Router Interface Configurations
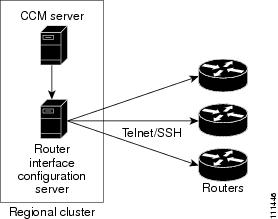
The regional Router Interface Configuration (RIC) server is used to manage router interfaces on Cisco Systems Universal Broadband Routers (uBRs) that manage cable modem termination systems (CMTSs). This module interacts with the CMTS servers to push the required cable modem configuration to edge devices, such as routers and switches (see the image below). The RIC server module is accessible only if you are assigned the ric-management subrole of the cfg-admin or central-cfg-admin role.
 Tip |
Add routers before you add any other subnets. This prevents the subnets that the router creates from possibly overlapping with those explicitly added, and prevents router synchronization errors later on. |
The view of the routers is available on the View Tree of Routers page. The tree levels are the routers, their router interfaces, and any child interfaces. Parent/child relationships can be either physical/virtual (as in Cable2/0 and Cable2/0.1) or primary/secondary (as in router interface bundling, where the bundle is identified by one of the interfaces; see Bundling Interfaces). This listing of router interfaces is available only after you create routers in the system and synchronize with them.
Managed Versus Virtual Routers
Managed routers are updated in the database as well as being physically updated and synchronized. When you edit a managed router, the router is also automatically updated and synchronized with the newest data.
Virtual routers are updated in the Cisco Prime Network Registrar database only. However, you can create, push, and reclaim subnets for a virtual router. You might define a virtual router when the RIC server cannot directly manage the router, but the virtual router should still be considered part of the topology.
You can define a virtual router by omitting the router type or connection credentials on the Add Router page or Edit Router page.
Secure Mode Connections with Routers
To enable secure communication between the RIC server and the routers, you must have the Cisco Prime Network Registrar Communications Security Option Release 1.1 installed. By default, secure connectivity is disabled and accessible over Telnet. However, you can specify whether you require or desire a Secure Shell (SSH) connection. Use the use-ssh attribute in the (expandable) Reserved attributes section of the Edit Router page. This attribute has the following values:
- disabled (preset value)—Uses simple Telnet for the connection.
- required —The router communicates with the edge device using SSH only, and not Telnet.
- desired —The router tries to communicate using SSH, but if it cannot, it uses Telnet.
 Note |
The SSH server should be set up so that the key length (modulus) is at least 1024 bits, using, for example, the command crypto key generate rsa general-keys modulus 1024 . |
 Feedback
Feedback