- BGP Features Roadmap
- Cisco BGP Overview
- Configuring a Basic BGP Network
- Connecting to a Service Provider Using External BGP
- Removing Private AS Numbers from the AS Path in BGP
- Configuring BGP Neighbor Session Options
- Configuring Internal BGP Features
- Configuring Advanced BGP Features
- Configuring Multiprotocol BGP (MP-BGP) Support for CLNS
- BGP Link Bandwidth
- iBGP Multipath Load Sharing
- BGP Multipath Load Sharing for Both eBGP and iBGP in an MPLS-VPN
- Loadsharing IP Packets Over More Than Six Parallel Paths
- BGP Policy Accounting
- BGP Cost Community
- BGP Support for IP Prefix Import from Global Table into a VRF Table
- BGP per Neighbor SoO Configuration
- BGP Next Hop Unchanged
- Per-VRF Assignment of BGP Router ID
- BGP Support for the L2VPN Address Family
- BGP 4 MIB Support for per-Peer Received Routes
- Detecting and Mitigating a BGP Slow Peer
- BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
- BGP: RT Constrained Route Distribution
IP Routing: BGP Configuration Guide, Cisco IOS Release 15.1S
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- July 26, 2010
Chapter: BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
- Finding Feature Information
- Contents
- Prerequisites for BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
- Information About BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
- How to Configure BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
The BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO) feature enables provider edge (PE) routers to maintain Border Gateway Protocol (BGP) state with customer edge (CE) routers and ensure continuous packet forwarding during a Route Processor (RP) switchover or during a planned In-Service Software Upgrade (ISSU) for a PE router. CE routers do not need to be Nonstop Forwarding (NSF)-capable or NSF-aware to benefit from BGP NSR capabilities on PE routers. Only PE routers need to be upgraded to support BGP NSR—no CE router upgrades are required. BGP NSR with SSO, thus, enables service providers to provide the benefits NSF with the additional benefits of NSR without requiring CE routers to be upgraded to support BGP graceful restart.
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the "Feature Information for BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)" section.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Contents
•![]() Prerequisites for BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
Prerequisites for BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
•![]() Information About BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
Information About BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
•![]() How to Configure BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
How to Configure BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
•![]() Configuration Examples for BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
Configuration Examples for BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
•![]() Feature Information for BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
Feature Information for BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
Prerequisites for BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
•![]() This document assumes that your network is configured to run BGP.
This document assumes that your network is configured to run BGP.
•![]() This document assumes that Multiprotocol Layer Switching (MPLS) Layer 3 Virtual Private Networks (VPNs) are configured.
This document assumes that Multiprotocol Layer Switching (MPLS) Layer 3 Virtual Private Networks (VPNs) are configured.
•![]() This document assumes that you are familiar NSF and SSO concepts and tasks.
This document assumes that you are familiar NSF and SSO concepts and tasks.
Information About BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
Overview of BGP NSR with SSO
Prior to the introduction of BGP NSR with SS0 in Cisco IOS Release 12.2(28)SB, BGP required that all neighboring devices participating in BGP NSF be configured to be either NSF-capable or NSF-aware (by configuring the devices to support the BGP graceful restart mechanism). BGP NSF, thus, required that all neighboring devices be upgraded to a version of Cisco IOS software that supports BGP graceful restart. However, in many MPLS VPN deployments, there are situations where PE routers engage in exterior BGP (eBGP) peering sessions with CE routers that do not support BGP graceful restart and cannot be upgraded to a software version that supports BGP graceful restart in the same time frame as the provider (P) routers.
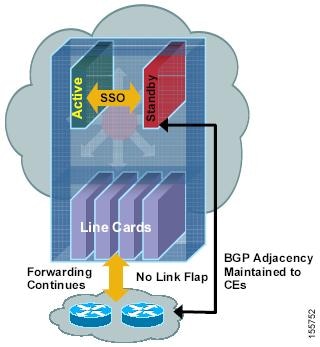
BGP NSR with SSO provides a high availability (HA) solution to service providers whose PE routers engage in eBGP peering relationships with CE routers that do not support BGP graceful restart. BGP NSR works with SSO to synchronize BGP state information between the active and standby RP. SSO minimizes the amount of time a network is unavailable to its users following a switchover. When the BGP NSR with SSO feature is configured, in the event of an RP switchover, the PE router uses BGP NSR with SSO to maintain BGP state for eBGP peering sessions with CEs that are not NSF-aware (see Figure 1).
Additionally, the BGP NSR with SSO feature dynamically detects NSF-aware peers and runs graceful restart with those CE routers. For eBGP peering sessions with NSF-aware peers and for internal BGP (iBGP) sessions with BGP Route Reflectors (RRs) in the service provider core, the PE uses NSF to maintain BGP state. BGP NSR with SSO, thus, enables service providers to provide the benefits of NSF with the additional benefits of NSR without requiring CE routers to be upgraded to support BGP graceful restart.
Figure 1 BGP NSR with SSO Operations During an RP Switchover
BGP NSR with SSO is supported in BGP peer, BGP peer group, and BGP session template configurations. To configure support for BGP NSR with SSO in BGP peer and BGP peer group configurations, use the neighbor ha-mode sso command in address family configuration mode for IPv4 VRF address family BGP peer sessions. To include support for Cisco BGP NSR with SSO in a peer session template, use the ha-mode sso command in session-template configuration mode.
Benefits of BGP NSR with SSO
•![]() Minimizes services disruptions—BGP NSR with SSO reduces impact on customer traffic during RP switchovers (scheduled or unscheduled events), extending HA deployments and benefits at the edge.
Minimizes services disruptions—BGP NSR with SSO reduces impact on customer traffic during RP switchovers (scheduled or unscheduled events), extending HA deployments and benefits at the edge.
•![]() Enhances high-availability NSF and SSO deployment at the edge—BGP NSR with SSO allows incremental deployment by upgrading the provider edge with the NSR capability so that customer-facing edge routers are synchronized automatically and no coordination or NSF awareness is needed with the customer side Cisco or third-party customer edge routers. The BGP NSR feature dynamically detects NSF-aware peers and runs graceful restart with those CE routers.
Enhances high-availability NSF and SSO deployment at the edge—BGP NSR with SSO allows incremental deployment by upgrading the provider edge with the NSR capability so that customer-facing edge routers are synchronized automatically and no coordination or NSF awareness is needed with the customer side Cisco or third-party customer edge routers. The BGP NSR feature dynamically detects NSF-aware peers and runs graceful restart with those CE routers.
•![]() Provides transparent route convergence—BGP NSR with SSO eliminates route flaps by keeping BGP state on both active and standby RPs and ensures continuous packet forwarding with minimal packet loss during RP failovers.
Provides transparent route convergence—BGP NSR with SSO eliminates route flaps by keeping BGP state on both active and standby RPs and ensures continuous packet forwarding with minimal packet loss during RP failovers.
How to Configure BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
•![]() Configuring a PE Router to Support BGP NSR with SSO (required)
Configuring a PE Router to Support BGP NSR with SSO (required)
•![]() Verifying BGP Support for NSR with SSO (optional)
Verifying BGP Support for NSR with SSO (optional)
Configuring a PE Router to Support BGP NSR with SSO
Perform this task to enable a PE router to maintain BGP state with CE routers and ensure continuous packet forwarding during a RP switchover or during a planned ISSU. BGP NSR with SSO enables service providers to provide the benefits NSF with the additional benefits of NSR without requiring CE routers to be upgraded to support BGP graceful restart.
BGP NSR with SSO is supported in BGP peer, BGP peer group, and BGP session template configurations. Perform one of the following tasks in this section on a PE router, depending on whether you want to configure support for BGP NSR with SSO in a peer, a peer group, or a session template configuration:
•![]() Configuring a Peer to Support BGP NSR with SSO
Configuring a Peer to Support BGP NSR with SSO
•![]() Configuring a Peer Group to Support BGP NSR with SSO
Configuring a Peer Group to Support BGP NSR with SSO
•![]() Configuring Support for BGP NSR with SSO in a Peer Session Template
Configuring Support for BGP NSR with SSO in a Peer Session Template
Prerequisites
•![]() These tasks assume that you are familiar with BGP peer, BGP peer group, and BGP session template concepts. For more information, see the "Configuring a Basic BGP Network" module.
These tasks assume that you are familiar with BGP peer, BGP peer group, and BGP session template concepts. For more information, see the "Configuring a Basic BGP Network" module.
•![]() The active and standby RP must be in SSO mode. For information about configuring SSO mode, see the "Configuring SSO" task in the Stateful Switchover document.
The active and standby RP must be in SSO mode. For information about configuring SSO mode, see the "Configuring SSO" task in the Stateful Switchover document.
•![]() Graceful restart should be enabled on the PE router. We recommend that you enable graceful restart on all BGP peers in the provider core that participate in BGP NSF. For more information about configuring graceful restart, see the "Configuring Advanced BGP Features" module.
Graceful restart should be enabled on the PE router. We recommend that you enable graceful restart on all BGP peers in the provider core that participate in BGP NSF. For more information about configuring graceful restart, see the "Configuring Advanced BGP Features" module.
•![]() CE routers must support the route refresh capability. For more information, refer to the "Configuring a Basic BGP Network" module in the Cisco IOS IP Routing: BGP Configuration Guide.
CE routers must support the route refresh capability. For more information, refer to the "Configuring a Basic BGP Network" module in the Cisco IOS IP Routing: BGP Configuration Guide.
Configuring a Peer to Support BGP NSR with SSO
Perform this task on a PE router if you want to configure a BGP peer to support BGP NSR with SSO.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() router bgp autonomous-system-number
router bgp autonomous-system-number
4. ![]() bgp graceful-restart [restart-time seconds] [stalepath-time seconds]
bgp graceful-restart [restart-time seconds] [stalepath-time seconds]
5. ![]() address-family ipv4 vrf vrf-name
address-family ipv4 vrf vrf-name
6. ![]() neighbor ip-address remote-as autonomous-system-number
neighbor ip-address remote-as autonomous-system-number
7. ![]() neighbor ip-address ha-mode sso
neighbor ip-address ha-mode sso
8. ![]() neighbor ip-address activate
neighbor ip-address activate
9. ![]() end
end
10. ![]() show ip bgp vpnv4 all sso summary
show ip bgp vpnv4 all sso summary
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
enable Router> enable |
Enables privileged EXEC mode. • |
Step 2 |
configure terminal Router# configure terminal |
Enters global configuration mode. |
Step 3 |
router bgp autonomous-system-number Router(config)# router bgp 40000 |
Enters router configuration mode for the specified routing process. |
Step 4 |
bgp graceful-restart [restart-time seconds] [stalepath-time seconds] Router(config-router)# bgp graceful-restart |
Enables the BGP graceful restart capability and BGP NSF awareness. • • |
Step 5 |
address-family ipv4 vrf vrf-name Router(config-router)# address-family ipv4 vrf test |
Enters address family configuration mode for IPv4 VRF address family sessions. • Note |
Step 6 |
neighbor ip-address remote-as autonomous-system-number Router(config-router-af)# neighbor 192.168.1.1 remote-as 45000 |
Adds the IP address of the neighbor in the specified autonomous system to the IPv4 multiprotocol BGP neighbor table of the local router. |
Step 7 |
neighbor ip-address ha-mode sso Router(config-router-af)# neighbor 192.168.1.1 ha-mode sso |
Configures the neighbor to support BGP NSR with SSO. |
Step 8 |
neighbor ip-address activate Router(config-router-af)# neighbor testgroup activate |
Enables the neighbor to exchange prefixes for the IPv4 address family with the local router. Note |
Step 9 |
end Router(config-router-af)# end |
Exits address family configuration mode and enters privileged EXEC mode. |
Step 10 |
show ip bgp vpnv4 all sso summary Router# show ip bgp vpnv4 all sso summary |
(Optional) Displays the number of BGP neighbors that are in SSO mode. |
Configuring a Peer Group to Support BGP NSR with SSO
Perform this task on a PE router if you want to configure a BGP peer group to support BGP NSR with SSO.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() router bgp autonomous-system-number
router bgp autonomous-system-number
4. ![]() bgp graceful-restart [restart-time seconds] [stalepath-time seconds]
bgp graceful-restart [restart-time seconds] [stalepath-time seconds]
5. ![]() address-family ipv4 vrf vrf-name
address-family ipv4 vrf vrf-name
6. ![]() neighbor peer-group-name peer-group
neighbor peer-group-name peer-group
7. ![]() neighbor ip-address remote-as autonomous-system-number
neighbor ip-address remote-as autonomous-system-number
8. ![]() neighbor ip-address peer-group peer-group-name
neighbor ip-address peer-group peer-group-name
9. ![]() neighbor peer-group-name ha-mode sso
neighbor peer-group-name ha-mode sso
10. ![]() neighbor peer-group-name activate
neighbor peer-group-name activate
11. ![]() end
end
12. ![]() show ip bgp vpnv4 all sso summary
show ip bgp vpnv4 all sso summary
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
enable Router> enable |
Enables privileged EXEC mode. • |
Step 2 |
configure terminal Router# configure terminal |
Enters global configuration mode. |
Step 3 |
router bgp autonomous-system-number Router(config)# router bgp 40000 |
Enters router configuration mode for the specified routing process. |
Step 4 |
bgp graceful-restart [restart-time seconds] [stalepath-time seconds] Router(config-router)# bgp graceful-restart |
Enables the BGP graceful restart capability and BGP NSF awareness. • • |
Step 5 |
address-family ipv4 vrf vrf-name Router(config-router)# address-family ipv4 vrf cisco |
Specifies the IPv4 address family and enters address family configuration mode. • Note |
Step 6 |
neighbor peer-group-name peer-group Router(config-router-af)# neighbor testgroup peer-group |
Creates a BGP peer group. |
Step 7 |
neighbor ip-address remote-as autonomous-system-number Router(config-router-af)# neighbor 192.168.1.1 remote-as 45000 |
Adds the IP address of the neighbor in the specified autonomous system to the IPv4 multiprotocol BGP neighbor table of the local router. |
Step 8 |
neighbor ip-address peer-group peer-group-name Router(config-router-af)# neighbor 192.168.1.1 peer-group testgroup |
Assigns the IP address of a BGP neighbor to a BGP peer group. |
Step 9 |
neighbor peer-group-name ha-mode sso Router(config-router-af)# neighbor 192.168.1.1 ha-mode sso |
Configures the BGP peer group to support BGP NSR with SSO. |
Step 10 |
neighbor peer-group-name activate Router(config-router-af)# neighbor testgroup activate |
Enables the neighbor to exchange prefixes for the IPv4 address family with the local router. |
Step 11 |
end Router(config-router-af)# end |
Exits address family configuration mode and returns to global configuration mode. |
Step 12 |
show ip bgp vpnv4 all sso summary Router# show ip bgp vpnv4 all sso summary |
(Optional) Displays the number of BGP neighbors that are in SSO mode. |
Configuring Support for BGP NSR with SSO in a Peer Session Template
Perform this task on a PE router if you want to configure support for BGP NSR with SSO in a BGP peer session template.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() router bgp autonomous-system-number
router bgp autonomous-system-number
4. ![]() template peer-session session-template-name
template peer-session session-template-name
5. ![]() ha-mode sso
ha-mode sso
6. ![]() exit-peer-session
exit-peer-session
7. ![]() end
end
8. ![]() show ip bgp template peer-session [session-template-name]
show ip bgp template peer-session [session-template-name]
DETAILED STEPS
What to Do Next
After the peer session template is created, the configuration of the peer session template can be inherited by or applied to another peer session template with the inherit peer-session or neighbor inherit peer-session command.
For more information about configuring peer session templates, see the "Configuring a Basic BGP Network" chapter in the Cisco IOS IP Routing: BGP Configuration Guide.
Verifying BGP Support for NSR with SSO
Perform this optional task to verify BGP NSR with SSO support.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show ip bgp vpnv4 all sso summary
show ip bgp vpnv4 all sso summary
3. ![]() show ip bgp vpnv4 all neighbors
show ip bgp vpnv4 all neighbors
DETAILED STEPS
Step 1 ![]() enable
enable
Enables privileged EXEC mode. Enter your password if prompted.
Router> enable
Step 2 ![]() show ip bgp vpnv4 all sso summary
show ip bgp vpnv4 all sso summary
This command is used to display the number of BGP neighbors that are in SSO mode.
The following is sample output from the show ip bgp vpnv4 all sso summary command:
Router# show ip bgp vpnv4 all sso summary
Stateful switchover support enabled for 40 neighbors
Step 3 ![]() show ip bgp vpnv4 all neighbors
show ip bgp vpnv4 all neighbors
This command displays VPN address information from the BGP table.
The following is sample output from the show ip bgp vpnv4 all neighbors command. The "Stateful switchover support" field indicates whether SSO is enabled or disabled. The "SSO Last Disable Reason" field displays information about the last BGP session that lost SSO capability.
Router# show ip bgp vpnv4 all neighbors 10.3.3.3
BGP neighbor is 10.3.3.3, vrf vrf1, remote AS 3, external link
Inherits from template 10vrf-session for session parameters
BGP version 4, remote router ID 10.1.105.12
BGP state = Established, up for 04:21:39
Last read 00:00:05, last write 00:00:09, hold time is 30, keepalive interval is 10 seconds
Configured hold time is 30, keepalive interval is 10 seconds
Minimum holdtime from neighbor is 0 seconds
Neighbor capabilities:
Route refresh: advertised and received(new)
Address family IPv4 Unicast: advertised and received
Stateful switchover support enabled
Message statistics:
InQ depth is 0
OutQ depth is 0
Sent Rcvd
Opens: 1 1
Notifications: 0 0
Updates: 1 4
Keepalives: 1534 1532
Route Refresh: 0 0
Total: 1536 1537
Default minimum time between advertisement runs is 30 seconds
For address family: VPNv4 Unicast
Translates address family IPv4 Unicast for VRF vrf1
BGP table version 25161, neighbor version 25161/0
Output queue size : 0
Index 7, Offset 0, Mask 0x80
7 update-group member
Inherits from template 10vrf-policy
Overrides the neighbor AS with my AS before sending updates
Outbound path policy configured
Route map for outgoing advertisements is Deny-CE-prefixes
Sent Rcvd
Prefix activity: ---- ----
Prefixes Current: 10 50 (Consumes 3400 bytes)
Prefixes Total: 10 50
Implicit Withdraw: 0 0
Explicit Withdraw: 0 0
Used as bestpath: n/a 0
Used as multipath: n/a 0
Outbound Inbound
Local Policy Denied Prefixes: -------- -------
route-map: 150 0
AS_PATH loop: n/a 760
Total: 150 760
Number of NLRIs in the update sent: max 10, min 10
Address tracking is enabled, the RIB does have a route to 10.3.3.3
Address tracking requires at least a /24 route to the peer
Connections established 1; dropped 0
Last reset never
Transport(tcp) path-mtu-discovery is enabled
TCP session must be opened passively
Connection state is ESTAB, I/O status: 1, unread input bytes: 0 Connection is ECN Disabled Local host: 10.0.21.1, Local port: 179 Foreign host: 10.0.21.3, Foreign port: 51205 Connection tableid (VRF): 1
Enqueued packets for retransmit: 0, input: 0 mis-ordered: 0 (0 bytes)
Event Timers (current time is 0x1625488):
Timer Starts Wakeups Next
Retrans 1746 210 0x0
TimeWait 0 0 0x0
AckHold 1535 1525 0x0
SendWnd 0 0 0x0
KeepAlive 0 0 0x0
GiveUp 0 0 0x0
PmtuAger 0 0 0x0
DeadWait 0 0 0x0
Linger 0 0 0x0
iss: 2241977291 snduna: 2242006573 sndnxt: 2242006573 sndwnd: 13097
irs: 821359845 rcvnxt: 821391670 rcvwnd: 14883 delrcvwnd: 1501
SRTT: 300 ms, RTTO: 303 ms, RTV: 3 ms, KRTT: 0 ms
minRTT: 0 ms, maxRTT: 300 ms, ACK hold: 200 ms Status Flags: passive open, retransmission timeout, gen tcbs
0x1000
Option Flags: VRF id set, always push, md5
Datagrams (max data segment is 4330 bytes):
Rcvd: 3165 (out of order: 0), with data: 1535, total data bytes: 31824
Sent: 3162 (retransmit: 210 fastretransmit: 0),with data: 1537, total data
bytes: 29300
SSO Last Disable Reason: Application Disable (Active)
Troubleshooting Tips
To troubleshoot BGP NSR with SSO, use the following commands in privileged EXEC mode, as needed:
•![]() debug ip bgp sso—Displays BGP-related SSO events or debugging information for BGP-related interactions between the active RP and the standby RP. This command is useful for monitoring or troubleshooting BGP sessions on a PE router during an RP switchover or during a planned ISSU.
debug ip bgp sso—Displays BGP-related SSO events or debugging information for BGP-related interactions between the active RP and the standby RP. This command is useful for monitoring or troubleshooting BGP sessions on a PE router during an RP switchover or during a planned ISSU.
•![]() debug ip tcp ha—Displays TCP HA events or debugging information for TCP stack interactions between the active RP and the standby RP. This is command is useful for troubleshooting SSO-aware TCP connections.
debug ip tcp ha—Displays TCP HA events or debugging information for TCP stack interactions between the active RP and the standby RP. This is command is useful for troubleshooting SSO-aware TCP connections.
•![]() show tcp—Displays the status of TCP connections. The display output will display the SSO capability flag and will indicate the reason that the SSO property failed on a TCP connection.
show tcp—Displays the status of TCP connections. The display output will display the SSO capability flag and will indicate the reason that the SSO property failed on a TCP connection.
•![]() show tcp ha connections—Displays connection-ID-to-TCP mapping data.
show tcp ha connections—Displays connection-ID-to-TCP mapping data.
Configuration Examples for BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
•![]() Configuring BGP NSR with SSO: Example
Configuring BGP NSR with SSO: Example
Configuring BGP NSR with SSO: Example
Figure 2 illustrates a sample BGP NSR with SSO network topology, and the configuration examples that follow show configurations from three routers in the topology: the RR1 router, the PE router, and the CE-1 router.

Note ![]() The configuration examples omit some of the configuration required for MPLS VPNs because the purpose of these examples is to illustrate the configuration of BGP NSR with SSO.
The configuration examples omit some of the configuration required for MPLS VPNs because the purpose of these examples is to illustrate the configuration of BGP NSR with SSO.
Figure 2 BGP NSR with SSO Example Topology
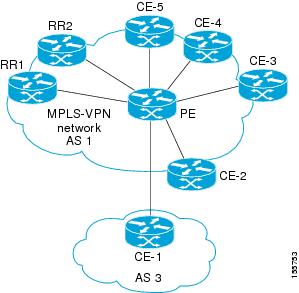
RR1 Configuration
The following example shows the BGP configuration for RR1 in Figure 2. RR1 is configured as a NSF-aware route reflector. In the event of an RP switchover, the PE router uses NSF to maintain the BGP state of the internal peering session with RR1.
!
router bgp 1
no synchronization
bgp log-neighbor-changes
bgp graceful-restart restart-time 120
bgp graceful-restart stalepath-time 360
bgp graceful-restart
neighbor 10.2.2.2 remote-as 1
neighbor 10.2.2.2 update-source Loopback0
no auto-summary
!
address-family vpnv4
neighbor 10.2.2.2 activate
neighbor 10.2.2.2 send-community both
neighbor 10.2.2.2 route-reflector-client
exit-address-family
!
PE Configuration
The following example shows the BGP NSR with SSO configuration for the PE router in Figure 2. The PE router is configured to support both NSF-awareness and the BGP NSR with SSO capability. In the event of an RP switchover, the PE router uses BGP NSR with SSO to maintain BGP state for the eBGP peering session with the CE-1 router, a CE router in this topology that is not NSF-aware, and uses NSF to maintain BGP state for the iBGP session with RR1. The PE router also detects if any of the other CE routers in the MPLS VPN network are NSF-aware and runs graceful restart with those CE routers.
!
router bgp 2
no synchronization
bgp log-neighbor-changes
bgp graceful-restart restart-time 120
bgp graceful-restart stalepath-time 360
bgp graceful-restart
neighbor 10.1.1.1 remote-as 1
neighbor 10.1.1.1 update-source Loopback0
no auto-summary
!
address-family vpnv4
neighbor 10.1.1.1 activate
neighbor 10.1.1.1 send-community both
exit-address-family
!
address-family ipv4 vrf ce-1
neighbor 10.3.3.3 remote-as 3
neighbor 10.3.3.3 ha-mode sso
neighbor 10.3.3.3 activate
neighbor 10.3.3.3 as-override
no auto-summary
no synchronization
exit-address-family
!
CE-1 Configuration
The following example shows the BGP configuration for CE-1 in Figure 2. The CE-1 router is configured as an external peer of the PE router. The CE-1 router is not configured to be NSF-capable or NSF-aware. The CE-1 router, however, does not need to be NSF-capable or NSF-aware to benefit from BGP NSR capabilities on the PE router nor does it need to be upgraded to support BGP NSR.
!
router bgp 3
neighbor 10.2.2.2 remote-as 1
!
Additional References
Related Documents
|
|
|
|---|---|
BGP concepts and configuration tasks |
"Cisco BGP Overview" module |
BGP commands: complete command syntax, command mode, command history, command defaults, usage guidelines, and examples |
|
BGP NSF awareness concepts, configuration tasks, and examples |
|
ISSU concepts, configuration tasks, and examples |
|
MPLS Layer 3 VPN concepts and configuration tasks |
|
MPLS Layer 3 VPN commands: complete command syntax, command mode, command history, command defaults, usage guidelines, and examples |
|
SSO concepts, configuration tasks, and examples |
Standards
|
|
|
|---|---|
No new or modified standards are supported by this feature, and support for existing standards has not been modified by this feature. |
— |
MIBs
RFCs
|
|
|
|---|---|
draft-ietf-idr-restart-06.txt |
Graceful Restart Mechanism for BGP |
Technical Assistance
Feature Information for BGP Support for Nonstop Routing (NSR) with Stateful Switchover (SSO)
Table 1 lists the release history for this feature.
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.

Note ![]() Table 1 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Table 1 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
 Feedback
Feedback