Cisco Nexus 1000V System Management Configuration Guide, Release 4.0(4)SV1(1)
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- May 20, 2009
Chapter: Configuring SPAN
Configuring Local SPAN and ERSPAN
This chapter describes how to configure the Local and ER Ethernet switched port analyzer (SPAN) feature to monitor traffic and includes the following topics:
•![]() Information About SPAN and ERSPAN
Information About SPAN and ERSPAN
•![]() SPAN Guidelines and Limitations
SPAN Guidelines and Limitations
•![]() Verifying the SPAN Configuration
Verifying the SPAN Configuration
•![]() Feature History for SPAN and ERSPAN
Feature History for SPAN and ERSPAN
Information About SPAN and ERSPAN
The Switched Port Analyzer (SPAN) feature (sometimes called port mirroring or port monitoring) allows network traffic to be analyzed by a network analyzer such as a Cisco SwitchProbe or other Remote Monitoring (RMON) probe.
SPAN lets you monitor traffic on one or more ports, or one or more VLANs, and send the monitored traffic to one or more destination ports where the network analyzer is attached.
This section includes the following topics:
SPAN Sources
The interfaces from which traffic can be monitored are called SPAN sources. These include Ethernet, virtual Ethernet, port-channel, and VLAN. When a VLAN is specified as a SPAN source, all supported interfaces in the VLAN are SPAN sources. Traffic can be monitored in the receive direction, the transmit direction, or both directions for Ethernet and virtual Ethernet source interfaces.
•![]() Receive source (Rx)—Traffic that enters the switch through this source port is copied to the SPAN destination port.
Receive source (Rx)—Traffic that enters the switch through this source port is copied to the SPAN destination port.
•![]() Transmit source (Tx)—Traffic that exits the switch through this source port is copied to the SPAN destination port.
Transmit source (Tx)—Traffic that exits the switch through this source port is copied to the SPAN destination port.
Characteristics of Source Ports
A source port has these characteristics:
•![]() Can be port type Ethernet, virtual Ethernet, port-channel, or VLAN.
Can be port type Ethernet, virtual Ethernet, port-channel, or VLAN.
•![]() Cannot be a destination port.
Cannot be a destination port.
•![]() Can be configured to monitor the direction of traffic —receive, transmit, or both.
Can be configured to monitor the direction of traffic —receive, transmit, or both.
•![]() Source ports can be in the same or different VLANs.
Source ports can be in the same or different VLANs.
•![]() For VLAN SPAN sources, all active ports in the source VLAN are included as source ports.
For VLAN SPAN sources, all active ports in the source VLAN are included as source ports.
•![]() Local SPAN sources must be on the same host (linecard) as the destination port.
Local SPAN sources must be on the same host (linecard) as the destination port.
SPAN Destinations
SPAN destinations refer to the interfaces that monitor source ports. This section includes the following topics:
•![]() Characteristics of Local SPAN Destination Ports
Characteristics of Local SPAN Destination Ports
•![]() Characteristics of ERSPAN Destination Ports
Characteristics of ERSPAN Destination Ports
Characteristics of Local SPAN Destination Ports
Each local SPAN session must have at least one destination port (also called a monitoring port) that receives a copy of traffic from the source ports or VLANs. A destination port has these characteristics:
•![]() Can be any physical or virtual Ethernet port or a port channel.
Can be any physical or virtual Ethernet port or a port channel.
•![]() Cannot be a source port.
Cannot be a source port.
•![]() Is excluded from the source list and is not monitored if it belongs to a source VLAN of any SPAN session.
Is excluded from the source list and is not monitored if it belongs to a source VLAN of any SPAN session.
•![]() Receive copies of transmitted and received traffic for all monitored source ports. If a destination port is oversubscribed, it can become congested. This congestion can affect traffic forwarding on one or more of the source ports.
Receive copies of transmitted and received traffic for all monitored source ports. If a destination port is oversubscribed, it can become congested. This congestion can affect traffic forwarding on one or more of the source ports.
•![]() Do not receive any forwarded traffic except copies of transmitted and received traffic for all monitored source ports.
Do not receive any forwarded traffic except copies of transmitted and received traffic for all monitored source ports.
•![]() Must be on the same host (linecard) as the source port.
Must be on the same host (linecard) as the source port.
•![]() In Local SPAN, the source interface and destination interface are on the same device.
In Local SPAN, the source interface and destination interface are on the same device.
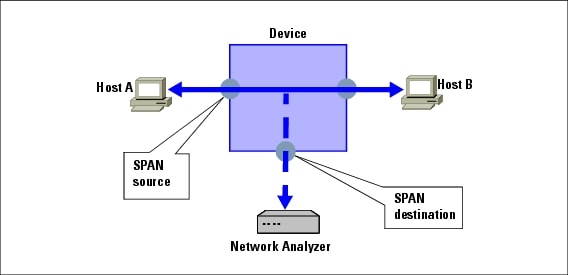
See Figure 9-1, Local SPAN.
Characteristics of ERSPAN Destination Ports
•![]() An ERSPAN destination is specified by an IP address.
An ERSPAN destination is specified by an IP address.
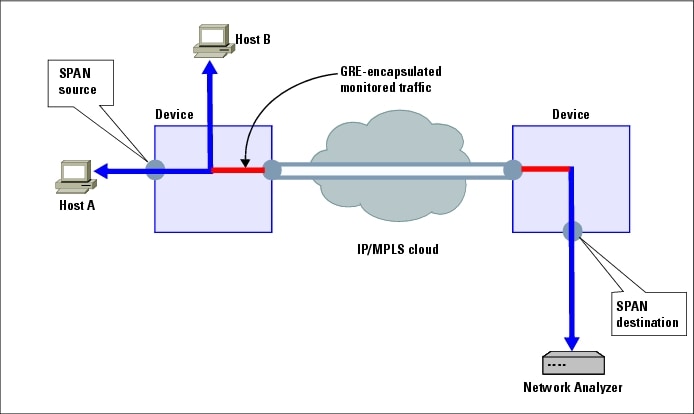
•![]() In ERSPAN, source SPAN interface and destination SPAN interface may be on different devices interconnected by an IP network. ERSPAN traffic is GRE-encapsulated. See Figure 9-2, ERSPAN.
In ERSPAN, source SPAN interface and destination SPAN interface may be on different devices interconnected by an IP network. ERSPAN traffic is GRE-encapsulated. See Figure 9-2, ERSPAN.
Local SPAN
In Local SPAN, the source interface and destination interface are on the same device. The network analyzer is attached directly to the SPAN destination port. The SPAN source can be a port or a VLAN interface.The destination, although usually a port, could also be a VLAN.
Figure 9-1 shows that traffic transmitted by host A is received on the SPAN source interface. Traffic (ACLs, QoS, and so forth) is processed as usual. Traffic is then replicated. The original packet is forwarded on toward host B. The replicated packet is then sent to the destination SPAN interface where the monitor is attached.
Local SPAN can replicate to one or more destination ports. Traffic can be filtered so that only traffic of interest is sent out the destination SPAN interface.
Local SPAN can monitor all traffic received on the source interface including BPDUs.
Figure 9-1 Local SPAN
Encapsulated Remote SPAN
Encapsulated remote (ER) SPAN monitors traffic in multiple network devices across an IP network and sends that traffic in an encapsulated envelope to destination analyzers. In contrast, Local SPAN cannot forward traffic through the IP network. ERSPAN can be used to monitor traffic remotely. ERSPAN sources can be ports or VLANs.
In Figure 9-2, the ingress and egress traffic for host A are monitored using ERSPAN. Encapsulated ERSPAN packets are routed from host A through the routed network to the destination device where they are de-capsulated and forwarded to the attached network analyzer. The destination may also be on the same L2 network as the source.
Figure 9-2 ERSPAN
SPAN Sessions
You can create up to 64 total SPAN sessions (Local SPAN plus ERSPAN) on your local device.
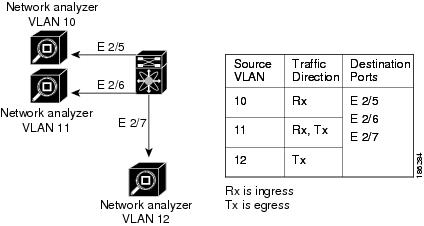
You can also create a SPAN session to monitor multiple VLAN sources and choose only VLANs of interest to transmit on multiple destination ports. For example, you can configure SPAN on a trunk port and monitor traffic from different VLANs on different destination ports.
Figure 9-3 shows a VLAN-based SPAN configuration that copies traffic from three VLANs to three specified destination ports. You can choose which VLANs to allow on each destination port to limit the traffic transmitted. In Figure 9-3, the device transmits packets from one VLAN at each destination port.

Note ![]() VLAN-based SPAN sessions cause all source packets to be copied to all destinations, whether the packets are required at the destination or not. VLAN traffic filtering occurs at transmit destination ports.
VLAN-based SPAN sessions cause all source packets to be copied to all destinations, whether the packets are required at the destination or not. VLAN traffic filtering occurs at transmit destination ports.
Figure 9-3 VLAN-based SPAN Configuration
.
SPAN Guidelines and Limitations
SPAN has the following configuration guidelines and limitations:
•![]() A maximum of 64 SPAN sessions (Local SPAN plus ERSPAN) can be configured on the VSM.
A maximum of 64 SPAN sessions (Local SPAN plus ERSPAN) can be configured on the VSM.
•![]() A maximum of 32 source VLANs are allowed in a session.
A maximum of 32 source VLANs are allowed in a session.
•![]() A maximum of 128 source interfaces are allowed in a session.
A maximum of 128 source interfaces are allowed in a session.

To avoid an overload on uplink ports, use caution when configuring ERSPAN, especially when sourcing VLANs.
•![]() A port can be configured in a maximum of 4 SPAN sessions.
A port can be configured in a maximum of 4 SPAN sessions.
•![]() The destination port used in one SPAN session cannot also be used as the destination port for another SPAN session.
The destination port used in one SPAN session cannot also be used as the destination port for another SPAN session.
•![]() You cannot configure a port as both a source and destination port.
You cannot configure a port as both a source and destination port.
•![]() In a SPAN session, packets that source ports receive may be replicated even though they are not transmitted on the ports. The following are examples of this behavior:
In a SPAN session, packets that source ports receive may be replicated even though they are not transmitted on the ports. The following are examples of this behavior:
–![]() Traffic that results from flooding
Traffic that results from flooding
–![]() Broadcast and multicast traffic
Broadcast and multicast traffic
•![]() For VLAN SPAN sessions switched on the same VLAN with both receive and transmit configured, two packets (one from receive and one from transmit) are forwarded from the destination port.
For VLAN SPAN sessions switched on the same VLAN with both receive and transmit configured, two packets (one from receive and one from transmit) are forwarded from the destination port.
Configuring SPAN
This section describes how to configure SPAN and includes the following procedures.
•![]() Configuring a Local SPAN Session
Configuring a Local SPAN Session
•![]() Configuring an ERSPAN Port Profile
Configuring an ERSPAN Port Profile
•![]() Configuring an ERSPAN Session
Configuring an ERSPAN Session
•![]() Verifying the SPAN Configuration
Verifying the SPAN Configuration
Configuring a Local SPAN Session
Use this procedure to configure a SPAN session.

Note ![]() If you are configuring ERSPAN, see the "Configuring an ERSPAN Session" procedure.
If you are configuring ERSPAN, see the "Configuring an ERSPAN Session" procedure.
BEFORE YOU BEGIN
•![]() You are logged in to the CLI in EXEC mode.
You are logged in to the CLI in EXEC mode.
•![]() You know the number of the SPAN session you are going to configure.
You know the number of the SPAN session you are going to configure.
•![]() The source and destination ports are already configured in either access or trunk mode. For more information, see the Cisco Nexus 1000V Interface Configuration Guide, Release 4.0(4)SV1(1).
The source and destination ports are already configured in either access or trunk mode. For more information, see the Cisco Nexus 1000V Interface Configuration Guide, Release 4.0(4)SV1(1).
•![]() SPAN sessions are created in the shut state by default.
SPAN sessions are created in the shut state by default.
•![]() When you create a SPAN session that already exists, any additional configuration is added to that session. To make sure the session is cleared of any previous configuration, you can delete the session first (see Step 2, no monitor session).
When you create a SPAN session that already exists, any additional configuration is added to that session. To make sure the session is cleared of any previous configuration, you can delete the session first (see Step 2, no monitor session).
•![]() This procedure involves creating the SPAN session in Monitor Configuration mode; and then, optionally, configuring allowed VLANs in Interface Configuration mode.
This procedure involves creating the SPAN session in Monitor Configuration mode; and then, optionally, configuring allowed VLANs in Interface Configuration mode.
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() no monitor session session-number
no monitor session session-number
3. ![]() monitor session session-number
monitor session session-number
4. ![]() description description
description description
5. ![]() source {interface type | vlan} {number | range} [rx | tx | both]
source {interface type | vlan} {number | range} [rx | tx | both]
6. ![]() (Optional) Repeat Step 5 to configure additional SPAN sources.
(Optional) Repeat Step 5 to configure additional SPAN sources.
7. ![]() (Optional) filter vlan {number | range}
(Optional) filter vlan {number | range}
8. ![]() (Optional) Repeat Step 7 to configure all source VLANs to filter.
(Optional) Repeat Step 7 to configure all source VLANs to filter.
9. ![]() destination interface type {number | range}
destination interface type {number | range}
10. ![]() (Optional) Repeat Step 9 to configure all SPAN destination ports.
(Optional) Repeat Step 9 to configure all SPAN destination ports.
11. ![]() no shut
no shut
12. ![]() (Optional) exit
(Optional) exit
13. ![]() (Optional) interface ethernet slot/port[-port]
(Optional) interface ethernet slot/port[-port]
14. ![]() (Optional) switchport trunk allowed vlan {vlan-range | add vlan-range | except vlan-range | remove vlan-range | all | none}
(Optional) switchport trunk allowed vlan {vlan-range | add vlan-range | except vlan-range | remove vlan-range | all | none}
15. ![]() (Optional) Repeat Step 13 and Step 14 to configure the allowed VLANs on each destination port.
(Optional) Repeat Step 13 and Step 14 to configure the allowed VLANs on each destination port.
16. ![]() (Optional) show interface ethernet slot/port[-port] trunk
(Optional) show interface ethernet slot/port[-port] trunk
17. ![]() (Optional) copy running-config startup-config
(Optional) copy running-config startup-config
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
config t Example: n1000v# config t n1000v(config)# |
Places you in the CLI Global Configuration mode. |
Step 2 |
no monitor session session-number Example: n1000v(config)# no monitor session 3 |
Clears the specified session. |
Step 3 |
monitor session session-number Example: n1000v(config)# monitor session 3 n1000v(config-monitor)# |
Creates a session with the given session number and places you in the CLI Monitor Configuration mode to further configure the session. |
Step 4 |
description description Example: n1000v(config-monitor)# description my_span_session_3 |
For the specified SPAN session, adds a description. • |
Step 5 |
source {interface type | vlan} Example 1: n1000v(config-monitor)# source interface ethernet 2/1-3, ethernet 3/1 rx Example 2: n1000v(config-monitor)# source interface port-channel 2 Example 3: n1000v(config-monitor)# source interface vethernet 12 both Example 4: n1000v(config-monitor)# source vlan 3, 6-8 tx |
For the specified session, configures the sources and the direction of traffic to monitor. • • • – – – |
Step 6 |
(Optional) Repeat Step 5 to configure additional SPAN sources. |
|
Step 7 |
filter vlan {number | range} Example: n1000v(config-monitor)# filter vlan 3-5, 7 |
(Optional) For the specified SPAN session, configures the filter from among the source VLANs. |
Step 8 |
(Optional) Repeat Step 7 to configure all source VLANs to filter. |
|
Step 9 |
destination interface type Example: n1000v(config-monitor)# destination interface ethernet 2/5, ethernet 3/7 |
For the specified SPAN session, configures the port(s) to act as destination(s) for copied source packets. • • • Note |
Step 10 |
(Optional) Repeat Step 9 to configure all SPAN destination ports. |
|
Step 11 |
no shut Example:
n1000v(config-monitor)# no shut |
Enables the SPAN session. By default, the session is created in the shut state. |
Step 12 |
exit Example: n1000v(config-monitor)# exit n1000v(config)# |
(Optional) Exits Monitor Configuration mode and places you in CLI Configuration mode. |
Step 13 |
interface ethernet slot/port[-port] Example: n1000v(config)# interface ethernet 2/5 n1000v(config-if)# |
(Optional) Places you in CLI Interface Configuration mode for the specified interface. |
Step 14 |
switchport trunk allowed vlan {vlan-range | add vlan-range | except vlan-range | remove vlan-range | all | none} Example: n1000v(config-if)# switchport trunk allowed vlan 3-5 |
(Optional) For the specified interface. configures the range of VLANS that are allowed on the interface. By default all VLANs are allowed on the interface. • • • • • • |
Step 15 |
(Optional) Repeat Step 13 and Step 14 to configure the allowed VLANs on each destination port. |
|
Step 16 |
show interface ethernet slot/port[-port] trunk Example: n1000v(config-if)# show interface ethernet 2/5 trunk |
(Optional) Displays the interface trunking configuration for the selected slot and port or range of ports. |
Step 17 |
copy running-config startup-config Example: n1000v(config-if)# copy running-config startup-config |
(Optional) Saves the running configuration persistently through reboots and restarts by copying it to the startup configuration. |
Configuring an ERSPAN Port Profile
Use this procedure to configure a port profile on the VSM to carry ERSPAN packets through the IP network to a remote destination analyzer.
BEFORE YOU BEGIN
•![]() You are logged in to the CLI in EXEC mode.
You are logged in to the CLI in EXEC mode.
•![]() This configuration must be completed for all hosts in the vCenter Server.
This configuration must be completed for all hosts in the vCenter Server.
•![]() You know the name to be used for this port profile.
You know the name to be used for this port profile.

Note ![]() The port profile name is used to configure the VMKNIC that is required on each of the ESX hosts.
The port profile name is used to configure the VMKNIC that is required on each of the ESX hosts.
•![]() You know the name of the VMware port group to which this profile maps.
You know the name of the VMware port group to which this profile maps.
•![]() You have the VMware documentation for adding a new virtual adapter.
You have the VMware documentation for adding a new virtual adapter.
•![]() You have already created the system VLAN and you know its VLAN ID which will be used in this configuration.
You have already created the system VLAN and you know its VLAN ID which will be used in this configuration.
For information about creating a system VLAN, see the Cisco Nexus 1000V Layer 2 Switching Configuration Guide, Release 4.0(4)SV1(1).
For more information about system port profiles, see the Cisco Nexus 1000V Port Profile Configuration Guide, Release 4.0(4)SV1(1).
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() port-profile port_profile_name
port-profile port_profile_name
3. ![]() capability l3control
capability l3control
4. ![]() vmware port-group pg_name
vmware port-group pg_name
5. ![]() switchport mode access
switchport mode access
6. ![]() switchport access vlan vlan_id
switchport access vlan vlan_id
7. ![]() no shutdown
no shutdown
8. ![]() system vlan vlan_id
system vlan vlan_id
9. ![]() state enabled
state enabled
10. ![]() (Optional) show port-profile name port_profile_name
(Optional) show port-profile name port_profile_name
11. ![]() (Optional) copy running-config startup-config
(Optional) copy running-config startup-config
DETAILED STEPS
Configuring an ERSPAN Session
Use this procedure to configure an ERSPAN session.

Note ![]() If you are configuring Local SPAN, see the "Configuring a Local SPAN Session" procedure.
If you are configuring Local SPAN, see the "Configuring a Local SPAN Session" procedure.
BEFORE YOU BEGIN
•![]() You are logged in to the CLI in EXEC mode.
You are logged in to the CLI in EXEC mode.
•![]() You know the number of the SPAN session you are going to configure.
You know the number of the SPAN session you are going to configure.
•![]() You have already configured an ERSPAN-capable port profile on the VSM using the "Configuring an ERSPAN Port Profile" procedure.
You have already configured an ERSPAN-capable port profile on the VSM using the "Configuring an ERSPAN Port Profile" procedure.
•![]() Using the VMware documentation for adding a new virtual adapter, you have already configured the required VMKNIC on each of the ESX hosts.
Using the VMware documentation for adding a new virtual adapter, you have already configured the required VMKNIC on each of the ESX hosts.
•![]() SPAN sessions are created in the shut state by default.
SPAN sessions are created in the shut state by default.
•![]() When you create a SPAN session that already exists, any additional configuration is added to that session. To make sure the session is cleared of any previous configuration, you can delete the session first (see Step 2, no monitor session).
When you create a SPAN session that already exists, any additional configuration is added to that session. To make sure the session is cleared of any previous configuration, you can delete the session first (see Step 2, no monitor session).
•![]() This procedure involves creating the SPAN session in ERSPAN Source Configuration mode.
This procedure involves creating the SPAN session in ERSPAN Source Configuration mode.
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() no monitor session session-number
no monitor session session-number
3. ![]() monitor session session-number type erspan-source
monitor session session-number type erspan-source
4. ![]() description description
description description
5. ![]() source {interface type | vlan} {number | range} [rx | tx | both]
source {interface type | vlan} {number | range} [rx | tx | both]
6. ![]() (Optional) Repeat Step 5 to configure additional ERSPAN sources.
(Optional) Repeat Step 5 to configure additional ERSPAN sources.
7. ![]() (Optional) filter vlan {number | range}
(Optional) filter vlan {number | range}
8. ![]() (Optional) Repeat Step 7 to configure all source VLANs to filter.
(Optional) Repeat Step 7 to configure all source VLANs to filter.
9. ![]() destination ip ip_address
destination ip ip_address
10. ![]() (Optional) ip ttl ttl_value
(Optional) ip ttl ttl_value
11. ![]() (Optional) ip prec ipp_value
(Optional) ip prec ipp_value
12. ![]() (Optional) ip dscp dscp_value
(Optional) ip dscp dscp_value
13. ![]() (Optional) mtu mtu_value
(Optional) mtu mtu_value
14. ![]() (Optional) erspan-id flow_id
(Optional) erspan-id flow_id
15. ![]() no shut
no shut
16. ![]() (Optional) show monitor session session_id
(Optional) show monitor session session_id
17. ![]() (Optional) exit
(Optional) exit
18. ![]() (Optional) copy running-config startup-config
(Optional) copy running-config startup-config
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
config t Example: n1000v# config t n1000v(config)# |
Places you in the CLI Global Configuration mode. |
Step 2 |
no monitor session session-number Example: n1000v(config)# no monitor session 3 |
Clears the specified session. |
Step 3 |
monitor session session-number type erspan-source Example: n1000v(config)# monitor session 3 type erspan n1000v(config-erspan-source)# |
Creates a session with the given session number and places you in the CLI ERSPAN Source Configuration mode. This configuration is saved in the running configuration. |
Step 4 |
description description Example: n1000v(config-erspan-src)# description my_erspan_session_3 n1000v(config-erspan-src)# |
For the specified ERSPAN session, adds a description and saves it in the running configuration. • |
Step 5 |
source {interface type | vlan} Example 1: n1000v(config-erspan-src)# source interface ethernet 2/1-3, ethernet 3/1 rx Example 2: n1000v(config-erspan-src)# source interface port-channel 2 Example 3: n1000v(config-erspan-src)# source interface vethernet 12 both Example 4: n1000v(config-erspan-src)# source vlan 3, 6-8 tx |
For the specified session, configures the source(s) and the direction of traffic to monitor, and saves them in the running configuration. • • • – – – |
Step 6 |
(Optional) Repeat Step 5 to configure additional ERSPAN sources. |
|
Step 7 |
filter vlan {number | range} Example: n1000v(config-erspan-src)# filter vlan 3-5, 7 |
(Optional) For the specified ERSPAN session, configures the VLANs, VLAN lists, or VLAN ranges to be monitored; and saves this in the running configuration. On the monitor port, only the traffic from the VLANs which match the VLAN filter list are replicated to the destination. |
Step 8 |
(Optional) Repeat Step 7 to configure all source VLANs to filter. |
|
Step 9 |
destination ip ip_address Example: n1000v(config-erspan-src)# destination ip 10.54.54.1 n1000v(config-monitor-erspan-src)# |
Configures the IP address of the host to which the encapsulated traffic is sent and saves it in the running configuration. |
Step 10 |
ip ttl ttl_value Example: n1000v(config-monitor-erspan-src)# ip ttl 64 n1000v(config-monitor-erspan-src)# |
(Optional) Specifies the IP time-to-live value, from 1-255, for the packets in the ERSPAN traffic, and saves it in the running configuration. |
Step 11 |
ip prec precedence_value Example: n1000v(config-monitor-erspan-src)# ip prec 1 n1000v(config-monitor-erspan-src)# |
(Optional) Specifies the IP precedence value, from 0-7, for the packets in the ERSPAN traffic, and saves it in the running configuration. |
Step 12 |
ip dscp dscp_value Example: n1000v(config-monitor-erspan-src)# ip dscp 24 n1000v(config-monitor-erspan-src)# |
(Optional) Specifies the IP DSCP value, from 0-63. for the packets in the ERSPAN traffic, and saves it in the running configuration. |
Step 13 |
mtu mtu_value Example: n1000v(config-monitor-erspan-src)# mtu 1000 n1000v(config-monitor-erspan-src)# |
(Optional) Specifies an MTU size for the ERSPAN traffic, and saves it in the running configuration. |
Step 14 |
erspan-id flow_id Example: n1000v(config-erspan-src)# erspan_id 51 |
Adds an ERSPAN ID (1-1023) to the session configuration and saves it in the running configuration. The session ERSPAN ID is added to the ERSPAN header of the encapsulated frame and can be used at the termination box to differentiate between various ERSPAN streams of traffic. |
Step 15 |
no shut Example:
n1000v(config-erspan-src)# no shut |
Enables the ERSPAN session and saves it in the running configuration. By default, the session is created in the shut state. |
Step 16 |
show monitor session session_id Example:
n1000v(config-erspan-src)# show monitor session 3 |
(Optional) Displays the ERSPAN session configuration as it exists in the running configuration. |
Step 17 |
exit Example: n1000v(config-erspan-src)# exit n1000v(config)# |
(Optional) Exits ERSPAN Source Configuration mode and returns you to CLI Configuration mode. |
Step 18 |
copy running-config startup-config Example: n1000v(config-if)# copy running-config startup-config |
(Optional) Saves the running configuration persistently through reboots and restarts by copying it to the startup configuration. |
Shutting Down a SPAN Session
Use this procedure to discontinue the copying of packets for a SPAN session. You can discontinue copying packets from one souce and destination; and then resume for another source and destination.
BEFORE YOU BEGIN
Before beginning this procedure, you must know or do the following:
•![]() You are logged in to the CLI in EXEC mode.
You are logged in to the CLI in EXEC mode.
•![]() You know which SPAN session that you want to shut down.
You know which SPAN session that you want to shut down.
•![]() You can shut down a SPAN session from either Global Configuration mode or Monitor Configuration mode.
You can shut down a SPAN session from either Global Configuration mode or Monitor Configuration mode.
SUMMARY STEPS
From Global Configuration mode:
1. ![]() config t
config t
2. ![]() monitor session {session-number | session-range | all} shut
monitor session {session-number | session-range | all} shut
3. ![]() show monitor
show monitor
4. ![]() copy running-config startup-config
copy running-config startup-config
From Monitor Configuration mode:
1. ![]() config t
config t
2. ![]() monitor session {session-number | session-range | all} [type erspan-source]
monitor session {session-number | session-range | all} [type erspan-source]
3. ![]() shut
shut
4. ![]() show monitor
show monitor
5. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Resuming a SPAN Session
Use this procedure to resume the copying of packets for a SPAN session. You can discontinue copying packets from one souce and destination; and then resume for another source and destination.
BEFORE YOU BEGIN
Before beginning this procedure, you must know or do the following:
•![]() You are logged in to the CLI in EXEC mode.
You are logged in to the CLI in EXEC mode.
•![]() You know which SPAN session that you want to configure.
You know which SPAN session that you want to configure.
•![]() You can resume the SPAN session from either Global Configuration mode or Monitor Configuration mode.
You can resume the SPAN session from either Global Configuration mode or Monitor Configuration mode.
SUMMARY STEPS
From Global Configuration mode:
1. ![]() config t
config t
2. ![]() no monitor session {session-number | session-range | all} shut
no monitor session {session-number | session-range | all} shut
3. ![]() show monitor
show monitor
4. ![]() copy running-config startup-config
copy running-config startup-config
From Monitor Configuration mode:
1. ![]() config t
config t
2. ![]() monitor session {session-number | session-range | all} [type erspan-source]
monitor session {session-number | session-range | all} [type erspan-source]
3. ![]() no shut
no shut
4. ![]() show monitor
show monitor
5. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Verifying the SPAN Configuration
To display the SPAN configuration, use the following commands:
Example Configurations
This section includes the following example configurations:
•![]() Span Session Example Configuration
Span Session Example Configuration
•![]() ERSPAN Session Example Configuration
ERSPAN Session Example Configuration
Span Session Example Configuration
To configure a SPAN session, follow these steps:
Step 1 ![]() Configure destination ports in access or trunk mode, and enable SPAN monitoring.
Configure destination ports in access or trunk mode, and enable SPAN monitoring.
n1000v# config t
n1000v(config)# interface ethernet 2/5
n1000v(config-if)# switchport
n1000v(config-if)# switchport mode trunk
n1000v(config-if)# no shut
n1000v(config-if)# exit
n1000v(config)#
Step 2 ![]() Configure a SPAN session.
Configure a SPAN session.
n1000v(config)# no monitor session 3
n1000v(config)# monitor session 3
n1000v(config-monitor)# source interface ethernet 2/1-3
n1000v(config-monitor)# source interface port-channel 2
n1000v(config-monitor)# source vlan 3, 6-8 tx
n1000v(config-monitor)# filter vlan 3-5, 7
n1000v(config-monitor)# destination interface ethernet 2/5
n1000v(config-monitor)# no shut
n1000v(config-monitor)# exit
n1000v(config)# show monitor session 3
n1000v(config)# copy running-config startup-config
ERSPAN Session Example Configuration
The following example shows how to create a bidirectional ERSPAN session for a source Ethernet interface and destination IP address. Packets arriving at the destination IP are identified by the ID 999 in their header.
n1000v(config)# monitor session 1 type erspan-source
n1000v(config-erspan-src)# source interface ethernet 3/3
n1000v(config-erspan-src)# destination ip 10.54.54.1
n1000v(config-erspan-src)# erspan-id 999
n1000v(config-erspan-src)# mtu 1000
n1000v(config-erspan-src)# no shut
n1000v(config)# show monitor session 1
session 1
---------------
type : erspan-source
state : up
source intf :
rx : Eth3/3
tx : Eth3/3
both : Eth3/3
source VLANs :
rx :
tx :
both :
filter VLANs : filter not specified
destination IP : 10.54.54.1
ERSPAN ID : 999
ERSPAN TTL : 64
ERSPAN IP Prec. : 0
ERSPAN DSCP : 0
ERSPAN MTU : 1000
n1000v# module vem 3 execute vemcmd show span
VEM SOURCE IP: 10.54.54.10
HW SSN ID DST LTL/IP ERSPAN ID
0 10.54.54.1 999
1 48 local
Additional References
For additional information related to implementing SPAN, see the following sections:
Related Documents
Standards
|
|
|
|---|---|
No new or modified standards are supported by this feature, and support for existing standards has not been modified by this feature. |
— |
Feature History for SPAN and ERSPAN
This section provides the SPAN and ERSPAN feature release history.
|
|
|
|
|---|---|---|
SPAN and ERSPAN |
4.0(4)SV1(1) |
This feature was introduced. |
 Feedback
Feedback