Contents
- Configuring IPv6 Client IP Address Learning
- Prerequisites for IPv6 Client Address Learning
- Information About IPv6 Client Address Learning
- SLAAC Address Assignment
- Stateful DHCPv6 Address Assignment
- Static IP Address Assignment
- Router Solicitation
- Router Advertisement
- Neighbor Discovery
- Neighbor Discovery Suppression
- RA Guard
- RA Throttling
- Configuring IPv6 Unicast (CLI)
- Configuring RA Guard Policy (CLI)
- Applying RA Guard Policy (CLI)
- Configuring RA Throttle Policy (CLI)
- Applying RA Throttle Policy on VLAN (CLI)
- Configuring IPv6 Snooping (CLI)
- Configuring IPv6 ND Suppress Policy (CLI)
- Configuring IPv6 Snooping on VLAN/PortChannel
- Configuring IPv6 on Switch (CLI)
- Configuring DHCP Pool (CLI)
- Configuring Stateless Auto Address Configuration Without DHCP (CLI)
- Configuring Stateless Auto Address Configuration With DHCP (CLI)
- Configuring Stateful DHCP Locally (CLI)
- Configuring Stateful DHCP Externally (CLI)
- Monitoring IPv6 Clients (GUI)
- Verifying IPv6 Address Learning Configuration
- Additional References
- Feature Information for IPv6 Client Address Learning
Configuring IPv6 Client IP Address Learning
Information About IPv6 Client Address Learning
Client Address Learning is configured on switch to learn the wireless client's IPv4 and IPv6 address and clients transition state maintained by the switch on an association, re-association, de-authentication and timeout.
There are three ways for IPv6 client to acquire IPv6 addresses:
For all of these methods, the IPv6 client always sends neighbor solicitation DAD (Duplicate Address Detection) request to ensure there is no duplicate IP address on the network. The switch snoops the client's NDP and DHCPv6 packets to learn about its client IP addresses.
- SLAAC Address Assignment
- Stateful DHCPv6 Address Assignment
- Static IP Address Assignment
- Router Solicitation
- Router Advertisement
- Neighbor Discovery
- Neighbor Discovery Suppression
- RA Guard
- RA Throttling
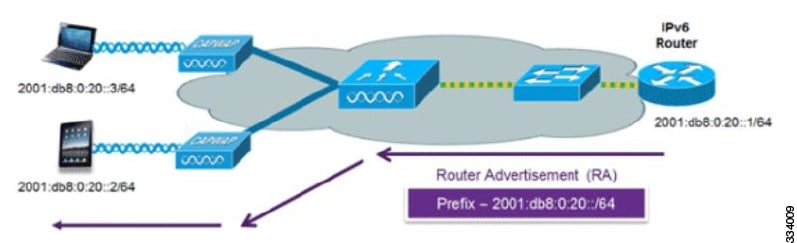
SLAAC Address Assignment
The most common method for IPv6 client address assignment is Stateless Address Auto-Configuration (SLAAC). SLAAC provides simple plug-and-play connectivity where clients self-assign an address based on the IPv6 prefix. This process is achieved
Stateless Address Auto-Configuration (SLAAC) is configured as follows:
- Host sends a router solicitation message.
- Hosts waits for a Router Advertisement message.
- Hosts take the first 64 bits of the IPv6 prefix from the Router Advertisement message and combines it with the 64 bit EUI-64 address (in the case of ethernet, this is created from the MAC Address) to create a global unicast message. The host also uses the source IP address, in the IP header, of the Router Advertisement message, as its default gateway.
- Duplicate Address Detection is performed by IPv6 clients in order to ensure that random addresses that are picked do not collide with other clients.
- The choice of algorithm is up to the client and is often configurable.
The last 64 bits of the IP v6 address can be learned based on the following 2 algorithms:
The following Cisco IOS configuration commands from a Cisco-capable IPv6 router are used to enable SLAAC addressing and router advertisements:
ipv6 unicast-routing interface Vlan20 description IPv6-SLAAC ip address 192.168.20.1 255.255.255.0 ipv6 address FE80:DB8:0:20::1 linklocal ipv6 address 2001:DB8:0:20::1/64 ipv6 enable endStateful DHCPv6 Address Assignment
The use of DHCPv6 is not required for IPv6 client connectivity if SLAAC is already deployed. There are two modes of operation for DHCPv6 called Stateless and Stateful.
The DHCPv6 Stateless mode is used to provide clients with additional network information that is not available in the router advertisement, but not an IPv6 address as this is already provided by SLAAC. This information can include the DNS domain name, DNS server(s), and other DHCP vendor-specific options. This interface configuration is for a Cisco IOS IPv6 router implementing stateless DHCPv6 with SLAAC enabled:
ipv6 unicast-routing ipv6 dhcp pool IPV6_DHCPPOOL address prefix 2001:db8:5:10::/64 domain-name cisco.com dns-server 2001:db8:6:6::1 interface Vlan20 description IPv6-DHCP-Stateless ip address 192.168.20.1 255.255.255.0 ipv6 nd other-config-flag ipv6 dhcp server IPV6_DHCPPOOL ipv6 address 2001:DB8:0:20::1/64 endThe DHCPv6 Stateful option, also known as managed mode, operates similarly to DHCPv4 in that it assigns unique addresses to each client instead of the client generating the last 64 bits of the address as in SLAAC. This interface configuration is for a Cisco IOS IPv6 router implementing stateful DHCPv6 on a local Switch:
ipv6 unicast-routing ipv6 dhcp pool IPV6_DHCPPOOL address prefix 2001:db8:5:10::/64 domain-name cisco.com dns-server 2001:db8:6:6::1 interface Vlan20 description IPv6-DHCP-Stateful ip address 192.168.20.1 255.255.255.0 ipv6 address 2001:DB8:0:20::1/64 ipv6 nd prefix 2001:DB8:0:20::/64 no-advertise ipv6 nd managed-config-flag ipv6 nd other-config-flag ipv6 dhcp server IPV6_DHCPPOOL endThis interface configuration is for a Cisco IOS IPv6 router implementing stateful DHCPv6 on an external DHCP server:
ipv6 unicast-routing domain-name cisco.com dns-server 2001:db8:6:6::1 interface Vlan20 description IPv6-DHCP-Stateful ip address 192.168.20.1 255.255.255.0 ipv6 address 2001:DB8:0:20::1/64 ipv6 nd prefix 2001:DB8:0:20::/64 no-advertise ipv6 nd managed-config-flag ipv6 nd other-config-flag ipv6 dhcp_relay destination 2001:DB8:0:20::2 endRouter Solicitation
A Router Solicitation message is issued by a host controller to facilitate local routers to transmit Router Advertisement from which it can obtain information about local routing or perform Stateless Auto-configuration. Router Advertisements are transmitted periodically and the host prompts with an immediate Router Advertisement using a Router Solicitation such as - when it boots or following a restart operation.
Related Tasks
Router Advertisement
A Router Advertisement message is issued periodically by a router or in response to a Router Solicitation message from a host. The information contained in these messages is used by hosts to perform Stateless Auto-configuration and to modify its routing table.
Related Tasks
Neighbor Discovery
IPv6 Neighbor Discovery is a set of messages and processes that determine relationships between neighboring nodes. Neighbor Discovery replaces ARP, ICMP Router Discovery, and ICMP Redirect used in IPv4.
IPv6 Neighbor Discovery inspection analyzes neighbor discovery messages in order to build a trusted binding table database, and IPv6 neighbor discovery packets that do not comply are dropped. The neighbor binding table in the switch tracks each IPv6 address and its associated MAC address. Clients are expired from the table according to Neighbor Binding timers.
Related Tasks
Neighbor Discovery Suppression
The IPv6 addresses of wireless clients are cached by the switch. When the switch receives an NS multicast looking for an IPv6 address, and if the target address is known to the switch and belongs to one of its clients, the switch will reply with an NA message on behalf of the client. The result of this process generates the equivalent of the Address Resolution Protocol (ARP) table of IPv4 but is more efficient - uses generally fewer messages.
Note
The switch acts like proxy and respond with NA, only when the ipv6 nd suppress command is configuredIf the switch does not have the IPv6 address of a wireless client, the switch will not respond with NA and forward the NS packet to the wireless side. To resolve this, an NS Multicast Forwarding knob is provided. If this knob is enabled, the switch gets the NS packet for the IPv6 address that it does not have (cache miss) and forwards it to the wireless side. This packet reaches the intended wireless client and the client replies with NA.
This cache miss scenario occurs rarely, and only very few clients which do not implement complete IPv6 stack may not advertise their IPv6 address during NDP.
Related Tasks
RA Guard
IPv6 clients configure IPv6 addresses and populate their router tables based on IPv6 router advertisement (RA) packets. The RA guard feature is similar to the RA guard feature of wired networks. RA guard increases the security of the IPv6 network by dropping the unwanted or rogue RA packets that come from wireless clients. If this feature is not configured, malicious IPv6 wireless clients announce themselves as the router for the network often with high priority, which would take higher precedence over legitimate IPv6 routers.
RA-Guard also examines the incoming RA's and decides whether to switch or block them based solely on information found in the message or in the switch configuration. The information available in the frames received is useful for RA validation:The following configuration information created on the switch is available to RA-Guard to validate against the information found in the received RA frame:
RA guard occurs at the switch. You can configure the switch to drop RA messages at the switch. All IPv6 RA messages are dropped, which protects other wireless clients and upstream wired network from malicious IPv6 clients.
//Create a policy for RA Guard// ipv6 nd raguard policy raguard-router trusted-port device-role router//Applying the RA Guard Policy on port/interface// interface tengigabitethernet1/0/1 (Katana) interface gigabitethernet1/0/1 (Edison) ipv6 nd raguard attach-policy raguard-routerRA Throttling
RA throttling allows the controller to enforce limits to RA packets headed toward the wireless network. By enabling RA throttling, routers that send many RA packets can be trimmed to a minimum frequency that will still maintain an IPv6 client connectivity. If a client sends an RS packet, an RA is sent back to the client. This RA is allowed through the controller and unicasted to the client. This process ensures that the new clients or roaming clients are not affected by the RA throttling.
Configuring IPv6 Unicast (CLI)
IPv6 unicasting must always be enabled on the switch and the controller. IPv6 unicast routing is disabled.
Before You BeginSUMMARY STEPSTo enable the forwarding of IPv6 unicast datagrams, use the ipv6 unicast-routing command in global configuration mode. To disable the forwarding of IPv6 unicast datagrams, use the no form of this command.
DETAILED STEPS
Command or Action Purpose Configuring RA Guard Policy (CLI)
SUMMARY STEPSConfigure RA Guard policy on the switch to add IPv6 client addresses and populate the router table based on IPv6 router advertisement packets.
2. ipv6 nd raguard policy raguard-router
3. trustedport
4. device-role router
5. exit
DETAILED STEPSRelated Concepts
Related References
Applying RA Guard Policy (CLI)
SUMMARY STEPS
2. interface tengigabitethernet 1/0/1
3. ipv6 nd raguard attach-policy raguard-router
4. exit
DETAILED STEPSRelated Concepts
Related Tasks
Configuring RA Throttle Policy (CLI)
SUMMARY STEPS
2. ipv6 nd ra-throttler policy ra-throttler1
3. throttleperiod500
4. max-through10
5. allow-atleast 5 at-most 10
DETAILED STEPSApplying RA Throttle Policy on VLAN (CLI)
SUMMARY STEPSApplying the RA Throttle policy on a VLAN. By enabling RA throttling, routers that send many RA packets can be trimmed to a minimum frequency that will still maintain an IPv6 client connectivity.
DETAILED STEPSConfiguring IPv6 Snooping (CLI)
SUMMARY STEPS
1. vlan configuration 1
2. ipv6 snooping
3. ipv6 nd suppress
4. exit
DETAILED STEPSConfiguring IPv6 ND Suppress Policy (CLI)
SUMMARY STEPSThe IPv6 neighbor discovery (ND) multicast suppress feature stops as many ND multicast neighbor solicit (NS) messages as possible by dropping them (and responding to solicitations on behalf of the targets) or converting them into unicast traffic. This feature runs on a layer 2 switch or a wireless controller and is used to reduce the amount of control traffic necessary for proper link operations.
When an address is inserted into the binding table, an address resolution request sent to a multicast address is intercepted, and the device either responds on behalf of the address owner or, at layer 2, converts the request into a unicast message and forwards it to its destination.
DETAILED STEPSConfiguring IPv6 Snooping on VLAN/PortChannel
SUMMARY STEPS
1. vlan config901
2. ipv6 nd suppress
3. end
4. interface gi1/0/1
5. ipv6 nd suppress
6. end
DETAILED STEPSConfiguring IPv6 on Switch (CLI)
SUMMARY STEPS
1. interface vlan 1
2. ip address fe80::1 link-local
3. ipv6 enable
4. end
DETAILED STEPSConfiguring DHCP Pool (CLI)
SUMMARY STEPS
1. ipv6 dhcp pool Vlan21
2. address prefix 2001:DB8:0:1:FFFF:1234::/64 lifetime 300 10
3. dns-server 2001:100:0:1::1
4. domain-name example.com
5. end
DETAILED STEPSConfiguring Stateless Auto Address Configuration Without DHCP (CLI)
SUMMARY STEPS
1. interface vlan 1
2. ip address fe80::1 link-local
3. ipv6 enable
4. no ipv6 nd managed-config-flag
5. no ipv6 nd other-config-flag
6. end
DETAILED STEPSConfiguring Stateless Auto Address Configuration With DHCP (CLI)
SUMMARY STEPS
1. interface vlan 1
2. ip address fe80::1 link-local
3. ipv6 enable
4. no ipv6 nd managed-config-flag
5. ipv6 nd other-config-flag
6. end
DETAILED STEPSConfiguring Stateful DHCP Locally (CLI)
SUMMARY STEPSThis interface configuration is for a Cisco IOS IPv6 router implementing stateful DHCPv6 on a local Switch
2. ipv6 unicast-routing
3. ipv6 dhcp pool IPv6_DHCPPOOL
4. address prefix 2001:DB8:0:1:FFFF:1234::/64
5. dns-server 2001:100:0:1::1
6. domain-name example.com
7. exit
8. interface vlan1
9. description IPv6-DHCP-Stateful
10. ipv6 address 2001:DB8:0:20::1/64
11. ip address 192.168.20.1 255.255.255.0
12. ipv6 nd prefix 2001:db8::/64 no-advertise
13. ipv6 nd managed-config-flag
14. ipv6 nd other-config-flag
15. ipv6 dhcp server IPv6_DHCPPOOL
DETAILED STEPSConfiguring Stateful DHCP Externally (CLI)
SUMMARY STEPSThis interface configuration is for a Cisco IOS IPv6 router implementing stateful DHCPv6 on an external DHCP server.
2. ipv6 unicast-routing
3. dns-server 2001:100:0:1::1
4. domain-name example.com
5. exit
6. interface vlan1
7. description IPv6-DHCP-Stateful
8. ipv6 address 2001:DB8:0:20::1/64
9. ip address 192.168.20.1 255.255.255.0
10. ipv6 nd prefix 2001:db8::/64 no-advertise
11. ipv6 nd managed-config-flag
12. ipv6 nd other-config-flag
13. ipv6 dhcp_relaydestination 2001:DB8:0:20::2
DETAILED STEPSMonitoring IPv6 Clients (GUI)
Verifying IPv6 Address Learning Configuration
SUMMARY STEPSThis example displays the output of the show ipv6 dhcp pool command. This command displays the IPv6 service configuration on the switch. The vlan 21 configured pool detail displays 6 clients that are currently using addresses from the pool.
1. show ipv6 dhcp pool
DETAILED STEPSAdditional References
Error Message Decoder
Description Link To help you research and resolve system error messages in this release, use the Error Message Decoder tool.
https://www.cisco.com/cgi-bin/Support/Errordecoder/index.cgi
MIBs
Technical Assistance
Description Link The Cisco Support website provides extensive online resources, including documentation and tools for troubleshooting and resolving technical issues with Cisco products and technologies.
To receive security and technical information about your products, you can subscribe to various services, such as the Product Alert Tool (accessed from Field Notices), the Cisco Technical Services Newsletter, and Really Simple Syndication (RSS) Feeds.
Access to most tools on the Cisco Support website requires a Cisco.com user ID and password.

 Feedback
Feedback