Feedback Feedback
|
Table Of Contents
Configuring Cisco Subscriber Service Switch Policies
Prerequisites for Configuring a Subscriber Service Switch Policy
Restrictions for Configuring a Subscriber Service Switch Policy
Information About the Subscriber Service Switch
Benefits of the Subscriber Service Switch
Backward Compatibility of Subscriber Service Switch Policies
Debug Commands Available for Subscriber Service Switch
How to Configure a Subscriber Service Switch Policy
Enabling Domain Preauthorization on a NAS
Creating a RADIUS User Profile for Domain Preauthorization
Enabling a Subscriber Service Switch Preauthorization
Troubleshooting the Subscriber Service Switch
Configuration Examples for Configuring a Subscriber Service Switch Policy
LAC Domain Authorization: Example
Domain Preauthorization RADIUS User Profile: Example
Subscriber Service Switch Preauthorization: Example
Verify Subscriber Service Switch Call Operation: Example
Troubleshooting the Subscriber Service Switch: Examples
Troubleshooting the Subscriber Service Switch Operation: Example
Troubleshooting the Subscriber Service Switch on the LAC—Normal Operation: Example
Troubleshooting the Subscriber Service Switch on the LAC—Authorization Failure: Example
Troubleshooting the Subscriber Service Switch on the LAC—Authentication Failure: Example
Troubleshooting the Subscriber Service Switch on the LNS—Normal Operation: Example
Troubleshooting the Subscriber Service Switch on the LNS—Tunnel Failure: Example
Feature Information for Configuring a Subscriber Service Switch Policy
Configuring Cisco Subscriber Service Switch Policies
First Published: May 2, 2005Last Updated: January 2, 2008The Subscriber Service Switch provides the framework for the management and scalability of PPP sessions that are switched from one virtual PPP link to another. It gives Internet service providers (ISPs) the flexibility to determining which services to provide to subscribers, the number of subscribers, and how to define the services. The primary focus of the Subscriber Service Switch is to direct PPP from one point to another using a Layer 2 subscriber policy. The policy manages tunneling of PPP in a policy-based bridging fashion.
Finding Feature Information in This Module
Your Cisco IOS software release may not support all of the features documented in this module. For the latest feature information and caveats, see the release notes for your Cisco IOS software release. To reach links to specific feature documentation in this module and to see a list of the releases in which each feature is supported, use the "Feature Information for Configuring a Subscriber Service Switch Policy" section.
Finding Support Information for Platforms and Cisco IOS and Catalyst OS Software Images
Use Cisco Feature Navigator to find information about platform support and Cisco IOS and Catalyst OS software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Contents
•
Prerequisites for Configuring a Subscriber Service Switch Policy
•
Restrictions for Configuring a Subscriber Service Switch Policy
•
Information About the Subscriber Service Switch
•
How to Configure a Subscriber Service Switch Policy
•
Configuration Examples for Configuring a Subscriber Service Switch Policy
•
Feature Information for Configuring a Subscriber Service Switch Policy
Prerequisites for Configuring a Subscriber Service Switch Policy
•
Before configuring a Subscriber Service Switch policy, you must understand the concepts presented in the "Understanding Broadband Access Aggregation" module.
•
Before configuring a Subscriber Service Switch policy, you must perform the PPP over Ethernet (PPPoE) configuration procedures in the "Providing Protocol Support for Broadband Access Aggregation of PPPoE Sessions" module or perform the PPP over ATM (PPPoA) configuration procedures in the "Providing Protocol Support for Broadband Access Aggregation of PPP over ATM Sessions" module.
Restrictions for Configuring a Subscriber Service Switch Policy
The Subscriber Service Switch provides the framework for the management and scalability of PPP sessions that are switched from one virtual PPP link to another. The Subscriber Server Switch provides the infrastructure for any protocol to plug into; however, the initial implementation provides switching PPP over Ethernet and PPP over ATM session to a Layer 2 Tunneling Protocol (L2TP) device such as an L2TP access concentrator (LAC) switch, and switching L2TP sessions to an L2TP tunnel switch only.
Information About the Subscriber Service Switch
The Subscriber Service Switch was developed in response to a need by Internet service providers (ISPs) for increased scalability and extensibility for remote access service selection and Layer 2 subscriber policy management. This Layer 2 subscriber policy is needed to manage tunneling of PPP in a policy-based bridging fashion.
To configure the Cisco Subscriber Server Switch policy, you should understand the following concepts:
•
Benefits of the Subscriber Service Switch
•
Backward Compatibility of Subscriber Service Switch Policies
•
Debug Commands Available for Subscriber Service Switch
Benefits of the Subscriber Service Switch
The Subscriber Service Switch provides the framework for the management and scalability of PPP sessions that are switched from one virtual PPP link to another. It gives Internet service providers (ISPs) the flexibility to determining which services to provide to subscribers, the number of subscribers, and how to define the services. In the past, remote access service selection was largely determined by the telephone number dialed or the PPP username and password entered during a PPP authentication cycle. However, broadband, cable, Virtual Private Network (VPN), and wireless access methods have created an environment where PPP sessions may be tunneled over a variety of protocols and media. The multitude of protocols, management domains, network infrastructure, and variety of services has created a complex environment for directing a subscriber to a given service or application. The problem is further complicated by the much greater density of total PPP sessions that can be transported over shared media versus traditional point-to-point links. The Subscriber Service Switch can provide a flexible and extensible decision point linking an incoming subscriber (typically a PPP session over some physical or virtual link) to another tunneled link or local termination for Layer 3 processing.
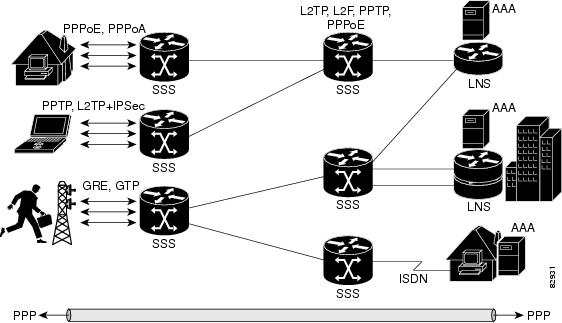
The Subscriber Service Switch is also scalable in situations where a subscriber's Layer 2 service is switched across virtual links. Examples include switching among PPPoA, PPPoE, L2TP, Layer 2 Forwarding Protocol (L2F), Point-to-Point Tunneling Protocol (PPTP), generic routing encapsulation (GRE), and General Packet Radio Service (GPRS) Tunneling Protocol (GTP wireless data standard).
Figure 1 shows how the Subscriber Service Switch provides its own centralized switching path that bypasses the virtual-access-based switching available in previous releases. In Figure 1, the Subscriber Service Switch is switching data traffic from personal computers in a home and corporate office and from a wireless user.
Figure 1 Basic Subscriber Service Switch Operation
Protocols that register with the Subscriber Service Switch application programming interface (API) can take advantage of this switching path. Bypassing the virtual access interface in this manner helps the Cisco IOS software to scale to the increased number of sessions that the market demands. The Subscriber Service Switch also improves network performance. For example, benchmark testing indicates that performance of L2TP multihop tasks occurs twice as fast in networks with the Subscriber Service Switch as in networks without it.
Backward Compatibility of Subscriber Service Switch Policies
All of the existing virtual private dialup network (VPDN), Multichassis Multilink PPP (MMLP), and local termination policies and configurations are maintained in the implementation of the Subscriber Service Switch; however, default policies may be overridden by the following configurations or events:
•
Resource Manager (RM) VPDN authorization is attempted before VPDN authorization.
•
VPDN authorization is attempted before Stack Group Forwarding (SGF) MMLP.
•
VPDN service authorization is attempted only when the vpdn enable command is configured.
•
RM VPDN service authorization is attempted only if RM is enabled.
•
SGF authorization is attempted only when the sgbp member command is configured and one or both of the following service keys are available from the subscriber: unauthenticated PPP name and endpoint discriminator.
•
The dnis and domain service keys, in that order, are used to authorize VPDN service, provided that VPDN service is enabled.
•
An unauthenticated PPP name is always reduced to a domain name by taking all characters from the right of the PPP name up to a configurable delimiter character (default is the @ character). Only the domain portion is used to locate a service.
•
If the vpdn authen-before-forward command is configured as a global configuration command, the authenticated PPP name is used to authorize VPDN service.
•
The vpdn-group command can define four configurations:
1.
Authorization for VPDN call termination (using the accept-dialin and accept-dialout keywords).
2.
Authorization for VPDN subscriber service (using the request-dialin and request-dialout keywords).
3.
A directive to collect further service keys and reauthorize (using the authen-before-forward keyword).
4.
A tunnel configuration.
The Subscriber Service Switch adds a general configuration framework to replace the first three aspects of a VPDN group.
•
If VPDN and SGF services either are not configured or cannot be authorized, local PPP termination service is selected. Further PPP authorization is still required to complete local termination.
•
A two-phase authorization scheme is enabled by the vpn domain authorization command. An NAS-Port-ID (NAS port identifier) key is used to locate the first service record, which contains a restricted set of values for the domain substring of the unauthenticated PPP name. This filtered service key then locates the final service. Cisco refers to this scheme as domain preauthorization.
•
Domain preauthorization will occur only when the NAS-Port-ID key is available.
•
When domain preauthorization is enabled, both authenticated and unauthenticated domain names are checked for restrictions.
•
It is possible to associate a fixed service with an ATM permanent virtual circuit (PVC), thus affecting any subscribers carried by the PVC. The vpn service command, in ATM VC or VC class configuration mode, and the associated key make up the generic service key.
•
When the generic service key is available, it will be used for authorization instead of the unauthenticated domain name.
•
If either the vpdn authen-before-forward or per vpdn-group authen-before-forward command is configured, the authenticated username is required and will be used to authorize VPDN service.
•
To determine whether the authen-before-forward command is configured in a VPDN group (using the vpdn-group command), an unauthenticated username or the generic service key is required as the initial-want key set.
•
When the global vpdn authen-before-forward command is not configured, the generic service key, if one is available, is used to determine whether the authen-before-forward function is configured in the VPDN group (using the vpdn-group command). If the generic service key is not available, the unauthenticated username will be used.
•
If an accounting-enabled key is available, the unauthenticated username is required.
•
VPDN multihop is allowed only when VPDN multihop is enabled.
•
SGF on the L2TP network server (LNS) is allowed only when VPDN multihop is enabled on the LNS.
•
Forwarding of SGF calls on the LAC is allowed only if VPDN multihop is enabled on the LAC.
•
SGF-to-SGF multihop is not allowed.
•
When PPP forwarding is configured, both Multilink PPP (MLP) and non-MLP calls are forwarded to the winner of the Stack Group Bidding Protocol (SGBP) bid.
•
Authentication is always required for forwarded Packet Data Serving Node (PDSN) calls.
•
When the directed-request function is enabled and activated using the ip host command, VPDN service authorization occurs only when the vpdn authorize directed-request command is used.
•
Fixed legacy policy is still maintained for RM.
Debug Commands Available for Subscriber Service Switch
The Subscriber Service Switch feature introduces five new EXEC mode debug commands to enable diagnostic output about Subscriber Service Switch call operation, as follows:
•
debug sss aaa authorization event—Displays messages about AAA authorization events that are part of normal call establishment.
•
debug sss aaa authorization fsm—Displays messages about AAA authorization state changes.
•
debug sss error—Displays diagnostic information about errors that may occur during Subscriber Service Switch call setup.
•
debug sss event—Displays diagnostic information about Subscriber Service Switch call setup events.
•
debug sss fsm—Displays diagnostic information about the Subscriber Service Switch call setup state.
The following EXEC mode debug commands already exist:
•
debug redundancy- This command is available on platforms that support redundancy.
•
debug sss elog—Collects SSS performance event data.
•
debug sss feature—Enables debug for SSS feature events
•
debug sss packet—Enables packet level event and information debugging for the Subscriber Service Switch.
•
debug sss policy—Enables debug for SSS policy module events.
•
debug sss service—Enables debug for service manager event.
These commands were designed to be used with Cisco IOS debug commands that exist for troubleshooting PPP and other Layer 2 call operations. Table 2 lists some of these debug commands.
Table 1 Additional Debugging Commands for Troubleshooting the Subscriber Service Switch
Note
The debug commands are intended only for troubleshooting purposes, because the volume of output generated by the software can result in severe performance degradation on the router.
How to Configure a Subscriber Service Switch Policy
The Subscriber Service Switch architecture is transparent, and existing PPP, VPDN, PPPoE, PPPoA, and authentication, authorization, and accounting (AAA) call configurations will continue to work in this environment. You can, however, enable Subscriber Service Switch preauthorization and Subscriber Service Switch type authorization. You may also find it helpful to verify Subscriber Service Switch call operation.
This section contains the following procedures:
•
Enabling Domain Preauthorization on a NAS (required)
•
Creating a RADIUS User Profile for Domain Preauthorization (required)
•
Enabling a Subscriber Service Switch Preauthorization (required)
•
Troubleshooting the Subscriber Service Switch (optional)
Enabling Domain Preauthorization on a NAS
Perform the following task to enable the NAS to perform domain authorization before tunneling.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
vpdn authorize domain
4.
exit
5.
show running-config
6.
Create a RADIUS user profile for domain preauthorization.
DETAILED STEPS
What to Do Next
Create a RADIUS user profile for domain preauthorization. See "Creating a RADIUS User Profile for Domain Preauthorization" section for more information.
Creating a RADIUS User Profile for Domain Preauthorization
Table 2 contains the attributes needed to enable domain preauthorization in a RADIUS user file. Refer to the Cisco IOS Security Configuration Guide for information about creating a RADIUS user profile.
Table 2 Attributes for the RADIUS User Profile for Domain Preauthorization
Enabling a Subscriber Service Switch Preauthorization
When Subscriber Service Switch preauthorization is enabled on an LAC, local configurations for session limit per VC and per VLAN are overwritten by the per-NAS-port session limit downloaded from the server. Perform this task to enable preauthorization.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
subscriber access {pppoe | pppoa} pre-authorize nas-port-id [aaa-method-list]
4.
show sss session [all]
5.
exit
DETAILED STEPS
What to Do Next
Information about troubleshooting a network running the Subscriber Service Switch can be found in the "Troubleshooting the Subscriber Service Switch" section.
Troubleshooting the Subscriber Service Switch
Perform this task to troubleshoot the Subscriber Service Switch. Examples of normal and failure operations can be found in the "Troubleshooting the Subscriber Service Switch: Examples" section. Reports from debug commands should be sent to technical personnel at Cisco Systems for evaluation.
Perform the following task to troubleshoot a network running the Subscriber Service Switch.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
no logging console
4.
Use Telnet to access a router port and repeat Steps 2 and 3.
5.
terminal monitor
6.
exit
7.
debug sss command-option
8.
configure terminal
9.
no terminal monitor
10.
exit
DETAILED STEPS
Step 1
enable
Example:Router> enable
Enables privileged EXEC mode.
•
Enter your password if prompted.
Step 2
configure terminal
Example:Router# configure terminal
Enters global configuration mode.
Step 3
no logging console
Example:Router(config)# no logging console
Disables all logging to the console terminal. To reenable logging to the console, use the logging console command.
Step 4
Use Telnet to access a router port and repeat Steps 2 and 3.
Enters global configuration mode in a recursive Telnet session, which allows the output to be redirected away from the console port.
Step 5
terminal monitor
Example:Router(config)# terminal monitor
Enables logging output on the virtual terminal.
Step 6
exit
Example:Router(config)# exit
Exits to privileged EXEC mode.
Step 7
debug sss command-option
Example:Router# debug sss error
Enables the debug command. See the "Debug Commands Available for Subscriber Service Switch" section and the "Additional Debugging Commands for Troubleshooting the Subscriber Service Switch" section for commands that can be entered.
Note
You can enter more than one debug command.
Step 8
configure terminal
Example:Router# configure terminal
Enters global configuration mode.
Step 9
no terminal monitor
Example:Router(config)# no terminal monitor
Disables logging on the virtual terminal.
Step 10
exit
Example:Router(config)# exit
Exits to privileged EXEC mode.
Configuration Examples for Configuring a Subscriber Service Switch Policy
This section provides the following configuration examples:
•
LAC Domain Authorization: Example
•
Domain Preauthorization RADIUS User Profile: Example
•
Subscriber Service Switch Preauthorization: Example
•
Verify Subscriber Service Switch Call Operation: Example
LAC Domain Authorization: Example
The following example shows the configuration necessary for the LAC to participate in domain preauthorization:
!aaa new-modelaaa authorization network default local group radius!vpdn authorize domain!radius-server host 10.9.9.9 auth-port 1645 acct-port 1646radius-server attribute nas-port format dradius-server key MyKeyradius-server vsa send authentication!Domain Preauthorization RADIUS User Profile: Example
The following example shows a typical domain preauthorization RADIUS user profile:
user = nas-port:10.9.9.9:0/0/0/30.33profile_id = 826profile_cycle = 1radius=Cisco {check_items= {2=cisco}reply_attributes= {9,1="vpdn:vpn-domain-list=net1.com,net2.com"6=5}}}Subscriber Service Switch Preauthorization: Example
The following partial example signals the Subscriber Service Switch to preauthorize the NAS-Port-ID string before authorizing the domain name. This policy applies only to all sessions with a PPPoE access type.
vpdn-group 3accept dialinprotocol pppoevirtual-template 1!! Signals Subscriber Service Switch to preauthorize the NAS-Port-ID string before! authorizing the domain name.subscriber access pppoe pre-authorize nas-port-id mlist-llid!Verify Subscriber Service Switch Call Operation: Example
The following example command output from the show sss session all command provides an extensive report of Subscriber Service Switch session activity. Each section shows the unique identifier for each session, which can be used to correlate that particular session with the session information retrieved from other show commands or debug command traces. See the following show vpdn session command output for an example of this unique ID correlation.
Router# show sss session allCurrent SSS Information: Total sessions 9SSS session handle is 40000013, state is connected, service is VPDNUnique ID is 9SIP subscriber access type(s) are PPPoE/PPPIdentifier is nobody3@example.comLast Changed 00:02:49Root SIP Handle is DF000010, PID is 49AAA unique ID is 10Current SIP options are Req Fwding/Req FwdeSSS session handle is B0000017, state is connected, service is VPDNUnique ID is 10SIP subscriber access type(s) are PPPoE/PPPIdentifier is nobody3@example.comLast Changed 00:02:05Root SIP Handle is B9000015, PID is 49AAA unique ID is 11Current SIP options are Req Fwding/Req FwdedSSS session handle is D6000019, state is connected, service is VPDNUnique ID is 11SIP subscriber access type(s) are PPPoE/PPPIdentifier is nobody3@example.comLast Changed 00:02:13Root SIP Handle is D0000016, PID is 49AAA unique ID is 12Current SIP options are Req Fwding/Req FwdedSSS session handle is 8C000003, state is connected, service is VPDNUnique ID is 3SIP subscriber access type(s) are PPPoE/PPPIdentifier is user3@example.comLast Changed 2d21hRoot SIP Handle is D3000002, PID is 49AAA unique ID is 3Current SIP options are Req Fwding/Req FwdedSSS session handle is BE00000B, state is connected, service is Local TermUnique ID is 6SIP subscriber access type(s) are PPPoE/PPPIdentifier is user1Last Changed 00:03:56Root SIP Handle is A9000009, PID is 49AAA unique ID is 7Current SIP options are Req Fwding/Req FwdedSSS session handle is DC00000D, state is connected, service is Local TermUnique ID is 7SIP subscriber access type(s) are PPPoE/PPPIdentifier is user2Last Changed 00:03:57Root SIP Handle is 2C00000A, PID is 49AAA unique ID is 8Current SIP options are Req Fwding/Req FwdedSSS session handle is DB000011, state is connected, service is VPDNUnique ID is 8SIP subscriber access type(s) are PPPoE/PPPIdentifier is nobody3@example.comLast Changed 00:02:58Root SIP Handle is 1000000F, PID is 49AAA unique ID is 9Current SIP options are Req Fwding/Req FwdedSSS session handle is 3F000007, state is connected, service is Local TermUnique ID is 2SIP subscriber access type(s) are PPPIdentifier is user1Last Changed 00:05:30Root SIP Handle is 8A000009, PID is 92AAA unique ID is 1Current SIP options are Req Fwding/Req FwdedSSS session handle is 97000005, state is connected, service is VPDNUnique ID is 4SIP subscriber access type(s) are PPPIdentifier is nobody2@example.comLast Changed 00:07:16Root SIP Handle is 32000000, PID is 92AAA unique ID is 5Current SIP options are Req Fwding/Req FwdedCorrelating the Unique ID in show vpdn session Command Output
The following partial sample output from the show vpdn session command provides extensive reports on call activity for all L2TP, L2F, and PPPoE sessions, and identifies the unique ID for each session.
Router# show vpdn session allL2TP Session Information Total tunnels 1 sessions 4Session id 5 is up, tunnel id 13695Call serial number is 3355500002Remote tunnel name is User03Internet address is 10.0.0.63Session state is established, time since change 00:03:5352 Packets sent, 52 received2080 Bytes sent, 1316 receivedLast clearing of "show vpdn" counters neverSession MTU is 1464 bytesSession username is nobody3@example.comInterfaceRemote session id is 692, remote tunnel id 58582UDP checksums are disabledSSS switching enabledNo FS cached header information availableSequencing is offUnique ID is 8Session id 6 is up, tunnel id 13695Call serial number is 3355500003Remote tunnel name is User03Internet address is 10.0.0.63Session state is established, time since change 00:04:2252 Packets sent, 52 received2080 Bytes sent, 1316 receivedLast clearing of "show vpdn" counters neverSession MTU is 1464 bytesSession username is nobody3@example.comInterfaceRemote session id is 693, remote tunnel id 58582UDP checksums are disabledSSS switching enabledNo FS cached header information availableSequencing is offUnique ID is 9Troubleshooting the Subscriber Service Switch: Examples
This section provides the following debugging session examples for a network running the Subscriber Service Switch:
•
Troubleshooting the Subscriber Service Switch Operation: Example
•
Troubleshooting the Subscriber Service Switch on the LAC—Normal Operation: Example
•
Troubleshooting the Subscriber Service Switch on the LAC—Authorization Failure: Example
•
Troubleshooting the Subscriber Service Switch on the LAC—Authentication Failure: Example
•
Troubleshooting the Subscriber Service Switch on the LNS—Normal Operation: Example
•
Troubleshooting the Subscriber Service Switch on the LNS—Tunnel Failure: Example
Reports from debug commands should be sent to technical personnel at Cisco Systems for evaluation.
Troubleshooting the Subscriber Service Switch Operation: Example
The following example shows the debug commands used and sample output for debugging Subscriber Service Switch operation:
Router# debug sss eventRouter# debug sss errorRouter# debug sss stateRouter# debug sss aaa authorization eventRouter# debug sss aaa authorization fsmSSS:SSS events debugging is onSSS error debugging is onSSS fsm debugging is onSSS AAA authorization event debugging is onSSS AAA authorization FSM debugging is on*Mar 4 21:33:18.248: SSS INFO: Element type is Access-Type, long value is 3*Mar 4 21:33:18.248: SSS INFO: Element type is Switch-Id, long value is -1509949436*Mar 4 21:33:18.248: SSS INFO: Element type is Nasport, ptr value is 6396882C*Mar 4 21:33:18.248: SSS INFO: Element type is AAA-Id, long value is 7*Mar 4 21:33:18.248: SSS INFO: Element type is AAA-ACCT_ENBL, long value is 1*Mar 4 21:33:18.248: SSS INFO: Element type is AccIe-Hdl, ptr value is 78000006*Mar 4 21:33:18.248: SSS MGR [uid:7]: Event service-request, state changed fromwait-for-req to wait-for-auth*Mar 4 21:33:18.248: SSS MGR [uid:7]: Handling Policy Authorize (1 pending sessions)*Mar 4 21:33:18.248: SSS PM [uid:7]: Need the following key: Unauth-User*Mar 4 21:33:18.248: SSS PM [uid:7]: Received Service Request*Mar 4 21:33:18.248: SSS PM [uid:7]: Event <need keys>, State: initial-req toneed-init-keys*Mar 4 21:33:18.248: SSS PM [uid:7]: Policy reply - Need more keys*Mar 4 21:33:18.248: SSS MGR [uid:7]: Got reply Need-More-Keys from PM*Mar 4 21:33:18.248: SSS MGR [uid:7]: Event policy-or-mgr-more-keys, state changed fromwait-for-auth to wait-for-req*Mar 4 21:33:18.248: SSS MGR [uid:7]: Handling More-Keys event*Mar 4 21:33:20.256: SSS INFO: Element type is Unauth-User, string value isnobody@example.com*Mar 4 21:33:20.256: SSS INFO: Element type is AccIe-Hdl, ptr value is 78000006*Mar 4 21:33:20.256: SSS INFO: Element type is AAA-Id, long value is 7*Mar 4 21:33:20.256: SSS INFO: Element type is Access-Type, long value is 0*Mar 4 21:33:20.256: SSS MGR [uid:7]: Event service-request, state changed fromwait-for-req to wait-for-auth*Mar 4 21:33:20.256: SSS MGR [uid:7]: Handling Policy Authorize (1 pending sessions)*Mar 4 21:33:20.256: SSS PM [uid:7]: Received More Initial Keys*Mar 4 21:33:20.256: SSS PM [uid:7]: Event <rcvd keys>, State: need-init-keys tocheck-auth-needed*Mar 4 21:33:20.256: SSS PM [uid:7]: Handling Authorization Check*Mar 4 21:33:20.256: SSS PM [uid:7]: Event <send auth>, State: check-auth-needed toauthorizing*Mar 4 21:33:20.256: SSS PM [uid:7]: Handling AAA service Authorization*Mar 4 21:33:20.256: SSS PM [uid:7]: Sending authorization request for 'example.com'*Mar 4 21:33:20.256: SSS AAA AUTHOR [uid:7]:Event <make request>, state changed from idleto authorizing*Mar 4 21:33:20.256: SSS AAA AUTHOR [uid:7]:Authorizing key example.com*Mar 4 21:33:20.260: SSS AAA AUTHOR [uid:7]:AAA request sent for key example.com*Mar 4 21:33:20.260: SSS AAA AUTHOR [uid:7]:Received an AAA pass*Mar 4 21:33:20.260: SSS AAA AUTHOR [uid:7]:Event <found service>, state changed fromauthorizing to complete*Mar 4 21:33:20.260: SSS AAA AUTHOR [uid:7]:Found service info for key example.com*Mar 4 21:33:20.260: SSS AAA AUTHOR [uid:7]:Event <free request>, state changed fromcomplete to terminal*Mar 4 21:33:20.260: SSS AAA AUTHOR [uid:7]:Free request*Mar 4 21:33:20.264: SSS PM [uid:7]: Event <found>, State: authorizing to end*Mar 4 21:33:20.264: SSS PM [uid:7]: Handling Service Direction*Mar 4 21:33:20.264: SSS PM [uid:7]: Policy reply - Forwarding*Mar 4 21:33:20.264: SSS MGR [uid:7]: Got reply Forwarding from PM*Mar 4 21:33:20.264: SSS MGR [uid:7]: Event policy-start-service-fsp, state changed fromwait-for-auth to wait-for-service*Mar 4 21:33:20.264: SSS MGR [uid:7]: Handling Connect-Forwarding-Service event*Mar 4 21:33:20.272: SSS MGR [uid:7]: Event service-fsp-connected, state changed fromwait-for-service to connected*Mar 4 21:33:20.272: SSS MGR [uid:7]: Handling Forwarding-Service-Connected eventTroubleshooting the Subscriber Service Switch on the LAC—Normal Operation: Example
The following example shows the debug commands used and sample output indicating normal operation of the Subscriber Service Switch on the LAC:
Router# debug sss eventRouter# debug sss errorRouter# debug sss aaa authorization eventRouter# debug sss aaa authorization fsmRouter# debug pppoe eventsRouter# debug pppoe errorsRouter# debug ppp negotiationRouter# debug vpdn l2x-eventsRouter# debug vpdn l2x-errorsRouter# debug vpdn sss eventsRouter# debug vpdn sss errorsRouter# debug vpdn call eventsRouter# debug vpdn call fsmRouter# debug vpdn eventsRouter# debug vpdn errorsSSS:SSS events debugging is onSSS error debugging is onSSS AAA authorization event debugging is onSSS AAA authorization FSM debugging is onPPPoE:PPPoE protocol events debugging is onPPPoE protocol errors debugging is onPPP:PPP protocol negotiation debugging is onVPN:L2X protocol events debugging is onL2X protocol errors debugging is onVPDN SSS events debugging is onVPDN SSS errors debugging is onVPDN call event debugging is onVPDN call FSM debugging is onVPDN events debugging is onVPDN errors debugging is on*Nov 15 12:23:52.523: PPPoE 0: I PADI R:0000.0c14.71d0 L:ffff.ffff.ffff 1/32ATM4/0.132*Nov 15 12:23:52.523: PPPoE 0: O PADO R:0000.0c14.71d0 L:00b0.c2e9.c870 1/32ATM4/0.132*Nov 15 12:23:52.527: PPPoE 0: I PADR R:0000.0c14.71d0 L:00b0.c2e9.c870 1/32ATM4/0.132*Nov 15 12:23:52.527: PPPoE : encap string prepared*Nov 15 12:23:52.527: [13]PPPoE 10: Access IE handle allocated*Nov 15 12:23:52.527: [13]PPPoE 10: pppoe SSS switch updated*Nov 15 12:23:52.527: [13]PPPoE 10: Service request sent to SSS*Nov 15 12:23:52.527: [13]PPPoE 10: Created R:00b0.c2e9.c870 L:0000.0c14.71d0 1/32ATM4/0.132*Nov 15 12:23:52.547: SSS INFO: Element type is Access-Type, long value is 3*Nov 15 12:23:52.547: SSS INFO: Element type is Switch-Id, long value is 2130706444*Nov 15 12:23:52.547: SSS INFO: Element type is Nasport, ptr value is 63C07288*Nov 15 12:23:52.547: SSS INFO: Element type is AAA-Id, long value is 14*Nov 15 12:23:52.547: SSS INFO: Element type is AccIe-Hdl, ptr value is B200000C*Nov 15 12:23:52.547: SSS MGR [uid:13]: Handling Policy Authorize (1 pendingsessions)*Nov 15 12:23:52.547: SSS PM [uid:13]: RM/VPDN disabled: RM/VPDN author not needed*Nov 15 12:23:52.547: SSS PM [uid:13]: Received Service Request*Nov 15 12:23:52.547: SSS PM [uid:13]: Handling Authorization Check*Nov 15 12:23:52.547: SSS PM [uid:13]: Policy requires 'Unauth-User' key*Nov 15 12:23:52.547: SSS PM [uid:13]: Policy reply - Need more keys*Nov 15 12:23:52.547: SSS MGR [uid:13]: Got reply Need-More-Keys from PM*Nov 15 12:23:52.547: SSS MGR [uid:13]: Handling More-Keys event*Nov 15 12:23:52.547: [13]PPPoE 10: State REQ_NASPORT Event MORE_KEYS*Nov 15 12:23:52.547: [13]PPPoE 10: O PADS R:0000.0c14.71d0 L:00b0.c2e9.c870 1/32ATM4/0.132*Nov 15 12:23:52.547: ppp13 PPP: Using default call direction*Nov 15 12:23:52.547: ppp13 PPP: Treating connection as a dedicated line*Nov 15 12:23:52.547: ppp13 PPP: Phase is ESTABLISHING, Active Open*Nov 15 12:23:52.547: ppp13 LCP: O CONFREQ [Closed] id 1 len 19*Nov 15 12:23:52.547: ppp13 LCP: MRU 1492 (0x010405D4)*Nov 15 12:23:52.547: ppp13 LCP: AuthProto CHAP (0x0305C22305)*Nov 15 12:23:52.547: ppp13 LCP: MagicNumber 0xB0EC4557 (0x0506B0EC4557)*Nov 15 12:23:52.547: [13]PPPoE 10: State START_PPP Event DYN_BIND*Nov 15 12:23:52.547: [13]PPPoE 10: data path set to PPP*Nov 15 12:23:52.571: ppp13 LCP: I CONFREQ [REQsent] id 1 len 14*Nov 15 12:23:52.571: ppp13 LCP: MRU 1492 (0x010405D4)*Nov 15 12:23:52.571: ppp13 LCP: MagicNumber 0x0017455D (0x05060017455D)*Nov 15 12:23:52.571: ppp13 LCP: O CONFACK [REQsent] id 1 len 14*Nov 15 12:23:52.571: ppp13 LCP: MRU 1492 (0x010405D4)*Nov 15 12:23:52.571: ppp13 LCP: MagicNumber 0x0017455D (0x05060017455D)*Nov 15 12:23:54.543: ppp13 LCP: TIMEout: State ACKsent*Nov 15 12:23:54.543: ppp13 LCP: O CONFREQ [ACKsent] id 2 len 19*Nov 15 12:23:54.543: ppp13 LCP: MRU 1492 (0x010405D4)*Nov 15 12:23:54.543: ppp13 LCP: AuthProto CHAP (0x0305C22305)*Nov 15 12:23:54.543: ppp13 LCP: MagicNumber 0xB0EC4557 (0x0506B0EC4557)*Nov 15 12:23:54.543: ppp13 LCP: I CONFACK [ACKsent] id 2 len 19*Nov 15 12:23:54.543: ppp13 LCP: MRU 1492 (0x010405D4)*Nov 15 12:23:54.543: ppp13 LCP: AuthProto CHAP (0x0305C22305)*Nov 15 12:23:54.543: ppp13 LCP: MagicNumber 0xB0EC4557 (0x0506B0EC4557)*Nov 15 12:23:54.543: ppp13 LCP: State is Open*Nov 15 12:23:54.543: ppp13 PPP: Phase is AUTHENTICATING, by this end*Nov 15 12:23:54.543: ppp13 CHAP: O CHALLENGE id 1 len 25 from "7200"*Nov 15 12:23:54.547: ppp13 CHAP: I RESPONSE id 1 len 38 from "nobody@example.com"*Nov 15 12:23:54.547: ppp13 PPP: Phase is FORWARDING, Attempting Forward*Nov 15 12:23:54.547: SSS INFO: Element type is Unauth-User, string value isnobody@example.com*Nov 15 12:23:54.547: SSS INFO: Element type is AccIe-Hdl, ptr value is B200000C*Nov 15 12:23:54.547: SSS INFO: Element type is AAA-Id, long value is 14*Nov 15 12:23:54.547: SSS INFO: Element type is Access-Type, long value is 0*Nov 15 12:23:54.547: SSS MGR [uid:13]: Handling Policy Authorize (1 pendingsessions)*Nov 15 12:23:54.547: SSS PM [uid:13]: Received More Keys*Nov 15 12:23:54.547: SSS PM [uid:13]: Handling Authorization Check*Nov 15 12:23:54.547: SSS PM [uid:13]: Handling AAA service Authorization*Nov 15 12:23:54.547: SSS PM [uid:13]: Sending authorization request for 'example.com'*Nov 15 12:23:54.547: SSS AAA AUTHOR [uid:13]:Event <make request>, state changedfrom idle to authorizing*Nov 15 12:23:54.547: SSS AAA AUTHOR [uid:13]:Authorizing key example.com*Nov 15 12:23:54.547: SSS AAA AUTHOR [uid:13]:AAA request sent for key example.com*Nov 15 12:23:54.551: SSS AAA AUTHOR [uid:13]:Received an AAA pass*Nov 15 12:23:54.551: SSS AAA AUTHOR [uid:13]:Event <found service>, state changedfrom authorizing to complete*Nov 15 12:23:54.551: SSS AAA AUTHOR [uid:13]:Found service info for key example.com*Nov 15 12:23:54.551: SSS AAA AUTHOR [uid:13]:Event <free request>, state changedfrom complete to terminal*Nov 15 12:23:54.551: SSS AAA AUTHOR [uid:13]:Free request*Nov 15 12:23:54.551: SSS PM [uid:13]: Handling Service Direction*Nov 15 12:23:54.551: SSS PM [uid:13]: Policy reply - Forwarding*Nov 15 12:23:54.551: SSS MGR [uid:13]: Got reply Forwarding from PM*Nov 15 12:23:54.551: SSS MGR [uid:13]: Handling Connect-Service event*Nov 15 12:23:54.551: VPDN CALL [uid:13]: Event connect req, state changed from idleto connecting*Nov 15 12:23:54.551: VPDN CALL [uid:13]: Requesting connection*Nov 15 12:23:54.551: VPDN CALL [uid:13]: Call request sent*Nov 15 12:23:54.551: VPDN MGR [uid:13]: Event client connect, state changed fromidle to connecting*Nov 15 12:23:54.551: VPDN MGR [uid:13]: Initiating compulsory connection to192.168.8.2*Nov 15 12:23:54.551: Tnl/Sn61510/7 L2TP: Session FS enabled*Nov 15 12:23:54.551: Tnl/Sn61510/7 L2TP: Session state change from idle towait-for-tunnel*Nov 15 12:23:54.551: uid:13 Tnl/Sn61510/7 L2TP: Create session*Nov 15 12:23:54.551: uid:13 Tnl/Sn61510/7 L2TP: O ICRQ to rp1 9264/0*Nov 15 12:23:54.551: [13]PPPoE 10: Access IE nas port called*Nov 15 12:23:54.555: Tnl61510 L2TP: Control channel retransmit delay set to 1seconds*Nov 15 12:23:54.555: uid:13 Tnl/Sn61510/7 L2TP: Session state change fromwait-for-tunnel to wait-reply*Nov 15 12:23:54.555: [13]PPPoE 10: State LCP_NEGO Event PPP_FWDING*Nov 15 12:23:54.559: uid:13 Tnl/Sn61510/7 L2TP: O ICCN to rp1 9264/13586*Nov 15 12:23:54.559: Tnl61510 L2TP: Control channel retransmit delay set to 1seconds*Nov 15 12:23:54.559: uid:13 Tnl/Sn61510/7 L2TP: Session state change fromwait-reply to established*Nov 15 12:23:54.559: uid:13 Tnl/Sn61510/7 L2TP: VPDN session up*Nov 15 12:23:54.559: VPDN MGR [uid:13]: Event peer connected, state changed fromconnecting to connected*Nov 15 12:23:54.559: VPDN MGR [uid:13]: Succeed to forward nobody@example.com*Nov 15 12:23:54.559: VPDN MGR [uid:13]: accounting start sent*Nov 15 12:23:54.559: VPDN CALL [uid:13]: Event connect ok, state changed fromconnecting to connected*Nov 15 12:23:54.559: VPDN CALL [uid:13]: Connection succeeded*Nov 15 12:23:54.559: SSS MGR [uid:13]: Handling Service-Connected event*Nov 15 12:23:54.559: ppp13 PPP: Phase is FORWARDED, Session Forwarded*Nov 15 12:23:54.559: [13]PPPoE 10: State LCP_NEGO Event PPP_FWDED*Nov 15 12:23:54.563: [13]PPPoE 10: data path set to SSS Switch*Nov 15 12:23:54.563: [13]PPPoE 10: Connected ForwardedTroubleshooting the Subscriber Service Switch on the LAC—Authorization Failure: Example
The following is sample output indicating call failure due to authorization failure:
*Nov 15 12:37:24.535: PPPoE 0: I PADI R:0000.0c14.71d0 L:ffff.ffff.ffff 1/32ATM4/0.132*Nov 15 12:37:24.535: PPPoE 0: O PADO R:0000.0c14.71d0 L:00b0.c2e9.c870 1/32ATM4/0.132*Nov 15 12:37:24.539: PPPoE 0: I PADR R:0000.0c14.71d0 L:00b0.c2e9.c870 1/32ATM4/0.132*Nov 15 12:37:24.539: PPPoE : encap string prepared*Nov 15 12:37:24.539: [18]PPPoE 15: Access IE handle allocated*Nov 15 12:37:24.539: [18]PPPoE 15: pppoe SSS switch updated*Nov 15 12:37:24.539: PPPoE 15: AAA pppoe_aaa_acct_get_retrieved_attrs*Nov 15 12:37:24.539: [18]PPPoE 15: AAA pppoe_aaa_acct_get_nas_port_details*Nov 15 12:37:24.539: [18]PPPoE 15: AAA pppoe_aaa_acct_get_dynamic_attrs*Nov 15 12:37:24.539: [18]PPPoE 15: AAA pppoe_aaa_acct_get_dynamic_attrs*Nov 15 12:37:24.539: [18]PPPoE 15: AAA unique ID allocated*Nov 15 12:37:24.539: [18]PPPoE 15: No AAA accounting method list*Nov 15 12:37:24.539: [18]PPPoE 15: Service request sent to SSS*Nov 15 12:37:24.539: [18]PPPoE 15: Created R:00b0.c2e9.c870 L:0000.0c14.71d0 1/32ATM4/0.132*Nov 15 12:37:24.559: SSS INFO: Element type is Access-Type, long value is 3*Nov 15 12:37:24.559: SSS INFO: Element type is Switch-Id, long value is -738197487*Nov 15 12:37:24.559: SSS INFO: Element type is Nasport, ptr value is 63C0E590*Nov 15 12:37:24.559: SSS INFO: Element type is AAA-Id, long value is 19*Nov 15 12:37:24.559: SSS INFO: Element type is AccIe-Hdl, ptr value is 5B000011*Nov 15 12:37:24.559: SSS MGR [uid:18]: Handling Policy Authorize (1 pendingsessions)*Nov 15 12:37:24.559: SSS PM [uid:18]: RM/VPDN disabled: RM/VPDN author not needed*Nov 15 12:37:24.559: SSS PM [uid:18]: Received Service Request*Nov 15 12:37:24.559: SSS PM [uid:18]: Handling Authorization Check*Nov 15 12:37:24.559: SSS PM [uid:18]: Policy requires 'Unauth-User' key*Nov 15 12:37:24.559: SSS PM [uid:18]: Policy reply - Need more keys*Nov 15 12:37:24.559: SSS MGR [uid:18]: Got reply Need-More-Keys from PM*Nov 15 12:37:24.559: SSS MGR [uid:18]: Handling More-Keys event*Nov 15 12:37:24.559: [18]PPPoE 15: State REQ_NASPORT Event MORE_KEYS*Nov 15 12:37:24.559: [18]PPPoE 15: O PADS R:0000.0c14.71d0 L:00b0.c2e9.c870 1/32ATM4/0.132*Nov 15 12:37:24.559: ppp18 PPP: Using default call direction*Nov 15 12:37:24.559: ppp18 PPP: Treating connection as a dedicated line*Nov 15 12:37:24.559: ppp18 PPP: Phase is ESTABLISHING, Active Open*Nov 15 12:37:24.559: ppp18 LCP: O CONFREQ [Closed] id 1 len 19*Nov 15 12:37:24.559: ppp18 LCP: MRU 1492 (0x010405D4)*Nov 15 12:37:24.559: ppp18 LCP: AuthProto CHAP (0x0305C22305)*Nov 15 12:37:24.559: ppp18 LCP: MagicNumber 0xB0F8A971 (0x0506B0F8A971)*Nov 15 12:37:24.559: [18]PPPoE 15: State START_PPP Event DYN_BIND*Nov 15 12:37:24.559: [18]PPPoE 15: data path set to PPP*Nov 15 12:37:24.563: ppp18 LCP: I CONFREQ [REQsent] id 1 len 14*Nov 15 12:37:24.563: ppp18 LCP: MRU 1492 (0x010405D4)*Nov 15 12:37:24.563: ppp18 LCP: MagicNumber 0x0023A93E (0x05060023A93E)*Nov 15 12:37:24.563: ppp18 LCP: O CONFACK [REQsent] id 1 len 14*Nov 15 12:37:24.563: ppp18 LCP: MRU 1492 (0x010405D4)*Nov 15 12:37:24.563: ppp18 LCP: MagicNumber 0x0023A93E (0x05060023A93E)*Nov 15 12:37:26.523: ppp18 LCP: I CONFREQ [ACKsent] id 2 len 14*Nov 15 12:37:26.523: ppp18 LCP: MRU 1492 (0x010405D4)*Nov 15 12:37:26.523: ppp18 LCP: MagicNumber 0x0023A93E (0x05060023A93E)*Nov 15 12:37:26.523: ppp18 LCP: O CONFACK [ACKsent] id 2 len 14*Nov 15 12:37:26.527: ppp18 LCP: MRU 1492 (0x010405D4)*Nov 15 12:37:26.527: ppp18 LCP: MagicNumber 0x0023A93E (0x05060023A93E)*Nov 15 12:37:26.575: ppp18 LCP: TIMEout: State ACKsent*Nov 15 12:37:26.575: ppp18 LCP: O CONFREQ [ACKsent] id 2 len 19*Nov 15 12:37:26.575: ppp18 LCP: MRU 1492 (0x010405D4)*Nov 15 12:37:26.575: ppp18 LCP: AuthProto CHAP (0x0305C22305)*Nov 15 12:37:26.575: ppp18 LCP: MagicNumber 0xB0F8A971 (0x0506B0F8A971)*Nov 15 12:37:26.575: ppp18 LCP: I CONFACK [ACKsent] id 2 len 19*Nov 15 12:37:26.575: ppp18 LCP: MRU 1492 (0x010405D4)*Nov 15 12:37:26.575: ppp18 LCP: AuthProto CHAP (0x0305C22305)*Nov 15 12:37:26.575: ppp18 LCP: MagicNumber 0xB0F8A971 (0x0506B0F8A971)*Nov 15 12:37:26.575: ppp18 LCP: State is Open*Nov 15 12:37:26.575: ppp18 PPP: Phase is AUTHENTICATING, by this end*Nov 15 12:37:26.575: ppp18 CHAP: O CHALLENGE id 1 len 25 from "7200"*Nov 15 12:37:26.579: ppp18 CHAP: I RESPONSE id 1 len 38 from "nobody@example.com"Nov 15 12:37:26.579: ppp18 PPP: Phase is FORWARDING, Attempting Forward*Nov 15 12:37:26.579: SSS INFO: Element type is Unauth-User, string value isnobody@example.com*Nov 15 12:37:26.579: SSS INFO: Element type is AccIe-Hdl, ptr value is 5B000011*Nov 15 12:37:26.579: SSS INFO: Element type is AAA-Id, long value is 19Nov 15 12:37:26.579: SSS INFO: Element type is Access-Type, long value is 0*Nov 15 12:37:26.579: SSS MGR [uid:18]: Handling Policy Authorize (1 pendingsessions)*Nov 15 12:37:26.579: SSS PM [uid:18]: Received More Keys*Nov 15 12:37:26.579: SSS PM [uid:18]: Handling Authorization Check*Nov 15 12:37:26.579: SSS PM [uid:18]: Handling AAA service Authorization*Nov 15 12:37:26.579: SSS PM [uid:18]: Sending authorization request for 'example.com'*Nov 15 12:37:26.579: SSS AAA AUTHOR [uid:18]:Event <make request>, state changedfrom idle to authorizing*Nov 15 12:37:26.579: SSS AAA AUTHOR [uid:18]:Authorizing key example.com*Nov 15 12:37:26.579: SSS AAA AUTHOR [uid:18]:AAA request sent for key example.com*Nov 15 12:37:26.587: SSS AAA AUTHOR [uid:18]:Received an AAA failure*Nov 15 12:37:26.587: SSS AAA AUTHOR [uid:18]:Event <service not found>, statechanged from authorizing to complete*Nov 15 12:37:26.587: SSS AAA AUTHOR [uid:18]:No service authorization info found*Nov 15 12:37:26.587: SSS AAA AUTHOR [uid:18]:Event <free request>, state changedfrom complete to terminal*Nov 15 12:37:26.587: SSS AAA AUTHOR [uid:18]:Free request*Nov 15 12:37:26.587: SSS PM [uid:18]: Handling Next Authorization Check*Nov 15 12:37:26.587: SSS PM [uid:18]: Default policy: SGF author not needed*Nov 15 12:37:26.587: SSS PM [uid:18]: Handling Default Service*Nov 15 12:37:26.587: SSS PM [uid:18]: Policy reply - Local terminate*Nov 15 12:37:26.591: SSS MGR [uid:18]: Got reply Local-Term from PM*Nov 15 12:37:26.591: SSS MGR [uid:18]: Handling Send-Client-Local-Term event*Nov 15 12:37:26.591: ppp18 PPP: Phase is AUTHENTICATING, Unauthenticated UserNov 15 12:37:26.595: ppp18 CHAP: O FAILURE id 1 len 25 msg is "Authenticationfailed"*Nov 15 12:37:26.599: ppp18 PPP: Sending Acct Event[Down] id[13]*Nov 15 12:37:26.599: ppp18 PPP: Phase is TERMINATING*Nov 15 12:37:26.599: ppp18 LCP: O TERMREQ [Open] id 3 len 4*Nov 15 12:37:26.599: ppp18 LCP: State is Closed*Nov 15 12:37:26.599: ppp18 PPP: Phase is DOWN*Nov 15 12:37:26.599: ppp18 PPP: Phase is TERMINATING*Nov 15 12:37:26.599: [18]PPPoE 15: State LCP_NEGO Event PPP_DISCNCT*Nov 15 12:37:26.599: [18]PPPoE 15: O PADT R:0000.0c14.71d0 L:00b0.c2e9.c870 1/32ATM4/0.132*Nov 15 12:37:26.599: [18]PPPoE 15: Destroying R:0000.0c14.71d0 L:00b0.c2e9.c8701/32 ATM4/0.132*Nov 15 12:37:26.599: [18]PPPoE 15: AAA account stopped*Nov 15 12:37:26.599: SSS MGR [uid:18]: Processing a client disconnect*Nov 15 12:37:26.599: SSS MGR [uid:18]: Handling Send-Service-Disconnect eventTroubleshooting the Subscriber Service Switch on the LAC—Authentication Failure: Example
The following is sample output indicating call failure due to authentication failure at the LNS:
*Nov 15 12:45:02.067: PPPoE 0: I PADI R:0000.0c14.71d0 L:ffff.ffff.ffff 1/32ATM4/0.132*Nov 15 12:45:02.071: PPPoE 0: O PADO R:0000.0c14.71d0 L:00b0.c2e9.c870 1/32ATM4/0.132*Nov 15 12:45:02.071: PPPoE 0: I PADR R:0000.0c14.71d0 L:00b0.c2e9.c870 1/32ATM4/0.132*Nov 15 12:45:02.071: PPPoE : encap string prepared*Nov 15 12:45:02.071: [21]PPPoE 18: Access IE handle allocated*Nov 15 12:45:02.071: [21]PPPoE 18: pppoe SSS switch updated*Nov 15 12:45:02.071: PPPoE 18: AAA pppoe_aaa_acct_get_retrieved_attrs*Nov 15 12:45:02.071: [21]PPPoE 18: AAA pppoe_aaa_acct_get_nas_port_details*Nov 15 12:45:02.071: [21]PPPoE 18: AAA pppoe_aaa_acct_get_dynamic_attrs*Nov 15 12:45:02.071: [21]PPPoE 18: AAA pppoe_aaa_acct_get_dynamic_attrs*Nov 15 12:45:02.071: [21]PPPoE 18: AAA unique ID allocated*Nov 15 12:45:02.071: [21]PPPoE 18: No AAA accounting method list*Nov 15 12:45:02.071: [21]PPPoE 18: Service request sent to SSS*Nov 15 12:45:02.071: [21]PPPoE 18: Created R:00b0.c2e9.c870 L:0000.0c14.71d0 1/32ATM4/0.132*Nov 15 12:45:02.091: SSS INFO: Element type is Access-Type, long value is 3*Nov 15 12:45:02.091: SSS INFO: Element type is Switch-Id, long value is 1946157076*Nov 15 12:45:02.091: SSS INFO: Element type is Nasport, ptr value is 63B34170*Nov 15 12:45:02.091: SSS INFO: Element type is AAA-Id, long value is 22*Nov 15 12:45:02.091: SSS INFO: Element type is AccIe-Hdl, ptr value is 71000014*Nov 15 12:45:02.091: SSS MGR [uid:21]: Handling Policy Authorize (1 pendingsessions)*Nov 15 12:45:02.091: SSS PM [uid:21]: RM/VPDN disabled: RM/VPDN author not needed*Nov 15 12:45:02.091: SSS PM [uid:21]: Received Service Request*Nov 15 12:45:02.091: SSS PM [uid:21]: Handling Authorization Check*Nov 15 12:45:02.091: SSS PM [uid:21]: Policy requires 'Unauth-User' key*Nov 15 12:45:02.091: SSS PM [uid:21]: Policy reply - Need more keys*Nov 15 12:45:02.091: SSS MGR [uid:21]: Got reply Need-More-Keys from PM*Nov 15 12:45:02.091: SSS MGR [uid:21]: Handling More-Keys event*Nov 15 12:45:02.091: [21]PPPoE 18: State REQ_NASPORT Event MORE_KEYS*Nov 15 12:45:02.091: [21]PPPoE 18: O PADS R:0000.0c14.71d0 L:00b0.c2e9.c870 1/32ATM4/0.132*Nov 15 12:45:02.091: ppp21 PPP: Using default call direction*Nov 15 12:45:02.091: ppp21 PPP: Treating connection as a dedicated line*Nov 15 12:45:02.091: ppp21 PPP: Phase is ESTABLISHING, Active Open*Nov 15 12:45:02.091: ppp21 LCP: O CONFREQ [Closed] id 1 len 19*Nov 15 12:45:02.091: ppp21 LCP: MRU 1492 (0x010405D4)*Nov 15 12:45:02.091: ppp21 LCP: AuthProto CHAP (0x0305C22305)*Nov 15 12:45:02.091: ppp21 LCP: MagicNumber 0xB0FFA4D8 (0x0506B0FFA4D8)*Nov 15 12:45:02.091: [21]PPPoE 18: State START_PPP Event DYN_BIND*Nov 15 12:45:02.091: [21]PPPoE 18: data path set to PPP*Nov 15 12:45:02.095: ppp21 LCP: I CONFREQ [REQsent] id 1 len 14*Nov 15 12:45:02.095: ppp21 LCP: MRU 1492 (0x010405D4*Nov 15 12:45:02.095: ppp21 LCP: MagicNumber 0x002AA481 (0x0506002AA481)*Nov 15 12:45:02.095: ppp21 LCP: O CONFACK [REQsent] id 1 len 14*Nov 15 12:45:02.095: ppp21 LCP: MRU 1492 (0x010405D4)*Nov 15 12:45:02.095: ppp21 LCP: MagicNumber 0x002AA481 (0x0506002AA481)*Nov 15 12:45:02.315: Tnl41436 L2TP: I StopCCN from rp1 tnl 31166*Nov 15 12:45:02.315: Tnl41436 L2TP: Shutdown tunnel*Nov 15 12:45:02.315: Tnl41436 L2TP: Tunnel state change from no-sessions-left toidle*Nov 15 12:45:04.055: ppp21 LCP: I CONFREQ [ACKsent] id 2 len 14*Nov 15 12:45:04.055: ppp21 LCP: MRU 1492 (0x010405D4)*Nov 15 12:45:04.059: ppp21 LCP: MagicNumber 0x002AA481 (0x0506002AA481)*Nov 15 12:45:04.059: ppp21 LCP: O CONFACK [ACKsent] id 2 len 14*Nov 15 12:45:04.059: ppp21 LCP: MRU 1492 (0x010405D4)*Nov 15 12:45:04.059: ppp21 LCP: MagicNumber 0x002AA481 (0x0506002AA481)*Nov 15 12:45:04.079: ppp21 LCP: TIMEout: State ACKsent*Nov 15 12:45:04.079: ppp21 LCP: O CONFREQ [ACKsent] id 2 len 19*Nov 15 12:45:04.079: ppp21 LCP: MRU 1492 (0x010405D4)*Nov 15 12:45:04.079: ppp21 LCP: AuthProto CHAP (0x0305C22305)*Nov 15 12:45:04.079: ppp21 LCP: MagicNumber 0xB0FFA4D8 (0x0506B0FFA4D8)*Nov 15 12:45:04.079: ppp21 LCP: I CONFACK [ACKsent] id 2 len 19*Nov 15 12:45:04.079: ppp21 LCP: MRU 1492 (0x010405D4)*Nov 15 12:45:04.079: ppp21 LCP: AuthProto CHAP (0x0305C22305)*Nov 15 12:45:04.079: ppp21 LCP: MagicNumber 0xB0FFA4D8 (0x0506B0FFA4D8)*Nov 15 12:45:04.079: ppp21 LCP: State is Open*Nov 15 12:45:04.079: ppp21 PPP: Phase is AUTHENTICATING, by this end*Nov 15 12:45:04.079: ppp21 CHAP: O CHALLENGE id 1 len 25 from "7200"*Nov 15 12:45:04.083: ppp21 CHAP: I RESPONSE id 1 len 38 from "nobody@example.com"*Nov 15 12:45:04.083: ppp21 PPP: Phase is FORWARDING, Attempting Forward*Nov 15 12:45:04.083: SSS INFO: Element type is Unauth-User, string value isnobody@example.com*Nov 15 12:45:04.083: SSS INFO: Element type is AccIe-Hdl, ptr value is 71000014*Nov 15 12:45:04.083: SSS INFO: Element type is AAA-Id, long value is 22*Nov 15 12:45:04.083: SSS INFO: Element type is Access-Type, long value is 0*Nov 15 12:45:04.083: SSS MGR [uid:21]: Handling Policy Authorize (1 pendingsessions)*Nov 15 12:45:04.083: SSS PM [uid:21]: Received More Keys*Nov 15 12:45:04.083: SSS PM [uid:21]: Handling Authorization Check*Nov 15 12:45:04.083: SSS PM [uid:21]: Handling AAA service Authorization*Nov 15 12:45:04.083: SSS PM [uid:21]: Sending authorization request for 'example.com'*Nov 15 12:45:04.083: SSS AAA AUTHOR [uid:21]:Event <make request>, state changedfrom idle to authorizing*Nov 15 12:45:04.083: SSS AAA AUTHOR [uid:21]:Authorizing key example.com*Nov 15 12:45:04.083: SSS AAA AUTHOR [uid:21]:AAA request sent for key example.com*Nov 15 12:45:04.095: SSS AAA AUTHOR [uid:21]:Received an AAA pass*Nov 15 12:45:04.095: SSS AAA AUTHOR [uid:21]:Event <found service>, state changedfrom authorizing to complete*Nov 15 12:45:04.095: SSS AAA AUTHOR [uid:21]:Found service info for key example.com*Nov 15 12:45:04.095: SSS AAA AUTHOR [uid:21]:Event <free request>, state changedfrom complete to terminal*Nov 15 12:45:04.095: SSS AAA AUTHOR [uid:21]:Free request*Nov 15 12:45:04.095: SSS PM [uid:21]: Handling Service Direction*Nov 15 12:45:04.095: SSS PM [uid:21]: Policy reply - Forwarding*Nov 15 12:45:04.095: SSS MGR [uid:21]: Got reply Forwarding from PM*Nov 15 12:45:04.099: SSS MGR [uid:21]: Handling Connect-Service event*Nov 15 12:45:04.099: VPDN CALL [uid:21]: Event connect req, state changed from idleto connecting*Nov 15 12:45:04.099: VPDN CALL [uid:21]: Requesting connection*Nov 15 12:45:04.099: VPDN CALL [uid:21]: Call request sent*Nov 15 12:45:04.099: VPDN MGR [uid:21]: Event client connect, state changed fromidle to connecting*Nov 15 12:45:04.099: VPDN MGR [uid:21]: Initiating compulsory connection to192.168.8.2*Nov 15 12:45:04.099: Tnl/Sn31399/10 L2TP: Session FS enabled*Nov 15 12:45:04.099: Tnl/Sn31399/10 L2TP: Session state change from idle towait-for-tunnel*Nov 15 12:45:04.099: uid:21 Tnl/Sn31399/10 L2TP: Create session*Nov 15 12:45:04.099: Tnl31399 L2TP: SM State idle*Nov 15 12:45:04.099: Tnl31399 L2TP: O SCCRQ*Nov 15 12:45:04.099: Tnl31399 L2TP: Control channel retransmit delay set to 1seconds*Nov 15 12:45:04.099: Tnl31399 L2TP: Tunnel state change from idle towait-ctl-reply*Nov 15 12:45:04.099: Tnl31399 L2TP: SM State wait-ctl-reply*Nov 15 12:45:04.099: [21]PPPoE 18: State LCP_NEGO Event PPP_FWDING*Nov 15 12:45:04.107: Tnl31399 L2TP: I SCCRP from rp1*Nov 15 12:45:04.107: Tnl31399 L2TP: Got a challenge from remote peer, rp1*Nov 15 12:45:04.107: Tnl31399 L2TP: Got a response from remote peer, rp1*Nov 15 12:45:04.107: Tnl31399 L2TP: Tunnel Authentication success*Nov 15 12:45:04.107: Tnl31399 L2TP: Tunnel state change from wait-ctl-reply toestablished*Nov 15 12:45:04.107: Tnl31399 L2TP: O SCCCN to rp1 tnlid 9349*Nov 15 12:45:04.107: Tnl31399 L2TP: Control channel retransmit delay set to 1seconds*Nov 15 12:45:04.107: Tnl31399 L2TP: SM State established*Nov 15 12:45:04.107: uid:21 Tnl/Sn31399/10 L2TP: O ICRQ to rp1 9349/0*Nov 15 12:45:04.107: [21]PPPoE 18: Access IE nas port called*Nov 15 12:45:04.107: uid:21 Tnl/Sn31399/10 L2TP: Session state change fromwait-for-tunnel to wait-reply*Nov 15 12:45:04.115: uid:21 Tnl/Sn31399/10 L2TP: O ICCN to rp1 9349/13589*Nov 15 12:45:04.115: Tnl31399 L2TP: Control channel retransmit delay set to 1seconds*Nov 15 12:45:04.115: uid:21 Tnl/Sn31399/10 L2TP: Session state change fromwait-reply to established*Nov 15 12:45:04.115: uid:21 Tnl/Sn31399/10 L2TP: VPDN session up*Nov 15 12:45:04.115: VPDN MGR [uid:21]: Event peer connected, state changed fromconnecting to connected*Nov 15 12:45:04.115: VPDN MGR [uid:21]: Succeed to forward nobody@example.com*Nov 15 12:45:04.115: VPDN MGR [uid:21]: accounting start sent*Nov 15 12:45:04.115: [21]PPPoE 18: AAA pppoe_aaa_acct_get_dynamic_attrs*Nov 15 12:45:04.115: [21]PPPoE 18: AAA pppoe_aaa_acct_get_dynamic_attrs*Nov 15 12:45:04.115: VPDN CALL [uid:21]: Event connect ok, state changed fromconnecting to connected*Nov 15 12:45:04.115: VPDN CALL [uid:21]: Connection succeeded*Nov 15 12:45:04.115: SSS MGR [uid:21]: Handling Service-Connected event*Nov 15 12:45:04.115: ppp21 PPP: Phase is FORWARDED, Session Forwarded*Nov 15 12:45:04.115: [21]PPPoE 18: State LCP_NEGO Event PPP_FWDED*Nov 15 12:45:04.115: [21]PPPoE 18: data path set to SSS Switch*Nov 15 12:45:04.119: [21]PPPoE 18: Connected Forwarded*Nov 15 12:45:04.119: ppp21 PPP: Process pending packets*Nov 15 12:45:04.139: uid:21 Tnl/Sn31399/10 L2TP: Result code(2): 2: Calldisconnected, refer to error msg*Nov 15 12:45:04.139: Error code(6): Vendor specific*Nov 15 12:45:04.139: Optional msg: Locally generated disconnect*Nov 15 12:45:04.139: uid:21 Tnl/Sn31399/10 L2TP: I CDN from rp1 tnl 9349, cl1358901:06:21: %VPDN-6-CLOSED: L2TP LNS 192.168.8.2 closed user nobody@example.com; Result2, Error 6, Locally generated disconnect*Nov 15 12:45:04.139: uid:21 Tnl/Sn31399/10 L2TP: disconnect (L2X) IETF:18/host-request Ascend: 66/VPDN Local PPP Disconnect*Nov 15 12:45:04.139: uid:21 Tnl/Sn31399/10 L2TP: Destroying session*Nov 15 12:45:04.139: uid:21 Tnl/Sn31399/10 L2TP: Session state change fromestablished to idle*Nov 15 12:45:04.139: VPDN MGR [uid:21]: Event peer disconnect, state changed fromconnected to disconnected*Nov 15 12:45:04.139: VPDN MGR [uid:21]: Remote disconnected nobody@example.com*Nov 15 12:45:04.139: VPDN MGR [uid:21]: accounting stop sent*Nov 15 12:45:04.139: Tnl31399 L2TP: Tunnel state change from established tono-sessions-left*Nov 15 12:45:04.143: Tnl31399 L2TP: No more sessions in tunnel, shutdown (likely)in 15 seconds*Nov 15 12:45:04.143: VPDN CALL [uid:21]: Event server disc, state changed fromconnected to disconnected*Nov 15 12:45:04.143: VPDN CALL [uid:21]: Server disconnected call*Nov 15 12:45:04.143: VPDN CALL [uid:21]: Event free req, state changed fromdisconnected to terminal*Nov 15 12:45:04.143: VPDN CALL [uid:21]: Free request*Nov 15 12:45:04.143: SSS MGR [uid:21]: Handling Send Client Disconnect*Nov 15 12:45:04.143: [21]PPPoE 18: State CNCT_FWDED Event SSS_DISCNCT*Nov 15 12:45:04.143: ppp21 PPP: Sending Acct Event[Down] id[16]*Nov 15 12:45:04.143: ppp21 PPP: Phase is TERMINATING*Nov 15 12:45:04.143: ppp21 LCP: State is Closed*Nov 15 12:45:04.143: ppp21 PPP: Phase is DOWN*Nov 15 12:45:04.143: [21]PPPoE 18: O PADT R:0000.0c14.71d0 L:00b0.c2e9.c870 1/32ATM4/0.132*Nov 15 12:45:04.143: [21]PPPoE 18: Destroying R:0000.0c14.71d0 L:00b0.c2e9.c8701/32 ATM4/0.132*Nov 15 12:45:04.143: [21]PPPoE 18: AAA pppoe_aaa_acct_get_dynamic_attrs*Nov 15 12:45:04.143: [21]PPPoE 18: AAA pppoe_aaa_acct_get_dynamic_attrs*Nov 15 12:45:04.143: [21]PPPoE 18: AAA account stopped*Nov 15 12:45:14.139: Tnl31399 L2TP: I StopCCN from rp1 tnl 9349*Nov 15 12:45:14.139: Tnl31399 L2TP: Shutdown tunnel*Nov 15 12:45:14.139: Tnl31399 L2TP: Tunnel state change from no-sessions-leftTroubleshooting the Subscriber Service Switch on the LNS—Normal Operation: Example
The following example shows the debug commands used and sample output indicating normal operation of the Subscriber Service Switch on the LNS:
Router# debug sss eventRouter# debug sss errorRouter# debug sss fsmRouter# debug ppp negotiationRouter# debug vpdn l2x-eventsRouter# debug vpdn l2x-errorsRouter# debug vpdn sss eventsRouter# debug vpdn sss errorsRouter# debug vpdn sss fsmSSS:SSS events debugging is onSSS error debugging is onSSS fsm debugging is onPPP:PPP protocol negotiation debugging is onVPN:L2X protocol events debugging is onL2X protocol errors debugging is onVPDN SSS events debugging is onVPDN SSS errors debugging is onVPDN SSS FSM debugging is on3d17h: Tnl9264 L2TP: I ICRQ from server1 tnl 615103d17h: Tnl/Sn9264/13586 L2TP: Session FS enabled3d17h: Tnl/Sn9264/13586 L2TP: Session state change from idle to wait-connect3d17h: Tnl/Sn9264/13586 L2TP: New session created3d17h: Tnl/Sn9264/13586 L2TP: O ICRP to server1 61510/73d17h: Tnl9264 L2TP: Control channel retransmit delay set to 1 seconds3d17h: Tnl/Sn9264/13586 L2TP: I ICCN from server1 tnl 61510, cl 73d17h: nobody@example.com Tnl/Sn9264/13586 L2TP: Session state change fromwait-connect to wait-for-service-selection3d17h: VPDN SSS []: Event start sss, state changed from IDLE to SSS3d17h: VPDN SSS [uid:707]: Service request sent to SSS3d17h: SSS INFO: Element type is Access-Type, long value is 43d17h: SSS INFO: Element type is Switch-Id, long value is 14931725613d17h: SSS INFO: Element type is Tunnel-Name, string value is server13d17h: SSS INFO: Element type is Can-SIP-Redirect, long value is 13d17h: SSS INFO: Element type is AAA-Id, long value is 167263d17h: SSS INFO: Element type is AccIe-Hdl, ptr value is D10001673d17h: SSS MGR [uid:707]: Event service-request, state changed from wait-for-req towait-for-auth3d17h: SSS MGR [uid:707]: Handling Policy Authorize (1 pending sessions)3d17h: SSS PM [uid:707]: RM/VPDN disabled: RM/VPDN author not needed3d17h: SSS PM [uid:707]: Multihop disabled: AAA author not needed3d17h: SSS PM [uid:707]: Multihop disabled: SGF author not needed3d17h: SSS PM [uid:707]: No more authorization methods left to try, providingdefault service3d17h: SSS PM [uid:707]: Received Service Request3d17h: SSS PM [uid:707]: Event <found>, State: initial-req to end3d17h: SSS PM [uid:707]: Handling Service Direction3d17h: SSS PM [uid:707]: Policy reply - Local terminate3d17h: SSS MGR [uid:707]: Got reply Local-Term from PM3d17h: SSS MGR [uid:707]: Event policy-connect local, state changed fromwait-for-auth to connected3d17h: SSS MGR [uid:707]: Handling Send-Client-Local-Term event3d17h: VPDN SSS [uid:707]: Event connect local, state changed from SSS to PPP3d17h: ppp707 PPP: Phase is ESTABLISHING3d17h: ppp707 LCP: I FORCED rcvd CONFACK len 153d17h: ppp707 LCP: MRU 1492 (0x010405D4)3d17h: ppp707 LCP: AuthProto CHAP (0x0305C22305)3d17h: ppp707 LCP: MagicNumber 0xB0EC4557 (0x0506B0EC4557)3d17h: ppp707 LCP: I FORCED sent CONFACK len 103d17h: ppp707 LCP: MRU 1492 (0x010405D4)3d17h: ppp707 LCP: MagicNumber 0x0017455D (0x05060017455D)3d17h: ppp707 PPP: Phase is FORWARDING, Attempting Forward3d17h: VPDN SSS [uid:707]: Event dyn bind resp, state changed from PPP to PPP3d17h: ppp707 PPP: Phase is AUTHENTICATING, Unauthenticated User3d17h: ppp707 PPP: Phase is FORWARDING, Attempting Forward3d17h: VPDN SSS [uid:707]: Event connect local, state changed from PPP to PPP3d17h: VPDN SSS [Vi4.2]: Event vaccess resp, state changed from PPP to PPP3d17h: VPDN SSS [Vi4.2]: Event stat bind resp, state changed from PPP to CNCT3d17h: Vi4.2 Tnl/Sn9264/13586 L2TP: Session state change fromwait-for-service-selection to established3d17h: Vi4.2 PPP: Phase is AUTHENTICATING, Authenticated User3d17h: Vi4.2 CHAP: O SUCCESS id 1 len 43d17h: Vi4.2 PPP: Phase is UP3d17h: Vi4.2 IPCP: O CONFREQ [Closed] id 1 len 103d17h: Vi4.2 IPCP: Address 172.16.0.0 (0x030681010000)3d17h: Vi4.2 PPP: Process pending packets3d17h: Vi4.2 IPCP: I CONFREQ [REQsent] id 1 len 103d17h: Vi4.2 IPCP: Address 10.0.0.0 (0x030600000000)3d17h: Vi4.2 AAA/AUTHOR/IPCP: Start. Her address 10.0.0.0, we want 10.0.0.03d17h: Vi4.2 AAA/AUTHOR/IPCP: Done. Her address 10.0.0.0, we want 10.0.0.03d17h: Vi4.2 IPCP: Pool returned 10.1.1.33d17h: Vi4.2 IPCP: O CONFNAK [REQsent] id 1 len 103d17h: Vi4.2 IPCP: Address 10.1.1.3 (0x03065B010103)3d17h: Vi4.2 IPCP: I CONFACK [REQsent] id 1 len 103d17h: Vi4.2 IPCP: Address 172.16.0.0 (0x030681010000)3d17h: Vi4.2 IPCP: I CONFREQ [ACKrcvd] id 2 len 103d17h: Vi4.2 IPCP: Address 10.1.1.3 (0x03065B010103)3d17h: Vi4.2 IPCP: O CONFACK [ACKrcvd] id 2 len 103d17h: Vi4.2 IPCP: Address 10.1.1.3 (0x03065B010103)3d17h: Vi4.2 IPCP: State is Open3d17h: Vi4.2 IPCP: Install route to 10.1.1.3Troubleshooting the Subscriber Service Switch on the LNS—Tunnel Failure: Example
The following is sample output indicating tunnel failure on the LNS:
3d17h: L2TP: I SCCRQ from server1 tnl 313993d17h: Tnl9349 L2TP: Got a challenge in SCCRQ, server13d17h: Tnl9349 L2TP: New tunnel created for remote server1, address 192.168.8.13d17h: Tnl9349 L2TP: O SCCRP to server1 tnlid 313993d17h: Tnl9349 L2TP: Control channel retransmit delay set to 1 seconds3d17h: Tnl9349 L2TP: Tunnel state change from idle to wait-ctl-reply3d17h: Tnl9349 L2TP: I SCCCN from server1 tnl 313993d17h: Tnl9349 L2TP: Got a Challenge Response in SCCCN from server13d17h: Tnl9349 L2TP: Tunnel Authentication success3d17h: Tnl9349 L2TP: Tunnel state change from wait-ctl-reply to established3d17h: Tnl9349 L2TP: SM State established3d17h: Tnl9349 L2TP: I ICRQ from server1 tnl 313993d17h: Tnl/Sn9349/13589 L2TP: Session FS enabled3d17h: Tnl/Sn9349/13589 L2TP: Session state change from idle to wait-connect3d17h: Tnl/Sn9349/13589 L2TP: New session created3d17h: Tnl/Sn9349/13589 L2TP: O ICRP to server1 31399/103d17h: Tnl9349 L2TP: Control channel retransmit delay set to 1 seconds3d17h: Tnl/Sn9349/13589 L2TP: I ICCN from server1 tnl 31399, cl 103d17h: nobody@example.com Tnl/Sn9349/13589 L2TP: Session state change fromwait-connect to wait-for-service-selection3d17h: VPDN SSS []: Event start sss, state changed from IDLE to SSS3d17h: VPDN SSS [uid:709]: Service request sent to SSS3d17h: SSS INFO: Element type is Access-Type, long value is 43d17h: SSS INFO: Element type is Switch-Id, long value is -19126022843d17h: SSS INFO: Element type is Tunnel-Name, string value is server13d17h: SSS INFO: Element type is Can-SIP-Redirect, long value is 13d17h: SSS INFO: Element type is AAA-Id, long value is 167293d17h: SSS INFO: Element type is AccIe-Hdl, ptr value is 8D00016A3d17h: SSS MGR [uid:709]: Event service-request, state changed from wait-for-req towait-for-auth3d17h: SSS MGR [uid:709]: Handling Policy Authorize (1 pending sessions)3d17h: SSS PM [uid:709]: RM/VPDN disabled: RM/VPDN author not needed3d17h: SSS PM [uid:709]: Multihop disabled: AAA author not needed3d17h: SSS PM [uid:709]: Multihop disabled: SGF author not neededd17h: SSS PM [uid:709]: No more authorization methods left to try, providing defaultservice3d17h: SSS PM [uid:709]: Received Service Request3d17h: SSS PM [uid:709]: Event <found>, State: initial-req to end3d17h: SSS PM [uid:709]: Handling Service Direction3d17h: SSS PM [uid:709]: Policy reply - Local terminate3d17h: SSS MGR [uid:709]: Got reply Local-Term from PM3d17h: SSS MGR [uid:709]: Event policy-connect local, state changed fromwait-for-auth to connected3d17h: SSS MGR [uid:709]: Handling Send-Client-Local-Term event3d17h: VPDN SSS [uid:709]: Event connect local, state changed from SSS to PPP3d17h: ppp709 PPP: Phase is ESTABLISHING3d17h: ppp709 LCP: I FORCED rcvd CONFACK len 153d17h: ppp709 LCP: MRU 1492 (0x010405D4)3d17h: ppp709 LCP: AuthProto CHAP (0x0305C22305)3d17h: ppp709 LCP: MagicNumber 0xB0FFA4D8 (0x0506B0FFA4D8)3d17h: ppp709 LCP: I FORCED sent CONFACK len 103d17h: ppp709 LCP: MRU 1492 (0x010405D4)3d17h: ppp709 LCP: MagicNumber 0x002AA481 (0x0506002AA481)3d17h: ppp709 PPP: Phase is FORWARDING, Attempting Forward3d17h: VPDN SSS [uid:709]: Event dyn bind resp, state changed from PPP to PPP3d17h: ppp709 PPP: Phase is AUTHENTICATING, Unauthenticated User3d17h: ppp709 CHAP: O FAILURE id 1 len 25 msg is "Authentication failed"3d17h: ppp709 PPP: Sending Acct Event[Down] id[4159]3d17h: ppp709 PPP: Phase is TERMINATING3d17h: ppp709 LCP: O TERMREQ [Open] id 1 len 43d17h: ppp709 LCP: State is Closed3d17h: ppp709 PPP: Phase is DOWN3d17h: ppp709 PPP: Phase is TERMINATING3d17h: VPDN SSS [uid:709]: Event peer disc, state changed from PPP to DSC3d17h: nobody@example.com Tnl/Sn9349/13589 L2TP: disconnect (AAA) IETF:17/user-error Ascend: 26/PPP CHAP Fail3d17h: nobody@example.com Tnl/Sn9349/13589 L2TP: O CDN to server1 31399/103d17h: Tnl9349 L2TP: Control channel retransmit delay set to 1 seconds3d17h: nobody@example.com Tnl/Sn9349/13589 L2TP: Destroying session3d17h: nobody@example.com Tnl/Sn9349/13589 L2TP: Session state change fromwait-for-service-selection to idle3d17h: VPDN SSS [uid:709]: Event vpdn disc, state changed from DSC to END3d17h: Tnl9349 L2TP: Tunnel state change from established to no-sessions-left3d17h: Tnl9349 L2TP: No more sessions in tunnel, shutdown (likely) in 10 seconds3d17h: SSS MGR [uid:709]: Processing a client disconnect3d17h: SSS MGR [uid:709]: Event client-disconnect, state changed from connected toend3d17h: SSS MGR [uid:709]: Handling Send-Service-Disconnect event3d17h: Tnl9349 L2TP: O StopCCN to server1 tnlid 313993d17h: Tnl9349 L2TP: Control channel retransmit delay set to 1 seconds3d17h: Tnl9349 L2TP: Tunnel state change from no-sessions-left to shutting-down3d17h: Tnl9349 L2TP: Shutdown tunnelWhere to Go Next
•
If you want to establish PPPoE session limits for sessions on a specific permanent virtual circuit or VLAN configured on an L2TP access concentrator, refer to the "Establishing PPPoE Session Limits per NAS Port" module.
•
If you want to use service tags to enable a PPPoE server to offer PPPoE clients a selection of service during call setup, refer to the "Offering PPPoE Clients a Selection of Services During Call Setup" module.
•
If you want to enable an L2TP access concentrator to relay active discovery and service selection functionality for PPPoE over a L2TP control channel to an LNS or tunnel switch, refer to the "Enabling PPPoE Relay Discovery and Service Selection Functionality" module.
•
If you want to configure a transfer upstream of the PPPoX session speed value, refer to the "Configuring Upstream Connections Speed Transfer" module.
•
If you want to use the Simple Network Management Protocol (SNMP) to monitor PPPoE sessions, refer to the "Monitoring PPPoE Sessions with SNMP" module.
•
If you want to identify a physical subscribe line for RADIUS communication with a RADIUS server, refer to the "Identifying a Physical Subscriber Line for RADIUS Access and Accounting" module.
•
If you want to configure a Cisco Subscriber Service Switch, see the "Configuring Cisco Subscriber Service Switch Policies" module.
Additional References
The following sections provide references related to configuring Cisco Subscriber Service Switch policies.
Related Documents
Broadband access aggregation concepts
Tasks for preparing for broadband access aggregation.
Broadband access commands: complete command syntax, command mode, command history, defaults, usage guidelines, and examples
"Wide-Area Networking Commands" chapter in the Cisco IOS Wide-Area Networking Command Reference
Configuration procedure for PPPoE.
"Providing Protocol Support for Broadband Access Aggregation of PPPoE Sessions"
Configuration procedures for PPPoA.
"Providing Protocol Support for Broadband Access Aggregation of PPP over ATM Sessions"
Standards
MIBs
None
To locate and download MIBs for selected platforms, Cisco IOS releases, and feature sets, use Cisco MIB Locator found at the following URL:
RFCs
RFC 2661
Layer Two Tunneling Protocol L2TP
RFC 2341
Cisco Layer Two Forwarding (Protocol) L2F
RFC 2516
A Method for Transmitting PPP Over Ethernet (PPPoE) (PPPoE Discovery)
Technical Assistance
Feature Information for Configuring a Subscriber Service Switch Policy
Table 3 lists the features in this module and provides links to specific configuration information. Only features that were introduced or modified in Cisco IOS Release 12.0(3)S or later releases appear in the table.
For information on a feature in this technology that is not documented here, see the "Configuring Broadband Access Aggregation Features Roadmap."
Not all commands may be available in your Cisco IOS software release. For release information about a specific command, see the command reference documentation.
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which Cisco IOS and Catalyst OS software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Note
Table 3 lists only the Cisco IOS software release that introduced support for a given feature in a given Cisco IOS software release train. Unless noted otherwise, subsequent releases of that Cisco IOS software release train also support that feature.
CCDE, CCENT, Cisco Eos, Cisco Lumin, Cisco Nexus, Cisco StadiumVision, Cisco TelePresence, Cisco WebEx, the Cisco logo, DCE, and Welcome to the Human Network are trademarks; Changing the Way We Work, Live, Play, and Learn and Cisco Store are service marks; and Access Registrar, Aironet, AsyncOS, Bringing the Meeting To You, Catalyst, CCDA, CCDP, CCIE, CCIP, CCNA, CCNP, CCSP, CCVP, Cisco, the Cisco Certified Internetwork Expert logo, Cisco IOS, Cisco Press, Cisco Systems, Cisco Systems Capital, the Cisco Systems logo, Cisco Unity, Collaboration Without Limitation, EtherFast, EtherSwitch, Event Center, Fast Step, Follow Me Browsing, FormShare, GigaDrive, HomeLink, Internet Quotient, IOS, iPhone, iQuick Study, IronPort, the IronPort logo, LightStream, Linksys, MediaTone, MeetingPlace, MeetingPlace Chime Sound, MGX, Networkers, Networking Academy, Network Registrar, PCNow, PIX, PowerPanels, ProConnect, ScriptShare, SenderBase, SMARTnet, Spectrum Expert, StackWise, The Fastest Way to Increase Your Internet Quotient, TransPath, WebEx, and the WebEx logo are registered trademarks of Cisco Systems, Inc. and/or its affiliates in the United States and certain other countries.
All other trademarks mentioned in this document or website are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (0809R)
Any Internet Protocol (IP) addresses used in this document are not intended to be actual addresses. Any examples, command display output, and figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses in illustrative content is unintentional and coincidental.
© 2008 Cisco Systems, Inc. All rights reserved.