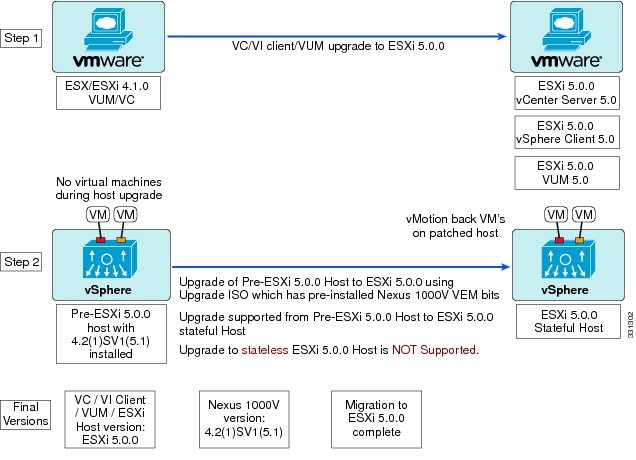
Figure 7-4 and Figure 7-5 show recommended workflows depending on the version of Cisco Nexus 1000V software that you have installed. These workflows are for stateful ESXi hosts. For information on stateless ESXi hosts, see Chapter 2, "Installing the VEM Software on a Stateless ESXi Host" section in the Cisco Nexus 1000V Installation and Upgrade Guide, Release 4.2(1)SV1(5.1) at http://www.cisco.com/en/US/docs/switches/datacenter/nexus1000/sw/4_2_1_s_v_1_5_1/install_upgrade/vsm_vem/guide/n1000v_installupgrade_install.html#wp1177567.
Figure 7-4 describes the upgrade workflow with Cisco Nexus 1000V Release 4.2(1)SV1(4) or SV1(4a) installed.
Figure 7-4 Workflow with a Cisco Nexus 1000V Version 4.2(1)SV1(4) or SV1(4a) Installed
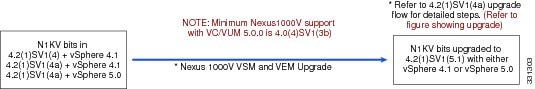
Figure 7-5 describes the upgrade workflow with Cisco Nexus 1000V Release 4.2(1)SV1(5.1) installed and you are upgrading from VMware 4.1 to 5.0.
Figure 7-5 Workflow with Cisco Nexus 1000V 4.2(1)SV1(5.1) Installed and Upgrading ESX from 4.1 to 5.0
You can upgrade the ESX/ESXi host as follows:

Note ![]() The upgrade ISO can be generated by using the procedure in the "Creating an Upgrade ISO with a VMware ESX Image and a Cisco Nexus 1000V VEM Image" section of the Cisco Nexus 1000V Installation and Upgrade Guide, Release 4.2(1)SV1(5.1) at http://www.cisco.com/en/US/docs/switches/datacenter/nexus1000/sw/4_2_1_s_v_1_5_1/install_upgrade/vsm_vem/guide/n1000v_installupgrade_upgrade_vmware.html#wp706205
The upgrade ISO can be generated by using the procedure in the "Creating an Upgrade ISO with a VMware ESX Image and a Cisco Nexus 1000V VEM Image" section of the Cisco Nexus 1000V Installation and Upgrade Guide, Release 4.2(1)SV1(5.1) at http://www.cisco.com/en/US/docs/switches/datacenter/nexus1000/sw/4_2_1_s_v_1_5_1/install_upgrade/vsm_vem/guide/n1000v_installupgrade_upgrade_vmware.html#wp706205
•![]() Upgrading the ESX/ESXi host with VEM software installed.
Upgrading the ESX/ESXi host with VEM software installed.
•![]() If you are using VUM to upgrade the host:
If you are using VUM to upgrade the host:
–![]() Prior to VMware vSphere 5.0, you must create a host patch baseline and include the appropriate VMware patch or update bulletins and the corresponding Cisco Nexus 1000V VEM bulletin in the baseline. You can then upgrade the host by applying the baseline to the host and remediating.
Prior to VMware vSphere 5.0, you must create a host patch baseline and include the appropriate VMware patch or update bulletins and the corresponding Cisco Nexus 1000V VEM bulletin in the baseline. You can then upgrade the host by applying the baseline to the host and remediating.
–![]() If you are using the vCLI, enter the vihostupdate command or the esxupdate command. For more information, see the "Installing ESXi 5.0.0 Host Software Using the CLI" section. See Appendix A, "Installing and Upgrading VMware" of the Cisco Nexus 1000V Installation and Upgrade Guide, Release 4.2(1)SV1(5.1) at
If you are using the vCLI, enter the vihostupdate command or the esxupdate command. For more information, see the "Installing ESXi 5.0.0 Host Software Using the CLI" section. See Appendix A, "Installing and Upgrading VMware" of the Cisco Nexus 1000V Installation and Upgrade Guide, Release 4.2(1)SV1(5.1) at
http://www.cisco.com/en/US/docs/switches/datacenter/nexus1000/sw/4_2_1_s_v_1_5_1/install_upgrade/vsm_vem/guide/n1000v_installupgrade_upgrade_vmware.html#wp635033.
•![]() Upgrading the VEM software
Upgrading the VEM software
–![]() When VEM upgrades are triggered from the VSM, the VEM software is automatically upgraded on the host.
When VEM upgrades are triggered from the VSM, the VEM software is automatically upgraded on the host.
–![]() If you are using the vCLI, enter the vihostupdate command or the esxupdate command. For more information, see the "Upgrading the VEM Software Using the CLI" section.
If you are using the vCLI, enter the vihostupdate command or the esxupdate command. For more information, see the "Upgrading the VEM Software Using the CLI" section.
Upgrading the VEMs Using VMware Update Manager from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
The following section describes how to update the Cisco Nexus 1000V from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)by using the VUM.
PROCEDURE

Step 1 ![]() Display the current configuration.
Display the current configuration.
switch (config)# show vmware vem upgrade status
Upgrade VIBs: System VEM Image
Upgrade Status:
Upgrade Notification Sent Time:
Upgrade Status Time(vCenter):
Upgrade Start Time:
Upgrade End Time(vCenter):
Upgrade Error:
Upgrade Bundle ID:
VSM: VEM400-201107031-RG
DVS: VEM400-201101030-BG

Note ![]() The minimum version of Cisco Nexus 1000V for VMware ESXi 5.0.0 hosts is Release 4.2(1)SV1(4a).
The minimum version of Cisco Nexus 1000V for VMware ESXi 5.0.0 hosts is Release 4.2(1)SV1(4a).
Step 2 ![]() Coordinate with and notify the server administrator of the VEM upgrade process.
Coordinate with and notify the server administrator of the VEM upgrade process.
switch (config)# vmware vem upgrade notify
Warning:
Please ensure the hosts are running compatible ESX versions for the upgrade. Refer to corresponding "Cisco Nexus 1000V and VMware Compatibility Information" guide.
Step 3 ![]() Verify that the upgrade notification was sent.
Verify that the upgrade notification was sent.
switch# show vmware vem upgrade status
Upgrade VIBs: Upgrade VEM Image
Upgrade Status: Upgrade Availability Notified in vCenter
Upgrade Notification Sent Time: Sun May 9 22:04:54 2010
Upgrade Status Time(vCenter):
Upgrade Start Time:
Upgrade End Time(vCenter):
Upgrade Error:
Upgrade Bundle ID:
VSM: VEM400-201107031-RG
DVS: VEM400-201101030-BG

Note ![]() Verify that the Upgrade Status contains the highlighted text. If the text is not present, check the Upgrade Error line and see the Cisco Nexus 1000V Troubleshooting Guide, Release 4.2(1)SV1(5.1).
Verify that the Upgrade Status contains the highlighted text. If the text is not present, check the Upgrade Error line and see the Cisco Nexus 1000V Troubleshooting Guide, Release 4.2(1)SV1(5.1).
Step 4 ![]() Verify that the server administrator has accepted the upgrade in vCenter.
Verify that the server administrator has accepted the upgrade in vCenter.
For more information about how the server administrator accepts the VEM upgrade, see the "Accepting the VEM Upgrade in vCenter Server" section.
Coordinate the notification acceptance with the server administrator. After the server administrator accepts the upgrade, proceed with the VEM upgrade.
switch# show vmware vem upgrade status
Upgrade VIBs: Upgrade VEM Image
Upgrade Status: Upgrade Accepted by vCenter Admin
Upgrade Notification Sent Time: Sun May 9 22:04:54 2010
Upgrade Status Time(vCenter): Tue May 11 07:42:32 2010
Upgrade Start Time:
Upgrade End Time(vCenter):
Upgrade Error:
Upgrade Bundle ID:
VSM: VEM400-201107031-RG
DVS: VEM400-201101030-BG

Note ![]() Verify that the Upgrade Status contains the highlighted text. If the text is not present, check the Upgrade Error line and see the Cisco Nexus 1000V Troubleshooting Guide, Release 4.2(1)SV1(5.1).
Verify that the Upgrade Status contains the highlighted text. If the text is not present, check the Upgrade Error line and see the Cisco Nexus 1000V Troubleshooting Guide, Release 4.2(1)SV1(5.1).
Step 5 ![]() Initiate the VUM upgrade process.
Initiate the VUM upgrade process.

Note ![]() Before entering the following command, communicate with the server administrator to confirm that the VUM process is operational.
Before entering the following command, communicate with the server administrator to confirm that the VUM process is operational.
vCenter locks the DVS and triggers VUM to upgrade the VEMs.
switch# vmware vem upgrade proceed
switch# show vmware vem upgrade status
Upgrade VIBs: Upgrade VEM Image
Upgrade Status: Upgrade In Progress in vCenter
Upgrade Notification Sent Time: Wed Mar 17 15:19:05 2010
Upgrade Status Time(vCenter): Wed Mar 17 17:28:46 2010
Upgrade Start Time: Wed Mar 17 15:20:06 2010
Upgrade End Time(vCenter):
Upgrade Error:
Upgrade Bundle ID:
VSM: VEM400-201107031-RG
DVS: VEM400-201107031-RG

Note ![]() The DVS bundle ID is updated and is highlighted.
The DVS bundle ID is updated and is highlighted.

Note ![]() If the ESX/ESXi host is using ESX/ESXi 4.1.0 or later releases and your DRS settings are enabled to allow it, VUM automatically vMotions the VMs from the host to another host in the cluster and places the ESX/ESXi in maintenance mode to upgrade the VEM. This process is continued for other hosts in the DRS cluster until all the hosts are upgraded in the cluster.
If the ESX/ESXi host is using ESX/ESXi 4.1.0 or later releases and your DRS settings are enabled to allow it, VUM automatically vMotions the VMs from the host to another host in the cluster and places the ESX/ESXi in maintenance mode to upgrade the VEM. This process is continued for other hosts in the DRS cluster until all the hosts are upgraded in the cluster.
Step 6 ![]() Check for the upgrade complete status.
Check for the upgrade complete status.
switch# show vmware vem upgrade status
Upgrade VIBs: System VEM Image
Upgrade Status: Upgrade Complete in vCenter
Upgrade Notification Sent Time: Wed Mar 17 15:19:05 2010
Upgrade Status Time(vCenter): Wed Mar 17 17:28:46 2010
Upgrade Start Time: Wed Mar 17 15:20:06 2010
Upgrade End Time(vCenter): Wed Mar 17 17:30:48 2010
Upgrade Error:
Upgrade Bundle ID:
VSM: VEM400-201107031-RG
DVS: VEM400-201107031-RG
Step 7 ![]() Clear the VEM upgrade status after the upgrade process is complete.
Clear the VEM upgrade status after the upgrade process is complete.
switch# vmware vem upgrade complete
switch# show vmware vem upgrade status
Upgrade VIBs: Upgrade VEM Image
Upgrade Status:
Upgrade Notification Sent Time:
Upgrade Status Time(vCenter):
Upgrade Start Time:
Upgrade End Time(vCenter):
Upgrade Error:
Upgrade Bundle ID:
VSM: VEM400-201107031-RG
DVS: VEM400-201107031-RG
Step 8 ![]() Verify that the upgrade process is complete.
Verify that the upgrade process is complete.
switch# show module
Mod Ports Module-Type Model Status
--- ----- -------------------------------- ------------------ ------------
1 0 Virtual Supervisor Module Nexus1000V ha-standby
2 0 Virtual Supervisor Module Nexus1000V active *
3 248 Virtual Ethernet Module NA ok
4 248 Virtual Ethernet Module NA ok
Mod Sw Hw
--- --------------- ------
1 4.2(1)SV1(5.1) 0.0
2 4.2(1)SV1(5.1) 0.0
3 4.2(1)SV1(5.1) VMware ESXi 5.0.0 Releasebuild-260247 (2.0)
4 4.2(1)SV1(5.1) VMware ESXi 5.0.0 Releasebuild-260247 (2.0)
Mod MAC-Address(es) Serial-Num
--- -------------------------------------- ----------
1 00-19-07-6c-5a-a8 to 00-19-07-6c-62-a8 NA
2 00-19-07-6c-5a-a8 to 00-19-07-6c-62-a8 NA
3 02-00-0c-00-03-00 to 02-00-0c-00-03-80 NA
4 02-00-0c-00-04-00 to 02-00-0c-00-04-80 NA
Mod Server-IP Server-UUID Server-Name
--- --------------- ------------------------------------ --------------------
1 10.78.109.100 NA NA
2 10.78.109.100 NA NA
3 10.78.109.104 1ee15784-f2e8-383e-8132-9026577ca1bb 10.78.109.104
4 10.78.109.102 44454c4c-4700-104e-804d-cac04f563153 10.78.109.102
* this terminal session

Note ![]() The line with the bold characters in the preceding example displays that all VEMs are upgraded to Release 4.2(1)SV1(5.1).
The line with the bold characters in the preceding example displays that all VEMs are upgraded to Release 4.2(1)SV1(5.1).
Step 9 ![]() The upgrade is complete.
The upgrade is complete.
Upgrading the VEMs Manually from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1)
The following section describes how to upgrade Cisco Nexus 1000V from Release 4.2(1)SV1(4) or 4.2(1)SV1(4a) to Release 4.2(1)SV1(5.1) manually.
BEFORE YOU BEGIN
Before starting the procedure, you must know or do the following:

Note ![]() If VUM is installed, it should be disabled.
If VUM is installed, it should be disabled.
To manually install or upgrade the Cisco Nexus 1000V VEM on an ESX/ESXi host by following the steps in the "Upgrading the VEM Software Using the CLI" section.
To upgrade the VEMs manually, perform the following steps as network administrator:

Note ![]() This procedure is performed by the network administrator. Before proceeding with the upgrade, make sure that the VMs are powered off if you are not running the required patch level.
This procedure is performed by the network administrator. Before proceeding with the upgrade, make sure that the VMs are powered off if you are not running the required patch level.

PROCEDURE
Step 1 ![]() Coordinate with and notify the server administrator of the VEM upgrade process.
Coordinate with and notify the server administrator of the VEM upgrade process.
switch (config)# vmware vem upgrade notify
Warning:
Please ensure the hosts are running compatible ESX versions for the upgrade. Refer to corresponding "Cisco Nexus 1000V and VMware Compatibility Information" guide.
Step 2 ![]() Verify that the upgrade notification was sent.
Verify that the upgrade notification was sent.
switch (config)# show vmware vem upgrade status
Upgrade Status: Upgrade Availability Notified in vCenter
Upgrade Notification Sent Time: Sun May 9 22:04:54 2010
Upgrade Status Time(vCenter):
Upgrade Start Time:
Upgrade End Time(vCenter):
Upgrade Error:
Upgrade Bundle ID:
VSM: VEM400-201107031-RG
DVS: VEM400-201101030-RG
Step 3 ![]() Verify that the server administrator has accepted the upgrade in vCenter Server.
Verify that the server administrator has accepted the upgrade in vCenter Server.
For details about the server administrator accepting the VEM upgrade, see the "Accepting the VEM Upgrade in vCenter Server" section.
After the server administrator accepts the upgrade, proceed with the VEM upgrade.
switch# show vmware vem upgrade status
Upgrade VIBs: Upgrade VEM Image
Upgrade Status: Upgrade Accepted by vCenter Admin
Upgrade Notification Sent Time: Sun May 9 22:04:54 2010
Upgrade Status Time(vCenter): Tue May 11 07:42:32 2010
Upgrade Start Time:
Upgrade End Time(vCenter):
Upgrade Error:
Upgrade Bundle ID:
VSM: VEM400-201107031-RG
DVS: VEM400-201101030-BG
Step 4 ![]() Perform on of the following:
Perform on of the following:
•![]() If the ESX host is not hosting the VSM, proceed to Step 5.
If the ESX host is not hosting the VSM, proceed to Step 5.
•![]() If the ESX host is hosting the VSM, coordinate with the server administrator to migrate the VSM to a host that is not being upgraded. Proceed to Step 5.
If the ESX host is hosting the VSM, coordinate with the server administrator to migrate the VSM to a host that is not being upgraded. Proceed to Step 5.
Step 5 ![]() Initiate the Cisco Nexus 1000V Bundle ID upgrade process.
Initiate the Cisco Nexus 1000V Bundle ID upgrade process.

Note ![]() If VUM is enabled in the vCenter environment, disable it before entering the vmware vem upgrade proceed command to prevent the new VIBs from being pushed to all the hosts.
If VUM is enabled in the vCenter environment, disable it before entering the vmware vem upgrade proceed command to prevent the new VIBs from being pushed to all the hosts.
Enter the vmware vem upgrade proceed command so that the Cisco Nexus 1000V Bundle ID on vCenter Server gets updated. If VUM is enabled and you do not update the Bundle ID, an incorrect VIB version is pushed to the VEM when you next add the ESX to the VSM.
switch# vmware vem upgrade proceed

Note ![]() If VUM is not installed, the "The object or item referred to could not be found" error appears in the vCenter Server's task bar. You can ignore this error message.
If VUM is not installed, the "The object or item referred to could not be found" error appears in the vCenter Server's task bar. You can ignore this error message.
switch# show vmware vem upgrade status
Upgrade VIBs: Upgrade VEM Image
Upgrade Status: Upgrade in Progress in vCenter
Upgrade Notification Sent Time: Wed Mar 17 15:19:05 2010
Upgrade Status Time(vCenter): Wed Mar 17 17:28:46 2010
Upgrade Start Time: Wed Mar 17 15:20:06 2010
Upgrade End Time(vCenter):
Upgrade Error:
Upgrade Bundle ID:
VSM: VEM400-201107031-RG
DVS: VEM400-201107031-RG
Step 6 ![]() Check for the Upgrade Complete status.
Check for the Upgrade Complete status.
switch# show vmware vem upgrade status
Upgrade VIBs: Upgrade VEM Image
Upgrade Status: Upgrade Complete in vCenter
Upgrade Notification Sent Time: Wed Mar 17 15:19:05 2010
Upgrade Status Time(vCenter): Wed Mar 17 17:28:46 2010
Upgrade Start Time: Wed Mar 17 15:20:06 2010
Upgrade End Time(vCenter): Wed Mar 17 17:28:48 2010
Upgrade Error:
Upgrade Bundle ID:
VSM: VEM400-201107031-RG
DVS: VEM400-201107031-RG
Step 7 ![]() Coordinate with and wait until the server administrator upgrades all ESX host VEMs with the new VEM software release and informs you that the upgrade process is complete.
Coordinate with and wait until the server administrator upgrades all ESX host VEMs with the new VEM software release and informs you that the upgrade process is complete.
The server administrator performs the manual upgrade using the vihostupdate command or the esxcli command. For more information, see the "Upgrading the VEM Software Using the CLI" section.
Step 8 ![]() Clear the VEM upgrade status after the upgrade process is complete.
Clear the VEM upgrade status after the upgrade process is complete.
switch# vmware vem upgrade complete
switch# show vmware vem upgrade status
Upgrade VIBs: Upgrade VEM Image
Upgrade Status:
Upgrade Notification Sent Time:
Upgrade Status Time(vCenter):
Upgrade Start Time:
Upgrade End Time(vCenter):
Upgrade Error:
Upgrade Bundle ID:
VSM: VEM400-201107031-RG
DVS: VEM400-201107031-RG
Step 9 ![]() Verify that the upgrade process is complete.
Verify that the upgrade process is complete.
switch# show module
Mod Ports Module-Type Model Status
--- ----- -------------------------------- ------------------ ------------
1 0 Virtual Supervisor Module Nexus1000V ha-standby
2 0 Virtual Supervisor Module Nexus1000V active *
3 248 Virtual Ethernet Module NA ok
4 248 Virtual Ethernet Module NA ok
Mod Sw Hw
--- --------------- ------
1 4.2(1)SV1(4a) 0.0
2 4.2(1)SV1(4a) 0.0
3 4.2(1)SV1(5.1) VMware ESXi 4.1.0 Releasebuild-260247 (2.0)
4 4.2(1)SV1(5.1) VMware ESXi 4.1.0 Releasebuild-260247 (2.0)
Mod MAC-Address(es) Serial-Num
--- -------------------------------------- ----------
1 00-19-07-6c-5a-a8 to 00-19-07-6c-62-a8 NA
2 00-19-07-6c-5a-a8 to 00-19-07-6c-62-a8 NA
3 02-00-0c-00-03-00 to 02-00-0c-00-03-80 NA
4 02-00-0c-00-04-00 to 02-00-0c-00-04-80 NA
Mod Server-IP Server-UUID Server-Name
--- --------------- ------------------------------------ --------------------
1 10.78.109.100 NA NA
2 10.78.109.100 NA NA
3 10.78.109.104 1ee15784-f2e8-383e-8132-9026577ca1bb 10.78.109.104
4 10.78.109.102 44454c4c-4700-104e-804d-cac04f563153 10.78.109.102
* this terminal session

Note ![]() The line with the bold characters in the preceding example display that all VEMs are upgraded to Release 4.2(1)SV1(5.1).
The line with the bold characters in the preceding example display that all VEMs are upgraded to Release 4.2(1)SV1(5.1).
Step 10 ![]() Run the VSM backup procedure.
Run the VSM backup procedure.
See the "Configuring VSM Backup and Recovery" chapter of the Cisco Nexus 1000V System Management Configuration Guide, Release 4.2(1)SV1(5.1).
The upgrade is complete.
Accepting the VEM Upgrade in vCenter Server
This section describes the steps that a server administrator follows to accept a VEM upgrade in vCenter Server.
BEFORE YOU BEGIN
Before starting the procedure, you must know or do the following:
•![]() The network and server administrators must coordinate the upgrade procedure with each other.
The network and server administrators must coordinate the upgrade procedure with each other.
•![]() You have received a notification in vCenter Server that a VEM software upgrade is available.
You have received a notification in vCenter Server that a VEM software upgrade is available.
Accepting the VEM Upgrade
The server administrator accepts the VEM upgrade after the network administrator has upgraded the VSM and notified vCenter server of the availability of the new VEM software version.

Note ![]() This procedure is performed by the server administrator.
This procedure is performed by the server administrator.
Step 1 ![]() In vCenter Server, choose Inventory > Networking.
In vCenter Server, choose Inventory > Networking.
Step 2 ![]() Click the vSphere Client DVS Summary tab to check for the availability of a software upgrade (see Figure 7-6).
Click the vSphere Client DVS Summary tab to check for the availability of a software upgrade (see Figure 7-6).
Figure 7-6 vSphere Client DVS Summary Tab
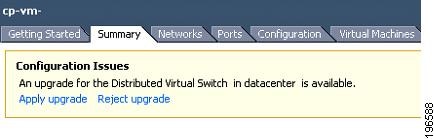
Step 3 ![]() Click Apply upgrade.
Click Apply upgrade.
The following actions occur:
•![]() The network administrator is notified that you are ready to apply the upgrade to the VEMs.
The network administrator is notified that you are ready to apply the upgrade to the VEMs.
•![]() The network administrator notifies vCenter to proceed with the VEM upgrades.
The network administrator notifies vCenter to proceed with the VEM upgrades.
•![]() If you are using VUM, vCenter locks the DVS and triggers VUM to upgrade the VEMs.
If you are using VUM, vCenter locks the DVS and triggers VUM to upgrade the VEMs.
Upgrading the VEM Software Using the CLI
You can upgrade the Cisco Nexus 1000V VEM software on an ESX/ESXi host by using the CLI.
BEFORE YOU BEGIN
Before starting the procedure, you must know or do the following:
•![]() If you are using the vCLI, do the following:
If you are using the vCLI, do the following:
–![]() You have downloaded and installed the VMware vCLI. For information about installing the vCLI, see the VMware vCLI documentation.
You have downloaded and installed the VMware vCLI. For information about installing the vCLI, see the VMware vCLI documentation.
–![]() You are logged in to the remote host where the vCLI is installed.
You are logged in to the remote host where the vCLI is installed.

Note ![]() The vSphere command-line interface (vCLI) command set allows you to enter common system administration commands against ESX/ESXi systems from any machine with network access to those systems. You can also enter most vCLI commands against a vCenter Server system and target any ESX/ESXi system that the vCenter Server system manages. vCLI commands are especially useful for ESXi hosts because ESXi does not include a service console.
The vSphere command-line interface (vCLI) command set allows you to enter common system administration commands against ESX/ESXi systems from any machine with network access to those systems. You can also enter most vCLI commands against a vCenter Server system and target any ESX/ESXi system that the vCenter Server system manages. vCLI commands are especially useful for ESXi hosts because ESXi does not include a service console.
•![]() If you are using the esxupdate command:
If you are using the esxupdate command:
–![]() You are logged in to the ESX host.
You are logged in to the ESX host.
•![]() Check the Cisco Nexus 1000V Compatibility Information, Release 4.2(1)SV1(5.1), for compatible versions.
Check the Cisco Nexus 1000V Compatibility Information, Release 4.2(1)SV1(5.1), for compatible versions.
•![]() You have already copied the VEM software installation file to the /tmp directory.
You have already copied the VEM software installation file to the /tmp directory.
•![]() You know the name of the VEM software file to be installed.
You know the name of the VEM software file to be installed.
PROCEDURE
Step 1 ![]() Go to the directory where the new VEM software was copied.
Go to the directory where the new VEM software was copied.
[root@serialport -]# cd tmp
[root@serialport tmp]#
Step 2 ![]() Determine the upgrade method that you want to use and enter the appropriate command:
Determine the upgrade method that you want to use and enter the appropriate command:
•![]() If you are using the vCLI, enter the vihostupdate command and install the ESX/ ESXi and VEM software simultaneously.
If you are using the vCLI, enter the vihostupdate command and install the ESX/ ESXi and VEM software simultaneously.
•![]() If you are on an ESXi host running ESXi 4.1, enter one of the following commands:
If you are on an ESXi host running ESXi 4.1, enter one of the following commands:
vihostupdate --install --bundle [path to Cisco updated VEM offline bundle]" --server [vsphere host IP address]

Note ![]() Put the host in maintenance mode before you enter the following command.
Put the host in maintenance mode before you enter the following command.
[root@serialport tmp]# vihostupdate --install --bundle VEM400-201107401.zip --server
192.0.2.0
Enter username: root
Enter password:
Please wait installation in progress ...
The update completed successfully, but the system needs to be rebooted for the changes to be effective.
[root@serialport tmp]#
•![]() If you are using the esxupdate command, from the ESX host /tmp directory, install the VEM software as shown in the following example:
If you are using the esxupdate command, from the ESX host /tmp directory, install the VEM software as shown in the following example:

Note ![]() When using the esxupdate command, you must log in to each host and enter the following command.
When using the esxupdate command, you must log in to each host and enter the following command.
esxupdate -b [VMware offline update bundle] update
This command loads the software manually onto the host, loads the kernel modules, and starts the VEM Agent on the running system.
Step 3 ![]() Display values with which to compare to Cisco Nexus 1000V Compatibility Information, Release 4.2(1)SV1(5.1).
Display values with which to compare to Cisco Nexus 1000V Compatibility Information, Release 4.2(1)SV1(5.1).
[root@serialport tmp]# vmware -v
VMware ESXi 5.0.0 build-469512
The highlighted text shows the upgraded Cisco VEM.
root@serialport tmp]# esxupdate query
-----Bulletin ID----- -----Installed----- ----------Summary----------
ESXi400-Update01 2011-07-28T14:30:58 VMware ESXi 4.0 Update 1
VEM400-201107273451115-BG 2011-07-28T14:48:36 Cisco Nexus 1000V 4.2(1)SV1(4a)
[root@host212 ~]# vem status -v
Package vssnet-esx4.1.0-00000-release
Version 4.2.1.1.4.1.0-1.9.1
Build 1
Date Wed Jul 27 04:42:14 PDT 2011
Number of PassThru NICs are 0
VEM modules are loaded
Switch Name Num Ports Used Ports Configured Ports MTU Uplinks
vSwitch0 32 2 32 1500 vmnic0
DVS Name Num Ports Used Ports Configured Ports Uplinks
byru-215 256 56 256 vmnic2,vmnic1
Number of PassThru NICs are 0
VEM Agent (vemdpa) is running
[root@host212 ~]# vem version -v
Number of PassThru NICs are 0
Running esx version -208167 x86_64
VEM Version: 4.2.1.1.4.1.0-1.9.1
VSM Version: 4.2(1)SV1(4a)
System Version: VMware ESX 4.0.0 Releasebuild-208167
Step 4 ![]() Display that the VEMs were upgraded by entering the following commands from the VSM:
Display that the VEMs were upgraded by entering the following commands from the VSM:
switch# show module
Mod Ports Module-Type Model Status
--- ----- -------------------------------- ------------------ ------------
1 0 Virtual Supervisor Module Nexus1000V active *
2 0 Virtual Supervisor Module Nexus1000V standby
3 248 Virtual Ethernet Module NA ok
Mod Sw Hw
--- --------------- ------
1 4.0(4)SV1(5.1) 0.0
2 4.0(4)SV1(5.1) 0.0
3 4.2(1)SV1(5.1) VMware ESXi 4.0.0 build-208167 (1.9)
Mod MAC-Address(es) Serial-Num
--- -------------------------------------- ----------
1 00-19-07-6c-5a-a8 to 00-19-07-6c-62-a8 NA
4 02-00-0c-00-04-00 to 02-00-0c-00-04-80 NA
Mod Server-IP Server-UUID Server-Name
--- --------------- ------------------------------------ --------------------
1 10.104.62.220 NA NA
4 10.104.62.217 3fa746d4-de2f-11de-bd5d-c47d4f7ca460 visor

Note ![]() The highlighted text in the previous command output confirms that the upgrade was successful.
The highlighted text in the previous command output confirms that the upgrade was successful.
Step 5 ![]()
•![]() If the upgrade was successful, the installation procedure is complete.
If the upgrade was successful, the installation procedure is complete.
You have completed this procedure.
Upgrading from Releases 4.0(4)SV1(3, 3a, 3b, 3c, 3d) to Release 4.2(1)SV1(5.1)
Upgrading from Releases 4.0(4)SV1(3, 3a, 3b, 3c, 3d) to Release 4.2(1)VSG1(3.1) is a two-step process.
1. ![]() See the "Upgrading from Releases 4.0(4)SV1(3, 3a, 3b, 3c, 3d) to Release 4.2(1)SV1(4a)" section in the Cisco Nexus 1000V Software Upgrade Guide, Release 4.2(1)SV1(4a).
See the "Upgrading from Releases 4.0(4)SV1(3, 3a, 3b, 3c, 3d) to Release 4.2(1)SV1(4a)" section in the Cisco Nexus 1000V Software Upgrade Guide, Release 4.2(1)SV1(4a).
2. ![]() See the "Upgrading to Release 4.2(1)SV1(5.1)" section.
See the "Upgrading to Release 4.2(1)SV1(5.1)" section.
 Feedback
Feedback