Contents
- VoIP Wireless Network
- Wireless LAN
- WLAN Standards and Technologies
- 802.11 Standards for WLAN Communications
- World Mode (802.11d)
- Supported Countries
- Radio Frequency Ranges
- 802.11 Data Rates, Transmit Power, Ranges, and Decibel Tolerances
- Wireless Modulation Technologies
- AP Channel and Domain Relationships
- WLANs and Roaming
- Bluetooth Wireless Technology
- VoIP Wireless Network Components
- Cisco Unified Wireless AP Interactions
- AP Association
- Voice QoS in Wireless Network
- Cisco Unified Communications Manager Interaction
- Security for Voice Communications in WLANs
- Authentication Methods
- Authenticated Key Management
- Encryption Methods
- AP Authentication and Encryption Options
- VoIP WLAN Deployment
- Supported Access Points
- Supported APs and Modes
- Supported Antennas
- Set Up Wireless LAN
- Set Up Wireless LAN in Cisco Unified Communications Manager Administration
- Wireless LAN on Cisco Unified IP Phone Setup
VoIP Wireless Network
This chapter provides an overview of the interaction between a wireless-capable Cisco Unified IP Phone 9971 and other key components of a VoIP network in a wireless local area network (WLAN) environment.
Note
For instructions on deploying and configuring a wireless Cisco Unified IP Phone 9971, see the Cisco Unified IP Phone 9971 Wireless LAN Deployment Guide at this location:
- Wireless LAN
- WLAN Standards and Technologies
- Bluetooth Wireless Technology
- VoIP Wireless Network Components
- Security for Voice Communications in WLANs
- VoIP WLAN Deployment
- Set Up Wireless LAN
Wireless LAN
With the introduction of wireless communication, Cisco Unified IP Phones with wireless capability, such as the Cisco Unified IP Phone 9971, can provide voice communication within the corporate WLAN. The Cisco Unified IP Phone depends upon and interacts with wireless access points (AP) and key Cisco IP telephony components, including Cisco Unified Communications Manager Administration, to provide wireless voice communication. Cisco Access Points can run in standalone or unified mode. Unified mode requires the Cisco Unified Wireless LAN Controller.
The Cisco Unified IP Phone 9971 exhibits Wi-Fi capabilities which can be used with 802.11a, 802.11b, and 802.11g Wi-Fi.
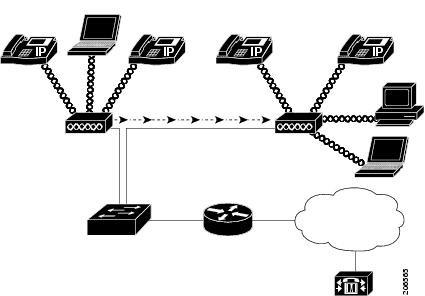
The following figure shows a typical WLAN topology that enables the wireless transmission of voice for wireless IP telephony.
When a Cisco Unified IP Phone powers on, it searches for and becomes associated with an AP if the phone wireless access is set to On.
The AP uses the connection to the wired network to transmit data and voice packets to and from the switches and routers. Voice signaling is transmitted to the Cisco Unified Communications Manager server for call processing and routing.
APs are critical components in a WLAN because they provide the wireless links or "hot spots" to the network. Cisco requires that APs that support voice communications use Cisco IOS Release 12.3(8)JA or later. Cisco IOS software provides features for managing voice traffic.
In some WLANs, each AP has a wired connection to an Ethernet switch, such as a Cisco Catalyst 3750, that is configured on a LAN. The switch provides access to gateways and the Cisco Unified Communications Manager server to support wireless IP telephony.
Some networks contain wired components that support wireless components. The wired components can comprise switches, routers, and bridges with special modules to enable wireless capability.
For more information about Cisco Unified Wireless Networks, see http://www.cisco.com/en/US/products/hw/wireless/index.html.
WLAN Standards and Technologies
- 802.11 Standards for WLAN Communications
- World Mode (802.11d)
- Radio Frequency Ranges
- 802.11 Data Rates, Transmit Power, Ranges, and Decibel Tolerances
- Wireless Modulation Technologies
- AP Channel and Domain Relationships
- WLANs and Roaming
802.11 Standards for WLAN Communications
Wireless LANs must follow the Institute of Electrical and Electronics Engineers (IEEE) 802.11 standards that define the protocols that govern all Ethernet-based wireless traffic. The Cisco Unified IP Phone supports the following standards:
- 802.11a: Uses the 5 GHz band that provides more channels and improved data rates by using OFDM technology. Dynamic Frequency Selection (DFS) and Transmit Power Control (TPC) support this standard.
- 802.11b:Specifies the radio frequency (RF) of 2.4 Ghz for both transmitting and receiving data at lower data rates (1, 2, 5.5, 11 Mbps).
- 802.11d: Enables access points to advertise their currently supported radio channels and transmit power levels. The 802.11d enabled client then uses that information to determine the channels and powers to use. The Cisco Unified IP Phone 9971 requires World mode (802.11d) to determine which channels are legally allowed for any given country. For supported channels, see the following table. Ensure that 802.11d is properly configured on the Cisco IOS Access Points or Cisco Unified Wireless LAN Controller.
- 802.11e: Quality of Service (QoS)
- 802.11g:Uses the same unlicensed 2.4 Ghz band as 802.11b, but extends the data rates to provide greater performance by using Orthogonal Frequency Division Multiplexing (OFDM) technology. OFDM is a physical-layer encoding technology for transmitting signals by using RF.
- 802.11h: 5 GHz spectrum and transmit power management
- 802.11i: Security
Part number
Band range
Available channels
5 GHz channel set
CP-9971-K9
2.412 – 2.484 GHz
5.180 – 5.240 GHz
5.260 – 5.320 GHz
5. 500 – 5.700 GHz
5.745 – 5.805 GHz
13 (14 in Japan)
4
4
11
4
UNII-2
UNII-2
UNII-2 Extended
UNII-3
Note
802.11j (channels 34, 38, 42, 46) and channel 165 are not supported.
Related Information
World Mode (802.11d)
If you are using the Cisco Unified IP Phone 9971 in World mode, you must enable World mode (802.11d). The Cisco Unified IP Phone 9971 uses 802.11d to determine which channels and transmit powers to use and inherits the client configuration from the associated access point.
Note
Enabling World mode (802.11d) may not be necessary if the frequency is 2.4GHz and the current access point is transmitting on a channel 1-11.
Because all countries support these frequencies, you can attempt to scan these channels regardless of World mode (802.11d) support. For the countries that support 2.4GHz, see Cisco Unified IP Phone 9971 Wireless LAN Deployment Guide at this location:
http://www.cisco.com/en/US/products/ps10453/products_implementation_design_guides_list.html
Enable World mode (802.11d) for the corresponding country where the access point is located. World mode is enabled automatically for the Cisco Unified Wireless LAN Controller.
You must enable World mode for Cisco Autonomous Access Points by using the following commands:
Supported Countries
The Cisco Unified IP Phone 9971 supports the following countries:
Argentina (AR)
India (IN)
Poland (PL)
Australia (AU)
Indonesia (ID)
Portugal (PT)
Austria (AT)
Ireland (IE)
Puerto Rico (PR)
Belgium (BE)
Israel (IL)
Romania (RO)
Brazil (BR)
Italy (IT)
Russian Federation (RU)
Bulgaria (BG)
Japan (JP)
Saudi Arabia (SA)
Canada (CA)
Korea (KR / KP)
Singapore (SG)
Chile (CL)
Latvia (LV)
Slovakia (SK)
Colombia (CO)
Liechtenstein (LI)
Slovenia (SI)
Costa Rica (CR)
Lithuania (LT)
South Africa (ZA)
Cyprus (CY)
Luxembourg (LU)
Spain (ES)
Czech Republic (CZ)
Malaysia (MY)
Sweden (SE)
Denmark (DK)
Malta (MT)
Switzerland (CH)
Estonia (EE)
Mexico (MX)
Taiwan (TW)
Finland (FI)
Monaco (MC)
Thailand (TH)
France (FR)
Netherlands (NL)
Turkey (TR)
Germany (DE)
New Zealand (NZ)
Ukraine (UA)
Gibraltar (GI)
Norway (NO)
United Arab Emirates (AE)
Greece (GR)
Oman (OM)
United Kingdom (GB)
Hong Kong (HK)
Panama (PA)
United States (US)
Hungary (HU)
Peru (PE)
Venezuela (VE)
Iceland (IS)
Philippines (PH)
Vietnam (VN)
Radio Frequency Ranges
WLAN communications use the following radio frequency (RF) ranges:
- 2.4 GHz: Many devices that use 2.4 GHz can potentially interfere with the 802.11b/g connection. Interference can produce a Denial of Service (DoS) scenario, possibly preventing successful 802.11 transmissions.
- 5 GHz: This range divides into several sections called Unlicensed National Information Infrastructure (UNII) bands, each of which has four channels. The channels are spaced at 20 MHz to provide nonoverlapping channels and more channels than 2.4 GHz provides.
802.11 Data Rates, Transmit Power, Ranges, and Decibel Tolerances
The following table lists the transmit (Tx) power capacities, data rates, ranges in feet and meters, and decibels that the receiver tolerates for the 801.11 standards.
Table 1 Tx power, data rates, ranges, and decibels by standard Standard
Maximum Tx power (See Note 1)
Data rate (See Note 2)
Range
Receiver sensitivity
802.11a
16 dBm
6 Mbps
604 ft (184 m)
-91 dBm
9 Mbps
604 ft (184 m)
-90 dBm
12 Mbps
551 ft (168 m)
-88 dBm
18 Mbps
545 ft (166 m)
-86 dBm
24 Mbps
512 ft (156 m)
-82 dBm
36 Mbps
420 ft (128 m)
-80 dBm
48 Mbps
322 ft (98 m)
-77 dBm
54 Mbps
289 ft (88 m)
-75 dBm
802.11g
16 dBm
6 Mbps
709 ft (216 m)
-91 dBm
9 Mbps
650 ft (198 m)
-90 dBm
12 Mbps
623 ft (190 m)
-87 dBm
18 Mbps
623 ft (190 m)
-86 dBm
24 Mbps
623 ft (190 m)
-82 dBm
36 Mbps
495 ft (151 m)
-80 dBm
48 Mbps
413 ft (126 m)
-77 dBm
54 Mbps
394 ft (120 m)
-76 dBm
802.11b
17 dBm
1 Mbps
1,010 ft (308 m)
-96 dBm
2 Mbps
951 ft (290 m)
-85 dBm
5.5 Mbps
919 ft (280 m)
-90 dBm
11 Mbps
902 ft (275 m)
-87 dBm
For more information about supported data rates, Tx power and Rx sensitivity for WLANs, see the Cisco Unified IP Phone 9971 Wireless LAN Deployment Guide at this location:
Wireless Modulation Technologies
Wireless communications use the following modulation technologies for signaling:
- Direct-Sequence Spread Spectrum (DSSS)
Prevents interference by spreading the signal over the frequency range or bandwidth. DSSS technology multiplexes chunks of data over several frequencies so that multiple devices can communicate without interference. Each device has a special code that identifies the data packets for the device and all other data packets are ignored. Cisco wireless 802.11b/g products use DSSS technology to support multiple devices on the WLAN.
- Orthogonal Frequency Division Multiplexing (OFDM)
Transmits signals by using RF. OFDM is a physical-layer encoding technology that breaks one high-speed data carrier into several lower-speed carriers to transmit in parallel across the RF spectrum. When used with 802.11g and 802.11a, OFDM can support data rates as high as 54 Mbps.
The following table provides a comparison of data rates, number of channels, and modulation technologies by standard.
AP Channel and Domain Relationships
APs transmit and receive RF signals over channels within the 2.4 GHz or 5 GHz frequency band. To provide a stable wireless environment and reduce channel interference, you must specify nonoverlapping channels for each AP. The recommended channels for 802.11b and 802.11g in North America are 1, 6, and 11.
Note
In a non-controller-based wireless network, we recommend that you statically configure channels for each AP. If your wireless network uses a controller, use the Auto-RF feature for minimal voice disruption.
For more information about AP channel and domain relationships, see Cisco Unified IP Phone 9971 Wireless LAN Deployment Guide at this location:
http://www.cisco.com/en/US/products/ps10453/products_implementation_design_guides_list.html
Related Information
WLANs and Roaming
The Cisco Unified IP Phone 9971 supports Cisco Centralized Key Management (CCKM), a centralized key management protocol, and provides a cache of session credentials on the wireless domain server (WDS). APs must register to the WDS for fast roaming to work. CCKM is also supported on the Cisco Unified Wireless LAN Controller alone.
The Cisco Unified IP Phone 9971 supports CCKM with 802.1x+WEP or WPA(TKIP) only. CCKM is not supported with WPA2 or WPA(AES). For details about CCKM, see the Cisco Fast Secure Roaming Application Note at:
http://www.cisco.com/en/US/products/hw/wireless/ps4570/prod_technical_reference09186a00801c5223.html
Bluetooth Wireless Technology
Bluetooth enables low-bandwidth wireless connections within a range of 30 feet (10 meters). The best performance is in the 3- to 6-foot (1- to 2-meter) range. Bluetooth wireless technology operates in the 2.4 GHz band, which is the same as the 802.11b/g band. Interference issues can occur. We recommend that you:
Related Information
VoIP Wireless Network Components
The Cisco Unified IP Phone must interact with several network components in the WLAN to successfully place and receive calls.
- Cisco Unified Wireless AP Interactions
- AP Association
- Voice QoS in Wireless Network
- Cisco Unified Communications Manager Interaction
Cisco Unified Wireless AP Interactions
Cisco Unified IP Phones use the same APs as wireless data devices. However, voice traffic over a WLAN requires different equipment configurations and layouts than a WLAN that is used exclusively for data traffic. Data transmission can tolerate a higher level of RF noise, packet loss, and channel contention than voice transmission. Packet loss during voice transmission can cause choppy or broken audio and can make the phone call inaudible. Packet errors can also cause blocky or frozen video.
Because the Cisco Unified IP Phone 9971 is a desktop (not mobile) phone, changes in the local environment can cause phones to roam between access points and can affect the voice and video performance. In contrast, data users remain in one place or occasionally move to another location. The ability to roam while maintaining a call is one of the advantages of wireless voice, so RF coverage needs to include stairwells, elevators, quiet corners outside conference rooms, and passageways.
To ensure good voice quality and optimal RF signal coverage, you must perform a site survey. The site survey determines settings that are suitable to wireless voice and assists in the design and layout of the WLAN; for example AP placement, power levels, and channel assignments.
After deploying and using wireless voice, you should continue to perform postinstallation site surveys. When you add a group of new users, install more equipment, or stack large amounts of inventory, you are changing the wireless environment. A postinstallation survey verifies that the AP coverage is still adequate for optimal voice communications.
Note
Packet loss occurs during roaming; however, the security mode and the presence of fast roaming determines how many packets are lost during transmission.
For more information about Voice QoS in a wireless network, see Cisco Unified IP Phone 9971 Wireless LAN Deployment Guide at:
http://www.cisco.com/en/US/products/ps10453/products_implementation_design_guides_list.html
AP Association
At startup, the Cisco Unified IP Phone scans for APs with SSIDs and encryption types that it recognizes. The phone builds and maintains a list of eligible APs and uses the following variables to determine the best AP:
- Received Signal Strength Indicator (RSSI):Signal strength of available APs within the RF coverage area. The phone attempts to associate with the AP with the highest RSSI value.
- Traffic Specification (TSpec): Calculation of call limits and WLAN load balancing. The TSpec value of each voice stream allows the system to allocate bandwidth to voice devices on a first-come, first-served basis.
The Cisco Unified IP Phone associates with the AP that has the highest RSSI and lowest channel usage values (QBSS) that posses matching SSID and encryption types. To ensure that voice traffic is handled properly, you must configure the correct QoS in the AP.
Voice QoS in Wireless Network
Voice traffic on the wireless LAN, like data traffic, is susceptible to delay, jitter, and packet loss. These issues do not impact the data end user, but can seriously impact a voice call. To ensure that voice traffic receives timely and reliable treatment with low delay and low jitter, you must use Quality of Service (QoS) and use separate virtual LANs (VLANs) for voice and data. By isolating the voice traffic onto a separate VLAN, you can use QoS to provide priority treatment for voice packets as they travel across the network. Also, use a separate VLAN for data traffic, not the default native VLAN that is typically used for all network devices.
You need the following VLANs on the network switches and the APs that support voice connections on the WLAN:
- Voice VLAN: Voice traffic to and from the wireless IP Phone
- Native VLAN: Data traffic to and from other wireless devices
Assign separate SSIDs to the voice and to the data VLANs. If you configure a separate management VLAN in the WLAN, do not associate an SSID with the management VLAN.
By separating the phones into a voice VLAN and marking voice packets with higher QoS, you can ensure that voice traffic gets priority treatment over data traffic, which results in lower packet delay and fewer lost packets.
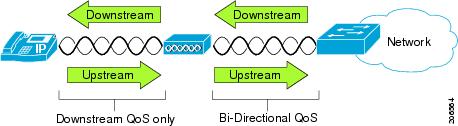
Unlike wired networks with dedicated bandwidths, wireless LANs consider traffic direction when implementing QoS. Traffic is classified as upstream or downstream from the point of view of the AP as shown in the following figure.
Beginning with Cisco IOS release 12.2(11)JA, Cisco Aironet APs support the contention-based channel access mechanism called Enhanced Distributed Coordination Function (EDCF). The EDCF type of QoS has up to eight queues for downstream (toward the 802.11b/g clients) QoS. You can allocate the queues based on these options:
- QoS or Differentiated Services Code Point (DSCP) settings for the packets
- Layer 2 or Layer 3 access lists
- VLANs for specific traffic
- Dynamic registration of devices
Although up to eight queues on the AP can be set up, you should use only two queues for voice traffic so as to ensure the best possible voice QoS. Place voice (RTP) and signaling (SCCP) traffic in the highest priority queue, and place data traffic in a best-effort queue. Although 802.11b/g EDCF does not guarantee that voice traffic is protected from data traffic, you should get the best statistical results by using this queuing model.
Note
The Cisco Unified IP Phone marks the SCCP signaling packets with a DSCP value of 24 (CS3) and RTP packets with DSCP value of 46 (EF).
To improve reliability of voice transmissions in a nondeterministic environment, the Cisco Unified IP Phone supports the IEEE 802.11e industry standard and is Wi-Fi Multimedia (WMM) capable. WMM enables differentiated services for voice, video, best effort data and other traffic. However, in order for these differentiated services to provide sufficient QoS for voice packets, only a certain amount of voice bandwidth can be serviced or admitted on a channel at one time. If the network can handle "N" voice calls with reserved bandwidth, when the amount of voice traffic is increased beyond this limit (to N+1 calls), the quality of all calls suffers.
To help address the problems of VoIP stability and roaming, an initial Call Admission Control (CAC) scheme is required. With CAC, QoS is maintained in a network overload scenario by ensuring that the number of active voice calls does not exceed the configured limits on the AP. The Cisco Unified IP Phone can integrate layer 2 TSpec admission control with layer 3 Cisco Unified Communications Manager admission control (RSVP). During times of network congestion, calling or called parties receive a fast busy indication. The system maintains a small bandwidth reserve so wireless phone clients can roam into a neighboring AP, even when the AP is at full capacity. After reaching the voice bandwidth limit, the next call is load-balanced to a neighboring AP without affecting the quality of the existing calls on the channel.
Implementing QoS in the connected Ethernet switch is highly desirable to maintain good voice quality. The COS and DSCP values that the Cisco Unified IP Phone sets do not need to be modified.
Note
The Cisco Unified IP Phone 9971 does not support Video CAC; however, Voice CAC is supported for WLANs.
Cisco Unified Communications Manager Interaction
Cisco Unified Communications Manager is the call control component in the network that handles and routes calls for the wireless IP phones. Cisco Unified Communications Manager manages the components of the IP telephony system (the phones, access gateways, and the resources) for such features as call conferencing and route planning. When you deploy a Cisco Unified IP Phone on a wireless LAN, you must use Cisco Unified Communications Manager Release 7.1(3) or later and the SIP protocol.
Before Cisco Unified Communications Manager can recognize a phone, the phone must register with Cisco Unified Communications Manager and be configured in the database.
You can find more information about configuring Cisco Unified Communications Manager to work with the IP phones and IP devices in the Cisco Unified Communications Manager Administration Guide and Cisco Unified Communications Manager System Guide.
Related Information
Security for Voice Communications in WLANs
Because all WLAN devices that are within range can receive all other WLAN traffic, securing voice communications is critical in WLANs. To ensure that intruders do not manipulate nor intercept voice traffic, the Cisco SAFE Security architecture supports the Cisco Unified IP Phone and Cisco Aironet APs. For more information about security in networks, see http://www.cisco.com/en/US/netsol/ns744/networking_solutions_program_home.html.
- Authentication Methods
- Authenticated Key Management
- Encryption Methods
- AP Authentication and Encryption Options
Authentication Methods
The Cisco Wireless IP telephony solution provides wireless network security that prevents unauthorized sign-ins and compromised communications by using the following authentication methods that the wireless Cisco Unified IP Phone 9971 supports:
- Open Authentication: Any wireless device can request authentication in an open system. The AP that receives the request may grant authentication to any requestor or only to requestors that are found on a list of users. Communication between the wireless device and AP could be nonencrypted or devices can use Wired Equivalent Privacy (WEP) keys to provide security. Devices that use WEP only attempt to authenticate with an AP that is using WEP.
- Shared Key Authentication: The AP sends an unencrypted challenge text string to any device that attempts to communicate with the AP. The device that is requesting authentication uses a preconfigured WEP key to encrypt the challenge text and sends it back to the AP. If the challenge text is encrypted correctly, the AP allows the requesting device to authenticate. A device can authenticate only if the device WEP key matches the WEP key on the APs. Shared key authentication can be less secure than open authentication with WEP because someone can monitor the challenges. An intruder can calculate the WEP key by comparing the unencrypted and encrypted challenge text strings.
- Extensible Authentication Protocol-Flexible Authentication via Secure Tunneling (EAP-FAST) Authentication: This client server security architecture encrypts EAP transactions within a Transport Level Security (TLS) tunnel between the AP and the RADIUS server, such as the Cisco Access Control Server (ACS). The TLS tunnel uses Protected Access Credentials (PACs) for authentication between the client (phone) and the RADIUS server. The server sends an Authority ID (AID) to the client (phone), which in turn selects the appropriate PAC. The client (phone) returns a PAC-Opaque to the RADIUS server. The server decrypts the PAC with the master key. Both endpoints now contain the PAC key and a TLS tunnel is created. EAP-FAST supports automatic PAC provisioning, but you must enable it on the RADIUS server.
Note
In the Cisco ACS, by default, the PAC expires in one week. If the phone has an expired PAC, authentication with the RADIUS server takes longer while the phone gets a new PAC. To avoid PAC provisioning delays, set the PAC expiration period to 90 days or longer on the ACS or RADIUS server.
- Light Extensible Authentication Protocol (LEAP): Cisco proprietary password-based mutual authentication scheme between the client (phone) and a RADIUS server. Cisco Unified IP Phone can use LEAP for authentication with the wireless network.
- Auto (AKM): Selects the 802.11 Authentication mechanism automatically from the configuration information that the AP, WPA-PSK, or WPA exhibits.
Authenticated Key Management
The following authentication schemes use the RADIUS server to manage authentication keys:
- WPA/WPA2: Uses RADIUS server information to generate unique keys for authentication. Because these keys are generated at the centralized RADIUS server, WPA/WPA2 provides more security than WPA preshared keys that are stored on the AP and phone.
- Cisco Centralized Key Management (CCKM): Uses RADIUS server and a wireless domain server (WDS) information to manage and authenticate keys. The WDS creates a cache of security credentials for CCKM-enabled client devices for fast and secure reauthentication.
With WPA/WPA2 and CCKM, encryption keys are not entered on the phone, but are automatically derived between the AP and phone. But the EAP username and password that are used for authentication must be entered on each phone.
Note
Only WPA(TKIP) and 802.1x(WEP) support CCKM.
Encryption Methods
To ensure that voice traffic is secure, the Cisco Unified IP Phone supports WEP, TKIP, and Advanced Encryption Standards (AES) for encryption. When these mechanisms are used for encryption, both the signalling Skinny Client Control Protocol (SCCP) packets and voice Real-Time Transport Protocol (RTP) packets are encrypted between the AP and the Cisco Unified IP Phone.
- WEP
With WEP use in the wireless network, authentication happens at the AP by using open or shared-key authentication. The WEP key that is setup on the phone must match the WEP key that is configured at the AP for successful connections. The Cisco Unified IP Phone supports WEP keys that use 40-bit encryption or a 128-bit encryption and remain static on the phone and AP.
EAP and CCKM authentication can use WEP keys for encryption. The RADIUS server manages the WEP key and passes a unique key to the AP after authentication for encrypting all voice packets; consequently, these WEP keys can change with each authentication.
- TKIP
WPA and CCKM use TKIP encryption that has several improvements over WEP. TKIP provides per-packet key ciphering and longer initialization vectors (IVs) that strengthen encryption. In addition, a message integrity check (MIC) ensures that encrypted packets are not being altered. TKIP removes the predictability of WEP that helps intruders decipher the WEP key.
- AES
An encryption method used for WPA2 authentication. This national standard for encryption uses a symmetrical algorithm that has the same key for encryption and decryption. AES uses Cipher Blocking Chain (CBC) encryption of 128 bits in size, which supports key sizes of 128, 192 and 256 bits, as a minimum. The Cisco Unified IP Phone supports a key size of 256 bits.
Note
The Cisco Unified IP Phone does not support Cisco Key Integrity Protocol (CKIP) with CMIC.
AP Authentication and Encryption Options
Authentication and encryption schemes are set up within the wireless LAN. VLANs are configured in the network and on the APs and specify different combinations of authentication and encryption. An SSID associates with a VLAN and the particular authentication and encryption scheme. In order for wireless client devices to authenticate successfully, you must configure the same SSIDs with their authentication and encryption schemes on the APs and on the Cisco Unified IP Phone.
Some authentication schemes require specific types of encryption. With Open authentication, you can use static WEP for encryption for added security. But if you are using Shared Key authentication, you must set static WEP for encryption, and you must configure a WEP key on the phone.
When you use Authenticated Key Management (AKM) for the Cisco Unified IP Phone, several choices for both authentication and encryption can be set up on the APs with different SSIDs. When the phone attempts to authenticate, it chooses the AP that advertises the authentication and encryption scheme that the phone can support. Auto (AKM) mode can authenticate by using WPA, WPA2, WPA Pre-shared key, or CCKM.
The following table provides a list of authentication and encryption schemes that are configured on the Cisco Aironet APs that the Cisco Unified IP Phone supports. The table shows the network configuration option for the phone that corresponds to the AP configuration.
Table 3 Authentication and Encryption Schemes Cisco AP configuration
Cisco Unified IP Phone configuration
Authentication
Key management
Common encryption
Authentication
Open
None
Open
Open (Static WEP)
WEP
Open+WEP
Shared key (Static WEP)
WEP
Shared+WEP
LEAP
802.1x
Optional CCKM
WEP
LEAP or Auto (AKM)
LEAP
WPA
WPA with optional CCKM
TKIP
LEAP or Auto (AKM)
LEAP
WPA2
WPA2
AES
LEAP or Auto (AKM)
EAP-FAST
802.1x
Optional CCKM
WEP
EAP-FAST
EAP-FAST with WPA
WPA
Optional CCKM
TKIP
EAP-FAST
EAP-FAST with WPA2
WPA2
AES
EAP-FAST
WPA-PSK
WPA-PSK
TKIP
Auto (AKM)
WPA2-PSK
WAP2-PSK
AES
Auto (AKM)
For additional information about Cisco WLAN Security, see http://www.cisco.com/en/US/products/hw/wireless/ps430/prod_brochure09186a00801f7d0b.html.
For more information about configuring authentication and encryption schemes on APs, see the Cisco Aironet Configuration Guide for your model and release under the following URL:
http://www.cisco.com/cisco/web/psa/configure.html?mode=prod&level0=278875243
VoIP WLAN Deployment
Supported Access Points
Supported APs and Modes
The following table lists the modes that each Cisco Access Point supports.
Table 4 Supported APs and Modes AP models
802.11b
802.11g
802.11a
Autonomous mode
Unified mode
Cisco Aironet 500 Series
Yes
Yes
No
Yes
Yes
Cisco Aironet 1100 Series
Yes
Yes
No
Yes
Yes
Cisco Aironet 1130 AG Series
Yes
Yes
Yes
Yes
Yes
Cisco Aironet 1140 Series
Yes
Yes
Yes
Yes
Yes
Cisco Aironet 1200 Series
Yes
Yes
Optional
Yes
Yes
Cisco Aironet 1230 AG Series
Yes
Yes
Yes
Yes
Yes
Cisco Aironet 1240 AG Series
Yes
Yes
Yes
Yes
Yes
Cisco Aironet 1250 Series
Yes
Yes
Yes
Yes
Yes
Cisco Aironet 1300 Series
Yes
Yes
No
Yes
Yes
NoteThe Cisco Unified IP Phone 9971 does not support Voice over the Wireless LAN (VoWLAN) via Outdoor MESH technology (Cisco 1500 series).
No support exists for third-party access points because no interoperability testing occurs with these access points. However, if the access point supports the key features and follows the standards, the Cisco Unified Wireless IP Phone is compliant.
Wi-Fi compliant APs that are manufactured by third-party vendors support the Cisco Unified Wireless IP Phone 9971, but might not support key features such as Wi-Fi MultiMedia (WMM), Unscheduled Auto Power Save Delivery (U-APSD), Traffic Specification (TSPEC), QoS Basic Service Set (QBSS), Dynamic Transmit Power Control (DTPC), or proxy ARP.
Supported Antennas
Some Cisco access points require or allow external antennas. See the following URL for the list of supported antennas and how these external antennas should be mounted:
http://www.cisco.com/en/US/prod/collateral/wireless/ps7183/ps469/product_data_sheet09186a008008883b.html
NoteThe Cisco Aironet Series 1130 and 1140 access points must be mounted on the ceiling because they possess omnidirectional antennas.
Set Up Wireless LAN
Ensure that the Wi-Fi coverage in the location where the wireless LAN is deployed is suitable for transmitting video and voice packets.
If the Wi-Fi connectivity for voice and video is enabled for the Cisco Unified IP Phone 9971, you authenticate the Wi-Fi network by using the WLAN Sign in application within your applications menu.
To enable the application, go to and enable WLAN network.
To change the username or password, go to .
For complete configuration information, see the Cisco Unified IP Phone 9971 Wireless LAN Deployment Guide at this location:
http://www.cisco.com/en/US/products/ps10453/products_implementation_design_guides_list.html
The Cisco Unified IP Phone 9971 Wireless LAN Deployment Guide includes the following configuration information:
Set Up Wireless LAN in Cisco Unified Communications Manager Administration
In Cisco Unified Communications Manager Administration, you must enable a parameter called "Wi-Fi" for the wireless Cisco Unified IP Phone 9971. This can be done in one of the following locations in Cisco Unified Communications Manager Administration:
- To enable wireless LAN on a specific phone, select the enable setting for the Wi-Fi parameter in the Product Specific Configuration Layout section () for the specific phone, and check the Override Common Settings check box.
- To enable wireless LAN for a group of phones, select the enable setting for the Wi-Fi parameter in a Common Phone Profile Configuration window (), check the Override Common Settings check box, then associate the phone () with that common phone profile.
- To enable wireless LAN for all WLAN-capable phones in your network, select the enable setting for the Wi-Fi parameter in the Enterprise Phone Configuration window (), and check the Override Common Settings check box.
Note
In the Phone Configuration window in Cisco Unified Communications Manager Administration (), use the wired-line MAC address when you configure the MAC address. Cisco Unified Communications Manager registration does not use the wireless MAC address.
Wireless LAN on Cisco Unified IP Phone Setup
Before the phone can connect to the WLAN, you must configure the network profile for the phone with the appropriate WLAN settings. You can use the Network Setup menu on the phone to access the WLAN Setup submenu and set up the WLAN configuration.
Related References

 Feedback
Feedback