- About this Manual
- Chapter 1, Shelf and Backplane Hardware
- Chapter 2, Common Control Cards
- Chapter 3, Electrical Cards
- Chapter 4, Optical Cards
- Chapter 5, Ethernet Cards
- Chapter 6, DWDM Cards
- Chapter 7, Card Protection
- Chapter 8, Cisco Transport Controller
- Chapter 9, Security and Timing
- Chapter 10, Circuits and Tunnels
- Chapter 11, SONET Topologies
- Chapter 12, DWDM Topologies
- Chapter 13, IP Networking
- Chapter 14, Alarm Monitoring and Management
- Chapter 15, Performance Monitoring
- Chapter 16, Ethernet Operation
- Chapter 17, FC_MR-4 Operations
- Chapter 18, SNMP
- Appendix A, Regulatory and Compliance Requirements
Cisco ONS 15454 Reference Manual, Release 4.6
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- March 20, 2015
Chapter: Chapter 11, SONET Topologies
SONET Topologies
This chapter explains Cisco ONS 15454 SONET topologies. For information about dense wavelength division multiplexing (DWDM) SONET topologies, refer to Chapter 12, "DWDM Topologies."
To provision topologies, refer to the Cisco ONS 15454 Procedure Guide.

Note ![]() The terms "Unidirectional Path Switched Ring" and "UPSR" may appear in Cisco literature. These terms do not refer to using Cisco ONS 15xxx products in a unidirectional path switched ring configuration. Rather, these terms, as well as "Path Protected Mesh Network" and "PPMN," refer generally to Cisco's path protection feature, which may be used in any topological network configuration. Cisco does not recommend using its path protection feature in any particular topological network configuration.
The terms "Unidirectional Path Switched Ring" and "UPSR" may appear in Cisco literature. These terms do not refer to using Cisco ONS 15xxx products in a unidirectional path switched ring configuration. Rather, these terms, as well as "Path Protected Mesh Network" and "PPMN," refer generally to Cisco's path protection feature, which may be used in any topological network configuration. Cisco does not recommend using its path protection feature in any particular topological network configuration.
Chapter topics include:
•![]() Bidirectional Line Switched Rings
Bidirectional Line Switched Rings
•![]() Four-Shelf Node Configurations
Four-Shelf Node Configurations
11.1 SONET Rings and TCC2 Cards
Table 11-1 shows the SONET rings that can be created on each ONS 15454 node using redundant TCC2 cards.
|
|
|
|---|---|
BLSRs |
5 |
2-Fiber BLSR |
5 |
4-Fiber BLSR |
1 |
Path Protection with SDCC |
|
Path Protection with LDCC |
|
Path Protection with LDCC and SDCC |
265 |
1 Total SDCC usage must be equal to or less than 68 SDCCs. 2 See the "Unidirectional Path Switched Rings" section. 3 Total LDCC usage must be equal to or less than 28 LDCCs. 4 See the "Unidirectional Path Switched Rings" section. 5 Total LDCC and SDCC usage must be equal to or less than 73. When LDCC is provisioned, an SDCC termination is allowed on the same port, but is not recommended. Using SDCC and LDCC on the same port is only needed during a software upgrade if the other end of the link does not support LDCC. You can provision SDCCs and LDCCs on different ports in the same node. |
11.2 Bidirectional Line Switched Rings
The ONS 15454 can support five concurrent bidirectional line switch rings (BLSRs) in one of the following configurations:
•![]() Five two-fiber BLSRs
Five two-fiber BLSRs
•![]() Four two-fiber and one four-fiber BLSR
Four two-fiber and one four-fiber BLSR
Each BLSR can have up to 32 ONS 15454s. Because the working and protect bandwidths must be equal, you can create only OC-12 (two-fiber only), OC-48, or OC-192 BLSRs. For information about BLSR protection channels, see the "10.8 BLSR Protection Channel Access Circuits" section on page 10-17.

Note ![]() For best performance, BLSRs should have one LAN connection for every ten nodes in the BLSR.
For best performance, BLSRs should have one LAN connection for every ten nodes in the BLSR.
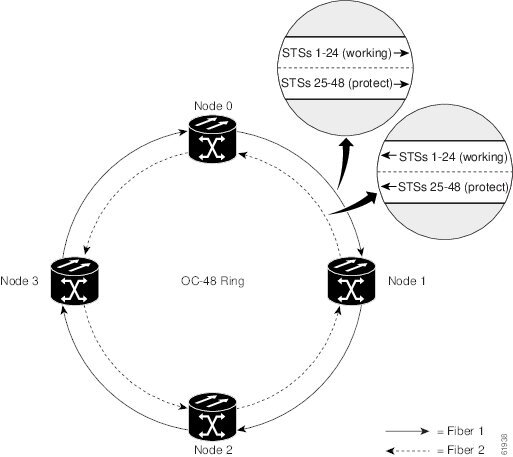
11.2.1 Two-Fiber BLSRs
In two-fiber BLSRs, each fiber is divided into working and protect bandwidths. For example, in an OC-48 BLSR (Figure 11-1), STSs 1 to 24 carry the working traffic, and STSs 25 to 48 are reserved for protection. Working traffic (STSs 1 to 24) travels in one direction on one fiber and in the opposite direction on the second fiber. The Cisco Transport Controller (CTC) circuit routing routines calculate the shortest path for circuits based on many factors, including user requirements, traffic patterns, and distance. For example, in Figure 11-1, circuits going from Node 0 to Node 1 typically travel on Fiber 1, unless that fiber is full, in which case circuits are routed on Fiber 2 through Node 3 and Node 2. Traffic from Node 0 to Node 2 (or Node 1 to Node 3) can be routed on either fiber, depending on circuit provisioning requirements and traffic loads.
Figure 11-1 Four-Node, Two-Fiber BLSR
The SONET K1, K2, and K3 bytes carry the information that governs BLSR protection switches. Each BLSR node monitors the K bytes to determine when to switch the SONET signal to an alternate physical path. The K bytes communicate failure conditions and actions taken between nodes in the ring.
If a break occurs on one fiber, working traffic targeted for a node beyond the break switches to the protect bandwidth on the second fiber. The traffic travels in a reverse direction on the protect bandwidth until it reaches its destination node. At that point, traffic is switched back to the working bandwidth.
Figure 11-2 shows a traffic pattern sample on a four-node, two-fiber BLSR.
Figure 11-2 Four-Node, Two-Fiber BLSR Traffic Pattern Sample
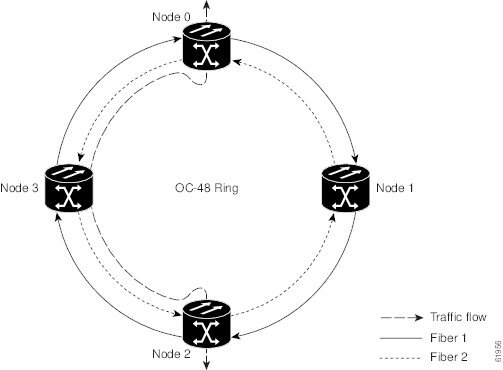
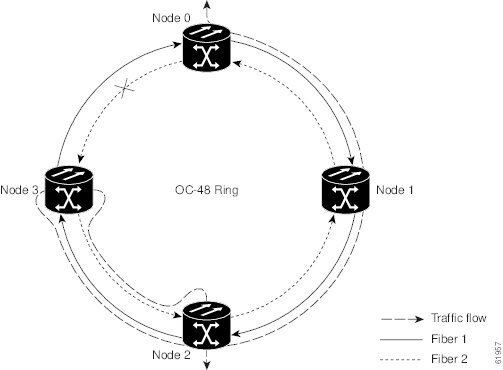
Figure 11-3 shows how traffic is rerouted following a line break between Node 0 and Node 3.
•![]() All circuits originating on Node 0 carried traffic to Node 2 on Fiber 2 are switched to the protect bandwidth of Fiber 1. For example, a circuit carrying traffic on STS-1 on Fiber 2 is switched to STS-25 on Fiber 1. A circuit carried on STS-2 on Fiber 2 is switched to STS-26 on Fiber 1. Fiber 1 carries the circuit to Node 3 (the original routing destination). Node 3 switches the circuit back to STS-1 on Fiber 2 where it is routed to Node 2 on STS-1.
All circuits originating on Node 0 carried traffic to Node 2 on Fiber 2 are switched to the protect bandwidth of Fiber 1. For example, a circuit carrying traffic on STS-1 on Fiber 2 is switched to STS-25 on Fiber 1. A circuit carried on STS-2 on Fiber 2 is switched to STS-26 on Fiber 1. Fiber 1 carries the circuit to Node 3 (the original routing destination). Node 3 switches the circuit back to STS-1 on Fiber 2 where it is routed to Node 2 on STS-1.
•![]() Circuits originating on Node 2 that normally carried traffic to Node 0 on Fiber 1 are switched to the protect bandwidth of Fiber 2 at Node 3. For example, a circuit carrying traffic on STS-2 on Fiber 1 is switched to STS-26 on Fiber 2. Fiber 2 carries the circuit to Node 0 where the circuit is switched back to STS-2 on Fiber 1 and then dropped to its destination.
Circuits originating on Node 2 that normally carried traffic to Node 0 on Fiber 1 are switched to the protect bandwidth of Fiber 2 at Node 3. For example, a circuit carrying traffic on STS-2 on Fiber 1 is switched to STS-26 on Fiber 2. Fiber 2 carries the circuit to Node 0 where the circuit is switched back to STS-2 on Fiber 1 and then dropped to its destination.
Figure 11-3 Four-Node, Two-Fiber BLSR Traffic Pattern Following Line Break
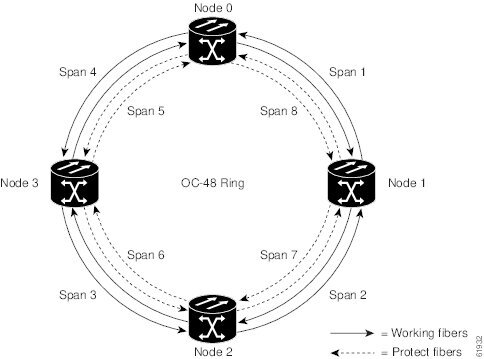
11.2.2 Four-Fiber BLSRs
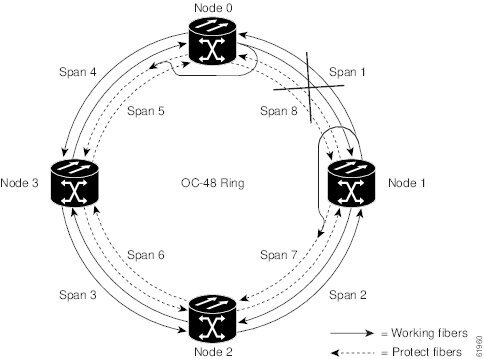
Four-fiber BLSRs double the bandwidth of two-fiber BLSRs. Because they allow span switching as well as ring switching, four-fiber BLSRs increase the reliability and flexibility of traffic protection. Two fibers are allocated for working traffic and two fibers for protection, as shown in Figure 11-4. To implement a four-fiber BLSR, you must install four OC-48, OC-48 AS, or OC-192 cards at each BLSR node.
Figure 11-4 Four-Node, Four-Fiber BLSR
Four-fiber BLSRs provide span and ring switching:
•![]() Span switching (Figure 11-5) occurs when a working span fails. Traffic switches to the protect fibers between the nodes (Node 0 and Node 1 in the example in Figure 11-5) and then returns to the working fibers. Multiple span switches can occur at the same time.
Span switching (Figure 11-5) occurs when a working span fails. Traffic switches to the protect fibers between the nodes (Node 0 and Node 1 in the example in Figure 11-5) and then returns to the working fibers. Multiple span switches can occur at the same time.
•![]() Ring switching (Figure 11-6) occurs when a span switch cannot recover traffic, such as when both the working and protect fibers fail on the same span. In a ring switch, traffic is routed to the protect fibers throughout the full ring.
Ring switching (Figure 11-6) occurs when a span switch cannot recover traffic, such as when both the working and protect fibers fail on the same span. In a ring switch, traffic is routed to the protect fibers throughout the full ring.
Figure 11-5 Four-Fiber BLSR Span Switch
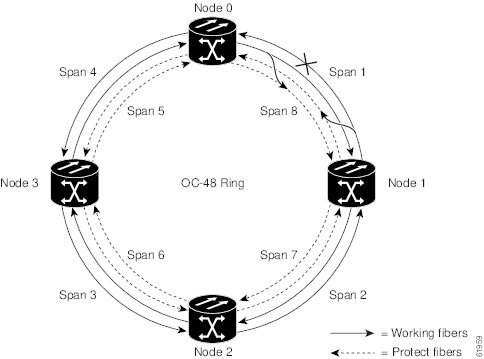
Figure 11-6 Four-Fiber BLSR Ring Switch
11.2.3 BLSR Bandwidth
BLSR nodes can terminate traffic coming from either side of the ring. Therefore, BLSRs are suited for distributed node-to-node traffic applications such as interoffice networks and access networks.
BLSRs allow bandwidth to be reused around the ring and can carry more traffic than a network with traffic flowing through one central hub. BLSRs can also carry more traffic than a path protection operating at the same OC-N rate. Table 11-2 shows the bidirectional bandwidth capacities of two-fiber BLSRs. The capacity is the OC-N rate divided by two, multiplied by the number of nodes in the ring minus the number of pass-through STS-1 circuits. Table 11-3 shows the bidirectional bandwidth capacities of four-fiber BLSRs.
|
|
|
|
|
|---|---|---|---|
OC-12 |
STS1-6 |
STS 7-12 |
|
OC-48 |
STS 1-24 |
STS 25-48 |
24 x N - PT |
OC-192 |
STS 1-96 |
STS 97-192 |
96 x N - PT |
1 N equals the number of ONS 15454 nodes configured as BLSR nodes. 2 PT equals the number of STS-1 circuits passed through ONS 15454 nodes in the ring (capacity can vary depending on the traffic pattern). |
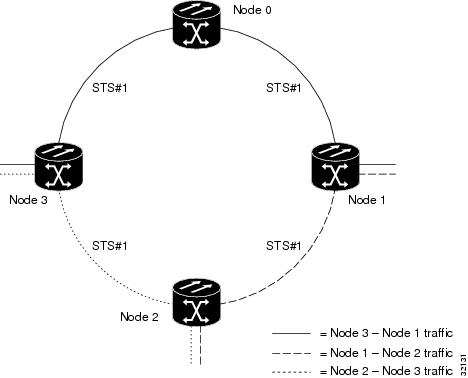
Figure 11-7 shows an example of BLSR bandwidth reuse. The same STS carries three different traffic sets simultaneously on different spans around the ring: one set from Node 3 to Node 1, another set from Node 1 to Node 2, and another set from Node 2 to Node 3.
Figure 11-7 BLSR Bandwidth Reuse
11.2.4 BLSR Application Example
Figure 11-8 shows a two-fiber BLSR implementation example with five nodes. A regional long-distance network connects to other carriers at Node 0. Traffic is delivered to the service provider's major hubs.
•![]() Carrier 1 delivers six DS-3s over two OC-3 spans to Node 0. Carrier 2 provides twelve DS-3s directly. Node 0 receives the signals and delivers them around the ring to the appropriate node.
Carrier 1 delivers six DS-3s over two OC-3 spans to Node 0. Carrier 2 provides twelve DS-3s directly. Node 0 receives the signals and delivers them around the ring to the appropriate node.
•![]() The ring also brings 14 DS-1s back from each remote site to Node 0. Intermediate nodes serve these shorter regional connections.
The ring also brings 14 DS-1s back from each remote site to Node 0. Intermediate nodes serve these shorter regional connections.
•![]() The ONS 15454 OC-3 card supports a total of four OC-3 ports so that two additional OC-3 spans can be added at little cost.
The ONS 15454 OC-3 card supports a total of four OC-3 ports so that two additional OC-3 spans can be added at little cost.
Figure 11-8 Five-Node Two-Fiber BLSR
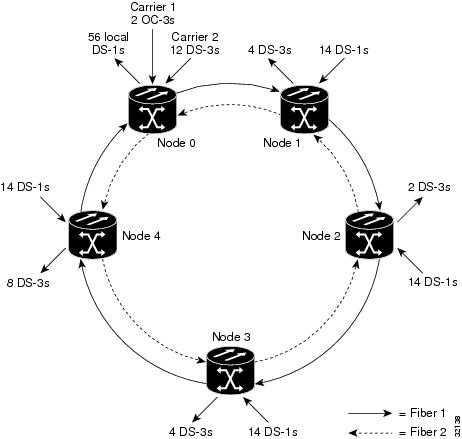
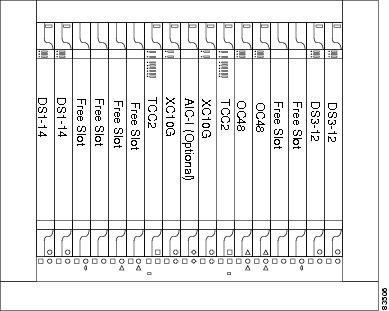
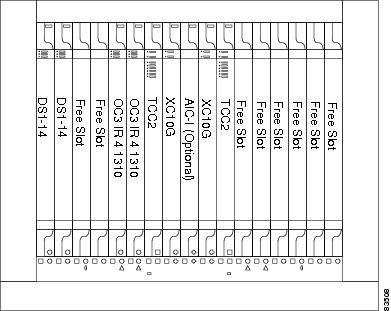
Figure 11-9 shows the shelf assembly layout for Node 0, which has one free slot. Figure 11-10 shows the shelf assembly layout for the remaining sites in the ring. In this BLSR configuration, an additional eight DS-3s at Node IDs 1 and 3 can be activated. An additional four DS-3s can be added at Node 4, and ten DS-3s can be added at Node 2. Each site has free slots for future traffic needs.
Figure 11-9 Shelf Assembly Layout for Node 0 in Figure 11-8
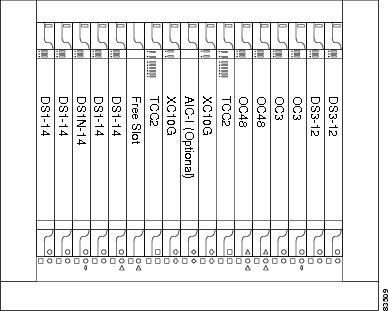
Figure 11-10 Shelf Assembly Layout for Nodes 1 to 4 in Figure 11-8
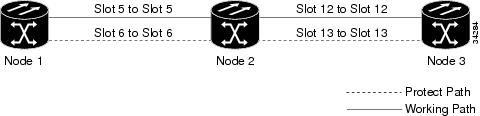
11.2.5 BLSR Fiber Connections
Plan your fiber connections and use the same plan for all BLSR nodes. For example, make the east port the farthest slot to the right and the west port the farthest slot to the left. Plug fiber connected to an east port at one node into the west port on an adjacent node. Figure 11-11 shows fiber connections for a two-fiber BLSR with trunk cards in Slot 5 (west) and Slot 12 (east). Refer to the Cisco ONS 15454 Procedure Guide for fiber connection procedures.

Note ![]() Always plug the transmit (Tx) connector of an OC-N card at one node into the receive (Rx) connector of an OC-N card at the adjacent node. Cards display an SF LED when Tx and Rx connections are mismatched.
Always plug the transmit (Tx) connector of an OC-N card at one node into the receive (Rx) connector of an OC-N card at the adjacent node. Cards display an SF LED when Tx and Rx connections are mismatched.
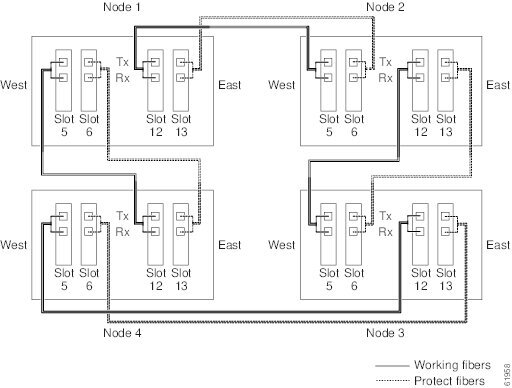
For four-fiber BLSRs, use the same east-west connection pattern for the working and protect fibers. Do not mix working and protect card connections. The BLSR does not function if working and protect cards are interconnected. Figure 11-12 shows fiber connections for a four-fiber BLSR. Slot 5 (west) and Slot 12 (east) carry the working traffic. Slot 6 (west) and Slot 13 (east) carry the protect traffic.
Figure 11-11 Connecting Fiber to a Four-Node, Two-Fiber BLSR
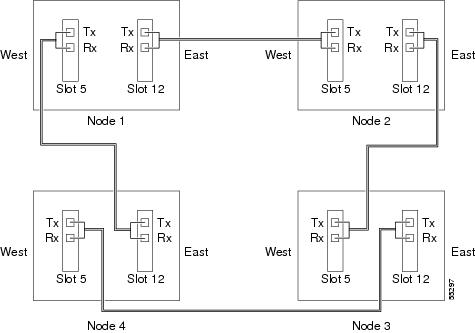
Figure 11-12 Connecting Fiber to a Four-Node, Four-Fiber BLSR
11.2.6 Two-Fiber BLSR to Four-Fiber BLSR Conversion
Two-fiber OC-48 or OC-192 BLSRs can be converted to four-fiber BLSRs. To convert the BLSR, install two OC-48 or OC-192 cards at each two-fiber BLSR node, then log into CTC and convert each node from two-fiber to four-fiber. The fibers that were divided into working and protect bandwidths for the two-fiber BLSR are now fully allocated for working BLSR traffic. Refer to the Cisco ONS 15454 Procedure Guide for BLSR conversion procedures.
11.3 Unidirectional Path Switched Rings
Path Protection configurations provide duplicate fiber paths around the ring. Working traffic flows in one direction and protection traffic flows in the opposite direction. If a problem occurs with the working traffic path, the receiving node switches to the path coming from the opposite direction.
CTC automates ring configuration. path protection traffic is defined within the ONS 15454 on a circuit-by-circuit basis. If a path-protected circuit is not defined within a 1+1 or BLSR line protection scheme and path protection is available and specified, CTC uses path protection as the default.
A path protection circuit requires two DCC-provisioned optical spans per node. path protection circuits can be created across these spans until their bandwidth is consumed.

Note ![]() If a path protection circuit is created manually by TL1, data communication channels (DCCs) are not needed; therefore, path protection circuits are limited by the cross-connection bandwidth, or the span bandwidth, but not by the number of DCCs.
If a path protection circuit is created manually by TL1, data communication channels (DCCs) are not needed; therefore, path protection circuits are limited by the cross-connection bandwidth, or the span bandwidth, but not by the number of DCCs.
The span bandwidth consumed by a path protection circuit is two times the circuit bandwidth, because the circuit is duplicated. The cross-connection bandwidth consumed by a path protection circuit is three times the circuit bandwidth at the source and destination nodes only. The cross-connection bandwidth consumed by an intermediate node has a factor of one.
The path protection circuit limit is the sum of the optical bandwidth containing 68 section data communication channels (SDCCs) or 28 line data communication channels (LDCCs), divided by two if you are using redundant TCC2 cards. The spans can be of any bandwidth from OC-3 to OC-192. The circuits can be of any size from VT1.5 to 192c.
Figure 11-13 shows a basic four-node path protection configuration. If Node ID 0 sends a signal to Node ID 2, the working signal travels on the working traffic path through Node ID 1. The same signal is also sent on the protect traffic path through Node ID 3. If a fiber break occurs (Figure 11-14), Node ID 2 switches its active receiver to the protect signal coming through Node ID 3.
Because each traffic path is transported around the entire ring, path protections are best suited for networks where traffic concentrates at one or two locations and is not widely distributed. path protection capacity is equal to its bit rate. Services can originate and terminate on the same path protection, or they can be passed to an adjacent access or interoffice ring for transport to the service-terminating location.
Figure 11-13 Basic Four-Node Path Protection
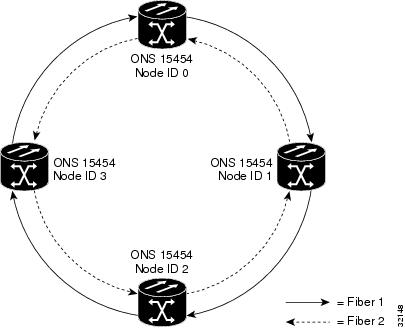
Figure 11-14 Path Protection with a Fiber Break
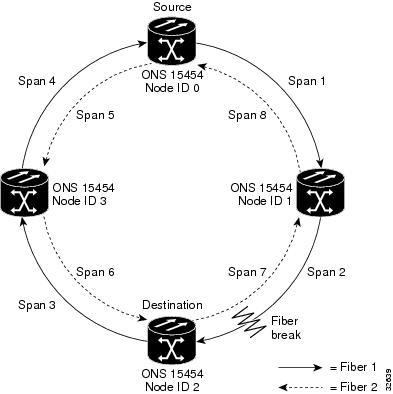
Figure 11-15 shows a common path protection application. OC-3 optics provide remote switch connectivity to a host Telcordia TR-303 switch. In the example, each remote switch requires eight DS-1s to return to the host switch. Figure 11-16 and Figure 11-17 show the shelf layout for each site.
Figure 11-15 Four-Port, OC-3 Path Protection
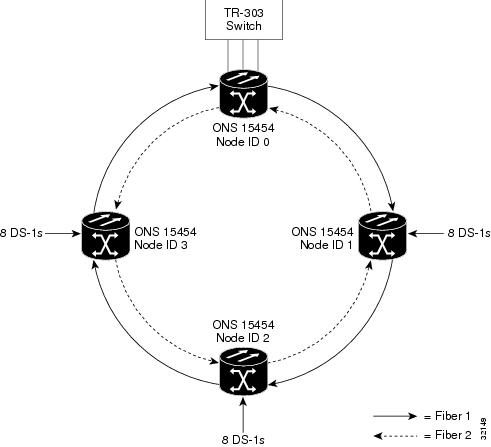
Node ID 0 has four DS1-14 cards to provide 56 active DS-1 ports. The other sites only require two DS1-14 cards to handle the eight DS-1s to and from the remote switch. You can use the other half of each ONS 15454 shelf assembly to provide support for a second or third ring to other existing or planned remote sites.
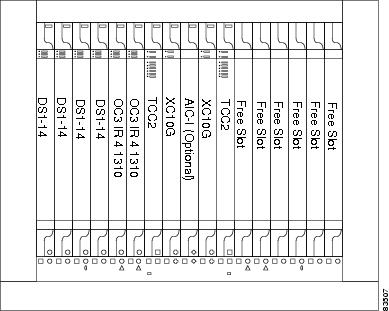
In the OC-3 path protection sample, Node ID 0 contains four DS1-14 cards and two OC3 IR 4 1310 cards. Six free slots can be provisioned with cards or left empty. Figure 11-16 shows the shelf setup for these cards.
Figure 11-16 Layout of Node ID 0 in the OC-3 Path Protection Example in Figure 11-15
In the Figure 11-15 example, Nodes IDs 1 to 3 each contain two DS1-14 cards and two OC3 IR 4 1310 cards. Eight free slots exist. They can be provisioned with other cards or left empty. Figure 11-17 shows the shelf assembly setup for this configuration example.
Figure 11-17 Layout of Node IDs 1 to 3 in the OC-3 Path Protection Example in Figure 11-15
11.4 Linear ADM Configurations
You can configure ONS 15454s as a line of add/drop multiplexers (ADMs) by configuring one set of OC-N cards as the working path and a second set as the protect path. Unlike rings, linear (point-to-point) ADMs require that the OC-N cards at each node be in 1+1 protection to ensure that a break to the working line is automatically routed to the protect line.
Figure 11-18 shows three ONS 15454s in a linear ADM configuration. Working traffic flows from Slot 5/Node 1 to Slot 5/Node 2, and from Slot 12/Node 2 to Slot 12/Node 3. You create the protect path by placing Slot 6 in 1+1 protection with Slot 5 at Nodes 1 and 2, and Slot 12 in 1+1 protection with Slot 13 at Nodes 2 and 3.
Figure 11-18 Linear (Point-to-Point) ADM Configuration
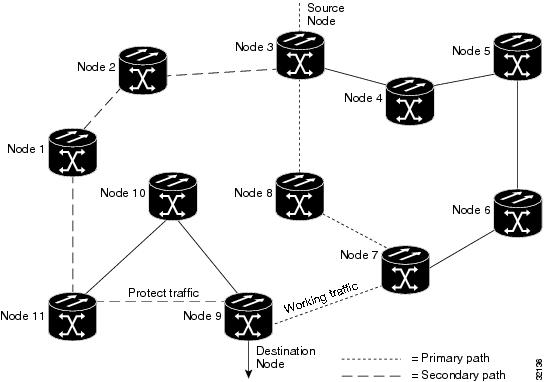
11.5 Path-Protected Mesh Networks
In addition to single BLSRs, path protection configurations, and ADMs, you can extend ONS 15454 traffic protection by creating path-protected mesh networks (PPMNs). PPMNs include multiple ONS 15454 SONET topologies and extend the protection provided by a single path protection to the meshed architecture of several interconnecting rings. In a PPMN, circuits travel diverse paths through a network of single or multiple meshed rings. When you create circuits, you can have CTC automatically route circuits across the PPMN, or you can manually route them. You can also choose levels of circuit protection. For example, if you choose full protection, CTC creates an alternate route for the circuit in addition to the main route. The second route follows a unique path through the network between the source and destination and sets up a second set of cross-connections.
For example, in Figure 11-19 a circuit is created from Node 3 to Node 9. CTC determines that the shortest route between the two nodes passes through Node 8 and Node 7, shown by the dotted line, and automatically creates cross-connections at Nodes 3, 8, 7, and 9 to provide the primary circuit path.
If full protection is selected, CTC creates a second unique route between Nodes 3 and 9 which, in this example, passes through Nodes 2, 1, and 11. Cross-connections are automatically created at Nodes 3, 2, 1, 11, and 9, shown by the dashed line. If a failure occurs on the primary path, traffic switches to the second circuit path. In this example, Node 9 switches from the traffic coming in from Node 7 to the traffic coming in from Node 11 and service resumes. The switch occurs within 50 ms.
Figure 11-19 Path-Protected Mesh Network
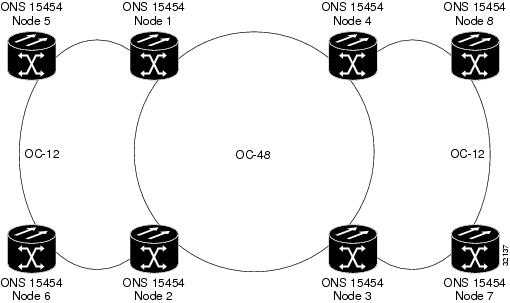
PPMN also allows spans with different SONET speeds to be mixed together in "virtual rings." Figure 11-20 shows Nodes 1, 2, 3, and 4 in a standard OC-48 ring. Nodes 5, 6, 7, and 8 link to the backbone ring through OC-12 fiber. The "virtual ring" formed by Nodes 5, 6, 7, and 8 uses both OC-48 and OC-12 cards.
Figure 11-20 PPMN Virtual Ring
11.6 Four-Shelf Node Configurations
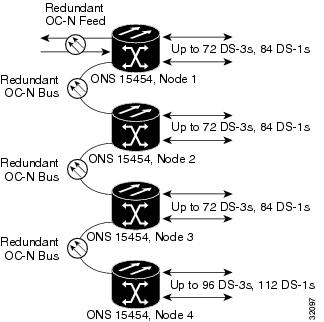
You can link multiple ONS 15454s using their OC-N cards (that is, create a fiber-optic bus) to accommodate more access traffic than a single ONS 15454 can support. Refer to the Cisco ONS 15454 Procedure Guide. For example, to drop more than 112 DS-1s or 96 DS-3s (the maximum that can be aggregated in a single node), you can link the nodes but not merge multiple nodes into a single ONS 15454. You can link nodes with OC-12 or OC-48 fiber spans as you would link any other two network nodes. The nodes can be grouped in one facility to aggregate more local traffic.
Figure 11-21 shows a four-shelf node setup. Each shelf assembly is recognized as a separate node in the ONS 15454 software interface and traffic is mapped using CTC cross-connect options. In Figure 11-21, each node uses redundant fiber-optic cards. Node 1 uses redundant OC-N transport and OC-N bus (connecting) cards for a total of four cards, with eight free slots remaining. Nodes 2 and 3 each use two redundant OC-N bus cards for a total of four cards, with eight free slots remaining. Node 4 uses redundant OC-12 bus cards for a total of two cards, with ten free slots remaining. The four-shelf node example presented here is one of many ways to set up a multiple-node configuration.
Figure 11-21 Four-Shelf Node Configuration
11.7 OC-N Speed Upgrades
A span is the optical fiber connection between two ONS 15454 nodes. In a span (optical speed) upgrade, the transmission rate of a span is upgraded from a lower to a higher OC-N signal but all other span configuration attributes remain unchanged. With multiple nodes, a span upgrade is a coordinated series of upgrades on all nodes in the ring or protection group. You can perform in-service span upgrades for the following ONS 15454 cards:
•![]() Single-port OC-12 to OC-48
Single-port OC-12 to OC-48
•![]() Single-port OC-12 to OC-192
Single-port OC-12 to OC-192
•![]() OC-48 to OC-192
OC-48 to OC-192
You can also perform in-service card upgrades for the following ONS 15454 cards:
•![]() Four-port OC-3 to eight-port OC-3
Four-port OC-3 to eight-port OC-3
•![]() Single-port OC-12 to four-port OC-12
Single-port OC-12 to four-port OC-12

Note ![]() Since the four-port OC-3 to eight-port OC-3 cards and the single-port OC-12 to four-port OC-12 cards are the same speed, they are not considered span upgrades.
Since the four-port OC-3 to eight-port OC-3 cards and the single-port OC-12 to four-port OC-12 cards are the same speed, they are not considered span upgrades.
Use the XC10G card, the TCC2 card, Software R4.0 or later, and the 15454-SA-ANSI shelf assembly to enable the OC48AS and the OC192 cards.
To perform a span upgrade, the higher-rate OC-N card must replace the lower-rate card in the same slot. If the upgrade is conducted on spans residing in a BLSR, all spans in the ring must be upgraded. The protection configuration of the original lower-rate OC-N card (two-fiber BLSR, four-fiber BLSR, path protection, and 1+1) is retained for the higher-rate OC-N card.
When performing span upgrades on a large number of nodes, we recommend that you upgrade all spans in a ring consecutively and in the same maintenance window. Until all spans are upgraded, mismatched card types are present.
We recommend using the Span Upgrade Wizard to perform span upgrades. Although you can also use the manual span upgrade procedures, the manual procedures are mainly provided as error recovery for the wizard. The Span Upgrade Wizard and the Manual Span Upgrade procedures require at least two technicians (one at each end of the span) who can communicate with each other during the upgrade. Upgrading a span is non-service affecting and causes no more than three switches, each of which is less than 50 ms in duration.

Note ![]() Span upgrades do not upgrade SONET topologies, for example, a 1+1 group to a two-fiber BLSR. Refer to the Cisco ONS 15454 Procedure Guide for topology upgrade procedures.
Span upgrades do not upgrade SONET topologies, for example, a 1+1 group to a two-fiber BLSR. Refer to the Cisco ONS 15454 Procedure Guide for topology upgrade procedures.
11.7.1 Span Upgrade Wizard
The Span Upgrade Wizard automates all steps in the manual span upgrade procedure (BLSR, path protection, and 1+1). The wizard can upgrade both lines on one side of a four-fiber BLSR or both lines of a 1+1 group; the wizard upgrades path protection configurations and two-fiber BLSRs one line at a time. The Span Upgrade Wizard requires that spans have DCCs enabled.
The Span Upgrade Wizard provides no way to back out of an upgrade. In the case of an error, you must exit the wizard and initiate the manual procedure to either continue with the upgrade or back out of it. To continue with the manual procedure, examine the standing conditions and alarms to identify the stage in which the wizard failure occurred.
11.7.2 Manual Span Upgrades
Manual span upgrades are mainly provided as error recovery for the Span Upgrade Wizard, but they can be used to perform span upgrades. Downgrading can be performed to back out of a span upgrade. The procedure for downgrading is the same as upgrading except that you choose a lower-rate card type. You cannot downgrade if circuits exist on the STSs that will be removed (the higher STSs).
Procedures for manual span upgrades can be found in the "Upgrade Cards and Spans" chapter in the ONS 15454 SDH Procedure Guide. Five manual span upgrade options are available:
•![]() Upgrade on a two-fiber BLSR
Upgrade on a two-fiber BLSR
•![]() Upgrade on a four-fiber BLSR
Upgrade on a four-fiber BLSR
•![]() Upgrade on a path protection
Upgrade on a path protection
•![]() Upgrade on a 1+1 protection group
Upgrade on a 1+1 protection group
•![]() Upgrade on an unprotected span
Upgrade on an unprotected span
 Feedback
Feedback