- Cisco Virtual Security Gateway for Nexus 1000V Series Switch Configuration Guide, Release 4.2(1)VSG1(1)
- Table of Content
- Preface
- Cisco Virtual Security Gateway Overview
- Cisco Virtual Security Gateway Command-Line Interface
- Configuring the Cisco Virtual Security Gateway Port Profile on the Cisco Nexus 1000V Series Switch
- Cisco Virtual Security Gateway System Management
- Cisco Virtual Security Gateway High Availability
- Cisco Virtual Security Gateway Firewall Profiles and Policy Objects
- Index
Cisco Virtual Security Gateway for Nexus 1000V Series Switch Configuration Guide, Release 4.2(1)VSG1(1)
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- April 11, 2014
Chapter: Cisco Virtual Security Gateway Firewall Profiles and Policy Objects
Cisco Virtual Security Gateway Firewall Profiles and Policy Objects
This chapter describes the Cisco Virtual Security Gateway (VSG) firewall profiles and policy objects.
Information About Cisco VSG Firewall Policy Objects
Use the Cisco Virtual Network Management Center (VNMC) to do all configuration and management of your Cisco VSG.

Note When the policy-agent (PA) is installed, the command-line interface (CLI) is unavailable for configuring policy-related objects on the Cisco VSG. When the PA is uninstalled (removed), you can again configure the policies (and policy objects) from the CLI; however, we recommend that you use the Cisco VNMC for all configuration and management of your VSG firewall policy objects.
Cisco VSG Prerequisites, Guidelines, and Limitations
Cisco VSG policy objects have the following prerequisites:
- You must have the NEXUS_VSG_SERVICES_PKG license installed on the Cisco Nexus 1000V Series switch.
- Ensure that you have enough licenses to cover the number of ESX hosts (VEMs) you want to protect.
- Create port profiles for the service and HA interfaces of Cisco VSG on Virtual Supervisor Module (VSM).
- You have the Cisco VSG software installed and the basic installation completed. For details, see the Cisco Virtual Security Gateway, Release 4.2(1)VSG1(1) and Cisco Virtual Network Management Center, Release 1.0.1 Installation Guide.
- The data IP address and management IP addresses must be configured. To configure the data IP address, see the Cisco Virtual Security Gateway, Release 4.2(1)VSG1(1) and Cisco Virtual Network Management Center, Release 1.0.1 Installation Guide.
- You have the attribute details required for your security policies.
- You are logged in to the Cisco VSG CLI in EXEC mode.
The Cisco VSG has the following configuration guidelines and limitations:
- The Management VLAN must be on the VM network vSwitch
- The HA and Service VLANs are configured on the uplink ports. (They are not required to be on the system VLAN.)
- Do not configure the same network IP address on the management and data interfaces (data0) of the Cisco VSG.
For any configuration and management tasks, the following requirements must be met:
- Your Cisco VSG software must be operating with three network adapters. The network labels are as follows:
–![]() Service (Eth0) as your port-profile
Service (Eth0) as your port-profile
–![]() Mgmt (Eth1) as your management VLAN
Mgmt (Eth1) as your management VLAN
–![]() HA (Eth2) as your port-profile
HA (Eth2) as your port-profile
- You have the Cisco VSG VM powered on and the data interface IP address (for data0) and management interface IP address configured.
See the Cisco Virtual Security Gateway, Release 4.2(1)VSG1(1) and Cisco Virtual Network Management Center, Release 1.0.1 Installation Guide, for details about assigning network labels to the network adapters.
Default Settings
Table 6-1 lists the default setting for the Cisco VSG parameters.
Cisco VSG Firewall Policy Objects
This section includes the following topics:
Zones
A zone is a logical group of virtual machines (VMs) or hosts. Zones simplify policy writing by allowing users to write policies based on zone attributes using zone names. The zone definitions map the VMs to the zones. The logical group definition can be based on the attributes associated with a VM or a host, such as VM attributes defined in the vCenter. Zone definitions can be written as condition-based subnet and endpoint IP addresses.
Because zones and object groups can be shared between various rules with different directions, the attributes used in an object group should not have a directional sense and must be neutral attributes.
This example shows how the zone is expressed in the show running-config command output:
Object Groups
An object group is a set of conditions that are relevant to an attribute. Because object groups and zones can be shared between various rules with different directions, the attributes used in an object group condition should not have a directional sense and must be neutral. An object group is a secondary policy object that assists in writing firewall rules. A rule condition can refer to an object group by using an operator.
This example shows how the object groups are expressed in the show running-config command output:
Rules
Firewall rules can consist of multiple conditions and actions. Rules can be defined in a policy as a condition-based subnet or endpoint IP addresses and VM attributes.
Actions are the result of a policy evaluation. You can define and associate one or more of the following actions within a specified rule:
This example shows how the rule is expressed in the show running-config command output:
Policies
Firewall policies bind rules to a given policy, creating a rank among the rules. A policy enforces network traffic on a Cisco VSG and is constructed by using the following set of policy objects:
A policy is bound to a Cisco VSG using a set of indirect associations. The security administrator can configure a security profile and then refer to a policy name within the security profile. The security profile is associated with a port profile that has a reference to a Cisco VSG.
This example shows how the policy is expressed in the show running-config command output:
This example shows how conditions are expressed in the show running-config command output:
Cisco Virtual Security Gateway Attributes
This section describes Cisco Virtual Security Gateway attributes.
Directional Attributes
A firewall policy is direction sensitive. An attribute in a rule condition requires that you have specified if the attribute is relevant to a source or a destination. The prefixes src., dst., or an attribute name are used to provide the sense of direction.
Neutral Attributes
Because object groups and zones can be shared between various rules with different directions, the attributes used in an object group should not have a directional sense. Attributes without a directional sense (that do not provide a direction prefix such as src. or dst.) are called neutral attributes.
Two rule conditions with different directions can share the same object group definition. A neutral attribute and net.ip-address used in the object-group can be associated with the directional attributes, such as src.net.ip-address and dst.net.ip-address, used in the different rules.
Attribute Classes
Cisco VSG attributes are classified into the following classes:
Attributes are used in configuring policy rules and conditions, or zone definition. Zones can be defined using VM attributes.
Network Attributes
This section describes the VSG network attributes (see Table 6-2 ).
VM Attributes
The VM attributes are attributes that are related to the virtual machine infrastructure and include the following classes of VM attributes:
- Virtual infrastructure attributes—These attributes are obtained from the VMware vCenter and are mapped to the names listed in Table 6-3 .
- Port profile attributes—These attributes are associated with port profiles.
- Custom attributes—These attributes can be configured under a service profile.
Table 6-3 describes the VM attributes supported.
|
vm.name2 |
|
|
vm.host-name 1 |
|
|
vm.os-fullname 1 |
|
|
vm.vapp-name 1 |
|
|
vm.cluster.name 1 |
|
|
vm.inventory-path 1 |
|
|
vm.portprofile-name 1 |
|
Custom attributes from the security profile of the associated port group. Note For every unique custom-attribute xxx, the synthesized attribute name is src.vm.custom.xxx or dst.vm.custom.xxx. The policy uses the synthesized attribute name. |
vm.custom.xxx 1 |
Custom VM attributes are user-defined attributes that can be configured under a service profile.
This example shows how to verify the VM attributes on a Cisco VSG using the show vsg vm command:
Zone Attributes
Table 6-4 lists the zone attributes supported by the Cisco VSG.
Zone name. This is a multi-valued attribute and can belong to multiple zones at the same time. |
zone.name3 |
Security Profiles
The security profile defines custom attributes that can be used to write policies. All the VMs tagged with a given port profile inherit the firewall policies and custom attributes defined in the security profile associated with that port profile. Each custom attribute is configured as a name value pair such as state = CA.
This example shows how to verify the security profile on a Cisco VSG using the show vsg security-profile brief command:
This example shows how to verify the security profile on a Cisco VSG using the show vsg security-profile command:
Viewing Security Profiles and Policies on the Cisco VNMC and the Cisco VSG
The Cisco VNMC GUI provides a view of the Cisco VSG security policy objects. The policy objects shown in the Cisco VNMC GUI are not necessarily shown in the same organizational path location as they appear in the Cisco VSG CLI when you enter the show runnning-config command.
For example, in the Cisco VNMC GUI, if the virtual data center DC1 is under the tenant and the application APP1 is under DC1, the vnsp app1-sp in the APP1 level is pointing to the policy set ps1 at the DC level.
Figure 6-1 shows the Cisco VNMC GUI organization structure.
Figure 6-1 Cisco VNMC Organizational Hierarchy for a Tenant, Data Center, and Application
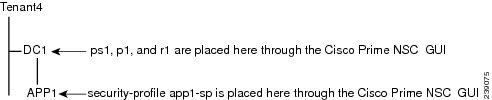
The output of the show running-config command shows that the policy set and its objects are resolved from the APP1 level where the security profile is defined. The actual location of the objects in the Cisco VNMC GUI is at the DC1 level.
The policy object DNs that are shown in the Cisco VSG show running-config command output are shown with a DN relative to where they are resolved from. The policy object DNs are not where the actual policy objects are in the Cisco VNMC organizational hierarchy.
However, security-profiles are shown with the DN where the actual security profile is created on the Cisco VNMC organizational hierarchy.
Policy objects are resolved upwards from where the security-profile is located in the Cisco VNMC organizational hierarchy.
EXAMPLE
In the following example, the VSG is configured with the following specifications:
- The security profile (VNSP) sp1 has policy-set ps1 in which there is a policy p1 that includes a rule, r1.
- The policy-set ps1 is located at root in the organization tree on the Cisco VNMC.
- The policy p1 is located at root in the organization tree on the Cisco VNMC.
- The rule r1 is placed in the policy p1 on the Cisco VNMC (the Cisco VNMC does not allow you to create a rule object in and of itself).
- The security profile sp1 is placed in tenant_d3337/dc1 on the VNMC.
All Cisco VSGs in the tenant_d3337 have the following show-running config command output (this configuration is replicated to all Cisco VSGs in the leaf path):

Note The policy objects above do not actually exist at the DC1 level of the organization tree on the Cisco VNMC, but are resolved from that location in the Cisco VNMC organization tree.
Service Firewall Logging
You can use the service firewall log to test and debug the firewall policies. During a policy evaluation, the policy engine displays the policy results of a policy evaluation. Both the users and the policy writer benefit from this tool when troubleshooting a policy.
BEFORE YOU BEGIN
Before beginning this procedure, you must do or know the following:
- Your Cisco VSG software must be operating with three network adapters. Assign the network labels as follows:
–![]() Service (Eth0) as your port profile
Service (Eth0) as your port profile
–![]() Mgmt (Eth1) as your management VLAN
Mgmt (Eth1) as your management VLAN
–![]() HA (Eth2) as your port profile
HA (Eth2) as your port profile
See the Cisco Virtual Security Gateway, Release 4.2(1)VSG1(1) and Cisco Virtual Network Management Center, Release 1.0.1 Installation Guide for details about assigning network labels to the network adapters.
Verifying the Cisco VSG Configuration
To display the Cisco VSG configuration, use the show running-config command.
 Feedback
Feedback