- RADIUS Attributes Overview and RADIUS IETF Attributes
- RADIUS Vendor-Proprietary Attributes
- RADIUS Vendor-Specific Attributes and RADIUS Disconnect-Cause Attribute Values
- Connect-Info RADIUS Attribute 77
- Encrypted Vendor-Specific Attributes
- RADIUS Attribute 8 Framed-IP-Address in Access Requests
- RADIUS Attribute 82 Tunnel Assignment ID
- RADIUS Tunnel Attribute Extensions
- RADIUS Attribute 66 Tunnel-Client-Endpoint Enhancements
- RADIUS Attribute Value Screening
- RADIUS Attribute 55 Event-Timestamp
- RADIUS Attribute 104
- RADIUS NAS-IP-Address Attribute Configurability
- RADIUS Attribute 5 NAS-Port Format Specified on a Per-Server Group Level
RADIUS Attributes Configuration Guide Cisco IOS XE Release 3S
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- July 11, 2017
Chapter: RADIUS Attributes Overview and RADIUS IETF Attributes
RADIUS Attributes Overview and RADIUS IETF Attributes
Remote Authentication Dial-In User Service (RADIUS) attributes are used to define specific authentication, authorization, and accounting (AAA) elements in a user profile, which are stored on the RADIUS program. This chapter lists the RADIUS attributes that are supported.
- Finding Feature Information
- RADIUS Attributes Overview
- RADIUS IETF Attributes
- Additional References
- Feature Information for RADIUS Attributes Overview and RADIUS IETF Attributes
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the Feature Information Table at the end of this document.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
RADIUS Attributes Overview
IETF Attributes Versus VSAs
RADIUS Internet Engineering Task Force (IETF) attributes are the original set of 255 standard attributes that are used to communicate AAA information between a client and a server. The IETF attributes are standard and the attribute data is predefined. All clients and servers that exchange AAA information using IETF attributes must agree on attribute data such as the exact meaning of the attributes and the general bounds of the values for each attribute.
RADIUS vendor-specific attributes (VSAs) are derived from a vendor-specific IETF attribute (attribute 26). Attribute 26 allows a vendor to create an additional 255 attributes; that is, a vendor can create an attribute that does not match the data of any IETF attribute and encapsulate it behind attribute 26. The newly created attribute is accepted if the user accepts attribute 26.
For more information on VSAs, refer to the chapter “RADIUS Vendor-Specific Attributes and RADIUS Disconnect-Cause Attribute Values.”
RADIUS Packet Format
The data between a RADIUS server and a RADIUS client is exchanged in RADIUS packets. The data fields are transmitted from left to right.
The figure below shows the fields within a RADIUS packet.
 Note |
For a diagram of VSAs, refer to Figure 1 in the chapter “RADIUS Vendor-Specific Attributes and RADIUS Disconnect-Cause Attribute Values.” |
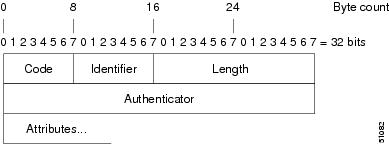
Each RADIUS packet contains the following information:
-
Code—The code field is one octet; it identifies one of the following types of RADIUS packets: - Identifier—The identifier field is one octet; it helps the RADIUS server match requests and responses and detect duplicate requests.
- Length—The length field is two octets; it specifies the length of the entire packet.
-
Authenticator—The authenticator field is 16 octets. The most significant octet is transmitted first; it is used to authenticate the reply from the RADIUS server. The two types of authenticators are:
RADIUS Packet Types
The following list defines the various types of RADIUS packet types that contain attribute information:
Access-Request—Sent from a client to a RADIUS server. The packet contains information that allows the RADIUS server to determine whether to allow access to a specific network access server (NAS), which will allow access to the user. A user performing authentication must submit an Access-Request packet. After the Access-Request packet is received, the RADIUS server must forward a reply.
Access-Accept—After a RADIUS server receives an Access-Request packet, it must send an Access-Accept packet if all attribute values in the Access-Request packet are acceptable. Access-Accept packets provide the configuration information necessary for the client to provide service to the user.
Access-Reject—After a RADIUS server receives an Access-Request packet, it must send an Access-Reject packet if any of the attribute values are not acceptable.
Access-Challenge—After the RADIUS server receives an Access-Accept packet, it can send the client an Access-Challenge packet, which requires a response. If the client does not know how to respond or if the packets are invalid, the RADIUS server discards the packets. If the client responds to the packet, a new Access-Request packet must be sent with the original Access-Request packet.
Accounting-Request—Sent from a client to a RADIUS accounting server, which provides accounting information. If the RADIUS server successfully records the Accounting-Request packet, it must submit an Accounting Response packet.
Accounting-Response—Sent by the RADIUS accounting server to the client to acknowledge that the Accounting-Request has been received and recorded successfully.
RADIUS Files
Understanding the types of files used by RADIUS is important for communicating AAA information from a client to a server. Each file defines a level of authentication or authorization for the user. The dictionary file defines which attributes the user’s NAS can implement, the clients file defines which users are allowed to make requests to the RADIUS server, and the users file defines which user requests the RADIUS server will authenticate based on security and configuration data.
Dictionary File
A dictionary file provides a list of attributes that are dependent on which attributes your NAS supports. However, you can add your own set of attributes to your dictionary for custom solutions. It defines attribute values, so you can interpret attribute output such as parsing requests. A dictionary file contains the following information:
- Name—The ASCII string “name” of the attribute, such as User-Name.
- ID—The numerical “name” of the attribute; for example, User-Name attribute is attribute 1.
-
Value type—Each attribute can be specified as one of the following five value types:
When the data type for a particular attribute is an integer, you can optionally expand the integer to equate to some string. The following sample dictionary includes an integer-based attribute and its corresponding values.
# dictionary sample of integer entry # ATTRIBUTE Service-Type 6 integer VALUE Service-Type Login 1 VALUE Service-Type Framed 2 VALUE Service-Type Callback-Login 3 VALUE Service-Type Callback-Framed 4 VALUE Service-Type Outbound 5 VALUE Service-Type Administrative 6 VALUE Service-Type NAS-Prompt 7 VALUE Service-Type Authenticate-Only 8 VALUE Service-Type Callback-NAS-Prompt 9 VALUE Service-Type Call-Check 10 VALUE Service-Type Callback-Administrative 11
Clients File
A clients file contains a list of RADIUS clients that are allowed to send authentication and accounting requests to the RADIUS server. To receive authentication, the name and authentication key that the client sends to the server must be an exact match with the data contained in the clients file.
The following is an example of a clients file. The key, as shown in this example, must be the same as the radius-server keySomeSecret command.
#Client Name Key #---------------- --------------- 10.1.2.3:256 test nas01 bananas nas02 MoNkEys nas07.foo.com SomeSecret
Users File
A RADIUS users file contains an entry for each user that the RADIUS server will authenticate; each entry, which is also known as a user profile, establishes an attribute the user can access.
The first line in any user profile is always a “user access” line; that is, the server must check the attributes on the first line before it can grant access to the user. The first line contains the name of the user, which can be up to 252 characters, followed by authentication information such as the password of the user.
Additional lines, which are associated with the user access line, indicate the attribute reply that is sent to the requesting client or server. The attributes sent in the reply must be defined in the dictionary file. When looking at a user file, note that the data to the left of the equal (=) character is an attribute defined in the dictionary file, and the data to the right of the equal character is the configuration data.
 Note |
A blank line cannot appear anywhere within a user profile. |
The following is an example of a RADIUS user profile (Merit Daemon format). In this example, the user name is company.com, the password is user1, and the user can access five tunnel attributes.
# This user profile includes RADIUS tunneling attributes
company.com Password="user1" Service-Type=Outbound
Tunnel-Type = :1:L2TP
Tunnel-Medium-Type = :1:IP
Tunnel-Server-Endpoint = :1:10.0.0.1
Tunnel-Password = :1:"welcome"
Tunnel-Assignment-ID = :1:"nas"
RADIUS IETF Attributes
 Note |
For RADIUS tunnel attributes, 32 tagged tunnel sets are supported for L2TP. |
Supported RADIUS IETF Attributes
Table 1 lists Cisco-supported IETF RADIUS attributes and the Cisco IOS release in which they are implemented. In cases where the attribute has a security server-specific format, the format is specified.
Refer to Table 2 for a description of each listed attribute.
 Note |
Attributes implemented in special (AA) or early development (T) releases are added to the next mainline image. |
| Number |
IETF Attribute |
11.1 |
11.2 |
11.3 |
11.3 AA |
11.3T |
12.0 |
12.1 |
12.2 |
|---|---|---|---|---|---|---|---|---|---|
| 1 |
User-Name |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 2 |
User-Password |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 3 |
CHAP-Password |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 4 |
NAS-IP Address |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 5 |
NAS-Port |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 6 |
Service-Type |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 7 |
Framed-Protocol |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 8 |
Framed-IP-Address |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 9 |
Framed-IP-Netmask |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 10 |
Framed-Routing |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 11 |
Filter-Id |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 12 |
Framed-MTU |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 13 |
Framed-Compression |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 14 |
Login-IP-Host |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 15 |
Login-Service |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 16 |
Login-TCP-Port |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 18 |
Reply-Message |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 19 |
Callback-Number |
no |
no |
no |
no |
no |
no |
yes |
yes |
| 20 |
Callback-ID |
no |
no |
no |
no |
no |
no |
no |
no |
| 22 |
Framed-Route |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 23 |
Framed-IPX-Network |
no |
no |
no |
no |
no |
no |
no |
no |
| 24 |
State |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 25 |
Class |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 26 |
Vendor-Specific |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 27 |
Session-Timeout |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 28 |
Idle-Timeout |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 29 |
Termination-Action |
no |
no |
no |
no |
no |
no |
no |
no |
| 30 |
Called-Station-Id |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 31 |
Calling-Station-Id |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 32 |
NAS-Identifier |
no |
no |
no |
no |
no |
no |
no |
yes |
| 33 |
Proxy-State |
no |
no |
no |
no |
no |
no |
no |
no |
| 34 |
Login-LAT-Service |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 35 |
Login-LAT-Node |
no |
no |
no |
no |
no |
no |
no |
yes |
| 36 |
Login-LAT-Group |
no |
no |
no |
no |
no |
no |
no |
no |
| 37 |
Framed-AppleTalk-Link |
no |
no |
no |
no |
no |
no |
no |
no |
| 38 |
Framed-AppleTalk- Network |
no |
no |
no |
no |
no |
no |
no |
no |
| 39 |
Framed-AppleTalk-Zone |
no |
no |
no |
no |
no |
no |
no |
no |
| 40 |
Acct-Status-Type |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 41 |
Acct-Delay-Time |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 42 |
Acct-Input-Octets |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 43 |
Acct-Output-Octets |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 44 |
Acct-Session-Id |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 45 |
Acct-Authentic |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 46 |
Acct-Session-Time |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 47 |
Acct-Input-Packets |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 48 |
Acct-Output-Packets |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 49 |
Acct-Terminate-Cause |
no |
no |
no |
yes |
yes |
yes |
yes |
yes |
| 50 |
Acct-Multi-Session-Id |
no |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 51 |
Acct-Link-Count |
no |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 52 |
Acct-Input-Gigawords |
no |
no |
no |
no |
no |
no |
no |
no |
| 53 |
Acct-Output-Gigawords |
no |
no |
no |
no |
no |
no |
no |
no |
| 55 |
Event-Timestamp |
no |
no |
no |
no |
no |
no |
no |
yes |
| 60 |
CHAP-Challenge |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 61 |
NAS-Port-Type |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 62 |
Port-Limit |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
yes |
| 63 |
Login-LAT-Port |
no |
no |
no |
no |
no |
no |
no |
no |
| 64 |
Tunnel-Type1 |
no |
no |
no |
no |
no |
no |
yes |
yes |
| 65 |
Tunnel-Medium-Type 1 |
no |
no |
no |
no |
no |
no |
yes |
yes |
| 66 |
Tunnel-Client-Endpoint |
no |
no |
no |
no |
no |
no |
yes |
yes |
| 67 |
Tunnel-Server-Endpoint 1 |
no |
no |
no |
no |
no |
no |
yes |
yes |
| 68 |
Acct-Tunnel-Connection-ID |
no |
no |
no |
no |
no |
no |
yes |
yes |
| 69 |
Tunnel-Password 1 |
no |
no |
no |
no |
no |
no |
yes |
yes |
| 70 |
ARAP-Password |
no |
no |
no |
no |
no |
no |
no |
no |
| 71 |
ARAP-Features |
no |
no |
no |
no |
no |
no |
no |
no |
| 72 |
ARAP-Zone-Access |
no |
no |
no |
no |
no |
no |
no |
no |
| 73 |
ARAP-Security |
no |
no |
no |
no |
no |
no |
no |
no |
| 74 |
ARAP-Security-Data |
no |
no |
no |
no |
no |
no |
no |
no |
| 75 |
Password-Retry |
no |
no |
no |
no |
no |
no |
no |
no |
| 76 |
Prompt |
no |
no |
no |
no |
no |
no |
yes |
yes |
| 77 |
Connect-Info |
no |
no |
no |
no |
no |
no |
no |
yes |
| 78 |
Configuration-Token |
no |
no |
no |
no |
no |
no |
no |
no |
| 79 |
EAP-Message |
no |
no |
no |
no |
no |
no |
no |
no |
| 80 |
Message-Authenticator |
no |
no |
no |
no |
no |
no |
no |
no |
| 81 |
Tunnel-Private-Group-ID |
no |
no |
no |
no |
no |
no |
no |
no |
| 82 |
Tunnel-Assignment-ID 1 |
no |
no |
no |
no |
no |
no |
yes |
yes |
| 83 |
Tunnel-Preference |
no |
no |
no |
no |
no |
no |
no |
yes |
| 84 |
ARAP-Challenge-Response |
no |
no |
no |
no |
no |
no |
no |
no |
| 85 |
Acct-Interim-Interval |
no |
no |
no |
no |
no |
no |
yes |
yes |
| 86 |
Acct-Tunnel-Packets-Lost |
no |
no |
no |
no |
no |
no |
no |
no |
| 87 |
NAS-Port-ID |
no |
no |
no |
no |
no |
no |
no |
no |
| 88 |
Framed-Pool |
no |
no |
no |
no |
no |
no |
no |
no |
| 90 |
Tunnel-Client-Auth-ID 2 |
no |
no |
no |
no |
no |
no |
no |
yes |
| 91 |
Tunnel-Server-Auth-ID |
no |
no |
no |
no |
no |
no |
no |
yes |
| 200 |
IETF-Token-Immediate |
no |
no |
no |
no |
no |
no |
no |
no |
Comprehensive List of RADIUS Attribute Descriptions
The table below lists and describes IETF RADIUS attributes. In cases where the attribute has a security server-specific format, the format is specified.
| Number |
IETF Attribute |
Description |
||
|---|---|---|---|---|
| 1 |
User-Name |
Indicates the name of the user being authenticated by the RADIUS server. |
||
| 2 |
User-Password |
Indicates the user’s password or the user’s input following an Access-Challenge. Passwords longer than 16 characters are encrypted using RFC 2865 specifications. |
||
| 3 |
CHAP-Password |
Indicates the response value provided by a PPP Challenge Handshake Authentication Protocol (CHAP) user in response to an Access-Challenge. |
||
| 4 |
NAS-IP Address |
Specifies the IP address of the network access server that is requesting authentication. The default value is 0.0.0.0/0. |
||
| 5 |
NAS-Port |
Indicates the physical port number of the network access server that is authenticating the user. The NAS-Port value (32 bits) consists of one or two 16-bit values (depending on the setting of the radius-server extended-portnames command). Each 16-bit number should be viewed as a 5-digit decimal integer for interpretation as follows: For asynchronous terminal lines, asynchronous network interfaces, and virtual asynchronous interfaces, the value is 00ttt, where ttt is the line number or asynchronous interface unit number. |
||
| 6 |
Service-Type |
Indicates the type of service requested or the type of service to be provided. Framed for known PPP or Serial Line Internet Protocol (SLIP) connection. Administrative-user for enable command. Login—Make a connection. Framed--Start SLIP or PPP. Administrative User--Start an EXEC or enable ok. Exec User—Start an EXEC session. Service type is indicated by a particular numeric value as follows: |
||
| 7 |
Framed-Protocol |
Indicates the framing to be used for framed access. No other framing is allowed. Framing is indicated by a numeric value as follows: |
||
| 8 |
Framed-IP-Address |
Indicates the IP address to be configured for the user, by sending the IP address of a user to the RADIUS server in the access-request. To enable this command, use the radius-server attribute 8 include-in-access-req command in global configuration mode. |
||
| 9 |
Framed-IP-Netmask |
Indicates the IP netmask to be configured for the user when the user is using a device on a network. This attribute value results in a static route being added for Framed-IP-Address with the mask specified. |
||
| 10 |
Framed-Routing |
Indicates the routing method for the user when the user is using a device on a network. Only “None” and “Send and Listen” values are supported for this attribute. Routing method is indicated by a numeric value as follows: |
||
| 11 |
Filter-Id |
Indicates the name of the filter list for the user and is formatted as follows: %d, %d.in, or %d.out. This attribute is associated with the most recent service-type command. For login and EXEC, use %d or %d.out as the line access list value from 0 to 199. For Framed service, use %d or %d.out as interface output access list, and %d.in for input access list. The numbers are self-encoding to the protocol to which they refer. |
||
| 12 |
Framed-MTU |
Indicates the maximum transmission unit (MTU) that can be configured for the user when the MTU is not negotiated by PPP. |
||
| 13 |
Framed-Compression |
Indicates a compression protocol used for the link. This attribute results in a “/compress” being added to the PPP or SLIP autocommand generated during EXEC authorization. This is not implemented for non-EXEC authorization. Compression protocol is indicated by a numeric value as follows: |
||
| 14 |
Login-IP-Host |
Indicates the host to which the user will connect when the Login-Service attribute is included. This begins immediately after login. |
||
| 15 |
Login-Service |
Indicates the service that should be used to connect the user to the login host. Service is indicated by a numeric value as follows: |
||
| 16 |
Login-TCP-Port |
Defines the TCP port with which the user is to be connected when the Login-Service attribute is also present. |
||
| 18 |
Reply-Message |
Indicates text that might be displayed to the user using the RADIUS server. You can include this attribute in user files; however, you cannot exceed a maximum of 16 Reply-Message entries per profile. |
||
| 19 |
Callback-Number |
Defines a dialing string to be used for callback. |
||
| 20 |
Callback-ID |
Defines the name (consisting of one or more octets) of a place to be called, to be interpreted by the network access server. |
||
| 22 |
Framed-Route |
Provides routing information to be configured for the user on this network access server. The RADIUS RFC format (net/bits [router [metric]]) and the old style dotted mask (net mask [router [metric]]) are supported. If the device field is omitted or 0, the peer IP address is used. Metrics are currently ignored. This attribute is access-request packets. |
||
| 23 |
Framed-IPX-Network |
Defines the IPX network number configured for the user. |
||
| 24 |
State |
Allows state information to be maintained between the network access server and the RADIUS server. This attribute is applicable only to CHAP challenges. |
||
| 25 |
Class |
(Accounting) Arbitrary value that the network access server includes in all accounting packets for this user if supplied by the RADIUS server. |
||
| 26 |
Vendor-Specific |
Allows vendors to support their own extended attributes not suitable for general use. The Cisco RADIUS implementation supports one vendor-specific option using the format recommended in the specification. Cisco's vendor-ID is 9, and the supported option has vendor-type 1, which is named “cisco-avpair.” The value is a string of the format: protocol : attribute sep value “Protocol” is a value of the Cisco “protocol” attribute for a particular type of authorization. “Attribute” and “value” are an appropriate AV pair defined in the Cisco TACACS+ specification, and “sep” is “=” for mandatory attributes and “*” for optional attributes. This allows the full set of features available for TACACS+ authorization to also be used for RADIUS. For example: cisco-avpair= ”ip:addr-pool=first“ cisco-avpair= ”shell:priv-lvl=15“ The first example causes Cisco’s Multiple Named ip address Pools” feature to be activated during IP authorization (during PPP’s IPCP address assignment). The second example causes a user logging in from a network access server to have immediate access to EXEC commands. Table 1 lists supported vendor-specific RADIUS attributes (IETF attribute 26). |
||
| 27 |
Session-Timeout |
Sets the maximum number of seconds of service to be provided to the user before the session terminates. This attribute value becomes the per-user absolute timeout. |
||
| 28 |
Idle-Timeout |
Sets the maximum number of consecutive seconds of idle connection allowed to the user before the session terminates. This attribute value becomes the per-user session-timeout. |
||
| 29 |
Termination-Action |
Termination is indicated by a numeric value as follows: |
||
| 30 |
Called-Station-Id |
(Accounting) Allows the network access server to send the telephone number the user called as part of the Access-Request packet (using Dialed Number Identification Service [DNIS] or a similar technology). This attribute is only supported on ISDN and modem calls on the Cisco AS5200 if used with PRI. |
||
| 31 |
Calling-Station-Id |
(Accounting) Allows the network access server to send the telephone number the call came from as part of the Access-Request packet (using Automatic Number Identification or a similar technology). This attribute has the same value as “remote-addr” from TACACS+. This attribute is only supported on ISDN and modem calls on the Cisco AS5200 if used with PRI. |
||
| 32 |
NAS-Identifier |
String identifying the network access server originating the Access-Request. Use the radius-server attribute 32 include-in-access-req global configuration command to send RADIUS attribute 32 in an Access-Request or Accounting-Request. By default, the Fully Qualified Domain Name (FQDN) is sent in the attribute when the format is not specified. |
||
| 33 |
Proxy-State |
Attribute that can be sent by a proxy server to another server when forwarding Access-Requests; this must be returned unmodified in the Access-Accept, Access-Reject or Access-Challenge and removed by the proxy server before sending the response to the network access server. |
||
| 34 |
Login-LAT-Service |
Indicates the system with which the user is to be connected by local area transport (LAT). This attribute is only available in the EXEC mode. |
||
| 35 |
Login-LAT-Node |
Indicates the node with which the user is automatically connected by LAT. |
||
| 36 |
Login-LAT-Group |
Identifies the LAT group codes that the user is authorized to use. |
||
| 37 |
Framed-AppleTalk-Link |
Indicates the AppleTalk network number that should be used for serial links, which is another AppleTalk device. |
||
| 38 |
Framed-AppleTalk- Network |
Indicates the AppleTalk network number that the network access server uses to allocate an AppleTalk node for the user. |
||
| 39 |
Framed-AppleTalk-Zone |
Indicates the AppleTalk Default Zone to be used for the user. |
||
| 40 |
Acct-Status-Type |
(Accounting) Indicates whether this Accounting-Request marks the beginning of the user service (start) or the end (stop). |
||
| 41 |
Acct-Delay-Time |
(Accounting) Indicates how many seconds the client has been trying to send a particular record. |
||
| 42 |
Acct-Input-Octets |
(Accounting) Indicates how many octets have been received from the port over the course of this service being provided. |
||
| 43 |
Acct-Output-Octets |
(Accounting) Indicates how many octets have been sent to the port in the course of delivering this service. |
||
| 44 |
Acct-Session-Id |
(Accounting) A unique accounting identifier that makes it easy to match start and stop records in a log file. Acct-Session ID numbers restart at 1 each time the device is power-cycled or the software is reloaded. To send this attribute in access-request packets, use the radius-server attribute 44 include-in-access-req command in global configuration mode. |
||
| 45 |
Acct-Authentic |
(Accounting) Indicates how the user was authenticated, whether by RADIUS, the network access server itself, or another remote authentication protocol. This attribute is set to “radius” for users authenticated by RADIUS; “remote” for TACACS+ and Kerberos; or “local” for local, enable, line, and if-needed methods. For all other methods, the attribute is omitted. |
||
| 46 |
Acct-Session-Time |
(Accounting) Indicates how long (in seconds) the user has received service. |
||
| 47 |
Acct-Input-Packets |
(Accounting) Indicates how many packets have been received from the port over the course of this service being provided to a framed user. |
||
| 48 |
Acct-Output-Packets |
(Accounting) Indicates how many packets have been sent to the port in the course of delivering this service to a framed user. |
||
| 49 |
Acct-Terminate-Cause |
(Accounting) Reports details on why the connection was terminated. Termination causes are indicated by a numeric value as follows:
|
||
| 50 |
Acct-Multi-Session-Id |
(Accounting) A unique accounting identifier used to link multiple related sessions in a log file. Each linked session in a multilink session has a unique Acct-Session-Id value, but shares the same Acct-Multi-Session-Id. |
||
| 51 |
Acct-Link-Count |
(Accounting) Indicates the number of links known in a given multilink session at the time an accounting record is generated. The network access server can include this attribute in any accounting request that might have multiple links. |
||
| 52 |
Acct-Input-Gigawords |
Indicates how many times the Acct-Input-Octets counter has wrapped around 2^32 over the course of the provided service. |
||
| 53 |
Acct-Output-Gigawords |
Indicates how many times the Acct-Output-Octets counter has wrapped around 2^32 while delivering service. |
||
| 55 |
Event-Timestamp |
Records the time that the event occurred on the NAS, the timestamp sent in attribute 55 is in seconds since January 1, 1970 00:00 UTC. To send RADIUS attribute 55 in accounting packets, use the radius-server attribute 55 include-in-acct-req command.
|
||
| 60 |
CHAP-Challenge |
Contains the Challenge Handshake Authentication Protocol challenge sent by the network access server to a PPP CHAP user. |
||
| 61 |
NAS-Port-Type |
Indicates the type of physical port the network access server is using to authenticate the user. Physical ports are indicated by a numeric value as follows: |
||
| 62 |
Port-Limit |
Sets the maximum number of ports provided to the user by the NAS. |
||
| 63 |
Login-LAT-Port |
Defines the port with which the user is to be connected by LAT. |
||
| 64 |
Tunnel-Type3 |
Indicates the tunneling protocol(s) used. Cisco software supports one possible value for this attribute: L2TP. |
||
| 65 |
Tunnel-Medium-Type1 |
Indicates the transport medium type used to create a tunnel. This attribute has only one available value for this release: IP. If no value is set for this attribute, IP is used as the default. |
||
| 66 |
Tunnel-Client-Endpoint |
Contains the address of the initiator end of the tunnel. It may be included in both Access-Request and Access-Accept packets to indicate the address from which a new tunnel is to be initiated. If the Tunnel-Client-Endpoint attribute is included in an Access-Request packet, the RADIUS server should take the value as a hint. This attribute should be included in Accounting-Request packets that contain Acct-Status-Type attributes with values of either Start or Stop, in which case it indicates the address from which the tunnel was initiated. This attribute, along with the Tunnel-Server-Endpoint and Acct-Tunnel-Connection-ID attributes, may be used to provide a globally unique method to identify a tunnel for accounting and auditing purposes. An enhancement has been added for the network access server to accept a value of 127.0.0.X for this attribute such that: 127.0.0.0 would indicate that loopback0 IP address has to be used, 127.0.0.1 would indicate that loopback1 IP address has to be used. 127.0.0.X would indicate that loopbackX IP address has to be used for the actual tunnel client endpoint IP address. This enhancement adds scalability across multiple network access servers. |
||
| 67 |
Tunnel-Server-Endpoint1 |
Indicates the address of the server end of the tunnel. The format of this attribute varies depending on the value of Tunnel-Medium-Type. Depending on your release only IP as a tunnel medium type may be supported and the IP address or the host name of LNS is valid for this attribute. |
||
| 68 |
Acct-Tunnel-Connection-ID |
Indicates the identifier assigned to the tunnel session. This attribute should be included in Accounting-Request packets that contain an Acct-Status-Type attribute having the value Start, Stop, or any of the values described above. This attribute, along with the Tunnel-Client-Endpoint and Tunnel-Server-Endpoint attributes, may be used to provide a method to uniquely identify a tunnel session for auditing purposes. |
||
| 69 |
Tunnel-Password1 |
Defines the password to be used to authenticate to a remote server. This attribute is converted into different AAA attributes based on the value of Tunnel-Type: AAA_ATTR_l2tp_tunnel_pw (L2TP), AAA_ATTR_nas_password (L2F), and AAA_ATTR_gw_password (L2F). By default, all passwords received are encrypted, which can cause authorization failures when a NAS attempts to decrypt a non-encrypted password. To enable attribute 69 to receive non-encrypted passwords, use the radius-server attribute 69 clear command in global configuration mode. |
||
| 70 |
ARAP-Password |
Identifies an Access-Request packet containing a Framed-Protocol of AppleTalk Remote Access Control (ARAP). |
||
| 71 |
ARAP-Features |
Includes password information that the NAS should send to the user in an ARAP feature flags packet. |
||
| 72 |
ARAP-Zone-Access |
Indicates how the ARAP zone list for the user should be used. |
||
| 73 |
ARAP-Security |
Identifies the ARAP Security Module to be used in an Access-Challenge packet. |
||
| 74 |
ARAP-Security-Data |
Contains the actual security module challenge or response in Access-Challenge and Access-Request packets. |
||
| 75 |
Password-Retry |
Indicates the number of times a user may attempt authentication before being disconnected. |
||
| 76 |
Prompt |
Indicates to the NAS whether it should echo the user’s response as it is entered or not echo it. (0 = no echo, 1 = echo) |
||
| 77 |
Connect-Info |
Provides additional call information for modem calls. This attribute is generated in start and stop accounting records. |
||
| 78 |
Configuration-Token |
Indicates the type of user profile to be used. This attribute should be used in large distributed authentication networks based on proxy. It is sent from a RADIUS Proxy Server to a RADIUS Proxy Client in an Access-Accept; it should not be sent to a NAS. |
||
| 79 |
EAP-Message |
Encapsulates Extended Access Protocol (EAP) packets that allow the NAS to authenticate dial-in users using EAP without having to understand the EAP protocol. |
||
| 80 |
Message-Authenticator |
Prevents spoofing Access-Requests using CHAP, ARAP, or EAP authentication methods. |
||
| 81 |
Tunnel-Private-Group-ID |
Indicates the group ID for a particular tunneled session. |
||
| 82 |
Tunnel-Assignment-ID1 |
Indicates to the tunnel initiator the particular tunnel to which a session is assigned. |
||
| 83 |
Tunnel-Preference |
Indicates the relative preference assigned to each tunnel. This attribute should be included if more than one set of tunneling attributes is returned by the RADIUS server to the tunnel initiator. |
||
| 84 |
ARAP-Challenge-Response |
Contains the response to the challenge of the dial-in client. |
||
| 85 |
Acct-Interim-Interval |
Indicates the number of seconds between each interim update in seconds for this specific session. This value can only appear in the Access-Accept message. |
||
| 86 |
Acct-Tunnel-Packets-Lost |
Indicates the number of packets lost on a given link. This attribute should be included in Accounting-Request packets that contain an Acct-Status-Type attribute having the value Tunnel-Link-Stop. |
||
| 87 |
NAS-Port-ID |
Contains a text string which identifies the port of the NAS that is authenticating the user. |
||
| 88 |
Framed-Pool |
Contains the name of an assigned address pool that should be used to assign an address for the user. If a NAS does not support multiple address pools, the NAS should ignore this attribute. |
||
| 90 |
Tunnel-Client-Auth-ID |
Specifies the name used by the tunnel initiator (also known as the NAS) when authenticating tunnel setup with the tunnel terminator. Supports L2F and L2TP protocols. |
||
| 91 |
Tunnel-Server-Auth-ID |
Specifies the name used by the tunnel terminator (also known as the Home Gateway) when authenticating tunnel setup with the tunnel initiator. Supports L2F and L2TP protocols. |
||
| 200 |
IETF-Token-Immediate |
Determines how RADIUS treats passwords received from login-users when their file entry specifies a hand-held security card server. The value for this attribute is indicated by a numeric value as follows: |
Additional References
Related Documents
Related Topic |
Document Title |
|---|---|
| Cisco IOS commands |
|
| Security commands |
|
RFCs
| RFC |
Title |
|---|---|
| RFC 2865 |
|
| RFC 2866 |
|
| RFC 2867 |
|
| RFC 2868 |
|
| RFC 2869 |
Technical Assistance
Description |
Link |
|---|---|
| The Cisco Support and Documentation website provides online resources to download documentation, software, and tools. Use these resources to install and configure the software and to troubleshoot and resolve technical issues with Cisco products and technologies. Access to most tools on the Cisco Support and Documentation website requires a Cisco.com user ID and password. |
Feature Information for RADIUS Attributes Overview and RADIUS IETF Attributes
The following table provides release information about the feature or features described in this module. This table lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
| Feature Name |
Releases |
Feature Information |
|---|---|---|
| RADIUS IETF Attributes |
Cisco IOS Release 11.1 |
This feature was introduced in Cisco IOS Release 11.1.
|
 Feedback
Feedback