使用Rapid7配置ISE 2.2以威脅為中心的NAC (TC-NAC)
下載選項
無偏見用語
本產品的文件集力求使用無偏見用語。針對本文件集的目的,無偏見係定義為未根據年齡、身心障礙、性別、種族身分、民族身分、性別傾向、社會經濟地位及交織性表示歧視的用語。由於本產品軟體使用者介面中硬式編碼的語言、根據 RFP 文件使用的語言,或引用第三方產品的語言,因此本文件中可能會出現例外狀況。深入瞭解思科如何使用包容性用語。
關於此翻譯
思科已使用電腦和人工技術翻譯本文件,讓全世界的使用者能夠以自己的語言理解支援內容。請注意,即使是最佳機器翻譯,也不如專業譯者翻譯的內容準確。Cisco Systems, Inc. 對這些翻譯的準確度概不負責,並建議一律查看原始英文文件(提供連結)。
目錄
簡介
本文檔介紹如何在身份服務引擎(ISE) 2.2上使用Rapid7配置以威脅為中心的NAC並進行故障排除。 威脅中心網路訪問控制(TC-NAC)功能使您能夠根據從威脅和漏洞介面卡接收的威脅和漏洞屬性建立授權策略。
必要條件
需求
思科建議您瞭解以下主題的基本知識:
-
思科身分辨識服務引擎
-
Nexpose漏洞掃描程式
採用元件
本文中的資訊係根據以下軟體和硬體版本:
- 思科身分辨識服務引擎版本2.2
- Cisco Catalyst 2960S交換器15.2(2a)E1
- Rapid7 Nexpose漏洞掃描程式企業版
- Windows 7 Service Pack 1
- Windows Server 2012 R2
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路正在作用,請確保您已瞭解任何指令可能造成的影響。
設定
高級流程圖
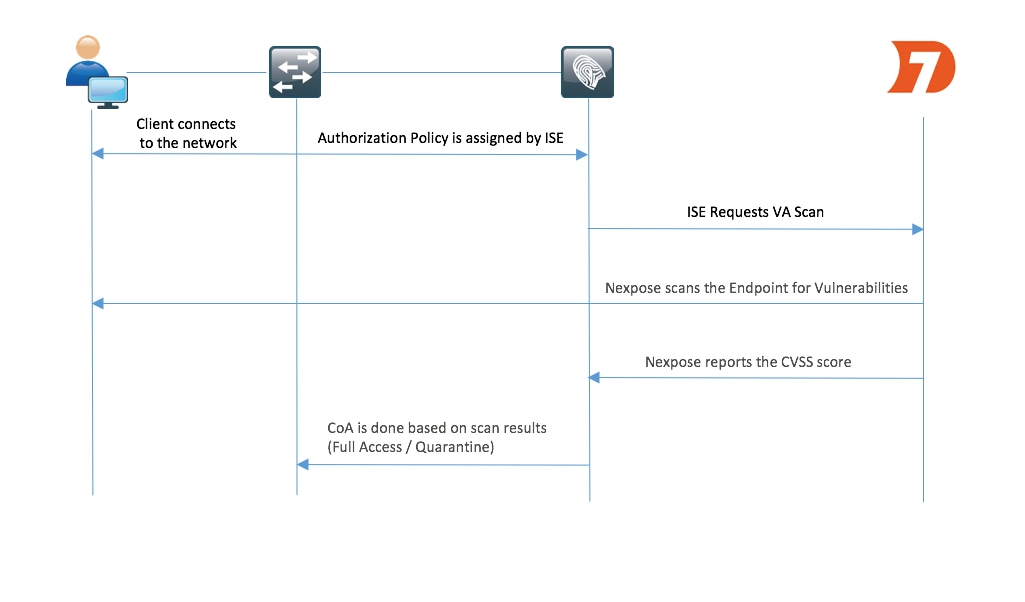
流程如下:
- 客戶端連線到網路,有限訪問被指定,並且配置檔案被指定,並選中Assess Vulnerabilities覈取方塊。
- PSN節點向MNT節點傳送系統日誌消息,確認身份驗證已發生,並且VA Scan是授權策略的結果。
- MNT節點使用以下資料向TC-NAC節點(使用管理WebApp)提交SCAN:
-MAC 地址
-IP 位址
- 掃描間隔
- 定期掃描已啟用
- 來源PSN - Nexpose TC-NAC(封裝在Docker容器中)與Nexpose掃描器通訊,以觸發掃描(如果需要)。
- Nexpose掃描程式掃描ISE請求的終端。
- Nexpose掃描程式將掃描結果傳送到ISE。
- 掃描結果將傳送回TC-NAC:
-MAC 地址
- 所有CVSS評分
- 所有漏洞(標題、CVEID) - TC-NAC使用步驟7中的所有資料更新PAN。
- 如果需要,將根據配置的授權策略觸發CoA。
部署和配置Nexpose掃描器
注意:本文檔中的Nexpose配置出於實驗目的,請諮詢Rapid7工程師以瞭解設計注意事項
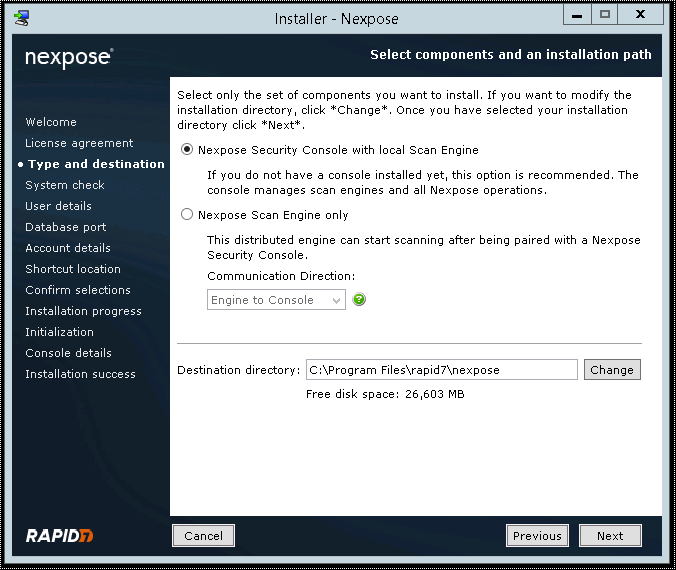
步驟 1.部署Nexpose掃描器。
Nexpose掃描器可從OVA檔案部署,安裝在Linux和Windows作業系統之上。在本檔案中,安裝是在Windows Server 2012 R2上完成的。從Rapid7網站下載映像並開始安裝。配置型別和目標時,選擇Nexpose Security Console with local Scan Engine
安裝完成後,伺服器將重新啟動。啟動後,Nexpose掃描器應可透過3780埠訪問,如下圖所示:
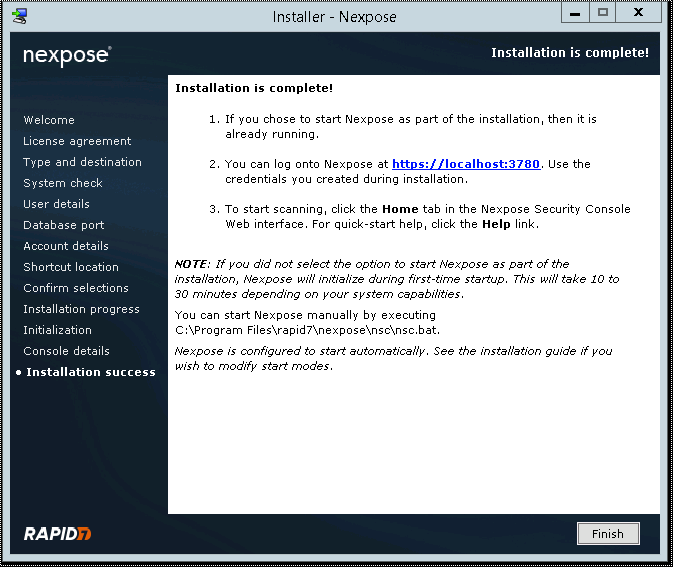
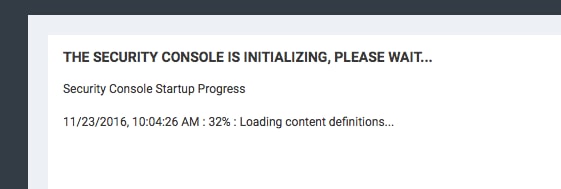
如圖所示,掃描器會經歷安全控制檯啟動過程:
之後若要存取GUI,應該提供授權金鑰。請注意,需要Enterprise Edition of Nexpose Scanner,如果安裝了Community Edition,則不會觸發掃描。
步驟 2.設定Nexpose掃描器。
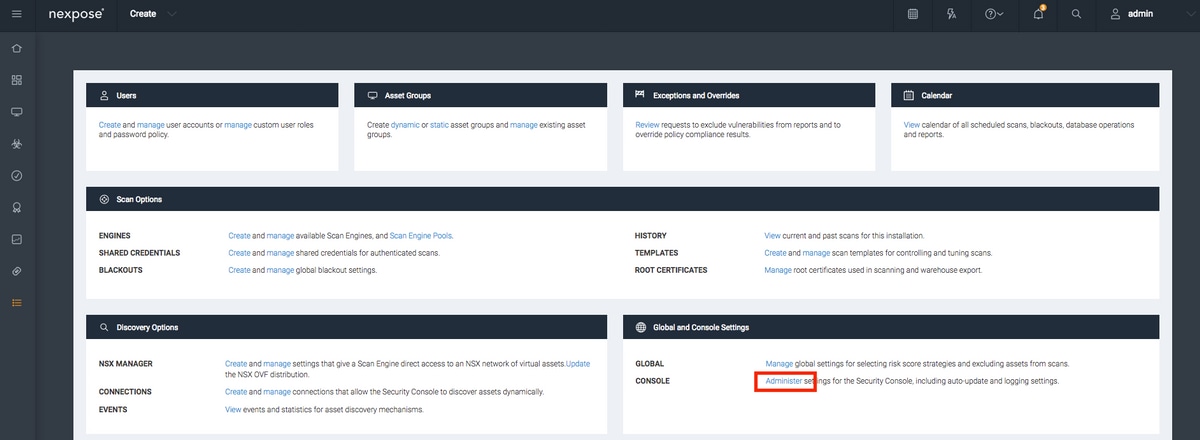
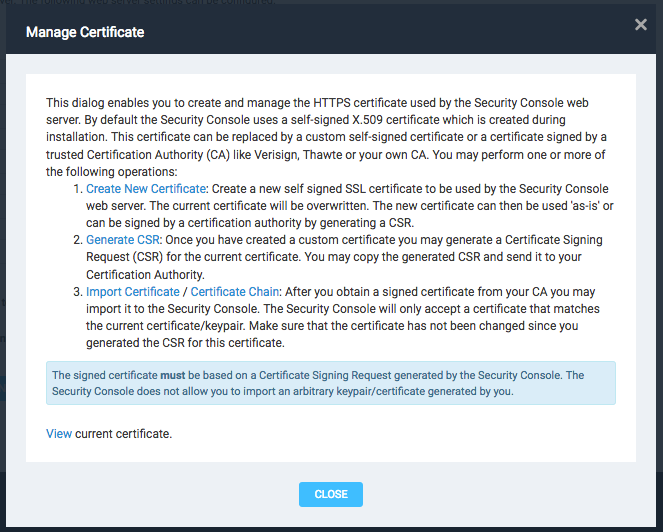
第一步是在Nexpose掃描器上安裝證書。本文檔中的證書由與ISE的管理證書(實驗室CA)相同的CA頒發。導航到管理>全局和控制檯設定。選擇控制檯下的管理,如圖所示。
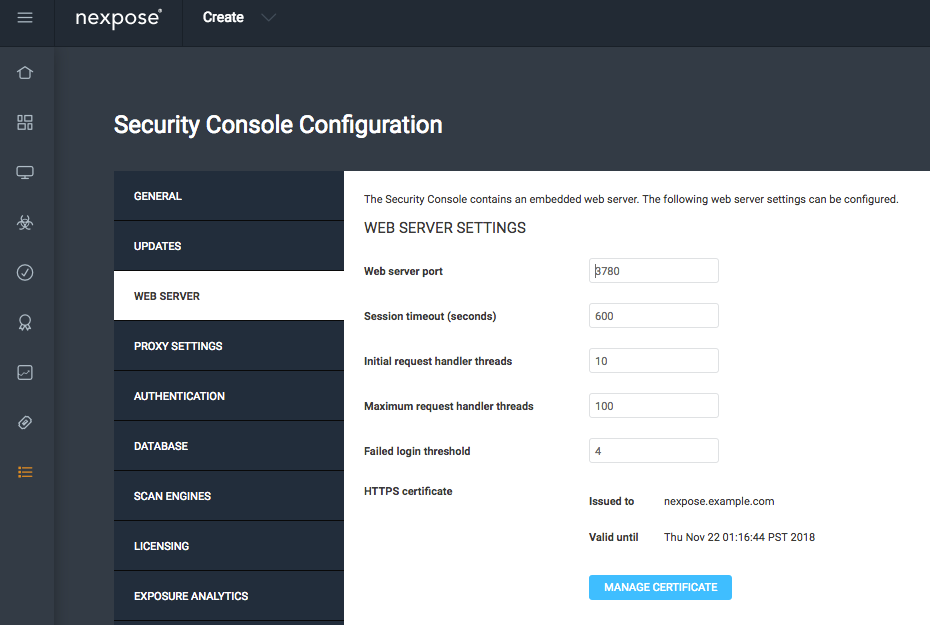
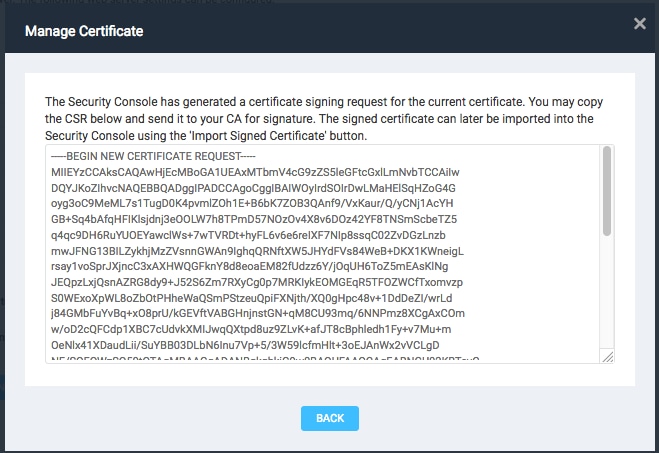
點選管理證書,如圖所示:
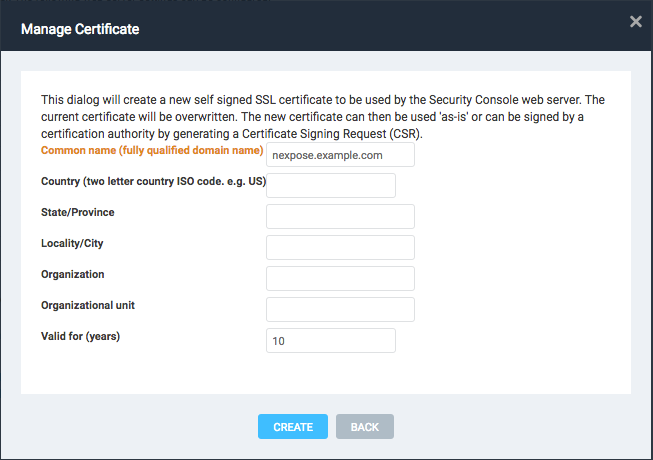
如圖所示,在建立新證書中按一下。輸入常用名以及您希望在Nexpose掃描器的身份證書中擁有的任何其他資料。確保ISE能夠使用DNS解析Nexpose掃描器FQDN。
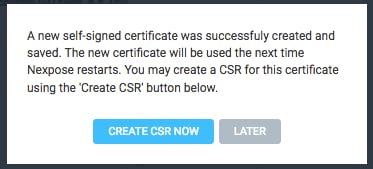
將證書簽名請求(CSR)導出到終端。
此時,您需要使用憑證授權單位(CA)簽署CSR。
透過按一下導入證書導入CA頒發的證書。
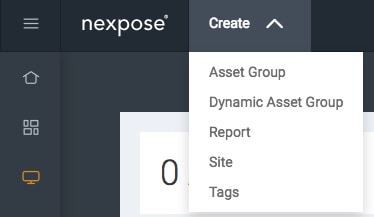
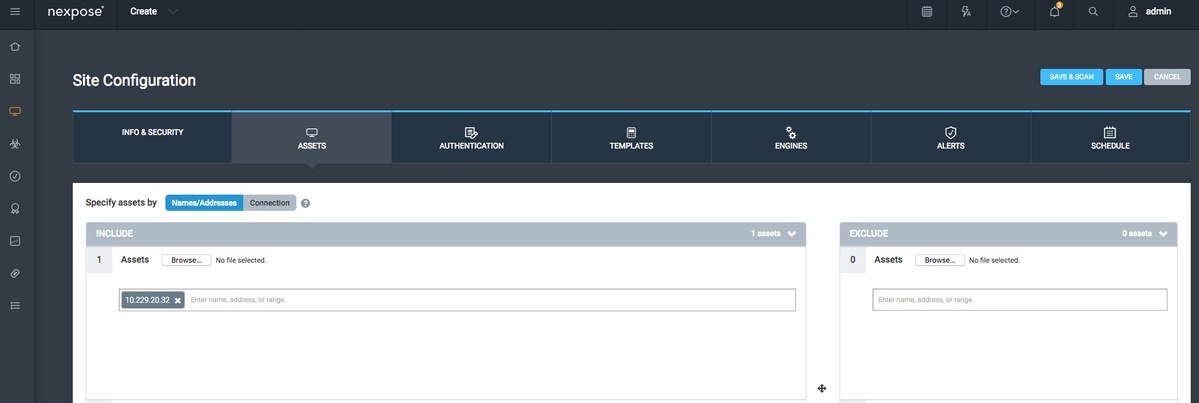
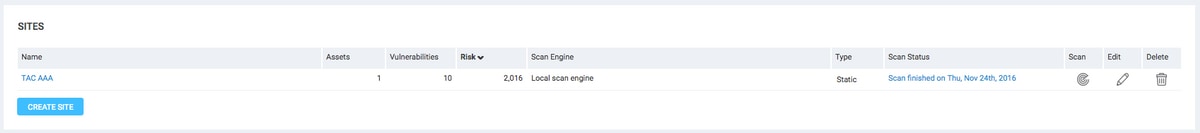
配置站點。站點包含您應該能夠掃描的資產,並且用於將ISE與Nexpose掃描器整合的帳戶應具有管理站點和建立報告的許可權。導航到建立>站點,如圖所示。
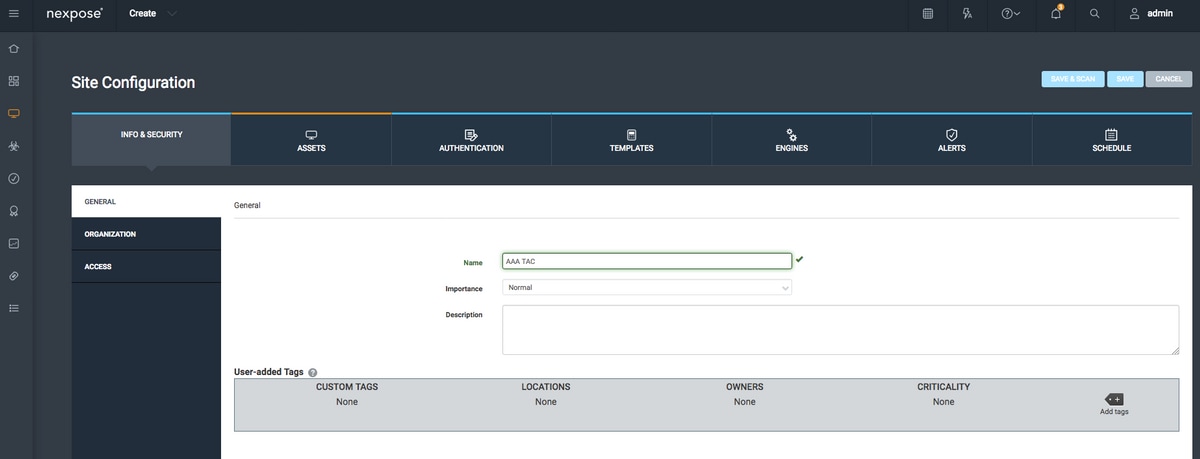
如圖所示,在Info & Security頁籤上輸入Name的站點。Assets頁籤應包含有效資產的ip地址,即符合漏洞掃描條件的終端。
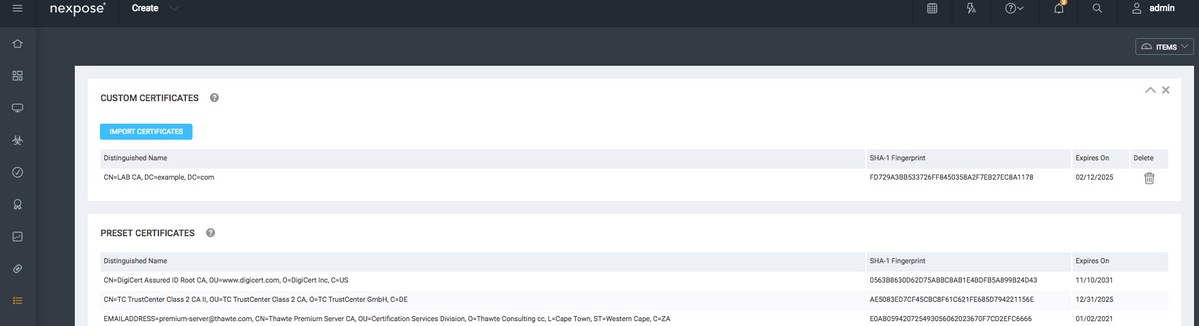
將已簽署ISE證書的CA證書導入到受信任的儲存中。導航到管理>根證書>管理>導入證書。
配置ISE
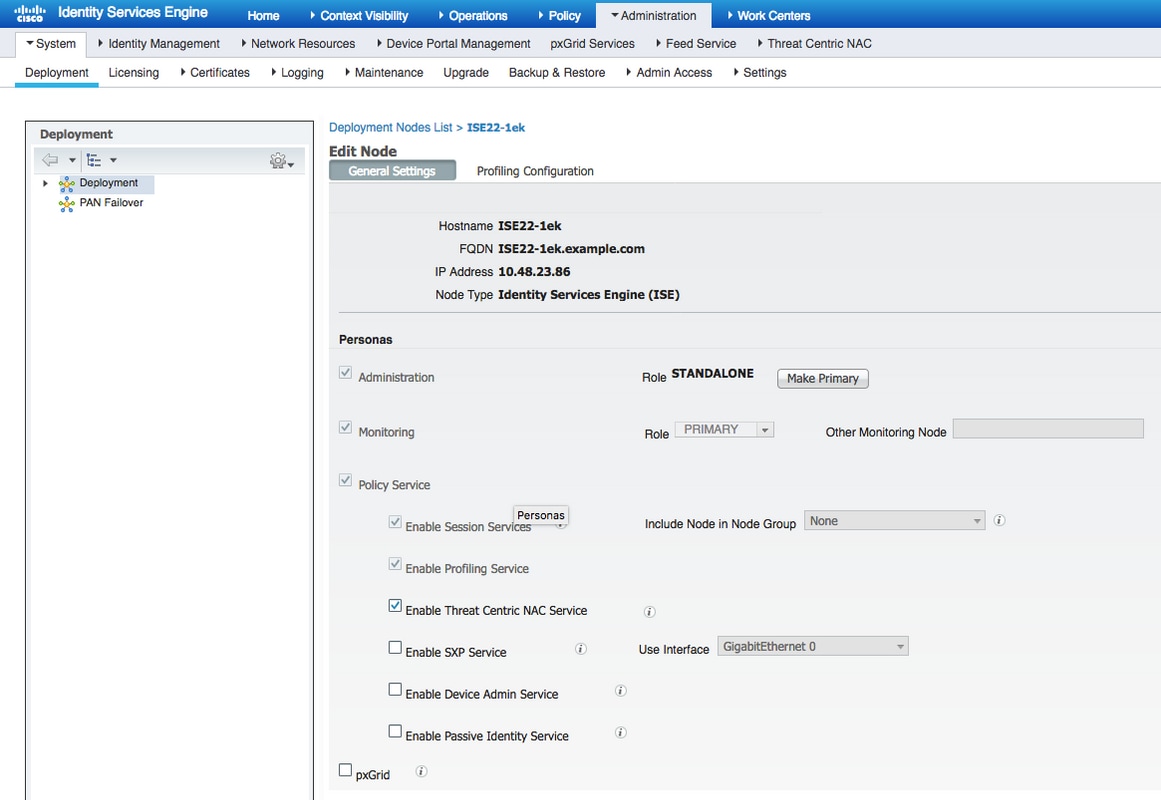
步驟 1.啟用TC-NAC服務。
在ISE節點上啟用TC-NAC服務。請注意以下事項:
- 以威脅為中心的NAC服務需要Apex許可證。
- 您需要一個單獨的策略服務節點(PSN),用於以威脅為中心的NAC服務。
- 在部署中僅可在一個節點上啟用以威脅為中心的NAC服務。
- 對於漏洞評估服務,每個供應商只能增加一個介面卡例項。
步驟 2.匯入Nexpose掃描器憑證。
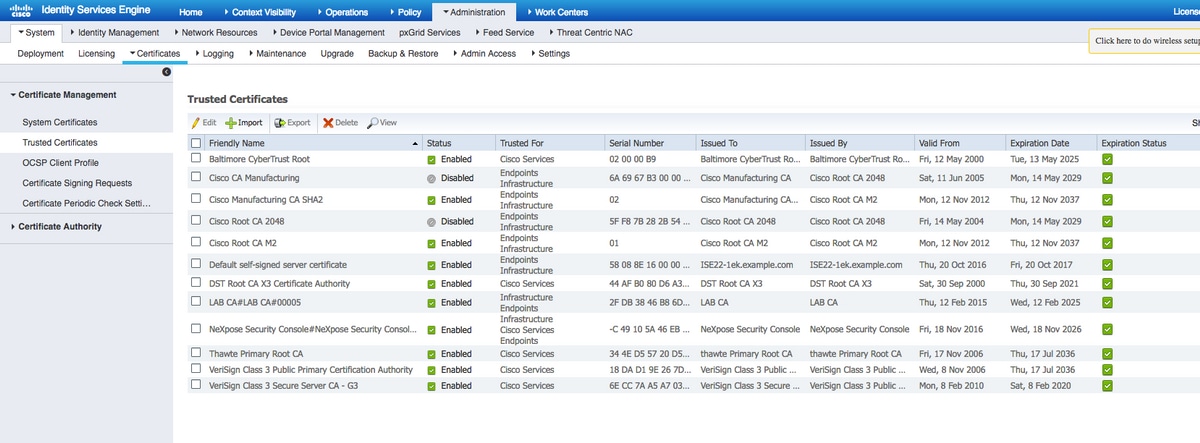
將Nexpose掃描器CA證書導入到思科ISE中的受信任證書庫中(Administration > Certificates > Certificate Management > Trusted Certificates > Import)。確保適當的根證書和中間證書導入(或存在)思科ISE受信任證書儲存中
步驟 3.配置Nexpose掃描器TC-NAC例項。
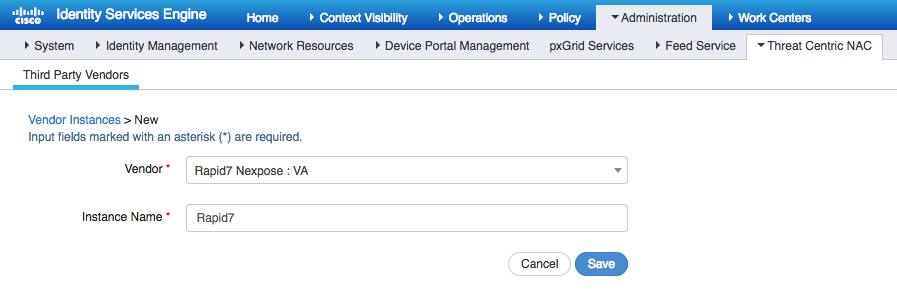
在Administration > Threat Centric NAC > Third Party Vendors處增加Rapid7例項。
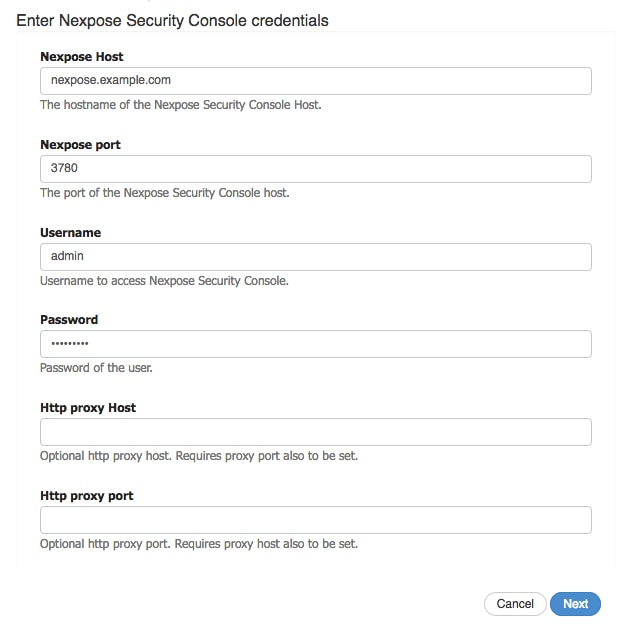
增加例項後,例項會轉換為Ready to Configure狀態。按一下此連結。配置Nexpose主機(掃描程式)和埠,預設值為3780。指定有權訪問正確站點的Username和Password。
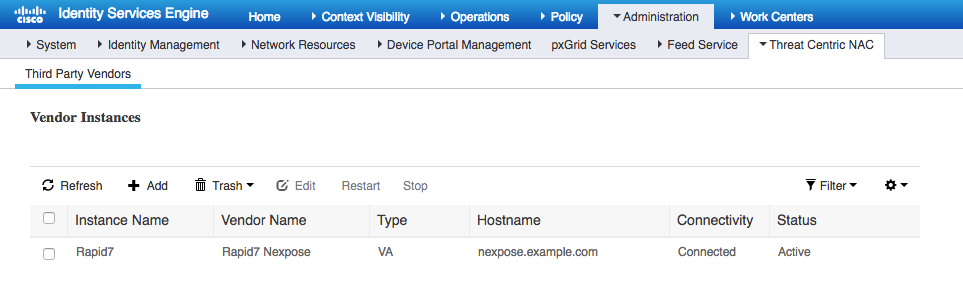
高級設定在《ISE 2.2管理指南》中有詳細記錄,可以在本文檔的「參考」部分找到該連結。按一下下一步和完成。「Nexpose例項」轉換為活動狀態並開始下載知識庫。
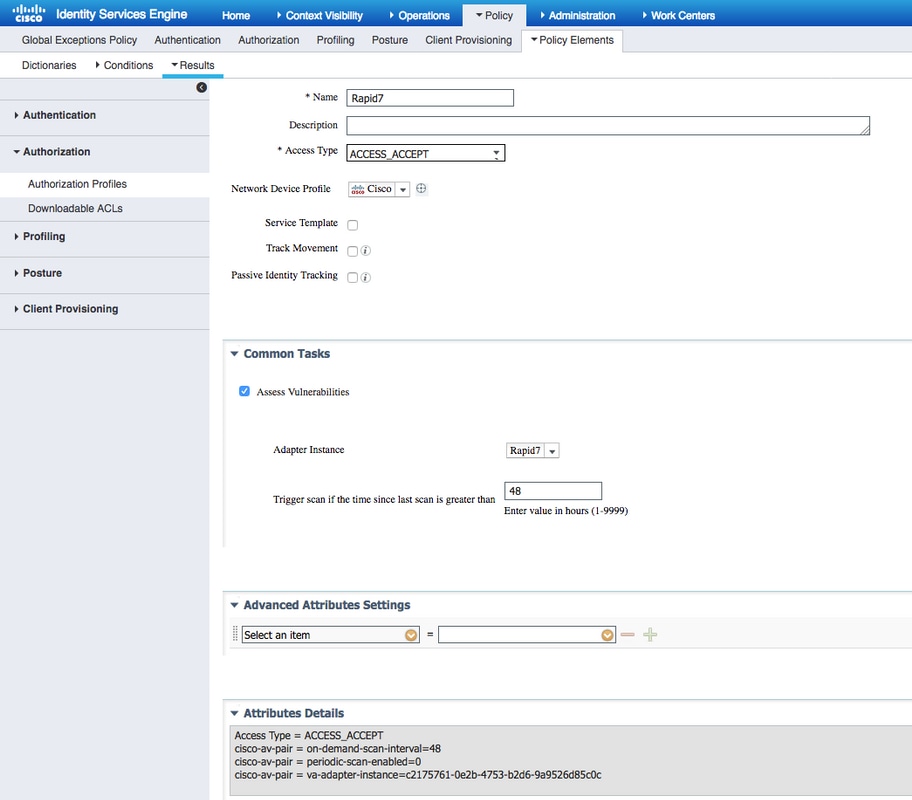
步驟 4.配置授權配置檔案以觸發VA掃描。
導航到策略>策略元素>結果>授權>授權配置檔案。新增設定檔。在Common Tasks下,選中Vulnerability Assessment覈取方塊。應根據您的網路設計選擇按需掃描間隔。
授權配置檔案包含這些av對:
cisco-av-pair = on-demand-scan-interval=48 cisco-av-pair = periodic-scan-enabled=0 cisco-av-pair = va-adapter-instance=c2175761-0e2b-4753-b2d6-9a9526d85c0c
它們被傳送到接入接受資料包內的網路裝置,儘管它們的真正目的是告知監控(MNT)節點應觸發掃描。MNT指示TC-NAC節點與Nexpose掃描器通訊。
步驟 5.配置授權策略。
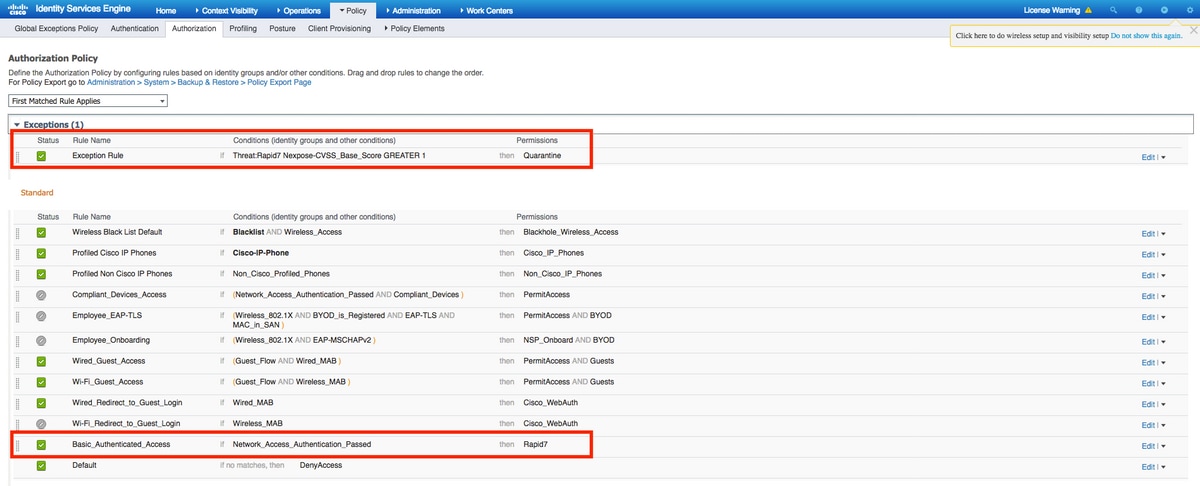
- 配置授權策略以使用步驟4中配置的新授權配置檔案。導航到策略>授權>授權策略,找到Basic_Authenticated_Access規則,然後按一下編輯。將許可權從PermitAccess更改為新建立的Standard Rapid7。這會導致對所有使用者進行漏洞掃描。按一下Save。
- 為隔離的電腦建立授權策略。導航到策略>授權>授權策略>例外,並建立例外規則。現在導航到條件>建立新條件(高級選項)>選擇屬性,向下滾動並選擇威脅。展開Threat屬性並選擇Nexpose-CVSS_Base_Score。將運算子更改為大於,並根據您的安全策略輸入一個值。隔離授權配置檔案應該為易受攻擊的電腦提供有限的訪問許可權。
驗證
身分辨識服務引擎
第一個連線觸發VA掃描。掃描完成後,如果新策略匹配,將觸發CoA重新身份驗證以應用新策略。
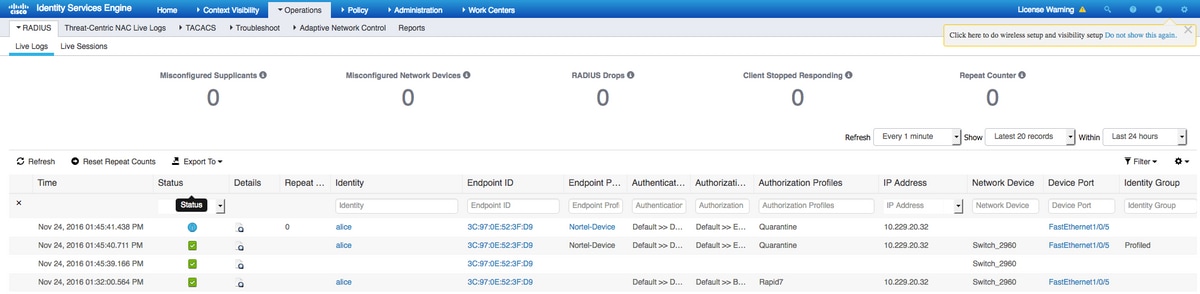
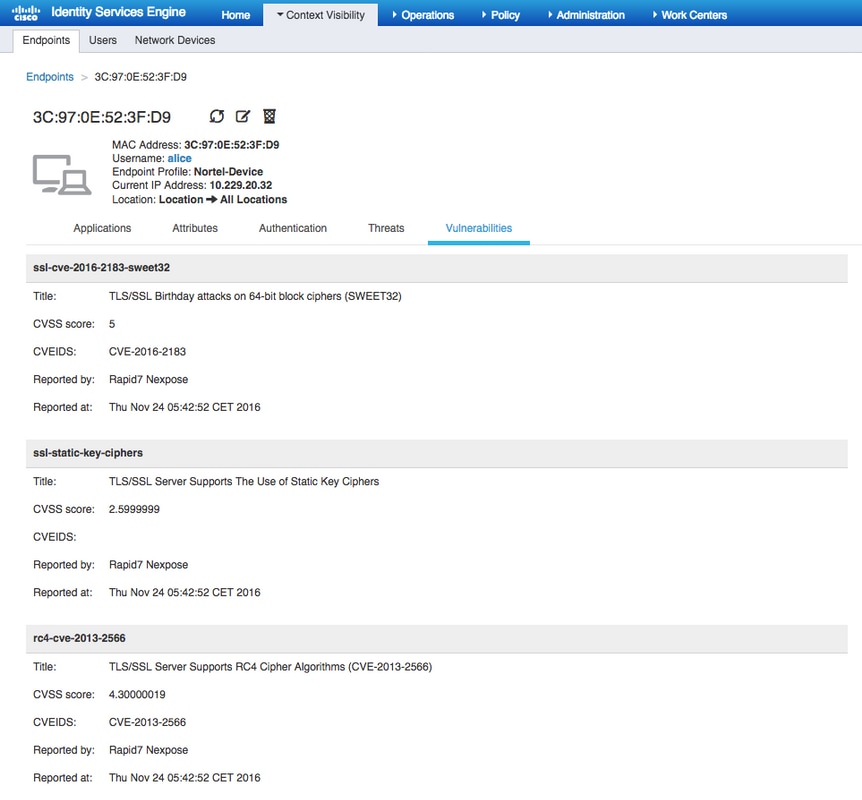
要驗證檢測到的是哪些漏洞,請導航到環境可視性>終端。使用Nexpose Scanner為其提供的評分檢查每個終端的漏洞。
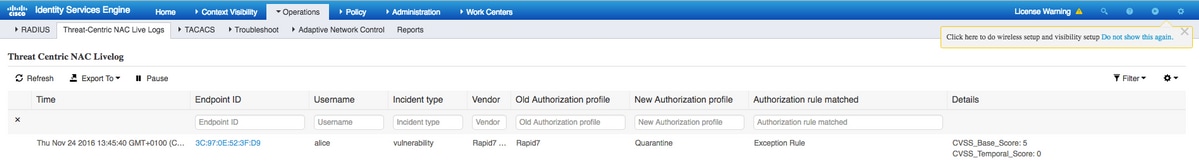
在操作(Operations) > TC-NAC即時日誌(TC-NAC Live Logs)中,您可以檢視應用的授權策略以及CVSS_Base_Score的詳細資訊。
Nexpose掃描器
當VA掃描由TC-NAC Nexpose Scan觸發並轉換為In-Progress狀態,且掃描程式開始探測終端時,如果在終端上運行wireshark捕獲,此時您將看到終端站與掃描程式之間的資料包交換。掃描程式完成後,在首頁下即可獲得結果。
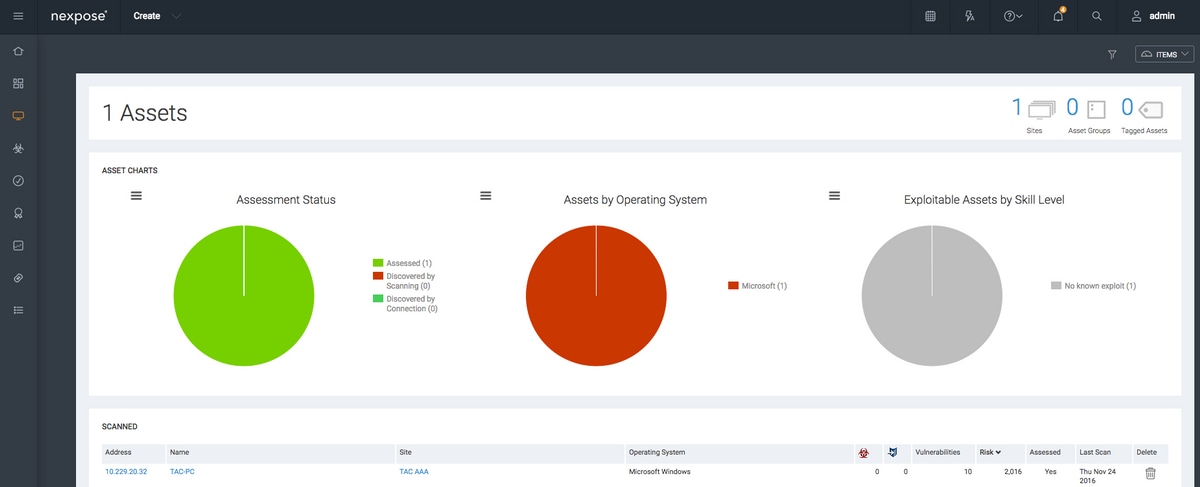
在Assets頁面下,您可以看到掃描結果顯示存在新的可用終結點,已辨識作業系統,並已檢測到10個漏洞。
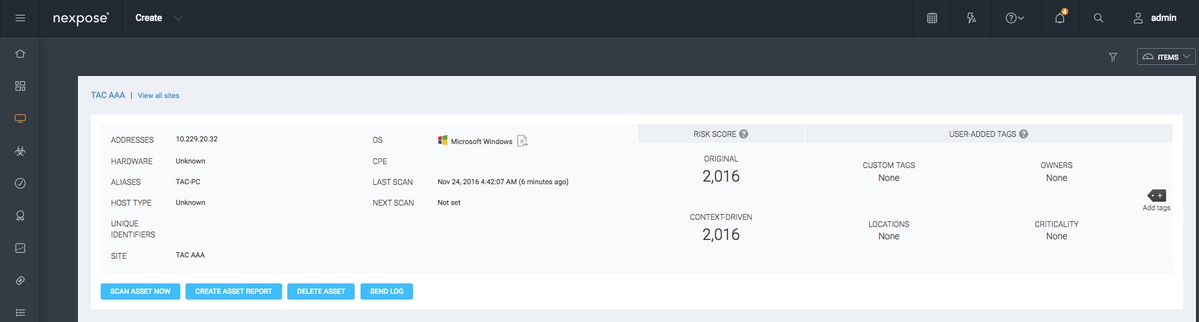
當您點選終端的IP地址Nexpose Scanner時,您會看到新選單,您可以在其中看到包括主機名、Risc評分和漏洞詳細清單的更多資訊
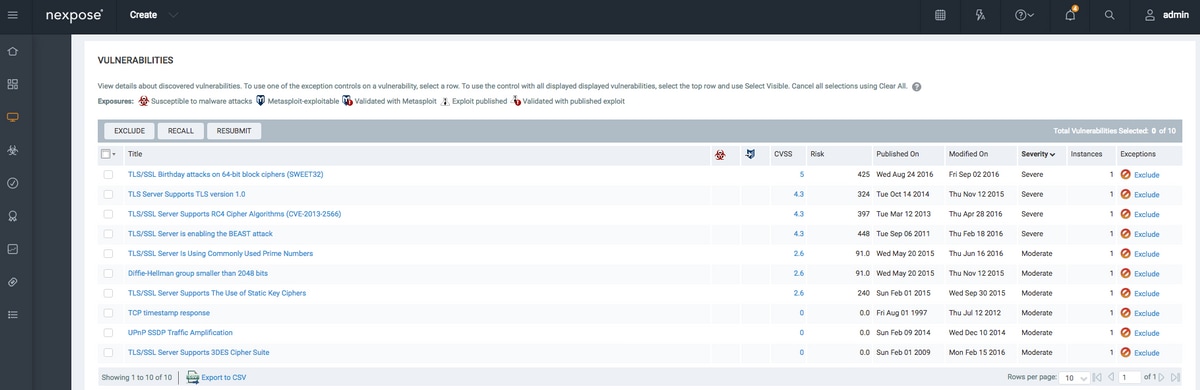
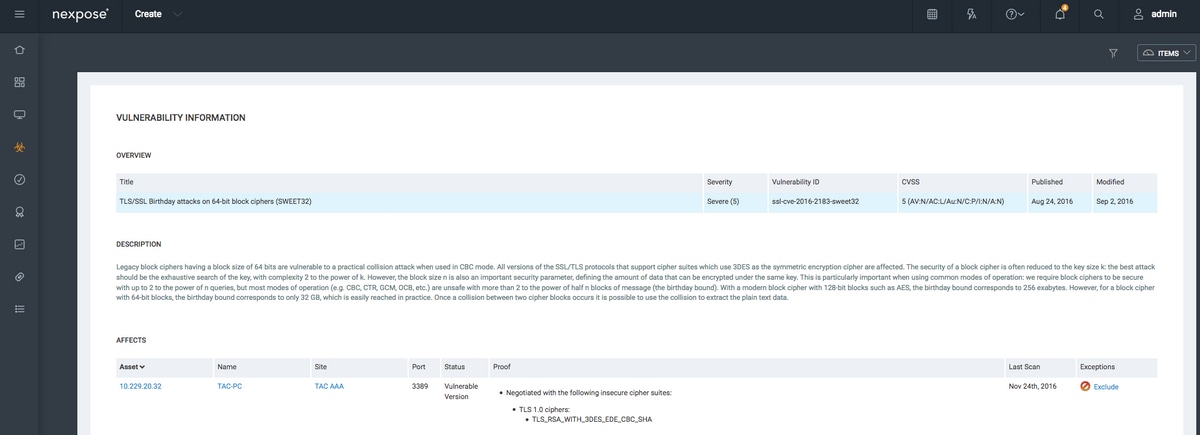
按一下Vulnerability本身時,圖中顯示完整的說明。
疑難排解
ISE上的調試
為了在ISE上啟用調試,請導航到Administration > System > Logging > Debug Log Configuration,選擇TC-NAC Node,並將Log Level va-runtime和va-service元件更改為DEBUG。

要檢查的日誌- varuntime.log。您可以直接從ISE CLI跟蹤它:
ISE21-3ek/admin# show logging application varuntime.log tail
TC-NAC Docker收到針對特定終端執行掃描的指令。
2016-11-24 13:32:04,436 DEBUG [Thread-94][] va.runtime.admin.mnt.EndpointFileReader -:::::- VA: Read va runtime. [{"operationType":1,"macAddress":"3C:97:0E:52:3F:D9","ipAddress":"10.229.20.32","ondemandScanInterval":"48","isPeriodicScanEnabled":false,"periodicScanEnabledString":"0","vendorInstance":"c2175761-0e2b-4753-b2d6-9a9526d85c0c","psnHostName":"ISE22-1ek","heartBeatTime":0,"lastScanTime":0}, {"operationType":1,"macAddress":"3C:97:0E:52:3F:D9","ipAddress":"10.229.20.32","isPeriodicScanEnabled":false,"heartBeatTime":0,"lastScanTime":0}]
2016-11-24 13:32:04,437 DEBUG [Thread-94][] va.runtime.admin.vaservice.VaServiceRemotingHandler -:::::- VA: received data from Mnt: {"operationType":1,"macAddress":"3C:97:0E:52:3F:D9","ipAddress":"10.229.20.32","ondemandScanInterval":"48","isPeriodicScanEnabled":false,"periodicScanEnabledString":"0","vendorInstance":"c2175761-0e2b-4753-b2d6-9a9526d85c0c","psnHostName":"ISE22-1ek","heartBeatTime":0,"lastScanTime":0}
2016-11-24 13:32:04,439 DEBUG [Thread-94][] va.runtime.admin.vaservice.VaServiceRemotingHandler -:::::- VA: received data from Mnt: {"operationType":1,"macAddress":"3C:97:0E:52:3F:D9","ipAddress":"10.229.20.32","isPeriodicScanEnabled":false,"heartBeatTime":0,"lastScanTime":0}
收到結果後,它會將所有漏洞資料儲存在上下文目錄中。
2016-11-24 13:45:28,378 DEBUG [Thread-94][] va.runtime.admin.vaservice.VaServiceRemotingHandler -:::::- VA: received data from Mnt: {"operationType":2,"isPeriodicScanEnabled":false,"heartBeatTime":1479991526437,"lastScanTime":0}
2016-11-24 13:45:33,642 DEBUG [pool-115-thread-19][] va.runtime.admin.vaservice.VaServiceMessageListener -:::::- Got message from VaService: [{"macAddress":"3C:97:0E:52:3F:D9","ipAddress":"10.229.20.32","lastScanTime":1479962572758,"vulnerabilities":["{\"vulnerabilityId\":\"ssl-cve-2016-2183-sweet32\",\"cveIds\":\"CVE-2016-2183\",\"cvssBaseScore\":\"5\",\"vulnerabilityTitle\":\"TLS/SSL Birthday attacks on 64-bit block ciphers (SWEET32)\",\"vulnerabilityVendor\":\"Rapid7 Nexpose\"}","{\"vulnerabilityId\":\"ssl-static-key-ciphers\",\"cveIds\":\"\",\"cvssBaseScore\":\"2.5999999\",\"vulnerabilityTitle\":\"TLS/SSL Server Supports The Use of Static Key Ciphers\",\"vulnerabilityVendor\":\"Rapid7 Nexpose\"}","{\"vulnerabilityId\":\"rc4-cve-2013-2566\",\"cveIds\":\"CVE-2013-2566\",\"cvssBaseScore\":\"4.30000019\",\"vulnerabilityTitle\":\"TLS/SSL Server Supports RC4 Cipher Algorithms (CVE-2013-2566)\",\"vulnerabilityVendor\":\"Rapid7 Nexpose\"}","{\"vulnerabilityId\":\"tls-dh-prime-under-2048-bits\",\"cveIds\":\"\",\"cvssBaseScore\":\"2.5999999\",\"vulnerabilityTitle\":\"Diffie-Hellman group smaller than 2048 bits\",\"vulnerabilityVendor\":\"Rapid7 Nexpose\"}","{\"vulnerabilityId\":\"tls-dh-primes\",\"cveIds\":\"\",\"cvssBaseScore\":\"2.5999999\",\"vulnerabilityTitle\":\"TLS/SSL Server Is Using Commonly Used Prime Numbers\",\"vulnerabilityVendor\":\"Rapid7 Nexpose\"}","{\"vulnerabilityId\":\"ssl-cve-2011-3389-beast\",\"cveIds\":\"CVE-2011-3389\",\"cvssBaseScore\":\"4.30000019\",\"vulnerabilityTitle\":\"TLS/SSL Server is enabling the BEAST attack\",\"vulnerabilityVendor\":\"Rapid7 Nexpose\"}","{\"vulnerabilityId\":\"tlsv1_0-enabled\",\"cveIds\":\"\",\"cvssBaseScore\":\"4.30000019\",\"vulnerabilityTitle\":\"TLS Server Supports TLS version 1.0\",\"vulnerabilityVendor\":\"Rapid7 Nexpose\"}"]}]
2016-11-24 13:45:33,643 DEBUG [pool-115-thread-19][] va.runtime.admin.vaservice.VaServiceMessageListener -:::::- VA: Save to context db, lastscantime: 1479962572758, mac: 3C:97:0E:52:3F:D9
2016-11-24 13:45:33,675 DEBUG [pool-115-thread-19][] va.runtime.admin.vaservice.VaPanRemotingHandler -:::::- VA: Saved to elastic search: {3C:97:0E:52:3F:D9=[{"vulnerabilityId":"ssl-cve-2016-2183-sweet32","cveIds":"CVE-2016-2183","cvssBaseScore":"5","vulnerabilityTitle":"TLS/SSL Birthday attacks on 64-bit block ciphers (SWEET32)","vulnerabilityVendor":"Rapid7 Nexpose"}, {"vulnerabilityId":"ssl-static-key-ciphers","cveIds":"","cvssBaseScore":"2.5999999","vulnerabilityTitle":"TLS/SSL Server Supports The Use of Static Key Ciphers","vulnerabilityVendor":"Rapid7 Nexpose"}, {"vulnerabilityId":"rc4-cve-2013-2566","cveIds":"CVE-2013-2566","cvssBaseScore":"4.30000019","vulnerabilityTitle":"TLS/SSL Server Supports RC4 Cipher Algorithms (CVE-2013-2566)","vulnerabilityVendor":"Rapid7 Nexpose"}, {"vulnerabilityId":"tls-dh-prime-under-2048-bits","cveIds":"","cvssBaseScore":"2.5999999","vulnerabilityTitle":"Diffie-Hellman group smaller than 2048 bits","vulnerabilityVendor":"Rapid7 Nexpose"}, {"vulnerabilityId":"tls-dh-primes","cveIds":"","cvssBaseScore":"2.5999999","vulnerabilityTitle":"TLS/SSL Server Is Using Commonly Used Prime Numbers","vulnerabilityVendor":"Rapid7 Nexpose"}, {"vulnerabilityId":"ssl-cve-2011-3389-beast","cveIds":"CVE-2011-3389","cvssBaseScore":"4.30000019","vulnerabilityTitle":"TLS/SSL Server is enabling the BEAST attack","vulnerabilityVendor":"Rapid7 Nexpose"}, {"vulnerabilityId":"tlsv1_0-enabled","cveIds":"","cvssBaseScore":"4.30000019","vulnerabilityTitle":"TLS Server Supports TLS version 1.0","vulnerabilityVendor":"Rapid7 Nexpose"}]}
要檢查的日誌- vaservice.log。您可以直接從ISE CLI跟蹤它:
ISE21-3ek/admin# show logging application vaservice.log tail
漏洞評估請求已提交至介面卡。
2016-11-24 12:32:05,783 DEBUG [endpointPollerScheduler-7][] cpm.va.service.util.VaServiceUtil -:::::- VA SendSyslog systemMsg : [{"systemMsg":"91019","isAutoInsertSelfAcsInstance":true,"attributes":["TC-NAC.ServiceName","Vulnerability Assessment Service","TC-NAC.Status","VA request submitted to adapter","TC-NAC.Details","VA request submitted to adapter for processing","TC-NAC.MACAddress","3C:97:0E:52:3F:D9","TC-NAC.IpAddress","10.229.20.32","TC-NAC.AdapterInstanceUuid","c2175761-0e2b-4753-b2d6-9a9526d85c0c","TC-NAC.VendorName","Rapid7 Nexpose","TC-NAC.AdapterInstanceName","Rapid7"]}]
2016-11-24 12:32:05,810 DEBUG [endpointPollerScheduler-7][] cpm.va.service.util.VaServiceUtil -:::::- VA SendSyslog systemMsg res: {"status":"SUCCESS","statusMessages":["SUCCESS"]}
AdapterMessageListener每隔5分鐘檢查一次掃描的狀態,直到掃描完成。
2016-11-24 12:36:28,143 DEBUG [SimpleAsyncTaskExecutor-2][] cpm.va.service.processor.AdapterMessageListener -:::::- Message from adapter : {"AdapterInstanceName":"Rapid7","AdapterInstanceUid":"7a2415e7-980d-4c0c-b5ed-fe4e9fadadbd","VendorName":"Rapid7 Nexpose","OperationMessageText":"Number of endpoints queued for checking scan results: 0, Number of endpoints queued for scan: 0, Number of endpoints for which the scan is in progress: 1"}
2016-11-24 12:36:28,880 DEBUG [endpointPollerScheduler-5][] cpm.va.service.util.VaServiceUtil -:::::- VA SendSyslog systemMsg : [{"systemMsg":"91019","isAutoInsertSelfAcsInstance":true,"attributes":["TC-NAC.ServiceName","Vulnerability Assessment Service","TC-NAC.Status","Adapter Statistics","TC-NAC.Details","Number of endpoints queued for checking scan results: 0, Number of endpoints queued for scan: 0, Number of endpoints for which the scan is in progress: 1","TC-NAC.AdapterInstanceUuid","7a2415e7-980d-4c0c-b5ed-fe4e9fadadbd","TC-NAC.VendorName","Rapid7 Nexpose","TC-NAC.AdapterInstanceName","Rapid7"]}]
介面卡會取得CVE以及CVSS評分。
2016-11-24 12:45:33,132 DEBUG [SimpleAsyncTaskExecutor-2][] cpm.va.service.processor.AdapterMessageListener -:::::- Message from adapter : {"returnedMacAddress":"","requestedMacAddress":"3C:97:0E:52:3F:D9","scanStatus":"ASSESSMENT_SUCCESS","lastScanTimeLong":1479962572758,"ipAddress":"10.229.20.32","vulnerabilities":[{"vulnerabilityId":"tlsv1_0-enabled","cveIds":"","cvssBaseScore":"4.30000019","vulnerabilityTitle":"TLS Server Supports TLS version 1.0","vulnerabilityVendor":"Rapid7 Nexpose"},{"vulnerabilityId":"rc4-cve-2013-2566","cveIds":"CVE-2013-2566","cvssBaseScore":"4.30000019","vulnerabilityTitle":"TLS/SSL Server Supports RC4 Cipher Algorithms (CVE-2013-2566)","vulnerabilityVendor":"Rapid7 Nexpose"},{"vulnerabilityId":"ssl-cve-2016-2183-sweet32","cveIds":"CVE-2016-2183","cvssBaseScore":"5","vulnerabilityTitle":"TLS/SSL Birthday attacks on 64-bit block ciphers (SWEET32)","vulnerabilityVendor":"Rapid7 Nexpose"},{"vulnerabilityId":"ssl-static-key-ciphers","cveIds":"","cvssBaseScore":"2.5999999","vulnerabilityTitle":"TLS/SSL Server Supports The Use of Static Key Ciphers","vulnerabilityVendor":"Rapid7 Nexpose"},{"vulnerabilityId":"tls-dh-primes","cveIds":"","cvssBaseScore":"2.5999999","vulnerabilityTitle":"TLS/SSL Server Is Using Commonly Used Prime Numbers","vulnerabilityVendor":"Rapid7 Nexpose"},{"vulnerabilityId":"tls-dh-prime-under-2048-bits","cveIds":"","cvssBaseScore":"2.5999999","vulnerabilityTitle":"Diffie-Hellman group smaller than 2048 bits","vulnerabilityVendor":"Rapid7 Nexpose"},{"vulnerabilityId":"ssl-cve-2011-3389-beast","cveIds":"CVE-2011-3389","cvssBaseScore":"4.30000019","vulnerabilityTitle":"TLS/SSL Server is enabling the BEAST attack","vulnerabilityVendor":"Rapid7 Nexpose"}]}
2016-11-24 12:45:33,137 INFO [SimpleAsyncTaskExecutor-2][] cpm.va.service.processor.AdapterMessageListener -:::::- Endpoint Details sent to IRF is {"3C:97:0E:52:3F:D9":[{"vulnerability":{"CVSS_Base_Score":5.0,"CVSS_Temporal_Score":0.0},"time-stamp":1479962572758,"title":"Vulnerability","vendor":"Rapid7 Nexpose"}]}
2016-11-24 12:45:33,221 DEBUG [endpointPollerScheduler-7][] cpm.va.service.util.VaServiceUtil -:::::- VA SendSyslog systemMsg : [{"systemMsg":"91019","isAutoInsertSelfAcsInstance":true,"attributes":["TC-NAC.ServiceName","Vulnerability Assessment Service","TC-NAC.Status","VA successfully completed","TC-NAC.Details","VA completed; number of vulnerabilities found: 7","TC-NAC.MACAddress","3C:97:0E:52:3F:D9","TC-NAC.IpAddress","10.229.20.32","TC-NAC.AdapterInstanceUuid","c2175761-0e2b-4753-b2d6-9a9526d85c0c","TC-NAC.VendorName","Rapid7 Nexpose","TC-NAC.AdapterInstanceName","Rapid7"]}]
2016-11-24 12:45:33,299 DEBUG [endpointPollerScheduler-7][] cpm.va.service.util.VaServiceUtil -:::::- VA SendSyslog systemMsg res: {"status":"SUCCESS","statusMessages":["SUCCESS"]}
相關資訊
修訂記錄
| 修訂 | 發佈日期 | 意見 |
|---|---|---|
1.0 |
14-Feb-2017 |
初始版本 |
由思科工程師貢獻
- 尤金·科爾內丘克Cisco TAC工程師
 意見
意見