Cisco ISE Authentication Policies
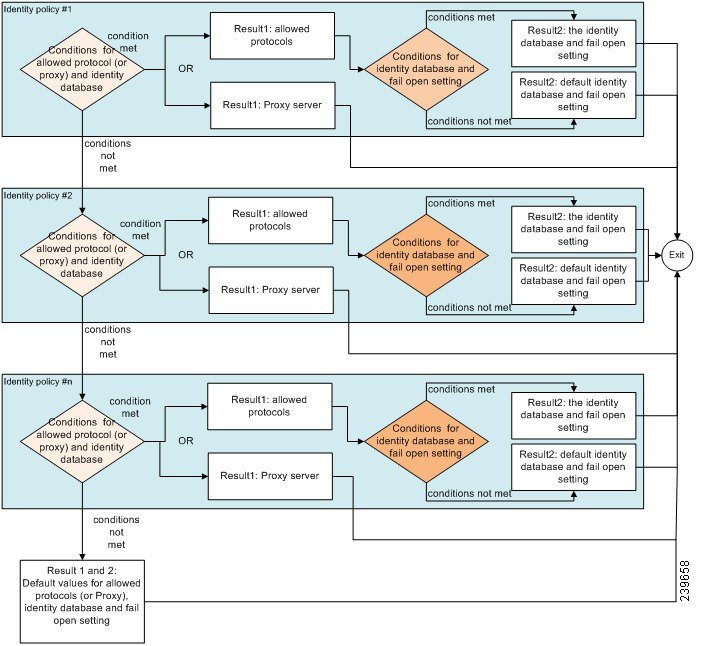
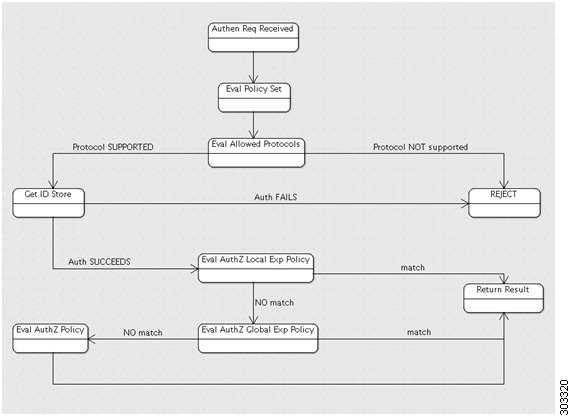
Authentication policies define the protocols that Cisco ISE uses to communicate with the network devices, and the identity sources that it uses for authentication. A policy is a set of conditions and a result. A policy condition consists of an operand (attribute), an operator (equal to, not equal to, greater than, and so on), and a value. Compound conditions are made up of one or more simple conditions that are connected by the AND or OR operator. At runtime, Cisco ISE evaluates a policy condition and then applies the result that you have defined based on whether the policy evaluation returns a true or a false value.
An authentication policy consists of the following:
-
Network Access Service—This service can be one of the following:
-
An allowed protocols service to choose the protocols to handle the initial request and protocol negotiation.
-
A proxy service that will proxy requests to an external RADIUS server for processing.
-
-
Identity Source—An identity source or an identity source sequence to be used for authentication.
After installation, a default identity authentication policy is available in Cisco ISE that is used for authentications. Any updates to the authentication policy will override the default settings.
Policy Condition Evaluation
During policy condition evaluation, Cisco ISE compares an attribute with a value. It is possible to run into a situation where the attribute specified in the policy condition may not have a value assigned in the request. In such cases, if the operator that is used for comparison is “not equal to,” then the condition will evaluate to true. In all other cases, the condition will evaluate to false.
For example, for a condition Radius.Calling_Station_ID Not Equal to 1.1.1.1, if the Calling Station ID is not present in the RADIUS request, then this condition will evaluate to true. This evaluation is not unique to the RADIUS dictionary and occurs because of the usage of the “Not Equal to” operator.
Supported Authentication Protocols
The following is a list of protocols that you can choose while defining your authentication policy:
-
Password Authentication Protocol (PAP)
-
Protected Extensible Authentication Protocol (PEAP)
-
Microsoft Challenge Handshake Authentication Protocol Version 2 (MS-CHAPv2)
-
Extensible Authentication Protocol-Message Digest 5 (EAP-MD5)
-
Extensible Authentication Protocol-Transport Layer Security (EAP-TLS)
-
Extensible Authentication Protocol-Flexible Authentication via Secure Tunneling (EAP-FAST)
-
Extensible Authentication Protocol-Tunneled Transport Layer Security (EAP-TTLS)
-
Protected Extensible Authentication Protocol-Transport Layer Security (PEAP-TLS)
Supported Authentication Types and Database
The authentication type is based on the protocols that are chosen. The authentication type is password based, where the authentication is performed against a database with the username and password that is presented in the request.
The identity method, which is the result of the authentication policy, can be any one of the following:
-
Deny access—Access to the user is denied and no authentication is performed.
-
Identity database—A single identity database that can be any one of the following:
-
Internal users
-
Guest users
-
Internal endpoints
-
Active Directory
-
Lightweight Directory Access Protocol (LDAP) database
-
RADIUS token server (RSA or SafeWord server)
-
Certificate authentication profile
-
-
Identity source sequences—A sequence of identity databases that is used for authentication.
By default, the identity source that Cisco ISE will look up for user information is the internal users database.
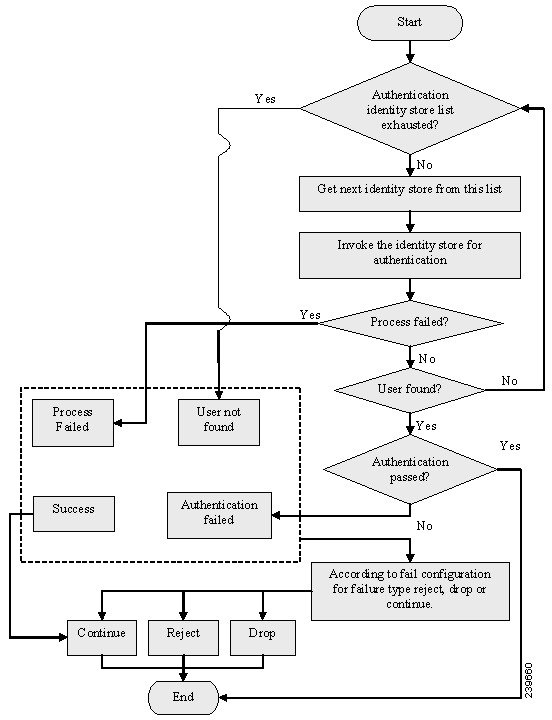
Types of Authentication Failures—Failovers
If you choose the identity method as deny access, a reject message is sent as a response to the request. If you choose an identity database or an identity source sequence and the authentication succeeds, the processing continues to the authorization policy. Some of the authentications fail and these are classified as follows:
-
Authentication failed—Received explicit response that authentication has failed such as bad credentials, disabled user, and so on. The default course of action is reject.
-
User not found—No such user was found in any of the identity databases. The default course of action is reject.
-
Process failed—Unable to access the identity database or databases. The default course of action is drop.
Cisco ISE allows you to configure any one of the following courses of action for authentication failures:
-
Reject—A reject response is sent.
-
Drop—No response is sent.
-
Continue—Cisco ISE continues with the authorization policy.
Even when you choose the Continue option, there might be instances where Cisco ISE cannot continue processing the request due to restrictions on the protocol that is being used. For authentications using PEAP, LEAP, EAP-FAST, EAP-TLS, or RADIUS MSCHAP, it is not possible to continue processing the request when authentication fails or user is not found.
When authentication fails, it is possible to continue to process the authorization policy for PAP/ASCII and MAC authentication bypass (MAB or host lookup). For all other authentication protocols, when authentication fails, the following happens:
-
Authentication failed—A reject response is sent.
-
User or host not found—A reject response is sent.
-
Process failure—No response is sent and the request is dropped.
Authentication Policy Terminology
The following are some of the commonly used terms in the authentication policy pages:
-
Allowed Protocols—Allowed protocols define the set of protocols that Cisco ISE can use to communicate with the device that requests access to the network resources.
-
Identity Source—Identity source defines which database Cisco ISE should use for user information. The database could be an internal database or an external identity source, such as Active Directory or LDAP. You can add a sequence of databases to an identity source sequence and list this sequence as the identity source in your policy. Cisco ISE will search for the credentials in the order in which the databases are listed in this sequence.
-
Failover Options—You can define what course of action Cisco ISE should take if the authentication fails, the user is not found, or if the process fails.


 Feedback
Feedback