- Preface
- Cisco ONS Documentation Roadmap for Release 9.2.1
- Chapter 1, Install the Shelf and Backplane Cable
- Chapter 2, Install Cards and Fiber-Optic Cable
- Chapter 3, Connect the PC and Log Into the GUI
- Chapter 4, Turn Up a Node
- Chapter 5, Turn Up a Network
- Chapter 6, Create Circuits and VT Tunnels
- Chapter 7, Manage Circuits
- Chapter 8, Manage Alarms
- Chapter 9, Monitor Performance
- Chapter 10, Change Card Settings
- Chapter 11, Change Node Settings
- Chapter 12, Upgrade Cards and Spans
- Chapter 13, Upgrade Network and Configurations
- Chapter 14, Add and Remove Nodes
- Chapter 15, Maintain the Node
- Chapter 16, Power Down the Node
- Chapter 17, DLPs A1 to A99
- Chapter 18, DLPs A100 to A199
- Chapter 19, DLPs A200 to A299
- Chapter 20, DLPs A300 to A399
- Chapter 21, DLPs A400 to A499
- Chapter 22, DLPs A500 to A599
- Chapter 23, DLPs A600 to A699
- Appendix A, CTC Information and Shortcuts
Cisco ONS 15454 Procedure Guide, Releases 9.1, 9.2, and 9.2.1
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- August 29, 2012
Chapter: Chapter 4, Turn Up a Node
Turn Up a Node
This chapter explains how to provision a single Cisco ONS 15454 node and turn it up for service, including assigning a node name, date and time, timing references, network attributes such as IP address and default router, users and user security, and card protection groups.
Before You Begin
Complete the procedures applicable to your site plan from the following chapters:
- Chapter 1, “Install the Shelf and Backplane Cable”
- Chapter 2, “Install Cards and Fiber-Optic Cable”
- Chapter 3, “Connect the PC and Log into the GUI”
This section lists the chapter procedures (NTPs). Turn to a procedure for applicable tasks (DLPs).
1.![]() A323 Verify Card Installation—Complete this procedure first.
A323 Verify Card Installation—Complete this procedure first.
2.![]() A30 Create Users and Assign Security —Complete this procedure to create Cisco Transport Controller (CTC) users and assign their security levels.
A30 Create Users and Assign Security —Complete this procedure to create Cisco Transport Controller (CTC) users and assign their security levels.
3.![]() A25 Set Up Name, Date, Time, and Contact Information—Continue with this procedure to set the node name, date, time, location, and contact information.
A25 Set Up Name, Date, Time, and Contact Information—Continue with this procedure to set the node name, date, time, location, and contact information.
4.![]() A261 Set Power Monitor Thresholds—Continue with this procedure to set the node battery power thresholds.
A261 Set Power Monitor Thresholds—Continue with this procedure to set the node battery power thresholds.
5.![]() A169 Set Up CTC Network Access—Continue with this procedure to provision the IP address, default router, subnet mask, and network configuration settings.
A169 Set Up CTC Network Access—Continue with this procedure to provision the IP address, default router, subnet mask, and network configuration settings.
6.![]() A358 Set up the ONS 15454 in Secure Mode—Continue with this procedure to connect the CTC in secure mode.
A358 Set up the ONS 15454 in Secure Mode—Continue with this procedure to connect the CTC in secure mode.
7.![]() A360 Enable EMS Secure Access—Continue with this procedure to enable EMS secure access and provide enhanced SFTP and SSH security.
A360 Enable EMS Secure Access—Continue with this procedure to enable EMS secure access and provide enhanced SFTP and SSH security.
8.![]() A375 Set Up Secure Access to the ONS 15454 TL1—Continue with this procedure to enable secure access to TL1.
A375 Set Up Secure Access to the ONS 15454 TL1—Continue with this procedure to enable secure access to TL1.
9.![]() A27 Set Up the ONS 15454 for Firewall Access—Continue with this procedure if the ONS 15454 will be accessed behind firewalls.
A27 Set Up the ONS 15454 for Firewall Access—Continue with this procedure if the ONS 15454 will be accessed behind firewalls.
10.![]() A355 Create FTP Host—Continue with this procedure if to create FTP host for ENE database backup.
A355 Create FTP Host—Continue with this procedure if to create FTP host for ENE database backup.
11.![]() A28 Set Up Timing—Continue with this procedure to set up the node’s SONET timing references.
A28 Set Up Timing—Continue with this procedure to set up the node’s SONET timing references.
12.![]() A324 Create Protection Groups —Complete this procedure, as needed, to set up 1:1, 1:N, 1+1, or Y-cable protection groups for ONS 15454 electrical and optical cards.
A324 Create Protection Groups —Complete this procedure, as needed, to set up 1:1, 1:N, 1+1, or Y-cable protection groups for ONS 15454 electrical and optical cards.
13.![]() A256 Set Up SNMP —Complete this procedure if Simple Network Management Protocol (SNMP) will be used for network monitoring.
A256 Set Up SNMP —Complete this procedure if Simple Network Management Protocol (SNMP) will be used for network monitoring.
14.![]() A364 Provision Node for SNMPv3—Complete this procedure if Simple Network Management Protocol Version 3 (SNMPv3) will be used for network monitoring.
A364 Provision Node for SNMPv3—Complete this procedure if Simple Network Management Protocol Version 3 (SNMPv3) will be used for network monitoring.
15.![]() A318 Provision OSI —Complete this procedure if the ONS 15454 will be connected in networks with network elements (NEs) that are based on the Open System Interconnection (OSI) protocol stack. This procedure provisions the TID Address Resolution Protocol (TARP), OSI routers, manual area addresses, subnetwork points of attachment, and IP over OSI tunnels.
A318 Provision OSI —Complete this procedure if the ONS 15454 will be connected in networks with network elements (NEs) that are based on the Open System Interconnection (OSI) protocol stack. This procedure provisions the TID Address Resolution Protocol (TARP), OSI routers, manual area addresses, subnetwork points of attachment, and IP over OSI tunnels.
NTP-A323 Verify Card Installation
This procedure verifies that an ONS 15454 node provisioned for SONET is ready for turn-up. |
|
An engineering work order, site plan, or other document specifying the ONS 15454 card installation. |
|
Step 1![]() Verify that two TCC2/TCC2P cards are installed in Slots 7 and 11.
Verify that two TCC2/TCC2P cards are installed in Slots 7 and 11.
Step 2![]() Verify that the green ACT (active) LED is illuminated on one TCC2/TCC2P card and the amber STBY (standby) LED is illuminated on the second TCC2/TCC2P card.
Verify that the green ACT (active) LED is illuminated on one TCC2/TCC2P card and the amber STBY (standby) LED is illuminated on the second TCC2/TCC2P card.

Note![]() If the TCC2/TCC2P cards are not installed, or if their LEDs are not operating as described, do not proceed. Repeat the A36 Install the TCC2/TCC2P Cards, or refer to the Cisco ONS 15454 Troubleshooting Guide to resolve installation problems before proceeding to Step 3.
If the TCC2/TCC2P cards are not installed, or if their LEDs are not operating as described, do not proceed. Repeat the A36 Install the TCC2/TCC2P Cards, or refer to the Cisco ONS 15454 Troubleshooting Guide to resolve installation problems before proceeding to Step 3.
Step 3![]() Verify that cross-connect cards (XCVT, XC10G, or XC-VXC-10G) are installed in Slots 8 and 10. The cross-connect cards must be the same type.
Verify that cross-connect cards (XCVT, XC10G, or XC-VXC-10G) are installed in Slots 8 and 10. The cross-connect cards must be the same type.
Step 4![]() Verify that the green ACT (active) LED is illuminated on one cross-connect card and the amber STBY (standby) LED is illuminated on the second cross-connect card.
Verify that the green ACT (active) LED is illuminated on one cross-connect card and the amber STBY (standby) LED is illuminated on the second cross-connect card.

Note![]() If the cross-connect cards are not installed, or if their LEDs are not operating as described, do not proceed. Repeat the A37 Install the XCVT, XC10G, or XC-VXC-10G Cards, or refer to the Cisco ONS 15454 Troubleshooting Guide to resolve installation problems before proceeding to Step 5.
If the cross-connect cards are not installed, or if their LEDs are not operating as described, do not proceed. Repeat the A37 Install the XCVT, XC10G, or XC-VXC-10G Cards, or refer to the Cisco ONS 15454 Troubleshooting Guide to resolve installation problems before proceeding to Step 5.
Step 5![]() If your site plan requires an AIC-I card, verify that it is installed in Slot 9 and its ACT (active) LED displays a solid green light.
If your site plan requires an AIC-I card, verify that it is installed in Slot 9 and its ACT (active) LED displays a solid green light.
Step 6![]() Verify that the DS-1, DS-3, EC-1, and DS3XM cards are installed in Slots 1 to 6 or 12 to 17 as designated by your installation plan.
Verify that the DS-1, DS-3, EC-1, and DS3XM cards are installed in Slots 1 to 6 or 12 to 17 as designated by your installation plan.

Note![]() The DS1/E1-56 and DS3/EC1-48 cards can only be installed in Slots 1 through 3 or 15 through 17.
The DS1/E1-56 and DS3/EC1-48 cards can only be installed in Slots 1 through 3 or 15 through 17.
Step 7![]() If Ethernet cards are installed, verify that the correct cross-connect cards are installed in Slots 8 and 10:
If Ethernet cards are installed, verify that the correct cross-connect cards are installed in Slots 8 and 10:
- E100T-12-G and E1000-2-G cards require XC10G or XC-VXC-10G cards.
- G1K-4, ML1000-2, ML100X-8, ML100T-12, and CE-1000-4 cards require XC10G or XC-VXC-10G cards if they are installed in Slots 1 to 6 or 12 to 17. If they are installed in Slots 5, 6, 11 and 12, any cross-connect card can be installed.
- ML-MR-10 cards require XC10G or XC-VXC-10G cards. The ML-MR-10 card is not compatible with the XCVT or XC card.
- CE-MR-10 cards can be installed in Slots 1 to 6 or 12 to 17, and can interoperate with any cross-connect card.
Step 8![]() If an E1000-2, E1000-2-G, G1K-4, ML100X-8, ML1000-2, CE-1000-4, CE-MR-10, or ML-MR-10 Ethernet card is installed, verify that it has a Gigabit Interface Converter (GBIC) or Small Form-Factor Pluggable (SFP) installed. If not, see the A469 Install a GBIC or SFP/XFP Device.
If an E1000-2, E1000-2-G, G1K-4, ML100X-8, ML1000-2, CE-1000-4, CE-MR-10, or ML-MR-10 Ethernet card is installed, verify that it has a Gigabit Interface Converter (GBIC) or Small Form-Factor Pluggable (SFP) installed. If not, see the A469 Install a GBIC or SFP/XFP Device.
Step 9![]() Verify that the OC-N cards (OC-3, OC-3-8, OC-12, OC-12-4, OC-48, OC-48 any slot [AS], OC-192, MRC-2.5G-4, and MRC-12) are installed in the slots designated by your site plan.
Verify that the OC-N cards (OC-3, OC-3-8, OC-12, OC-12-4, OC-48, OC-48 any slot [AS], OC-192, MRC-2.5G-4, and MRC-12) are installed in the slots designated by your site plan.
Step 10![]() Verify that the correct cross-connect cards are installed in Slots 8 and 10:
Verify that the correct cross-connect cards are installed in Slots 8 and 10:
Step 11![]() Verify that all installed OC-N cards display a solid amber STBY LED.
Verify that all installed OC-N cards display a solid amber STBY LED.
Step 12![]() If transponder or muxponder cards are installed (TXP_MR_10G, TXP_MR_2.5G, TXPP_MR_2.5G, MXP_MR_2.5G, MXPP_MR_2.5G, MXP_2.5G_10G, TXP_MR_10E, TXP_MR_10E_L, TXP_MR_10E_C, MXP_2.5G_10E, MXP_2.5G_10E_C, MXP_2.5G_10E_L, MXP_MR_10DME_L, MXP_MR_10DME_C, ADM-10G, GE_XP, and 10GE_XP), verify that they are installed in Slots 1 to 6 or 12 to 17 and have GBIC or SFP connectors installed. For information about installing and provisioning TXP and MXP cards, refer to the Cisco ONS 15454 DWDM Procedure Guide.
If transponder or muxponder cards are installed (TXP_MR_10G, TXP_MR_2.5G, TXPP_MR_2.5G, MXP_MR_2.5G, MXPP_MR_2.5G, MXP_2.5G_10G, TXP_MR_10E, TXP_MR_10E_L, TXP_MR_10E_C, MXP_2.5G_10E, MXP_2.5G_10E_C, MXP_2.5G_10E_L, MXP_MR_10DME_L, MXP_MR_10DME_C, ADM-10G, GE_XP, and 10GE_XP), verify that they are installed in Slots 1 to 6 or 12 to 17 and have GBIC or SFP connectors installed. For information about installing and provisioning TXP and MXP cards, refer to the Cisco ONS 15454 DWDM Procedure Guide.
Step 13![]() If Fibre Channel cards (FC-MR-4) are installed, verify one of the following:
If Fibre Channel cards (FC-MR-4) are installed, verify one of the following:
Step 14![]() Verify that fiber-optic cables (fiber) are installed and connected to the locations indicated in the site plan. If the fiber is not installed, complete the A247 Install Fiber-Optic Cables.
Verify that fiber-optic cables (fiber) are installed and connected to the locations indicated in the site plan. If the fiber is not installed, complete the A247 Install Fiber-Optic Cables.
Step 15![]() Verify that fiber is routed correctly in the shelf assembly and fiber boots are installed properly. If the fiber is not routed on the shelf assembly, complete the A245 Route Fiber-Optic Cables. If the fiber boots are not installed, complete the A45 Install the Fiber Boot.
Verify that fiber is routed correctly in the shelf assembly and fiber boots are installed properly. If the fiber is not routed on the shelf assembly, complete the A245 Route Fiber-Optic Cables. If the fiber boots are not installed, complete the A45 Install the Fiber Boot.
Step 16![]() Verify that the software release shown on the LCD matches the software release indicated in your site plan. If the release does not match, perform one of the following procedures:
Verify that the software release shown on the LCD matches the software release indicated in your site plan. If the release does not match, perform one of the following procedures:
Stop. You have completed this procedure.
NTP-A30 Create Users and Assign Security
This procedure creates ONS 15454 users and assigns their security levels. |
|
Step 1![]() Complete the A60 Log into CTC at the node where you need to create users. If you are already logged in, continue with Step 2.
Complete the A60 Log into CTC at the node where you need to create users. If you are already logged in, continue with Step 2.

Note![]() You must log in as a Superuser to create additional users. The CISCO15 user provided with each ONS 15454 can be used to set up other ONS 15454 users. You can add up to 500 users to one ONS 15454.
You must log in as a Superuser to create additional users. The CISCO15 user provided with each ONS 15454 can be used to set up other ONS 15454 users. You can add up to 500 users to one ONS 15454.
Step 2![]() Complete the A74 Create a New User on a Single Node or the A75 Create a New User on Multiple Nodes as needed.
Complete the A74 Create a New User on a Single Node or the A75 Create a New User on Multiple Nodes as needed.

Note![]() You must add the same user name and password to each node a user will access.
You must add the same user name and password to each node a user will access.
Step 3![]() As needed, complete the A456 Configure the Node for RADIUS Authentication. Remote Authentication Dial in User Service (RADIUS) validates remote users trying to connect to the network.
As needed, complete the A456 Configure the Node for RADIUS Authentication. Remote Authentication Dial in User Service (RADIUS) validates remote users trying to connect to the network.
Step 4![]() If you want to modify the security policy settings, including password aging and idle user timeout policies, complete the A205 Modify Users and Change Security.
If you want to modify the security policy settings, including password aging and idle user timeout policies, complete the A205 Modify Users and Change Security.
Stop. You have completed this procedure.
NTP-A25 Set Up Name, Date, Time, and Contact Information
This procedure provisions identification information for the node, including the node name, a contact name and phone number, the location of the node, and the date, time, and time zone. |
|
Step 1![]() Complete the A60 Log into CTC for the node you will turn up. If you are already logged in, continue with Step 2.
Complete the A60 Log into CTC for the node you will turn up. If you are already logged in, continue with Step 2.
Step 2![]() Click the Provisioning > General tabs.
Click the Provisioning > General tabs.
Step 3![]() Enter the following information in the fields listed:
Enter the following information in the fields listed:
- Node Name/TID—Type a name for the node. For Transaction Language 1 (TL1) compliance, names must begin with an alpha character and have no more than 20 alphanumeric (a-z, A-Z, 0-9) characters.
- Contact—(Optional) Type the name of the node contact person and the phone number, up to 255 characters.
- Latitude—Enter the node latitude: N (North) or S (South), degrees, and minutes (optional).
- Longitude—Enter the node longitude: E (East) or W (West), degrees, and minutes (optional).

Tip You can drag and drop the node icon on the network view map to position nodes manually. To create the same network map visible for all ONS 15454 users, complete the A172 Create a Logical Network Map.

Note![]() The latitude and longitude values only indicate the geographical position of the nodes in the actual network and not the CTC node position.
The latitude and longitude values only indicate the geographical position of the nodes in the actual network and not the CTC node position.
If you do not use an SNTP or NTP server, complete the Date and Time fields. The ONS 15454 will use these fields for alarm dates and times. By default, CTC displays all alarms in the CTC computer time zone for consistency. To change the display to the node time zone, complete the A112 Display Alarms and Conditions Using Time Zone.

Note![]() Using an NTP or SNTP server ensures that all ONS 15454 network nodes use the same date and time reference. The server synchronizes the node’s time after power outages or software upgrades.
Using an NTP or SNTP server ensures that all ONS 15454 network nodes use the same date and time reference. The server synchronizes the node’s time after power outages or software upgrades.
If you check the Use NTP/SNTP Server check box, complete the following fields:
–![]() Use NTP/SNTP Server—Type the IP address of the primary NTP/SNTP server connected to the ONS 15454 or of another ONS 15454/15600/15310-CL/15310-MA as GNE with NTP/SNTP enabled that is connected to the ONS 15454 ENE.
Use NTP/SNTP Server—Type the IP address of the primary NTP/SNTP server connected to the ONS 15454 or of another ONS 15454/15600/15310-CL/15310-MA as GNE with NTP/SNTP enabled that is connected to the ONS 15454 ENE.
–![]() Backup NTP/SNTP Server—Type the IP address of the secondary NTP/SNTP server connected to the ONS 15454 or of another ONS 15454/15600/15310-CL/15310-MA with NTP/SNTP enabled that is connected to the ONS 15454 ENE.
Backup NTP/SNTP Server—Type the IP address of the secondary NTP/SNTP server connected to the ONS 15454 or of another ONS 15454/15600/15310-CL/15310-MA with NTP/SNTP enabled that is connected to the ONS 15454 ENE.
When the primary NTP/SNTP server fails or is not reachable, the node uses the secondary NTP/SNTP server to synchronize its date and time. If both the primary and secondary NTP/SNTP servers fail or are not reachable, an SNTP-FAIL alarm is raised. The node checks for the availability of the primary or secondary NTP/SNTP server at regular intervals until it can get the time from any one of the NTP/SNTP servers. After the node gets the time from any one server, it synchronizes its date and time with the server’s date and time and the SNTP-FAIL alarm is cleared. For each retry and resynchronization, the node checks the availability of the primary NTP/SNTP server first, followed by the secondary NTP/SNTP server. The node synchronizes its date and time every hour.

Note You will not be able to identify which NTP/SNTP server is being used for synchronization.
If you check gateway network element (GNE) for the ONS 15454 SOCKS proxy server (see A249 Provision IP Settings), external ONS 15454s must reference the gateway ONS 15454 for NTP/SNTP timing. For more information about the ONS 15454 gateway settings, refer to the “Management Network Connectivity” chapter in the Cisco ONS 15454 Reference Manual.

Note![]() In ONS 15454 Software Release 9.0 and later, you can configure an IPv6 address for an NTP/SNTP server, in addition to an IPv4 address.
In ONS 15454 Software Release 9.0 and later, you can configure an IPv6 address for an NTP/SNTP server, in addition to an IPv4 address.

- Date—If Use NTP/SNTP Server is not checked, type the current date (mm/dd/yyyy, for example, September 24, 2002 is 09/24/2002).
- Time—If Use NTP/SNTP Server is not checked, type the current time in the format hh:mm:ss, for example, 11:24:58. The ONS 15454 uses a 24-hour clock, so 10:00 PM is entered as 22:00:00.
- Time Zone—Click the field and choose a city within your time zone from the drop-down list. The list displays the 80 World Time Zones from –11 through 0 (GMT) to +14. Continental United States time zones are GMT-05:00 (Eastern), GMT-06:00 (Central), GMT-07:00 (Mountain), and GMT-08:00 (Pacific).
- Use Daylight Savings Time—Check this check box if the time zone that you chose uses Daylight Savings Time.
- Insert AIS-V on STS-1 SD-P—Check this check box if you want Alarm Indication Signal Virtual Tributary (AIS-V) conditions inserted on VT circuits carried by STS-1s when the STS-1 crosses its Signal Degrade Path (SD-P) bit error rate (BER) threshold. On protected circuits, traffic will be switched. If the switch cannot be performed, or if circuits are not protected, traffic will be dropped when the STS-1 SD-P BER threshold is reached.
- SD-P BER—If you selected Insert AIS-V, you can choose the SD-P BER level from the SD-P BER drop-down list.
Step 5![]() In the confirmation dialog box, click Yes.
In the confirmation dialog box, click Yes.
Step 6![]() Review the node information. If you need to make corrections, repeat Steps 3 through 5 to enter the corrections. If the information is correct, continue with the A261 Set Power Monitor Thresholds.
Review the node information. If you need to make corrections, repeat Steps 3 through 5 to enter the corrections. If the information is correct, continue with the A261 Set Power Monitor Thresholds.
Stop. You have completed this procedure.
NTP-A261 Set Power Monitor Thresholds
Step 1![]() Complete the A60 Log into CTC for the node you will set up. If you are already logged in, continue with Step 2.
Complete the A60 Log into CTC for the node you will set up. If you are already logged in, continue with Step 2.
Step 2![]() In node view, click the Provisioning > General > Power Monitor tabs.
In node view, click the Provisioning > General > Power Monitor tabs.
Step 3![]() To change the extreme low battery voltage threshold in 0.5 VDC increments, choose a voltage from the ELWBATVG(Vdc) drop-down list.
To change the extreme low battery voltage threshold in 0.5 VDC increments, choose a voltage from the ELWBATVG(Vdc) drop-down list.
Step 4![]() To change the low battery voltage threshold in 0.5 VDC increments, choose a voltage from the LWBATVG(Vdc) drop-down list.
To change the low battery voltage threshold in 0.5 VDC increments, choose a voltage from the LWBATVG(Vdc) drop-down list.
Step 5![]() To change the high battery voltage threshold in 0.5 VDC increments, choose a voltage from the HIBATVG(Vdc) drop-down list.
To change the high battery voltage threshold in 0.5 VDC increments, choose a voltage from the HIBATVG(Vdc) drop-down list.
Step 6![]() To change the extreme high battery voltage threshold in 0.5 VDC increments, choose a voltage from the EHIBATVG(Vdc) drop-down list.
To change the extreme high battery voltage threshold in 0.5 VDC increments, choose a voltage from the EHIBATVG(Vdc) drop-down list.
Stop. You have completed this procedure.
NTP-A169 Set Up CTC Network Access
Step 1![]() Complete the A60 Log into CTC. If you are already logged in, continue with Step 2.
Complete the A60 Log into CTC. If you are already logged in, continue with Step 2.
Step 2![]() Complete the A249 Provision IP Settings to provision the ONS 15454 IP address, subnet mask, default router, DHCP server, IIOP listener port, and SOCKS proxy server settings.
Complete the A249 Provision IP Settings to provision the ONS 15454 IP address, subnet mask, default router, DHCP server, IIOP listener port, and SOCKS proxy server settings.

Tip If you cannot log into the node, you can change its IP address, default router, and network mask by using the LCD on the ONS 15454 fan-tray assembly (unless LCD provisioning is suppressed). See the A64 Set the IP Address, Default Router, and Network Mask Using the LCD for instructions. However, you cannot use the LCD to provision any other network settings.
Step 3![]() If you want to turn on the ONS 15454 secure mode, which allows two IP addresses to be provisioned for the node if TCC2P cards are installed, complete the A433 Enable Node Secure Mode. Refer to the “Management Network Connectivity” chapter in the Cisco ONS 15454 Reference Manual for information about secure mode.
If you want to turn on the ONS 15454 secure mode, which allows two IP addresses to be provisioned for the node if TCC2P cards are installed, complete the A433 Enable Node Secure Mode. Refer to the “Management Network Connectivity” chapter in the Cisco ONS 15454 Reference Manual for information about secure mode.
Step 4![]() If static routes are needed, complete the A65 Create a Static Route. Refer to the “Management Network Connectivity” chapter in the Cisco ONS 15454 Reference Manual for further information about static routes.
If static routes are needed, complete the A65 Create a Static Route. Refer to the “Management Network Connectivity” chapter in the Cisco ONS 15454 Reference Manual for further information about static routes.
Step 5![]() If the ONS 15454 is connected to a LAN or WAN that uses OSPF and you want to share routing information between the LAN/WAN and the ONS network, complete the A250 Set Up or Change Open Shortest Path First Protocol.
If the ONS 15454 is connected to a LAN or WAN that uses OSPF and you want to share routing information between the LAN/WAN and the ONS network, complete the A250 Set Up or Change Open Shortest Path First Protocol.
Step 6![]() If the ONS 15454 is connected to a LAN or WAN that uses RIP, complete the A251 Set Up or Change Routing Information Protocol.
If the ONS 15454 is connected to a LAN or WAN that uses RIP, complete the A251 Set Up or Change Routing Information Protocol.
Step 7![]() Complete the A558 Provision the Designated SOCKS Servers after the network is provisioned if SOCKS proxy is enabled and you are experiencing long login and NE discovery times. This can occur in large networks that have a high ENE-to-GNE ratio and a low number of ENEs with LAN connectivity.
Complete the A558 Provision the Designated SOCKS Servers after the network is provisioned if SOCKS proxy is enabled and you are experiencing long login and NE discovery times. This can occur in large networks that have a high ENE-to-GNE ratio and a low number of ENEs with LAN connectivity.
If these conditions do not exist, you are completed with this procedure.
Stop. You have completed this procedure.
NTP-A358 Set up the ONS 15454 in Secure Mode
This procedure provisions ONS 15454s and CTC computers for secure access. |
|
Step 1![]() In node view, click the Provisioning > Security > Access pane.
In node view, click the Provisioning > Security > Access pane.
Step 2![]() Under the EMS Access area, change the Access State to Secure.
Under the EMS Access area, change the Access State to Secure.
Step 3![]() Click Apply. The CTC disconnects and reconnects through a secure socket connection.
Click Apply. The CTC disconnects and reconnects through a secure socket connection.
Step 4![]() To create a secure connection, enter https://node-address.
To create a secure connection, enter https://node-address.

Note![]() After setting up a CTC connection in secure mode, http requests are automatically redirected to https mode.
After setting up a CTC connection in secure mode, http requests are automatically redirected to https mode.
Step 5![]() A first time connection is authenticated by the Website Certification is Not Known dialog box. Accept the certificate and click OK. The Security Error: Domain Name Mismatch dialog box appears. Click OK to continue.
A first time connection is authenticated by the Website Certification is Not Known dialog box. Accept the certificate and click OK. The Security Error: Domain Name Mismatch dialog box appears. Click OK to continue.
Stop. You have completed this procedure.
NTP-A360 Enable EMS Secure Access
This procedure enables EMS secure access. This procedure enables enhanced SFTP and SSH security. |
|
Step 1![]() In shelf view, click the Provisioning > Security > Access pane.
In shelf view, click the Provisioning > Security > Access pane.
Step 2![]() Under the EMS Access area, change the Access State to Secure.
Under the EMS Access area, change the Access State to Secure.
Step 3![]() Click Apply. The CTC disconnects and reconnects through a secure socket connection.
Click Apply. The CTC disconnects and reconnects through a secure socket connection.
Step 4![]() Set the listener port value by choosing “Other constant” radio button.
Set the listener port value by choosing “Other constant” radio button.
Stop. You have completed this procedure.
NTP-A375 Set Up Secure Access to the ONS 15454 TL1
This procedure provisions ONS 15454s for secure access to TL1. |
|
Step 1![]() In the node view, click the Provisioning > Security > Access pane.
In the node view, click the Provisioning > Security > Access pane.
Step 2![]() Under the TL1 Access area, change the Access State to Secure.
Under the TL1 Access area, change the Access State to Secure.
Existing non-secure TL1 sessions, if any, are terminated.
Step 4![]() To create a secure TL1 connection, enter the following command at the UNIX or Linux prompt:
To create a secure TL1 connection, enter the following command at the UNIX or Linux prompt:
ssh -l username node-ip -p port-number
The port number for secure TL1 is 4083.

Note![]() Use any SSH client on Windows.
Use any SSH client on Windows.
Stop. You have completed this procedure.
NTP-A27 Set Up the ONS 15454 for Firewall Access
This procedure provisions ONS 15454s and CTC computers for access through firewalls. |
|
IIOP listener port number provided by your LAN or firewall administrator |
|
Step 1![]() Log into a node that is behind the firewall. See the A60 Log into CTC for instructions. If you are already logged in, continue with Step 2.
Log into a node that is behind the firewall. See the A60 Log into CTC for instructions. If you are already logged in, continue with Step 2.
Step 2![]() Complete the A67 Provision the IIOP Listener Port on the ONS 15454.
Complete the A67 Provision the IIOP Listener Port on the ONS 15454.
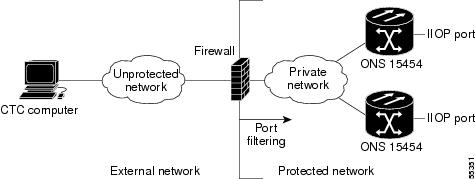
Figure 4-1 shows an ONS 15454 in a protected network and the CTC computer in an external network. For the computer to access the ONS 15454s, you must provision the IIOP listener port specified by your firewall administrator on the ONS 15454.
Figure 4-1 Nodes Behind a Firewall
Step 3![]() If the CTC computer resides behind a firewall, complete the A68 Provision the IIOP Listener Port on the CTC Computer.
If the CTC computer resides behind a firewall, complete the A68 Provision the IIOP Listener Port on the CTC Computer.
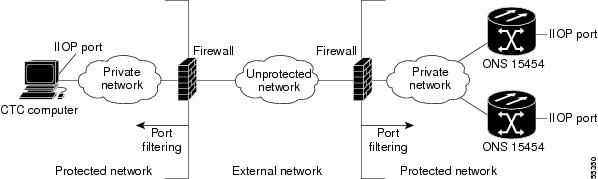
Figure 4-2 shows a CTC computer and ONS 15454 behind firewalls. For the computer to access the ONS 15454, you must provision the IIOP port on the CTC computer and on the ONS 15454.
Figure 4-2 CTC Computer and ONS 15454s Residing Behind Firewalls
Stop. You have completed this procedure.
This procedure provisions an FTP Host that you can use to perform database backup and restore or software download to an End Network Element (ENE) when proxy or firewall is enabled. |
|
Step 1![]() Complete the A60 Log into CTC. If you are already logged in, continue with Step 2.
Complete the A60 Log into CTC. If you are already logged in, continue with Step 2.
Step 2![]() If you want to turn on the ONS 15454 secure mode, which allows two IPv4 addresses to be provisioned for the node if TCC2P cards are installed, complete the A433 Enable Node Secure Mode. Refer to the “Management Network Connectivity” chapter in the Cisco ONS 15454 Reference Manual for information about secure mode.
If you want to turn on the ONS 15454 secure mode, which allows two IPv4 addresses to be provisioned for the node if TCC2P cards are installed, complete the A433 Enable Node Secure Mode. Refer to the “Management Network Connectivity” chapter in the Cisco ONS 15454 Reference Manual for information about secure mode.
Step 3![]() In Node view, click the Provisioning > Network > FTP Hosts tabs.
In Node view, click the Provisioning > Network > FTP Hosts tabs.
Step 5![]() Enter a valid IP address in the FTP Host Address field. A maximum of 12 host can be entered.
Enter a valid IP address in the FTP Host Address field. A maximum of 12 host can be entered.

Note![]() In ONS 15454 Software Release 9.0 and later, you can configure an IPv6 address for an FTP server, in addition to an IPv4 address.
In ONS 15454 Software Release 9.0 and later, you can configure an IPv6 address for an FTP server, in addition to an IPv4 address.
Step 6![]() The Mask is automatically set according to the Net/Subnet Mask length specified in “A249 Provision IP Settings” section. To change the Mask, click the Up/Down arrows on the Length menu.
The Mask is automatically set according to the Net/Subnet Mask length specified in “A249 Provision IP Settings” section. To change the Mask, click the Up/Down arrows on the Length menu.
Step 7![]() Check the FTP Relay Enable radio button to allow FTP commands at the GNE relay. If you will enable the relay at a later time, go to Step 9. Certain TL1 commands executed on an ENE require FTP access into the Data Communication Network (DCN), the FTP relay on the GNE provides this access. The FTP hosts that you have configured in CTC can be used with the TL1 COPY-RFILE (for database backup and restore or software download) or COPY-IOSCFG (for Cisco IOS Configuration File backup and restore) commands.
Check the FTP Relay Enable radio button to allow FTP commands at the GNE relay. If you will enable the relay at a later time, go to Step 9. Certain TL1 commands executed on an ENE require FTP access into the Data Communication Network (DCN), the FTP relay on the GNE provides this access. The FTP hosts that you have configured in CTC can be used with the TL1 COPY-RFILE (for database backup and restore or software download) or COPY-IOSCFG (for Cisco IOS Configuration File backup and restore) commands.
Step 8![]() Enter the time, in minutes, that FTP Relay will be enabled. A valid entry is a number between 0 and 60. The number 0 disallows FTP command relay. After the specified time has elapsed the FTP Relay Enable flag is unset and FTP command relay is disallowed.
Enter the time, in minutes, that FTP Relay will be enabled. A valid entry is a number between 0 and 60. The number 0 disallows FTP command relay. After the specified time has elapsed the FTP Relay Enable flag is unset and FTP command relay is disallowed.
Step 10![]() Repeat Step 4 through Step 9 to provision additional FTP Hosts.
Repeat Step 4 through Step 9 to provision additional FTP Hosts.
Stop. You have completed this procedure.
Step 1![]() Complete the A60 Log into CTC at the node where you will set up timing. If you are already logged in, continue with Step 2.
Complete the A60 Log into CTC at the node where you will set up timing. If you are already logged in, continue with Step 2.
Step 2![]() Complete the A69 Set Up SONET External or Line Timing if an external building integrated timing supply (BITS) source is available. This is the most common SONET timing setup procedure.
Complete the A69 Set Up SONET External or Line Timing if an external building integrated timing supply (BITS) source is available. This is the most common SONET timing setup procedure.
Step 3![]() If you cannot complete Step 2 (an external BITS source is not available), complete the A70 Set Up Internal Timing. This task can only provide Stratum 3 timing.
If you cannot complete Step 2 (an external BITS source is not available), complete the A70 Set Up Internal Timing. This task can only provide Stratum 3 timing.
Step 4![]() Complete the A555 Set Up SDH External or Line Timing if an external BITS source providing SDH timing (64 KHz, E1, or 2 MHz) is available. Use this task for a SONET shelf running on external SDH timing.
Complete the A555 Set Up SDH External or Line Timing if an external BITS source providing SDH timing (64 KHz, E1, or 2 MHz) is available. Use this task for a SONET shelf running on external SDH timing.

Note![]() For information about SONET timing, refer to the “Timing” chapter in the Cisco ONS 15454 Reference Manual or to Telcordia GR-253-CORE.
For information about SONET timing, refer to the “Timing” chapter in the Cisco ONS 15454 Reference Manual or to Telcordia GR-253-CORE.
Stop. You have completed this procedure.
NTP-A324 Create Protection Groups
Step 1![]() Complete the A60 Log into CTC at the node where you want to create the protection group. If you are already logged in, continue with Step 2.
Complete the A60 Log into CTC at the node where you want to create the protection group. If you are already logged in, continue with Step 2.
Table 4-1 describes the protection types available on the ONS 15454.
Step 2![]() Complete one or more of the following tasks depending on the protection groups you want to create:
Complete one or more of the following tasks depending on the protection groups you want to create:

Note![]() If a protect card is not installed, you can complete the A332 Change Tunnel Type and continue with the card protection provisioning.
If a protect card is not installed, you can complete the A332 Change Tunnel Type and continue with the card protection provisioning.

Note![]() A 1+1 protection group can only be provisioned between the same equipment type, using the same port number, and the same port rate. The MRC- 4 (MRC- 4 to MRC- 4 pairing) or MRC-12 (MRC-12 to MRC-12 pairing) cards can be in the same slot type or in different slot type; one in low speed-slot and one in high-speed slot.
A 1+1 protection group can only be provisioned between the same equipment type, using the same port number, and the same port rate. The MRC- 4 (MRC- 4 to MRC- 4 pairing) or MRC-12 (MRC-12 to MRC-12 pairing) cards can be in the same slot type or in different slot type; one in low speed-slot and one in high-speed slot.

Note![]() To create Y-cable protection groups for TXP and MXP cards, refer to the Cisco ONS 15454 DWDM Procedure Guide.
To create Y-cable protection groups for TXP and MXP cards, refer to the Cisco ONS 15454 DWDM Procedure Guide.
Stop. You have completed this procedure.
This procedure provisions the SNMP parameters so that you can use SNMP management software with the ONS 15454. |
|
Step 1![]() Complete the A60 Log into CTC at the node where you want to set up SNMP. If you are already logged in, continue with Step 2.
Complete the A60 Log into CTC at the node where you want to set up SNMP. If you are already logged in, continue with Step 2.
Step 2![]() In node view, click the Provisioning > SNMP tabs.
In node view, click the Provisioning > SNMP tabs.
Step 3![]() In the Trap Destinations area, click Create.
In the Trap Destinations area, click Create.
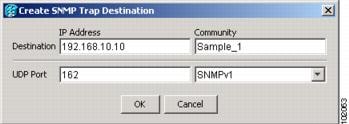
Step 4![]() Complete the following in the Create SNMP Trap Destination dialog box (Figure 4-3):
Complete the following in the Create SNMP Trap Destination dialog box (Figure 4-3):

Note![]() In ONS 15454 Software R9.0 and later, you can configure IPv6 addresses for SNMPv1/v2/v3 trap destinations, Get/Set requests and proxy targets, in addition to IPv4 addresses
In ONS 15454 Software R9.0 and later, you can configure IPv6 addresses for SNMPv1/v2/v3 trap destinations, Get/Set requests and proxy targets, in addition to IPv4 addresses

Note![]() The community name is a form of authentication and access control. The community name assigned to the ONS 15454 is case-sensitive and must match the community name of the network management system (NMS).
The community name is a form of authentication and access control. The community name assigned to the ONS 15454 is case-sensitive and must match the community name of the network management system (NMS).
- UDP Port—The default User Datagram Protocol (UDP) port for SNMP is 162. (More information about provisioning the UDP port is also given in the A449 Set Up SNMP for a GNE and the A450 Set Up SNMP for an ENE.)
- Trap Version—Choose either SNMPv1 or SNMPv2. Refer to your NMS documentation to determine whether to use SNMPv1 or SNMPv2.
Figure 4-3 Creating an SNMP Trap
Step 5![]() Click OK. The node IP address of the node where you provisioned the new trap destination appears in the Trap Destinations area.
Click OK. The node IP address of the node where you provisioned the new trap destination appears in the Trap Destinations area.
Step 6![]() Click the node IP address in the Trap Destinations area. Verify the SNMP information that appears in the Selected Destination list.
Click the node IP address in the Trap Destinations area. Verify the SNMP information that appears in the Selected Destination list.
Step 7![]() If you want to set up SNMP remote monitoring (RMON) on GNEs and ENEs, complete the following tasks as required, depending on the protection groups you want to create:
If you want to set up SNMP remote monitoring (RMON) on GNEs and ENEs, complete the following tasks as required, depending on the protection groups you want to create:
Stop. You have completed this procedure.



Note![]() This procedure requires provisioning of non-ONS equipment including routers and third party network elements. Do not begin until you have the capability to complete that provisioning.
This procedure requires provisioning of non-ONS equipment including routers and third party network elements. Do not begin until you have the capability to complete that provisioning.
Step 1![]() Complete the A60 Log into CTC at the node where you want to provision the OSI routing mode. If you are already logged in, continue with Step 2.
Complete the A60 Log into CTC at the node where you want to provision the OSI routing mode. If you are already logged in, continue with Step 2.
Step 2![]() As needed, complete the following tasks:
As needed, complete the following tasks:
- A534 Provision OSI Routing Mode—Complete this task first.
- A535 Provision or Modify TARP Operating Parameters—Complete this task next.
- A536 Add a Static TID to NSAP Entry to the TARP Data Cache—Complete this task as needed.
- A538 Add a TARP Manual Adjacency Table Entry—Complete this task as needed.
- A539 Provision OSI Routers—Complete this task as needed.
- A540 Provision Additional Manual Area Addresses—Complete this task as needed.
- A541 Enable the OSI Subnet on the LAN Interface—Complete this task as needed.
- A542 Create an IP-Over-CLNS Tunnel—Complete this task as needed.
Stop. You have completed this procedure.
NTP-A364 Provision Node for SNMPv3
Step 1![]() Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Step 2![]() In node view, click the Provisioning > SNMP > SNMP V3 tabs.
In node view, click the Provisioning > SNMP > SNMP V3 tabs.
Step 3![]() Complete the following tasks as required:
Complete the following tasks as required:

Note![]() A group named default_group is defined in the initial configuration. The default group has read and notify access to the complete MIB tree.
A group named default_group is defined in the initial configuration. The default group has read and notify access to the complete MIB tree.

Note![]() A view named full_view is defined in the initial configuration. It includes the complete MIB tree supported on the node.
A view named full_view is defined in the initial configuration. It includes the complete MIB tree supported on the node.
Stop. You have completed this procedure.
NTP-A365 Provision Node to Send SNMPv3 Traps
Step 1![]() Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Step 2![]() In node view, click the Provisioning > SNMP > SNMP V3 tabs.
In node view, click the Provisioning > SNMP > SNMP V3 tabs.
Step 3![]() Complete the following tasks as required:
Complete the following tasks as required:
- A584 Create an SNMPv3 User
- A586 Create Group Access
- A585 Create MIB Views
- A589 Create Notification Filters
- A587 Configure SNMPv3 Trap Destination. When you configure an SNMPv3 trap destination, use the IP address of the NMS, and the port number on which the NMS is listening for traps.
Stop. You have completed this procedure.
NTP-A366 Manually Provision a GNE/ENE to Manage an ENE using SNMPv3
This procedure describes how to manually configure a GNE/ENE to allow the NMS to manage an ENE using SNMPv3. |
|
Step 1![]() Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Step 4![]() Click Provisioning > SNMP > SNMP V3 > General and note the context engine ID. The context engine ID is required in Step 8
Click Provisioning > SNMP > SNMP V3 > General and note the context engine ID. The context engine ID is required in Step 8![]() .
.
Step 6![]() Complete the A584 Create an SNMPv3 User to create an SNMPv3 user on the GNE.
Complete the A584 Create an SNMPv3 User to create an SNMPv3 user on the GNE.
Step 7![]() Complete the following tasks as needed on the ENE:
Complete the following tasks as needed on the ENE:
Step 8![]() Complete the A590 Manually Configure the SNMPv3 Proxy Forwarder Table. Use the context engine ID from Step 4, the local user details created in Step 6, and the remote user created in Step 7.
Complete the A590 Manually Configure the SNMPv3 Proxy Forwarder Table. Use the context engine ID from Step 4, the local user details created in Step 6, and the remote user created in Step 7.
Stop. You have completed this procedure.
NTP-A367 Automatically Provision a GNE to Manage an ENE using SNMPv3
This procedure describes how to automatically configure a GNE to allow an NMS to manage an ENE using SNMPv3. |
|
Step 1![]() Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Step 4![]() Complete the A584 Create an SNMPv3 User to create an SNMPv3 user on the GNE.
Complete the A584 Create an SNMPv3 User to create an SNMPv3 user on the GNE.
Step 5![]() Complete the A591 Automatically Configure the SNMPv3 Proxy Forwarder Table. Use the GNE user that you defined in Step 4 when you configure the Proxy Forwarder table.
Complete the A591 Automatically Configure the SNMPv3 Proxy Forwarder Table. Use the GNE user that you defined in Step 4 when you configure the Proxy Forwarder table.

Note![]() When you use the automatic procedure, CTC automatically creates an ons_proxy user on the ENE, provides ENE user details for the proxy configuration, and the context engine ID of the ENE.
When you use the automatic procedure, CTC automatically creates an ons_proxy user on the ENE, provides ENE user details for the proxy configuration, and the context engine ID of the ENE.
Stop. You have completed this procedure.
NTP-A368 Manually Provision a GNE/ENE to Send SNMPv3 Traps from an ENE using SNMPv3
This procedure describes how to manually configure the GNE/ENE to allow an ENE to send SNMPv3 traps to the NMS. |
|
Step 1![]() Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Step 4![]() Complete the A584 Create an SNMPv3 User to create an SNMPv3 user on the GNE.
Complete the A584 Create an SNMPv3 User to create an SNMPv3 user on the GNE.
Step 5![]() On the GNE, complete the A587 Configure SNMPv3 Trap Destination. The target IP address must be the IPv4 or IPv6 address of the NMS. For the UDP Port number, use the port number on which the NMS is listening for traps. Use the user name configured in Step 4. Also, specify a target tag name.
On the GNE, complete the A587 Configure SNMPv3 Trap Destination. The target IP address must be the IPv4 or IPv6 address of the NMS. For the UDP Port number, use the port number on which the NMS is listening for traps. Use the user name configured in Step 4. Also, specify a target tag name.
Step 7![]() Complete the A584 Create an SNMPv3 User to create an SNMPv3 user on the ENE.
Complete the A584 Create an SNMPv3 User to create an SNMPv3 user on the ENE.
Step 8![]() Complete the following tasks as required:
Complete the following tasks as required:
- A586 Create Group Access to create a group on the ENE
- A585 Create MIB Views to create a MIB view on the ENE
- A589 Create Notification Filters
Step 9![]() On the ENE, complete the A587 Configure SNMPv3 Trap Destination. The target IP address should be the IP address of the GNE. The UDP port number is 161. Use the user name configured in Step 7.
On the ENE, complete the A587 Configure SNMPv3 Trap Destination. The target IP address should be the IP address of the GNE. The UDP port number is 161. Use the user name configured in Step 7.
Step 10![]() From the network view, click the Provisioning > SNMPv3 tabs.
From the network view, click the Provisioning > SNMPv3 tabs.
Step 11![]() Complete the A592 Manually Configure the SNMPv3 Proxy Trap Forwarder Table.
Complete the A592 Manually Configure the SNMPv3 Proxy Trap Forwarder Table.
The source of the trap must be the IP address of the ENE. For the context engine ID field, provide the context engine ID of the ENE. Also, you need to specify the target tag defined in Step 5, and the incoming user details configured in Step 7.
Stop. You have completed this procedure.
NTP-A369 Automatically Provision a GNE/ENE to Send SNMPv3 Traps from an ENE Using SNMPv3
This procedure describes how to automatically configure the GNE/ENE to allow an ENE to send SNMPv3 traps to the NMS. |
|
Step 1![]() Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Complete the A60 Log into CTC on the node on which you want to set up SNMPv3. If you are already logged in, go to Step 2.
Step 4![]() Complete the task A584 Create an SNMPv3 User to create an SNMPv3 user on the GNE.
Complete the task A584 Create an SNMPv3 User to create an SNMPv3 user on the GNE.
Step 5![]() On the GNE, complete the following tasks:
On the GNE, complete the following tasks:
- A587 Configure SNMPv3 Trap Destination. The target IP address must be the IPv4 or IPv6 address of the NMS. For the UDP Port number, use the port number on which the NMS is listening for traps. Also, specify a target tag name.
- A593 Automatically Configure the SNMPv3 Proxy Trap Forwarder Table. Use the target tag configured in Step 4. Use the IP address of the ENE as the source of trap. The following details are created automatically:
–![]() A user named ons_trap_user on the ENE
A user named ons_trap_user on the ENE
–![]() Trap destination on the ENE with an IP address of the GNE as the target IP and 161 as the UDP port number
Trap destination on the ENE with an IP address of the GNE as the target IP and 161 as the UDP port number
–![]() Remote user details of the ENE on the GNE
Remote user details of the ENE on the GNE
Stop. You have completed this procedure.
 Feedback
Feedback