- Setting Up Prime Network and Using Prime Network with Cisco Prime Central
- Managing the Prime Network Software Image, Features, and Backups
- Managing Prime Network Components: Gateways, Units, and AVMs
- Configuring Device VNEs and Troubleshooting VNE Problems
- Managing Redundancy for Units and Processes
- Controlling Device Access and Authorization Using Device Scopes
- Managing User Accounts and Authentication
- Managing the Oracle Database and System Data
- Controlling Event Monitoring
- Managing Device Configuration Operations
- Managing System Security
- Changing VNE Polling, Reachability, Discovery, and Persistency and Working with Unmanaged Segments (Cloud VNEs)
- Configuring Devices So They Can Be Properly Modeled and Managed by Prime Network
- Changing System Defaults in the Registry
- Prime Network Log Files
- VNE Properties Reference
Cisco Prime Network Administrator Guide, 4.3.2
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- July 19, 2017
Chapter: Managing User Accounts and Authentication
- User Authentication and Authorization Overview
- Checking Existing User Accounts
- Configuring Global User Password Settings
- Configuring Global User Permissions: Account Inactivity, Device Credential Requirements, and Global Job Scheduling
- Configuring Global Report Security Settings (Public Reports)
- Configuring E-Mail Notification Address in Global Report Settings
- Changing GUI Client User Passwords
- Creating a New User Account and Viewing User Properties
- Changing User Accounts and Device Scope Access
- Changing the Minimum User Access Role for the Events and Administration Clients
- Configuring External User Authentication (LDAP)
- Controlling Which Maps Users Can Access
- Re-enabling User Accounts
- Deleting a Prime Network User Account
- Tracking User-Related Events
Managing User Accounts and Authentication

Note User authentication and authorization by Prime Network is disabled if Prime Network is installed with Cisco Prime Central. If you want to prevent users from managing tickets from the Prime Network clients, see Disabling Ticket Management in the Prime Network Vision and Events Clients.
User account settings determine the actions users can perform in Prime Network. Each user has an access role that determines the GUI-based tasks they can perform. Device-based tasks are determined by the device scopes that are applied to a user’s account, and the privileges they have for that scope. You can also control which maps users can access.
These topics explain how to create and manage user accounts. These topics also explain how to change global password rules and how to change the default access role required to log into the Events GUI client.
- User Authentication and Authorization Overview
- Checking Existing User Accounts
- Configuring Global User Password Settings
- Configuring Global User Permissions: Account Inactivity, Device Credential Requirements, and Global Job Scheduling
- Configuring Global Report Security Settings (Public Reports)
- Configuring E-Mail Notification Address in Global Report Settings
- Creating a New User Account and Viewing User Properties
- Changing User Accounts and Device Scope Access
- Changing the Minimum User Access Role for the Events and Administration Clients
- Configuring External User Authentication (LDAP)
- Controlling Which Maps Users Can Access
- Re-enabling User Accounts
- Deleting a Prime Network User Account
- Tracking User-Related Events
If you want to find out who is logged into the gateway (and disconnect them, if necessary), see Managing Client and User Sessions.
User Authentication and Authorization Overview

Note Most user authentication and authorization features by Prime Network are disabled if Prime Network is installed with Cisco Prime Central. See Configuring Global User Permissions: Account Inactivity, Device Credential Requirements, and Global Job Scheduling for the exceptions.
In Prime Network , user authentication and authorization is controlled by a combination of device scopes, user roles, and other settings in a user’s account. While device scopes determine which devices a user can access and what they can do to those devices, user roles and account settings determine the GUI tasks a user can perform.
User Authentication
User authentication is managed either locally by Prime Network, or externally by an LDAP application. Either method can be used to validate user accounts and passwords, thus controlling who can log into Prime Network. If you use Prime Network for authentication, user information and passwords are stored in the Prime Network Oracle database. If you use an external LDAP application for authentication, passwords are stored on the external LDAP server. (User authorization information—that is, roles and scopes—is always stored in the Prime Network Oracle database. The external LDAP server, if used, only stores passwords.) The external authentication method has a special user called the emergency user . In Prime Network, root is designated as the external authentication emergency user. This means if Prime Network loses communication with the LDAP server, Prime Network will allow root (and only root) to log in. The root user can then change the authentication method to local, and edit user accounts so that those users can subsequently log in. Prime Network uses LDAP version 3.
Other User Account Settings that Affect Authentication
When you create a user’s account, you can also specify the intervals at which users must change their passwords. Prime Network also has authentication settings that are controlled at the global level, such as how many login attempts are permitted before the user is locked out, and when to lock the account due to user inactivity. If a user account is locked, you can easily reenable it from their user account dialog box.
Change the Authentication Method
If you want to change to external authentication, you must do the following:
- Perform the necessary installation prerequisites. Refer to the Cisco Prime Network 4.3.2 Installation Guide .
- Configure Prime Network so that it can communicate with the LDAP server. See Using an External LDAP Server for Password Authentication.
If you want to change from external authentication to Prime Network authentication, you can import the user information from the LDAP server into Prime Network. That procedure is described in the Changing from External to Local Authentication.
User Authorization
User authorization is controlled by a combination of user roles, device scopes, and other user account settings.
Prime Network provides five predefined security access roles that you can assign to a user when you create their account: Viewer, Operator, OperatorPlus, Configurator, and Administrator. These roles determine which actions a user is permitted to perform in the Prime Network GUI clients. Table 7-1 describes the five user roles.

Note Users with higher user roles can perform all the actions for which lower roles are authorized. For example, the Configurator is authorized to perform all the actions that the Viewer, Operator and OperatorPlus can perform.
When you create a user account, you assign one user access role to the account. This role determines the user’s default permissions, which in turn determine the GUI-based functions the user can perform (those that do not affect devices).
When a new user is defined as an Administrator, this user can perform all administrative actions, including opening all maps, working with all scopes, and managing the system using Prime Network Administration. These activities are performed with the highest privileges. Prime Network Administration supports multiple administrators.
Device scopes control which devices a user can access, and the actions they can perform on those devices. When you create the user account, you assign one or more device scopes to the user’s account, along with a security level for that scope. Detailed information about device scopes and security levels is provided in Controlling Device Access and Authorization Using Device Scopes. You can add device scopes to a user account Changing User Accounts and Device Scope Access.
Other Settings that Affect Authorization
These settings also affect authorization:
- When you create a user’s account, you can also specify whether the user is permitted to create public (shared) reports and manage jobs. See Configuring Global User Permissions: Account Inactivity, Device Credential Requirements, and Global Job Scheduling.
- Ticket actions can be disabled from the Global Settings branch. This disallows both Vision and Events client users from ticket operations such as clearing, acknowledging and deacknowledging, clearing, adding notes, and so forth. By default, ticket actions remain enabled when you are using Prime Network with Cisco Prime Central. If you want to disable ticket operations in Prime Network, see Disabling Ticket Management in the Prime Network Vision and Events Clients.
Checking Existing User Accounts
To check existing user accounts, click Users in the navigation area. Figure 7-1 shows an example of the Prime Network Administration window with Users selected.
Note If Prime Network is installed with Cisco Prime Central, you can view user properties but you cannot add or change them.
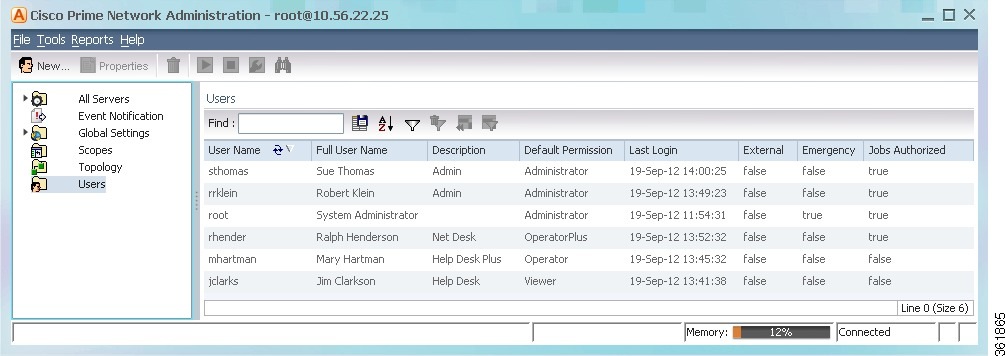
The following describes the columns that are displayed in the Users table.
The default permission of the user, such as Viewer or Administrator. For example, a user with the default permission Viewer can view maps and the Device List. Note The default permission applies only at an application level; that is, it applies to all activities that are related to GUI functionality and not the activities related to devices. Device access is controlled through the device scopes mechanism. |
|
Indicates whether an external authentication server is used for account and password verification. |
|
Indicates that a user is designated as an emergency user for the external authentication server, in case the external server goes down. |
|
Indicates whether the user can schedule jobs when the global Job Scheduling setting is enabled. (See Configuring Global User Permissions: Account Inactivity, Device Credential Requirements, and Global Job Scheduling. |
Configuring Global User Password Settings

Note This feature is disabled if Prime Network is installed with Cisco Prime Central.
To change the global user password settings listed in Table 7-2 , choose Global Settings > Security Settings > Password Settings . Changes are applied after you click Apply .
Number of attempts before a user’s account is disabled. (Administrators can reenable accounts as described in Changing User Accounts and Device Scope Access.) |
||
Password cannot contain more than ___ consecutive characters from the previous passwords |
||
|
Note You can set the password character length between 8-32. The minimum supported character length for change in user password for Prime Network administration is 8, however the minimum supported character length for change in user password during Prime Network installation is 9. |
||
Number of days before the password expires. User will receive a warning during the login that his password is about to expire in x days. |
||
Configuring Global User Permissions: Account Inactivity, Device Credential Requirements, and Global Job Scheduling
The global User Account Settings page allows you to configure the following features that affect all Prime Network users:
- When users accounts should be disabled due to account inactivity (30 days by default)
- Whether users must enter device credentials before executing any features that user command scripts (disabled by default)
- Whether users can schedule jobs only if they have been granted this privilege in their user account (disabled by default)
To change these settings, choose Global Settings > Security Settings > User Account Settings . Changes are applied to new users; for existing users in active sessions, the changes are applied the next time they log in.
Changes the timer for when Prime Network should disable a user account due to inactivity. To disable this setting (so that accounts are never disabled), enter 0. |
||
Check the Ask for user credentials when running device configuration operations check box to enter their device credentials when they execute command scripts from these features:
If the feature is enabled, users are prompted for their username and password when they run a command. Provisioning and Audit events display an additional column that lists the user name. Prime Network Vision instances must be restarted after enabling and disabling the execution of commands. You must logout and then login again for the changes to take effect. When PN connects to a device, only certain combinations of device credentials are supported. For example, the credential sequence must start with a username and password, the following sequences are allowed. Note Ensure to uncheck the Ask for user credentials when running device configuration operations check box for devices with an unsupported device credential sequence. While connecting to a device through SSH, PN takes the username and password entered by the user and the rest of the device credential sequence is taken from the vne properties. For transactions (activation workflows), users must have the same credentials for all devices in the transaction because Prime Network propagates the credentials to all command scripts in the transaction. Once the credentials are entered, they are used throughout the current GUI client session for all subsequent commands. This feature is not available for scheduled commands or for SNMP commands. In those cases, the VNE credentials will be used (this is the Prime Network default behavior). VNE credentials are not exposed; events will display the device username as From VNE login . Note You can also configure Prime Network to generate a warning message whenever a user executes a command script. See Adding a Warning Message to Command Scripts. (If Prime Network is used with Prime Central, this is enabled by default.) |
||
Check the Allow only authorized users to schedule jobs check box to enable user authorization for any Prime Network features that use jobs. This feature works with the job setting in individual user accounts (see Creating a New User Account and Viewing User Properties). If global Job Scheduling is enabled, job privileges are controlled by the settings in individual user accounts:
If global Job Scheduling is disabled (which is the default), the setting in individual user accounts is ignored. (If Prime Network is used with Prime Central where Job Scheduling is enabled by default, job privileges are controlled by the settings in individual user accounts.) |
Configuring Global Report Security Settings (Public Reports)

Note This feature is disabled if Prime Network is installed with Cisco Prime Central.
To change the global report setting listed in Table 7-4 , choose Global Settings > Report Settings .
Allows all users to create shared (public) reports. When a report is public, all users can view the contents; reports are not filtered according to scopes or security privileges. |
||
Specifies how long to save a report. (For information on Prime Network data purging, see Purging Reports.) |
||
Specifies the maximum disk size, in MB, at which reports should be purged. (For information on Prime Network data purging, see Purging Reports.) |
Configuring E-Mail Notification Address in Global Report Settings
To avoid entering the email address details each time while creating a report, you can configure an Email Server name or an IP and From Address details in the Global Report Settings. When these values are saved in a registry, you an use these values every time when an email notification is sent from the Prime Network Administrator or Vision client.
To enter e-mail notification settings:
Step 1 Launch the Prime Network Administrator client.
Step 2 Expand the Global Settings node and then click Reports Settings.
Step 3 I n the left pane, in the Email Notification Settings area, enter the E-mail Server and From Address details.These details are used while sending reports from Prime Network Administration or Vision client.
Figure 7-2 E-mail Notification Settings

Changing GUI Client User Passwords

Note This feature is disabled if Prime Network is installed with Cisco Prime Central. If Prime Network is using an external LDAP server for authentication, do not use this procedure; instead, change the password in the LDAP server.
Users can change their own password when they are logged into any GUI client and they select Tools > Change User Password . The password will be changed across all Prime Network GUI clients: Vision, Events, Administration, Change and Configuration Management, and the BQL client.
Administrators can change user passwords by editing a user’s account settings; see Changing User Accounts and Device Scope Access.
To change the root password, see Changing System Passwords (Oracle Database, Graphs Tool, root, bos* Users).
Step 1 Select Users in the navigation pane.
Step 2 Right-click the users account, then choose Change Password .
Step 3 Enter the new password in the Password and Confirm Password fields.
Step 4 Click OK. A confirmation message is displayed.
Creating a New User Account and Viewing User Properties

Note These features are disabled if Prime Network is installed with Cisco Prime Central. If a user tries to log into Prime Network, they will be redirected to the suite login page. The only exception is the Prime Network emergency user, who will still be allowed to log into standalone Prime Network. If you migrate from standalone to working with Cisco Prime Central, you must create the Cisco Prime Central users using the Cisco Prime Portal portal, even if the users already existed in standalone mode. (Cisco Prime Central will advise you that the user already existed in Prime Network and will retrieve the user properties and apply them to the new Cisco Prime Central user.)
The following procedure describes how to define a user account.
Check the global security settings to see the current system defaults. You might also want to check the device scopes that are currently available.
Step 1 Right-click Users and choose New User to open the New User dialog box.
Step 2 Enter the general information about the user in the General Settings area. For existing users, click the General tab to display this information.
If checked, Prime Network will only let the user log in if the user’s password can be validated by an external LDAP server. The password fields are disabled. (If external authentication is being used, the box is checked by default. See Using an External LDAP Server for Password Authentication.) Click Test Connection to confirm the connection between the gateway and the LDAP server. |
|
Enter the new Prime Network password, which is then stored in the Prime Network Oracle database. Passwords must adhere to the global password rules set by the administrator (see Configuring Global User Password Settings). This field is disabled if you are using LDAP (external user) for authentication. Note You can set the password character length between 8-32. |
|
Note To use this feature, global Job Scheduling must be enabled (it is disabled by default). See Table 7-3.) Gives the user authority to schedule jobs across the product. If the global authorization mode is disabled, this setting is ignored. |
Step 3 Click Next and configure the GUI client and device authorization settings for the user. For existing users, click the Authorization tab to display these settings.
Select the role that will control the actions the user can perform in the Prime Network, such as which functions they can use in the GUI clients. Click Read More for a description of the roles; you can also get more information from User Authentication. For information on the special All Managed Elements scope, see What Are Device Scopes?. |
|
Select scopes and apply the security levels to them that will control the actions the user can perform on devices. You can apply different security levels for different scopes. If you do not apply a security level to a scope, it defaults to the Viewer level. Note Users will not see any devices in the GUI client unless a device scope is assigned to their account. Use the following buttons to manage scopes. Note that the edit and remove buttons only affect the scopes assigned to this user.
|
Step 4 Click Next and enter the account settings for the user. For existing users, click the Account tab to display these settings. (If you are creating a new account, you can also click Finish to accept the default account settings. The default settings are provided in the following.)
Enables and disables the user account. You can manually lock or unlock a user’s account at any time. A user whose account is locked cannot log into the system until you reenable their account. The user account is automatically locked if:
|
||
Check this check box to force the user to change their user password when they next log in. This field is disabled if the gateway server is using external LDAP authentication. |
||
Maximum number of Prime Network client sessions that a user can be running at any one time (to protect performance). This includes BQL sessions and workflow invocations. Leaving this field blank means the user can have unlimited connections. |
||
Forces the user to change their password after a specific number of days. Uncheck this check box to allow the user to retain their current password indefinitely. This field is disabled if the gateway server is using external LDAP authentication. |
Controlled by Global Settings; see Configuring Global User Password Settings. |
Step 5 Click Finish. and Prime Network creates the account. After the confirmation message is displayed, click Close to close the dialog box. The new account is displayed in the Users table.
Changing User Accounts and Device Scope Access

Note These features are disabled if Prime Network is installed with Cisco Prime Central.
Administrators can view, edit, or disable an individual user’s account settings. To change global settings such as password rules and inactivity periods, see Managing System Security.
Step 1 Select Users to populate the list of existing user accounts.
Step 2 Right-click a user account and choose Properties to open the user properties dialog box.
Step 3 Edit the following fields, as required (not all fields are editable).
The role that will control the actions the user can perform in the Prime Network, such as which functions they can use in the GUI clients. For information on how to make changes, see Configuring Global User Password Settings. |
|
Scopes and security levels that will control the actions the user can perform on devices. For information on how to make changes, see Configuring Global User Password Settings. |
|
Force the user to change their user password when they next log in. This field is disabled if the gateway server is using external LDAP authentication. |
|
The maximum number of Prime Network client sessions that the user can be running at any one time. This includes all client types. |
|
Forces the user to change their password after a specific number of days. Uncheck this check box to allow the user to retain their current password indefinitely. This field is disabled if the gateway server is using external LDAP authentication. |
|
Step 4 Click Apply to apply your changes, and click OK to close the Properties dialog box
Changing the Minimum User Access Role for the Events and Administration Clients

Note This feature is disabled if Prime Network is installed with Cisco Prime Central.
By default, only users with Administrator privileges can log into the Administration and Events clients. You can adjust Prime Network to allow users with lower privileges to log into these clients.
When you change the required role to a lower role, the higher roles inherit the access. For example, if you change the required security level to Operator, then users with Operator, OperatorPlus, Configuration, and Administrator privileges will be permitted to log into the Events GUI client.

Note This procedure requires a gateway restart.
Change the Minimum Role for the Events Client
Step 1 Choose Tools > Registry Controller > User Accounts from the main menu of the Administration GUI client.
Step 2 In the User Access Role for Events GUI Client drop-down list, select a role and click Apply .
Step 3 Restart the gateway for your changes to take effect. See Stopping and Restarting Prime Network Components.
Change the Minimum Role for the Administration Client
To change the minimum user access role for the Administration client, you must use the registry editor CLI. This example shows how to change the minimum role to Configurator.
If you want this user to have the same privileges as the default Administrator role, you must also grant the user access to the AllManaged Elements device scope (when you create the user’s account).
Step 1 Log into the gateway server as pnuser .
Step 2 Run the following commands to change the minimum access role from Administrator to Configurator:
#
./runRegTool.sh -gs 127.0.0.1 add 0.0.0.0 site/plugin/BOSPlugin/commands/com.sheer.metromission.plugin.bos.commands.UpdateDevicePackageName
#
./runRegTool.sh -gs 127.0.0.1 add 0.0.0.0 site/plugin/BosManagePlugin/commands/com.sheer.metromission.plugin.bosmanage.oldcommands.GetSuiteUseStatus
#
./runRegTool.sh -gs 127.0.0.1 set 127.0.0.1 avm11/services/plugin/ClientPlugin/isConfiguratorEnabledForAnaManage true
#
./runRegTool.sh -gs 127.0.0.1 set 0.0.0.0 site/plugin/ClientPlugin/eventVisionRole configurator
#
./runRegTool.sh -gs 127.0.0.1 set 0.0.0.0 site/plugin/BosManagePlugin/commands/com.sheer.metromission.plugin.bosmanage.commands.UpdateBosManage/default plugin/default_roles/configurator
#
./runRegTool.sh -gs 127.0.0.1 set 0.0.0.0 site/plugin/BosManagePlugin/commands/com.sheer.metromission.plugin.bosmanage.oldcommands.CreateDevice/default plugin/default_roles/configurator
#
./runRegTool.sh -gs 127.0.0.1 set 0.0.0.0 site/plugin/BosManagePlugin/commands/com.sheer.metromission.plugin.bosmanage.oldcommands.DeleteDevice/default plugin/default_roles/configurator
#
./runRegTool.sh -gs 127.0.0.1 set 0.0.0.0 site/plugin/BosManagePlugin/commands/com.sheer.metromission.plugin.bosmanage.oldcommands.CreateAvm/default plugin/default_roles/configurator
#
./runRegTool.sh -gs 127.0.0.1 set 0.0.0.0 site/plugin/BosManagePlugin/commands/com.sheer.metromission.plugin.bosmanage.oldcommands.DeleteAvm/default plugin/default_roles/configurator
#
./runRegTool.sh -gs 127.0.0.1 set 0.0.0.0 site/plugin/BosManagePlugin/commands/com.sheer.metromission.plugin.bosmanage.oldcommands.UnloadAvm/default plugin/default_roles/configurator
#
./runRegTool.sh -gs 127.0.0.1 set 0.0.0.0 site/plugin/BosManagePlugin/commands/com.sheer.metromission.plugin.bosmanage.oldcommands.CreateMC/default plugin/default_roles/configurator
#
./runRegTool.sh -gs 127.0.0.1 set 0.0.0.0 site/plugin/BosManagePlugin/commands/com.sheer.metromission.plugin.bosmanage.oldcommands.DeleteMC/default plugin/default_roles/configurator
#
./runRegTool.sh -gs 127.0.0.1 set 0.0.0.0 site/plugin/BosManagePlugin/commands/com.sheer.metromission.plugin.bosmanage.oldcommands.GetSuiteUseStatus/default plugin/default_roles/configurator
#
./runRegTool.sh -gs 127.0.0.1 set 0.0.0.0 site/plugin/BOSPlugin/commands/com.sheer.metromission.plugin.bos.commands.UpdateDevicePackageName/default plugin/default_roles/configurator
Step 3 Restart the gateway for your changes to take effect. See Stopping and Restarting Prime Network Components.
Configuring External User Authentication (LDAP)
- Using an External LDAP Server for Password Authentication
- Changing from External to Local Authentication

Note These features are disabled if Prime Network is installed with Cisco Prime Central. If a user tries to log into Prime Network, they will be redirected to the suite login page. The only exception is the Prime Network emergency user, who will still be allowed to log into standalone Prime Network.
User authentication is managed either locally by Prime Network, or externally by an LDAP application. Either method can be used to validate user accounts and passwords, thus controlling who can log into Prime Network. If you use Prime Network, user information and passwords are stored in the Prime Network Oracle database. If you use an external LDAP application, passwords are stored on the external LDAP server. (User authorization information (roles and scopes) is always stored in the Prime Network Oracle database. The external LDAP server, if used, only stores passwords.) The external authentication method has a special user called the emergency user . In Prime Network, root is designated as the external authentication emergency user. This means if Prime Network loses communication with the LDAP server, Prime Network will allow root (and only root) to log in. The root user can then change the authentication method to local, and edit user accounts so that those users can subsequently log in. Prime Network uses LDAP version 3.
User authorization is managed through a combination of user access roles and scopes. For detailed information on these topics, see User Authentication, and What Are Device Scopes?.
Using an External LDAP Server for Password Authentication

Note These features are disabled if Prime Network is installed with Cisco Prime Central.
The following topics describe how you can use an external LDAP server to perform user authentication. By default, Prime Network uses internal authentication, which means passwords are stored in and verified against the data that is stored in the Prime Network Oracle database. If you want to use external authentication, these topics will guide you through the process.
How Does External Authentication Work?

Note These features are disabled if Prime Network is installed with Cisco Prime Central.
User authentication can be managed locally by Prime Network or externally by a Lightweight Directory Access Protocol (LDAP) application. If you use an external authentication, user information is checked against what is stored in the external LDAP server (instead of the Prime Network Oracle database). The external authentication server only stores login and password information; information pertaining to user roles and scopes is stored in the Prime Network Oracle database.
As illustrated in Figure 7-3, when a user logs in to the GUI client, the gateway server contacts the LDAP server to authenticate the user. If the user is successfully authenticated, the LDAP server sends a confirmation to the gateway server, and the gateway server allows the user to log into Prime Network. From that point on, the user can perform functions and access network elements as specified by their roles and scopes (see Changing a User’s Device Scope Security Level).
Figure 7-3 User Authentication Process with External LDAP Server

The root user is the emergency user. The LDAP emergency user is validated only by Prime Network. Consequently, if the LDAP server goes down, root can log back into Prime Network.

Note If Prime Network is installed with Cisco Prime Central, the emergency user will still be allowed to log into Prime Network.
Prerequisites for Using LDAP

Note These features are disabled if Prime Network is installed with Cisco Prime Central.
You must meet the following prerequisites before you can configure Prime Network to use LDAP:
- The LDAP server must be reachable from the Prime Network server, including port 389 for nonencrypted communication, 636 for encrypted communication.
- The LDAP server must support LDAPv3 protocol.
- Windows Server 2003 Active Directory must be configured. Configuring a Secure Connection with the Windows Server 2003 Active Directory
- For encrypted communication, a certificate must be installed on the Prime Network server. See Installing the LDAP Certificate on the Prime Network Gateway Server.
Configuring a Secure Connection with the Windows Server 2003 Active Directory
To manage users in the Active Directory from Java, the connection to the server must be secure. Follow these procedures to make the server connection secure.
If you are using Secure Socket Layer (SSL) for encryption between the Prime Network server and the LDAP server, the Windows server must be a domain controller installed with an Enterprise Certificate Authority. To guarantee a secure connection, you must request and install the appropriate certificate.

Note This procedure requires a gateway restart.
To obtain the certificate from the LDAP server and place it on the gateway:
Step 1 Use Router Discovery Protocol (RDP) to log into the remote LDAP server.
Step 2 Choose Start > Programs > Administrative Tools > Domain Controller Security Policy .
Step 3 In the left pane, choose Security Settings > Public Key Policies > Automatic Certificate Request Settings .
Step 4 Right-click the right pane and choose New > Automatic Certificate Request .
Step 6 Choose Domain Controller and click Next .
Step 9 After the server restarts, enter the following command on the command line:
The SSL port 636 should be active; for example:
TCP 0.0.0.0:636 0.0.0.0:0 LISTENING
Installing the LDAP Certificate on the Prime Network Gateway Server
Prime Network requires a certificate to open a context with the LDAP server. To import the certificate into the system .truststore file, complete the following steps:
Step 1 Download the certificate from the relevant LDAP workstation:
a. From the client workstation, go to http:// ldaphost /certsrv, where ldaphost is the fully qualified domain name or IP address of the LDAP server.
b. For blade LDAP, enter the service provider username and password.
c. Click Download a CA certificate, certificate chain, or CRL .
d. Choose Previous cmpdc in the CA certificate option.
e. Click Download CA certificate .
f. Save the certnew.cer file on the workstation. You can rename the file as CA. LDAP-IP-address .cer.
Step 2 Log into your workstation.
Step 3 Go to ~/Main/resourcebundle/com/sheer and copy the .cer file to that directory.
Step 4 Enter the following command on the command line:
# keytool -import -alias LDAPID -file CA.LDAP-IP-address.cer -keystore .truststore

Note Use the password in the security.properties file in this directory. Be sure to use a unique ID to set a unique alias.
Step 5 Enter the following command to check your LDAP certificates on the system .truststore file:
#
keytool -list -keystore .truststore
Step 6 Restart the prime network gateway:
Configuring Prime Network to Communicate with the External LDAP Server

Note These features are disabled if Prime Network is installed with Cisco Prime Central.
Use this procedure to configure the Prime Network gateway server to communicate with the LDAP server, and to test the connection after it is configured. You can configure a primary and secondary LDAP server. This procedure uses LDAP terminology, such as distinguished name (DN), common name (CN), and domain component (DC). An LDAP distinguished name uniquely identifies a user in the LDAP database, similar to a full filename but in reverse order. CNs and DCs are attributes of the domain name.
Make sure you have performed the required prerequisites that are described in the Cisco Prime Network 4.3.2 Installation Guide :
- The LDAP server is correctly configured.
- You know the port number needed for the SSL or simple encryption protocol. These are normally 636 for SSL and 389 for simple.
- If you select SSL for the Application-LDAP Protocol, the SSL certificate must be installed on the Prime Network gateway.
You must have Administrator privileges (user access role) to use this and all other functions in Prime Network Administration.

Note This procedure requires a gateway restart.
To configure the Prime Network gateway server to communicate with the LDAP server:
Step 1 Choose Global Settings > Security > Authentication Method . Figure 7-4 provides an example of the Authentication Method window.
Figure 7-4 Authentication Method Window

Step 2 Click LDAP Authentication to activate the LDAP Settings area.
Step 3 Complete the LDAP settings. The settings include specifying LDAP schema attributes, such as CN (common name) and DC (domain component).
LDAP server name and port number, in the following format: ldap:// host.company .com: port
To specify a primary and secondary LDAP server, use the following format: ldap:// host1.company .com: port1 ldap:// host2.company .com: port2 |
|
From the drop-down list box, choose Within Group or Subgroup . |
|
First part of the LDAP DN, which is used to uniquely identify users. Enter the information exactly as shown: (The actual format is CN= Value , which specifies the common name for specific users. = Value will be automatically populated with Prime Network usernames.) |
|
Second part of the LDAP distinguished name, which specifies the location in the directory: |
|
Encryption protocol used for communication between the Prime Network gateway server and the LDAP server. Note The encryption protocol used must be configured on both the Prime Network gateway server and the LDAP server.
|
Step 4 Click Test Connection to test the connection between the gateway server and the LDAP server.
Step 6 Restart the gateway for your changes to take effect. See Stopping and Restarting Prime Network Components.
You can now manage user passwords using the external LDAP server.
Importing Users from the LDAP Server to Prime Network

Note These features are disabled if Prime Network is installed with Cisco Prime Central.
To import users from an LDAP server into Prime Network, you must first create and LDAP Data Interchange Format (LDIF) file using the ldifde command, and then import the file into Prime Network using the import_users_from_LDIF_file.pl command.
This command produces an LDIF file for a Windows LDAP server:
#
ldifde -l description,displayName,userPrincipalName,email -f desired-filename -r objectClass=user
The following shows sample contents of an LDIF file named users.LDF:
dn: CN=
xxx
,CN=Users,DC=ldapsj,DC=com
description
changetype: add
description:
displayName:
xxx
email:
xxx@mail.com
userPrincipalName: xxx@acme.com
yyyy
dn: CN=
,CN=Users,DC=ldapsj,DC=com
description
changetype: add
description:
displayName:
yyy
email:
yyy@mail.com
userPrincipalName:
yyy
@acme.com
description
dn: CN=zzz,CN=Users,DC=ldapsj,DC=com
changetype: add
description:
displayName:
zzz
email:
zzz@mail.com
userPrincipalName:
zzz
@acme.com
The import_users_from_LDIF_file.pl command has the following syntax:
import_users_from_LDIF_file.pl ldif-filename [ roleName ] username-attribute-name [ user-desc-attribute-name ] [ full-name-attribute-name ] [ user-email-attribute-name ]
The following command imports the LDAP users listed in the users.LDF file into Prime Network. It creates three users with a Viewer role. It is executed from the NETWORKHOME /Main/scripts directory.
#
import_users_from_LDIF_file.pl users.LDF userPrincipalName description displayName email

Note All imported users are created with non-Prime Network authentication permissions (LDAP authentication). If the username already exists in Prime Network, the new user is not created.
Changing from External to Local Authentication

Note The Authentication Method feature is disabled if Prime Network is installed with Cisco Prime Central. However, the emergency user will still be allowed to log into Prime Network.
If Prime Network is using external authentication and cannot communicate with the LDAP server, the only user permitted to log back into Prime Network is root. This is because root is the emergency user, and is validated only by Prime Network. The root user can then log into Prime Network, change the authentication method to local, and edit user accounts so that those users can subsequently log in. For information on editing user accounts, see Changing User Accounts and Device Scope Access.
You must have Administrator privileges (user access role) to use this and all other functions in Prime Network Administration.

Note This procedure requires a gateway restart.
To change from external to local authentication, follow this procedure:
Step 1 Choose Global Settings > Security > Authentication Method .
Step 2 Click Prime Network Authentication to activate local authentication.
Step 4 Restart the gateway for your changes to take effect. See Stopping and Restarting Prime Network Components.
Step 5 Reconfigure user accounts accordingly (see Changing User Accounts and Device Scope Access).
Controlling Which Maps Users Can Access

Note These features are disabled if Prime Network is installed with Cisco Prime Central.
By default, users can access any Vision GUI client maps that have been created by other users. You can control this by enabling the map assignment mechanism.

Note This procedure requires a gateway restart.
Step 1 Enable the map assignment mechanism.
a. Choose Tools > Registry Controller > User Accounts from the main menu of the Administration GUI client.
b. In the User Access to Existing Maps setting, select True from the drop-down list and click Apply .
c. Restart the gateway for your changes to take effect. See Stopping and Restarting Prime Network Components.
Step 2 Specify which maps users can access:
a. In the Users tree in the Administration GUI client, right-click a user and choose Properties.
b. Click the Maps tab. The Maps tab lists all maps saved in the Oracle database. Those that are not assigned to the user are listed on the left.
c. To assign maps to the user account, move them from the left side to the right side, and click OK .
Re-enabling User Accounts

Note This feature is disabled if Prime Network is installed with Cisco Prime Central.
User accounts can become locked or disabled for two reasons:
- A user entered the wrong password, exceeding the number of permitted retries. The retries setting is controlled from the Password Settings window.
- The user has not logged in, exceeding the account inactivity period.
The settings that control these actions are specified in the Global Settings; see Configuring Global User Permissions: Account Inactivity, Device Credential Requirements, and Global Job Scheduling.
Step 1 Select Users to populate the list of existing user accounts.
Step 2 Right-click a user account and choose Properties to open the user properties dialog box.
Step 3 In the Account tab, check the Enable Account check box.
Deleting a Prime Network User Account

Note This feature is disabled if Prime Network is installed with Cisco Prime Central.
If you want to disable a user account but not delete it, see Changing User Accounts and Device Scope Access.
Step 1 Select Users in the navigation pane.
Step 2 Right-click the account you want to remove, then choose Delete .
The account is deleted and is removed from the content area.
Tracking User-Related Events
The following table provides ways you can get historical information on user-related events. You can tailor your search or reports by specifying keywords (such as user ).
 Feedback
Feedback