將安全防火牆ASA調配到CSM
下載選項
無偏見用語
本產品的文件集力求使用無偏見用語。針對本文件集的目的,無偏見係定義為未根據年齡、身心障礙、性別、種族身分、民族身分、性別傾向、社會經濟地位及交織性表示歧視的用語。由於本產品軟體使用者介面中硬式編碼的語言、根據 RFP 文件使用的語言,或引用第三方產品的語言,因此本文件中可能會出現例外狀況。深入瞭解思科如何使用包容性用語。
關於此翻譯
思科已使用電腦和人工技術翻譯本文件,讓全世界的使用者能夠以自己的語言理解支援內容。請注意,即使是最佳機器翻譯,也不如專業譯者翻譯的內容準確。Cisco Systems, Inc. 對這些翻譯的準確度概不負責,並建議一律查看原始英文文件(提供連結)。
簡介
本檔案介紹將安全防火牆調適型安全裝置(ASA)設定為思科安全管理員(CSM)的過程。
必要條件
需求
思科建議您瞭解以下主題:
- 安全防火牆ASA
- CSM
採用元件
本文中的資訊係根據以下軟體和硬體版本:
- 安全防火牆ASA版本9.18.3
- CSM版本4.28
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路運作中,請確保您瞭解任何指令可能造成的影響。
背景資訊
CSM有助於實現一致的策略實施和安全事件快速故障排除,從而提供整個安全部署的總結報告。藉助其集中式介面,組織可以高效擴展和管理各種思科安全裝置,並提高可視性。
設定
在下一個示例中,虛擬ASA調配到CSM以進行集中管理。
組態
為HTTPS管理配置ASA
步驟1.建立具有所有許可權的使用者。
命令列(CLI)語法:
configure terminal
username < user string > password < password > privilege < level number >這會轉換為下一個命令示例,該示例具有使用者csm-user和口令cisco123,如下所示:
ciscoasa# configure terminal
ciscoasa(config)# username csm-user password cisco123 privilege 15
提示:對於此整合,也接受外部身份驗證使用者。
步驟2.啟用HTTP伺服器。
命令列(CLI)語法:
configure terminal
http server enable步驟3.允許對CSM伺服器IP地址進行HTTPS訪問。
命令列(CLI)語法:
configure terminal
http < hostname > < netmask > < interface name >這轉換為下一個命令示例,該示例允許任何網路通過外部介面(GigabitEthernet0/0)上的HTTPS訪問ASA:
ciscoasa# configure terminal
ciscoasa(config)# http 0.0.0.0 0.0.0.0 outside步驟4.驗證是否可以從CSM伺服器訪問HTTPS。
開啟任何Web瀏覽器並鍵入下一個語法:
https://< ASA IP address >/這會轉換為上一步中允許HTTPS訪問的outside介面IP地址的下一個示例:
https://10.8.4.11/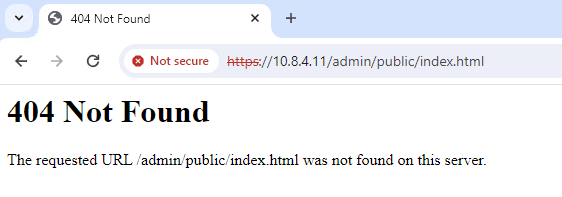 ASA HTTPS響應
ASA HTTPS響應

提示:此步驟中預計出現錯誤404 Not Found,因為此ASA未安裝思科自適應安全裝置管理器(ASDM),但頁面重定向到URL /admin/public/index.html時,會出現HTTPS響應。
將安全防火牆ASA調配到CSM
步驟1.開啟並登入CSM客戶端。
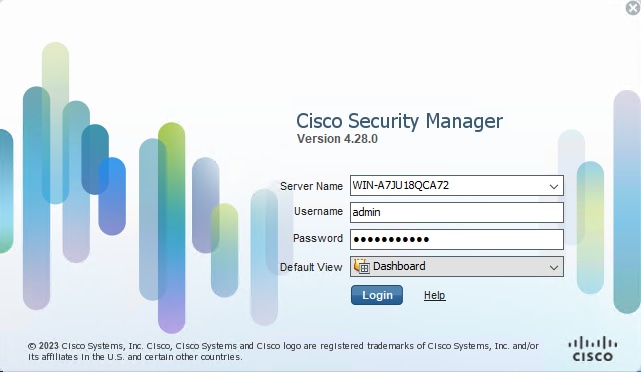 CSM客戶端登入
CSM客戶端登入
步驟2.開啟配置管理器。
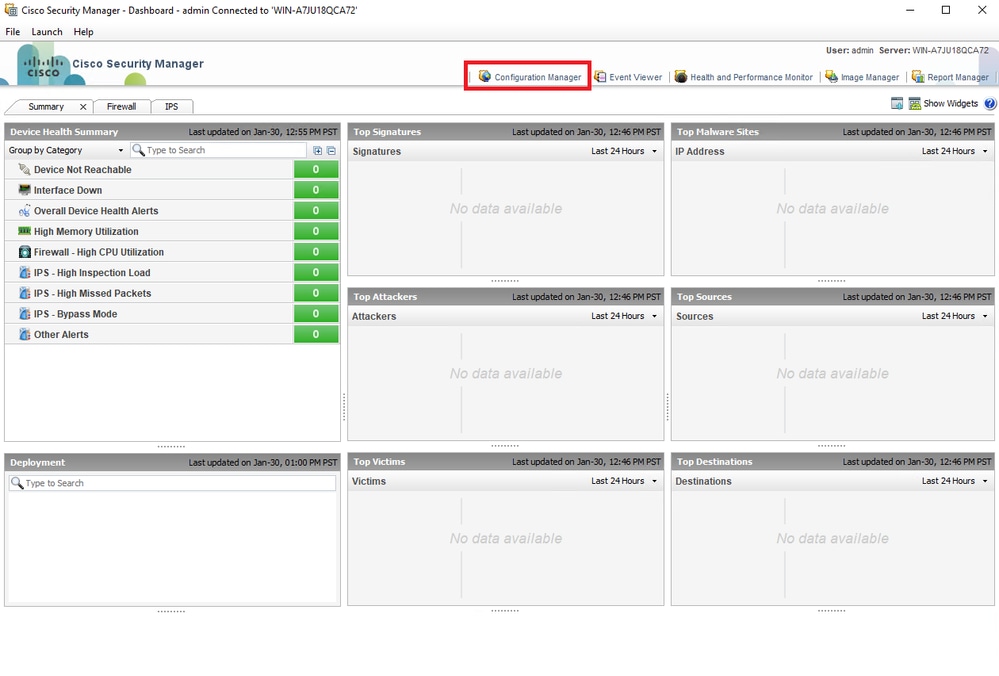 CSM客戶端控制面板
CSM客戶端控制面板
步驟3.導覽至Devices > New Device。
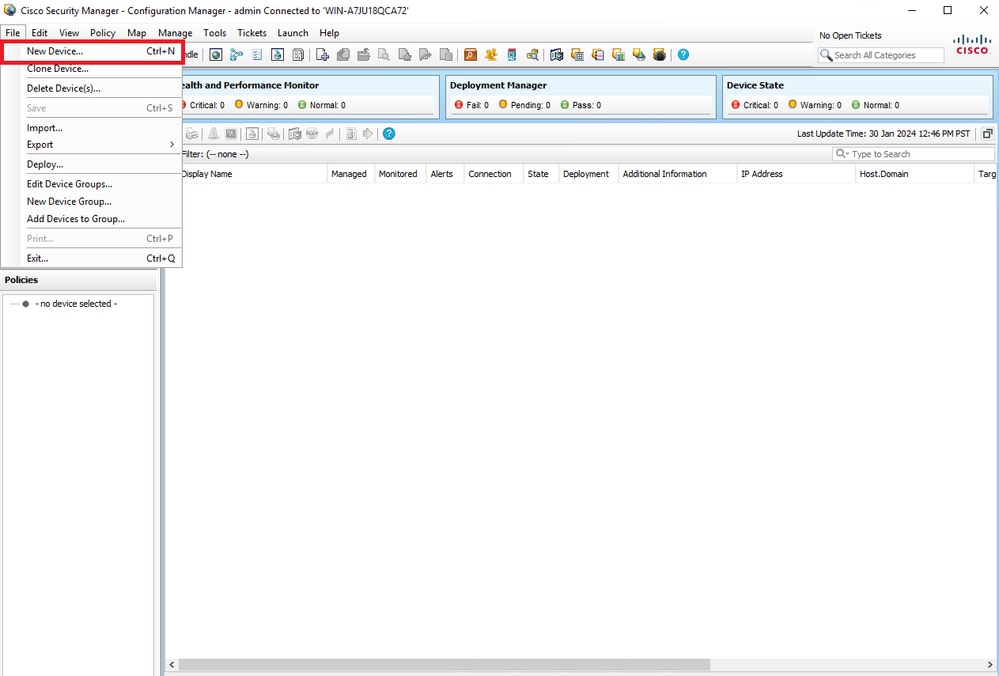 CSM配置管理器
CSM配置管理器
步驟4.根據所需結果選擇滿足要求的新增選項。由於網路中已設定了配置的ASA,因此此示例的最佳選項是Add Device From Network,然後按一下Next。
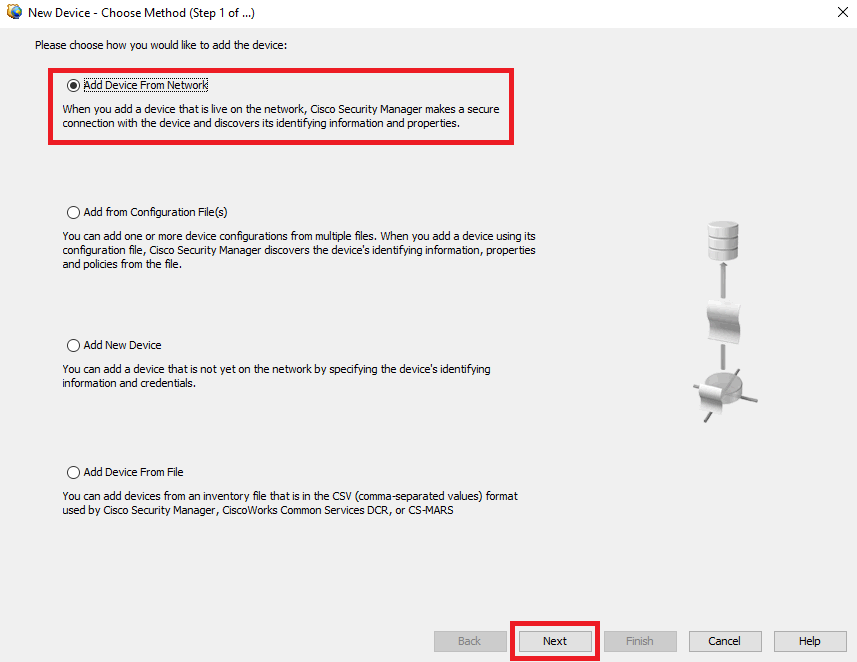 裝置新增方法
裝置新增方法
步驟5.根據安全防火牆ASA上的配置和發現設定完成所需資料。然後,按一下Next。
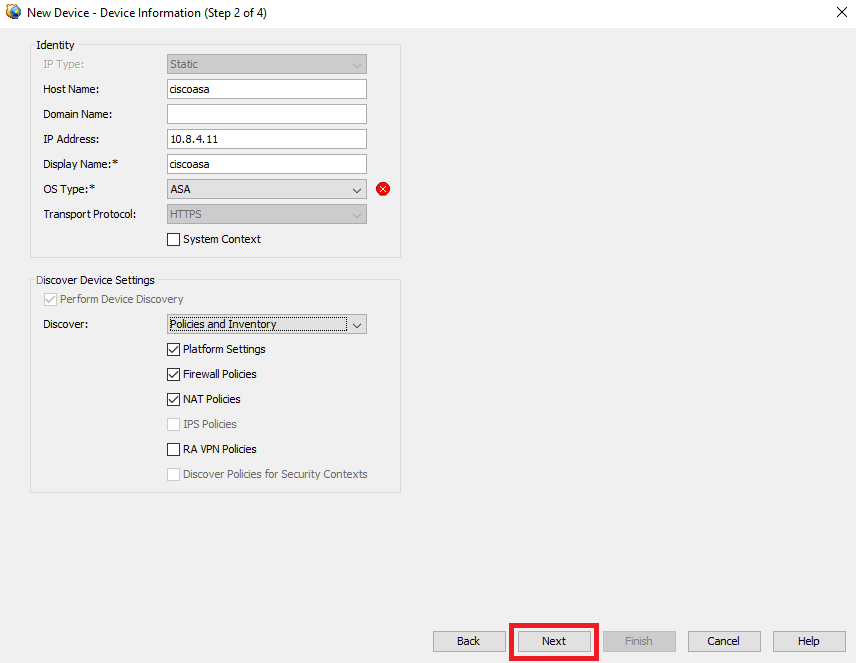 ASA設定
ASA設定
步驟6.從ASA上配置的CSM使用者和enable密碼完成所需的憑據。
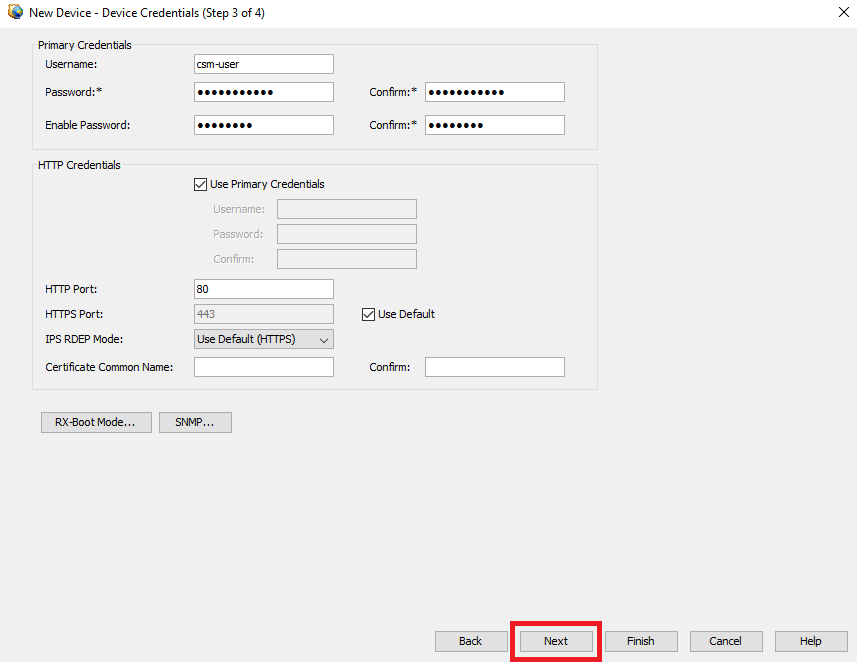 ASA憑據
ASA憑據
步驟7.選擇所需的組,或在不需要時跳過此步驟,然後按一下完成。
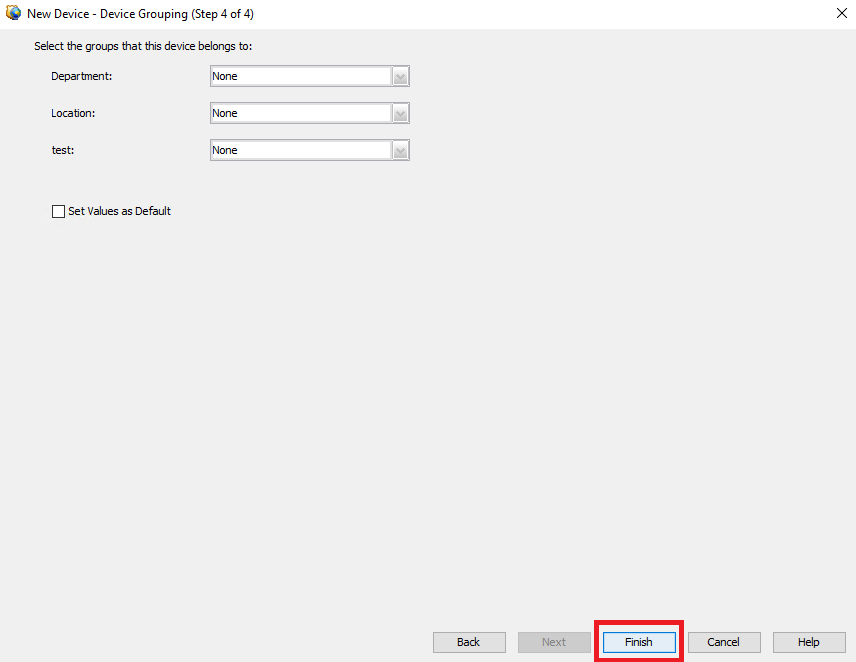 CSM組選擇
CSM組選擇
步驟8.出於控制目的生成票證請求,請按一下OK。
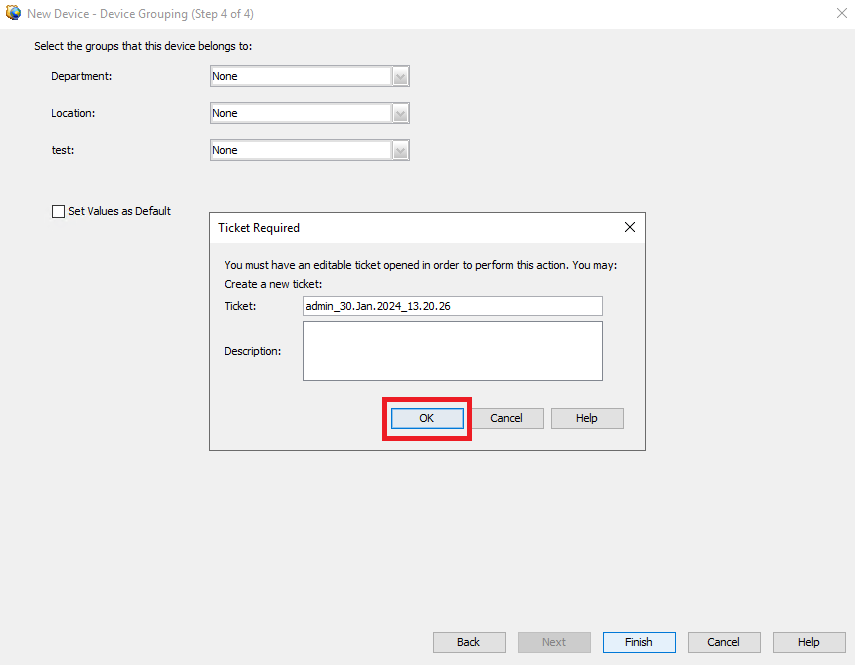 CSM票證建立
CSM票證建立
步驟9.驗證發現過程是否無錯誤,然後按一下Close。
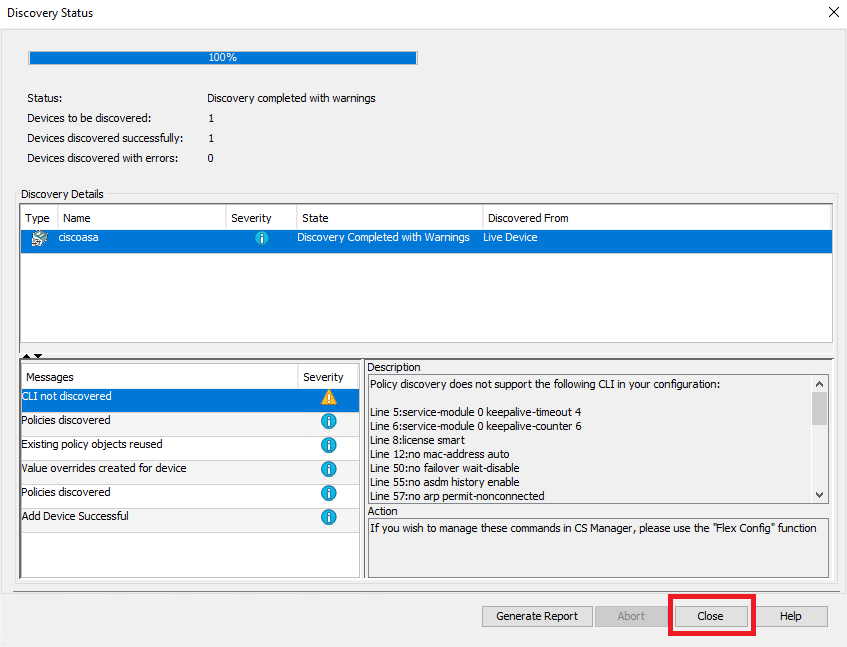 ASA發現
ASA發現

提示:警告被接受為成功輸出,因為CSM並不支援所有ASA功能。
步驟10.驗證ASA現在是否顯示為CSM客戶端上已註冊並顯示正確的資訊。
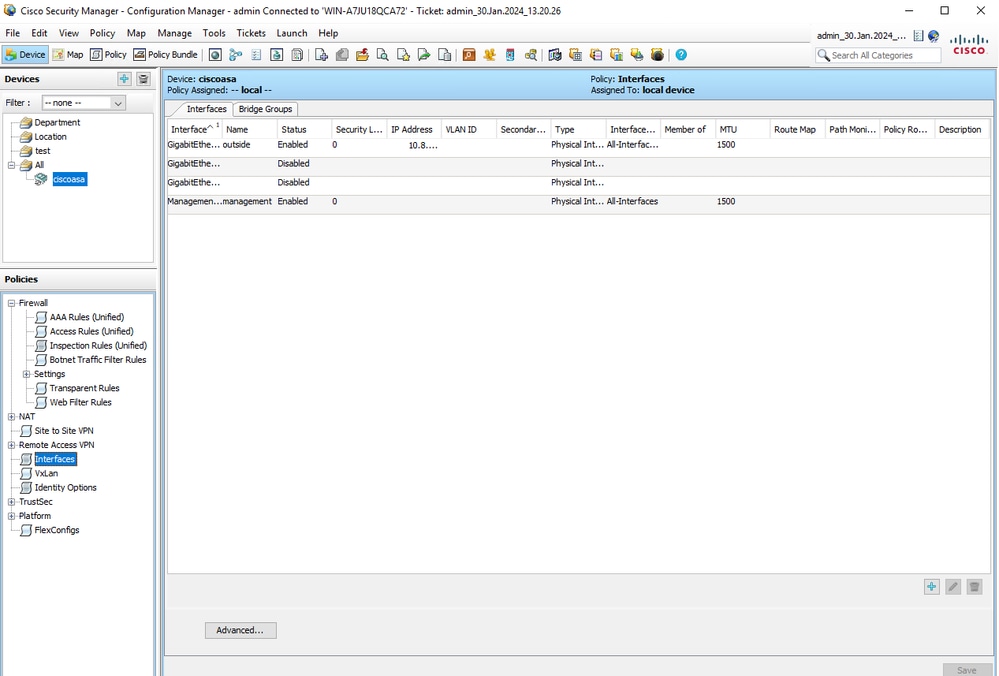 已註冊ASA資訊
已註冊ASA資訊
驗證
ASA上提供HTTPS調試用於故障排除。使用下一個命令:
debug http以下是CSM註冊調試成功的示例:
ciscoasa# debug http
debug http enabled at level 1.
ciscoasa# HTTP: processing handoff to legacy admin server [/admin/exec//show%20version]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20version HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒^^u
HTTP: processing GET URL '/admin/exec//show%20version' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/config]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/config HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒e
HTTP: processing GET URL '/admin/config' from host 10.8.4.12
HTTP: Authentication username = ''
HTTP: processing handoff to legacy admin server [/admin/exec//show%20version]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20version HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒^^u
HTTP: processing GET URL '/admin/exec//show%20version' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//sh%20module%20%7c%20in%20(CX%20Security%20Services%20Processor-%7ccxsc%20ASA%20CX5)]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//sh%20module%20%7c%20in%20(CX%20Security%20Services%20Processor-%7ccxsc%20ASA%20CX5) HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒^2▒^aware_123▒
HTTP: processing GET URL '/admin/exec//sh%20module%20%7c%20in%20(CX%20Security%20Services%20Processor-%7ccxsc%20ASA%20CX5)' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//sh%20module%20%7c%20in%20(FirePOWER)]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//sh%20module%20%7c%20in%20(FirePOWER) HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒▒▒▒
HTTP: processing GET URL '/admin/exec//sh%20module%20%7c%20in%20(FirePOWER)' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//sh%20cluster%20info]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//sh%20cluster%20info HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒^
HTTP: processing GET URL '/admin/exec//sh%20cluster%20info' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//sh%20inventory]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//sh%20inventory HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒^^u
HTTP: processing GET URL '/admin/exec//sh%20inventory' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//sh%20vm]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//sh%20vm HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒
2▒^^^u
HTTP: processing GET URL '/admin/exec//sh%20vm' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/config]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/config HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒e
HTTP: processing GET URL '/admin/config' from host 10.8.4.12
HTTP: Authentication username = ''
HTTP: processing handoff to legacy admin server [/admin/exec//show%20version]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20version HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒^^u
HTTP: processing GET URL '/admin/exec//show%20version' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20inventory]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20inventory HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒u
HTTP: processing GET URL '/admin/exec//show%20inventory' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20password%20encryption]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20password%20encryption HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒^^
HTTP: processing GET URL '/admin/exec//show%20password%20encryption' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20running-config%20all%20tunnel-group]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20running-config%20all%20tunnel-group HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒2▒^▒^e
HTTP: processing GET URL '/admin/exec//show%20running-config%20all%20tunnel-group' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20running-config%20all%20group-policy]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20running-config%20all%20group-policy HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒2▒^▒^e
HTTP: processing GET URL '/admin/exec//show%20running-config%20all%20group-policy' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20crypto%20ca%20trustpool%20detail]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20crypto%20ca%20trustpool%20detail HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒2▒^2▒^▒^e
HTTP: processing GET URL '/admin/exec//show%20crypto%20ca%20trustpool%20detail' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20snmp-server%20engineID]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20snmp-server%20engineID HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒^P_▒
HTTP: processing GET URL '/admin/exec//show%20snmp-server%20engineID' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20version]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20version HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒▒^u
HTTP: processing GET URL '/admin/exec//show%20version' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20failover]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20failover HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒^u
HTTP: processing GET URL '/admin/exec//show%20failover' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//dir%20%2frecursive%20all-filesystems]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//dir%20%2frecursive%20all-filesystems HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒2▒^2▒^2▒^▒^e
HTTP: processing GET URL '/admin/exec//dir%20%2frecursive%20all-filesystems' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20asdm%20image]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20asdm%20image HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒^
2▒^^^
HTTP: processing GET URL '/admin/exec//show%20asdm%20image' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20running-config%20webvpn]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20running-config%20webvpn HTTP/1.1
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
Cache-Control: no-cache
Pragma: no-cache
Host: 10.8.4.11
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
▒▒▒P_▒
HTTP: processing GET URL '/admin/exec//show%20running-config%20webvpn' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20vpn-sessiondb%20full%20webvpn]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20vpn-sessiondb%20full%20webvpn HTTP/1.1
Host: 10.8.4.1110.8.4.11
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
▒▒▒^2▒^1
HTTP: processing GET URL '/admin/exec//show%20vpn-sessiondb%20full%20webvpn' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20vpn-sessiondb%20full%20ra-ikev1-ipsec]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20vpn-sessiondb%20full%20ra-ikev1-ipsec HTTP/1.1
Host: 10.8.4.1110.8.4.11
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
▒▒▒
HTTP: processing GET URL '/admin/exec//show%20vpn-sessiondb%20full%20ra-ikev1-ipsec' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20vpn-sessiondb%20full%20ra-ikev2-ipsec]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20vpn-sessiondb%20full%20ra-ikev2-ipsec HTTP/1.1
Host: 10.8.4.1110.8.4.11
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
▒▒▒
HTTP: processing GET URL '/admin/exec//show%20vpn-sessiondb%20full%20ra-ikev2-ipsec' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
HTTP: processing handoff to legacy admin server [/admin/exec//show%20vpn-sessiondb%20full%20anyconnect]
HTTP: admin session verified = [0]
HTTP MSG: GET /admin/exec//show%20vpn-sessiondb%20full%20anyconnect HTTP/1.1
Host: 10.8.4.1110.8.4.11
Authorization: Basic OmNpc2NvMTIz
User-Agent: CSM
▒▒▒1
HTTP: processing GET URL '/admin/exec//show%20vpn-sessiondb%20full%20anyconnect' from host 10.8.4.12
HTTP: Authentication username = ''
Exited from HTTP Cli Exec
修訂記錄
| 修訂 | 發佈日期 | 意見 |
|---|---|---|
1.0 |
12-Feb-2024
|
初始版本 |
由思科工程師貢獻
- Carlos Eduardo Arteaga PortilloCisco Security Technical Consulting Engineer
 意見
意見