Cisco ASA 5585-X Quick Start Guide
Available Languages
Table of Contents
Cisco ASA 5585-X Quick Start Guide
3. Network Considerations for Multiple SSPs
4. Connect Interface Cables and Verify Connectivity
6. Run ASDM Wizards and Advanced Configuration
1. Package Contents
This section lists the package contents of each chassis. Note that contents are subject to change, and your exact contents might contain additional or fewer items.
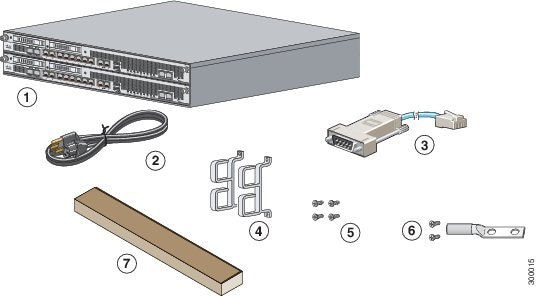
Note![]() : The ASA 5585-X with SSP-10, SSP-20, or SSP-40 ships with one power supply module installed and one power cable. The ASA 5585-X with SSP-60, ships with two power supply modules installed and two power cables.
: The ASA 5585-X with SSP-10, SSP-20, or SSP-40 ships with one power supply module installed and one power cable. The ASA 5585-X with SSP-60, ships with two power supply modules installed and two power cables.
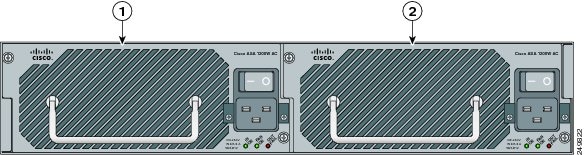
2. Power On the ASA
1.![]() Attach the power cable to the back of the ASA. If you have redundant power supplies, you must connect both power cables to the back of the chassis.
Attach the power cable to the back of the ASA. If you have redundant power supplies, you must connect both power cables to the back of the chassis.
2.![]() Connect the power cables to the electrical outlets.
Connect the power cables to the electrical outlets.
3.![]() Power on the ASA. If you have redundant power supplies, you must power on both modules.
Power on the ASA. If you have redundant power supplies, you must power on both modules.
4.![]() Check the Power LED on the front of the ASA; the AC ON indicator should be green, the FAN ON indicator should be green, and the OUT OK indicator should be off.
Check the Power LED on the front of the ASA; the AC ON indicator should be green, the FAN ON indicator should be green, and the OUT OK indicator should be off.
3. Network Considerations for Multiple SSPs
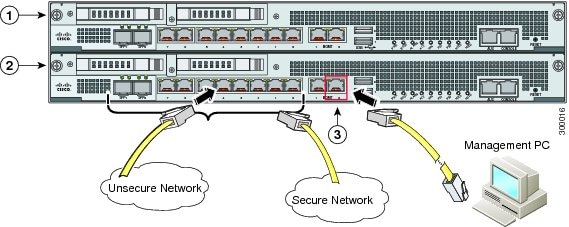
The ASA SSP resides in slot 0 (bottom). A second SSP (or network module) can be installed in slot 1 (top). When you install a non-ASA SSP in slot 1, all non-management interfaces belong to the ASA in slot 0, while the management interfaces belong to the module. If you install dual ASA SSPs, then they are completely independent systems.
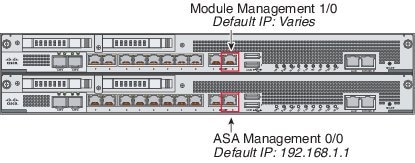
Default Configuration for Management
See the following table for default configurations for the Management interfaces depending on which module is installed in slot 1. Note that the left-hand Management interface (when facing the back of the chassis) is not configured by default.
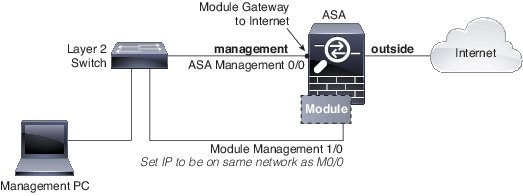
All management traffic to and from the non-ASA SSP must enter and exit the Management 1/0 or 1/1 interface. Because this interface is not an ASA data interface, traffic cannot pass through the ASA over the backplane; you need to physically cable the management interface to an ASA interface. Non-ASA SSPs usually need Internet access for updates. See the following typical cabling setup to allow SSP access to the Internet through the ASA management interface. Other options are possible, depending on how you want to connect your network; for example, you can make the Management 1/0 interface outside facing; or you can route between it and a different ASA interface if you have an inside router; and so on.
4. Connect Interface Cables and Verify Connectivity
1.![]() Cable the management and data interfaces. See 3. Network Considerations for Multiple SSPs for a sample cabling scenario.
Cable the management and data interfaces. See 3. Network Considerations for Multiple SSPs for a sample cabling scenario.
2.![]() If you do not use the Management 0/0 for ASA management, you need to configure a data interface for management. Do one of the following, then recable the computer so it is on the new management network:
If you do not use the Management 0/0 for ASA management, you need to configure a data interface for management. Do one of the following, then recable the computer so it is on the new management network:
–![]() Connect to the console port to configure a data interface for management with CLI. See the Getting Started chapter in the general operations configuration guide for detailed steps.
Connect to the console port to configure a data interface for management with CLI. See the Getting Started chapter in the general operations configuration guide for detailed steps.
–![]() Temporarily connect to Management 0/0, launch ASDM (see 5. Launch ASDM), and configure a data interface for management.
Temporarily connect to Management 0/0, launch ASDM (see 5. Launch ASDM), and configure a data interface for management.
3.![]() If you are using the fiber interfaces, you need an SFP+ module for 10-Gigabit Ethernet (a license may be required) or an SFP module for Gigabit Ethernet. (SFP or SFP+ modules are not included.)
If you are using the fiber interfaces, you need an SFP+ module for 10-Gigabit Ethernet (a license may be required) or an SFP module for Gigabit Ethernet. (SFP or SFP+ modules are not included.)
The interfaces available depend on your model. See the hardware guide for more information.
4.![]() Check the LINK/ACT indicators to verify interface connectivity.
Check the LINK/ACT indicators to verify interface connectivity.
5.![]() For software module configuration, see the ASA FirePOWER quick start guide, ASA CX quick start guide, or IPS quick start guide.
For software module configuration, see the ASA FirePOWER quick start guide, ASA CX quick start guide, or IPS quick start guide.
5. Launch ASDM
Using ASDM, you can use wizards to configure basic and advanced features. See the ASDM release notes on Cisco.com for the requirements to run ASDM.
1.![]() On the computer connected to the ASA Management 0/0 interface, launch a web browser.
On the computer connected to the ASA Management 0/0 interface, launch a web browser.
2.![]() In the Address field, enter the following URL: https://192.168.1.1/admin. The Cisco ASDM web page appears.
In the Address field, enter the following URL: https://192.168.1.1/admin. The Cisco ASDM web page appears.
3.![]() Click one of the available options: Install ASDM Launcher, Run ASDM, or Run Startup Wizard.
Click one of the available options: Install ASDM Launcher, Run ASDM, or Run Startup Wizard.
4.![]() Follow the onscreen instructions to launch ASDM according to the option you chose. The Cisco ASDM-IDM Launcher appears.
Follow the onscreen instructions to launch ASDM according to the option you chose. The Cisco ASDM-IDM Launcher appears.
Note: If you choose to click Install ASDM Launcher, in some cases you need to install an identity certificate for the ASA and a separate certificate for the ASA FirePOWER module according to Install an Identity Certificate for ASDM.
5.![]() Leave the username and password fields empty, and click OK. The main ASDM window appears.
Leave the username and password fields empty, and click OK. The main ASDM window appears.
6. Run ASDM Wizards and Advanced Configuration
ASDM includes many wizards to configure your security policy. See the Wizards menu for all available wizards, including the Startup Wizard for initial deployment. To continue configuring your ASA, see the documents available for your software version at Navigating the Cisco ASA Series Documentation.
Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R)
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback