User Guide for Cisco Secure ACS to Cisco ISE Migration Tool, Release 2.2.0.1
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- August 8, 2017
Chapter: Migrate Data from Cisco Secure ACS to Cisco ISE
Migrate Data from Cisco Secure ACS to Cisco ISE
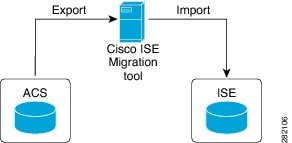
This chapter describes exporting and importing Cisco Secure ACS, Release 5.5 or later data into Cisco ISE, Release 2.2 system using the migration tool.
- Export Data from Cisco Secure ACS
- Import Data in to Cisco ISE
- Migrated Data Verification in Cisco ISE
- Resume a Failed Data Migration
- Migrate Data from a Single Cisco Secure ACS Appliance
- Migrate Data from a Distributed Environment
Export Data from Cisco Secure ACS
After starting the migration tool, complete the following steps to export data from Cisco Secure ACS to the migration tool.
The migration
tool maintains a cache for the exported objects and retrieves them for
subsequent exports.

Note
Password Compliance during Export
The migration tool adheres to password compliance during the export process.
-
Password Complexity
Following is the list of error messages that occur during the export process if the password of the user does not meet the password complexity requirements:
user: Failed to Export because its password does not match with the password Complexity
Password length should be minimum of '5' characters.
Password should not contain 'cisco' or its characters in reverse.
Password should not contain 'hello' or its characters in reverse.
Password should not contain repeated characters four or more times consecutively.
Password should contain at least one Lower case character.
Password should contain at least one Upper case character.
Password should contain at least one Numeric Character.
Password should contain at least one non alphanumeric characters.

Note
You will receive only specific error messages applicable for the set password from the list of error messages.
-
Password hash
If you enable password hash for internal user in Cisco Secure ACS and try to export the internal user, the migration tool displays the following error message:
user: Failed to Export because its configured with Password Hash which is not supported by ISE, disable this configuration in ACS and export again.
Import Data in to Cisco ISE
Migrated Data Verification in Cisco ISE
To verify that the Cisco Secure ACS data is migrated into Cisco ISE, log into the Cisco ISE and check that the various Cisco Secure ACS objects can be viewed.
Resume a Failed Data Migration
The migration tool maintains a checkpoint at each stage of the import or export operation. This means that if the process of importing or exporting fails, you do not have to restart the process from the beginning. You can start from the last checkpoint before the failure occurred.
If the migration process fails, the migration tool terminates the process. When you restart the migration tool after a failure, a dialog box is displayed that allows you to choose to resume the previous import/export or discard the previous process and start a new migration process. If you choose to resume the previous process, the migration process resumes from the last checkpoint. Resuming from a failure also resumes the report to run from the previous process.
Migrate Data from a Single Cisco Secure ACS Appliance
When you are ready to start migrating Cisco Secure ACS, Release 5.5 or later data to a Cisco ISE, Release 2.2, ensure that it is to a standalone Cisco ISE node. After the migration is successfully completed, you can begin any deployment configuration (such as setting up Administrator ISE and Policy Service ISE personas).
It is a requirement that the migration import phase be performed on a “clean” new installation of the Cisco ISE software on a supported hardware appliance. For a list of supported hardware appliances, refer to the Cisco Identity Services Engine Hardware Installation Guide, Release 2.2.
If you have a single Cisco Secure ACS appliance in your environment (or several Cisco Secure ACS appliances, but not in a distributed setup), run the migration tool against the Cisco Secure ACS appliance.
You can use the migration tool and the following migration procedure in cases where Cisco Secure ACS and Cisco ISE use the same hardware; the CSACS-1121 appliance:
Migrate Data from a Distributed Environment
If you have a large internal database, Cisco recommends that you run the migration from a standalone primary appliance and not from a primary appliance that is connected to several secondary appliances. After the completion of the migration process, you can register all the secondary appliances.
In a distributed environment, there is one primary Cisco Secure ACS appliance and one or more secondary Cisco Secure ACS appliances that interoperate with the primary appliance.
If you are running Cisco Secure ACS in a distributed environment, you must:
 Feedback
Feedback