Cisco Application Policy Infrastructure Controller Enterprise Module Upgrade Guide, Release 1.2.x
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- May 26, 2016
Chapter: Before You Begin
Before You Begin
Read the following information carefully, before you begin an upgrade.
- Review Supported Upgrade Paths
- Review Time Taken for Upgrade
- Review Available Cisco APIC-EM Ports
- Back Up the Controller Database and Files
Review Supported Upgrade Paths
You can directly upgrade to Cisco APIC-EM, Release 1.2.0.x from any of the following releases:
If you encounter any problems with upgrading from releases 1.0.2.8 or 1.0.3.4, then see the release notes for the workaround procedure. If you using a release version earlier than the above Cisco APIC-EM releases, then you must first upgrade to one of the releases listed above (with the latest patch) and then upgrade to Release 1.2.0.x.
Review Time Taken for Upgrade
The upgrade process for the Cisco APIC-EM may take up to approximately 60 minutes to complete. The actual time taken for an upgrade varies depending upon a number of factors, including the scale of your network deployment, number of endpoints involved, and applications in use (EasyQoS, IWAN, and Network Plug and Play).
 Note | Services will be restarted at different times during the upgrade process and for this reason, not all the applications will start up at once. |
Review Available Cisco APIC-EM Ports
The following tables list the Cisco APIC-EM ports that permit incoming traffic, as well as the Cisco APIC-EM ports that are used for outgoing traffic. You should ensure that these ports on the controller are open for both incoming and outgoing traffic flows.
The following table lists Cisco APIC-EM ports that permit incoming traffic into the controller.
|
Port Number |
Permitted Traffic |
Protocol (TCP or UDP) |
|---|---|---|
|
22 |
SSH |
TCP |
|
67 |
bootps |
UDP |
|
80 |
HTTP |
TCP |
|
123 |
NTP |
UDP |
|
162 |
SNMP |
UDP |
|
443 |
HTTPS |
TCP |
|
500 |
ISAKMP In order for deploying multiple hosts across firewalls in certain deployments, the IPSec ISAKMP ( (Internet Security Association and Key Management Protocol) UDP port 500 has to be allowed to be traversed. |
UDP |
|
14141 |
Grapevine console |
TCP |
|
16026 |
SCEP |
TCP |
The following table lists Cisco APIC-EM ports that are used for outgoing traffic from the controller.
|
Port Number |
Permitted Traffic |
Protocol (TCP or UDP) |
||
|---|---|---|---|---|
|
22 |
SSH (to the network devices) |
TCP |
||
|
23 |
Telnet (to the network devices) |
TCP |
||
|
53 |
DNS |
UDP |
||
|
80 |
Port 80 may be used for an outgoing proxy configuration. Additionally, other common ports such as 8080 may also be used when a proxy is being configured by the Cisco APIC-EM configuration wizard (if a proxy is already in use for your network).
|
TCP |
||
|
123 |
NTP |
UDP |
||
|
161 |
SNMP agent |
UDP |
||
|
443 |
HTTPS |
TCP |
||
|
500 |
ISAKMP In order for deploying multiple hosts across firewalls in certain deployments, the IPSec ISAKMP ( (Internet Security Association and Key Management Protocol) UDP port 500 has to be allowed to be traversed. |
UDP |
Back Up the Controller Database and Files
Before performing an upgrade, you should back up your controller's database and files using the Backup & Restore window of the GUI.
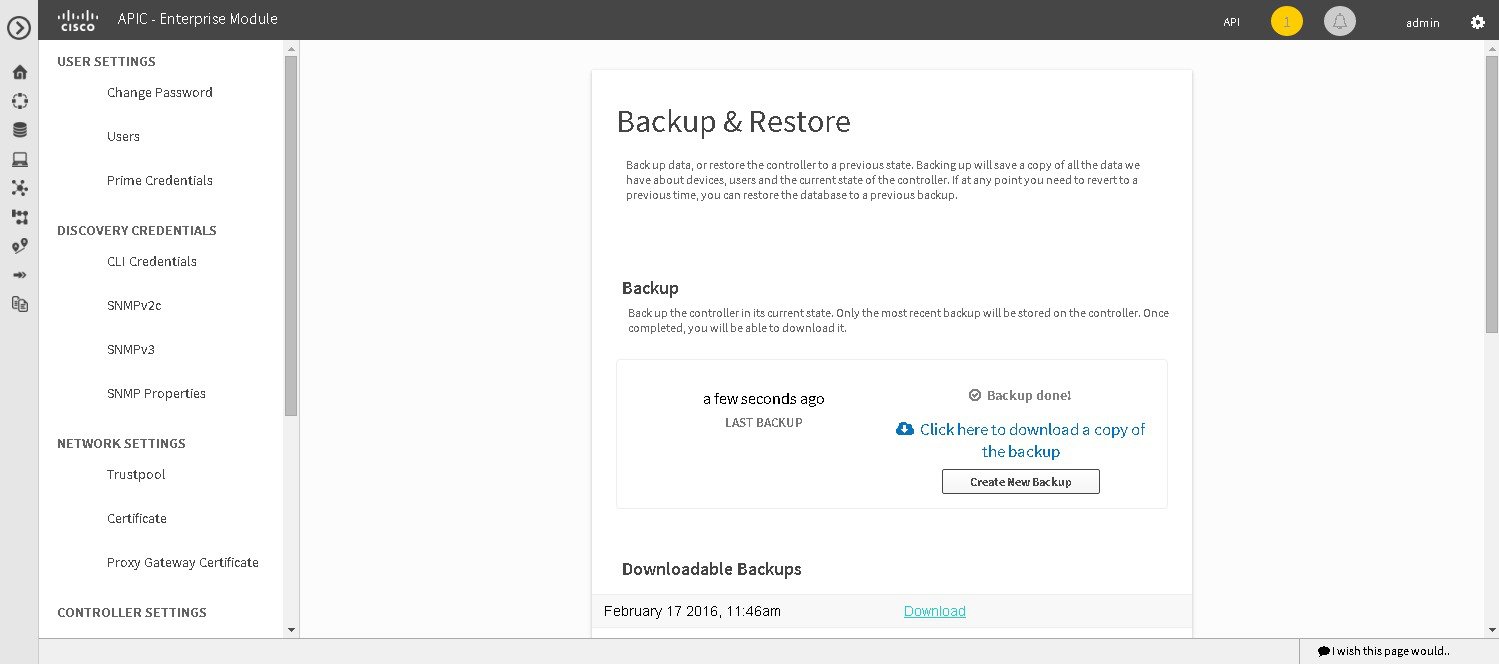
 Note | In a multi-host cluster, the database and files are replicated and shared across three hosts. When backing up and restoring in a multi-host cluster, you need to first back up on only one of the three hosts in the cluster. For detailed information about both back up and restore, see the Cisco Application Policy Infrastructure Controller Enterprise Module Deployment Guide. |
You must have administrator (ROLE_ADMIN) permissions to perform this procedure.
For information about the user permissions required to perform tasks using the Cisco APIC-EM, see the chapter, Managing Users and Roles in the Cisco Application Policy Infrastructure Controller Enterprise Module Configuration Guide.
 Feedback
Feedback