Cisco 1000 Series Connected Grid Routers Security Software Configuration Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- June 27, 2014
Chapter: Configuring Control-Plane Policing
Configuring Control-Plane Policing
This chapter describes how to configure Control-Plane Policing (CoPP) on the Cisco 1000 Series Connected Grid Routers (hereafter referred to as the Cisco CG-OS router).
Information About CoPP
To prevent the Cisco CG-OS router from Denial of Service (DoS) attacks, the system employs control-plane policing (CoPP or CPP). CoPP increases security on the router by protecting the system from unnecessary or DoS traffic and gives priority to important control-plane and management traffic.
To protect the control plane against DoS attacks and to restrict specific flows, there should be a flexible way to police different classes of traffic destined to the CPU.
For information on deploying CoPP:
http://www.cisco.com/en/US/prod/collateral/iosswrel/ps6537/ps6586/ps6642/prod_white_paper0900aecd804fa16a.html
For information on CoPP best practices:
http://www.cisco.com/web/about/security/intelligence/coppwp_gs.html
CoPP can protect the control and management planes and ensure routing stability, accessibility, and packet delivery. CoPP uses a dedicated control-plane configuration through Cisco Modular QoS CLI (MQC) to provide filtering and rate-limiting capabilities for control-plane packets. (See Using Modular CLI in the Cisco 1000 Series Connected Grid Routers QoS Software Configuration Guide. ) CoPP policy can be used to protect the CPU from DoS attacks by restricting SYNC packets, FIN packets, and IP fragments.
CoPP manager (Coppmgr) is the part of CG-OS that processes control-plane configuration commands. Because CoPP uses MQC, it must interact with the Access Control List (ACL) manager for the ACLs, and the QoS manager for the class maps.
When a CoPP policy refers to a QoS class map, the QoS manager sends the changes in the class map to the clients that use the policy. Similarly, when an ACL, referenced by CoPP policy, changes, the
CG-OS software sends that change to the client by employing the ACL manager.
Key Concepts
CoPP involves the following actions:
Rate— Defines the amount of traffic sent by the Cisco CG-OS router in a given interval.
Policing— The process of limiting traffic to a prescribed rate. Allows the definition of a rate and a burst. The router does not forward any further traffic for a given interval after the specified amount has passed through the interface.
Burst— Defines the amount of traffic that can be held in the queue for future transmission. Traffic in excess of the burst can be either dropped or have its priority setting reduced.
Figure 10-1 demonstrates that committed information rate (CIR) [4] and burst rate [3] are integral to policing. While the traffic allowed within the time window is at the rate of committed information rate, traffic is only dropped after the burst rate is reached.
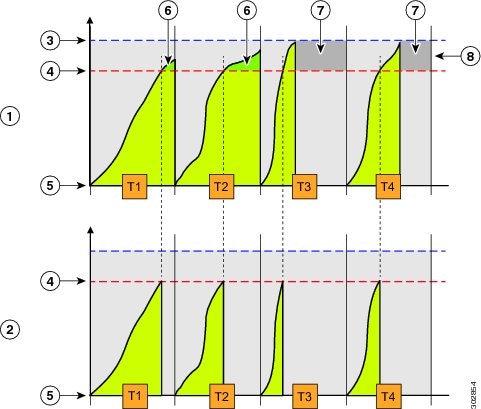
The CG-OS router does not have a burst rate [8]. The sampling window duration [T x ] is in seconds. The CIR [4] is in packets per second. The router drops packets that exceed the CIR setting [7]. The router does not support additional actions such as marking traffic.
In Figure 10-1, at 5-second intervals, the router allows for the committed number of packets [4] for the specified flow and drops additional packets. The committed number of packets [4] is calculated by multiplying by 5 the committed information rate provided in the input.
Prerequisites
Refer to the Before You Begin paragraph at the beginning of each section for prerequisites.
Guidelines and Limitations
The Cisco CG-OS router supports a limited set of the policing parameters for CoPP.
The router supports the following commands shown in bold:
The CG-OS router does not support the following CoPP policing parameters when defining a policy map and class-map at the (config-pmap-c)# prompt:
Configuring CoPP
This section includes the following topics:
- Configuring an ACL
- Configuring a Class Map
- Configuring a Policy Map
- Configuring the Control-Plane
- Verifying Configuration
Configuring an ACL
A CoPP policy protects the CPU from DoS attacks by restricting synchronization (sync) packets, finish (FIN) packets and IP fragments.
This section provides details on configuring an ACL for CoPP.
See
Configuring IP ACLs
in this guide for more information on configuring ACLs on the
Cisco CG-OS router.
DETAILED STEPS
Configuring a Class Map
Create a class map for the control-plane and classify traffic based on the ACL.
See Configuring Priority Queuing in the Cisco 1000 Series Connected Grid Routers QoS Software Configuration Guide for more information on configuring class maps on the Cisco CG-OS router.
BEFORE YOU BEGIN
Configure an ACL. See Configuring an ACL.
DETAILED STEPS
Configuring a Policy Map
Configure a policy map for the control-plane and define a policing action within a subordinate class map.
See Configuring Priority Queuing in the Cisco 1000 Series Connected Grid Routers QoS Software Configuration Guide for more information on configuring policy maps on the Cisco CG-OS router.
BEFORE YOU BEGIN
See Guidelines and Limitations for a summary of supported policing commands.
Create a class map. ( See Configuring a Class Map.)
DETAILED STEPS
Configuring the Control-Plane
Apply the policy map created in Configuring a Policy Map to the control-plane.
BEFORE YOU BEGIN
Create a policy map. (See Configuring a Policy Map.)
Verifying Configuration
To display information about the CoPP configuration, enter any or all of the following commands:
show ip traffic
To see whether CoPP has initiated policing to drop packets, enter the show ip traffic command.
 Feedback
Feedback