- Index
- Preface
- Introduction to Cisco WAAS
- Planning Your WAAS Network
- Using Device Groups and Device Locations
- Configuring Traffic Interception
- Configuring Network Settings
- Configuring Administrative Login Authentication, Authorization, and Accounting
- Creating and Managing Administrator User Accounts and Groups
- Creating and Managing IP Access Control Lists for WAAS Devices
- Configuring Other System Settings
- Using the WAE Device Manager GUI
- Configuring Wide Area File Services
- Configuring Application Acceleration
- Configuring and Managing WAAS Print Services
- Configuring Virtualization
- Maintaining Your WAAS System
- Monitoring and Troubleshooting Your WAAS Network
- Configuring SNMP Monitoring
- Default Application Policies
Cisco Wide Area Application Services Configuration Guide (Software Version 4.1.3)
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- March 18, 2015
Chapter: Monitoring and Troubleshooting Your WAAS Network
- Viewing System Information from the System Dashboard Window
- Troubleshooting Devices Using Alerts
- Viewing Device Information
- Traffic Summary Report
- Traffic Optimization Report
- Optimization Summary Report
- HTTP Acceleration Report
- Video Acceleration Report
- SSL Acceleration Report
- MAPI Acceleration Report
- NFS Acceleration Report
- Topology Report
- Connections Statistics Report
- CIFS Acceleration Report
- CPU Statistics Report
- Disks Report
Monitoring and Troubleshooting Your WAAS Network
This chapter describes the monitoring and troubleshooting tools available in the WAAS Central Manager GUI that can help you identify and resolve issues with your WAAS system.

Note ![]() Throughout this chapter, the term WAAS device is used to refer collectively to the WAAS Central Managers and WAEs in your network. The term WAE refers to WAE appliances and WAE Network Modules (the NME-WAE family of devices).
Throughout this chapter, the term WAAS device is used to refer collectively to the WAAS Central Managers and WAEs in your network. The term WAE refers to WAE appliances and WAE Network Modules (the NME-WAE family of devices).
This chapter contains the following sections:
•![]() Viewing System Information from the System Dashboard Window
Viewing System Information from the System Dashboard Window
•![]() Troubleshooting Devices Using Alerts
Troubleshooting Devices Using Alerts
•![]() Customizing a Dashboard or Report
Customizing a Dashboard or Report
•![]() Using Predefined Reports to Monitor WAAS
Using Predefined Reports to Monitor WAAS
•![]() Configuring Transaction Logging
Configuring Transaction Logging
•![]() Viewing the System Message Log
Viewing the System Message Log
•![]() Troubleshooting Using Diagnostic Tests
Troubleshooting Using Diagnostic Tests
•![]() Using the show and clear Commands from the WAAS Central Manager GUI
Using the show and clear Commands from the WAAS Central Manager GUI
Viewing System Information from the System Dashboard Window
The WAAS Central Manager GUI allows you to view general and detailed information about your WAAS network from the System Dashboard window. This section describes the System Dashboard window and contains the following topics:
Figure 16-1 shows the System Dashboard window.
Figure 16-1 System Dashboard Window
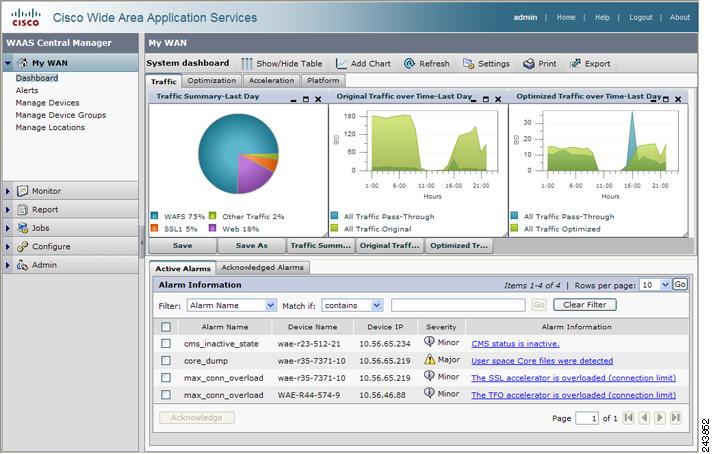
The information displayed in the charts in the System Dashboard window is based on a snapshot of your WAAS network that represents the state of your WAE devices at the end of every two polling periods. You may configure the interval between polls in the WAAS Central Manager GUI (Configure > System Properties > System.monitoring.collectRate). The default polling rate is 300 seconds (5 minutes). Alarms are presented in real time and are independent of the polling rate.
Monitoring Graphs and Charts
The default System Dashboard window contains four tabs that show several graphical displays about the application traffic processed by your WAAS system:
•![]() The Traffic tab contains the following graphical displays:
The Traffic tab contains the following graphical displays:
–![]() Traffic Summary chart—Displays the nine applications with the highest percentage of traffic in the WAAS network for the last hour.
Traffic Summary chart—Displays the nine applications with the highest percentage of traffic in the WAAS network for the last hour.
–![]() Original Traffic over Time graph—Displays the amount of original and pass-through traffic over the last hour.
Original Traffic over Time graph—Displays the amount of original and pass-through traffic over the last hour.
–![]() Optimized Traffic over Time graph—Displays the amount of optimized and pass-through traffic over the last hour.
Optimized Traffic over Time graph—Displays the amount of optimized and pass-through traffic over the last hour.
•![]() The Optimization tab contains the following graphical displays:
The Optimization tab contains the following graphical displays:
–![]() Compression Summary chart—Displays the ten applications with the highest percentage of traffic reduction for the WAAS network for the last hour. The percent calculation excludes pass-through traffic.
Compression Summary chart—Displays the ten applications with the highest percentage of traffic reduction for the WAAS network for the last hour. The percent calculation excludes pass-through traffic.
–![]() Bandwidth Optimization chart—Displays the effective increased bandwidth capacity of the WAN link as a result of WAAS optimization, as a multiple of the actual bandwidth.
Bandwidth Optimization chart—Displays the effective increased bandwidth capacity of the WAN link as a result of WAAS optimization, as a multiple of the actual bandwidth.
–![]() Traffic Volume and Reduction chart—Displays the volume of original and optimized traffic, and the percentage of traffic reduction, for the last hour.
Traffic Volume and Reduction chart—Displays the volume of original and optimized traffic, and the percentage of traffic reduction, for the last hour.
•![]() The Acceleration tab contains the following graphical displays:
The Acceleration tab contains the following graphical displays:
–![]() HTTP: Estimated Time Savings graph—Displays an estimate of the amount of connection setup time saved for HTTP traffic for the last hour due to the HTTP accelerator.
HTTP: Estimated Time Savings graph—Displays an estimate of the amount of connection setup time saved for HTTP traffic for the last hour due to the HTTP accelerator.
–![]() MAPI: Estimated Time Savings graph—Displays an estimate of the amount of response time saved for MAPI traffic for the last hour due to the MAPI accelerator.
MAPI: Estimated Time Savings graph—Displays an estimate of the amount of response time saved for MAPI traffic for the last hour due to the MAPI accelerator.
–![]() NFS: Estimated Time Savings graph—Displays an estimate of the amount of response time saved for NFS traffic for the last hour due to the NFS accelerator.
NFS: Estimated Time Savings graph—Displays an estimate of the amount of response time saved for NFS traffic for the last hour due to the NFS accelerator.
•![]() The Platform tab contains the following graphical display:
The Platform tab contains the following graphical display:
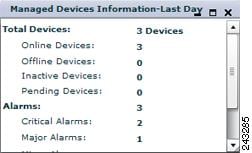
–![]() Managed Devices Information—Displays the total number of WAAS devices in your network, showing the number that are online, offline, inactive, and pending. This display also shows the number of alarms of different severities and the software versions that are deployed in your network.
Managed Devices Information—Displays the total number of WAAS devices in your network, showing the number that are online, offline, inactive, and pending. This display also shows the number of alarms of different severities and the software versions that are deployed in your network.
Numbers shown in charts and graphs are rounded to whole units (KB, MB, or GB), while those displayed in tables are rounded to three decimal places. Data values exported to CSV files are in bytes, so are not rounded.
You can customize the graphical displays and tables that are displayed on the system dashboard. For more information, see the "Customizing a Dashboard or Report" section. Individual charts are described in more detail in the "Chart Descriptions" section.
Much of the device, statistical, and alarm information that is presented in the system dashboard and associated graphs and charts is also available programmatically through the monitoring API. For more information, see the Cisco Wide Area Application Services API Reference.

Note ![]() You must synchronize the clock on each WAE device within 5 minutes of the primary and secondary WAAS Central Managers for statistics to be consistent and reliable. For information on using an NTP server to keep all your WAAS devices synchronized, see the "Configuring NTP Settings" section on page 9-5. Additionally, if the network delay for the Central Manager to receive statistical updates from the WAEs is greater than 5 minutes, statistics aggregation may not operate as expected.
You must synchronize the clock on each WAE device within 5 minutes of the primary and secondary WAAS Central Managers for statistics to be consistent and reliable. For information on using an NTP server to keep all your WAAS devices synchronized, see the "Configuring NTP Settings" section on page 9-5. Additionally, if the network delay for the Central Manager to receive statistical updates from the WAEs is greater than 5 minutes, statistics aggregation may not operate as expected.
Alarm Panel
The alarm panel in the System Dashboard window provides a near real-time view of incoming alarms. The panel refreshes every 2 minutes to reflect updates to the system alarm database.
The alarm panel contains two tabs: Active Alarms and Acknowledged Alarms. The Active Alarms tab displays a dynamic view of all incoming alarms. You may remove an alarm from the active display by acknowledging the alarm. Acknowledged alarms are moved to the Acknowledged Alarms view. You may choose to unacknowledged an alarm and return it to the Active view at any time.
Only Active alarms can be acknowledged in the alarm panel. Pending, Offline, and Inactive alarms cannot be acknowledged in the alarm panel.
For either view, the alarm panel also allows you to filter your view of the alarms in the list. Filtering allows you to find alarms in the list that match the criteria that you set.
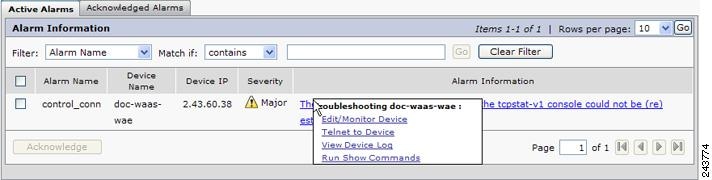
When you roll your mouse over an item under the Alarm Information column, a contextual popup menu appears. The popup menu provides links to the troubleshooting and monitoring windows in the WAAS Central Manager GUI. For more information on these links, see the "Troubleshooting Devices Using Alerts" section.
Figure 16-2 shows the alarm panel in the System Dashboard window.
Figure 16-2 System Dashboard Window Alarm Panel
To acknowledge an active alarm and move it from Active Alarms to the separate Acknowledged Alarms section, follow these steps:
Step 1 ![]() From the System Dashboard window alarm panel, check the check box next to the name of the alarm that you want to acknowledge.
From the System Dashboard window alarm panel, check the check box next to the name of the alarm that you want to acknowledge.
Step 2 ![]() Click the Acknowledge button.
Click the Acknowledge button.
A dialog box pops up that allows you to enter comments about the alarm.
Step 3 ![]() Enter a comment and click OK. Alternatively, click Cancel to return to the Active Alarm panel without completing the acknowledge action.
Enter a comment and click OK. Alternatively, click Cancel to return to the Active Alarm panel without completing the acknowledge action.
Comments enable you to share information about the cause or solution of a particular problem that caused the alarm. The comments field accepts up to 512 characters. You may use any combination of alpha, numeric, and special characters in this field.
The alarm will be moved to the Acknowledged Alarms tab.
To filter and sort alarms displayed in the System Dashboard window alarm panel, follow these steps:
Step 1 ![]() From the Filter drop-down list, choose one of the following filtering options:
From the Filter drop-down list, choose one of the following filtering options:
•![]() Alarm Name
Alarm Name
•![]() Device Name
Device Name
•![]() Device IP
Device IP
•![]() Severity
Severity
•![]() Alarm Information
Alarm Information
Step 2 ![]() From the Match if drop-down list, choose one of the following match conditions:
From the Match if drop-down list, choose one of the following match conditions:
•![]() contains
contains
•![]() starts with
starts with
•![]() ends with
ends with
•![]() is exactly
is exactly
•![]() not exactly
not exactly
•![]() not contain
not contain
•![]() empty
empty
•![]() not empty
not empty
•![]() clear
clear
Step 3 ![]() Enter a match string in the text entry field. This field accepts any alphanumeric text, including special characters.
Enter a match string in the text entry field. This field accepts any alphanumeric text, including special characters.
Step 4 ![]() Click Go.
Click Go.
Step 5 ![]() To sort alarm entries, click a column header.
To sort alarm entries, click a column header.
Entries are sorted alphabetically (in ASCII order). The sort order (ascending or descending) is indicated by an arrow in the column header that points up for ascending order.
Step 6 ![]() To clear the filter, click Clear.
To clear the filter, click Clear.
Device Alarms
Device alarms are associated with device objects and pertain to applications and services running on your WAAS devices. Device alarms are defined by the reporting application or service. Device alarms can also reflect reporting problems between the device and the WAAS Central Manager GUI. Table 16-1 describes the various device alarms that can appear.
Troubleshooting Devices Using Alerts
The WAAS Central Manager GUI allows you to view the alarms on each device and troubleshoot a device in the Troubleshooting Devices window.
To troubleshoot a device from the Troubleshooting Devices window, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, invoke the Troubleshooting Devices window in one of these ways:
From the WAAS Central Manager GUI navigation pane, invoke the Troubleshooting Devices window in one of these ways:
•![]() Choose My WAN > Alerts to view alarms on all devices.
Choose My WAN > Alerts to view alarms on all devices.
•![]() Choose My WAN > Manage Devices and click the device alarm light bar in the Device Status column to view alarms on a single device.
Choose My WAN > Manage Devices and click the device alarm light bar in the Device Status column to view alarms on a single device.
The Troubleshooting Devices window appears, either in the WAAS Central Manager window or as a separate popup window. (See Figure 16-3.)
Figure 16-3 Troubleshooting Devices Window
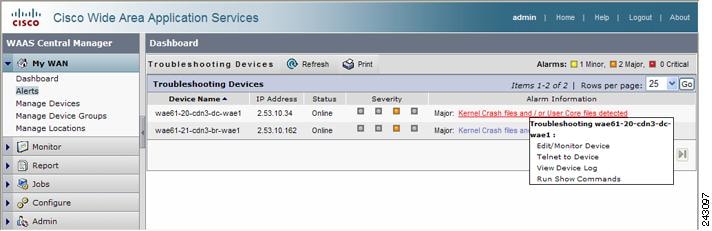
Step 2 ![]() In the Alarm Information column, hold your mouse over an alarm message until the Troubleshooting tools contextual menu appears. The popup menu provides links to the troubleshooting and monitoring windows in the WAAS Central Manager GUI.
In the Alarm Information column, hold your mouse over an alarm message until the Troubleshooting tools contextual menu appears. The popup menu provides links to the troubleshooting and monitoring windows in the WAAS Central Manager GUI.
Step 3 ![]() Choose the troubleshooting tool that you want to use, and click the link. The link takes you to the appropriate window in the WAAS Central Manager GUI. Table 16-2 describes the tools available for device alarms.
Choose the troubleshooting tool that you want to use, and click the link. The link takes you to the appropriate window in the WAAS Central Manager GUI. Table 16-2 describes the tools available for device alarms.
|
|
|
|
|---|---|---|
Update Software |
Choose device, Jobs > Software Update |
Displays Software Update window for this device. Appears only if the device software version is lower than the Central Manager. |
Edit/Monitor Device |
Device Dashboard |
Displays Device Dashboard window for configuration. |
Telnet to Device |
Opens a Telnet window |
Initiates a Telnet session using the device IP address. |
View Device Log |
Choose device, Admin > Logs |
Displays system message logs filtered for this device. |
Run Show Commands |
Choose device, Troubleshoot > CLI Commands > Show Commands |
Displays device show command tool. For more information, see the "Using the show and clear Commands from the WAAS Central Manager GUI" section. |
Viewing Device Information
The WAAS Central Manager GUI allows you to view basic and detailed information about a device from the following two windows:
•![]() Devices Window—Displays a list of all the devices in your WAAS network along with basic information about each device such as the device status and the current software version installed on the device.
Devices Window—Displays a list of all the devices in your WAAS network along with basic information about each device such as the device status and the current software version installed on the device.
•![]() Device Dashboard Window—Displays detailed information about a specific device, such as the installed software version and whether the device is online or offline.
Device Dashboard Window—Displays detailed information about a specific device, such as the installed software version and whether the device is online or offline.
Each window is explained in the sections that follow.
Devices Window
The Devices window lists all the WAAS devices that are registered with the WAAS Central Manager. To view this list, choose My WAN > Manage Devices in the WAAS Central Manager GUI.
Figure 16-4 shows an example of the Devices window.
Figure 16-4 Devices Window
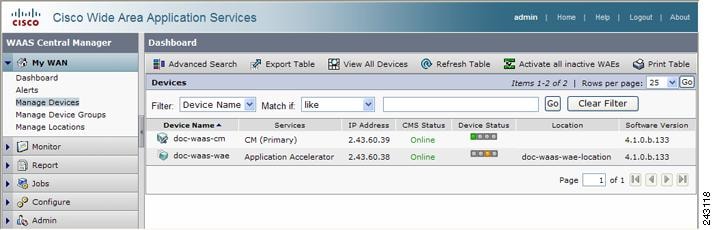
This window displays the following information about each device:
•![]() Services enabled on the device. See Table 16-3 for a description of these services.
Services enabled on the device. See Table 16-3 for a description of these services.
•![]() IP address of the device.
IP address of the device.
•![]() CMS Status (Online, Offline, Pending, or Inactive). For more information about the status, see the "Device Alarms" section.
CMS Status (Online, Offline, Pending, or Inactive). For more information about the status, see the "Device Alarms" section.
•![]() Device Status. The system status reporting mechanism uses four alarm lights to identify problems that need to be resolved. Each light represents a different alarm level as follows:
Device Status. The system status reporting mechanism uses four alarm lights to identify problems that need to be resolved. Each light represents a different alarm level as follows:
–![]() Green—No alarms (the system is in excellent health)
Green—No alarms (the system is in excellent health)
–![]() Yellow—Minor alarms
Yellow—Minor alarms
–![]() Orange—Major alarms
Orange—Major alarms
–![]() Red—Critical alarms
Red—Critical alarms
When you roll your mouse over the alarm light bar, a popup message provides further details about the number of alarms. Click the alarm light bar to troubleshoot the device. For more information, see the "Troubleshooting Devices Using Alerts" section.
•![]() Location associated with the device. For more information about locations, see Chapter 3, "Using Device Groups and Device Locations."
Location associated with the device. For more information about locations, see Chapter 3, "Using Device Groups and Device Locations."
•![]() Software version installed and running on the device.
Software version installed and running on the device.
Any WAE devices that are at a higher software version level than the WAAS Central Manager are shown in red. Also, if the standby WAAS Central Manager has a different version level from the primary WAAS Central Manager, the standby WAAS Central Manager is shown in red.
|
|
|
|---|---|
CM (Primary) |
The device has been enabled as the primary WAAS Central Manager. For information on primary and standby Central Manager devices, see the "Converting a Standby Central Manager to a Primary Central Manager" section on page 15-25. |
CM (Standby) |
The device has been enabled as a standby WAAS Central Manager. For information on primary and standby Central Manager devices, see the "Converting a Standby Central Manager to a Primary Central Manager" section on page 15-25. |
Application Accelerator |
The device has been enabled as an application accelerator. |
Replication Accelerator |
The device has been enabled as a replication accelerator. (Supported only on 4.0.19 or later 4.0.x devices.) |
Edge |
The device has been enabled with legacy WAFS Edge services so it can accelerate data stored on a remote file server. For information on enabling WAFS, see Chapter 11, "Configuring Wide Area File Services." |
Core |
The device has been enabled with legacy WAFS Core services so it can accelerate data stored on a remote file server. For information on enabling WAFS, see Chapter 11, "Configuring Wide Area File Services." |
The device has been enabled with legacy print services so it can act as a print server to branch office clients. For information on setting up a print server, see Chapter 13, "Configuring and Managing WAAS Legacy Print Services." |
Device Dashboard Window
The Device Dashboard window provides detailed information about a WAAS device such as the device model, IP address, interception method, and device-specific charts. (See Figure 16-5.)
To access the Device Dashboard window, go to My WAN > Manage Devices and click the Edit icon next to the device that you want to view.
Figure 16-5 Device Dashboard Window

From the Device Dashboard window, you can perform the following tasks:
•![]() View charts and graphs about the application traffic processed by the selected WAE device. (No charts or graphs are displayed if a WAAS Central Manager device is selected.)
View charts and graphs about the application traffic processed by the selected WAE device. (No charts or graphs are displayed if a WAAS Central Manager device is selected.)
•![]() Customize the charts displayed in the chart panel in the top of the window. For more information, see the "Customizing a Dashboard or Report" section. Individual charts are described in more detail in the "Chart Descriptions" section.
Customize the charts displayed in the chart panel in the top of the window. For more information, see the "Customizing a Dashboard or Report" section. Individual charts are described in more detail in the "Chart Descriptions" section.
•![]() View basic details such as whether the device is online, the device's IP address and hostname, the software version running on the device, and the amount of memory installed in the device.
View basic details such as whether the device is online, the device's IP address and hostname, the software version running on the device, and the amount of memory installed in the device.
•![]() View the device groups to which the device belongs. For more information about device groups, see Chapter 3, "Using Device Groups and Device Locations."
View the device groups to which the device belongs. For more information about device groups, see Chapter 3, "Using Device Groups and Device Locations."
•![]() View the users that are defined on the device and unlock any locked out users. For more information, see the "Viewing and Unlocking Device Users" section.
View the users that are defined on the device and unlock any locked out users. For more information, see the "Viewing and Unlocking Device Users" section.
•![]() Click Update Software to update the software on the device. For more information, see Chapter 15, "Maintaining Your WAAS System."
Click Update Software to update the software on the device. For more information, see Chapter 15, "Maintaining Your WAAS System."
•![]() Click Device GUI to open the WAE Device Manager. For more information on managing a device using this GUI, see Chapter 10, "Using the WAE Device Manager GUI."
Click Device GUI to open the WAE Device Manager. For more information on managing a device using this GUI, see Chapter 10, "Using the WAE Device Manager GUI."
•![]() Click Telnet to establish a Telnet session into the device and issue CLI commands.
Click Telnet to establish a Telnet session into the device and issue CLI commands.
•![]() Assign and unassign the device to baseline groups. For more information, see Chapter 3, "Using Device Groups and Device Locations."
Assign and unassign the device to baseline groups. For more information, see Chapter 3, "Using Device Groups and Device Locations."
Viewing and Unlocking Device Users
To view the users that are defined on a device, go to My WAN > Manage Devices and click the Edit icon next to the device that you want to view. Then from the navigation pane, choose Device Users. (On a Central Manager device, choose CM Users.)
The list of users is displayed in a table that shows the username, number of login failures, maximum number of login failures allowed, and the time of the last failed login. To view the details on a user, click the View icon next to the user.
If a user is locked out because they reached the maximum number of failed login attempts, you can unlock the user by checking the box next to the username and clicking the Unlock button below the table.
Customizing a Dashboard or Report
You can customize the system and device dashboards and any report. The dashboards and reports work the same way. For more information about creating custom reports, see the "Managing Reports" section.
If the charts panel (see Figure 16-6) in the upper part of the window has tabs, you can click other tabs to display other groups of charts.
You can use the minimize, maximize, and close buttons on the top of individual chart panes to minimize, maximize, and close the chart. When a chart is maximized, the middle button changes to a restore button that restores the chart to its smaller size. You can move a chart pane by clicking and dragging its title bar. You can resize a chart by clicking and dragging on the resize control in the lower right corner of the chart pane.
Figure 16-6 Charts Panel
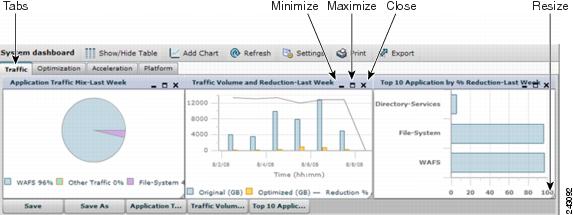
Icons across the top of the dashboard allow you to do the following:
•![]() Show/Hide Table—Shows or hides the table panel in the lower part of the window. For the system dashboard, this is the Alarms table, and for the device dashboard, it is the Device Information table. Dashboard tables are fixed and cannot be changed. You can include different tables in custom reports.
Show/Hide Table—Shows or hides the table panel in the lower part of the window. For the system dashboard, this is the Alarms table, and for the device dashboard, it is the Device Information table. Dashboard tables are fixed and cannot be changed. You can include different tables in custom reports.
•![]() Add Chart—Adds a graphical chart to the charts panel. You can display a maximum of six charts. For details on adding a chart, see the "Adding a Chart" section. Individual charts are described in more detail in the "Chart Descriptions" section.
Add Chart—Adds a graphical chart to the charts panel. You can display a maximum of six charts. For details on adding a chart, see the "Adding a Chart" section. Individual charts are described in more detail in the "Chart Descriptions" section.
•![]() Refresh—Refreshes the charts and tables with new information.
Refresh—Refreshes the charts and tables with new information.
•![]() Settings—Sets the time frame and included applications for the data presented in each chart. For details on these settings, see the "Configuring Chart Settings" section.
Settings—Sets the time frame and included applications for the data presented in each chart. For details on these settings, see the "Configuring Chart Settings" section.
•![]() Print—Prints the charts panel.
Print—Prints the charts panel.
•![]() Export—Exports the chart statistical data to a CSV file. The statistical data shown in charts is rounded to whole units (KB, MB, or GB), while the exported data contains exact byte values.
Export—Exports the chart statistical data to a CSV file. The statistical data shown in charts is rounded to whole units (KB, MB, or GB), while the exported data contains exact byte values.
Buttons below the charts panel allow you to do the following:
•![]() Save—Saves the dashboard or report with its current settings. The next time you view it, it is displayed with these settings.
Save—Saves the dashboard or report with its current settings. The next time you view it, it is displayed with these settings.
•![]() Save As—Saves the report with its current settings under a new name.
Save As—Saves the report with its current settings under a new name.
•![]() Chart Names—Displays or hides the named chart.
Chart Names—Displays or hides the named chart.
Adding a Chart
To add a chart to a dashboard or report, follow these steps:
Step 1 ![]() From the dashboard or report chart panel, click the Add Chart icon in the taskbar. The Add Chart window is displayed, as shown in Figure 16-7.
From the dashboard or report chart panel, click the Add Chart icon in the taskbar. The Add Chart window is displayed, as shown in Figure 16-7.
Figure 16-7 Adding a Chart

Step 2 ![]() Expand any of the chart categories by clicking on the plus sign next to the category.
Expand any of the chart categories by clicking on the plus sign next to the category.
Step 3 ![]() Check the box next to each chart that you want to display. Individual charts are described in more detail in the "Chart Descriptions" section.
Check the box next to each chart that you want to display. Individual charts are described in more detail in the "Chart Descriptions" section.
Remember that a report can contain a maximum of six charts.
Step 4 ![]() Click Add.
Click Add.
If you want to delete a chart from a dashboard or report, click the Close button on the chart and save the report.
Configuring Chart Settings
To configure the data presented in a chart, follow these steps:
Step 1 ![]() From the dashboard or report chart panel, click the Settings icon in the taskbar. The Settings window is displayed, as shown in Figure 16-8.
From the dashboard or report chart panel, click the Settings icon in the taskbar. The Settings window is displayed, as shown in Figure 16-8.
Figure 16-8 Chart Settings
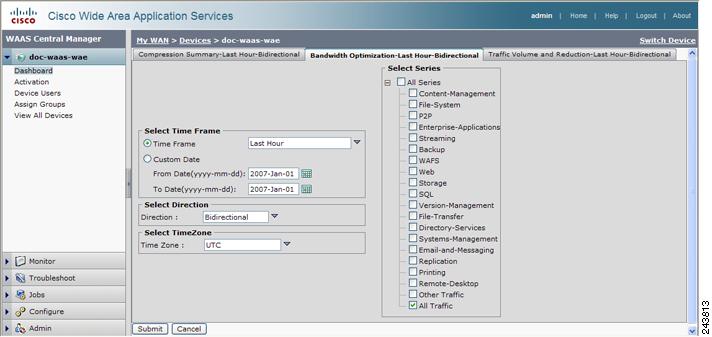
Step 2 ![]() Click on the tab corresponding to the chart that you want to change.
Click on the tab corresponding to the chart that you want to change.
Step 3 ![]() In the Select Time Frame area, choose a time frame for the chart. Choose one of these options by clicking on the appropriate radio button:
In the Select Time Frame area, choose a time frame for the chart. Choose one of these options by clicking on the appropriate radio button:
•![]() Time Frame—Choose one of several common time frames from the drop-down list:
Time Frame—Choose one of several common time frames from the drop-down list:
–![]() Last Hour—Displays data for the past hour (in five-minute intervals). You can change this interval using the System.monitoring.collectRate configuration setting described in the "Modifying the Default System Configuration Properties" section on page 9-17.
Last Hour—Displays data for the past hour (in five-minute intervals). You can change this interval using the System.monitoring.collectRate configuration setting described in the "Modifying the Default System Configuration Properties" section on page 9-17.
–![]() Last Day—Displays data for the past day (in hourly intervals).
Last Day—Displays data for the past day (in hourly intervals).
–![]() Last Week—Displays data for the past week (in daily intervals).
Last Week—Displays data for the past week (in daily intervals).
–![]() Last Month—Displays data for the past month (in daily intervals).
Last Month—Displays data for the past month (in daily intervals).
•![]() Custom Date—Enter starting and ending dates in the From Date and To Date fields. Click the calendar icon to choose dates from a popup calendar.
Custom Date—Enter starting and ending dates in the From Date and To Date fields. Click the calendar icon to choose dates from a popup calendar.
Step 4 ![]() From the Direction drop-down list, choose one of the following options:
From the Direction drop-down list, choose one of the following options:
•![]() Bidirectional—Includes LAN to WAN traffic as well as WAN to LAN traffic traveling through this WAAS device.
Bidirectional—Includes LAN to WAN traffic as well as WAN to LAN traffic traveling through this WAAS device.
•![]() Inbound—Includes traffic from the WAN to the client through this WAAS device
Inbound—Includes traffic from the WAN to the client through this WAAS device
•![]() Outbound—Includes traffic traveling from a client to the WAN through this WAAS device.
Outbound—Includes traffic traveling from a client to the WAN through this WAAS device.
The Select Direction area appears only when you are configuring certain device level charts.
Step 5 ![]() From the Time Zone drop-down list, choose one of the following options:
From the Time Zone drop-down list, choose one of the following options:
•![]() UTC—Sets the time zone of the report to UTC.
UTC—Sets the time zone of the report to UTC.
•![]() CDM Local Time—Sets the time zone of the report to the time zone of the WAAS Central Manager.
CDM Local Time—Sets the time zone of the report to the time zone of the WAAS Central Manager.
•![]() CE Local Time—Sets the time zone of the report to the time zone of the WAE device. This option appears only when you are configuring a device level chart.
CE Local Time—Sets the time zone of the report to the time zone of the WAE device. This option appears only when you are configuring a device level chart.
Step 6 ![]() In the Select Series area, click the plus sign to expand the All Series list. Place a check mark next to the applications whose statistics you want to include in the chart data. This optional area applies only to specific chart types. To include all applications, choose All Traffic.
In the Select Series area, click the plus sign to expand the All Series list. Place a check mark next to the applications whose statistics you want to include in the chart data. This optional area applies only to specific chart types. To include all applications, choose All Traffic.
Step 7 ![]() Click Submit.
Click Submit.
Chart Descriptions
This section describes the charts that you can choose to include in a dashboard or report. The following categories of reports are available:
Traffic Analysis Charts
This section describes these charts:
Traffic Summary
The Traffic Summary chart (see Figure 16-9) displays the top nine applications with the highest percent of traffic. Each section in the pie chart represents an application as a percent of the total traffic on your network or device. Nonclassified, nonmonitored, and applications with less than 2 percent of the total traffic are grouped together into the Other category.
Figure 16-9 Traffic Summary Chart
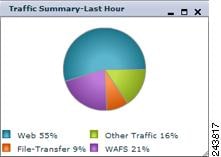
Formula:
(App Traffic/ Total Traffic) * 100
App Traffic is the Original traffic (Original Excluding Pass-Through + Pass-Through) flowing for an application.
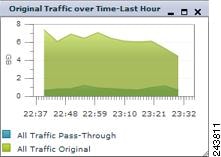
Original Traffic Over Time
The Original Traffic over Time chart (see Figure 16-10) displays a graph of the amount of original and pass-through traffic. You can choose which applications to include; the default is all traffic. The chart in the display is an area chart; the pass-through traffic data is indicated by the color blue and is shown behind the optimized data, which is indicated by the color green.
Figure 16-10 Original Traffic Over Time Chart
Optimization Charts
This section describes these charts:
•![]() Compression by Application Over Time
Compression by Application Over Time
Compression Summary
The Compression Summary chart (see Figure 16-11) displays a bar chart of the percentage of traffic reduction (excluding pass-through traffic) for the top ten applications with the highest amount of traffic.
Figure 16-11 Compression Summary Chart
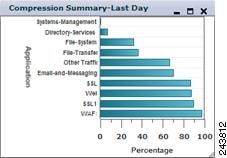
Formula:
% Reduction Excluding Pass-Through = (Original Excluding Pass-Through - Optimized) / (Original Excluding Pass-Through)
Compression Over Time
The Compression over Time chart (see Figure 16-12) displays a a graph of the percentage of total traffic that was reduced by using the WAAS optimization techniques. The chart in the display is an area chart; all traffic excluding pass-through is indicated by the color blue and is shown behind all traffic including pass-through, which is indicated by the color green.
Figure 16-12 Compression Over Time Chart
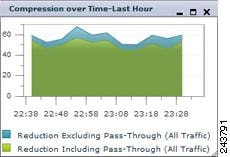
Formula:
% Reduction Including Pass-Through = (Original Excluding Pass-Through - Optimized) / (Original Excluding Pass-Through + Pass-Through)
% Reduction Excluding Pass-Through = (Original Excluding Pass-Through - Optimized) / (Original Excluding Pass-Through)
Compression by Application Over Time
The Compression by Application over Time chart (see Figure 16-13) displays a graph of the percent of total traffic that was reduced on the WAE device using the WAAS optimization techniques. This chart excludes pass-through traffic in the results. You can choose which applications to include; the default is all traffic.
Figure 16-13 Compression By Application Over Time Chart
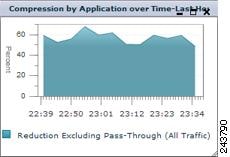
Formula:
% Reduction Excluding PT = (Original Excl Pass-Through - Optimized) / (Original Excl Pass-Through)
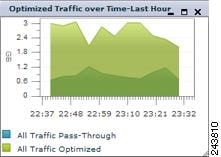
Optimized Traffic Over Time
The Optimized Traffic over Time chart (see Figure 16-14) displays a graph of the amount of optimized and pass-through traffic processed on the WAE device. The chart in the display is an area chart; the pass-through traffic data is indicated by the color blue and is shown behind the optimized data, which is indicated by the color green. The traffic units (bytes, KB, MB, or GB) at the left side depend upon the range.
Figure 16-14 Optimized Traffic Over Time Chart
Traffic Volume and Reduction
The Traffic Volume and Reduction chart (see Figure 16-15) displays the amount of original and optimized traffic in a bar chart, along with the percentage of traffic reduction (excluding pass-through traffic) as a line. The traffic units (bytes, KB, MB, or GB) at the left side depend upon the range. The percentage of traffic reduction units are shown at the right side of the chart.
Figure 16-15 Traffic Volume and Reduction Chart
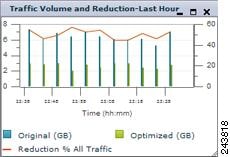
Formula:
% Reduction Excluding PT = (Original - Optimized - Pass-Through) / (Original - Pass-Through)
Bandwidth Optimization
The Bandwidth Optimization chart (see Figure 16-16) displays the effective increased bandwidth capacity of the WAN link as a result of WAAS optimization, as a value between 1X (times) and 100X. You can choose which applications to include; the default is all traffic.
Figure 16-16 Bandwidth Optimization Chart
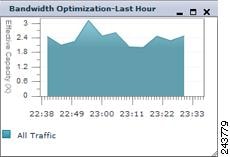
Formula:
Effective WAN Capacity = 1 / (1-% Reduction Excluding Pass-Through)
% Reduction Excluding Pass-Through = (Original Excluding Pass-Through - Optimized) / (Original Excluding Pass-Through)
Acceleration Charts
This section describes these charts:
•![]() HTTP
HTTP
•![]() CIFS
CIFS
•![]() MAPI
MAPI
•![]() NFS
NFS
•![]() SSL
SSL
HTTP
This section describes these charts:
HTTP: Estimated Time Savings
The HTTP Estimated Time Savings chart (see Figure 16-17) displays a graph of the estimated percentage of response time saved by the HTTP accelerator due to fast connection reuse.
Figure 16-17 HTTP Estimated Time Savings Chart

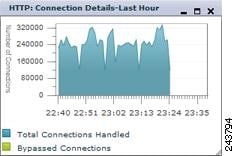
HTTP: Connection Details
The HTTP Connection Details chart (see Figure 16-18) displays the HTTP session connection statistics, showing the total number of connections handled with the number of unaccelerated (bypassed) connections. The chart in the display is an area chart; the total number of connections handled is indicated by the color blue and is shown behind the number of bypassed connections, which is indicated by the color green.
Figure 16-18 HTTP Connection Details Chart
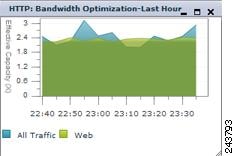
HTTP: Bandwidth Optimization
The HTTP Bandwidth Optimization chart (see Figure 16-19) displays the effective bandwidth capacity of the WAN link as a result of HTTP acceleration, as a multiplier of its base capacity. The chart in the display is an area chart; data for all traffic is indicated by the color blue and is shown behind web (HTTP) traffic, which is indicated by the color green.
If the chart has no data, monitoring may be disabled for the application definition that includes this type of traffic. Check that monitoring is enabled for the Web application.
Figure 16-19 HTTP Bandwidth Optimization Chart
CIFS
This section describes these charts:
•![]() CIFS: Client Average Throughput
CIFS: Client Average Throughput
•![]() CIFS: Connected CIFS Core Count
CIFS: Connected CIFS Core Count
•![]() CIFS: CIFS Edge-CIFS Core Traffic
CIFS: CIFS Edge-CIFS Core Traffic
•![]() CIFS: Connected CIFS Edge Count
CIFS: Connected CIFS Edge Count
All CIFS charts are available only at the device level and the specific charts available depend on the mode of the device: transparent CIFS accelerator mode, WAFS legacy mode as an Edge device, or WAFS legacy mode as a Core device.
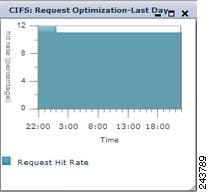
CIFS: Request Optimization
The CIFS Request Optimization chart (see Figure 16-20) displays the percentage of requests that are served locally from the CIFS cache. This chart is available only for a device that is operating in transparent CIFS accelerator mode or WAFS legacy mode as an Edge device.
Figure 16-20 CIFS Request Optimization Chart
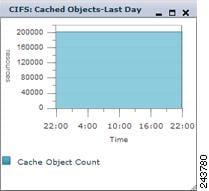
CIFS: Cached Objects
The CIFS Cached Objects chart (see Figure 16-21) displays the number of objects in the CIFS cache. This chart is available only for a device that is operating in transparent CIFS accelerator mode or WAFS legacy mode as an Edge device.
Figure 16-21 CIFS Cached Objects Chart
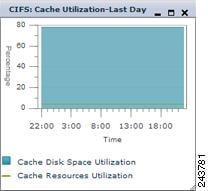
CIFS: Cache Utilization
The CIFS Cache Utilization chart (see Figure 16-22) displays the utilization percentage of the CIFS cache. This chart is available only for a device that is operating in transparent CIFS accelerator mode or WAFS legacy mode as an Edge device.
Figure 16-22 CIFS Cache Utilization Chart
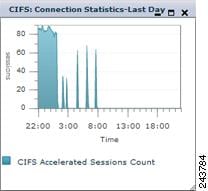
CIFS: Connection Statistics
The CIFS Connection Statistics chart (see Figure 16-23) displays the number of CIFS accelerated sessions. This chart is available only for a device that is operating in transparent CIFS accelerator mode or WAFS legacy mode as an Edge device.
Figure 16-23 CIFS Connection Statistics Chart
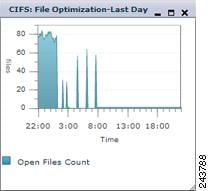
CIFS: File Optimization
The CIFS File Optimization chart (see Figure 16-24) displays the number of open CIFS files. This chart is available only for a device that is operating in transparent CIFS accelerator mode or WAFS legacy mode as an Edge device.
Figure 16-24 CIFS File Optimization Chart
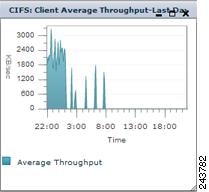
CIFS: Client Average Throughput
The CIFS Client Average Throughput chart (see Figure 16-25) displays the average throughput (in KB/second) between the WAAS device and its clients. This chart is available only for a device that is operating in transparent CIFS accelerator mode or WAFS legacy mode as an Edge device.
Figure 16-25 CIFS Client Average Throughput Chart
CIFS: Connected CIFS Core Count
The CIFS Connected CIFS Core Count chart (see Figure 16-26) displays the number of connected CIFS Core devices. This chart is available only for a device that is operating in WAFS legacy mode as an Edge device.
Figure 16-26 CIFS Connected CIFS Core Count Chart
CIFS: CIFS Edge-CIFS Core Traffic
The CIFS Edge-CIFS Core Traffic chart (see Figure 16-27) displays the amount of traffic between the Edge device and the CIFS core devices that are connected to it. This chart is available only for a device that is operating in WAFS legacy mode as an Edge device.
Figure 16-27 CIFS Edge-CIFS Core Traffic Chart
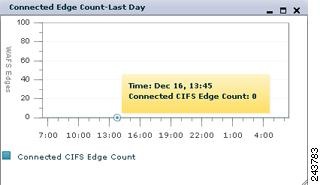
CIFS: Connected CIFS Edge Count
The CIFS Connected CIFS Edge Count chart (see Figure 16-28) displays the number of connected CIFS Edge devices. This chart is available only for a device that is operating in WAFS legacy mode as a Core device.
Figure 16-28 CIFS Connected CIFS Edge Count Chart
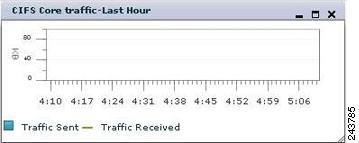
CIFS: CIFS Core Traffic
The CIFS Core Traffic chart (see Figure 16-29) displays the amount of traffic between the Core device and the CIFS Edge devices that are connected to it. This chart is available only for a device that is operating in WAFS legacy mode as a Core device.
Figure 16-29 CIFS Core Traffic Chart
MAPI
This section describes these charts:
•![]() MAPI: Response Time Optimization
MAPI: Response Time Optimization
•![]() MAPI: Acceleration Bypass Reason
MAPI: Acceleration Bypass Reason
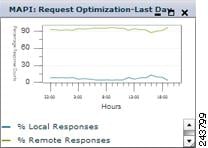
MAPI: Request Optimization
The MAPI Request Optimization chart (see Figure 16-30) displays the percentage of local and remote MAPI command responses. A local response is one that is sent to the client without waiting for a response from the peer WAE. A remote response comes from the remote server.
Figure 16-30 MAPI Request Optimization Chart
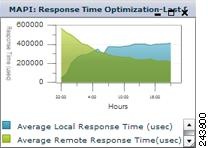
MAPI: Response Time Optimization
The MAPI Response Time Optimization chart (see Figure 16-31) compares the average time (in microseconds) used for local and remote MAPI responses.
Figure 16-31 MAPI Response Time Optimization Chart
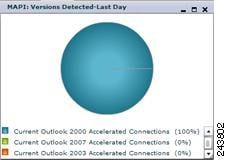
MAPI: Versions Detected
The MAPI Versions Detected pie chart (see Figure 16-32) displays the number of connections detected from different versions (2000, 2003, 2007) of the Microsoft Outlook client.
Figure 16-32 MAPI Versions Detected Chart
MAPI: Estimated Time Savings
The MAPI Estimated Time Savings chart (see Figure 16-33) displays a graph of the estimated percentage of response time saved by the MAPI accelerator.
Figure 16-33 MAPI Estimated Time Savings Chart

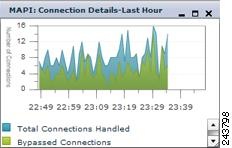
MAPI: Connection Details
The MAPI Connection Details chart (see Figure 16-34) displays the MAPI session connection statistics, showing the total number of connections handled with the number of unaccelerated (bypassed) connections. The chart in the display is an area chart; the total number of connections handled is indicated by the color blue and is shown behind the number of bypassed connections, which is indicated by the color green.
Figure 16-34 MAPI Connection Details Chart
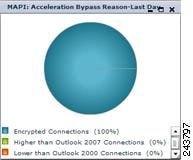
MAPI: Acceleration Bypass Reason
The MAPI Acceleration Bypass Reason pie chart (see Figure 16-35) displays the reasons that MAPI traffic is not accelerated: encrypted connections, Outlook version is higher than version 2007, and Outlook version is lower than version 2000.
Figure 16-35 MAPI Acceleration Bypass Reason Chart
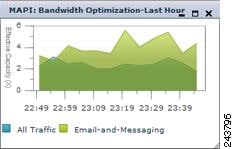
MAPI: Bandwidth Optimization
The MAPI Bandwidth Optimization chart (see Figure 16-36) displays the effective bandwidth capacity of the WAN link as a result of MAPI acceleration, as a multiplier of its base capacity. The chart in the display is an area chart; data for all traffic is indicated by the color blue and is shown behind e-mail and messaging (MAPI) traffic, which is indicated by the color green.
If the chart has no data, monitoring may be disabled for the application definition that includes this type of traffic. Check that monitoring is enabled for the Email-and-Messaging application.
Figure 16-36 MAPI Bandwidth Optimization Chart
NFS
This section describes these charts:
•![]() NFS: Response Time Optimization
NFS: Response Time Optimization
•![]() NFS: Acceleration Bypass Reason
NFS: Acceleration Bypass Reason
NFS: Request Optimization
The NFS Request Optimization chart (see Figure 16-37) displays the percentage of local and remote NFS command responses. A local response is one that is sent to the client without waiting for a response from the peer WAE. A remote response comes from the remote server.
Figure 16-37 NFS Request Optimization Chart

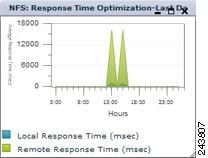
NFS: Response Time Optimization
The NFS Response Time Optimization chart (see Figure 16-38) compares the average time (in milliseconds) used for local and remote NFS responses.
Figure 16-38 NFS Response Time Optimization Chart
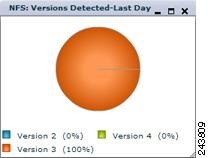
NFS: Versions Detected
The NFS Versions Detected pie chart (see Figure 16-39) displays the number of NFS messages detected for each NFS version (2, 3, and 4). The NFS accelerator works with NFS version 3 traffic, so you will want to see this type of traffic for best results.
Figure 16-39 NFS Versions Detected Chart
NFS: Estimated Time Savings
The NFS Estimated Time Savings chart (see Figure 16-40) displays a graph of the estimated percentage of response time saved by the NFS accelerator.
Figure 16-40 NFS Estimated Time Savings Chart

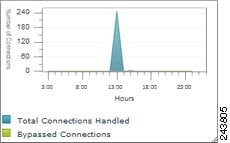
NFS: Connection Details
The NFS Connection Details chart (see Figure 16-41) displays the NFS session connection statistics, showing the total number of connections handled with the number of unaccelerated (bypassed) connections. The chart in the display is an area chart; the total number of connections handled is indicated by the color blue and is shown behind the number of bypassed connections, which is indicated by the color green.
Figure 16-41 NFS Connection Details Chart
NFS: Acceleration Bypass Reason
The NFS Acceleration Bypass Reason pie chart (see Figure 16-42) displays the reasons that NFS traffic is not accelerated: unknown authentication flavor or unknown NFS version.
Figure 16-42 NFS Acceleration Bypass Reason Chart
NFS: Bandwidth Optimization
The NFS Bandwidth Optimization chart (see Figure 16-43) displays the effective bandwidth capacity of the WAN link as a result of NFS acceleration, as a multiplier of its base capacity. The chart in the display is an area chart; data for all traffic is indicated by the color blue and is shown behind file system (NFS) traffic, which is indicated by the color green.
If the chart has no data, monitoring may be disabled for the application definition that includes this type of traffic. Check that monitoring is enabled for the File-System application.
Figure 16-43 NFS Bandwidth Optimization Chart

Video
This section describes these charts:
•![]() Video: Acceleration Bypass Reason
Video: Acceleration Bypass Reason
•![]() Video: Bandwidth Optimization
Video: Bandwidth Optimization
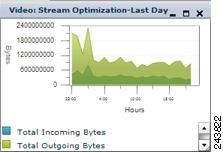
Video: Stream Optimization
The Video Stream Optimization chart (see Figure 16-44) compares the amounts of incoming and outgoing traffic. The chart in the display is an area chart; the total incoming bytes is indicated by the color blue and is shown behind the total outgoing bytes, which is indicated by the color green.
Figure 16-44 Video Stream Optimization Chart
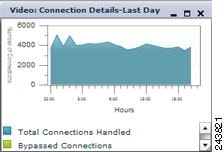
Video: Connection Details
The Video Connection Details chart (see Figure 16-45) displays the video session connection statistics, showing the total number of connections handled with the number of unaccelerated (bypassed) connections. The chart in the display is an area chart; the total number of connections handled is indicated by the color blue and is shown behind the number of bypassed connections, which is indicated by the color green.
Figure 16-45 Video Connection Details Chart
Video: Acceleration Bypass Reason
The Video Acceleration Bypass Reason pie chart (see Figure 16-46) displays the reasons that video traffic is not accelerated: Windows Media VOD, aggregate bitrate overload, other reasons, stream bitrate overload, session count overload, or unsupported transmission type (this means unsupported transport, unsupported player, or unsupported protocol).
Figure 16-46 Video Acceleration Bypass Reason Chart
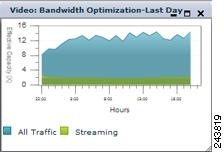
Video: Bandwidth Optimization
The Video Bandwidth Optimization chart (see Figure 16-47) displays the effective bandwidth capacity of the WAN link as a result of video acceleration, as a multiplier of its base capacity. The chart in the display is an area chart; data for all traffic is indicated by the color blue and is shown behind streaming video traffic, which is indicated by the color green.
If the chart has no data, monitoring may be disabled for the application definition that includes this type of traffic. Check that monitoring is enabled for the Streaming application.
Figure 16-47 Video Bandwidth Optimization Chart
SSL
This section describes these charts:
•![]() SSL: Acceleration Bypass Reason
SSL: Acceleration Bypass Reason
SSL: Acceleration Bypass Reason
The SSL Acceleration Bypass Reason pie chart (see Figure 16-48) displays the reasons that SSL traffic is not accelerated: version mismatch, cipher mismatch, revocation failure, certificate verification failure, other failure, and non-SSL traffic.
Figure 16-48 SSL Acceleration Bypass Reason Chart
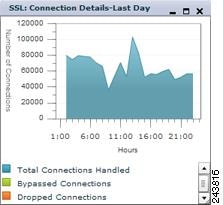
SSL: Connection Details
The SSL Connection Details chart (see Figure 16-49) displays the SSL session connection statistics, showing the total number of connections handled, the number of unaccelerated (bypassed) connections, and the number of dropped connections. The chart in the display is an area chart; the total number of connections handled is indicated by the color blue and is shown behind the number of bypassed connections in green, which is shown behind the number of dropped connections in orange.
Figure 16-49 SSL Connection Details Chart
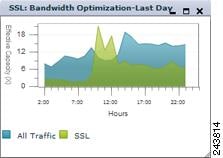
SSL: Bandwidth Optimization
The SSL Bandwidth Optimization chart (see Figure 16-50) displays the effective bandwidth capacity of the WAN link as a result of SSL acceleration, as a multiplier of its base capacity. The chart in the display is an area chart; data for all traffic is indicated by the color blue and is shown behind SSL traffic, which is indicated by the color green.
If the chart has no data, monitoring may be disabled for the application definition that includes this type of traffic. Check that monitoring is enabled for the SSL application.
Figure 16-50 SSL Bandwidth Optimization Chart
Platform Charts
This section describes these charts:
Managed Devices Information
The Managed Devices Information chart (see Figure 16-51) displays information about the number of devices managed by the WAAS Central Manager, the device status, number of alarms, and software versions.
Figure 16-51 Managed Devices Information Chart
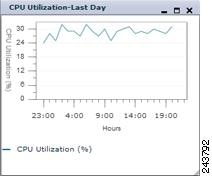
CPU Utilization
The CPU Utilization chart (see Figure 16-52) displays the percentage of CPU utilization for the device. This chart is available only when a specific WAAS device is selected.
Figure 16-52 CPU Utilization Chart
Using Predefined Reports to Monitor WAAS
The WAAS Central Manager includes a number of predefined reports that you can use to monitor the system operation. These reports are available in the Monitor drawer in the navigation pane. The reports consist of a combination of specific charts and graphs and a statistical table displayed in the lower part of the window.
You can customize these predefined reports by editing them with the Manage Report function available in the Report drawer, as described in the "Viewing and Editing Reports" section.
The following predefined reports are available at the WAAS system level and at the WAE device level:
•![]() Optimization
Optimization
•![]() Acceleration
Acceleration
The following predefined reports are available only at the device level:
•![]() Optimization
Optimization
–![]() Connections Statistics Report
Connections Statistics Report
•![]() Acceleration
Acceleration
•![]() Platform
Platform
Traffic Summary Report
The Traffic Summary report (see Figure 16-53) displays a summary of all traffic.
Figure 16-53 Traffic Summary Report

The following charts are included:
The Traffic Summary table is displayed below the charts. Each row in the table displays the total traffic information for each device that is registered to this Central Manager. The device names are shown in the first column. The formulas used to calculate the values are listed in Table 16-4.
For some values, different formulas are used at the system and device levels, and these formulas are noted in the table. The terms used in the table are defined as follows:
•![]() Original Inbound—Traffic that is entering the WAE from the LAN (clients) and needs to be optimized before being sent out on the WAN to a peer WAE.
Original Inbound—Traffic that is entering the WAE from the LAN (clients) and needs to be optimized before being sent out on the WAN to a peer WAE.
•![]() Original Outbound—Traffic that is exiting the WAE to the LAN (clients) after being received on the WAN from a peer WAE.
Original Outbound—Traffic that is exiting the WAE to the LAN (clients) after being received on the WAN from a peer WAE.
•![]() Optimized Inbound—Traffic that is entering the WAE from the WAN and needs to be processed (deoptimized) before being sent out on the LAN to clients.
Optimized Inbound—Traffic that is entering the WAE from the WAN and needs to be processed (deoptimized) before being sent out on the LAN to clients.
•![]() Optimized Outbound—Traffic that is exiting the WAE to the WAN and a peer WAE after being optimized.
Optimized Outbound—Traffic that is exiting the WAE to the WAN and a peer WAE after being optimized.
•![]() Pass-Through—Traffic that is being passed through the WAE and not optimized.
Pass-Through—Traffic that is being passed through the WAE and not optimized.
To get the statistics at the system and device group levels, the Original Inbound, Original Outbound, Optimized Inbound, Optimized Outbound, Pass-through Client and Pass-through Server bytes of all devices are added together. The values Reduction % (incl. pass-through), Reduction % (excl. pass-through), and Effective Capacity are calculated using these added values of all devices.
Traffic Optimization Report
The Traffic Optimization report displays the application traffic mix.
The following charts are included:
The Application Traffic Mix table is displayed below the charts. Each row in the table displays the total traffic information for each application. The formulas used to calculate the values are listed in Table 16-4.
Optimization Summary Report
The Optimization Summary report displays the pass-through traffic mix report.
The following charts are included:
•![]() Compression by Application Over Time
Compression by Application Over Time
The Pass-Through Traffic Mix table is displayed below the charts. Each row in the table displays the pass-through traffic information for each application. The formulas used to calculate the values are listed in Table 16-4.
HTTP Acceleration Report
The HTTP Acceleration report displays the HTTP acceleration statistics.
The following charts are included:
The HTTP Acceleration Statistics table is displayed below the charts. Each row in the table displays statistical information for each device that is registered to this Central Manager. The device names are shown in the first column. The % Time Saved value is calculated by the following formula applied to the aggregated samples:
% Time Saved = Total Time Saved / (Total Time Saved + Total Round Trip Time For All Connections)
Video Acceleration Report
The Video Acceleration report displays the video acceleration statistics.
The following charts are included on two tabs:
•![]() Summary tab:
Summary tab:
–![]() Video: Bandwidth Optimization
Video: Bandwidth Optimization
•![]() Details tab:
Details tab:
–![]() Video: Acceleration Bypass Reason
Video: Acceleration Bypass Reason
The Video Acceleration Statistics table is displayed below the charts. Each row in the table displays statistical information for each device that is registered to this Central Manager. The device names are shown in the first column.
SSL Acceleration Report
The SSL Acceleration report displays the SSL acceleration statistics.
The following charts are included:
•![]() SSL: Acceleration Bypass Reason
SSL: Acceleration Bypass Reason
The SSL Acceleration Statistics table is displayed below the charts. Each row in the table displays statistical information for each device that is registered to this Central Manager. The device names are shown in the first column.
MAPI Acceleration Report
The MAPI Acceleration report displays the MAPI acceleration statistics.
The following charts are included on two tabs:
•![]() Summary tab:
Summary tab:
•![]() Details tab:
Details tab:
–![]() MAPI: Response Time Optimization
MAPI: Response Time Optimization
–![]() MAPI: Acceleration Bypass Reason
MAPI: Acceleration Bypass Reason
The MAPI Acceleration Statistics table is displayed below the charts. Each row in the table displays statistical information for each device that is registered to this Central Manager. The device names are shown in the first column. The % Time Saved value is calculated by the following formula applied to the aggregated samples:
% Time Saved = (Down - Up) * 100 / (Down)
If(Down != 0)
where:
Down = (New local request count + New remote request count) * Avg. local response time
Up = ((New local request count * Avg. local response time) + (New remote request count * Avg. remote response time))
NFS Acceleration Report
The NFS Acceleration report displays the NFS acceleration statistics.
The following charts are included on two tabs:
•![]() Summary tab:
Summary tab:
•![]() Details tab:
Details tab:
–![]() NFS: Response Time Optimization
NFS: Response Time Optimization
–![]() NFS: Acceleration Bypass Reason
NFS: Acceleration Bypass Reason
The NFS Acceleration Statistics table is displayed below the charts. Each row in the table displays statistical information for each device that is registered to this Central Manager. The device names are shown in the first column. The % Time Saved value is calculated by the following formula applied to the aggregated samples:
% Time Saved = (Down - Up) * 100 / (Down)
If(Down != 0)
where:
Down = (New local request count + Remote replies) * Avg. local response time
Up = ((New local request count * Avg. local response time) + (Remote replies * Avg. remote response time))
Topology Report
The Topology report at the system level displays a topology map that shows a graphical representation of all the connections between the WAE devices.
The topology map uses blue squares to show connections between devices. Use the legend to the right of the grid to associate the device name with the number that appears at the top of the grid. Use the drop-down lists at the top of the window to perform the following tasks:
•![]() Display connections between your various locations instead of between devices.
Display connections between your various locations instead of between devices.
•![]() Sort the grid by the number of connections instead of by device name.
Sort the grid by the number of connections instead of by device name.
Click the View icon next to the WAE to view a list of peer devices for a specific WAE. The TFO Peer List window appears, which is the same as the device level Topology report.
At the device level, the Topology report lists all the peer devices connected to a specific WAE so that you can see the relationship between devices in your WAAS network. The TFO Peer List window displays information about each peer device involved in optimized connections with this WAE. To go to the system level Topology report, click the Topology icon in the taskbar.
If a peer device is not registered with the WAAS Central Manager, the message "Unknown, this peer is not being managed by CM" is shown for the name and "Unknown" is displayed for the IP address.

Note ![]() The WAAS Central Manager device does not have any peers because it does not participate with any WAEs to optimize traffic. For this reason, the topology feature is not available on the WAAS Central Manager device.
The WAAS Central Manager device does not have any peers because it does not participate with any WAEs to optimize traffic. For this reason, the topology feature is not available on the WAAS Central Manager device.
Connections Statistics Report
The Connections Statistics report displays a connection summary table for the device and is available at the device level only. The table displays all of the TCP connections handled by the device and corresponds to the show statistics connection EXEC mode command. (See Figure 16-54.)
Figure 16-54 Device Connections Summary Table
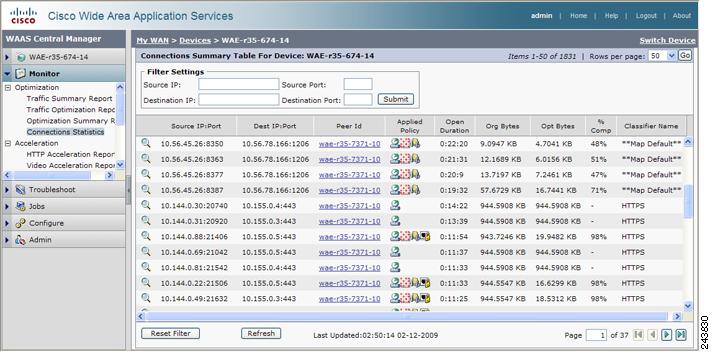
This window displays the following information about each connection:
•![]() Source IP address and port
Source IP address and port
•![]() Destination IP address and port
Destination IP address and port
•![]() Peer ID—Hostname of the peer device
Peer ID—Hostname of the peer device
•![]() Applied Policy (icons represent TFO, DRE, LZ, and an application accelerator, respectively)
Applied Policy (icons represent TFO, DRE, LZ, and an application accelerator, respectively)
•![]() Open Duration—Number of hours, minutes, and seconds that the connection has been open
Open Duration—Number of hours, minutes, and seconds that the connection has been open
•![]() Total number of original bytes
Total number of original bytes
•![]() Total number of optimized bytes
Total number of optimized bytes
•![]() Percentage of compression
Percentage of compression
•![]() Classifier name
Classifier name
The data in the Connections Summary Table is retrieved from the device one time when you view the window for the first time.
Click the Refresh button at the bottom of the window to refresh the data in the Connections Summary Table.
From the Connections Summary Table for Device window, you may perform the following tasks:
•![]() Apply filter settings to display particular connections based on criteria that you choose.
Apply filter settings to display particular connections based on criteria that you choose.
•![]() View connection details.
View connection details.
•![]() Click the Reset Filter button to reset the filter options and refresh the table.
Click the Reset Filter button to reset the filter options and refresh the table.
Click the Details icon next to the connection entry in the summary table to view connection details. The Connection Details window appears. This window contains connection addresses, port information, policy information, and traffic statistics. The Connection Details window also displays graphs that plot real-time traffic statistics and are refreshed every two seconds. (See Figure 16-55.)
Figure 16-55 Connection Details
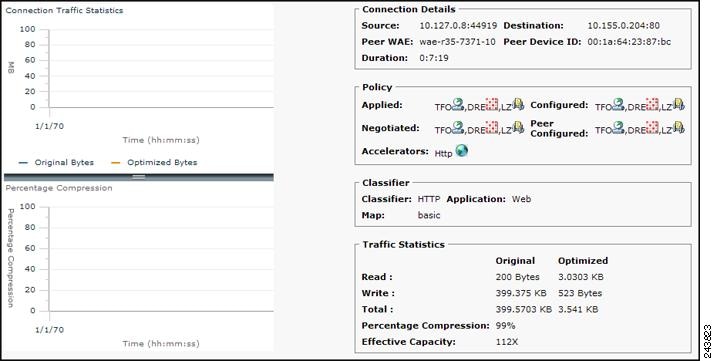

Note ![]() If the value for Percentage Compression is negative, the Percentage Compression and Effective Capacity values do not appear.
If the value for Percentage Compression is negative, the Percentage Compression and Effective Capacity values do not appear.
CIFS Acceleration Report
The CIFS Acceleration report displays the CIFS acceleration statistics and is available at the device level only. Different charts are available depending on the CIFS accelerator mode (transparent CIFS accelerator, legacy CIFS Edge, or legacy CIFS Core).
For a transparent CIFS accelerator device, the following charts are included on two tabs:
•![]() Summary tab:
Summary tab:
•![]() Details tab:
Details tab:
–![]() CIFS: Client Average Throughput
CIFS: Client Average Throughput
For a legacy CIFS Edge device, the following charts are included on two tabs:
•![]() Summary tab:
Summary tab:
•![]() Details tab:
Details tab:
–![]() CIFS: Connected CIFS Core Count
CIFS: Connected CIFS Core Count
–![]() CIFS: CIFS Edge-CIFS Core Traffic
CIFS: CIFS Edge-CIFS Core Traffic
–![]() CIFS: Client Average Throughput
CIFS: Client Average Throughput
For a legacy CIFS Core device, the following charts are included:
•![]() Summary tab:
Summary tab:
–![]() CIFS: Connected CIFS Edge Count
CIFS: Connected CIFS Edge Count

Note ![]() When you use the Print icon in the taskbar to print the CIFS Acceleration report to a PDF file, all the CIFS charts will display the time in WAE local time (the CE Local Time setting), regardless of the chart time zone settings that you have configured.
When you use the Print icon in the taskbar to print the CIFS Acceleration report to a PDF file, all the CIFS charts will display the time in WAE local time (the CE Local Time setting), regardless of the chart time zone settings that you have configured.
CPU Statistics Report
The CPU Statistics report displays the CPU Utilization chart.
To change the report time frame, click Settings.
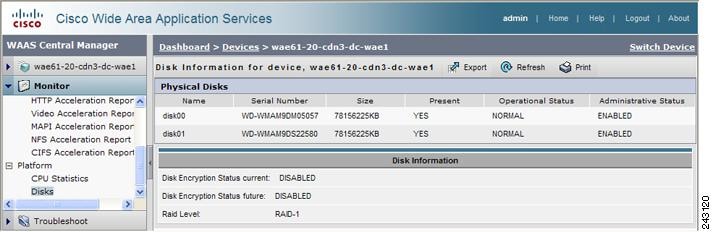
Disks Report
The Disks Report displays physical and logical disk information. (See Figure 16-56.)
The report window displays the following information about each disk:
•![]() Physical disk information, including the disk name, serial number, and disk size.
Physical disk information, including the disk name, serial number, and disk size.
•![]() Present status. The Present field will show either Yes if the disk is present, or Not Applicable if the disk is administratively shut down.
Present status. The Present field will show either Yes if the disk is present, or Not Applicable if the disk is administratively shut down.
•![]() Operational status (NORMAL, REBUILD, BAD, UNKNOWN, or Online).
Operational status (NORMAL, REBUILD, BAD, UNKNOWN, or Online).
•![]() Administrative status (ENABLED or DISABLED). When the Administrative Status field shows DISABLED, the Present field will show Not Applicable.
Administrative status (ENABLED or DISABLED). When the Administrative Status field shows DISABLED, the Present field will show Not Applicable.
•![]() Current and future disk encryption status.
Current and future disk encryption status.
•![]() RAID level. For RAID-5 devices, the Disk Information window includes the RAID device name, RAID status, and RAID device size.
RAID level. For RAID-5 devices, the Disk Information window includes the RAID device name, RAID status, and RAID device size.
•![]() Error information, if any errors are detected.
Error information, if any errors are detected.
From this window, you may save all disk information details to an Excel spreadsheet by clicking the Export Table icon in the taskbar.
Figure 16-56 Disk Information for Device Window
Managing Reports
The WAAS Central Manager allows you to edit any of the predefined reports and to create custom reports. Additionally, you can schedule reports to be generated periodically such as daily, weekly, or monthly. When a scheduled report is generated, a link to the report is e-mailed to notify the recipients.
This section contains the following topics:
Creating Custom Reports
A report consists of one or more charts in the chart panel (upper portion of the window) and a table in the table panel (lower portion of the window). The system and device dashboard displays are examples of predefined reports, along with the other reports available in the Monitor drawer.
Reports can be created only at the system level, not at the device level.
To create a custom report, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose Report > Manage Reports.
From the WAAS Central Manager GUI navigation pane, choose Report > Manage Reports.
Step 2 ![]() Click the Create New Report icon in the taskbar. The Custom Report window appears, as shown in Figure 16-57.
Click the Create New Report icon in the taskbar. The Custom Report window appears, as shown in Figure 16-57.
Figure 16-57 Creating a Report
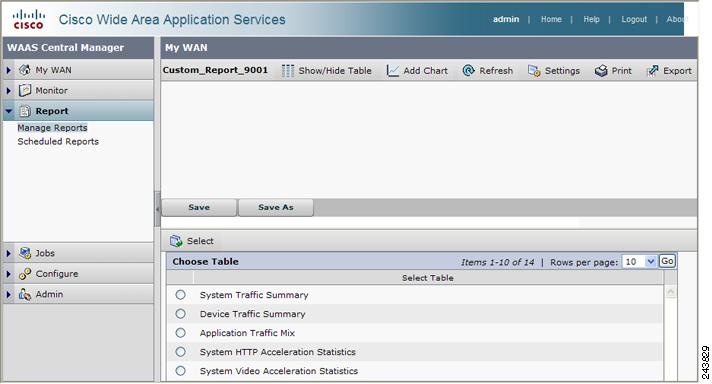
Step 3 ![]() Choose a table to display in the lower table panel of the report by clicking the radio button next to the table in the Choose Table area and then clicking the Select button above the Choose Table area.
Choose a table to display in the lower table panel of the report by clicking the radio button next to the table in the Choose Table area and then clicking the Select button above the Choose Table area.
Step 4 ![]() Add one or more charts to be displayed in the upper chart panel of the report by clicking the Add Chart icon in the taskbar. The Add Chart window is displayed, as shown in Figure 16-7.
Add one or more charts to be displayed in the upper chart panel of the report by clicking the Add Chart icon in the taskbar. The Add Chart window is displayed, as shown in Figure 16-7.
Step 5 ![]() Expand any of the chart categories by clicking on the plus sign next to the category.
Expand any of the chart categories by clicking on the plus sign next to the category.
Step 6 ![]() Check the box next to each chart that you want to display. See the "Chart Descriptions" section for a description of the charts.
Check the box next to each chart that you want to display. See the "Chart Descriptions" section for a description of the charts.
A report can contain a maximum of six charts.
Step 7 ![]() Click Add.
Click Add.
Step 8 ![]() Customize any of the chart settings by clicking the Settings icon in the taskbar. For more information, see the "Configuring Chart Settings" section.
Customize any of the chart settings by clicking the Settings icon in the taskbar. For more information, see the "Configuring Chart Settings" section.
Step 9 ![]() Click the Save As button below the chart panel to save the report with a new name. The Save As popup window appears.
Click the Save As button below the chart panel to save the report with a new name. The Save As popup window appears.
(If you use the Save button, the report is saved with a default name such as Custom_Report_9001.)
Step 10 ![]() Enter the report name and any notes about the report.
Enter the report name and any notes about the report.
Step 11 ![]() Click Submit.
Click Submit.
If you want to delete a chart from a dashboard or report, click the Close button on the chart and save the report.
All of the taskbar icons above the charts panel and the buttons below the charts panel work as described in the "Customizing a Dashboard or Report" section.
Viewing and Editing Reports
To view or edit a report, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose Report > Manage Reports.
From the WAAS Central Manager GUI navigation pane, choose Report > Manage Reports.
Step 2 ![]() Check the box next to the report that you want to view or edit.
Check the box next to the report that you want to view or edit.
If you do not see the report that you are looking for, you may need to navigate to another page of the Reports table.
Step 3 ![]() To delete a report, click the Delete icon in the taskbar.
To delete a report, click the Delete icon in the taskbar.
Step 4 ![]() To view or edit a report, click the Edit icon in the taskbar. The report is displayed.
To view or edit a report, click the Edit icon in the taskbar. The report is displayed.
Alternatively, click the magnifying glass icon next to a report as a shortcut to viewing it.
Step 5 ![]() If you want to change any of the charts in the report, use the standard chart editing methods as described in the "Creating Custom Reports" section.
If you want to change any of the charts in the report, use the standard chart editing methods as described in the "Creating Custom Reports" section.
Step 6 ![]() Click Save or Save As to save the report.
Click Save or Save As to save the report.
When editing a report, you cannot change the table that is displayed in the table panel. If you want to change the table, you must create a new report.
When viewing a report, click the Refresh button below the table panel to refresh the data in the table.
Admin users can view, edit, and delete reports created by all users and can view and edit predefined reports. Non-admin users can view, edit, and delete only reports created by themselves and can view and edit predefined reports.
Scheduling Reports
You can schedule reports to be generated once or periodically such as daily, weekly, or monthly. When a scheduled report is generated, a link to the report is e-mailed to notify the recipients.
To schedule a report, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose Report > Manage Reports.
From the WAAS Central Manager GUI navigation pane, choose Report > Manage Reports.
Step 2 ![]() Check the box next to the report that you want to schedule.
Check the box next to the report that you want to schedule.
If you do not see the report that you are looking for, you may need to navigate to another page of the Reports table.
Step 3 ![]() Click the Schedule icon in the taskbar. The scheduling window appears, as shown in Figure 16-58.
Click the Schedule icon in the taskbar. The scheduling window appears, as shown in Figure 16-58.
Figure 16-58 Scheduling a Report
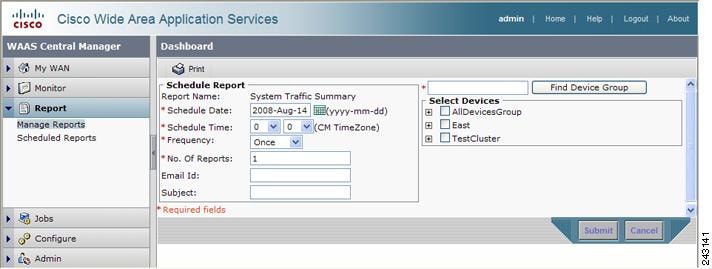
Step 4 ![]() In the Schedule Date field, enter the schedule date in the format YYYY-MM-DD, or click the calendar icon to display a calendar popup window from which to choose the date.
In the Schedule Date field, enter the schedule date in the format YYYY-MM-DD, or click the calendar icon to display a calendar popup window from which to choose the date.
Step 5 ![]() In the Schedule Time field, choose the hours and minutes from the drop-down lists. The time represents the local time at the WAAS Central Manager.
In the Schedule Time field, choose the hours and minutes from the drop-down lists. The time represents the local time at the WAAS Central Manager.
Step 6 ![]() In the Frequency drop-down list, choose Once, Daily, Weekly, or Monthly for the report frequency.
In the Frequency drop-down list, choose Once, Daily, Weekly, or Monthly for the report frequency.
Step 7 ![]() In the No. of Reports field, enter the number of times that a reoccurring report is to be generated. After being generated the specified number of times, the report is no longer generated.
In the No. of Reports field, enter the number of times that a reoccurring report is to be generated. After being generated the specified number of times, the report is no longer generated.
Step 8 ![]() In the Email Id field, enter the e-mail address of the report recipient. Only a single email address is allowed but it can be a distribution list.
In the Email Id field, enter the e-mail address of the report recipient. Only a single email address is allowed but it can be a distribution list.
Step 9 ![]() In the Subject field, enter the subject of the e-mail message.
In the Subject field, enter the subject of the e-mail message.
Step 10 ![]() In the Select Devices area, select the devices that are to be included in the statistics for the report. Place a check in the box next to each device or device group that you want to include.
In the Select Devices area, select the devices that are to be included in the statistics for the report. Place a check in the box next to each device or device group that you want to include.
To find (highlight) a device group in a long list, enter the device group name in the field above the list and click Find Device Group. The search is case sensitive.
Step 11 ![]() Click Submit.
Click Submit.
Step 12 ![]() Configure the e-mail server settings for e-mail notification when reports are generated. For more information, see the "Configuring the E-mail Notification Server" section on page 9-22.
Configure the e-mail server settings for e-mail notification when reports are generated. For more information, see the "Configuring the E-mail Notification Server" section on page 9-22.
Managing Scheduled Reports
To view or delete a scheduled report, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose Report > Scheduled Reports. The Scheduled Reports window lists the scheduled reports.
From the WAAS Central Manager GUI navigation pane, choose Report > Scheduled Reports. The Scheduled Reports window lists the scheduled reports.
Step 2 ![]() (Optional) If you want to view a report, click the plus sign on the row for the schedule. The row expands to show the report instances for the schedule. Each instance shows the report name, devices selected, scheduled time, completed time, frequency, status, and user that scheduled the report.
(Optional) If you want to view a report, click the plus sign on the row for the schedule. The row expands to show the report instances for the schedule. Each instance shows the report name, devices selected, scheduled time, completed time, frequency, status, and user that scheduled the report.
Check the box next to the report instance that you want to view and click the View Completed Report icon on the taskbar; or, click the Completed link in the status column. You can view only completed reports. If a report instance has a status of Not Started or In Progress, you must wait for it to complete before you can view the report.

Note ![]() For each completed instance of a scheduled report, the Frequency column will show Once and the Completed Time will show the date and time the report was generated. These instances are the viewable instances of the report—one for each instance. There is also one instance shown with a Frequency of Daily, Weekly, or Monthly (depending on the schedule period), and no Completed Time. That instance is not viewable and represents the scheduled report object.
For each completed instance of a scheduled report, the Frequency column will show Once and the Completed Time will show the date and time the report was generated. These instances are the viewable instances of the report—one for each instance. There is also one instance shown with a Frequency of Daily, Weekly, or Monthly (depending on the schedule period), and no Completed Time. That instance is not viewable and represents the scheduled report object.
Step 3 ![]() (Optional) If you want to delete a report, check the box next to one or more report instances that you want to delete and click the Delete Selected Reports icon on the taskbar. You must select report instances, not the schedule name above a group of instances. If all report instances are deleted, the schedule is also deleted.
(Optional) If you want to delete a report, check the box next to one or more report instances that you want to delete and click the Delete Selected Reports icon on the taskbar. You must select report instances, not the schedule name above a group of instances. If all report instances are deleted, the schedule is also deleted.
WAAS stores the 10 most recently completed or failed report instances for each custom report. This number is configurable by the System.monitoring.maxReports system property. For details on changing this property, see the "Modifying the Default System Configuration Properties" section on page 9-17.
Admin users can view reports scheduled by all users. Non-admin users can view only reports scheduled by themselves.
Any changes to predefined report settings are stored separately for individual users. That is, if one user changes a predefined scheduled report, only that user will see the changes, and other users (including admin users) will continue to see the report with default settings.
Configuring Flow Monitoring
Flow monitoring applications collect traffic data that is used for application trend studies, network planning, and vendor-deployment impact studies. This section describes how to configure the flow monitoring feature on the WAE and includes the following topics:
•![]() Example Using NetQoS for Flow Monitoring
Example Using NetQoS for Flow Monitoring
The NetQoS monitoring application can interoperate with the WAAS software to provide flow monitoring. To integrate this application with the WAAS software, you configure the NetQoS FlowAgent module on the WAE devices. The NetQoS FlowAgent module on the WAE collects important metrics of packet flows, which are then sent across the network to the NetQoS SuperAgent. This monitoring agent analyzes the data and generates reports. For this feature to work, additional configuration is required on the NetQoS FlowAgent. (See the "Example Using NetQoS for Flow Monitoring" section.)
The monitoring agent is composed of two modules: the console (or host) and the collector. The WAE initiates two types of connections to these two monitoring agent modules: a temporary connection to the console and a persistent connection to the collector. You configure the console IP address on the WAE by entering the flow monitor tcpstat-v1 host configuration mode command in either the WAE CLI or through the Central Manager GUI. This temporary connection is referred to as the control connection. The control connection uses TCP port 7878. Its purpose is to obtain the IP address and port number of the collector to which the WAE is assigned. The WAE also pulls the configuration information regarding which servers are to be monitored over the control connection. Once the WAE obtains the IP address and port number of the collector, the WAE opens a persistent connection to the collector. Collected summary data for the servers that are being monitored is sent over this persistent connection.
You may place the console (or host) module and the collector module on a single device or on separate devices. These connections are independent of one another. A failure of one connection does not cause the failure of the other connection and vice versa.
The state of these connections and various operation statistics display when you use the show statistics flow monitor tcpstat-v1 EXEC mode command. Connection errors and data transfer errors trigger alarms on the WAE and in the Central Manager GUI. (See the "Alarms for Flow Monitoring" section.) To display debug information, use the debug flow monitor tcpstat-v1 EXEC mode command.
To configure flow monitoring on your WAEs using the Central Manager GUI, follow these steps:
Step 1 ![]() Create a new device group for configuring flow monitoring on multiple devices. Choose My WAN > Manage Device Groups > Create New Device Group to create a device group.
Create a new device group for configuring flow monitoring on multiple devices. Choose My WAN > Manage Device Groups > Create New Device Group to create a device group.
a. ![]() When you create the device group, check the Automatically assign all newly activated devices to this group check box to enable this option.
When you create the device group, check the Automatically assign all newly activated devices to this group check box to enable this option.
b. ![]() Add your existing WAE devices to this new device group.
Add your existing WAE devices to this new device group.
Step 2 ![]() From the Device Group listing window, click the Edit icon next to the name of the flow monitoring configuration device group that you want to configure.
From the Device Group listing window, click the Edit icon next to the name of the flow monitoring configuration device group that you want to configure.
Step 3 ![]() In the navigation pane, choose Configure > Monitoring > Flow Monitor. The Flow Monitor Settings for Device Group window appears.
In the navigation pane, choose Configure > Monitoring > Flow Monitor. The Flow Monitor Settings for Device Group window appears.
Step 4 ![]() Check the Enable check box.
Check the Enable check box.
Step 5 ![]() In the tcpstat-v1 Host field, enter the IP address of the monitoring agent console.
In the tcpstat-v1 Host field, enter the IP address of the monitoring agent console.
This configuration allows the WAE to establish a temporary connection (a control connection) to the console for the purpose of obtaining the IP address of the collector device. You must configure the collector IP address information from the console device. (See the configuration documentation for the NetQoS flow monitoring application software.)
Step 6 ![]() Click Submit to apply the settings to the devices in this device group.
Click Submit to apply the settings to the devices in this device group.
To configure flow monitoring on the WAE using the CLI, follow these steps:
Step 1 ![]() Register the WAE with the IP address of the monitoring agent console:
Register the WAE with the IP address of the monitoring agent console:
WAE(config)# flow monitor tcpstat-v1 host 10.1.2.3
This configuration allows the WAE to establish a temporary connection (a control connection) to the console (or host) for the purpose of obtaining the IP address of the collector device. You must configure the collector IP address information from the console device. (See the configuration documentation for the NetQoS flow monitoring application software.)
Step 2 ![]() Enable flow monitoring on the WAE appliance:
Enable flow monitoring on the WAE appliance:
WAE(config)# flow monitor tcpstat-v1 enable
Step 3 ![]() Check the configuration by using the show running-config EXEC command.
Check the configuration by using the show running-config EXEC command.
Alarms for Flow Monitoring
Table 16-5 describes the four different alarms that may be raised when errors occur with flow monitoring.
Example Using NetQoS for Flow Monitoring
NetQoS integrates with the WAAS software by running the NetQoS FlowAgent on WAE devices. FlowAgent is a software module developed by NetQoS that resides on the WAE appliance. The FlowAgent collects metrics about the packet flows, which are then sent across the network to a NetQoS SuperAgent. The SuperAgent measures the round-trip times, server response times, and data transfer times, analyzes the data, and generates reports.

Note ![]() When you use flow monitoring with the NetQoS SuperAgent, the flow monitor on the WAE captures optimized traffic only.
When you use flow monitoring with the NetQoS SuperAgent, the flow monitor on the WAE captures optimized traffic only.
To configure flow monitoring with NetQoS, follow these steps:
Step 1 ![]() From the WAE CLI or Central Manager GUI, enter the SuperAgent Master Console IP address in the tcpstat-v1 Host field on your WAE appliances.
From the WAE CLI or Central Manager GUI, enter the SuperAgent Master Console IP address in the tcpstat-v1 Host field on your WAE appliances.
If you are configuring multiple appliances through a device group, wait for the configuration to propagate to all the appliances in the device list.
Step 2 ![]() From the NetQoS SuperAgent console, assign a WAE to a SuperAgent Aggregator (known as the collector in WAAS terminology) and configure the NetQoS Networks, Servers, and Applications entities.
From the NetQoS SuperAgent console, assign a WAE to a SuperAgent Aggregator (known as the collector in WAAS terminology) and configure the NetQoS Networks, Servers, and Applications entities.

Note ![]() For information about using the NetQoS SuperAgent Master Console and configuring NetQoS SuperAgent entities, go to the following website: http://www.netqos.com
For information about using the NetQoS SuperAgent Master Console and configuring NetQoS SuperAgent entities, go to the following website: http://www.netqos.com
Configuring System Logging
Use the WAAS system logging feature to set specific parameters for the system log file (syslog). This file contains authentication entries, privilege level settings, and administrative details. The system log file is located on the system file system (sysfs) partition as /local1/syslog.txt.
To enable system logging, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices (or Manage Device Groups).
From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices (or Manage Device Groups).
Step 2 ![]() Click the Edit icon next to the device or device group for which you want to enable system logging.
Click the Edit icon next to the device or device group for which you want to enable system logging.
Step 3 ![]() From the navigation pane, choose Configure > Monitoring > Log Settings > System Log. The System Log Settings window appears. (See Figure 16-59.)
From the navigation pane, choose Configure > Monitoring > Log Settings > System Log. The System Log Settings window appears. (See Figure 16-59.)
Figure 16-59 System Log Settings Window
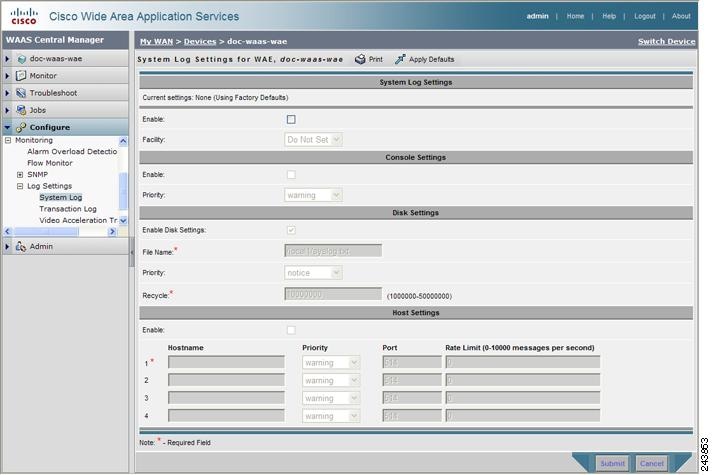
Step 4 ![]() Under the System Log Settings section, check the Enable check box to enable system logging. By default, this option is disabled.
Under the System Log Settings section, check the Enable check box to enable system logging. By default, this option is disabled.
Step 5 ![]() From the Facility drop-down list, choose the appropriate facility.
From the Facility drop-down list, choose the appropriate facility.
Step 6 ![]() Enable system log files to be sent to the console:
Enable system log files to be sent to the console:
a. ![]() In the Console Settings section, check the Enable check box.
In the Console Settings section, check the Enable check box.
b. ![]() From the Priority drop-down list, choose the severity level of the message that should be sent to the specified remote syslog host. The default priority-code is "warning" (level 4). Each syslog host is capable of receiving a different level of event messages. (See Table 16-6 for a list of priority levels.)
From the Priority drop-down list, choose the severity level of the message that should be sent to the specified remote syslog host. The default priority-code is "warning" (level 4). Each syslog host is capable of receiving a different level of event messages. (See Table 16-6 for a list of priority levels.)
Step 7 ![]() Enable syslog files to be sent to disk:
Enable syslog files to be sent to disk:
a. ![]() In the Disk Settings section, check the Enable Disk Settings check box.
In the Disk Settings section, check the Enable Disk Settings check box.
b. ![]() In the File Name field, enter a path and a filename where the syslog files will be stored on disk.
In the File Name field, enter a path and a filename where the syslog files will be stored on disk.
c. ![]() From the Priority drop-down list, choose the severity level of the message that should be sent to the specified remote syslog host. The default priority-code is "warning" (level 4). Each syslog host is capable of receiving a different level of event messages. (See Table 16-6 for a list of priority levels.)
From the Priority drop-down list, choose the severity level of the message that should be sent to the specified remote syslog host. The default priority-code is "warning" (level 4). Each syslog host is capable of receiving a different level of event messages. (See Table 16-6 for a list of priority levels.)
d. ![]() In the Recycle field, specify the size of the syslog file (in bytes) that can be recycled when it is stored on disk. The default value of the file size is 10000000.
In the Recycle field, specify the size of the syslog file (in bytes) that can be recycled when it is stored on disk. The default value of the file size is 10000000.
Whenever the current log file size surpasses the recycle size, the log file is rotated. (The default recycle size for the log file is 10,000,000 bytes.) The log file cycles through at most five rotations, and each rotation is saved as log_file_name.[1-5] under the same directory as the original log.
The rotated log file is configured in the File Name field (or by using the logging disk filename command).
Step 8 ![]() Enable syslog files to be sent to a host:
Enable syslog files to be sent to a host:
a. ![]() In the Host Settings section, check the Enable check box. You can configure up to four hosts to which syslog messages can be sent. For more information, see the "Multiple Hosts for System Logging" section."
In the Host Settings section, check the Enable check box. You can configure up to four hosts to which syslog messages can be sent. For more information, see the "Multiple Hosts for System Logging" section."
b. ![]() In the Hostname field, enter a hostname or IP address of the remote syslog host. Specify up to three more remote syslog hosts in the Hostname fields 2 through 4. You must specify at least one hostname if you have enabled system logging to a host.
In the Hostname field, enter a hostname or IP address of the remote syslog host. Specify up to three more remote syslog hosts in the Hostname fields 2 through 4. You must specify at least one hostname if you have enabled system logging to a host.
c. ![]() From the Priority drop-down list, choose the severity level of the message that should be sent to the specified remote syslog host. The default priority-code is "warning" (level 4). Each syslog host is capable of receiving a different level of event messages. (See Table 16-6 for a list of priority levels.)
From the Priority drop-down list, choose the severity level of the message that should be sent to the specified remote syslog host. The default priority-code is "warning" (level 4). Each syslog host is capable of receiving a different level of event messages. (See Table 16-6 for a list of priority levels.)
d. ![]() In the Port field, specify the destination port on the remote host to which the WAAS device should send the message. The default port number is 514.
In the Port field, specify the destination port on the remote host to which the WAAS device should send the message. The default port number is 514.
e. ![]() In the Rate Limit field, specify the number of messages per second that are allowed to be sent to the remote syslog host. To limit bandwidth and other resource consumption, messages to the remote syslog host can be rate limited. If this limit is exceeded, the specified remote syslog host drops the messages. There is no default rate limit, and by default all syslog messages are sent to all of the configured syslog hosts.
In the Rate Limit field, specify the number of messages per second that are allowed to be sent to the remote syslog host. To limit bandwidth and other resource consumption, messages to the remote syslog host can be rate limited. If this limit is exceeded, the specified remote syslog host drops the messages. There is no default rate limit, and by default all syslog messages are sent to all of the configured syslog hosts.
Step 9 ![]() Click Submit.
Click Submit.
To configure system logging from the CLI, you can use the logging global configuration command.
This section contains the following topics:
•![]() Multiple Hosts for System Logging
Multiple Hosts for System Logging
Priority Levels
Table 16-6 lists the different priority levels of detail to send to the recipient of the syslog messages for a corresponding event.
Multiple Hosts for System Logging
Each syslog host can receive different priority levels of syslog messages. You can configure different syslog hosts with a different syslog message priority code to enable the WAAS device to send varying levels of syslog messages to the four external syslog hosts. For example, a WAAS device can be configured to send messages that have a priority code of "error" (level 3) to the remote syslog host that has an IP address of 10.10.10.1 and messages that have a priority code of "warning" (level 4) to the remote syslog host that has an IP address of 10.10.10.2.
If you want to achieve syslog host redundancy or failover to a different syslog host, you must configure multiple syslog hosts on the WAAS device and assign the same priority code to each configured syslog host (for example, assigning a priority code of "critical" (level 2) to syslog host 1, syslog host 2, and syslog host 3).
In addition to configuring up to four logging hosts, you can also configure the following for multiple syslog hosts:
•![]() A port number different from the default port number, 514, on the WAAS device to send syslog messages to a logging host.
A port number different from the default port number, 514, on the WAAS device to send syslog messages to a logging host.
•![]() A rate limit for the syslog messages, which limits the rate at which messages are sent to the remote syslog server (messages per second) to control the amount of bandwidth used by syslog messages.
A rate limit for the syslog messages, which limits the rate at which messages are sent to the remote syslog server (messages per second) to control the amount of bandwidth used by syslog messages.
Configuring Transaction Logging
This section contains the following topics:
Enabling Transaction Logging
To enable transaction logging for TFO flows and video streams, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices (or Manage Device Groups).
From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices (or Manage Device Groups).
Step 2 ![]() Click the Edit icon next to the device or device group for which you want to enable system logging. The Device Dashboard window or the Modifying Device Group window appears.
Click the Edit icon next to the device or device group for which you want to enable system logging. The Device Dashboard window or the Modifying Device Group window appears.
Step 3 ![]() From the navigation pane, choose Configure > Monitoring > Log Settings > Transaction Log for TFO transaction logging, or Configure > Monitoring > Log Settings > Video Acceleration Transaction Log for video transaction logging. The Transaction Log Settings window appears. (See Figure 16-60.) The Video Transaction Log Settings window looks the same, but does not include the General Settings area at the top.
From the navigation pane, choose Configure > Monitoring > Log Settings > Transaction Log for TFO transaction logging, or Configure > Monitoring > Log Settings > Video Acceleration Transaction Log for video transaction logging. The Transaction Log Settings window appears. (See Figure 16-60.) The Video Transaction Log Settings window looks the same, but does not include the General Settings area at the top.
Figure 16-60 Transaction Log Settings Window
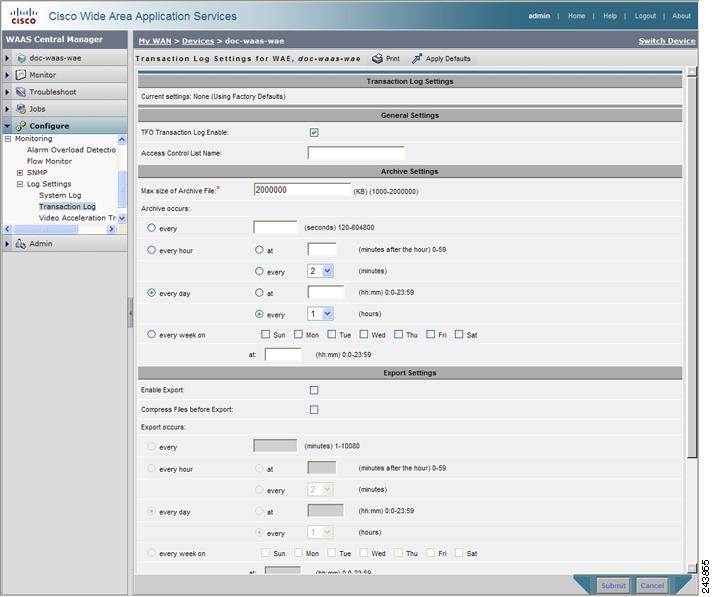
Step 4 ![]() Under the General Settings heading, check the TFO Transaction Log Enable check box to enable transaction logging. This check box does not appear for video transaction logging.
Under the General Settings heading, check the TFO Transaction Log Enable check box to enable transaction logging. This check box does not appear for video transaction logging.
The fields on the window become active.
Step 5 ![]() In the Access Control List Name field, optionally enter the name of an access control list that you want to use to limit transaction logging. If you specify an access control list, only transactions from hosts that are defined in the access list are logged. This field does not appear for video transaction logging.
In the Access Control List Name field, optionally enter the name of an access control list that you want to use to limit transaction logging. If you specify an access control list, only transactions from hosts that are defined in the access list are logged. This field does not appear for video transaction logging.
Use the ip access-list global configuration command to define an access list.
Step 6 ![]() Under the Archive Settings heading, specify values for the following fields:
Under the Archive Settings heading, specify values for the following fields:
•![]() Max Size of Archive File—Maximum size (in kilobytes) of the archive file to be maintained on the local disk. This value is the maximum size of the archived file to be maintained on the local disk. The range is 1000 to 2000000. The default is 2000000.
Max Size of Archive File—Maximum size (in kilobytes) of the archive file to be maintained on the local disk. This value is the maximum size of the archived file to be maintained on the local disk. The range is 1000 to 2000000. The default is 2000000.
•![]() Archive Occurs Every (interval)—Interval at which the working log data is cleared and moved into the archive log.
Archive Occurs Every (interval)—Interval at which the working log data is cleared and moved into the archive log.
Step 7 ![]() Configure the fields in the Export Settings section to export the transaction log file to an FTP server.
Configure the fields in the Export Settings section to export the transaction log file to an FTP server.
Table 16-7 describes the fields in the Export Settings section.
Step 8 ![]() Click Submit.
Click Submit.
A "Click Submit to Save" message appears in red next to the Current Settings line when there are pending changes to be saved after you have applied default or device group settings. You can also revert to the previously configured settings by clicking Reset. The Reset button is visible only when you have applied default or group settings to change the current device settings but have not yet submitted the changes.
If you try to leave this window without saving the modified settings, a warning dialog box prompts you to submit the changes. This dialog box only appears if you are using the Internet Explorer browser.
To enable and configure transaction logging from the CLI, you can use the transaction-logs global configuration command.
Transaction Logs
TFO transaction logs are kept on the local disk in the directory /local1/logs/tfo. Video (Windows media) logs are kept in the directory /local1/logs/wmt/wms-90.
When you enable transaction logging, you can specify the interval at which the working log should be archived by moving the data to an archive log. The archive log files are located on the local disk in the directory /local1/logs/.
Because multiple archive files are saved, the filename includes the time stamp when the file was archived. Because the files can be exported to an FTP/SFTP server, the filename also contains the IP address of this WAAS device.
The archive filenames for TFO transactions use this format:
tfo_IPADDRESS_YYYYMMDD_HHMMSS.txt.
The archive filenames for Windows media transactions use this format:
wms_90_IPADDRESS_YYYYMMDD_HHMMSS.txt.
Viewing the System Message Log
Using the system message log feature of the WAAS Central Manager GUI, you can view information about events that have occurred in your WAAS network. The WAAS Central Manager logs messages from registered devices with a severity level of "warning" or higher.
To view logged information for your WAAS network, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose Admin > Logs > System Messages. The System Message Log window appears. (See Figure 16-61.)
From the WAAS Central Manager GUI navigation pane, choose Admin > Logs > System Messages. The System Message Log window appears. (See Figure 16-61.)
Figure 16-61 System Message Log
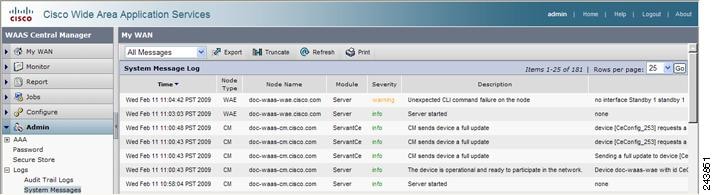
Step 2 ![]() From the System Message Log drop-down list, choose one of the following types of messages to display:
From the System Message Log drop-down list, choose one of the following types of messages to display:
•![]() All
All
•![]() CLI
CLI
•![]() Critical
Critical
•![]() Database
Database
Step 3 ![]() (Optional) Click a column heading by node type, node name, module, or message text to sort the messages. By default, messages are listed chronologically.
(Optional) Click a column heading by node type, node name, module, or message text to sort the messages. By default, messages are listed chronologically.

Note ![]() If no name is available for a node, the name displayed is "Unavailable." This might occur if the node has been deleted or has been reregistered with WAAS software.
If no name is available for a node, the name displayed is "Unavailable." This might occur if the node has been deleted or has been reregistered with WAAS software.
Step 4 ![]() (Optional) Truncate the message log so that not as many messages appear in the table, by completing the following steps:
(Optional) Truncate the message log so that not as many messages appear in the table, by completing the following steps:
a. ![]() Click the Truncate icon in the taskbar. The Truncate System Message Log window appears.
Click the Truncate icon in the taskbar. The Truncate System Message Log window appears.
b. ![]() Choose one of the following options:
Choose one of the following options:
–![]() Size Truncation—Limits the messages in the log to the number you specify. The log uses a first in, first out process to remove old messages once the log reaches the specified number.
Size Truncation—Limits the messages in the log to the number you specify. The log uses a first in, first out process to remove old messages once the log reaches the specified number.
–![]() Date Truncation—Limits the messages in the log to the number of days you specify.
Date Truncation—Limits the messages in the log to the number of days you specify.
–![]() Message Truncation—Removes messages from the log that match the specified pattern.
Message Truncation—Removes messages from the log that match the specified pattern.
c. ![]() Click Submit when finished specifying the truncation parameters.
Click Submit when finished specifying the truncation parameters.
Step 5 ![]() If you have many event messages, you may need to view multiple pages to view the activity in which you are interested. Click the forward (>>) and back (<<) buttons to move between pages. Alternatively, click the link for a specific page number to jump to that page.
If you have many event messages, you may need to view multiple pages to view the activity in which you are interested. Click the forward (>>) and back (<<) buttons to move between pages. Alternatively, click the link for a specific page number to jump to that page.
Viewing the Audit Trail Log
The WAAS Central Manager logs user activity in the system. The only activities that are logged are those that change the WAAS network. This feature provides accountability for users' actions by describing the time and action of the task. Logged activities include the following:
•![]() Creation of WAAS network entities
Creation of WAAS network entities
•![]() Modification and deletion of WAAS network entities
Modification and deletion of WAAS network entities
•![]() System configurations
System configurations
To view audit trail logs, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose Admin > Logs > Audit Trail Logs.
From the WAAS Central Manager GUI navigation pane, choose Admin > Logs > Audit Trail Logs.
The Audit Log window appears. (See Figure 16-62.) All logged transactions in the WAAS Central Manager are listed by date and time, user, actual transaction that was logged, and the IP address of the machine that was used.
Figure 16-62 Audit Log Window
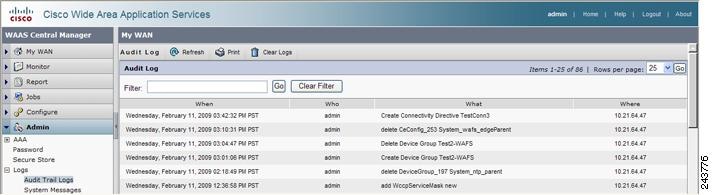
Step 2 ![]() Choose a number from the Rows drop-down list to determine the number of rows that you want to display.
Choose a number from the Rows drop-down list to determine the number of rows that you want to display.
Viewing the Device Log
To view information about events that have occurred on a specific device in your WAAS network, you can use the system message log feature available in the WAAS Central Manager GUI.
To view events that have occurred on your entire WAAS network, see the "Viewing the System Message Log" section.
To view the logged information for a WAAS device, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices. The Devices window appears.
From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices. The Devices window appears.
Step 2 ![]() Click the Edit icon next to the device for which you want to view the system message log details. The Device Dashboard window appears.
Click the Edit icon next to the device for which you want to view the system message log details. The Device Dashboard window appears.
Step 3 ![]() In the navigation pane, choose Admin > Logs. The System Message Log for Device window appears.
In the navigation pane, choose Admin > Logs. The System Message Log for Device window appears.
Step 4 ![]() Choose the type of messages to be displayed from the System Message Log drop-down list.
Choose the type of messages to be displayed from the System Message Log drop-down list.
You can view the following types of messages in the system log:
•![]() All (default)
All (default)
•![]() CLI
CLI
•![]() Critical
Critical
•![]() Database
Database
Step 5 ![]() Click a column heading to arrange the messages chronologically by node type, node name, or module. By default, messages are displayed chronologically.
Click a column heading to arrange the messages chronologically by node type, node name, or module. By default, messages are displayed chronologically.
If no name is available for a node because the node has been deleted or reregistered with the WAAS software, the message displayed is "Unavailable."
Step 6 ![]() If you have many event messages, you may need to use the forward (>>) and back (<<) buttons to move between pages. Alternatively, click the link for a specific page number to move to that particular page.
If you have many event messages, you may need to use the forward (>>) and back (<<) buttons to move between pages. Alternatively, click the link for a specific page number to move to that particular page.
Enabling the Kernel Debugger
The WAAS Central Manager GUI allows you to enable or disable access to the kernel debugger (kdb). Once enabled, kernel debugger is automatically activated when kernel problems occur.
To enable the kernel debugger, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices (or Manage Device Groups).
From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices (or Manage Device Groups).
Step 2 ![]() Click the Edit icon next to the WAAS device (or device group) that you want to debug.
Click the Edit icon next to the WAAS device (or device group) that you want to debug.
Step 3 ![]() In the navigation Pane, choose Troubleshoot > Kernel Debugger. The Kernel Debugger window appears.
In the navigation Pane, choose Troubleshoot > Kernel Debugger. The Kernel Debugger window appears.
Step 4 ![]() Check the Enable check box to enable the kernel debugger, and click Submit. By default, this option is disabled.
Check the Enable check box to enable the kernel debugger, and click Submit. By default, this option is disabled.
Troubleshooting Using Diagnostic Tests
WAAS includes various troubleshooting tools as described in the following sections:
•![]() Troubleshooting Using the GUI
Troubleshooting Using the GUI
•![]() Troubleshooting Using the CLI
Troubleshooting Using the CLI
Troubleshooting Using the GUI
The WAAS Central Manager includes a troubleshooting and diagnostic reporting facility.
To perform diagnostic tests, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices (or Manage Device Groups).
From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices (or Manage Device Groups).
Step 2 ![]() Click the Edit icon next to the name of the device (or device group) for which you want to perform diagnostic tests.
Click the Edit icon next to the name of the device (or device group) for which you want to perform diagnostic tests.
Step 3 ![]() In the navigation pane, choose Troubleshoot > Diagnostics Tests. The Diagnostic Tool window appears.
In the navigation pane, choose Troubleshoot > Diagnostics Tests. The Diagnostic Tool window appears.
Step 4 ![]() Check the check box next to each diagnostic test that you want to run, or check the top check box to run all tests. The following tests are available:
Check the check box next to each diagnostic test that you want to run, or check the top check box to run all tests. The following tests are available:
•![]() Device Operation—Check device status, presence of coredump files or alarms of major or critical severity.
Device Operation—Check device status, presence of coredump files or alarms of major or critical severity.
•![]() Basic Configuration—Check device basic network configuration.
Basic Configuration—Check device basic network configuration.
•![]() Basic Connectivity—Check device connectivity to configured external devices (DNS, authentication, NTP servers, etc.).
Basic Connectivity—Check device connectivity to configured external devices (DNS, authentication, NTP servers, etc.).
•![]() Physical Interface—Check configuration and operation of device physical interfaces.
Physical Interface—Check configuration and operation of device physical interfaces.
•![]() Traffic Optimization—Check TFO configuration and operation.
Traffic Optimization—Check TFO configuration and operation.
•![]() WCCP configuration and operation—Check configuration and operation of WCCP traffic interception.
WCCP configuration and operation—Check configuration and operation of WCCP traffic interception.
•![]() Inline configuration and operation—Check configuration and operation of inline group interfaces.
Inline configuration and operation—Check configuration and operation of inline group interfaces.
•![]() WAFS configuration and operation—Check configuration and operation of WAFS services.
WAFS configuration and operation—Check configuration and operation of WAFS services.
Step 5 ![]() Click Run.
Click Run.
Step 6 ![]() View the test results in the lower part of the window. You may have to scroll the window to see all results.
View the test results in the lower part of the window. You may have to scroll the window to see all results.
For tests that fail, error messages describe the problem and provide recommended solutions.
You can run the same diagnostic tests again and refresh the results by clicking the Refresh icon in the taskbar.
To print the results, click the Print icon in the taskbar.
Troubleshooting Using the CLI
You can use the test EXEC command to perform diagnostic and connectivity tests.
You can use network-level tools to intercept and analyze packets as they pass through your network. Two of these tools are TCPdump and Tethereal, which you can access from the CLI by using the tcpdump and tethereal EXEC commands.
The WAAS device also supports multiple debugging modes, reached with the debug EXEC command. These modes allow you to troubleshoot problems from configuration errors to print spooler problems. We recommend that you use the debug command only at the direction of Cisco TAC.
The output associated with the debug command is written to either the syslog file in /local1/syslog.txt or the debug log associated with the module in the file /local1/errorlog/module_name-errorlog.current.
The output associated with the debug accelerator name module command for an application accelerator is written to the file nameao-errorlog.current, where name is the accelerator name. The accelerator information manager debug output is written to the file aoim-errorlog.current.
The debug log file associated with a module will be rotated to a backup file when the current file reaches its maximum size. The backup files are named as follows: name-errorlog.#, where # is the backup file number.
For any debug command, system logging must be enabled. The command to enable logging is the logging disk enable global configuration command, which is enabled by default.
If a debug command module uses the syslog for debug output, then the logging disk priority debug global configuration command must be configured (the default is logging disk priority notice).
If a debug command module uses the debug log for output, then the output can be filtered based on priority level configuration for the four different levels of debug log output, as follows:
•![]() For filtering on critical debug messages only, use the following global configuration command: logging disk priority critical.
For filtering on critical debug messages only, use the following global configuration command: logging disk priority critical.
•![]() For filtering on critical and error level debug messages, use the following global configuration command: logging disk priority error.
For filtering on critical and error level debug messages, use the following global configuration command: logging disk priority error.
•![]() For filtering on critical, error, and trace debug level debug messages, use the following global configuration command: logging disk priority debug.
For filtering on critical, error, and trace debug level debug messages, use the following global configuration command: logging disk priority debug.
•![]() For seeing all debug log messages, which include critical, error, trace and detail messages, use the following global configuration command: logging disk priority detail.
For seeing all debug log messages, which include critical, error, trace and detail messages, use the following global configuration command: logging disk priority detail.
Regardless of the priority level configuration, any syslog messages at the LOG_ERROR or higher priority will be automatically written to the debug log associated with a module.
For more details on these CLI commands, see the Cisco Wide Area Application Services Command Reference.
Using the show and clear Commands from the WAAS Central Manager GUI
To use the WAAS Central Manager GUI show and clear command tool, follow these steps:
Step 1 ![]() From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices.
From the WAAS Central Manager GUI navigation pane, choose My WAN > Manage Devices.
Step 2 ![]() Click the Edit icon next to the device for which you want to issue a show or clear command.
Click the Edit icon next to the device for which you want to issue a show or clear command.
Step 3 ![]() From the navigation pane, choose Troubleshoot > CLI Commands and then click either Show Commands or Clear Commands.
From the navigation pane, choose Troubleshoot > CLI Commands and then click either Show Commands or Clear Commands.
Step 4 ![]() From the drop-down list, choose a show or clear command.
From the drop-down list, choose a show or clear command.
Step 5 ![]() Enter arguments for the command, if any.
Enter arguments for the command, if any.
Step 6 ![]() Click Submit to display the command output.
Click Submit to display the command output.
A window appears, displaying the command output for that device.
You can also use the show EXEC commands from the CLI. For more information, see the Cisco Wide Area Application Services Command Reference.
 Feedback
Feedback