Catalyst 6500 Series SSL Services Module Installation and Configuration Note, 1.1
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- March 18, 2015
Chapter: Overview
Overview
The SSL Services Module is a Layer 4-through-Layer 7 service module that you can install into the Catalyst 6500 series switch. The module terminates secure sockets layer (SSL) transactions and accelerates the encryption and decryption of data used in SSL sessions.
The module operates either in a standalone configuration or with the Content Switching Module (CSM). In a standalone configuration, secure traffic is directed to the module using policy-based routing (PBR). When used with the CSM, only encrypted client traffic is forwarded to the module, while clear text traffic is forwarded to the real servers.
The SSL Services Module uses the SSL protocol to enable secure transactions of data through privacy, authentication, and data integrity; the protocol relies upon certificates, public keys, and private keys.
The certificates, which are similar to digital ID cards, verify the identity of the server to the clients. The certificates, which are issued by certificate authorities, include the name of the entity to which the certificate was issued, the entity's public key, and the time stamps that indicate the certificate's expiration date.
The public and private keys are the ciphers that are used to encrypt and decrypt information. The public key is shared without any restrictions, but the private key is never shared. Each public-private key pair works together; data that is encrypted with the public key can only be decrypted with the corresponding private key.
These sections describe the SSL Services Module:
Features
The SSL Services Module has these features:
•![]() Accelerates SSL transactions to help alleviate the server processing load
Accelerates SSL transactions to help alleviate the server processing load
•![]() Enables intelligent content switching using the CSM to server load balance (SLB) traffic
Enables intelligent content switching using the CSM to server load balance (SLB) traffic
•![]() Provides centralized management (for the key, certificate, and configuration management)
Provides centralized management (for the key, certificate, and configuration management)
Table 1-1 lists the available features.
|
|
|---|
|
|
|
|
– – – |
|
|
SSL 3.0 |
SSL 3.1/TLS 1.0 |
SSL 2.0 (only ClientHello support) |
Session reuse |
Session renegotiation |
|
|
ARC4 |
DES |
3DES |
|
|
RSA |
|
|
MD5 |
SHA1 |
|
|
SSL_RSA_WITH_RC4_128_MD5 |
SSL_RSA_WITH_RC4_128_SHA |
SSL_RSA_WITH_DES_CSC_SHA |
SSL_RSA_WITH_3DES_EDE_CBC_SHA |
|
|
RSA key pair generation for server certificates |
Secure server key storage in SSL Services Module Flash memory device |
Server certificate enrollment |
Importing and exporting of server key and certificate |
Duplicating keys and certificates on standby SSL Services Module using the key and certificate import and export mechanism |
|
|
Manual key archival, recovery, and backup |
Key and certificate renewal using the CLI |
Graceful rollover of expiring server keys and certificates |
Auto-enrollment of server certificates |
|
|
RFC 1323 |
Connection aging |
Connection rate |
Up to 64,000 concurrent client connections |
Up to 192,000 concurrent connections (includes 2 MSL3 ) |
Up to 300 Mbps throughput |
|
|
Client NAT |
Server NAT/PAT5 |
|
|
Multiple modules in a single chassis when used with the CSM6 ; the CSM provides server load balancing |
|
|
Failure detection (SLB7 health monitoring schemes) |
System-level redundancy (stateless) (when used with the CSM) |
Module-level redundancy (stateless) (when used with the CSM) |
|
|
OIR8 (after properly shutdown) |
Graceful shutdown |
|
|
Total SSL connections attempt per virtual server |
Total SSL connections successfully established per virtual server |
Total SSL connections failed per virtual server |
Total SSL alert errors per virtual server |
Total SSL resumed sessions per virtual server |
Total encrypted/decrypted packets/bytes per virtual server |
|
|
Direct connection to the module console port |
Secure Shell (SSHv1) session |
Telnet |
|
|
Up to 300 Mbps throughput |
Up to 256 proxy servers |
Up to 64,000 simultaneous sessions |
Stores up to 356 key pairs |
Stores up to 356 certificates |
Supports the following RSA key sizes: – – – – – |
Up to 3000 sessions per second |
1 MSFC = Multilayer Switch Feature Card 2 PFC = Policy Feature Card 3 MSL = Maximum Segment Lifetime 4 NAT = Network Address Translation 5 PAT = Port Address Translation 6 CSM = Content Switching Module 7 SLB = Server Load Balancing 8 OIR = Online Insertion And Removal |
Front Panel Description
The SSL Services Module front panel (see Figure 1-1) includes a STATUS LED, a FIPS (Federal Information Processing Standards ) LED, a SHUTDOWN button, and a console port.
Figure 1-1 SSL Services Module Front Panel
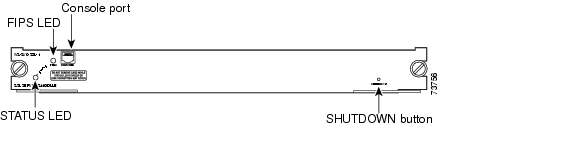
These sections describe the SSL Services Module front panel:
STATUS LED
The STATUS LED indicates the operating states of the module. Table 1-2 describes the LED operation.
FIPS LED
The Federal Information Processing Standards (FIPS) LED currently is not used.
SHUTDOWN Button

To avoid corrupting the SSL Services Module hard disk, you must correctly shut down the SSL Services Module before you remove it from the chassis or disconnect the power. You can shut down the module by entering the hw-mod module mod shutdown command in privileged mode from the router CLI.
If the SSL Services Module fails to respond to this command, shut down the module by using a small, pointed object (such as a paper clip) to access the SHUTDOWN button on the front panel.
The shutdown procedure may require several minutes. The STATUS LED turns off when the module shuts down.
 Feedback
Feedback