Switch(config)#ip nbar custom MYDOMAIN composite server-name *mydomain.com id 13
在 Catalyst 9000 系列交換器上設定並驗證 NetFlow、AVC 及 ETA
下載選項
無偏見用語
本產品的文件集力求使用無偏見用語。針對本文件集的目的,無偏見係定義為未根據年齡、身心障礙、性別、種族身分、民族身分、性別傾向、社會經濟地位及交織性表示歧視的用語。由於本產品軟體使用者介面中硬式編碼的語言、根據 RFP 文件使用的語言,或引用第三方產品的語言,因此本文件中可能會出現例外狀況。深入瞭解思科如何使用包容性用語。
關於此翻譯
思科已使用電腦和人工技術翻譯本文件,讓全世界的使用者能夠以自己的語言理解支援內容。請注意,即使是最佳機器翻譯,也不如專業譯者翻譯的內容準確。Cisco Systems, Inc. 對這些翻譯的準確度概不負責,並建議一律查看原始英文文件(提供連結)。
簡介
本文件說明如何設定並驗證 NetFlow、Application Visibility and Control (AVC) 及加密流量分析 (ETA)。
必要條件
需求
思科建議您瞭解以下主題:
- Netflow
- AVC
- ETA
採用元件
本文件中的資訊是以執行 Cisco IOS® XE 軟體 16.12.4. 的 Catalyst 9300 交換器為準。
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路運作中,請確保您瞭解任何指令可能造成的影響。
相關產品
本文件也適用於以下硬體和軟體版本:
- 9200(僅支援 NetFlow 與 AVC)
- 9300(支援 NetFlow、AVC 與 ETA)
- 9400(支援 NetFlow、AVC 與 ETA)
- 9500(僅支援 NetFlow 與 AVC)
- 9600(僅支援 NetFlow 與 AVC)
- Cisco IOS XE 16.12 與更新版本
背景資訊
- Flexible NetFlow 是新一代的流量技術,會收集並測量資料,讓網路中的所有路由器或交換器成為遙測的來源。
- Flexible NetFlow 可進行極為精細又準確的流量測量以及高階聚合式流量收集。
- Flexible NetFlow 使用流量來提供用於計費、網路監視和網路規劃的統計資料。
- 流是到達源介面且金鑰值相同的單向資料包流。金鑰是封包內欄位中已識別的值。您透過流量記錄來建立流量以定義流量的唯一金鑰。
附註:平台(fed)命令可能有所不同。命令可以是 與 的語法。如果示例中註明的語法未解析出,請嘗試變體。show platform fed show platform fed switch
網路圖表
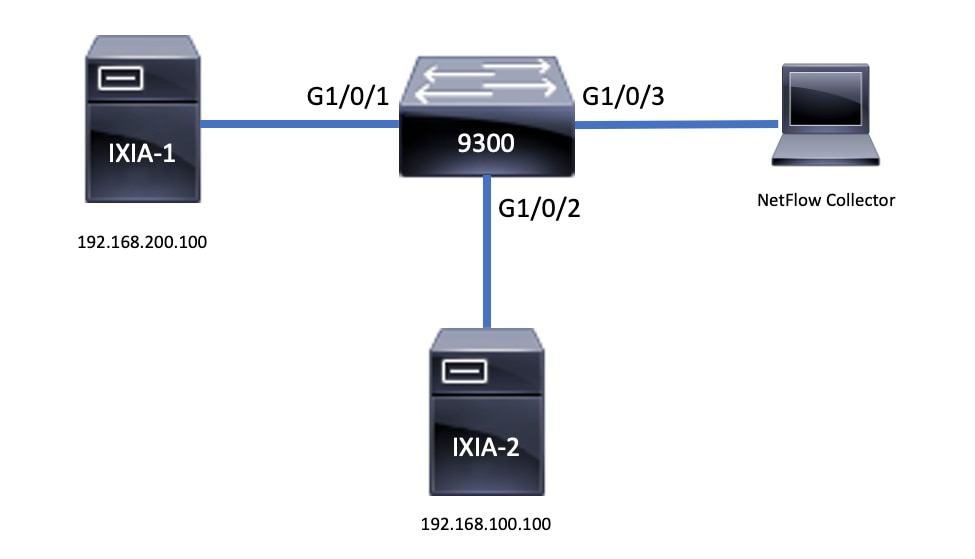
設定
元件
NetFlow 組態包含三個主要元件,這些元件能夠以多種變化結合使用,以執行流量分析與資料匯出。
流量記錄
- 記錄是金鑰與非金鑰欄位的組合。Flexible NetFlow 記錄可以指派至 Flexible NetFlow 流量監視器,以定義用於流量資料儲存的快取。
- Flexible NetFlow 包含幾筆預先定義且可以用來監視流量的記錄。
- Flexible NetFlow 還允許按照金鑰欄位與非金鑰欄位規格,為 Flexible NetFlow 流量監視器快取定義自訂記錄,以便按照您的特定需求自訂資料收集。
如範例所示,流量記錄組態詳細資料如下:
flow record TAC-RECORD-IN
match flow direction
match ipv4 source address
match interface input
match ipv4 destination address
match ipv4 protocol
collect counter packets long
collect counter bytes long
collect timestamp absolute last
collect transport tcp flags
flow record TAC-RECORD-OUT
match flow direction
match interface output
match ipv4 source address
match ipv4 destination address
match ipv4 protocol
collect counter packets long
collect counter bytes long
collect timestamp absolute last
collect transport tcp flags
流量匯出器
- 流量匯出器用來將流量監視器快取中的資料匯出至遠端系統(功用為 NetFlow 收集器的伺服器),以進行分析和儲存。
- 將流量匯出器指派至流量監視器,以便為流量監視器提供資料匯出功能。
如範例所示,流量匯出器組態詳細資料如下:
flow exporter TAC-EXPORT
destination 192.168.69.2
source Vlan69
流量監視器
- 流量監視器是套用於介面的 Flexible NetFlow 元件,以執行網路流量監視。
- 流資料從網路流量收集,並在進程運行時增加到流監控器快取。程序是以流量記錄中的金鑰與非金鑰欄位為基礎。
如範例所示,流量監視器組態詳細資料如下:
flow monitor TAC-MONITOR-IN
exporter TAC-EXPORT
record TAC-RECORD-IN
flow monitor TAC-MONITOR-OUT
exporter TAC-EXPORT
record TAC-RECORD-OUT
Switch#show run int g1/0/1
Building configuration...
Current configuration : 185 bytes
!
interface GigabitEthernet1/0/1
switchport access vlan 42
switchport mode access
ip flow monitor TAC-MONITOR-IN input
ip flow monitor TAC-MONITOR-OUT output
load-interval 30
end
流量取樣工具(選用)
- 在路由器組態中建立流量取樣工具作為個別的元件。
- 流量取樣工具會限制選取供分析的封包數量,以減少使用 Flexible NetFlow 之裝置的負載。
- 流量取樣工具用來減少使用 Flexible NetFlow 之裝置的負載,方法是透過限制選取供分析的封包數量。
- 流量取樣器可以交換路由器效能的準確度。經過流量監視器分析的封包如果數量減少,儲存在流量監視器快取中的資訊準確度就會受到影響。
如範例所示,流量取樣工具組態範例:
sampler SAMPLE-TAC
description Sample at 50%
mode random 1 out-of 2
Switch(config)#interface GigabitEthernet1/0/1
Switch(config-if)#ip flow monitor TAC-MONITOR-IN sampler SAMPLE-TAC input
Switch(config-if)#end
限制
- 完整Flexible NetFlow需要Cisco DNA附加許可證,否則取樣NetFlow僅可用。
- 流量匯出器無法使用管理連接埠作為來源。
這並非完整的清單,請參閱組態指南,瞭解適用的平台與代碼。
驗證
無須依賴平台的驗證
驗證組態並確認所需的 NetFlow 元件是否存在:
- 流量記錄
- 流量匯出器
- 流量監視器
- 流量取樣工具(選用)
提示:要檢視一個命令中的流記錄、流匯出器和流監控器輸出,請運行show running-config flow monitor 。
如範例所示,流量監視器與輸入方向及其相關聯元件息息相關:
Switch#show running-config flow monitor TAC-MONITOR-IN expand Current configuration: ! flow record TAC-RECORD-IN match ipv4 protocol match ipv4 source address match ipv4 destination address match interface input match flow direction collect transport tcp flags collect counter bytes long collect counter packets long collect timestamp absolute last ! flow exporter TAC-EXPORT destination 192.168.69.2 source Vlan69 ! flow monitor TAC-MONITOR-IN exporter TAC-EXPORT record TAC-RECORD-IN !
如範例所示,流量監視器與輸出方向及其相關聯元件息息相關:
Switch#show run flow monitor TAC-MONITOR-OUT expand Current configuration: ! flow record TAC-RECORD-OUT match ipv4 protocol match ipv4 source address match ipv4 destination address match interface output match flow direction collect transport tcp flags collect counter bytes long collect counter packets long collect timestamp absolute last ! flow exporter TAC-EXPORT destination 192.168.69.2 source Vlan69 ! flow monitor TAC-MONITOR-OUT exporter TAC-EXPORT record TAC-RECORD-OUT !
執行命令 。 show flow monitor 此輸出有助於確認資料已記錄:
Switch#show flow monitor TAC-MONITOR-IN statistics Cache type: Normal (Platform cache) Cache size: 10000 Current entries: 1 Flows added: 1 Flows aged: 0
運行命令 以確認NetFlow快取有輸出:show flow monitor
Switch#show flow monitor TAC-MONITOR-IN cache Cache type: Normal (Platform cache) Cache size: 10000 Current entries: 1 Flows added: 1 Flows aged: 0 IPV4 SOURCE ADDRESS: 192.168.200.100 IPV4 DESTINATION ADDRESS: 192.168.100.100 INTERFACE INPUT: Gi1/0/1 FLOW DIRECTION: Input IP PROTOCOL: 17 tcp flags: 0x00 counter bytes long: 4606617470 counter packets long: 25311085 timestamp abs last: 22:44:48.579
運行命令 以確認導出器是否傳送了資料包:show flow exporter
Switch#show flow exporter TAC-EXPORT statistics
Flow Exporter TAC-EXPORT:
Packet send statistics (last cleared 00:08:38 ago):
Successfully sent: 2 (24 bytes)
Client send statistics:
Client: Flow Monitor TAC-MONITOR-IN
Records added: 0
Bytes added: 12
- sent: 12
Client: Flow Monitor TAC-MONITOR-OUT
Records added: 0
Bytes added: 12
- sent: 12需依賴平台的驗證
NetFlow 初始化 - NFL 分割區資料表
- NetFlow 分割區會針對不同功能進行初始化,每個方向(輸入與輸出)有 16 個分割區。
- NetFlow 分割區資料表組態分為全域排配置,它會進一步細分為輸入流量排與輸出流量排。
主要欄位
- 分割區數量
- 分割區啟用狀態
- 分割區限制
- 目前分割區使用情況
要檢視NetFlow分割槽表,您可以運行命令 。show platform software fed switch active|standby|member| fnf sw-table-sizes asic
附註:建立的流特定於交換機和asic核心。需要相應地指定交換器編號(主用、備用等)。輸入的ASIC編號與對應的介面繫結,使用 來確定與介面對應的ASIC。show platform software fed switch active|standby|member ifm mappings 若為影子選項,一律使用 0。
Switch#show platform software fed switch active fnf sw-table-sizes asic 0 shadow 0
---------------------------------
Global Bank Allocation
---------------------------------
Ingress Banks : Bank 0 Bank 1
Egress Banks : Bank 2 Bank 3
---------------------------------
Global flow table Info <--- Provides the number of entries used per direction
INGRESS usedBankEntry 0 usedOvfTcamEntry 0
EGRESS usedBankEntry 0 usedOvfTcamEntry 0
---------------------------------
Flows Statistics
INGRESS TotalSeen=0 MaxEntries=0 MaxOverflow=0
EGRESS TotalSeen=0 MaxEntries=0 MaxOverflow=0
---------------------------------
Partition Table
---------------------------------
## Dir Limit CurrFlowCount OverFlowCount MonitoringEnabled
0 ING 0 0 0 0
1 ING 16640 0 0 1 <-- Current flow count in hardware
2 ING 0 0 0 0
3 ING 16640 0 0 0
4 ING 0 0 0 0
5 ING 8192 0 0 1
6 ING 0 0 0 0
7 ING 0 0 0 0
8 ING 0 0 0 0
9 ING 0 0 0 0
10 ING 0 0 0 0
11 ING 0 0 0 0
12 ING 0 0 0 0
13 ING 0 0 0 0
14 ING 0 0 0 0
15 ING 0 0 0 0
0 EGR 0 0 0 0
1 EGR 16640 0 0 1 <-- Current flow count in hardware
2 EGR 0 0 0 0
3 EGR 16640 0 0 0
4 EGR 0 0 0 0
5 EGR 8192 0 0 1
6 EGR 0 0 0 0
7 EGR 0 0 0 0
8 EGR 0 0 0 0
9 EGR 0 0 0 0
10 EGR 0 0 0 0
11 EGR 0 0 0 0
12 EGR 0 0 0 0
13 EGR 0 0 0 0
14 EGR 0 0 0 0
15 EGR 0 0 0 0流量監視器
流量監視器組態包含以下項目:
1. NetFlow ACL 組態會在 ACL TCAM 資料表中建立項目。
ACL TCAM 項目包含以下內容:
- 查詢相符的金鑰
- 用於 NetFlow 查詢的結果參數,其中包含以下內容:
- 設定檔 ID
- NetFlow ID
2. 流量遮罩組態,會在 NflLookupTable 與 NflFlowMaskTable 中建立項目。
- 按照 NetFlow ACL 結果參數編制索引以找出 NetFlow 查詢的流量遮罩
NetFlow ACL
要檢視NetFlow ACL配置,請運行命令 。show platform hardware fed switch active fwd-asic resource tcam table nfl_acl asic
提示:如果有埠ACL(PACL),則在該介面對映到的ASIC上建立該條目。如果是路由器 ACL (RACL),則所有 ASIC 皆存在此項目。
- 在此輸出中有 NFCMD0 與 NFCMD1,皆為 4 位元值。為了計算設定檔 ID,請將值轉換為二進位。
- 在此輸出中,NFCMD0為1,NFCMD1為2。轉換為二進位制時:000100010
- 在 Cisco IOS XE 16.12 與更新版本的組合式 8 位元中,前 4 個位元是設定檔 ID,而第 7 個位元則表示查詢已啟用。 如範例所示 (00010010),設定檔 ID 為 1。
- 在 Cisco IOS XE 16.11 與舊版程式碼的組合式 8 位元中,前 6 個位元是設定檔 ID,而第 7 個位元則表示查詢已啟用。如範例所示 (00010010),設定檔 ID 為 4。
Switch#show platform hardware fed switch active fwd-asic resource tcam table nfl_acl asic 0
Printing entries for region INGRESS_NFL_ACL_CONTROL (308) type 6 asic 0
========================================================
Printing entries for region INGRESS_NFL_ACL_GACL (309) type 6 asic 0
========================================================
Printing entries for region INGRESS_NFL_ACL_PACL (310) type 6 asic 0
========================================================
TAQ-2 Index-32 (A:0,C:0) Valid StartF-1 StartA-1 SkipF-0 SkipA-0
Input IPv4 NFL PACL
Labels Port Vlan L3If Group
M: 00ff 0000 0000 0000
V: 0001 0000 0000 0000
vcuResults l3Len l3Pro l3Tos SrcAddr DstAddr mtrid vrfid SH
M: 00000000 0000 00 00 00000000 00000000 00 0000 0000
V: 00000000 0000 00 00 00000000 00000000 00 0000 0000
RMAC RA MEn IPOPT MF NFF DF SO DPT TM DSEn l3m
M: 0 0 0 0 0 0 0 0 0 0 0 0
V: 0 0 0 0 0 0 0 0 0 0 0 0
SrcPort DstPortIITypeCode TCPFlags TTL ISBM QosLabel ReQOS S_P2P D_P2P
M: 0000 0000 00 00 0000 00 0 0 0
V: 0000 0000 00 00 0000 00 0 0 0
SgEn SgLabel AuthBehaviorTag l2srcMiss l2dstMiss ipTtl SgaclDeny
M: 0 000000 0 0 0 0 0
V: 0 000000 0 0 0 0 0
NFCMD0 NFCMD1 SMPLR LKP1 LKP2 PID QOSPRI MQLBL MPLPRO LUT0PRI CPUCOPY
1 2 0 1 0 0 0 0 0 0x0000f 0
Start/Skip Word: 0x00000003
Start Feature, Terminate
-----------------------------------------
Printing entries for region INGRESS_NFL_ACL_VACL (311) type 6 asic 0
========================================================
Printing entries for region INGRESS_NFL_ACL_RACL (312) type 6 asic 0
========================================================
Printing entries for region INGRESS_NFL_ACL_SSID (313) type 6 asic 0
========================================================
Printing entries for region INGRESS_NFL_CATCHALL (314) type 6 asic 0
========================================================
TAQ-2 Index-224 (A:0,C:0) Valid StartF-1 StartA-1 SkipF-0 SkipA-0
Input IPv4 NFL RACL
Labels Port Vlan L3If Group
M: 0000 0000 0000 0000
V: 0000 0000 0000 0000
vcuResults l3Len l3Pro l3Tos SrcAddr DstAddr mtrid vrfid SH
M: 00000000 0000 00 00 00000000 00000000 00 0000 0000
V: 00000000 0000 00 00 00000000 00000000 00 0000 0000
RMAC RA MEn IPOPT MF NFF DF SO DPT TM DSEn l3m
M: 0 0 0 0 0 0 0 0 0 0 0 0
V: 0 0 0 0 0 0 0 0 0 0 0 0
SrcPort DstPortIITypeCode TCPFlags TTL ISBM QosLabel ReQOS S_P2P D_P2P
M: 0000 0000 00 00 0000 00 0 0 0
V: 0000 0000 00 00 0000 00 0 0 0
SgEn SgLabel AuthBehaviorTag l2srcMiss l2dstMiss ipTtl SgaclDeny
M: 0 000000 0 0 0 0 0
V: 0 000000 0 0 0 0 0
NFCMD0 NFCMD1 SMPLR LKP1 LKP2 PID QOSPRI MQLBL MPLPRO LUT0PRI CPUCOPY
0 0 0 0 0 0 0 0 0 0x00000 0
Start/Skip Word: 0x00000003
Start Feature, Terminate
-----------------------------------------
TAQ-2 Index-225 (A:0,C:0) Valid StartF-0 StartA-0 SkipF-0 SkipA-0
Input IPv4 NFL PACL
Labels Port Vlan L3If Group
M: 0000 0000 0000 0000
V: 0000 0000 0000 0000
vcuResults l3Len l3Pro l3Tos SrcAddr DstAddr mtrid vrfid SH
M: 00000000 0000 00 00 00000000 00000000 00 0000 0000
V: 00000000 0000 00 00 00000000 00000000 00 0000 0000
RMAC RA MEn IPOPT MF NFF DF SO DPT TM DSEn l3m
M: 0 0 0 0 0 0 0 0 0 0 0 0
V: 0 0 0 0 0 0 0 0 0 0 0 0
SrcPort DstPortIITypeCode TCPFlags TTL ISBM QosLabel ReQOS S_P2P D_P2P
M: 0000 0000 00 00 0000 00 0 0 0
V: 0000 0000 00 00 0000 00 0 0 0
SgEn SgLabel AuthBehaviorTag l2srcMiss l2dstMiss ipTtl SgaclDeny
M: 0 000000 0 0 0 0 0
V: 0 000000 0 0 0 0 0
NFCMD0 NFCMD1 SMPLR LKP1 LKP2 PID QOSPRI MQLBL MPLPRO LUT0PRI CPUCOPY
0 0 0 0 0 0 0 0 0 0x00000 0
Start/Skip Word: 0x00000000
No Start, Terminate
-----------------------------------------
TAQ-2 Index-226 (A:0,C:0) Valid StartF-0 StartA-0 SkipF-0 SkipA-0
Input IPv6 NFL PACL
Labels Port Vlan L3If Group
Mask 0x0000 0x0000 0x0000 0x0000
Value 0x0000 0x0000 0x0000 0x0000
vcuResult dstAddr0 dstAddr1 dstAddr2 dstAddr3 srcAddr0
00000000 00000000 00000000 00000000 00000000 00000000
00000000 00000000 00000000 00000000 00000000 00000000
srcAddr1 srcAddr2 srcAddr3 TC HL l3Len fLabel vrfId toUs
00000000 00000000 00000000 00 00 0000 00000 000 0
00000000 00000000 00000000 00 00 0000 00000 000 0
l3Pro mtrId AE FE RE HE MF NFF SO IPOPT RA MEn RMAC DPT TMP l3m
00 00 0 0 0 0 0 0 0 0 0 0 0 0 0 0
00 00 0 0 0 0 0 0 0 0 0 0 0 0 0 0
DSE srcPort dstPortIITypeCode tcpFlags IIPresent cZId dstZId
0 0000 0000 00 00 00 00
0 0000 0000 00 00 00 00
v6RT AH ESP mREn ReQOS QosLabel PRole VRole AuthBehaviorTag
M: 0 0 0 0 0 00 0 0 0
V: 0 0 0 0 0 00 0 0 0
SgEn SgLabel
M: 0 000000
V: 0 000000
NFCMD0 NFCMD1 SMPLR LKP1 LKP2 PID QOSPRI MQLBL MPLPRO LUT0PRI CPUCOPY
0 0 0 0 0 0 0 0 0 0x00000 0
Start/Skip Word: 0x00000000
No Start, Terminate
-----------------------------------------
TAQ-2 Index-228 (A:0,C:0) Valid StartF-0 StartA-0 SkipF-0 SkipA-0
conversion to string vmr l2p not supported
-----------------------------------------
TAQ-2 Index-230 (A:0,C:0) Valid StartF-0 StartA-0 SkipF-0 SkipA-0
Input MAC NFL PACL
Labels Port Vlan L3If Group
M: 0000 0000 0000 0000
V: 0000 0000 0000 0000
arpSrcHwAddr arpDestHwAddr arpSrcIpAddr arpTargetIp arpOperation
M: 000000000000 000000000000 00000000 00000000 0000
V: 000000000000 000000000000 00000000 00000000 0000
TRUST SNOOP SVALID DVALID
M: 0 0 0 0
V: 0 0 0 0
arpHardwareLength arpHardwareType arpProtocolLength arpProtocolType
M: 00000000 00000000 00000000 00000000
V: 00000000 00000000 00000000 00000000
VlanId l2Encap l2Protocol cosCFI srcMAC dstMAC ISBM QosLabel
M: 000 0 0000 0 000000000000 000000000000 00 00
V: 000 0 0000 0 000000000000 000000000000 00 00
ReQOS isSnap isLLC AuthBehaviorTag
M: 0 0 0 0
V: 0 0 0 0
NFCMD0 NFCMD1 SMPLR LKP1 LKP2 PID QOSPRI MQLBL MPLPRO LUT0PRI CPUCOPY
0 0 0 0 0 0 0 0 0 0x00000 0
Start/Skip Word: 0x00000000
No Start, Terminate
-----------------------------------------流量遮罩
運行命令 以檢視硬體中是否安裝了流掩碼。show platform software fed switch active|standby|member fnf fmask-entry asic 您也可以在這裡找到金鑰欄位清單的數量。
Switch#show platform software fed switch active fnf fmask-entry asic 1 entry 1 --------------------------------- mask0_valid : 1 Mask hdl0 : 1 Profile ID : 0 Feature 0 : 148 Fmsk0 RefCnt: 1 Mask M1 : [511:256] => :00000000 00000000 00000000 00000000 00000000 00000000 00000000 00000000 [255:000] => :FFFFFFFF 00000000 FFFFFFFF 03FF0000 00000000 00FF0000 00000000 C00000FF Mask M2 : Key Map : Source Field-Id Size NumPFields Pfields 002 090 04 01 (0 1 1 1) 002 091 04 01 (0 1 1 0) 002 000 01 01 (0 1 0 7) 000 056 08 01 (0 0 2 4) 001 011 11 04 (0 0 0 1) (0 0 0 0) (0 1 0 6) (0 0 2 0) 000 067 32 01 (0 1 12 0) 000 068 32 01 (0 1 12 2)
流量統計資料與時間戳記卸載資料
運行命令show platform software fed switch active fnf flow-record asic ,檢視netflow統計資訊以及時間戳。
Switch#show platform software fed switch active fnf flow-record asic 1 start-index 1 num-flows 1
1 flows starting at 1 for asic 1:-------------------------------------------------
Idx 996 :
{90, ALR_INGRESS_NET_FLOW_ACL_LOOKUP_TYPE1 = 0x01}
{91, ALR_INGRESS_NET_FLOW_ACL_LOOKUP_TYPE2 = 0x01}
{0, ALR_INGRESS_NFL_SPECIAL1 = 0x00}
{56, PHF_INGRESS_L3_PROTOCOL = 0x11}
{11 PAD-UNK = 0x0000}
{67, PHF_INGRESS_IPV4_DEST_ADDRESS = 0xc0a86464}
{68, PHF_INGRESS_IPV4_SRC_ADDRESS = 0xc0a8c864}
FirstSeen = 0x4b2f, LastSeen = 0x4c59, sysUptime = 0x4c9d
PKT Count = 0x000000000102d5df, L2ByteCount = 0x00000000ca371638
Switch#show platform software fed switch active fnf flow-record asic 1 start-index 1 num-flows 1
1 flows starting at 1 for asic 1:-------------------------------------------------
Idx 996 :
{90, ALR_INGRESS_NET_FLOW_ACL_LOOKUP_TYPE1 = 0x01}
{91, ALR_INGRESS_NET_FLOW_ACL_LOOKUP_TYPE2 = 0x01}
{0, ALR_INGRESS_NFL_SPECIAL1 = 0x00}
{56, PHF_INGRESS_L3_PROTOCOL = 0x11}
{11 PAD-UNK = 0x0000}
{67, PHF_INGRESS_IPV4_DEST_ADDRESS = 0xc0a86464}
{68, PHF_INGRESS_IPV4_SRC_ADDRESS = 0xc0a8c864}
FirstSeen = 0x4b2f, LastSeen = 0x4c5b, sysUptime = 0x4c9f
PKT Count = 0x0000000001050682, L2ByteCount = 0x00000000cbed1590Application Visibility and Control (AVC)
背景資訊
- Application Visibility and Control (AVC) 這項解決方案,利用網路型應用程式辨識版本 2 (NBAR2)、NetFlow V9 以及各種報告和管理工具 (Cisco Prime),透過深度封包檢測 (DPI) 將應用程式分類。
- AVC 可以設定在獨立交換器或者交換器堆疊的有線存取連接埠。
- AVC 也可以使用在思科無線控制器以識別以 DPI 為基礎的應用程式,然後使用特定 DSCP 值加以標記。它也可以收集各種無線效能指標,例如應用程式與用戶端的頻寬使用情況。
效能與規模
效能:每個交換器成員每秒都能處理 500 個連線,而且 CPU 使用率不到 50%。超過此使用率,則無法保證 AVC 服務。
擴充:每 24 個存取連接埠的處理能力,最高可達 5,000 個雙向流量(約為每個存取連接埠 200 個流量)。
有線 AVC 限制
- 您無法同時在相同介面上設定 AVC 與加密流量分析 (ETA)。
- 封包分類僅支援單點傳播 IPv4 (TCP/UDP) 流量。
- NBAR 型 QoS 原則組態僅支援有線的實體連接埠。這包含第 2 層存取與主幹連接埠和第 3 層路由連接埠。
- NBAR 型 QoS 原則組態不支援連接埠-通道成員、交換器虛擬介面 (SVI) 或子介面。
- NBAR2 型分類子 (match protocol),僅支援標記與管制的 QoS 動作。
- 匹配協定在所有策略中限製為255個不同的協定(8位硬體限制)。
附註:這不是所有限制的完整清單。有關您的平台和代碼版本,請參閱相應的AVC配置指南。
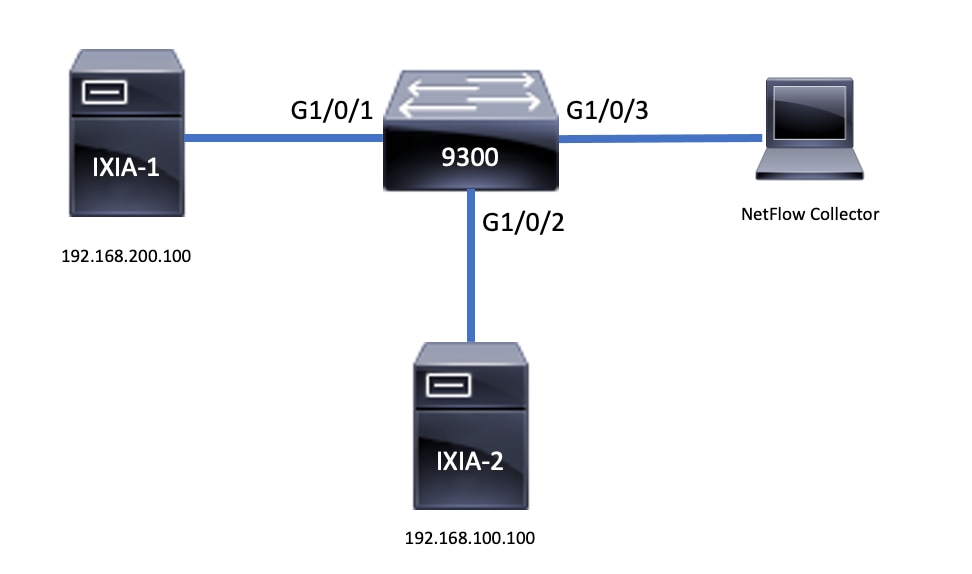
網路圖表
元件
AVC配置由構成解決方案的三個主要元件組成:
可視性:通訊協定探索
- 通訊協定探索透過 NBAR 來進行,可以按照介面、方向和應用程式提供位元組/封包的統計資料。
- 通過介面配置為特定介面啟用協定發現:
ip nbar protocol-discovery.
如輸出所示,如何啟用通訊協定探索:
Switch(config)#interface fi4/0/5
Switch(config-if)#ip nbar protocol-discovery
Switch(config-if)#exit
Switch#show run int fi4/0/5
Building configuration...
Current configuration : 70 bytes
!
interface FiveGigabitEthernet4/0/5
ip nbar protocol-discovery
end
控制:基於應用的QoS
相較於傳統 QoS 比對 IP 位址與 UDP/TCP 連接埠,AVC 透過應用程式型 QoS 實現更細膩的控制,可讓您比對應用程式,並透過 QoS 動作(如標記與管制)提供更精細的控制。
- 動作會在彙總流量(非各流量)上執行。
- 施行應用程式型 QoS 時需建立類別對應、進行通訊協定配對,然後建立原則對應。
- 應用程式型 QoS 原則會附加至介面。
如輸出所示,應用程式型 QoS 的組態範例:
Switch(config)#class-map WEBEX
Switch(config-cmap)#match protocol webex-media
Switch(config)#end
Switch(config)#policy-map WEBEX
Switch(config-pmap)#class WEBEX
Switch(config-pmap-c)#set dscp af41
Switch(config)#end
Switch(config)#interface fi4/0/5
Switch(config-if)#service-policy input WEBEX
Switch(config)#end
Switch#show run int fi4/0/5
Building configuration...
Current configuration : 98 bytes
!
interface FiveGigabitEthernet4/0/5
service-policy input WEBEX
ip nbar protocol-discovery
end
應用程式型 Flexible NetFlow
有線AVC FNF支援兩種預定義流記錄:舊式雙向流記錄和新的方向流記錄。
雙向流量記錄會追蹤用戶端/伺服器應用程式的統計資料。
如輸出所示,雙向流量記錄的組態範例:
Switch(config)#flow record BIDIR-1
Switch(config-flow-record)#match ipv4 version
Switch(config-flow-record)#match ipv4 protocol
Switch(config-flow-record)#match application name
Switch(config-flow-record)#match connection client ipv4 address
Switch(config-flow-record)#match connection server ipv4 address
Switch(config-flow-record)#match connection server transport port
Switch(config-flow-record)#match flow observation point
Switch(config-flow-record)#collect flow direction
Switch(config-flow-record)#collect connection initiator
Switch(config-flow-record)#collect connection new-connections
Switch(config-flow-record)#collect connection client counter packets long
Switch(config-flow-record)#connection client counter bytes network long
Switch(config-flow-record)#collect connection server counter packets long
Switch(config-flow-record)#connection server counter bytes network long
Switch(config-flow-record)#collect timestamp absolute first
Switch(config-flow-record)#collect timestamp absolute last
Switch(config-flow-record)#end
Switch#show flow record BIDIR-1
flow record BIDIR-1:
Description: User defined
No. of users: 0
Total field space: 78 bytes
Fields:
match ipv4 version
match ipv4 protocol
match application name
match connection client ipv4 address
match connection server ipv4 address
match connection server transport port
match flow observation point
collect flow direction
collect timestamp absolute first
collect timestamp absolute last
collect connection initiator
collect connection new-connections
collect connection server counter packets long
collect connection client counter packets long
collect connection server counter bytes network long
collect connection client counter bytes network long
方向性記錄是輸入/輸出的應用程式統計資料。
如輸出所示,輸入與輸出方向性記錄的組態範例:
註:命令 指定與輸入介面匹配。match interface input命令 指定與輸出介面匹配。match interface output命令 對於AVC支援是必需的。match application name
Switch(config)#flow record APP-IN
Switch(config-flow-record)#match ipv4 version
Switch(config-flow-record)#match ipv4 protocol
Switch(config-flow-record)#match ipv4 source address
Switch(config-flow-record)#match ipv4 destination address
Switch(config-flow-record)#match transport source-port
Switch(config-flow-record)#match transport destination-port
Switch(config-flow-record)#match interface input
Switch(config-flow-record)#match application name
Switch(config-flow-record)#collect interface output
Switch(config-flow-record)#collect counter bytes long
Switch(config-flow-record)#collect counter packets long
Switch(config-flow-record)#collect timestamp absolute first
Switch(config-flow-record)#collect timestamp absolute last
Switch(config-flow-record)#end
Switch#show flow record APP-IN
flow record APP-IN:
Description: User defined
No. of users: 0
Total field space: 58 bytes
Fields:
match ipv4 version
match ipv4 protocol
match ipv4 source address
match ipv4 destination address
match transport source-port
match transport destination-port
match interface input
match application name
collect interface output
collect counter bytes long
collect counter packets long
collect timestamp absolute first
collect timestamp absolute last
Switch(config)#flow record APP-OUT
Switch(config-flow-record)#match ipv4 version
Switch(config-flow-record)#match ipv4 protocol
Switch(config-flow-record)#match ipv4 source address
Switch(config-flow-record)#match ipv4 destination address
Switch(config-flow-record)#match transport source-port
Switch(config-flow-record)#match transport destination-port
Switch(config-flow-record)#match interface output
Switch(config-flow-record)#match application name
Switch(config-flow-record)#collect interface input
Switch(config-flow-record)#collect counter bytes long
Switch(config-flow-record)#collect counter packets long
Switch(config-flow-record)#collect timestamp absolute first
Switch(config-flow-record)#collect timestamp absolute last
Switch(config-flow-record)#end
Switch#show flow record APP-OUT
flow record APP-OUT:
Description: User defined
No. of users: 0
Total field space: 58 bytes
Fields:
match ipv4 version
match ipv4 protocol
match ipv4 source address
match ipv4 destination address
match transport source-port
match transport destination-port
match interface output
match application name
collect interface input
collect counter bytes long
collect counter packets long
collect timestamp absolute first
collect timestamp absolute last
流量匯出器
建立流量匯出器以定義匯出參數。
如輸出所示,流量匯出器的組態範例:
Switch(config)#flow exporter AVC
Switch(config-flow-exporter)#destination 192.168.69.2
Switch(config-flow-exporter)#source vlan69
Switch(config-flow-exporter)#end
Switch#show run flow exporter AVC
Current configuration:
!
flow exporter AVC
destination 192.168.69.2
source Vlan69
!
流量監視器
建立流量監視器以建立其與流量記錄的關聯。
如輸出所示,流量監視器的組態範例:
Switch(config)#flow monitor AVC-MONITOR
Switch(config-flow-monitor)#record APP-OUT
Switch(config-flow-monitor)#exporter AVC
Switch(config-flow-monitor)#end
Switch#show run flow monitor AVC-MONITOR
Current configuration:
!
flow monitor AVC-MONITOR
exporter AVC
record APP-OUT
建立流量監視器與介面的關聯
您最多可以將具有不同預先定義記錄的兩個不同 AVC 監視器,同時附加至一個介面。
如輸出所示,流量監視器的組態範例:
Switch(config)#interface fi4/0/5
Switch(config-if)#ip flow monitor AVC-MONITOR out
Switch(config-if)#end
Switch#show run interface fi4/0/5
Building configuration...
Current configuration : 134 bytes
!
interface FiveGigabitEthernet4/0/5
ip flow monitor AVC-MONITOR output
service-policy input WEBEX
ip nbar protocol-discovery
end
NBAR2
NBAR2 動態無中斷通訊協定套件升級
協定包是更新裝置上NBAR2協定支援的軟體套件,無需更換裝置上的Cisco軟體。協定包包含由NBAR2正式支援的應用程式的資訊,這些應用程式經過編譯和打包在一起。對於每個應用程式,協定包都包含有關應用程式簽名和應用程式屬性的資訊。每個軟體版本皆已內建與其搭配的通訊協定套件。
- NBAR2 提供的方法可直接更新通訊協定封包,不必使用流量也不會造成服務中斷,且無須修改裝置上的軟體映像。
- NBAR2 protocol-packets可從思科軟體中心下載,地址為:NBAR2 Protocol Pack Library。
NBAR2 通訊協定套件升級
在安裝新的通訊協定套件之前,您必須先將通訊協定封包複製到所有交換器上的快閃記憶體。 若要載入新的通訊協定套件,請使用命令 。ip nbar protocol-pack flash:
您無須重新載入交換器,即可升級 NBAR2。
如輸出所示,載入 NBAR2 通訊協定套件的組態範例:
Switch(config)#ip nbar protocol-pack flash:newProtocolPack
要恢復為內建協定包,請使用命令 。default ip nbar protocol-pack
如輸出所示,回復為內建通訊協定套件的組態範例:
Switch(config)#default ip nbar protocol-pack顯示 NBAR2 通訊協定套件資訊
若要顯示通訊協定套件資訊,請使用下列命令:
show ip nbar versionshow ip nbar protocol-pack active detail
如輸出所示,這類命令的輸出範例:
Switch#show ip nbar version
NBAR software version: 37
NBAR minimum backward compatible version: 37
NBAR change ID: 293126
Loaded Protocol Pack(s):
Name: Advanced Protocol Pack
Version: 43.0
Publisher: Cisco Systems Inc.
NBAR Engine Version: 37
State: Active
Switch#show ip nbar protocol-pack active detail
Active Protocol Pack:
Name: Advanced Protocol Pack
Version: 43.0
Publisher: Cisco Systems Inc.
NBAR Engine Version: 37
State: Active
NBAR2 自訂應用程式
NBAR2 支援使用自訂通訊協定來識別自訂應用程式。自訂通訊協定支援 NBAR2 目前不支援的通訊協定與應用程式。
這些通訊協定與應用程式包含以下項目:
- 組織的特定應用程式
- 某地理位置限定的應用程式
NBAR2提供了一種通過命令手動自定義應用程式的方法ip nbar custom 。
附註:自定義應用優先於內建協定
有各種類型的應用程式自訂項目:
一般通訊協定自訂
- HTTP
- SSL
- DNS
複合:基於多個協定 — server-name進行自定義。
第 3 層/第 4 層自訂
-
IPv4 位址
-
DSCP 值
-
TCP/UDP 連接埠
-
流量來源或目的地方向
位元組偏移:根據裝載中特定位元組值進行自訂
HTTP 自訂
HTTP 自訂能以下列 HTTP 欄位組合為基礎:
-
cookie - HTTP Cookie
-
host - 包含資源的來源伺服器主機名稱
-
method - HTTP 方法
-
referrer - 取得資源請求的位址
-
url - 統一資源定位器路徑
-
user-agent - 傳送請求的代理程式所使用的軟體
-
version - HTTP 版本
-
via - HTTP via 欄位
範例自訂應用程式名稱為 MYHTTP,使用 HTTP 主機 *mydomain.com 搭配選擇器 ID 10。
Switch(config)#ip nbar custom MYHTTP http host *mydomain.com id 10
SSL 自訂
可以透過從 SSL 伺服器名稱指示 (SNI) 或通用名稱 (CN) 擷取的資訊,針對 SSL 加密流量進行自訂。
範例自訂應用程式名稱為 MYSSL,使用 SSL 唯一名稱 mydomain.com 搭配選擇器 ID 11。
Switch(config)#ip nbar custom MYSSL ssl unique-name *mydomain.com id 11
DNS 自訂
NBAR2 會檢查 DNS 請求與回應流量,並且可以建立 DNS 回應與應用程式的關聯。從 DNS 回應傳回的 IP 位址會經過快取,並用於之後與該特定應用程式相關聯的封包流量。
命令 用於DNS自定義。ip nbar customapplication-namedns domain-nameidapplication-id 若要延伸應用程式,請使用命令 。ip nbar custom application-name dns domain-name domain-name extends existing-application
名為MYDNS的自定義應用程式示例,該應用程式使用具有選擇器ID 12的DNS域名mydomain.com。
Switch(config)#ip nbar custom MYDNS dns domain-name *mydomain.com id 12
複合自訂
NBAR2 提供的方法,可以根據顯示在 HTTP、SSL 或 DNS 中的網域名稱來自訂應用程式。
範例自訂應用程式名稱為 MYDOMAIN,使用 HTTP、SSL 或 DNS 網域名稱 mydomain.com 搭配選擇器 ID 13。
L3/L4 自訂
第 3 層/第 4 層自訂以封包元組為基礎,並且一律與流量的第一個封包配對。
範例自訂應用程式 LAYER4CUSTOM 與 IP 位址 10.56.1.10 和 10.56.1.11、TCP 以及 DSCP ef 相符,搭配選擇器 ID 14。
Switch(config)#ip nbar custom LAYER4CUSTOM transport tcp id 14
Switch(config-custom)#ip address 10.56.1.10 10.56.1.11
Switch(config-custom)#dscp ef
Switch(config-custom)#end
監視自訂應用程式
要監控自定義應用程式,請使用下面列出的show命令:
show ip nbar protocol-id | inc自定義
Switch#show ip nbar protocol-id | inc Custom
LAYER4CUSTOM 14 Custom
MYDNS 12 Custom
MYDOMAIN 13 Custom
MYHTTP 10 Custom
MYSSL 11 Custom
show ip nbar protocol-id CUSTOM_APP
Switch#show ip nbar protocol-id MYSSL Protocol Name id type ---------------------------------------------- MYSSL 11 Custom
驗證 AVC
驗證AVC功能需要多個步驟。本節提供命令和示例輸出。
要驗證NBAR是否處於活動狀態,您可以運行命令 control-plane。show ip nbar
重要領域:
- 在正確的情況下必須啟用NBAR狀態。
- NBAR配置狀態必須在正確的場景中就緒。
Switch#show ip nbar control-plane
NGCP Status:
============
graph sender info:
NBAR state is ACTIVATED
NBAR config send mode is ASYNC
NBAR config state is READY
NBAR update ID 3
NBAR batch ID ACK 3
NBAR last batch ID ACK clients 1 (ID: 4)
Active clients 1 (ID: 4)
NBAR max protocol ID ever 1935
NBAR Control-Plane Version: 37
<snip>
使用 命令驗證每個交換機成員是否都有一個活動資料平面:show platform software fed switch active|standby|member wdavc function wdavc_stile_cp_show_info_ui
在正確的情況下,DP啟用必須為TRUE。
Switch#show platform software fed switch active wdavc function wdavc_stile_cp_show_info_ui
Is DP activated : TRUE
MSG ID : 3
Maximum number of flows: 262144
Current number of graphs: 1
Requests queue state : WDAVC_STILE_REQ_QUEUE_STATE_UP
Number of requests in queue : 0
Max number of requests in queue (TBD): 1
Counters:
activate_msgs_rcvd : 1
graph_download_begin_msgs_rcvd : 3
stile_config_msgs_rcvd : 1584
graph_download_end_msgs_rcvd : 3
deactivate_msgs_rcvd : 0
intf_proto_disc_msgs_rcvd : 1
intf_attach_msgs_rcvd : 2
cfg_response_msgs_sent : 1593
num_of_handle_msg_from_fmanfp_events : 1594
num_of_handle_request_from_queue : 1594
num_of_handle_process_requests_events : 1594
使用命令 顯示關鍵資訊:show platform software fed switch active|standby|member wdavc flows
Switch#show platform software fed switch active wdavc flows
CurrFlows=1, Watermark=1
IX |IP1 |IP2 |PORT1|PORT2|L3 |L4 |VRF |TIMEOUT|APP |TUPLE|FLOW |IS FIF |BYPASS|FINAL |#PKTS |BYPASS
| | | | |PROTO|PROTO|VLAN|SEC |NAME |TYPE |TYPE |SWAPPED | | | |PKT
--------------------------------------------------------------------------------------
1 |192.168.100.2 |192.168.200.2 |68 |67 |1 |17 |0 |360 |unknown |Full |Real Flow|Yes |True |True |40 |40
主要欄位:
CurrFlows:展示AVC跟蹤的活動流數量。
水印:展示AVC歷史上跟蹤的最大流量數。
超時秒:不活動超時取決於標識的應用程式。
應用程式名稱:確定的應用程式
流型別:Real Flow表示此資料是因入站資料而建立的。Pre Flow 表示這是因為傳入資料而建立的流量。預先流量用於預期的媒體流量.
元組型別:實際流量始終為整元組。預流為完整元組或半元組。
旁路:如果設定為TRUE,則表示軟體不需要更多資料包來標識此流。
最終版:如果設定為TRUE,則表示此流不再更改應用程式。
繞過PKT:達到最終分類需要多少資料包。
#PKTS:有多少資料包實際被轉發到軟體中用於此流。
檢視有關當前流的其他詳細資訊。您可以使用該命show platform software fed switch active wdavc function wdavc_ft_show_all_flows_seg_ui令。
Switch#show platform software fed switch active wdavc function wdavc_ft_show_all_flows_seg_ui
CurrFlows=1, Watermark=1
IX |IP1 |IP2 |PORT1|PORT2|L3 |L4 |VRF |TIMEOUT|APP |TUPLE |FLOW |IS FIF |BYPASS|FINAL |#PKTS |BYPASS
| | | | |PROTO|PROTO|VLAN|SEC |NAME |TYPE |TYPE |SWAPPED | | | |PKT
---------------------------------------------------------------------------------------------------------------------------------------------------------------------
1 |192.168.100.2 |192.168.200.2|68 |67 |1 |17 |0 |360 |unknown |Full |Real Flow|Yes |True |True |40 |40
SEG IDX |I/F ID |OPST I/F |SEG DIR |FIF DIR |Is SET |DOP ID |NFL HDL |BPS PND |APP PND |FRST TS |LAST TS |BYTES |PKTS |TCP FLGS
------------------------------------------------------------------------------------------------------------------------------------
0 |9 |---- |Ingress |True |True |0 |50331823 |0 |0 |177403000|191422000|24252524|70094 |0
主要欄位
I/F ID:指定介面ID。
SEG DIR:指定輸出方向的輸入。
FIF DIR:確定是否這是流發起程式方向。
NFL HDL:硬體中的流ID。
要檢視硬體中的條目,請運行命令show platform software fed switch active fnf flow-record asic 。
附註:要選擇ASIC,它是埠對映到的ASIC例項。要標識ASIC,請使用命令對映。如果對特定流不感興趣show platform software fed switch active|standby|member ifm,可將啟動索引設定為0。否則,必須指定起始索引。如果是 num-flows,會指定可以檢視的流量數量,上限為 10。
Switch#show platform software fed switch active fnf flow-record asic 3 start-index 0 num-flows 1
1 flows starting at 0 for asic 3:-------------------------------------------------
Idx 175 :
{90, ALR_INGRESS_NET_FLOW_ACL_LOOKUP_TYPE1 = 0x01}
{91, ALR_INGRESS_NET_FLOW_ACL_LOOKUP_TYPE2 = 0x01}
{0, ALR_INGRESS_NFL_SPECIAL1 = 0x00}
{11 PAD-UNK = 0x0000}
{94, PHF_INGRESS_DEST_PORT_OR_ICMP_OR_IGMP_OR_PIM_FIRST16B = 0x0043}
{93, PHF_INGRESS_SRC_PORT = 0x0044}
{67, PHF_INGRESS_IPV4_DEST_ADDRESS = 0xc0a8c802}
{68, PHF_INGRESS_IPV4_SRC_ADDRESS = 0xc0a86402}
{56, PHF_INGRESS_L3_PROTOCOL = 0x11}
FirstSeen = 0x2b4fb, LastSeen = 0x2eede, sysUptime = 0x2ef1c
PKT Count = 0x000000000001216f, L2ByteCount = 0x0000000001873006
查看資料路徑中的各種錯誤與警告
使用命令 檢視可能的流表錯誤:show platform software fed switch active|standby|member wdavc function wdavc_ft_show_stats_ui | inc err|warn|fail
Switch#show platform software fed switch active wdavc function wdavc_ft_show_stats_ui | inc err|warn|fail
Bucket linked exceed max error : 0
extract_tuple_non_first_fragment_warn : 0
ft_client_err_alloc_fail : 0
ft_client_err_detach_fail : 0
ft_client_err_detach_fail_intf_attach : 0
ft_inst_nfl_clock_sync_err : 0
ft_ager_err_invalid_timeout : 0
ft_intf_err_alloc_fail : 0
ft_intf_err_detach_fail : 0
ft_inst_err_unreg_client_all : 0
ft_inst_err_inst_del_fail : 0
ft_flow_seg_sync_nfl_resp_pend_del_warn : 0
ager_sm_cb_bad_status_err : 0
ager_sm_cb_received_err : 0
ft_ager_to_time_no_mask_err : 0
ft_ager_to_time_latest_zero_ts_warn : 0
ft_ager_to_time_seg_zero_ts_warn : 0
ft_ager_to_time_ts_bigger_curr_warn : 0
ft_ager_to_ad_nfl_resp_error : 0
ft_ager_to_ad_req_all_recv_error : 0
ft_ager_to_ad_req_error : 0
ft_ager_to_ad_resp_error : 0
ft_ager_to_ad_req_restart_timer_due_err : 0
ft_ager_to_flow_del_nfl_resp_error : 0
ft_ager_to_flow_del_all_recv_error : 0
ft_ager_to_flow_del_req_error : 0
ft_ager_to_flow_del_resp_error : 0
ft_consumer_timer_start_error : 0
ft_consumer_tw_stop_error : 0
ft_consumer_memory_error : 0
ft_consumer_ad_resp_error : 0
ft_consumer_ad_resp_fc_error : 0
ft_consumer_cb_err : 0
ft_consumer_ad_resp_zero_ts_warn : 0
ft_consumer_ad_resp_zero_pkts_bytes_warn : 0
ft_consumer_remove_on_count_zero_err : 0
ft_ext_field_ref_cnt_zero_warn : 0
ft_ext_gen_ref_cnt_zero_warn : 0
使用命令 查看任何可能的NBAR錯誤:show platform software fed switch active wdavc function wdavc_stile_stats_show_ui | inc err
Switch#show platform software fed switch active wdavc function wdavc_stile_stats_show_ui | inc err
find_flow_error : 0
add_flow_error : 0
remove_flow_error : 0
detach_fo_error : 0
is_forward_direction_error : 0
set_flow_aging_error : 0
ft_process_packet_error : 0
sys_meminfo_get_error : 0
確認封包已複製到 CPU
使用命令 驗證是否已將資料包克隆到CPU進行NBAR處理:show platform software fed switch active punt cpuq 21 | inc received
附註:在實驗室中,此數字沒有增加。
Switch#show platform software fed switch active punt cpuq 21 | inc received
Packets received from ASIC : 63
找出 CPU 擁塞
在擁塞時,資料包可以在傳送到WDAVC進程之前被丟棄。使用命令 進行驗證:show platform software fed switch active wdavc function fed_wdavc_show_ots_stats_ui
Switch#show platform software fed switch active wdavc function fed_wdavc_show_ots_stats_ui
OTS Limits
----------------------------------------------
ots_queue_max : 20000
emer_bypass_ots_queue_stress : 4000
emer_bypass_ots_queue_normal : 200
OTS Statistics
----------------------------------------------
total_requests : 40
total_non_wdavc_requests : 0
request_empty_field_data_error : 0
request_invalid_di_error : 0
request_buf_coalesce_error : 0
request_invalid_format_error : 0
request_ip_version_error : 0
request_empty_packet_error : 0
memory_allocation_error : 0
emergency_bypass_requests_warn : 0
dropped_requests : 0
enqueued_requests : 40
max_ots_queue : 0
提示:要清除點投計數器資訊,請使用命令show platform software fed switch active wdavc function fed_wdavc_clear_ots_stats_ui。
找出規模問題
如果硬體中沒有可用的FNF條目,則流量不屬於NBAR2分類。使用命令 確認:show platform software fed switch active fnf sw-table-sizes asic
附註:建立的流特定於交換機和asic核心。需要相應地指定交換器編號(主用、備用等)。輸入的ASIC編號與對應的介面繫結,使用 來確定與介面對應的ASIC。show platform software fed switch active|standby|member ifm mappings若為影子選項,一律使用 0。
Switch#show platform software fed switch active fnf sw-table-sizes asic 3 shadow 0
---------------------------------
Global Bank Allocation
---------------------------------
Ingress Banks : Bank 0
Egress Banks : Bank 1
---------------------------------
Global flow table Info
INGRESS usedBankEntry 1 usedOvfTcamEntry 0
EGRESS usedBankEntry 0 usedOvfTcamEntry 0 <-- 256 means TCAM entries are full
---------------------------------
Flows Statistics
INGRESS TotalSeen=1 MaxEntries=1 MaxOverflow=0
EGRESS TotalSeen=0 MaxEntries=0 MaxOverflow=0
---------------------------------
Partition Table
---------------------------------
## Dir Limit CurrFlowCount OverFlowCount MonitoringEnabled
0 ING 0 0 0 0
1 ING 16640 1 0 1
2 ING 0 0 0 0
3 ING 16640 0 0 0
4 ING 0 0 0 0
5 ING 8192 0 0 1
6 ING 0 0 0 0
7 ING 0 0 0 0
8 ING 0 0 0 0
9 ING 0 0 0 0
10 ING 0 0 0 0
11 ING 0 0 0 0
12 ING 0 0 0 0
13 ING 0 0 0 0
14 ING 0 0 0 0
15 ING 0 0 0 0
0 EGR 0 0 0 0
1 EGR 16640 0 0 1
2 EGR 0 0 0 0
3 EGR 16640 0 0 0
4 EGR 0 0 0 0
5 EGR 8192 0 0 1
6 EGR 0 0 0 0
7 EGR 0 0 0 0
8 EGR 0 0 0 0
9 EGR 0 0 0 0
10 EGR 0 0 0 0
11 EGR 0 0 0 0
12 EGR 0 0 0 0
13 EGR 0 0 0 0
14 EGR 0 0 0 0
15 EGR 0 0 0 0
加密流量分析 (ETA)
背景資訊
- ETA 著重於識別加密流量中的惡意軟體通訊,方法是透過被動監視、擷取相關資料元素,以及結合行為建模和具有雲端全域安全性的機器學習。
- ETA 運用 NetFlow 的遙測以及加密惡意軟體偵測與加密合規性,並將此資料傳送至 Cisco Stealthwatch。
- ETA提取兩個主要的資料元素:初始資料包(IDP)和資料包長度和時間序列(SPLT)。
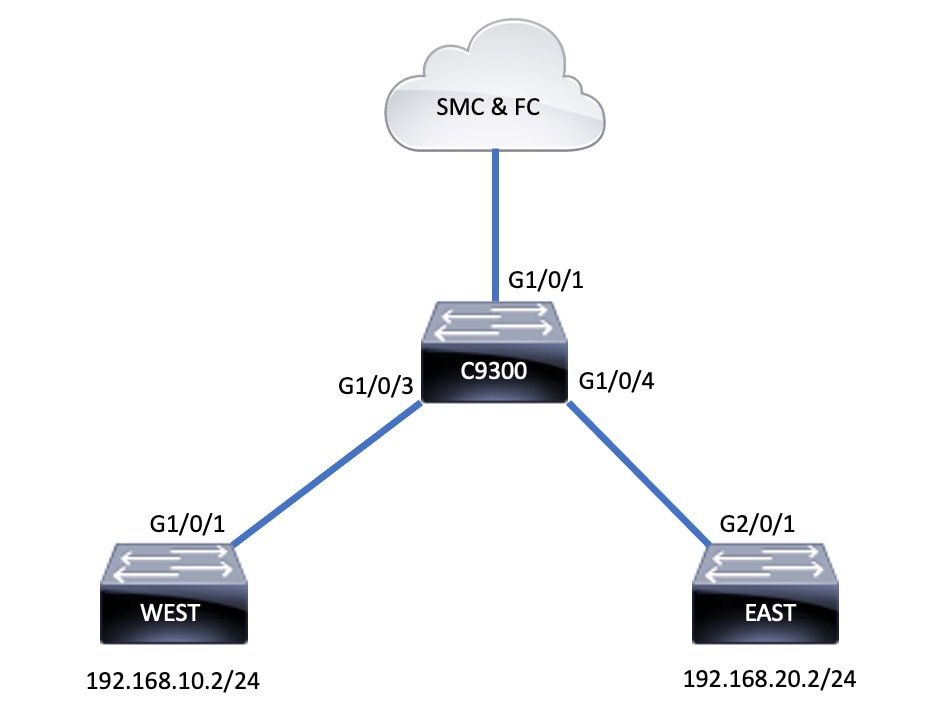
網路圖表
元件
ETA 包含在建立 ETA 解決方案時,搭配使用的數種不同元件:
- NetFlow – 定義網路裝置匯出的資料元素的標準,用以描述網路上的流量。
- Cisco Stealthwatch – 運用包含 NetFlow、IPFIX、Proxy 記錄與原始封包的深度封包檢測在內的網路遙測的強大功能,以提供進階網路能見度、資安情報與分析資料。
- Cisco Cognitive Intelligence – 找出略過安全控制項或透過無人監視的管道進入,並在組織環境內的惡意活動。
- 加密流量分析 – Cisco IOS XE 功能,使用進階行為式演算法,以透過加密流量的 Intraflow 中繼資料分析找出惡意流量模式,偵測隱藏在加密流量中的潛在威脅。
附註:本文此部分僅重點介紹在Catalyst 9000系列交換機上配置和驗證ETA和NetFlow,但不涵蓋部署到Cognitive Intelligence Cloud的Stealthwatch管理控制檯(SMC)和流量收集器(FC)。
限制
- 部署ETA需要思科DNA優勢發揮作用
- 同一介面上不支援 ETA 與傳輸 (TX) 交換連接埠分析器 (SPAN)。
這並非完整的清單,請參閱適當的組態指南,瞭解交換器與代碼版本的所有限制。
組態
如輸出所示,在交換器上全域啟用 ETA 並定義流量匯出目的地:
C9300(config)#et-analytics
C9300(config-et-analytics)#ip flow-export destination 172.16.18.1 2055
提示:必須使用埠2055,不要使用其他埠號。
接著,請按照輸出所示方式設定 Flexible NetFlow:
設定流量記錄
C9300(config)#flow record FNF-RECORD
C9300(config-flow-record)#match ipv4 protocol
C9300(config-flow-record)#match ipv4 source address
C9300(config-flow-record)#match ipv4 destination address
C9300(config-flow-record)#match transport source-port
C9300(config-flow-record)#match transport destination-port
C9300(config-flow-record)#collect counter bytes long
C9300(config-flow-record)#collect counter packets long
C9300(config-flow-record)#collect timestamp absolute first
C9300(config-flow-record)#collect timestamp absolute last
設定流量監視器
C9300(config)#flow exporter FNF-EXPORTER
C9300(config-flow-exporter)#destination 172.16.18.1
C9300(config-flow-exporter)#transport udp 2055
C9300(config-flow-exporter)#template data timeout 30
C9300(config-flow-exporter)#option interface-table
C9300(config-flow-exporter)#option application-table timeout 10
C9300(config-flow-exporter)#exit
設定流量記錄
C9300(config)#flow monitor FNF-MONITOR
C9300(config-flow-monitor)#exporter FNF-EXPORTER
C9300(config-flow-monitor)#record FNF-RECORD
C9300(config-flow-monitor)#end
套用流量監視器
C9300(config)#int range g1/0/3-4
C9300(config-if-range)#ip flow mon FNF-MONITOR in
C9300(config-if-range)#ip flow mon FNF-MONITOR out
C9300(config-if-range)#end
在交換器介面上啟用 ETA
C9300(config)#interface range g1/0/3-4
C9300(config-if-range)#et-analytics enable
驗證
確認 ETA 監視器 (eta-mon) 為作用中。確認是否透過命令 分配了狀態。show flow monitor eta-mon
C9300#show flow monitor eta-mon
Flow Monitor eta-mon:
Description: User defined
Flow Record: eta-rec
Flow Exporter: eta-exp
Cache:
Type: normal (Platform cache)
Status: allocated
Size: 10000 entries
Inactive Timeout: 15 secs
Active Timeout: 1800 secs
確認 ETA 快取已經填入。當在同一介面上配置NetFlow和ETA時,請利用 而不是 ,因為 的輸出為空:show flow monitor show flow monitor eta-mon cache show flow monitor eta-mon cache
C9300#show flow monitor FNF-MONITOR cache
Cache type: Normal (Platform cache)
Cache size: 10000
Current entries: 4
Flows added: 8
Flows aged: 4
- Inactive timeout ( 15 secs) 4
IPV4 SOURCE ADDRESS: 192.168.10.2
IPV4 DESTINATION ADDRESS: 192.168.20.2
TRNS SOURCE PORT: 0
TRNS DESTINATION PORT: 0
IP PROTOCOL: 1
counter bytes long: 500
counter packets long: 5
timestamp abs first: 21:53:23.390
timestamp abs last: 21:53:23.390
IPV4 SOURCE ADDRESS: 192.168.20.2
IPV4 DESTINATION ADDRESS: 192.168.10.2
TRNS SOURCE PORT: 0
TRNS DESTINATION PORT: 0
IP PROTOCOL: 1
counter bytes long: 500
counter packets long: 5
timestamp abs first: 21:53:23.390
timestamp abs last: 21:53:23.390
IPV4 SOURCE ADDRESS: 192.168.20.2
IPV4 DESTINATION ADDRESS: 192.168.10.2
TRNS SOURCE PORT: 0
TRNS DESTINATION PORT: 0
IP PROTOCOL: 1
counter bytes long: 500
counter packets long: 5
timestamp abs first: 21:53:23.390
timestamp abs last: 21:53:23.390
IPV4 SOURCE ADDRESS: 192.168.10.2
IPV4 DESTINATION ADDRESS: 192.168.20.2
TRNS SOURCE PORT: 0
TRNS DESTINATION PORT: 0
IP PROTOCOL: 1
counter bytes long: 500
counter packets long: 5
timestamp abs first: 21:53:23.390
timestamp abs last: 21:53:23.390
使用 命令驗證流是否導出到SMC和FC。show flow exporter eta-exp statistics
C9300#show flow exporter eta-exp statistics
Flow Exporter eta-exp:
Packet send statistics (last cleared 03:05:32 ago):
Successfully sent: 3 (3266 bytes)
Client send statistics:
Client: Flow Monitor eta-mon
Records added: 4
- sent: 4
Bytes added: 3266
- sent: 3266
確認 SPLT 與 IDP 已透過命令 匯出至 FC。show platform software fed switch active fnf et-analytics-flows
C9300#show platform software fed switch active fnf et-analytics-flows
ET Analytics Flow dump
=================
Total packets received : 20
Excess packets received : 0
Excess syn received : 0
Total eta records added : 4
Current eta records : 0
Total eta splt exported : 2
Total eta IDP exported : 2
使用 命令驗證為et-analytics配置的介面。show platform software et-analytics interfaces
C9300#show platform software et-analytics interfaces
ET-Analytics interfaces
GigabitEthernet1/0/3
GigabitEthernet1/0/4
ET-Analytics VLANs
使用命令 查看ETA的全局狀態:show platform software et-analytics global
C9300#show plat soft et-analytics global
ET-Analytics Global state
=========================
All Interfaces : Off
IP Flow-record Destination : 10.31.126.233 : 2055
Inactive timer : 15
ET-Analytics interfaces
GigabitEthernet1/0/3
GigabitEthernet1/0/4
ET-Analytics VLANs
修訂記錄
| 修訂 | 發佈日期 | 意見 |
|---|---|---|
3.0 |
13-Nov-2025
|
已更新格式以符合思科指南。 |
2.0 |
19-Dec-2023
|
重新認證 |
1.0 |
07-Oct-2022
|
初始版本 |
 意見
意見